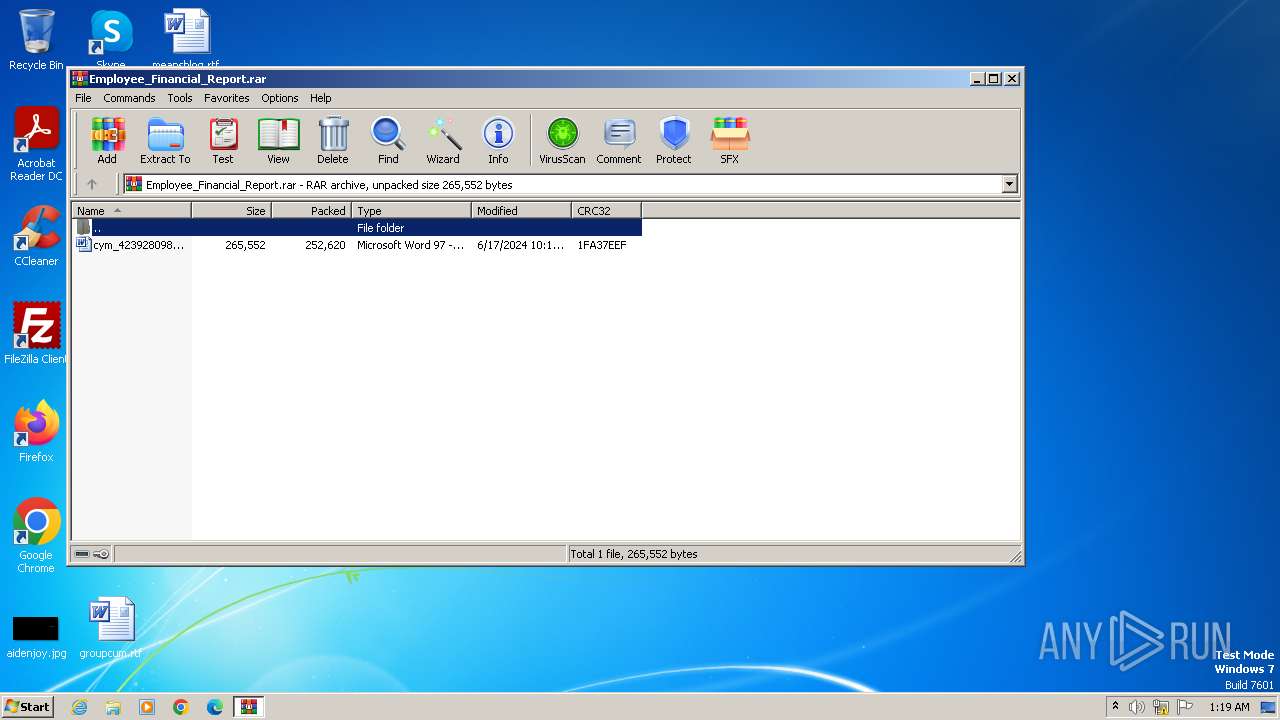
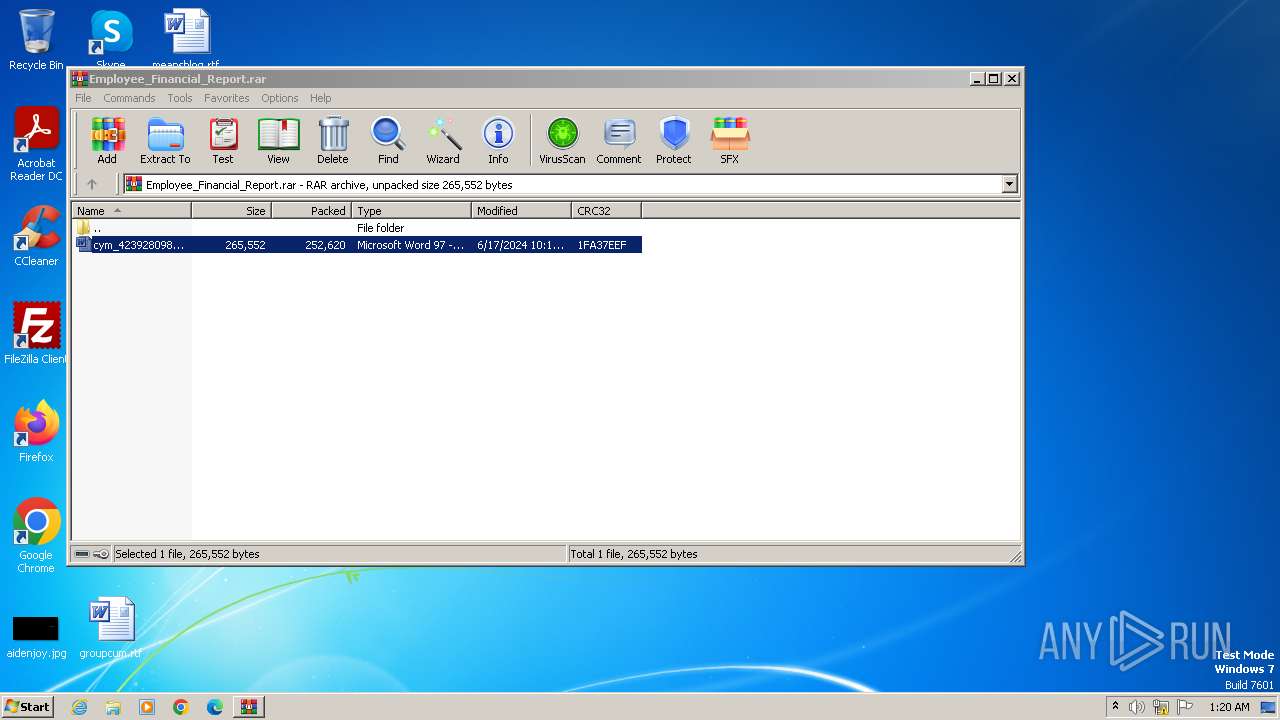
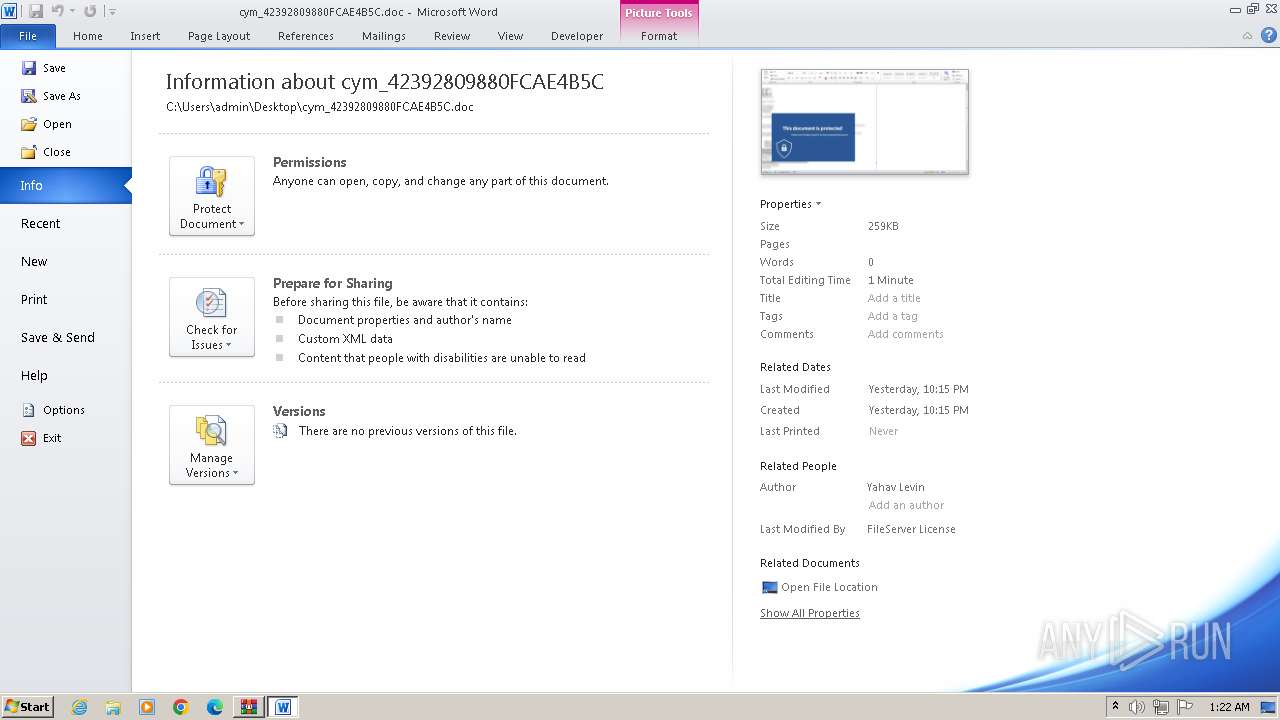
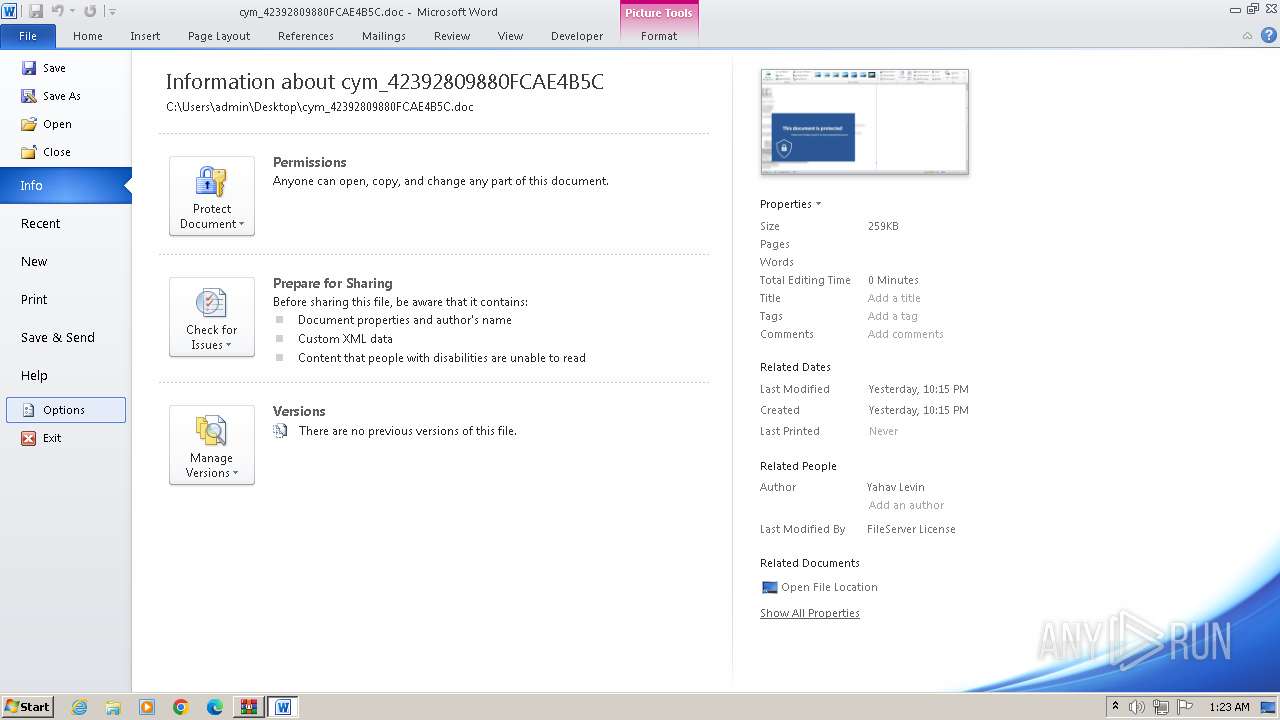
| File name: | Employee_Financial_Report.rar |
| Full analysis: | https://app.any.run/tasks/e47656ba-ce1e-4f15-8db9-d66fcff87087 |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2024, 00:19:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | DCB1CD3E7BE7BB2398A488F4ECC4FCE8 |
| SHA1: | E6B1317615B010A17B229D8F910ADEDFCA816180 |
| SHA256: | 31FC12A6B1D9746388404F015CD8E05F2316D5E1616788C745677D58CEAD6AD0 |
| SSDEEP: | 6144:fgSZxUcKL8abgG2120YvqtUlHpwmavusGZV0VzF7:fgCU18Vx1UvdFavujVIZ7 |
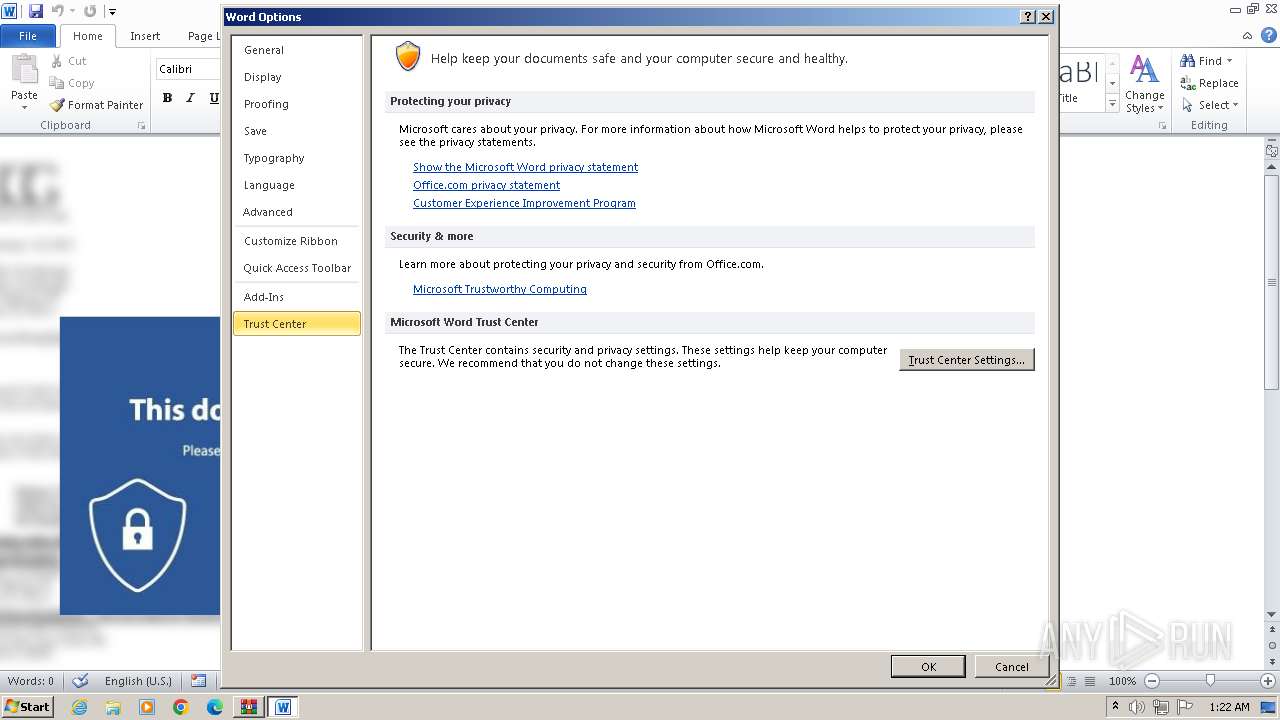
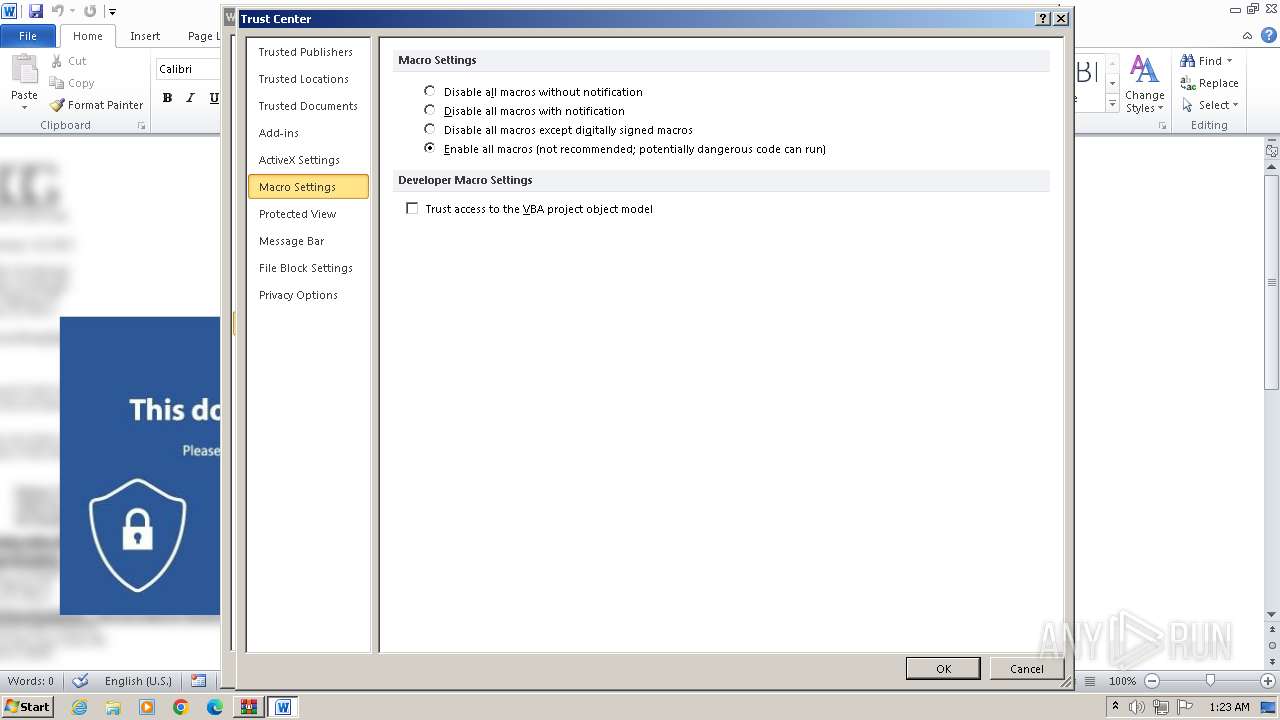
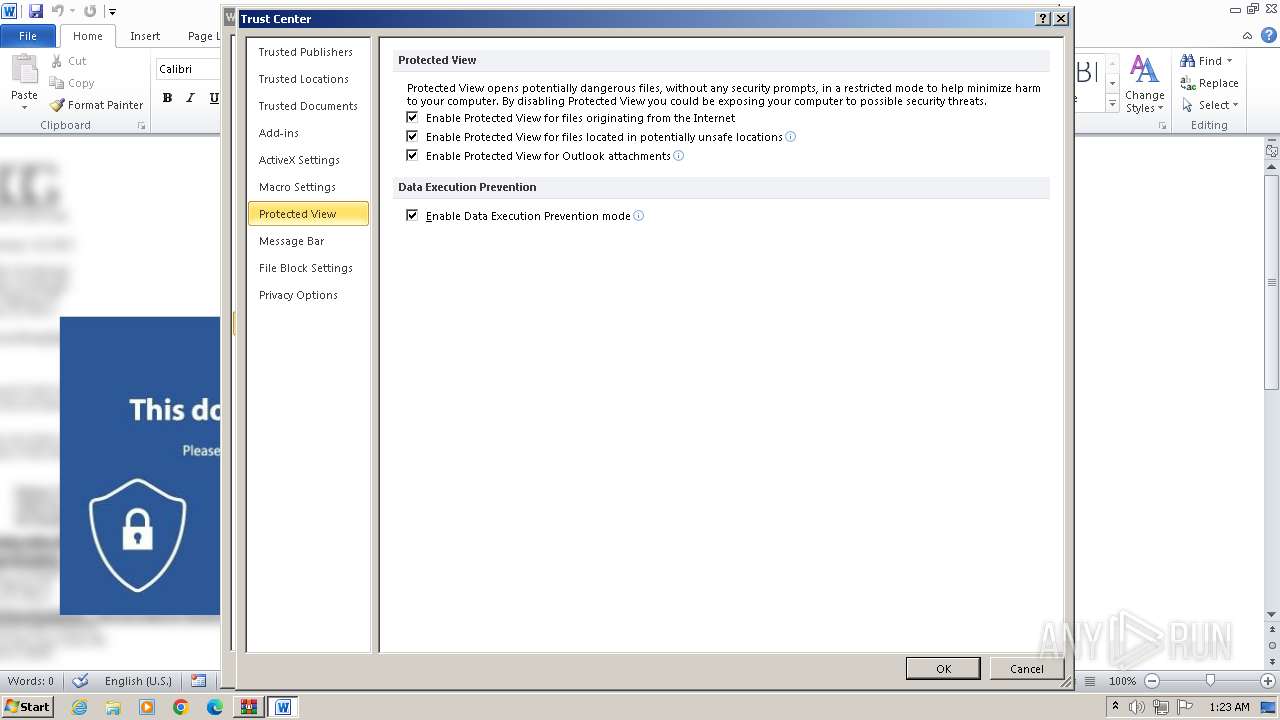
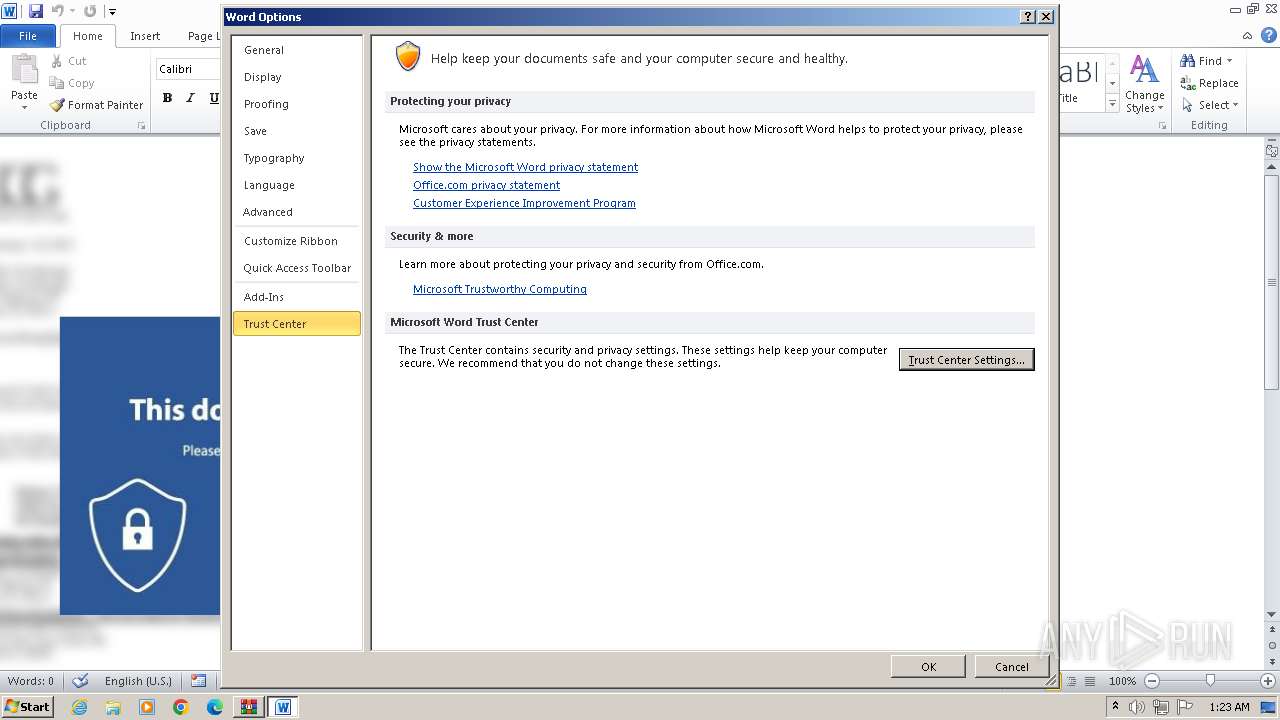
MALICIOUS
Gets TEMP folder path (SCRIPT)
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
Unusual execution from MS Office
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
Accesses environment variables (SCRIPT)
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 2972)
- WINWORD.EXE (PID: 676)
Uses base64 encoding (SCRIPT)
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
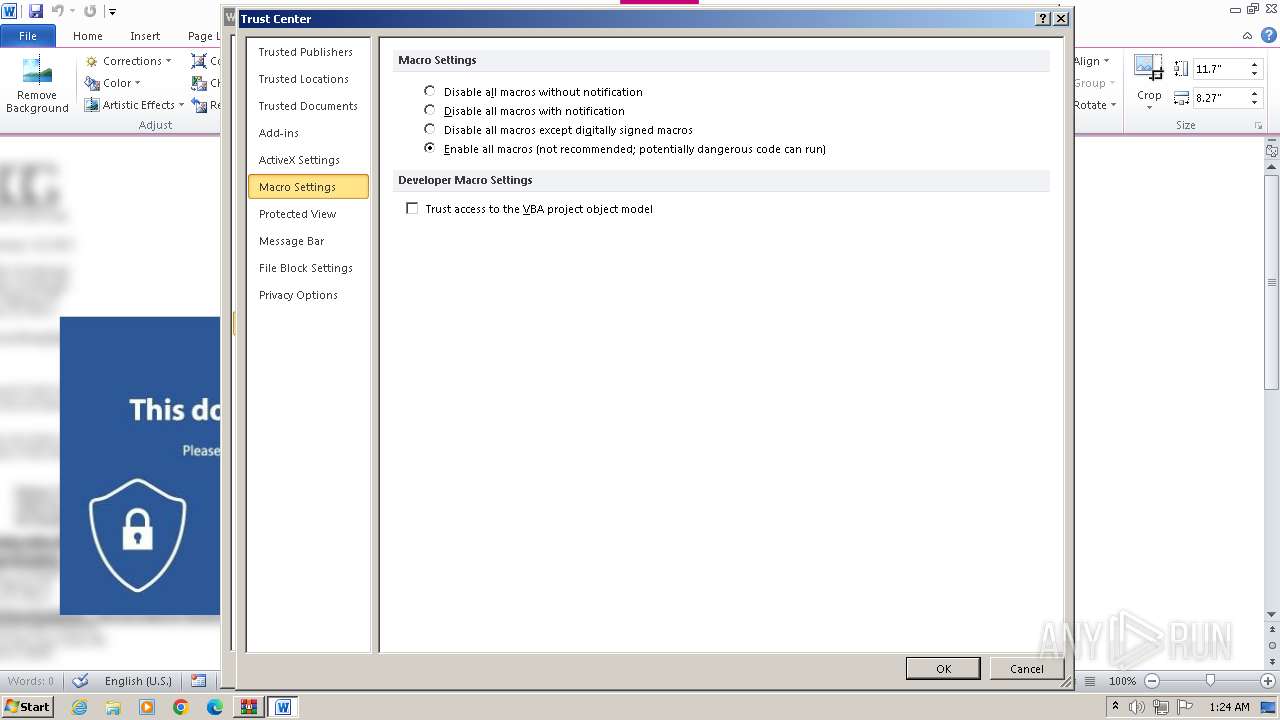
Bypass execution policy to execute commands
- powershell.exe (PID: 1876)
- powershell.exe (PID: 2020)
- powershell.exe (PID: 2764)
- powershell.exe (PID: 2720)
Microsoft Office executes commands via PowerShell or Cmd
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2116)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 600)
- cmd.exe (PID: 3172)
Run PowerShell with an invisible window
- powershell.exe (PID: 1876)
- powershell.exe (PID: 2020)
- powershell.exe (PID: 2764)
- powershell.exe (PID: 2720)
Drops the executable file immediately after the start
- powershell.exe (PID: 1876)
SUSPICIOUS
Writes binary data to a Stream object (SCRIPT)
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
Creates XML DOM element (SCRIPT)
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
Sets XML DOM element text (SCRIPT)
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 2972)
- WINWORD.EXE (PID: 676)
Runs shell command (SCRIPT)
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
The process executes Powershell scripts
- cmd.exe (PID: 2116)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 600)
- cmd.exe (PID: 3172)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2116)
- cmd.exe (PID: 2512)
- cmd.exe (PID: 600)
- cmd.exe (PID: 3172)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1876)
- powershell.exe (PID: 2020)
- powershell.exe (PID: 2764)
Reads the Internet Settings
- powershell.exe (PID: 1876)
- powershell.exe (PID: 2020)
- powershell.exe (PID: 2764)
Executable content was dropped or overwritten
- powershell.exe (PID: 1876)
INFO
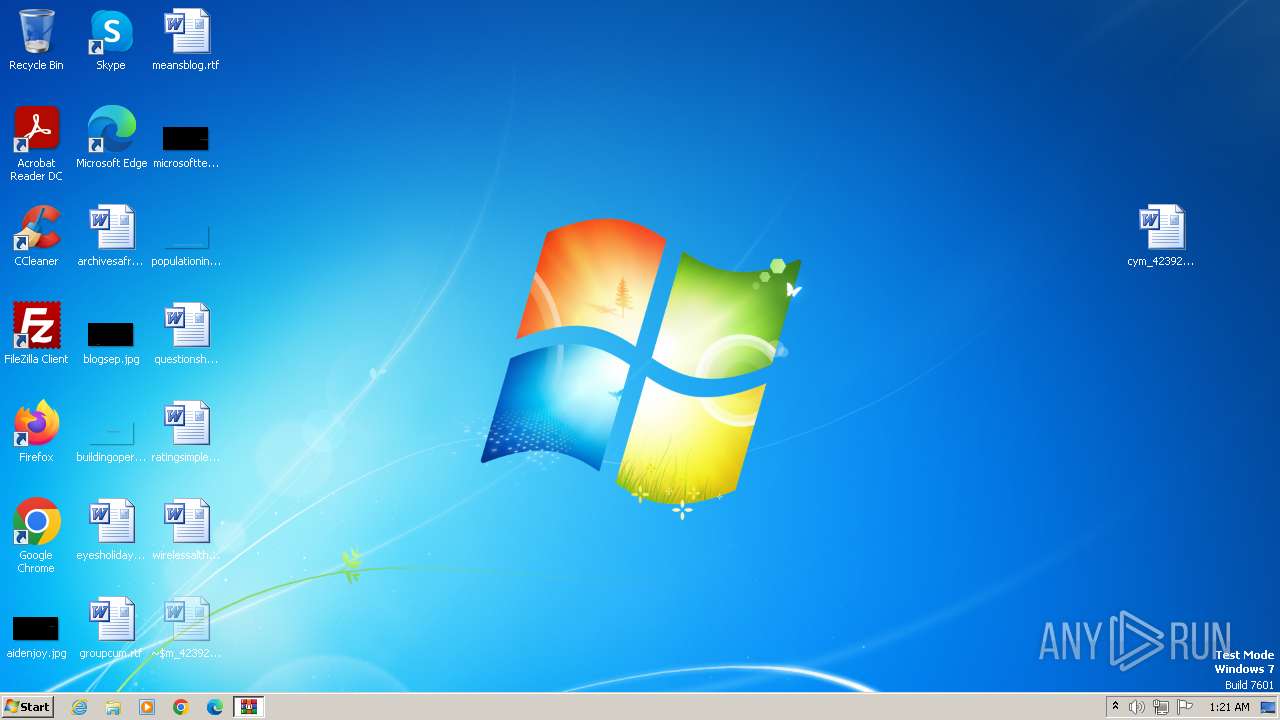
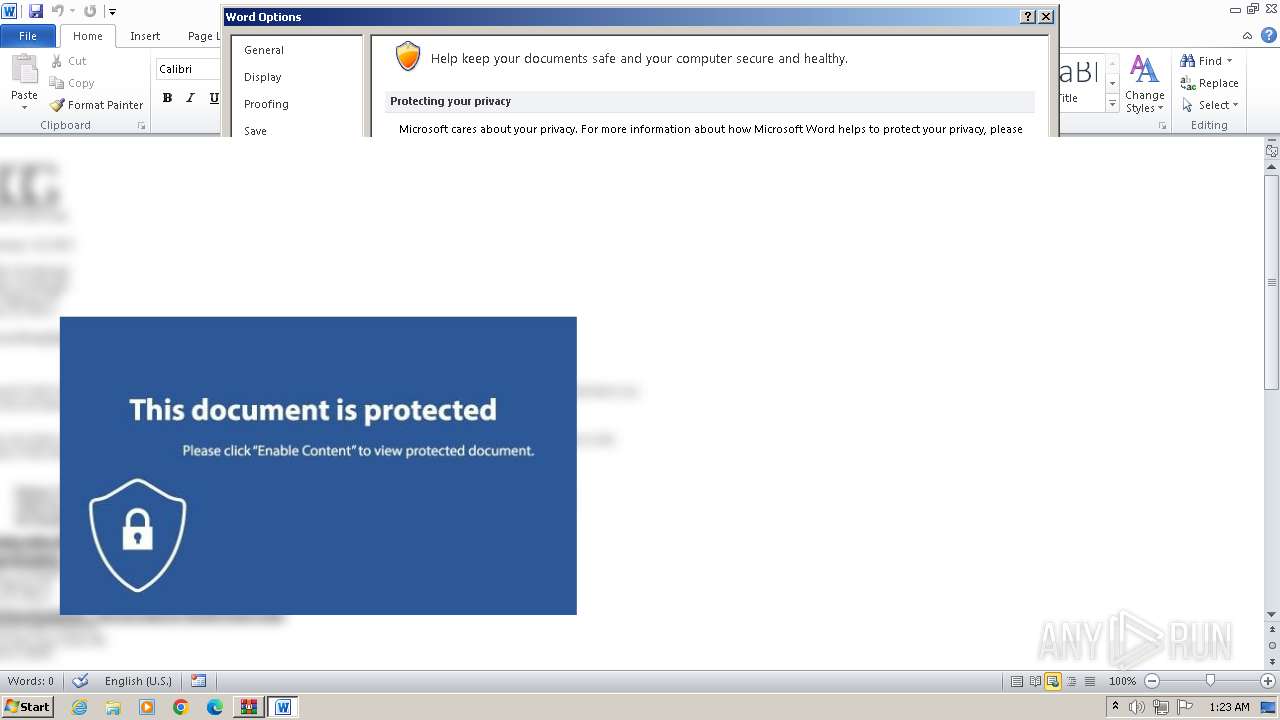
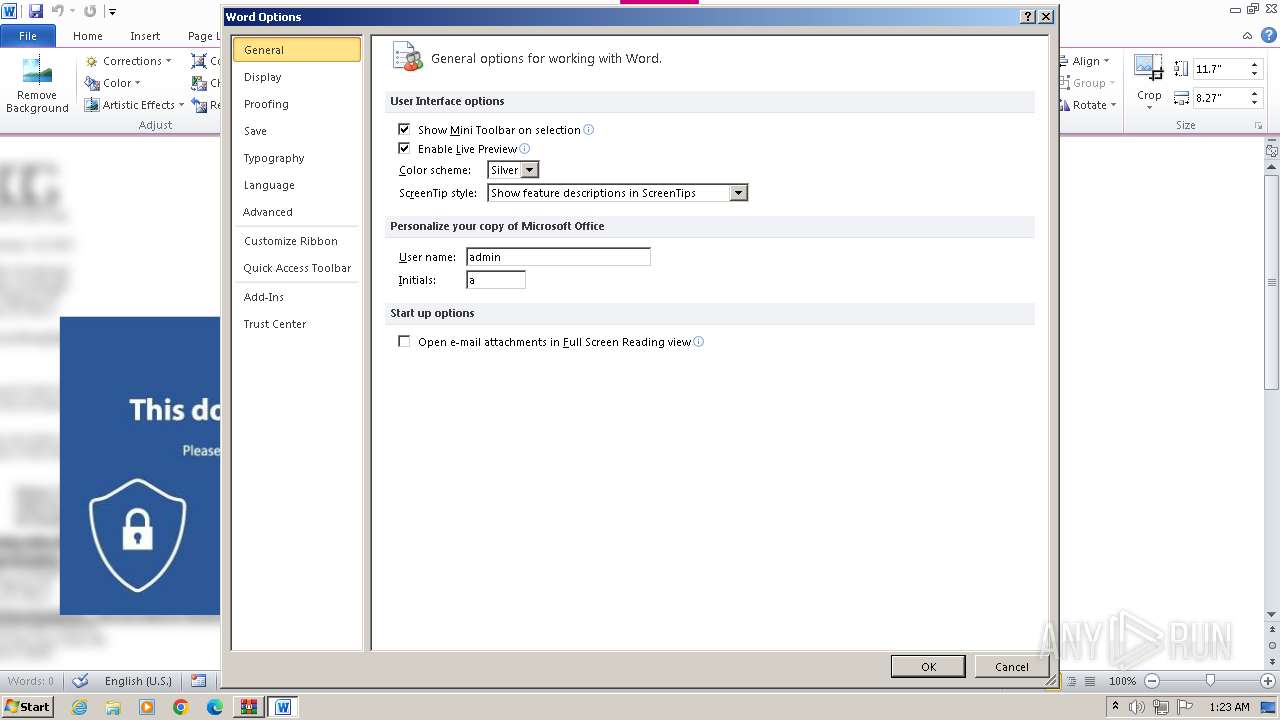
Manual execution by a user
- WINWORD.EXE (PID: 4092)
- WINWORD.EXE (PID: 2268)
- wmpnscfg.exe (PID: 1948)
- WINWORD.EXE (PID: 676)
- WINWORD.EXE (PID: 2972)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 1876)
- powershell.exe (PID: 2020)
- powershell.exe (PID: 2764)
Disables trace logs
- powershell.exe (PID: 1876)
- powershell.exe (PID: 2020)
- WINWORD.EXE (PID: 676)
- powershell.exe (PID: 2764)
- WINWORD.EXE (PID: 2972)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1876)
- powershell.exe (PID: 2764)
- powershell.exe (PID: 2020)
Checks supported languages
- wmpnscfg.exe (PID: 1948)
Reads the computer name
- wmpnscfg.exe (PID: 1948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
61
Monitored processes
14
Malicious processes
5
Suspicious processes
6
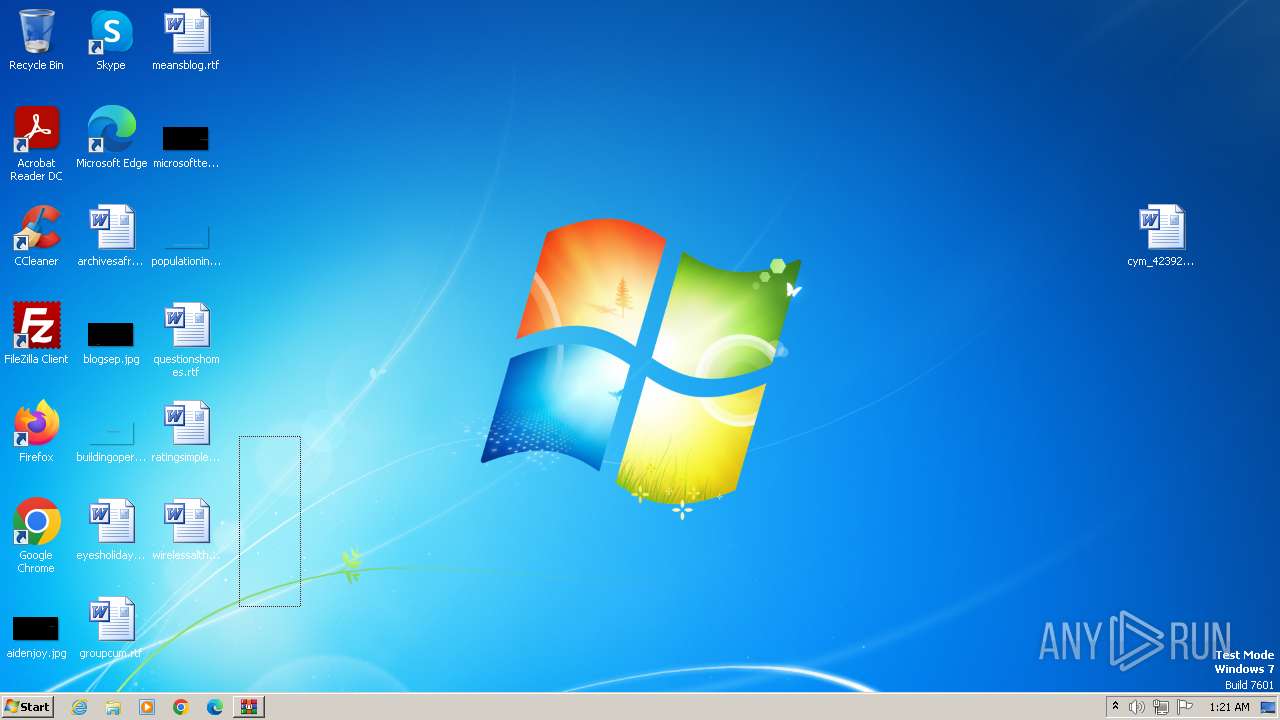
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\Windows\System32\cmd.exe" /cpowershell.exe -windowstyle hidden -ep Bypass C:\Users\admin\AppData\Local\Temp\cym_21520854280804637B4.ps1 | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
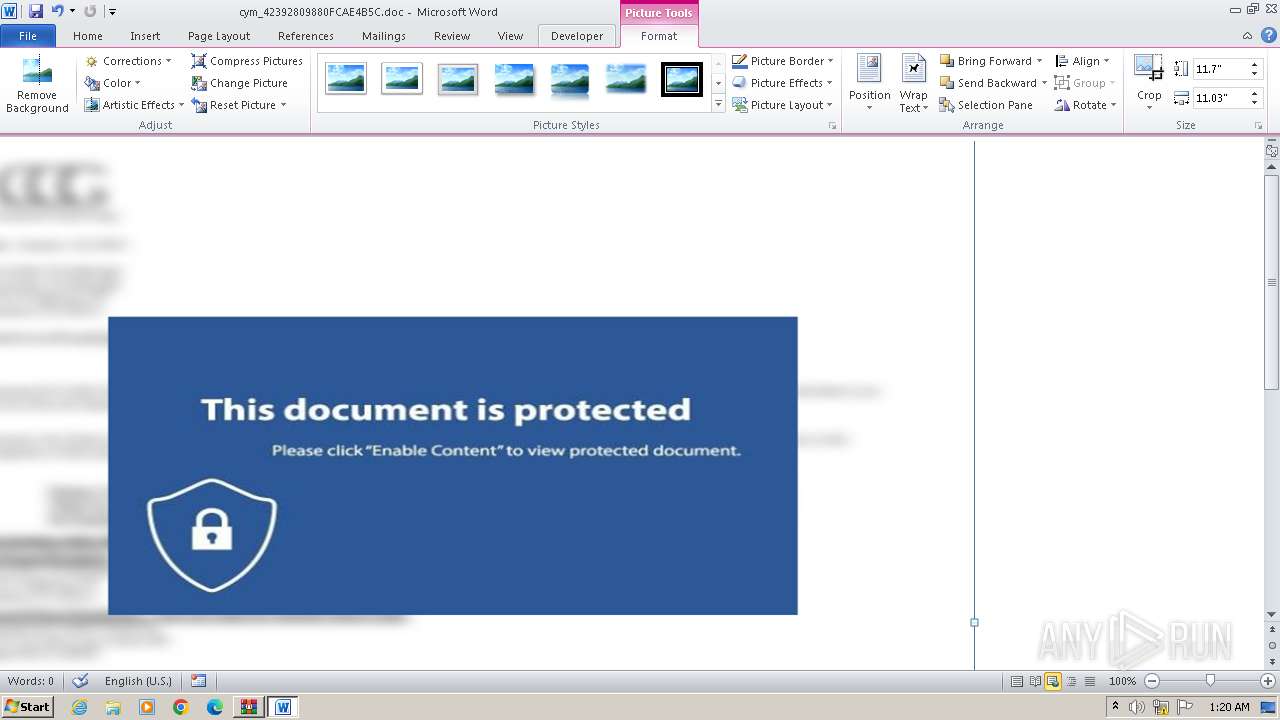
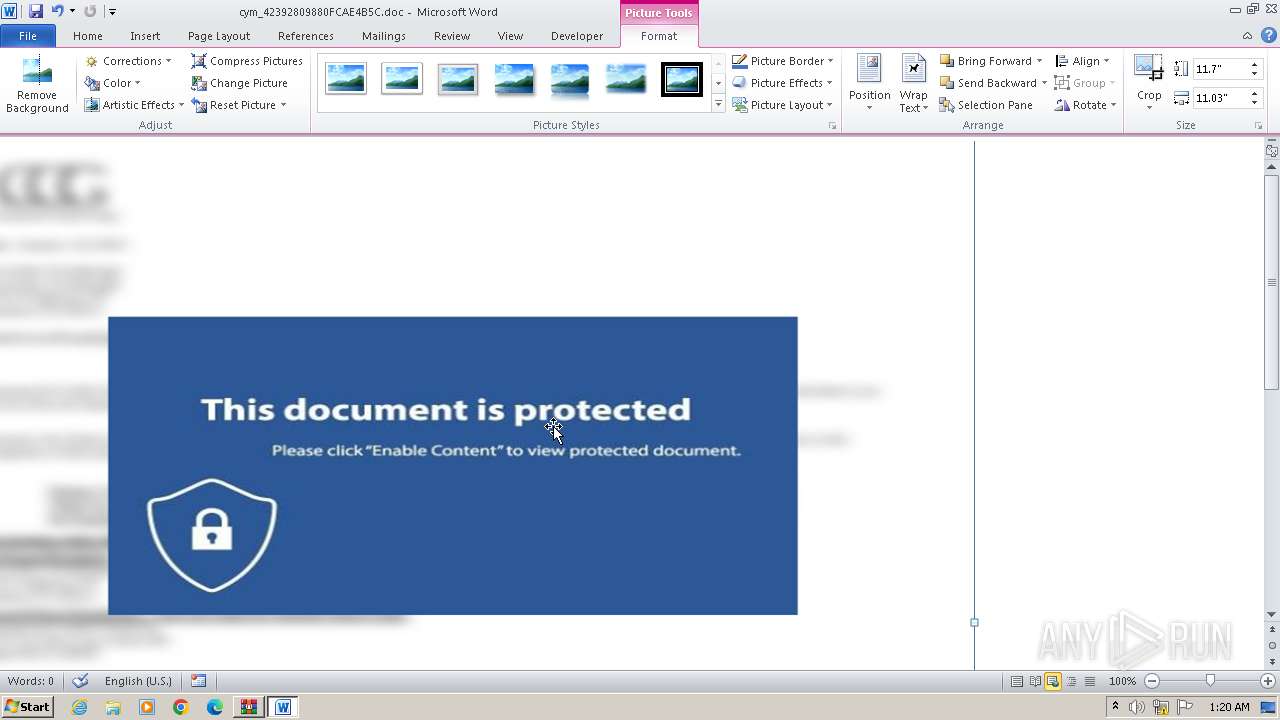
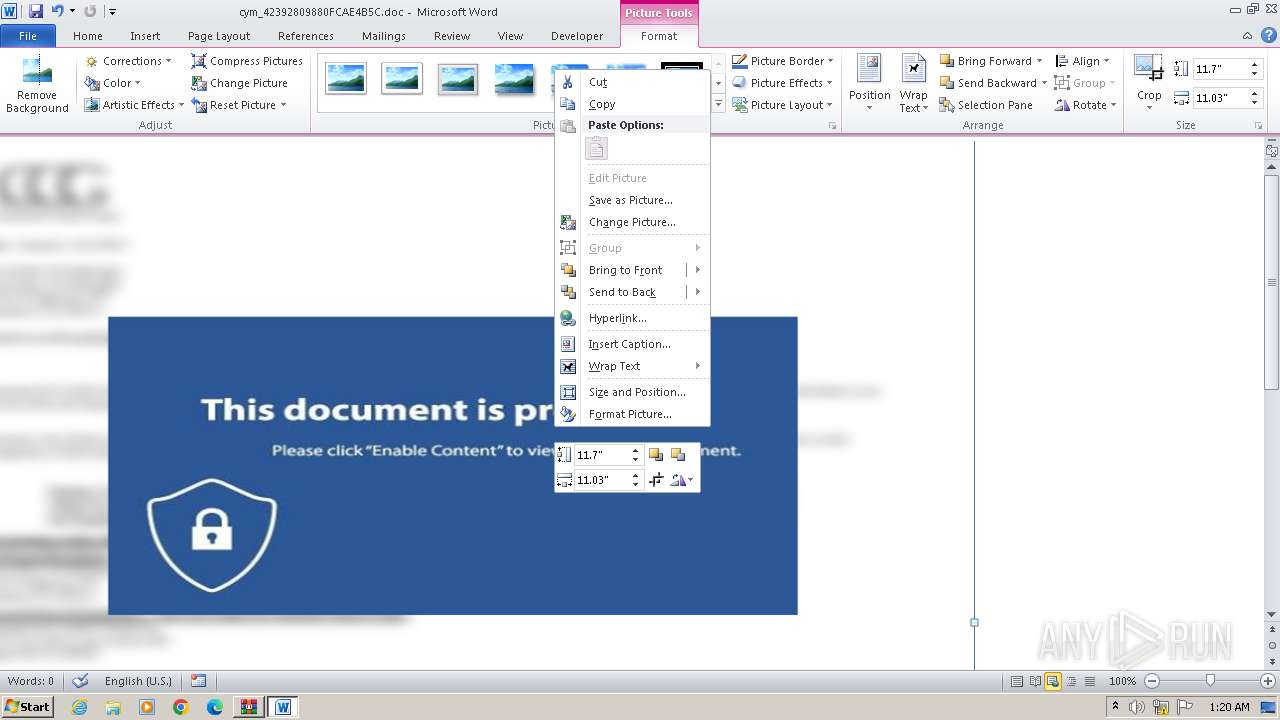
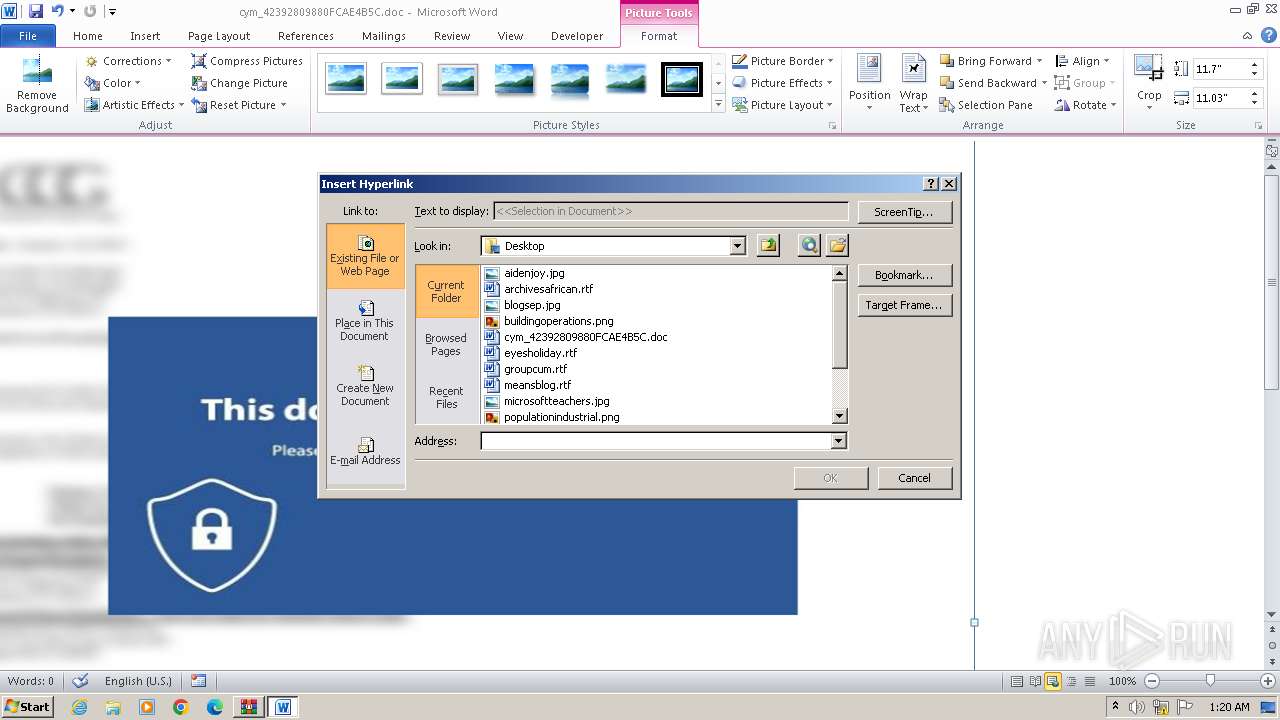
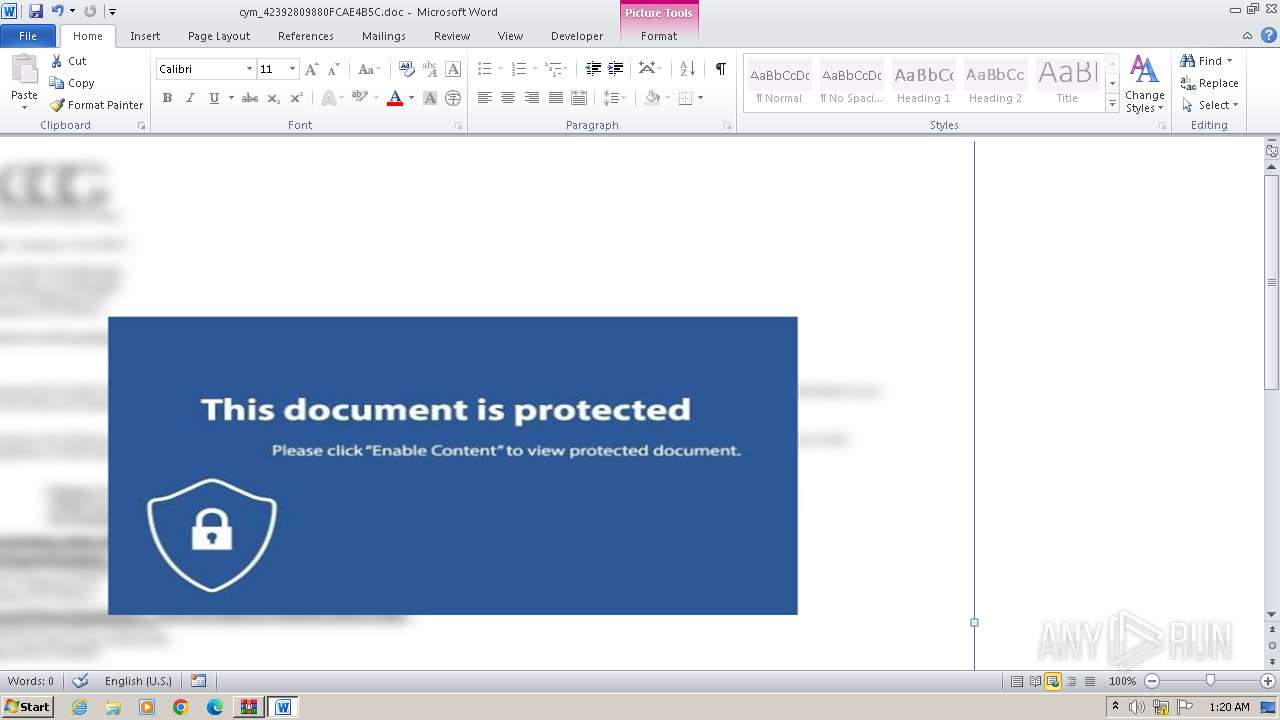
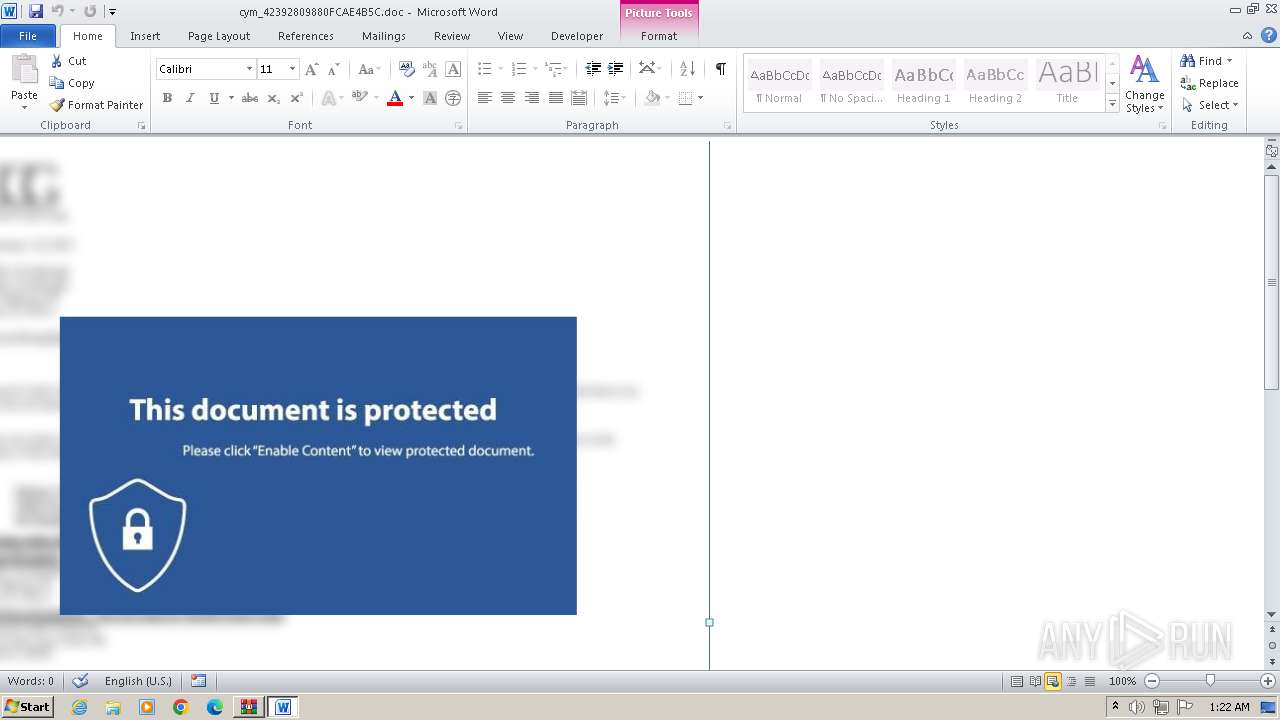
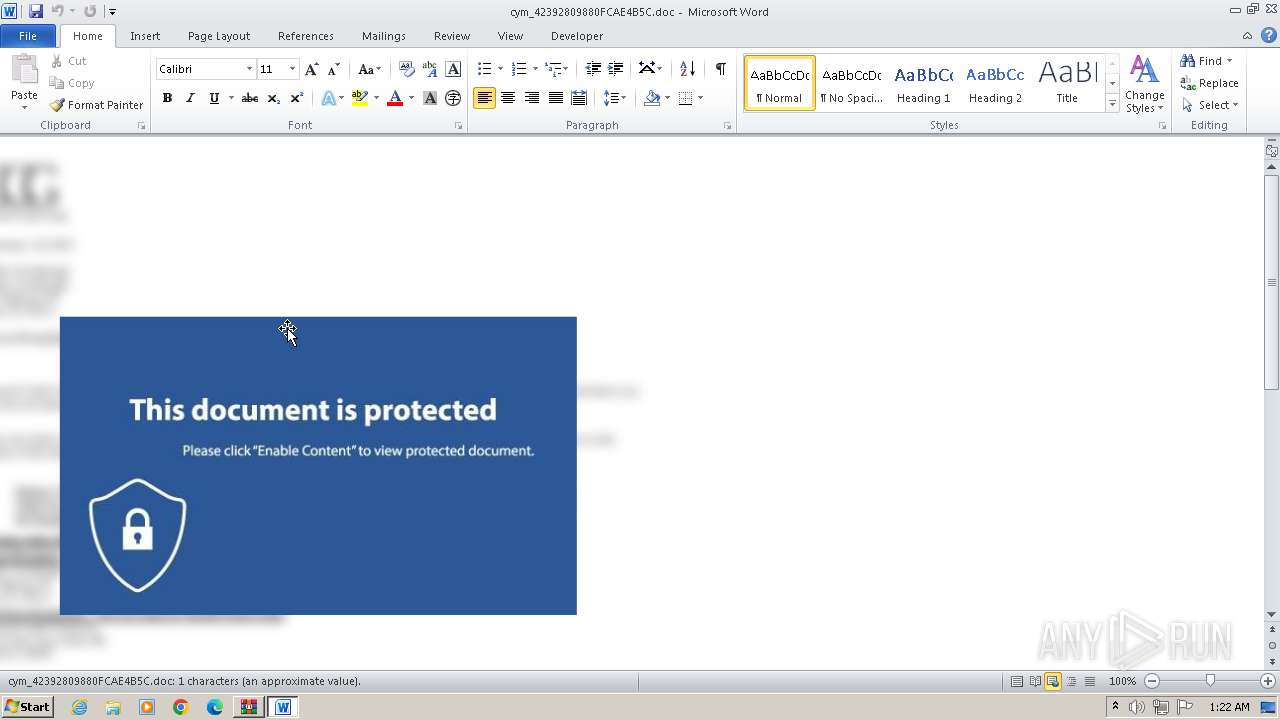
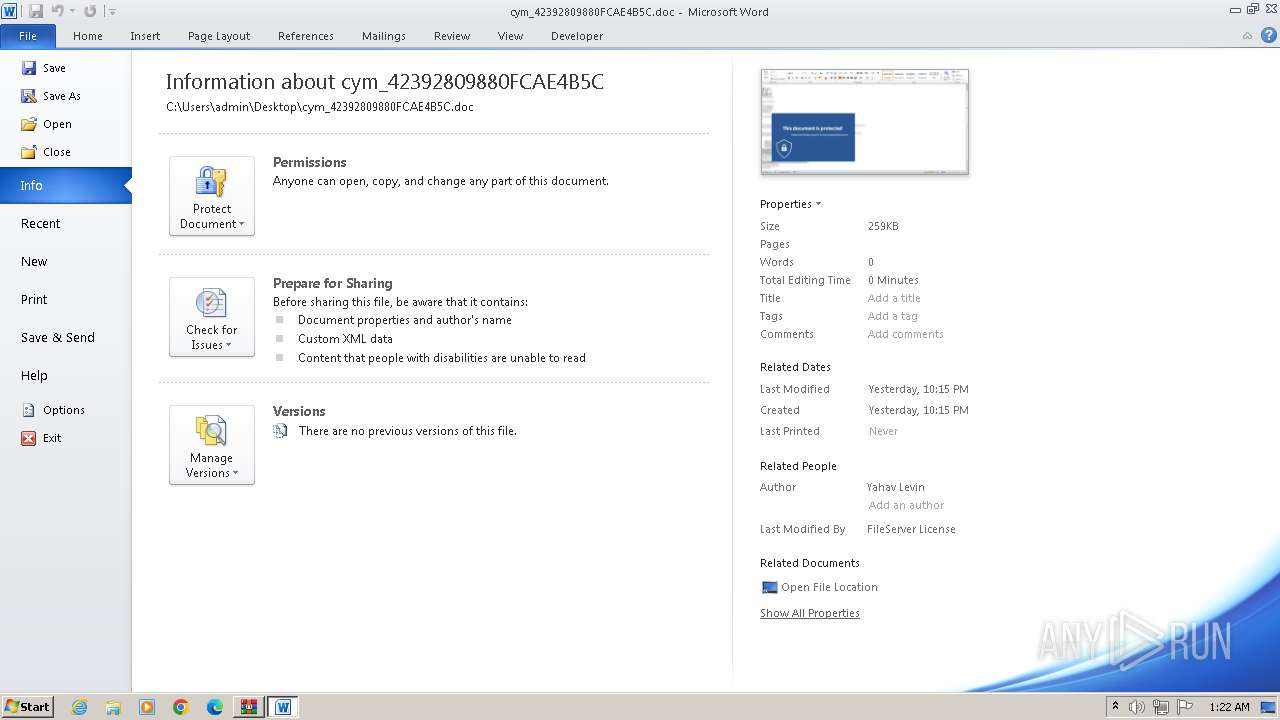
| 676 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\cym_42392809880FCAE4B5C.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1876 | powershell.exe -windowstyle hidden -ep Bypass C:\Users\admin\AppData\Local\Temp\cym_21520854280804637B4.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2020 | powershell.exe -windowstyle hidden -ep Bypass C:\Users\admin\AppData\Local\Temp\cym_21520854280804637B4.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2116 | "C:\Windows\System32\cmd.exe" /cpowershell.exe -windowstyle hidden -ep Bypass C:\Users\admin\AppData\Local\Temp\cym_21520854280804637B4.ps1 | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\cym_42392809880FCAE4B5C.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2512 | "C:\Windows\System32\cmd.exe" /cpowershell.exe -windowstyle hidden -ep Bypass C:\Users\admin\AppData\Local\Temp\cym_21520854280804637B4.ps1 | C:\Windows\System32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2720 | powershell.exe -windowstyle hidden -ep Bypass C:\Users\admin\AppData\Local\Temp\cym_21520854280804637B4.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2764 | powershell.exe -windowstyle hidden -ep Bypass C:\Users\admin\AppData\Local\Temp\cym_21520854280804637B4.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
110 759
Read events
87 426
Write events
21 825
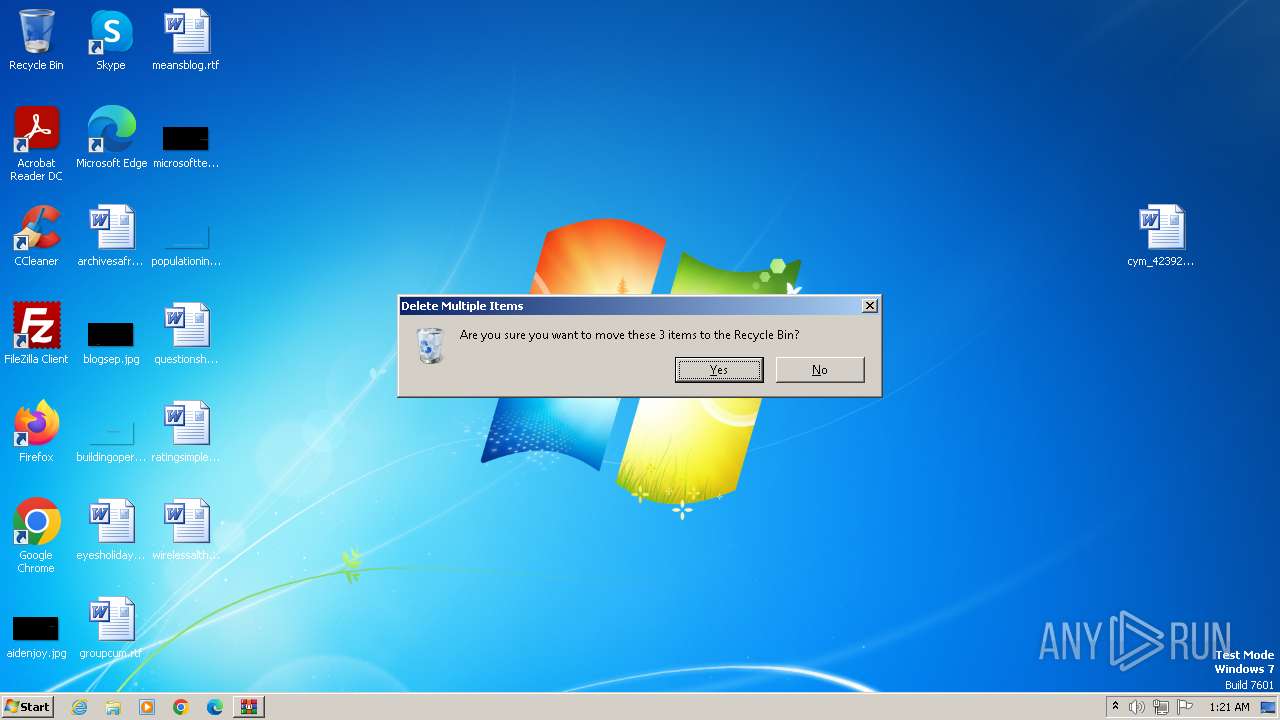
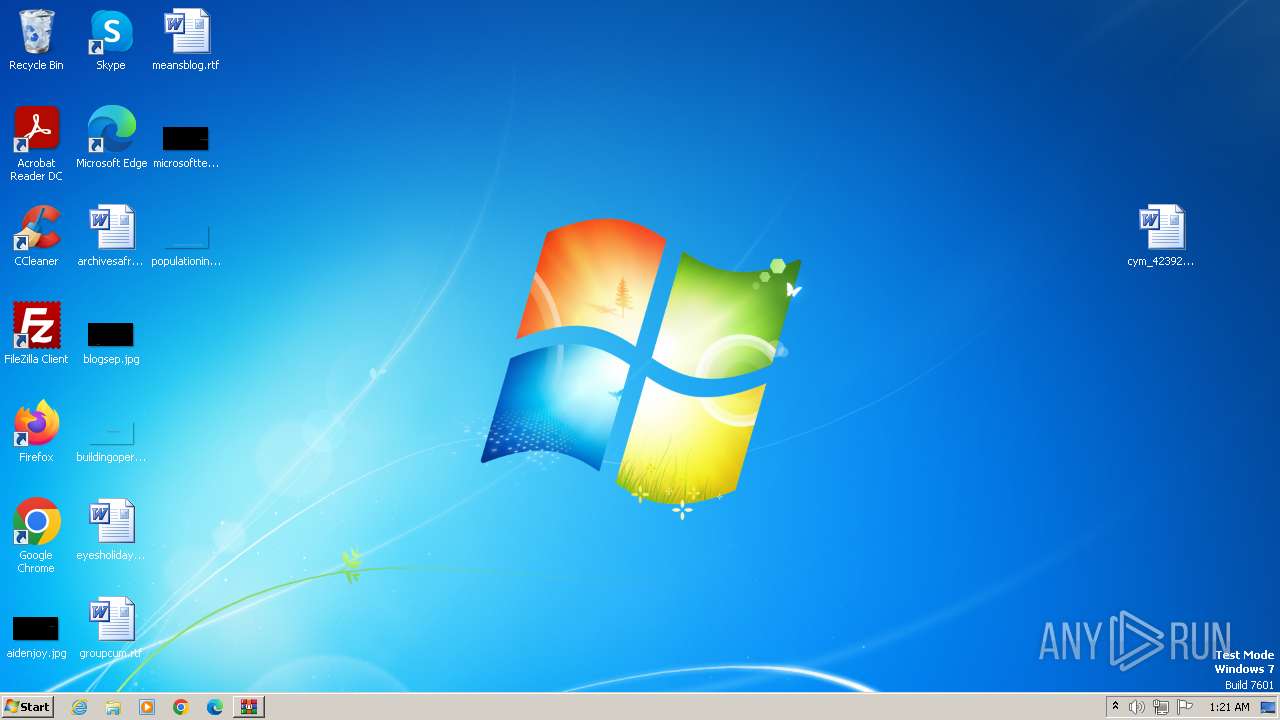
Delete events
1 508
Modification events
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Employee_Financial_Report.rar | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
2
Suspicious files
34
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR76C8.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2268 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR855.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\340aa1fu.zw5.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\cym_42392809880FCAE4B5C.doc.LNK | binary | |
MD5:4A6D4F0CE91F09E452C32817595834DC | SHA256:2721BCFC4013490268A464AEF24620FC5B732E64C1F3C04BE8A1DB34BE217233 | |||
| 1876 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6675EDE59684F4A119D2E5DA282AFBE6 | SHA256:5026C5EE8FA9ACB21718BF1FAD563C0A3FD5BC79327611FDF9C4ABD2647CE829 | |||
| 1876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\16d18f7737f0f27ec9a7dd3e29f700cb_APT_SCENARIO_CONTROLCPL_nativeransomwaregeneratedkeyWinAESRIPlace_6670a204efa1be044b6a5af2.exe | executable | |
MD5:79160AEDA15E0ECA50DB28E6A567E267 | SHA256:7764BDC3CC8E2A14F096DA9840C2F342E6CDF257FCBDB65203F655FDE2BAEF39 | |||
| 2268 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:B69944E38E2115C1D9C5D3B174CE0C0B | SHA256:A0751FE3D33BBF18F9F1EAFDC1493ADBFE255A962C21A905B6E2AA4822BE2D70 | |||
| 676 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9A15.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\cym_21520854280804637B4.ps1 | text | |
MD5:AE7EA757454D4DB29BE9CCCAFB334E82 | SHA256:E36428354AFE650B925B975B8C43D96423FE793F500F567E862DAFB8B8831AF5 | |||
| 4092 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{D1EE9C81-8BB0-4F43-897E-81F7CDACCB04}.tmp | smt | |
MD5:776DDBF564363117D4864FB53BB98E88 | SHA256:B3E7CDAAFA8F7DD45A37A4E8F1B19E0FF95074766527466BCA037C4B8C4347B8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
10
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
676 | WINWORD.EXE | GET | 200 | 52.109.32.97:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | unknown | — | — | unknown |
2972 | WINWORD.EXE | GET | 200 | 52.109.32.97:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1876 | powershell.exe | 3.5.66.116:443 | cym-files-download.s3.eu-west-1.amazonaws.com | AMAZON-02 | IE | unknown |
2020 | powershell.exe | 52.218.108.176:443 | cym-files-download.s3.eu-west-1.amazonaws.com | AMAZON-02 | IE | unknown |
676 | WINWORD.EXE | 52.109.32.97:80 | office14client.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
2764 | powershell.exe | 52.218.57.248:443 | cym-files-download.s3.eu-west-1.amazonaws.com | AMAZON-02 | IE | unknown |
2972 | WINWORD.EXE | 52.109.32.97:80 | office14client.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cym-files-download.s3.eu-west-1.amazonaws.com |
| unknown |
office14client.microsoft.com |
| whitelisted |