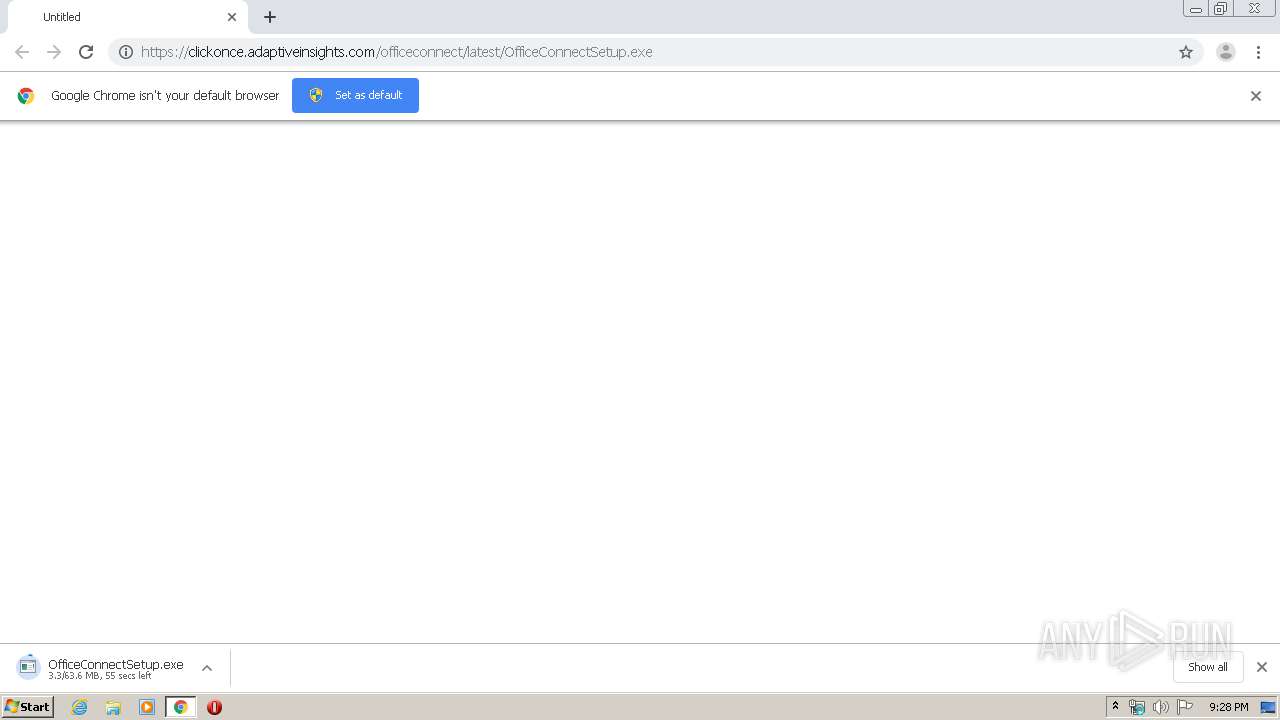
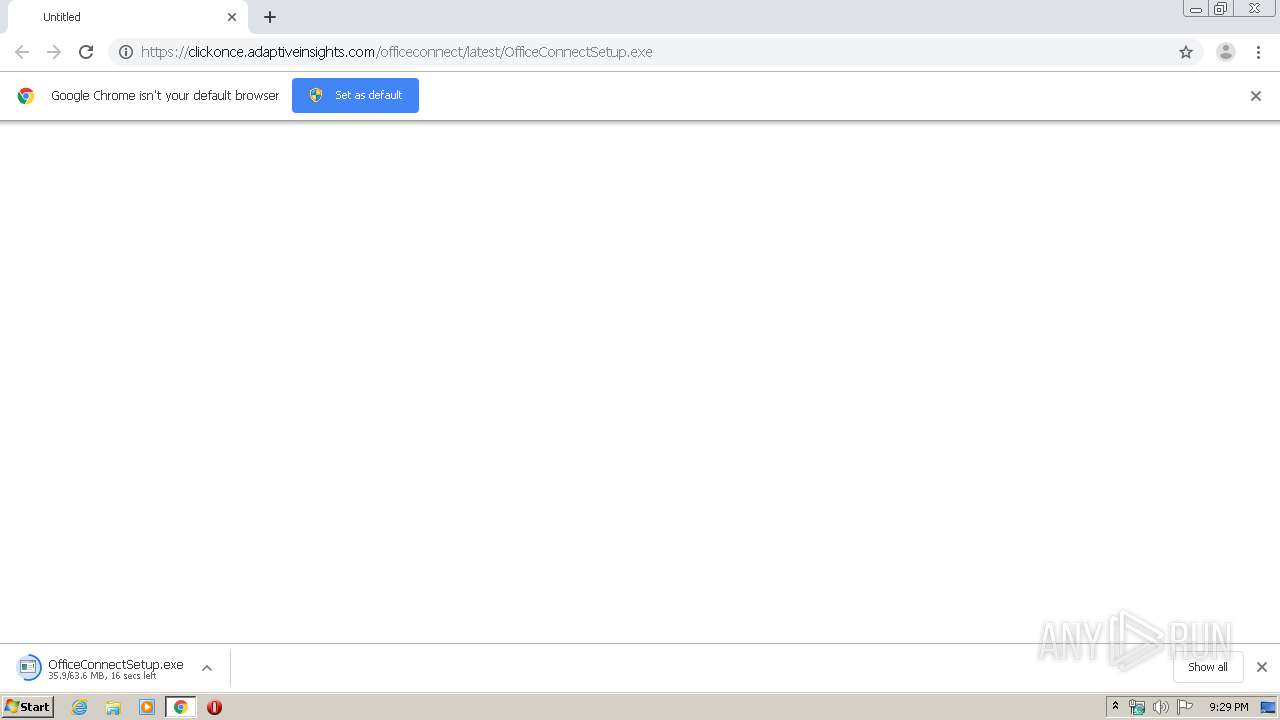
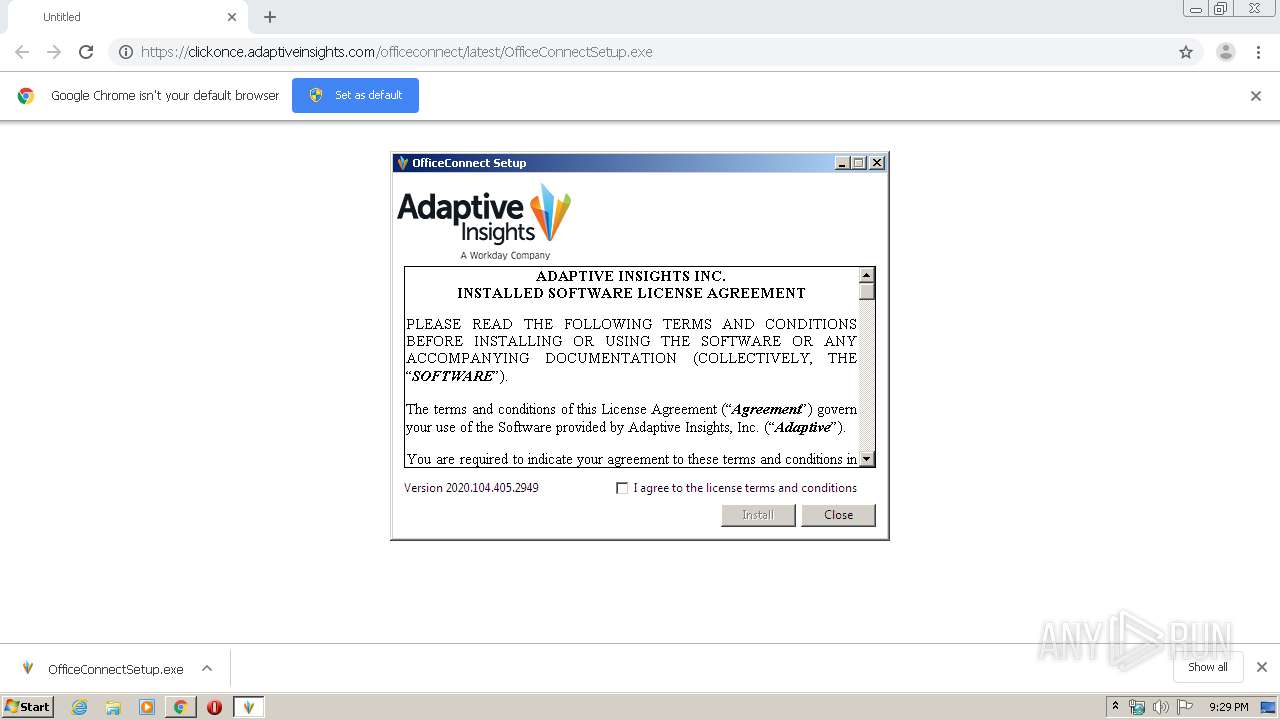
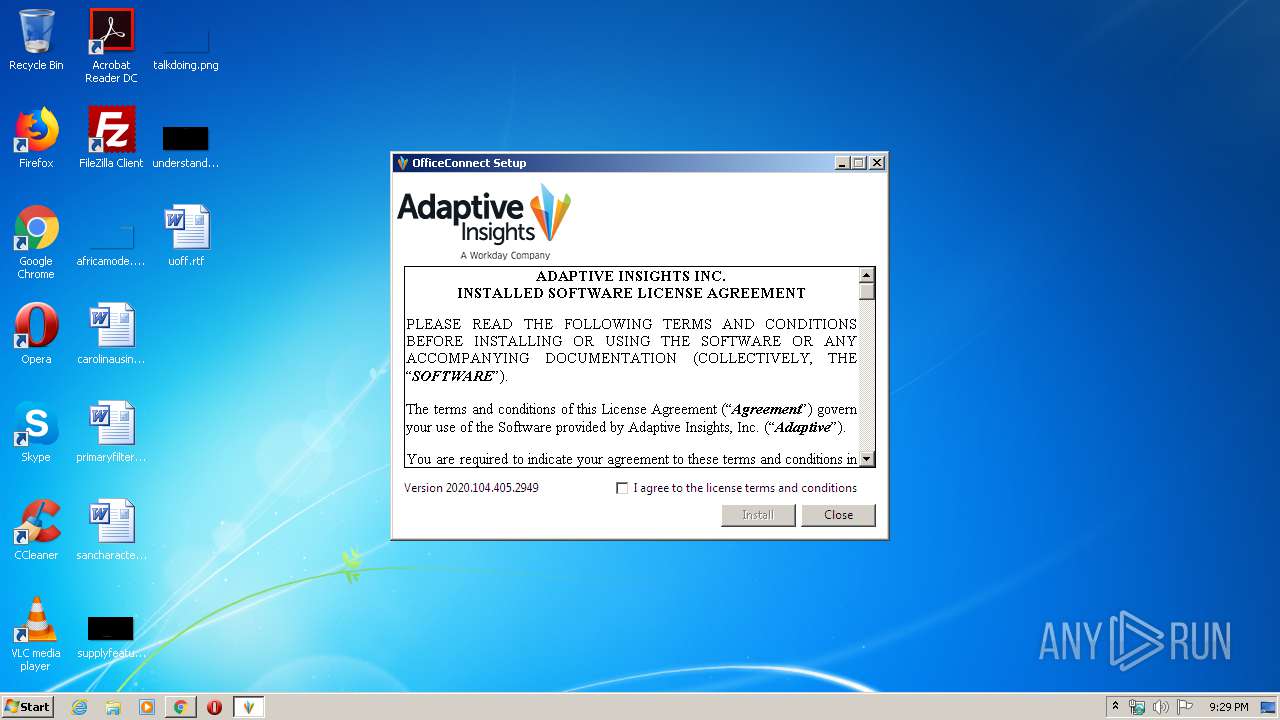
| URL: | https://clickonce.adaptiveinsights.com/officeconnect/latest/OfficeConnectSetup.exe |
| Full analysis: | https://app.any.run/tasks/e8d8124a-37d5-41a5-b0ce-9c0ba0927fea |
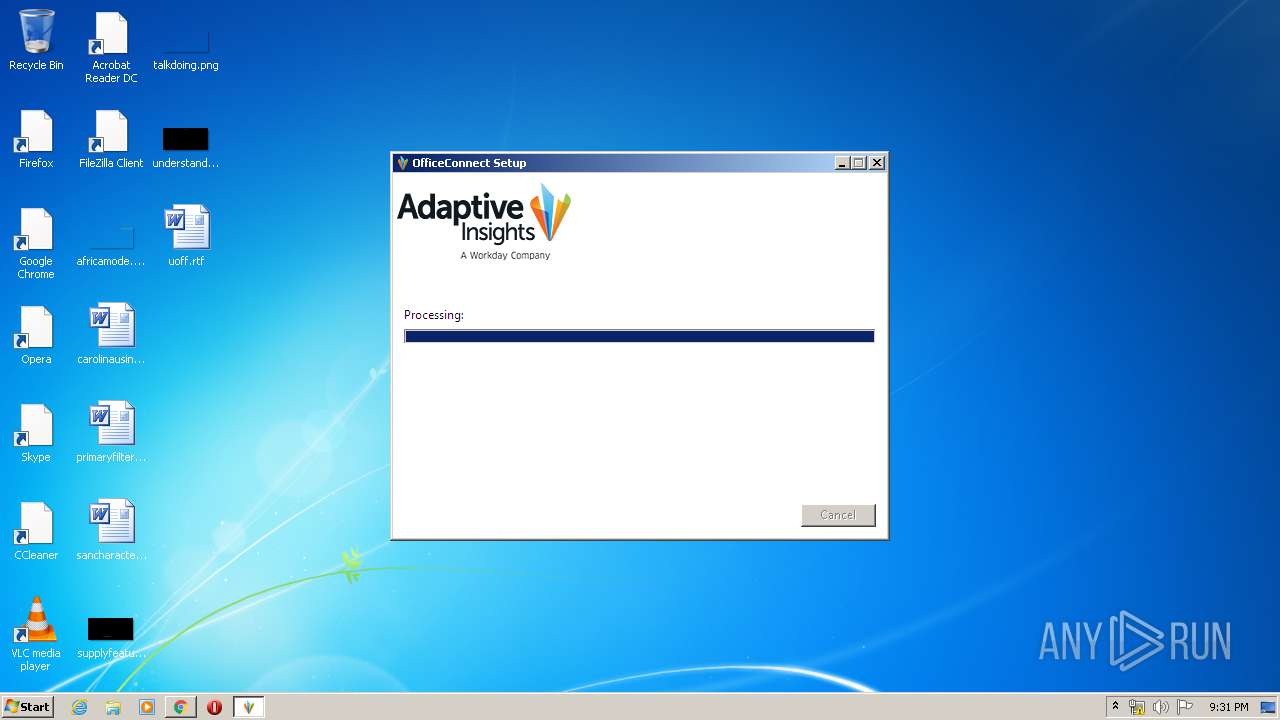
| Verdict: | Malicious activity |
| Analysis date: | April 20, 2020, 20:28:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3EEDC76D5E8F28176B2EA1F580FBE4D5 |
| SHA1: | 62C3689F8F9070A27F9A57B2F9E24161737E8E91 |
| SHA256: | 31C93A99FFFFADDF4CCC1B03B484F88738504F6204F82A31D4148D53288A73BE |
| SSDEEP: | 3:N8UALBEupLttKDQXFAL43f2/AGnRlA:2UAL3pLt4DQX6k3eIWvA |
MALICIOUS
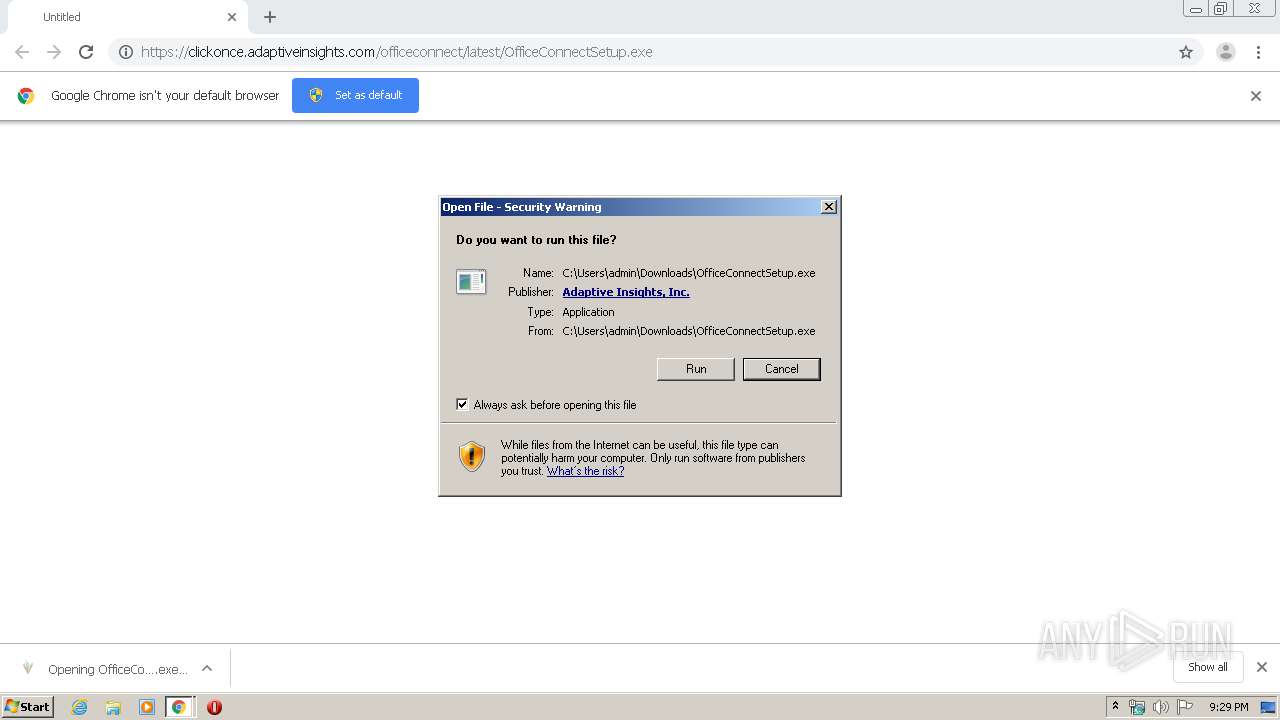
Application was dropped or rewritten from another process
- OfficeConnectSetup.exe (PID: 252)
- OfficeConnectSetup.exe (PID: 2548)
- Setup.exe (PID: 2660)
- vstor40_x86.exe (PID: 2076)
- install.exe (PID: 256)
- OfficeConnectSetup.exe (PID: 940)
- AdaptiveEventLogComponentsSetup.exe (PID: 2060)
- AdaptiveEventLogComponentsSetup.exe (PID: 2120)
- AdaptiveEventLogComponentsSetup.exe (PID: 3708)
Loads dropped or rewritten executable
- OfficeConnectSetup.exe (PID: 2548)
- Setup.exe (PID: 2660)
- install.exe (PID: 256)
- addinutil.exe (PID: 3556)
- AdaptiveEventLogComponentsSetup.exe (PID: 2120)
- rundll32.exe (PID: 2240)
- rundll32.exe (PID: 1908)
- rundll32.exe (PID: 3320)
- rundll32.exe (PID: 3596)
- EXCEL.EXE (PID: 1296)
Actions looks like stealing of personal data
- vstor_redist.exe (PID: 3132)
Changes settings of System certificates
- msiexec.exe (PID: 3012)
- rundll32.exe (PID: 1908)
- Setup.exe (PID: 2660)
Loads the Task Scheduler COM API
- ngen.exe (PID: 3192)
- ngen.exe (PID: 3804)
- ngen.exe (PID: 1348)
- ngen.exe (PID: 4020)
- ngen.exe (PID: 3204)
- ngen.exe (PID: 1024)
- ngen.exe (PID: 564)
- ngen.exe (PID: 2944)
- ngen.exe (PID: 3868)
- ngen.exe (PID: 3832)
- ngen.exe (PID: 3216)
- ngen.exe (PID: 580)
- ngen.exe (PID: 3344)
- ngen.exe (PID: 3424)
- ngen.exe (PID: 840)
- ngen.exe (PID: 2124)
- ngen.exe (PID: 3400)
- ngen.exe (PID: 3752)
- ngen.exe (PID: 1704)
- ngen.exe (PID: 2492)
- ngen.exe (PID: 3636)
- ngen.exe (PID: 3496)
- ngen.exe (PID: 2792)
- ngen.exe (PID: 2932)
- ngen.exe (PID: 3816)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 1348)
- ngen.exe (PID: 3804)
- ngen.exe (PID: 2872)
- ngen.exe (PID: 2740)
- ngen.exe (PID: 2408)
- ngen.exe (PID: 2212)
- ngen.exe (PID: 1828)
- ngen.exe (PID: 1852)
- ngen.exe (PID: 2596)
- ngen.exe (PID: 1488)
- ngen.exe (PID: 3400)
- ngen.exe (PID: 3556)
- ngen.exe (PID: 3952)
- ngen.exe (PID: 2844)
- ngen.exe (PID: 3364)
- ngen.exe (PID: 3088)
- ngen.exe (PID: 4004)
- ngen.exe (PID: 2360)
- ngen.exe (PID: 2296)
- ngen.exe (PID: 3812)
- ngen.exe (PID: 1488)
- ngen.exe (PID: 3368)
- ngen.exe (PID: 2888)
- ngen.exe (PID: 3088)
- ngen.exe (PID: 2768)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 2884)
- ngen.exe (PID: 3780)
- ngen.exe (PID: 2340)
- ngen.exe (PID: 3148)
- ngen.exe (PID: 3624)
- ngen.exe (PID: 1780)
- ngen.exe (PID: 2932)
- ngen.exe (PID: 3784)
- ngen.exe (PID: 4072)
- ngen.exe (PID: 1232)
- ngen.exe (PID: 3064)
- ngen.exe (PID: 1704)
Changes the autorun value in the registry
- OfficeConnectSetup.exe (PID: 2548)
- AdaptiveEventLogComponentsSetup.exe (PID: 3708)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 1296)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3760)
- OfficeConnectSetup.exe (PID: 2548)
- OfficeConnectSetup.exe (PID: 252)
- OfficeConnectSetup.exe (PID: 940)
- vstor_redist.exe (PID: 3132)
- vstor40_x86.exe (PID: 2076)
- msiexec.exe (PID: 3012)
- AdaptiveEventLogComponentsSetup.exe (PID: 2120)
- AdaptiveEventLogComponentsSetup.exe (PID: 2060)
- AdaptiveEventLogComponentsSetup.exe (PID: 3708)
- rundll32.exe (PID: 1908)
Starts itself from another location
- OfficeConnectSetup.exe (PID: 2548)
- AdaptiveEventLogComponentsSetup.exe (PID: 2120)
Executed as Windows Service
- vssvc.exe (PID: 2852)
Creates a software uninstall entry
- OfficeConnectSetup.exe (PID: 2548)
- AdaptiveEventLogComponentsSetup.exe (PID: 3708)
Searches for installed software
- OfficeConnectSetup.exe (PID: 940)
- AdaptiveEventLogComponentsSetup.exe (PID: 3708)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3012)
- Setup.exe (PID: 2660)
Modifies the open verb of a shell class
- msiexec.exe (PID: 3012)
Creates COM task schedule object
- msiexec.exe (PID: 3012)
Creates files in the Windows directory
- ngen.exe (PID: 3192)
- ngen.exe (PID: 3804)
- ngen.exe (PID: 1348)
- ngen.exe (PID: 3204)
- ngen.exe (PID: 564)
- ngen.exe (PID: 3868)
- ngen.exe (PID: 1024)
- ngen.exe (PID: 3216)
- ngen.exe (PID: 2944)
- ngen.exe (PID: 3832)
- ngen.exe (PID: 3344)
- ngen.exe (PID: 580)
- ngen.exe (PID: 3424)
- msiexec.exe (PID: 3012)
- ngen.exe (PID: 2124)
- ngen.exe (PID: 840)
- ngen.exe (PID: 3400)
- ngen.exe (PID: 3752)
- ngen.exe (PID: 1704)
- ngen.exe (PID: 2492)
- ngen.exe (PID: 2792)
- ngen.exe (PID: 3636)
- ngen.exe (PID: 2932)
- ngen.exe (PID: 3496)
- ngen.exe (PID: 1348)
- ngen.exe (PID: 3816)
- ngen.exe (PID: 3804)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 2872)
- ngen.exe (PID: 4020)
- ngen.exe (PID: 1704)
- ngen.exe (PID: 2740)
- ngen.exe (PID: 2408)
- ngen.exe (PID: 1852)
- ngen.exe (PID: 2596)
- ngen.exe (PID: 1828)
- ngen.exe (PID: 3400)
- ngen.exe (PID: 3088)
- ngen.exe (PID: 1488)
- ngen.exe (PID: 3952)
- ngen.exe (PID: 3364)
- ngen.exe (PID: 2844)
- ngen.exe (PID: 3556)
- ngen.exe (PID: 4004)
- ngen.exe (PID: 2360)
- ngen.exe (PID: 2296)
- ngen.exe (PID: 3812)
- ngen.exe (PID: 2696)
- ngen.exe (PID: 1488)
- ngen.exe (PID: 4072)
- ngen.exe (PID: 2888)
- ngen.exe (PID: 3368)
- ngen.exe (PID: 3088)
- ngen.exe (PID: 2768)
- ngen.exe (PID: 3148)
- ngen.exe (PID: 3780)
- ngen.exe (PID: 3624)
- ngen.exe (PID: 2340)
- ngen.exe (PID: 1780)
- ngen.exe (PID: 2932)
- ngen.exe (PID: 3784)
- ngen.exe (PID: 2884)
- ngen.exe (PID: 1232)
- ngen.exe (PID: 3064)
- ngen.exe (PID: 2212)
Removes files from Windows directory
- msiexec.exe (PID: 3012)
Creates files in the program directory
- AdaptiveEventLogComponentsSetup.exe (PID: 3708)
- EXCEL.EXE (PID: 1296)
Creates files in the user directory
- msiexec.exe (PID: 3012)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3760)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 3480)
INFO
Reads the hosts file
- chrome.exe (PID: 3760)
- chrome.exe (PID: 2784)
Reads Internet Cache Settings
- chrome.exe (PID: 3760)
- EXCEL.EXE (PID: 1296)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2852)
Application launched itself
- chrome.exe (PID: 3760)
- msiexec.exe (PID: 3012)
Reads settings of System Certificates
- msiexec.exe (PID: 3012)
- Setup.exe (PID: 2660)
- EXCEL.EXE (PID: 1296)
Loads dropped or rewritten executable
- msiexec.exe (PID: 3012)
- MsiExec.exe (PID: 1732)
- MsiExec.exe (PID: 2488)
Creates files in the program directory
- msiexec.exe (PID: 3012)
Creates a software uninstall entry
- msiexec.exe (PID: 3012)
Dropped object may contain Bitcoin addresses
- OfficeConnectSetup.exe (PID: 2548)
- msiexec.exe (PID: 3012)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1296)
Manual execution by user
- EXCEL.EXE (PID: 1296)
Reads Environment values
- EXCEL.EXE (PID: 1296)
Creates files in the user directory
- EXCEL.EXE (PID: 1296)
Reads internet explorer settings
- EXCEL.EXE (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
248
Monitored processes
112
Malicious processes
14
Suspicious processes
69
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | "C:\Users\admin\Downloads\OfficeConnectSetup.exe" | C:\Users\admin\Downloads\OfficeConnectSetup.exe | chrome.exe | ||||||||||||
User: admin Company: Adaptive Insights, Inc. Integrity Level: MEDIUM Description: OfficeConnect Exit code: 0 Version: 2020.104.405.2949 Modules
| |||||||||||||||
| 256 | c:\a447b56dcec0da688481de1d8b\install.exe /q | c:\a447b56dcec0da688481de1d8b\install.exe | — | vstor40_x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: External Installer Exit code: 0 Version: 10.0.60825.0 built by: VSTO_Rel Modules
| |||||||||||||||
| 564 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "c:\Program Files\Common Files\Microsoft Shared\VSTA\Pipeline.v10.0\HostSideAdapters\Microsoft.VisualStudio.Tools.Applications.HostAdapter.v10.0.dll" /queue:3 /NoDependencies | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 580 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "c:\Program Files\Common Files\Microsoft Shared\VSTA\Pipeline.v10.0\Contracts\Microsoft.VisualStudio.Tools.Applications.Contract.v10.0.dll" /queue:3 /NoDependencies | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4001409011402729175,14750124980937577654,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11549364230927354243 --mojo-platform-channel-handle=3888 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4001409011402729175,14750124980937577654,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15377259579397444679 --mojo-platform-channel-handle=4068 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 840 | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe install "Microsoft.VisualStudio.Tools.Applications.ServerDocument.v9.0, Version=9.0.0.0, Culture=neutral, PublicKeyToken=b03f5f7f11d50a3a" /queue:3 /NoDependencies | c:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 940 | "C:\Users\admin\AppData\Local\Temp\{5EB8DBA0-D9E0-41A7-B633-4D6CD0D2BADD}\.be\OfficeConnectSetup.exe" -q -burn.elevated BurnPipe.{5DF88605-41AB-4C41-A93C-7F50316E01C3} {814F7E75-0AB8-4C08-A224-10CB6C016F0E} 2548 | C:\Users\admin\AppData\Local\Temp\{5EB8DBA0-D9E0-41A7-B633-4D6CD0D2BADD}\.be\OfficeConnectSetup.exe | OfficeConnectSetup.exe | ||||||||||||
User: admin Company: Adaptive Insights, Inc. Integrity Level: HIGH Description: OfficeConnect Exit code: 0 Version: 2020.104.405.2949 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4001409011402729175,14750124980937577654,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9973583272551238568 --mojo-platform-channel-handle=4808 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,4001409011402729175,14750124980937577654,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12483158948164962880 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
12 984
Read events
5 833
Write events
6 665
Delete events
486
Modification events
| (PID) Process: | (3760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3796) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3760-13231888128973125 |
Value: 259 | |||
| (PID) Process: | (3760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3760) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3760) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
448
Suspicious files
53
Text files
488
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E9E0601-EB0.pma | — | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2a8bcbfb-b441-4824-add1-d4822fc6ab98.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFa6e315.TMP | — | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa6e1fc.TMP | text | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3760 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa6e4ca.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
26
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2784 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
2784 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
1052 | svchost.exe | GET | 200 | 104.18.24.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIGkp0%2Fv9GUvNUu1EP06Tu7%2BChyAQUkZ47RGw9V5xCdyo010%2FRzEqXLNoCEyAAASWxwt68EQiA3cUAAAABJbE%3D | US | der | 1.79 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/GTSGIAG3/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT27bBjYjKBmjX2jXWgnQJKEapsrQQUd8K4UJpndnaxLcKG0IOgfqZ%2BuksCCC7Rp3EQG0zo | US | binary | 5 b | whitelisted |
2784 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAP%2B7xu1tkg0miCVD4vGl1M%3D | US | der | 471 b | whitelisted |
2784 | chrome.exe | GET | 200 | 172.217.130.73:80 | http://r4---sn-2gb7sn7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=84.17.36.60&mm=28&mn=sn-2gb7sn7r&ms=nvh&mt=1587414622&mv=m&mvi=3&pl=26&shardbypass=yes | US | crx | 816 Kb | whitelisted |
2784 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEApoVvYeHhFzOoJmuoBKFzQ%3D | US | der | 471 b | whitelisted |
1296 | EXCEL.EXE | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTIyCPRUzvKHRw7iRE1lF%2BfcLu%2FjgQUypJnUmHervy6Iit%2FHIdMJftvmVgCEAmr%2BqQUsxXHQ7yGP0ng34E%3D | US | der | 471 b | whitelisted |
2784 | chrome.exe | GET | 200 | 173.194.150.231:80 | http://r1---sn-2gb7sn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=84.17.36.60&mm=28&mn=sn-2gb7sn7s&ms=nvh&mt=1587414622&mv=m&mvi=0&pl=26&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2784 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 172.217.18.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 172.217.21.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 172.217.16.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 173.194.150.231:80 | r1---sn-2gb7sn7s.gvt1.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2784 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1296 | EXCEL.EXE | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
clickonce.adaptiveinsights.com |
| unknown |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
addinutil.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
addinutil.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
addinutil.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
addinutil.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
addinutil.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
addinutil.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
addinutil.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
addinutil.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
addinutil.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
addinutil.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|