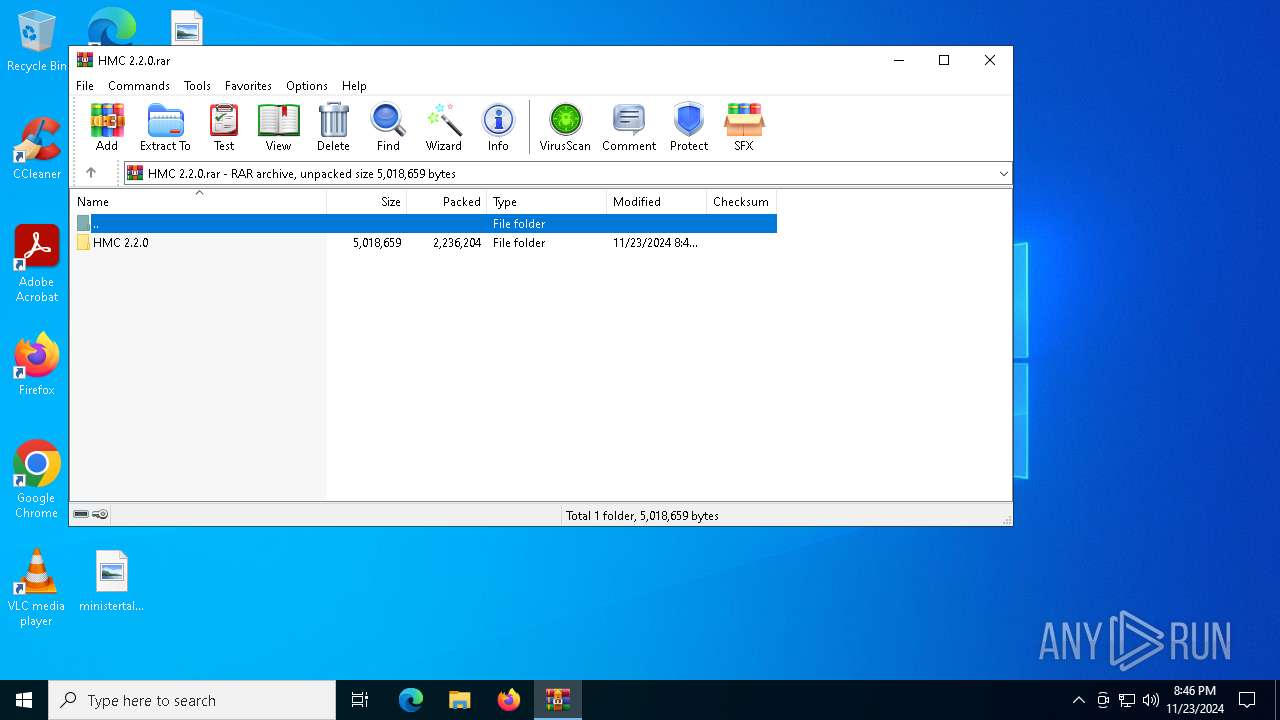
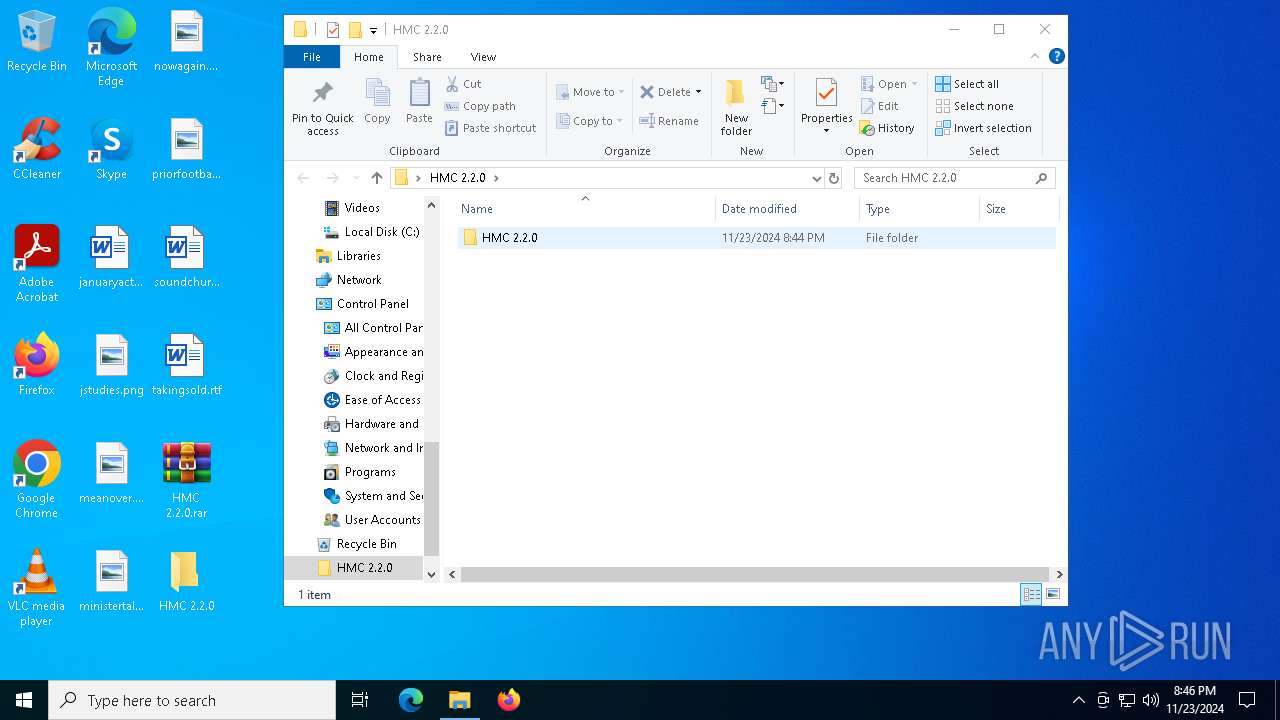
| File name: | HMC 2.2.0.rar |
| Full analysis: | https://app.any.run/tasks/cddb1210-5f77-4412-83f9-8e9c81bb896c |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2024, 20:45:56 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 913E3EDA7A9D92A7BB005AACCB0CEBFE |
| SHA1: | BEF91EFDA15090D1217BFA8616AE8488A5BDF5D3 |
| SHA256: | 31B3E57390530B0820474099514851E4973FB715044879D3B934A45DA3278B40 |
| SSDEEP: | 98304:FvCtNeSZ7DVuJJFW7frGQQN/rIy//TNv14lXi0pkdgnV26WKdRK5fCODlSIpfBH9:84Y20w |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 4672)
- WinRAR.exe (PID: 5300)
Executes application which crashes
- MSBuild.exe (PID: 1480)
Possible usage of Discord/Telegram API has been detected (YARA)
- MSBuild.exe (PID: 1480)
INFO
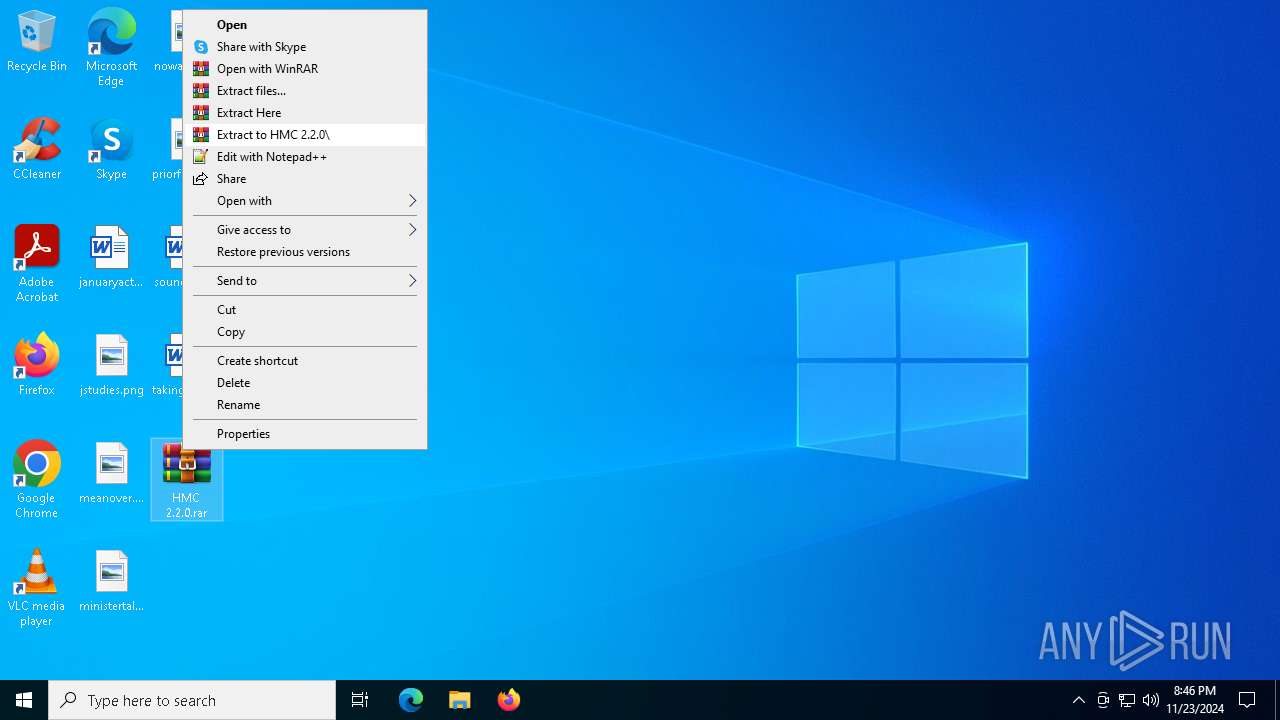
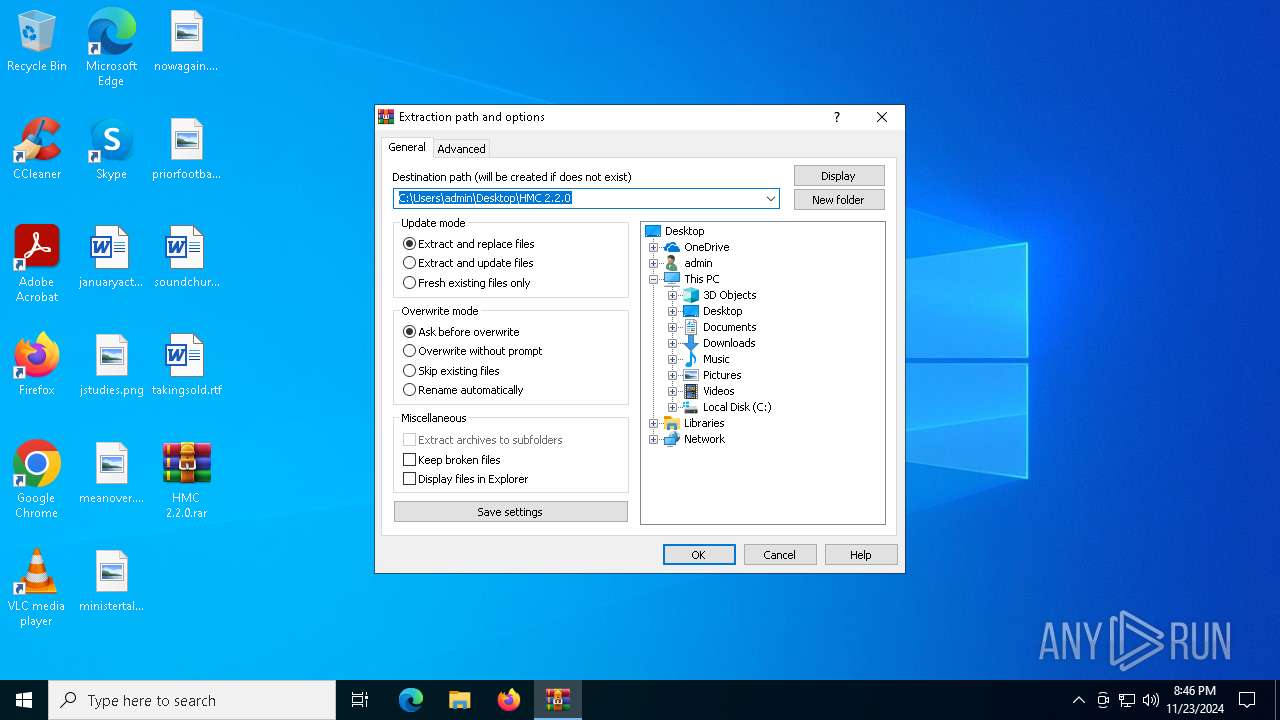
Manual execution by a user
- WinRAR.exe (PID: 5300)
- HMC 2.2.0.exe (PID: 5740)
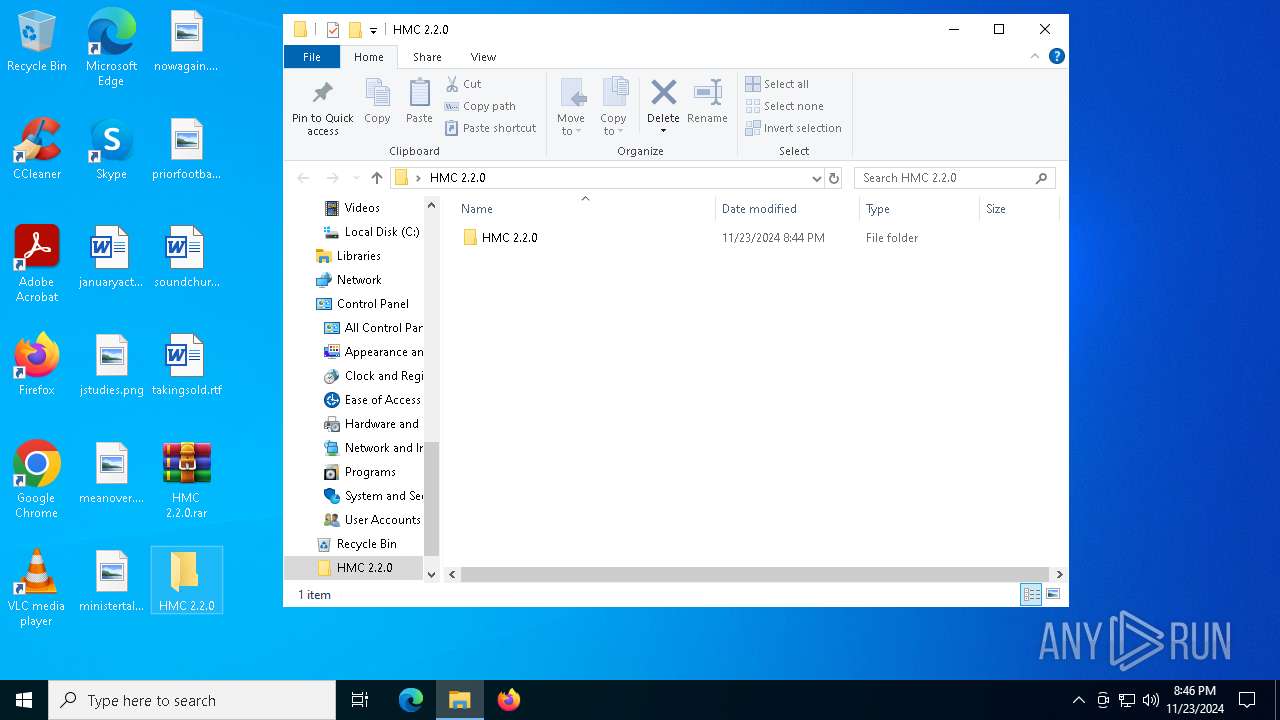
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5300)
The process uses the downloaded file
- WinRAR.exe (PID: 5300)
Reads the computer name
- HMC 2.2.0.exe (PID: 5740)
- MSBuild.exe (PID: 1480)
Sends debugging messages
- MSBuild.exe (PID: 1480)
Checks proxy server information
- WerFault.exe (PID: 6192)
Reads the machine GUID from the registry
- HMC 2.2.0.exe (PID: 5740)
Checks supported languages
- MSBuild.exe (PID: 1480)
- HMC 2.2.0.exe (PID: 5740)
Creates files or folders in the user directory
- WerFault.exe (PID: 6192)
Reads the software policy settings
- WerFault.exe (PID: 6192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 70462 |
| UncompressedSize: | 180224 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | HMC 2.2.0/advpack.dll |
Total processes
135
Monitored processes
6
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1480 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | HMC 2.2.0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 2148734499 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 4672 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\HMC 2.2.0.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5300 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\HMC 2.2.0.rar" "?\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 5316 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5740 | "C:\Users\admin\Desktop\HMC 2.2.0\HMC 2.2.0\HMC 2.2.0.exe" | C:\Users\admin\Desktop\HMC 2.2.0\HMC 2.2.0\HMC 2.2.0.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Stub Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 6192 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 1480 -s 988 | C:\Windows\SysWOW64\WerFault.exe | MSBuild.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 936
Read events
5 898
Write events
25
Delete events
13
Modification events
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\HMC 2.2.0.rar | |||
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (4672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
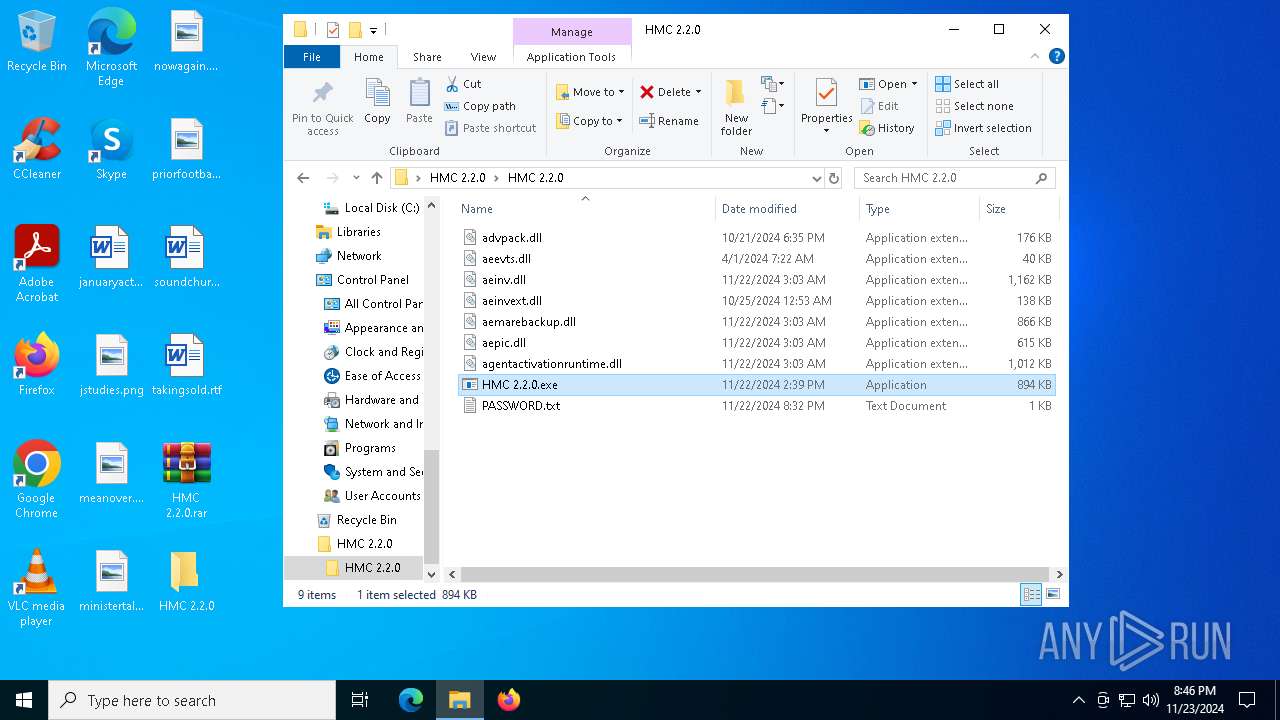
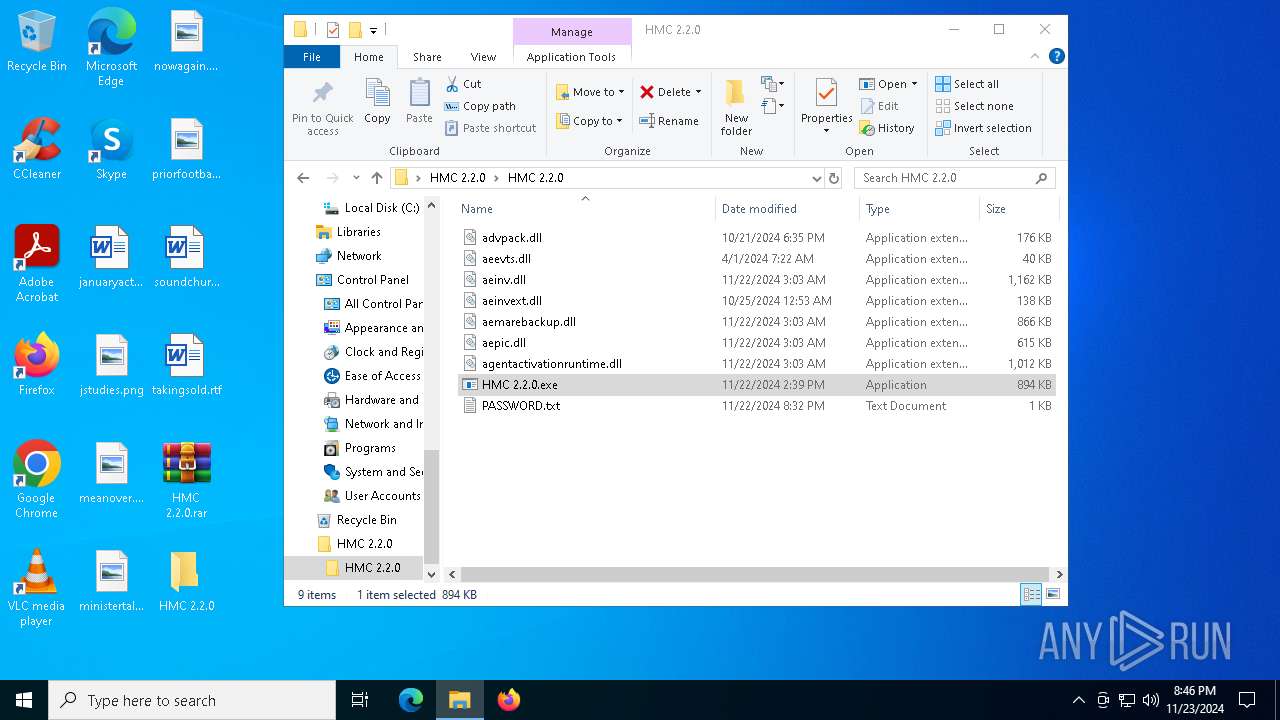
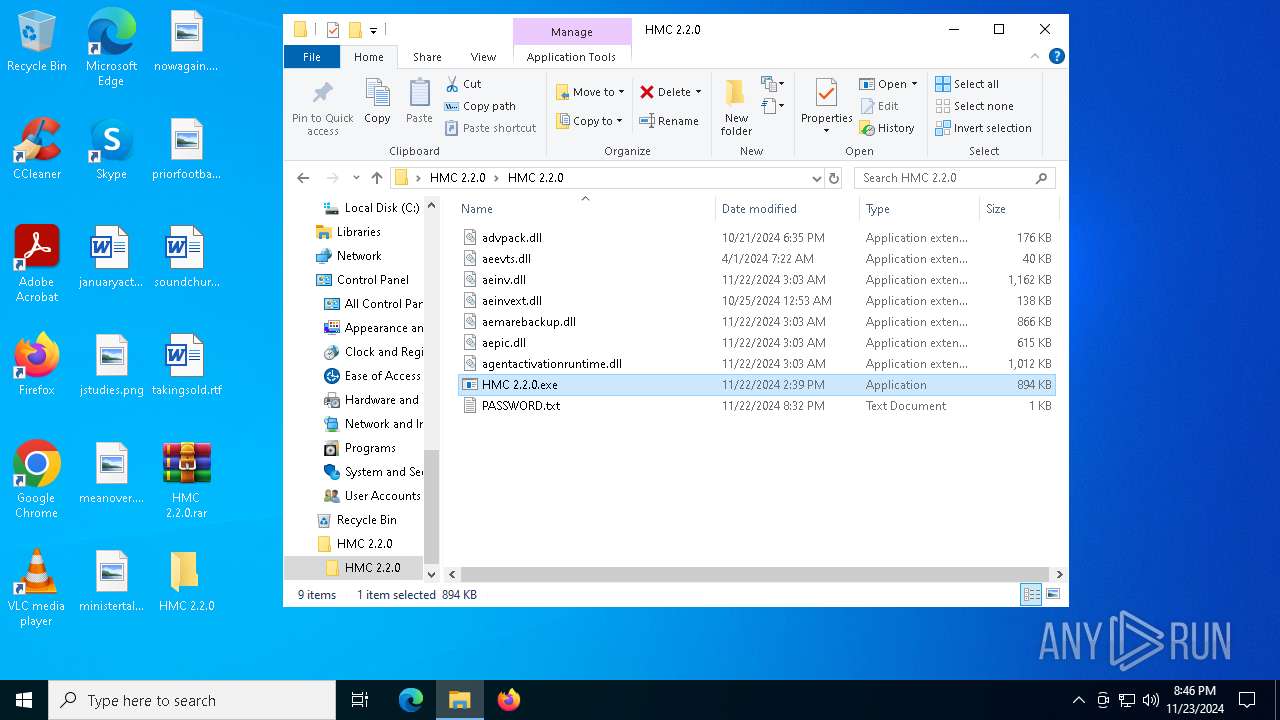
Executable files
8
Suspicious files
5
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6192 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_MSBuild.exe_8d0718ce377c99fa5d8861ab2a65928ce8cb14_69d9334a_fa72ec4f-ec17-4f12-aec6-5ec51531ebb4\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6192 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\MSBuild.exe.1480.dmp | — | |
MD5:— | SHA256:— | |||
| 6192 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | der | |
MD5:F0CF5B1794ECA7CD73F9C020DAAB8EF2 | SHA256:2AF00EDCE7EF3266897E52DC81E8DE3B7A079028C0F1F96EAFF9E38AD342F617 | |||
| 5300 | WinRAR.exe | C:\Users\admin\Desktop\HMC 2.2.0\HMC 2.2.0\advpack.dll | executable | |
MD5:327C4CBBA43881847674C831E4B1A672 | SHA256:D91AF176C416E14D9533614287FE1175FCD193EE8125280EE777C92EF7E683B9 | |||
| 5300 | WinRAR.exe | C:\Users\admin\Desktop\HMC 2.2.0\HMC 2.2.0\aepic.dll | executable | |
MD5:A039814FA8BB5E0258FC75DA497F3CA5 | SHA256:5AE3B209390D6E5A6A25E3CD9FC15F5A58C8167D6EDC6488CC65B854EF234681 | |||
| 6192 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERA433.tmp.WERInternalMetadata.xml | xml | |
MD5:EAD973A92EA5D4E85E6320C6F38A66BC | SHA256:DAF9E6072FB0DDFD57B1C6AB0F465055DD45F69FBF21C9CCFE9F63357AF665DA | |||
| 5300 | WinRAR.exe | C:\Users\admin\Desktop\HMC 2.2.0\HMC 2.2.0\HMC 2.2.0.exe | executable | |
MD5:D88DF6EBC50187269FB9038A80776DF8 | SHA256:B85AC3BDEAE6D374A14895A1417F25BFBD481EE44C26C320F1E6DA34FF6508BB | |||
| 5300 | WinRAR.exe | C:\Users\admin\Desktop\HMC 2.2.0\HMC 2.2.0\agentactivationruntime.dll | executable | |
MD5:44DFA56134ED49E584A12780E5C2E9C9 | SHA256:367F1FD7DCF1AF6C3E1F1D8A37F471350FE8EB0A5B1680E990C2A5497B2B5CBE | |||
| 6192 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:F6F53CD09A41E968C363419B279D3112 | SHA256:6D2BB01CC7A9BADE2113B219CAC1BDA86B2733196B7E1BD0C807CE1E396B1892 | |||
| 5300 | WinRAR.exe | C:\Users\admin\Desktop\HMC 2.2.0\HMC 2.2.0\PASSWORD.txt | text | |
MD5:CF82A9577F8E6FA17CE3CCF4DAAF94E9 | SHA256:CCE5B821596B76AA7137DA40AE522195BE76FD67A17470921077E0AA226D8045 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
36
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3220 | svchost.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3220 | svchost.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6316 | SIHClient.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6316 | SIHClient.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
244 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6192 | WerFault.exe | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6192 | WerFault.exe | GET | 200 | 2.23.9.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2088 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3220 | svchost.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3220 | svchost.exe | 2.23.9.218:80 | www.microsoft.com | AKAMAI-AS | CZ | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 23.212.110.176:443 | www.bing.com | Akamai International B.V. | CZ | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
MSBuild.exe | CLR: Managed code called FailFast without specifying a reason.
|