| File name: | 0318.ps1 |
| Full analysis: | https://app.any.run/tasks/7c8c7386-4875-4230-8221-dd1d3f0e11c4 |
| Verdict: | Malicious activity |
| Analysis date: | March 18, 2020, 14:06:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text |
| MD5: | 0F8C854E12E2F376FCDC5AF97117222A |
| SHA1: | F884253FFC84E6313809EE751A7A7B84281CCD82 |
| SHA256: | 31B2DC5A2B235C9FB794911B45EDB5FA6DF6336A337DFBA91F2264D7A0CB9232 |
| SSDEEP: | 6:sGSQj9o8G56ONXxoy3Acn31kKxzD5CCJJNoYvn:sovMr9vkMcCJZvn |
MALICIOUS
No malicious indicators.SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2580)
- powershell.exe (PID: 3224)
Creates files in the user directory
- powershell.exe (PID: 3832)
- powershell.exe (PID: 2580)
- powershell.exe (PID: 2916)
- powershell.exe (PID: 3224)
Executes PowerShell scripts
- powershell.exe (PID: 3224)
- powershell.exe (PID: 2580)
Application launched itself
- powershell.exe (PID: 3224)
- powershell.exe (PID: 2580)
INFO
Manual execution by user
- powershell.exe (PID: 3224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
4
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2580 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\0318.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
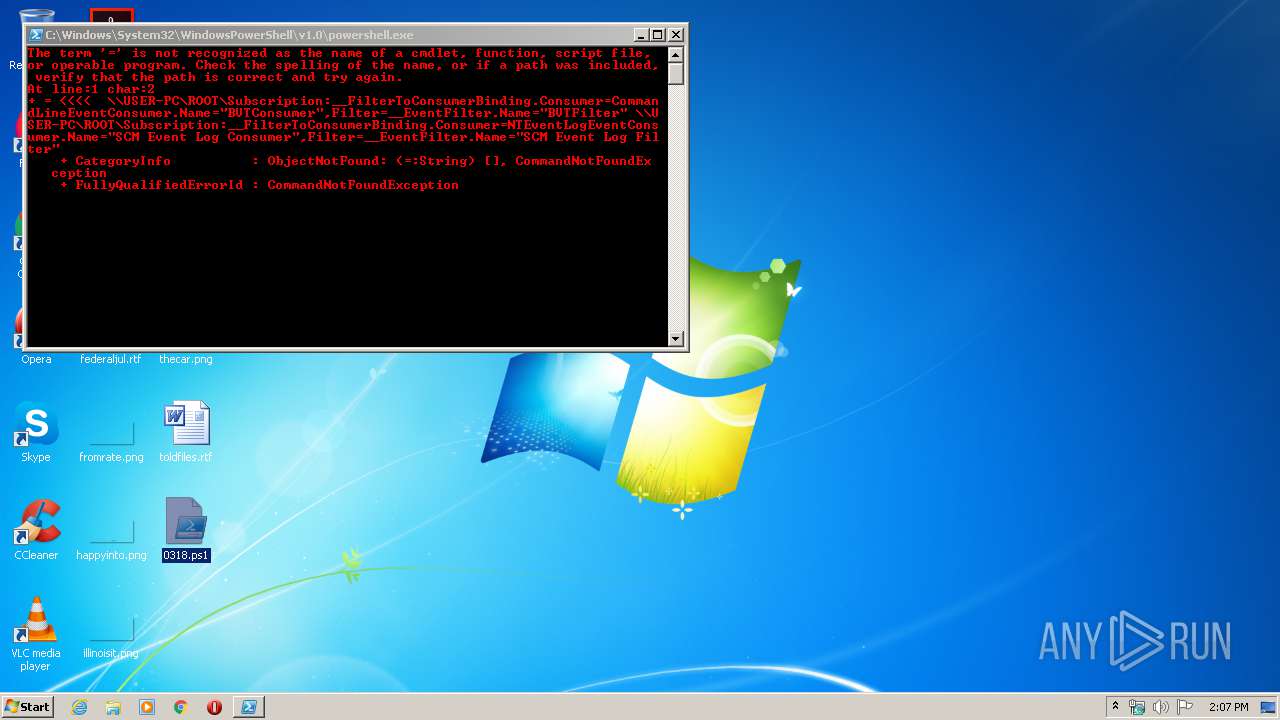
| 2916 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" = "\\USER-PC\ROOT\Subscription:__FilterToConsumerBinding.Consumer="CommandLineEventConsumer.Name=\"BVTConsumer\"",Filter="__EventFilter.Name=\"BVTFilter\"" \\USER-PC\ROOT\Subscription:__FilterToConsumerBinding.Consumer="NTEventLogEventConsumer.Name=\"SCM Event Log Consumer\"",Filter="__EventFilter.Name=\"SCM Event Log Filter\""" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3224 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" "-file" "C:\Users\admin\Desktop\0318.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3832 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" = "\\USER-PC\ROOT\Subscription:__FilterToConsumerBinding.Consumer="CommandLineEventConsumer.Name=\"BVTConsumer\"",Filter="__EventFilter.Name=\"BVTFilter\"" \\USER-PC\ROOT\Subscription:__FilterToConsumerBinding.Consumer="NTEventLogEventConsumer.Name=\"SCM Event Log Consumer\"",Filter="__EventFilter.Name=\"SCM Event Log Filter\""" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 044
Read events
804
Write events
240
Delete events
0
Modification events
| (PID) Process: | (2580) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2580) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2580) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3832) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2580) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2580) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2580) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2580) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2580) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2580) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
0
Suspicious files
8
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CFQIHJZSET8AX5CW9QFS.temp | — | |
MD5:— | SHA256:— | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8P3LBWT6YBE1DP4UPMTG.temp | — | |
MD5:— | SHA256:— | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\L3JJYYVVGD27EGA3ZVRE.temp | — | |
MD5:— | SHA256:— | |||
| 2916 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EUUUV6UHAEXKZUS7J1FK.temp | — | |
MD5:— | SHA256:— | |||
| 2580 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa66913.TMP | binary | |
MD5:— | SHA256:— | |||
| 2580 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa66fc9.TMP | binary | |
MD5:— | SHA256:— | |||
| 3832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa6bec4.TMP | binary | |
MD5:— | SHA256:— | |||
| 3224 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | powershell.exe | GET | — | 45.140.88.159:80 | http://winupdate.firewall-gateway.de/ze6.ps1 | unknown | — | — | malicious |
2580 | powershell.exe | GET | — | 45.140.88.159:80 | http://winupdate.firewall-gateway.de/ze6.ps1 | unknown | — | — | malicious |
3224 | powershell.exe | GET | — | 45.140.88.159:80 | http://winupdate.firewall-gateway.de/ze6.ps1 | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | powershell.exe | 45.140.88.159:80 | winupdate.firewall-gateway.de | — | — | suspicious |
3224 | powershell.exe | 45.140.88.159:80 | winupdate.firewall-gateway.de | — | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
winupdate.firewall-gateway.de |
| malicious |