| File name: | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2 |
| Full analysis: | https://app.any.run/tasks/f00b9496-3a2d-4b50-a23a-32628bb8f817 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 21:59:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 8BDC0EC3ACF010D35D64F2244513E340 |
| SHA1: | FC8BB6507C90F8EBA72344DC27905849FA30ECA7 |
| SHA256: | 31B1E1BDFF2029FDDFEA53DA3CD49666085B9C8D1070F2D544CF8190CECDB5A2 |
| SSDEEP: | 196608:FaDPebP3QT8LADqtlbVHm/NdSxmbU6G/jPB8OabzSIiN5Y9nc+YrCw:FaDer02lb9m/XNKPB0bzSIk5vrCw |
MALICIOUS
Loads dropped or rewritten executable
- python.exe (PID: 2800)
- python.exe (PID: 3140)
- python.exe (PID: 2132)
- python.exe (PID: 1704)
- python.exe (PID: 3412)
- python.exe (PID: 2676)
- 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe (PID: 2476)
Changes the autorun value in the registry
- python.exe (PID: 3140)
- python.exe (PID: 2676)
Uses Task Scheduler to run other applications
- python.exe (PID: 3140)
- python.exe (PID: 2676)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3872)
- schtasks.exe (PID: 3904)
Application was dropped or rewritten from another process
- python.exe (PID: 3412)
- python.exe (PID: 2800)
- python.exe (PID: 3140)
- python.exe (PID: 2132)
- python.exe (PID: 2676)
- python.exe (PID: 1704)
- ns38AF.tmp (PID: 3192)
SUSPICIOUS
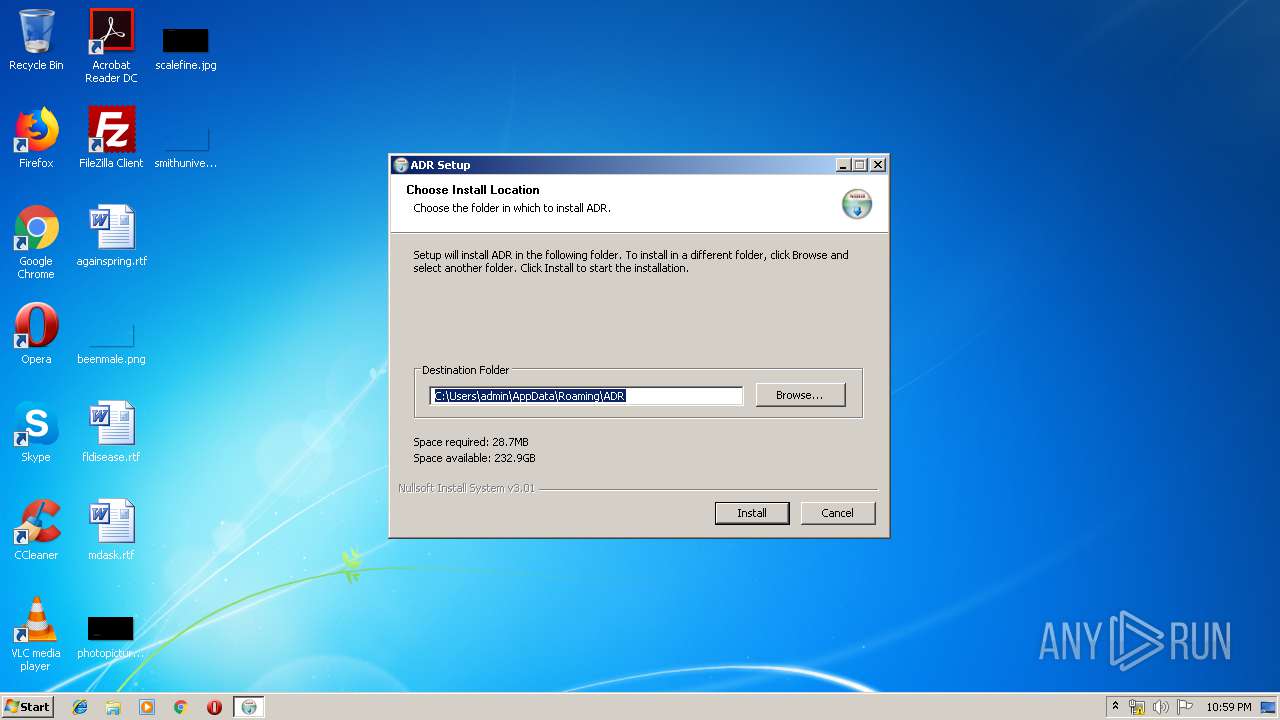
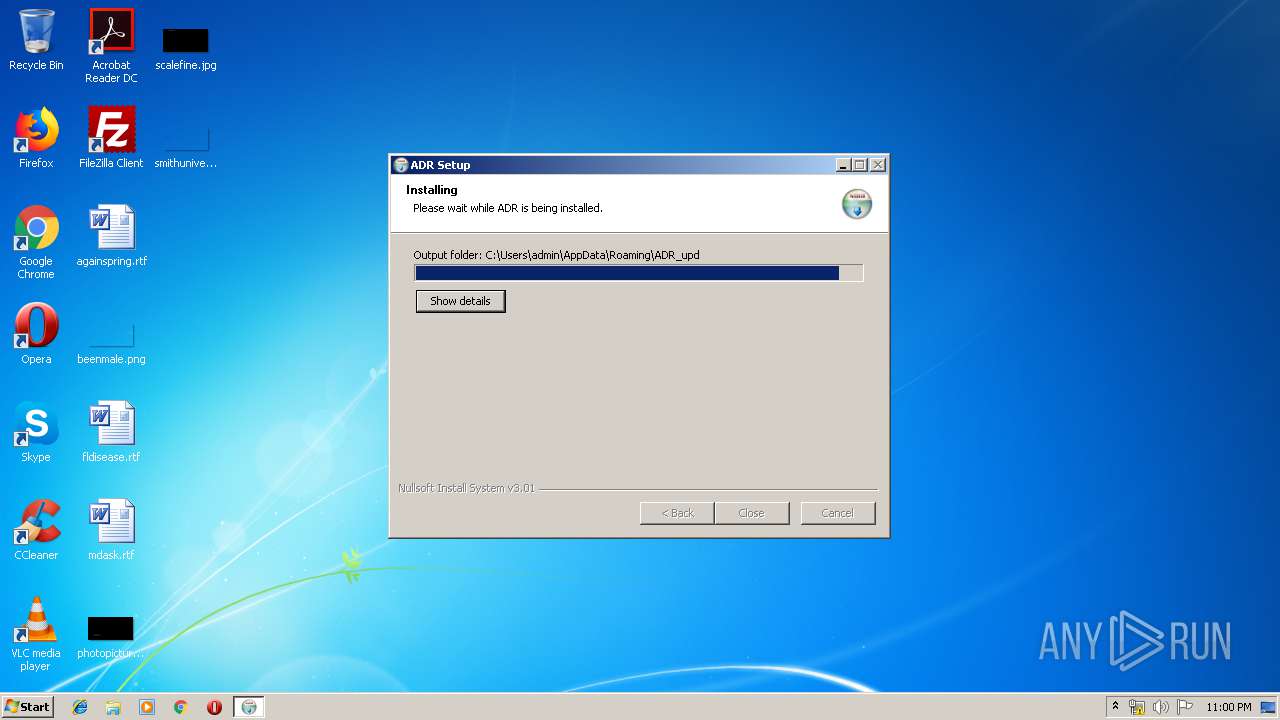
Creates a software uninstall entry
- 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe (PID: 2476)
Starts application with an unusual extension
- 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe (PID: 2476)
Loads Python modules
- python.exe (PID: 2800)
- python.exe (PID: 2132)
- python.exe (PID: 3140)
- python.exe (PID: 2676)
- python.exe (PID: 1704)
Creates files in the user directory
- python.exe (PID: 2800)
- 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe (PID: 2476)
- python.exe (PID: 1704)
Application launched itself
- python.exe (PID: 2800)
- python.exe (PID: 3412)
Starts itself from another location
- python.exe (PID: 2800)
Changes tracing settings of the file or console
- 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe (PID: 2476)
Executable content was dropped or overwritten
- 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe (PID: 2476)
INFO
Dropped object may contain Bitcoin addresses
- 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe (PID: 2476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:11 22:51:02+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 186880 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x346c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | ADR installer |
| FileDescription: | ADR installer |
| FileVersion: | 1.0.0 |
| ProductName: | ADR |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Dec-2016 21:51:02 |
| Detected languages: |
|
| Comments: | ADR installer |
| FileDescription: | ADR installer |
| FileVersion: | 1.0.0 |
| ProductName: | ADR |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Dec-2016 21:51:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000655F | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49212 |
.rdata | 0x00008000 | 0x000014B0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03317 |
.data | 0x0000A000 | 0x0002B018 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.1105 |
.ndata | 0x00036000 | 0x00020000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00056000 | 0x00004518 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.89274 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2963 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1704 | python\python.exe start.pyc settings.ini rules.ini httpfilter | C:\Users\admin\AppData\Roaming\ADR\python\python.exe | — | python.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.7.0b4 Modules
| |||||||||||||||
| 2132 | python\python.exe start.pyc app | C:\Users\admin\AppData\Roaming\ADR_upd\python\python.exe | python.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 1 Version: 3.7.0b4 Modules
| |||||||||||||||
| 2476 | "C:\Users\admin\AppData\Local\Temp\31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe" | C:\Users\admin\AppData\Local\Temp\31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ADR installer Exit code: 0 Version: 1.0.0 Modules
| |||||||||||||||
| 2676 | python\python.exe start.pyc --act=inst ml3 | C:\Users\admin\AppData\Roaming\ADR\python\python.exe | python.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.7.0b4 Modules
| |||||||||||||||
| 2800 | python\python.exe start.pyc --subid="" --pb="" firstlaunch | C:\Users\admin\AppData\Roaming\ADR_upd\python\python.exe | ns38AF.tmp | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.7.0b4 Modules
| |||||||||||||||
| 3140 | python\python.exe start.pyc --act=inst ml3 | C:\Users\admin\AppData\Roaming\ADR_upd\python\python.exe | python.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.7.0b4 Modules
| |||||||||||||||
| 3192 | "C:\Users\admin\AppData\Local\Temp\nsm389E.tmp\ns38AF.tmp" python\python.exe start.pyc --subid="" --pb="" firstlaunch | C:\Users\admin\AppData\Local\Temp\nsm389E.tmp\ns38AF.tmp | — | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3412 | python\python.exe start.pyc launchall | C:\Users\admin\AppData\Roaming\ADR\python\python.exe | — | python.exe | |||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.7.0b4 Modules
| |||||||||||||||
| 3872 | schtasks /create /f /tn "ADR_upd" /xml "C:\Users\admin\AppData\Local\Temp\tmpshuf2nhm" | C:\Windows\system32\schtasks.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3904 | schtasks /create /f /tn "ADR" /xml "C:\Users\admin\AppData\Local\Temp\tmpmkfsq8kc" | C:\Windows\system32\schtasks.exe | — | python.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
408
Read events
384
Write events
24
Delete events
0
Modification events
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_CURRENT_USER\Software\ADR |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Roaming\ADR | |||
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\ADR |
| Operation: | write | Name: | DisplayName |
Value: ADR | |||
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\ADR |
| Operation: | write | Name: | UninstallString |
Value: C:\Users\admin\AppData\Roaming\ADR\uninstall.exe | |||
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\ADR |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Roaming\ADR\uninstall.exe | |||
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2476) 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
142
Suspicious files
13
Text files
12
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\start.bin | binary | |
MD5:— | SHA256:— | |||
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\settings.ini | text | |
MD5:— | SHA256:— | |||
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\start.pyc | binary | |
MD5:— | SHA256:— | |||
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\filter.bin | binary | |
MD5:— | SHA256:— | |||
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\rules.ini | text | |
MD5:— | SHA256:— | |||
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\python\_decimal.pyd | executable | |
MD5:4A79334D2269E146730E43F2109B2DDF | SHA256:7EB21CED53F0C3BEE99D716D6A3507AF4BE0715AB5E4C17A421CE8C471DAD7E4 | |||
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\python\_bz2.pyd | executable | |
MD5:D0F296E00B1DB1DABAD352D337DBF5E7 | SHA256:72D74C648A78414E4715652051228F1E8CEBF0A03A3771DF8AEC4645BC89585D | |||
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\python\_asyncio.pyd | executable | |
MD5:A93D01F1FBD5FDD7B47574CD7D7429A5 | SHA256:CA96A1FF0DD538F6C58A9124E081F508F036BD15229FA9F919C79234F41CC47B | |||
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\python\_distutils_findvs.pyd | executable | |
MD5:F87CC67A246AA09A5704D6C8F209CD40 | SHA256:9FD534872373A8E288A7EB8DAC28AE93558929034E9791058531701772F10507 | |||
| 2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | C:\Users\admin\AppData\Roaming\ADR\python\_elementtree.pyd | executable | |
MD5:7C384AEFFC09CF63DC763727EC51904E | SHA256:A708D643FF5C3E14256E3FAE56E71596FC7D624F3773D5A59E99C169FB26F468 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | GET | 200 | 5.45.120.64:80 | http://savery.cc/install.php?id=-1&source=source22 | EE | text | 279 b | suspicious |
2800 | python.exe | GET | 200 | 216.58.207.78:80 | http://www.google-analytics.com/collect?v=1&t=pageview&tid=&z=128525407&cid=6cec3aae-7256-4af4-8af3-f36b2780db7e&ua=Mozilla%2F5.0+%28Windows+NT+6.1%3B+rv%3A47.0%29+Gecko%2F20100101+Firefox%2F47.0&sr=1280x720&de=cp1252&ul=en_US&dl=%2Finstaller%2FinstallSuccess&cd1=Win6.1&cd4=&cd5=2019-05-24+22%3A00%3A09.984875Z | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2800 | python.exe | 216.58.207.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2132 | python.exe | 8.8.8.8:53 | — | Google Inc. | US | malicious |
2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | 5.45.120.64:80 | savery.cc | Fastvps Eesti Ou | EE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
savery.cc |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2800 | python.exe | Attempted Information Leak | ET POLICY Python-urllib/ Suspicious User Agent |
2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | A Network Trojan was detected | ET POLICY User-Agent (NSIS_Inetc (Mozilla)) - Sometimes used by hostile installers |
2476 | 31b1e1bdff2029fddfea53da3cd49666085b9c8d1070f2d544cf8190cecdb5a2.exe | Misc activity | SUSPICIOUS [PTsecurity] Suspicious HTTP header - Sometimes used by hostile installer |
1 ETPRO signatures available at the full report