| File name: | ScreenConnect.ClientSetup.exe |
| Full analysis: | https://app.any.run/tasks/b9fb068e-4a0a-43ce-bf0b-ef7a2432a204 |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2024, 00:15:15 |
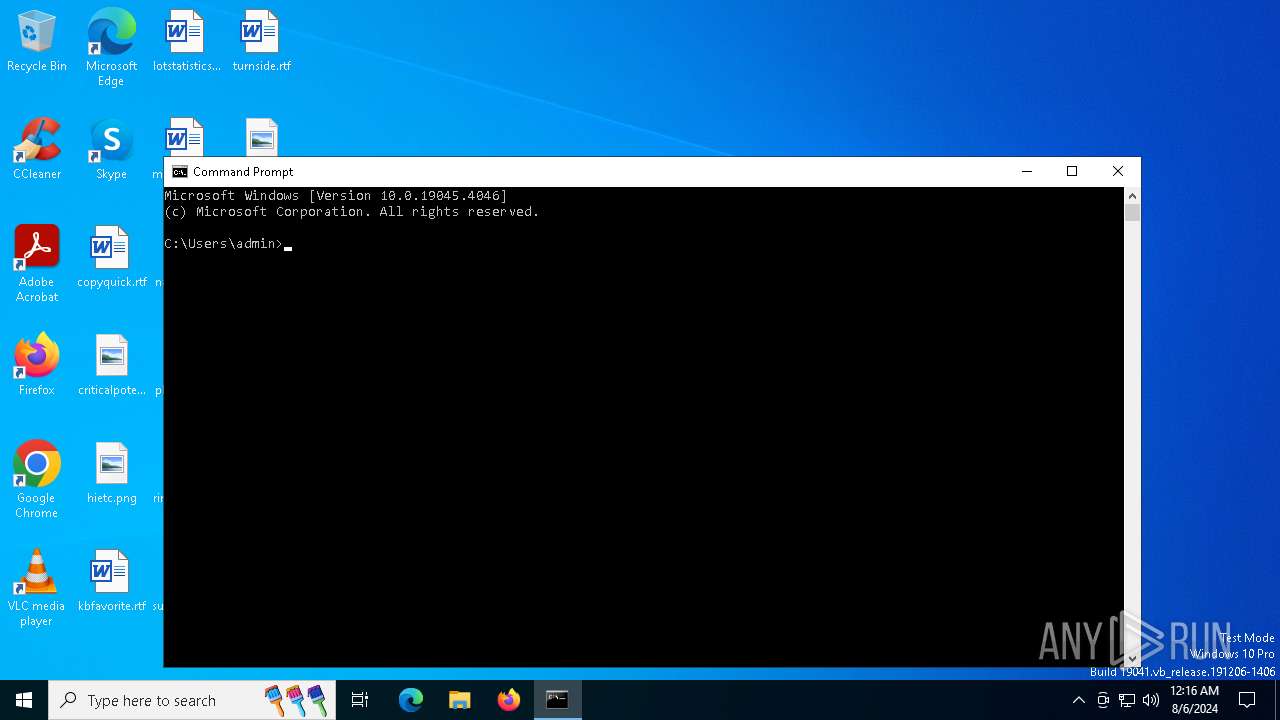
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A27269890DC74188A69E34D540B0A8C6 |
| SHA1: | 7853BE6A2C4F8FA8BB26D0B0B145C3F970F24689 |
| SHA256: | 319F8C367CD88D25BD3CF31B48DBB7137DC1EF9F74D985E65F43F3CD96A03E57 |
| SSDEEP: | 98304:GuQh6msqnDMvAO1OytH9awXB0DXe3S+5OmxlGwP3AW5JTGG0DR/WMMo+bMQzhM5U:C2DAcDFM5sE |
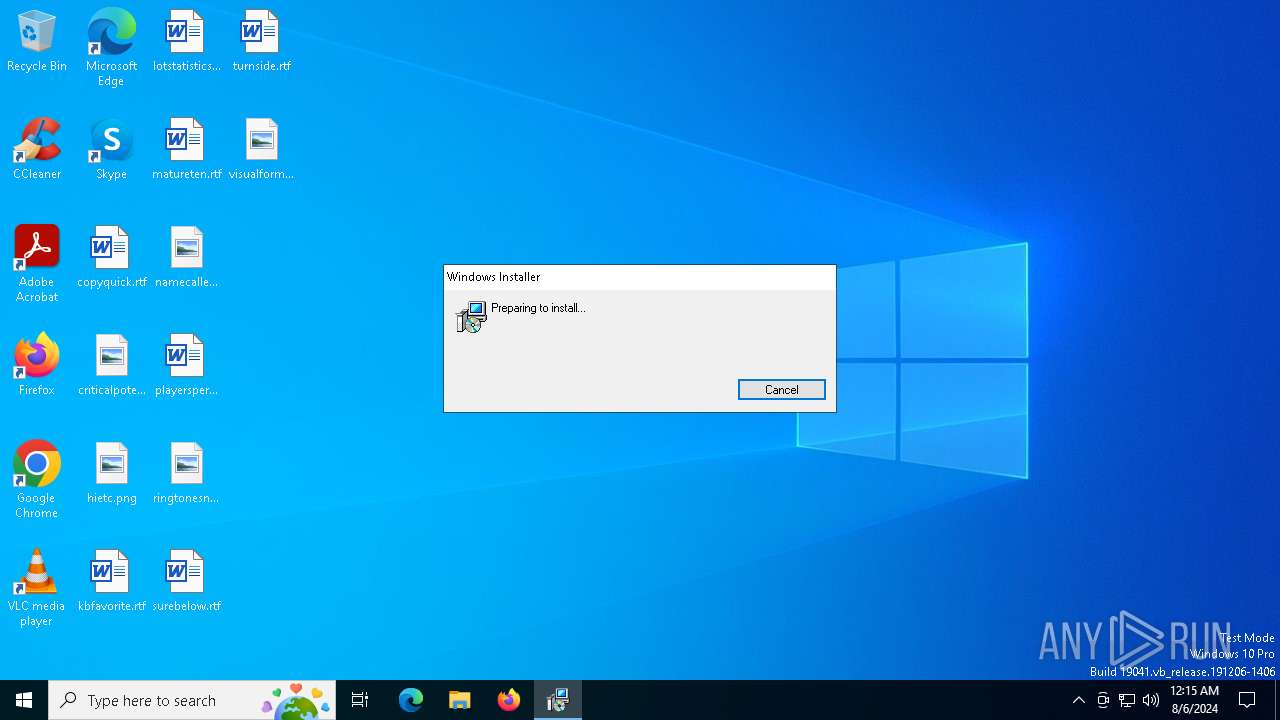
MALICIOUS
Drops the executable file immediately after the start
- ScreenConnect.ClientSetup.exe (PID: 6408)
- msiexec.exe (PID: 6612)
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 6764)
SUSPICIOUS
Reads security settings of Internet Explorer
- ScreenConnect.ClientSetup.exe (PID: 6408)
Reads the date of Windows installation
- ScreenConnect.ClientSetup.exe (PID: 6408)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 6764)
- VSSVC.exe (PID: 6828)
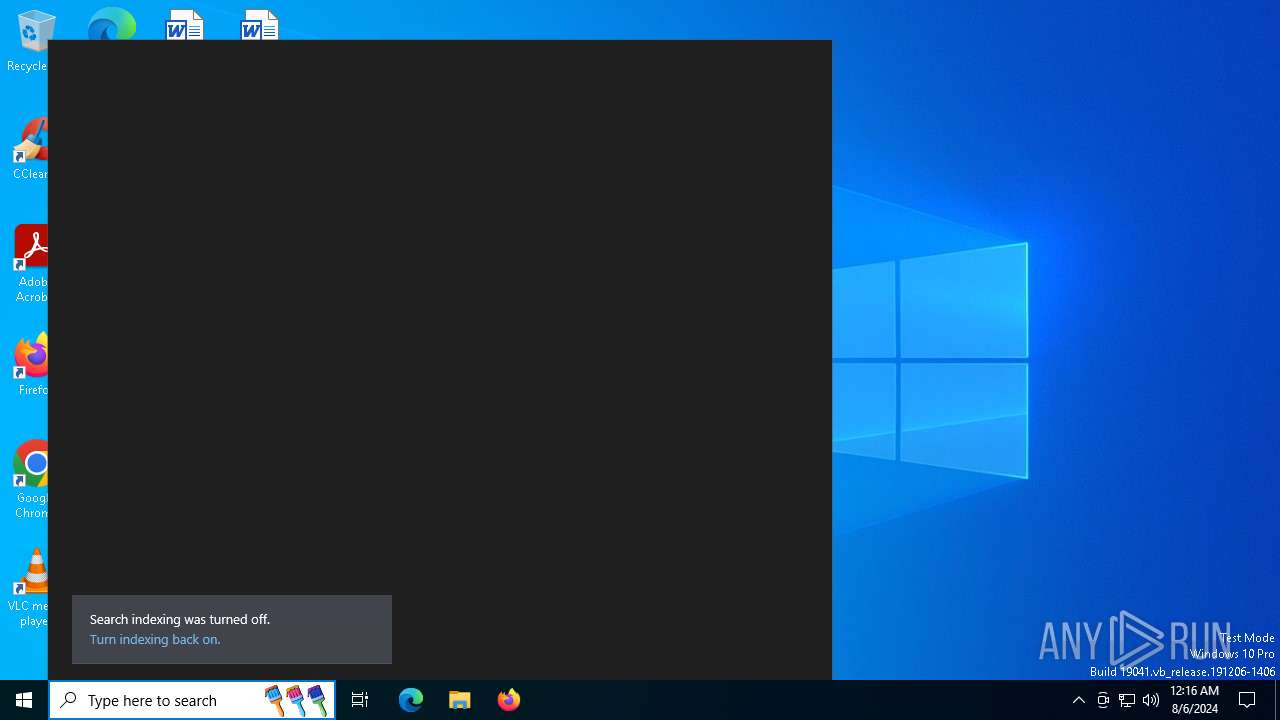
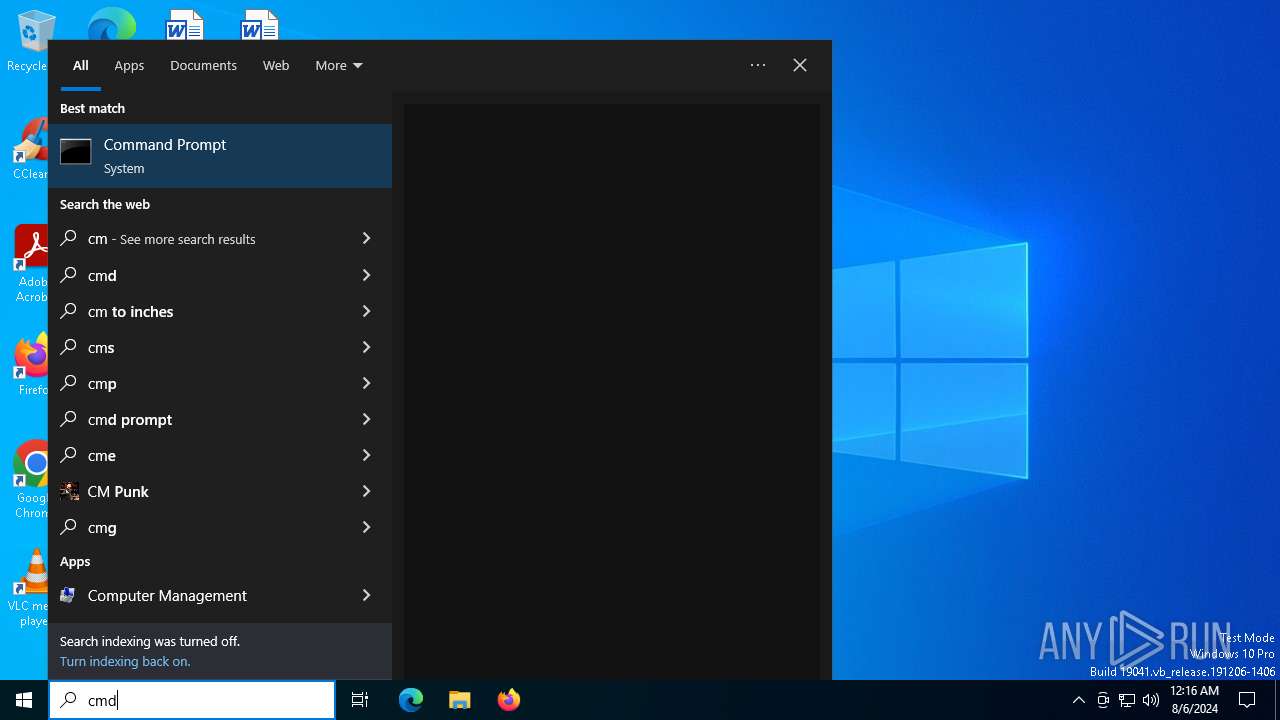
Identifying current user with WHOAMI command
- cmd.exe (PID: 7484)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 6764)
Executable content was dropped or overwritten
- rundll32.exe (PID: 6760)
There is functionality for taking screenshot (YARA)
- ScreenConnect.ClientService.exe (PID: 6764)
INFO
Checks supported languages
- ScreenConnect.ClientSetup.exe (PID: 6408)
- msiexec.exe (PID: 6612)
- msiexec.exe (PID: 6708)
Create files in a temporary directory
- ScreenConnect.ClientSetup.exe (PID: 6408)
- rundll32.exe (PID: 6760)
Reads the machine GUID from the registry
- ScreenConnect.ClientSetup.exe (PID: 6408)
Reads the computer name
- ScreenConnect.ClientSetup.exe (PID: 6408)
- msiexec.exe (PID: 6708)
- msiexec.exe (PID: 6612)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6612)
- msiexec.exe (PID: 6496)
Drops the executable file immediately after the start
- rundll32.exe (PID: 6760)
- msiexec.exe (PID: 6496)
Manual execution by a user
- cmd.exe (PID: 7484)
Process checks computer location settings
- ScreenConnect.ClientSetup.exe (PID: 6408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:18 20:10:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 45568 |
| InitializedDataSize: | 5513216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ad |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
158
Monitored processes
19
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files (x86)\ScreenConnect Client (4560edfdd60fa971)\ScreenConnect.WindowsClient.exe" "RunRole" "2903befc-faa8-4ea2-b4d3-001a1a756ad0" "User" | C:\Program Files (x86)\ScreenConnect Client (4560edfdd60fa971)\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: admin Company: ScreenConnect Software Integrity Level: MEDIUM Description: ScreenConnect Client Version: 24.1.7.8892 Modules
| |||||||||||||||
| 4128 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 4316 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4576 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6128 | C:\Windows\syswow64\MsiExec.exe -Embedding C43B7D78F06C7350E392F120531EEF3D E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6192 | C:\Windows\syswow64\MsiExec.exe -Embedding B316F74A273B4931C6B8409ED3B3F7E4 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6360 | "C:\Users\admin\AppData\Local\Temp\ScreenConnect.ClientSetup.exe" | C:\Users\admin\AppData\Local\Temp\ScreenConnect.ClientSetup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6408 | "C:\Users\admin\AppData\Local\Temp\ScreenConnect.ClientSetup.exe" | C:\Users\admin\AppData\Local\Temp\ScreenConnect.ClientSetup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
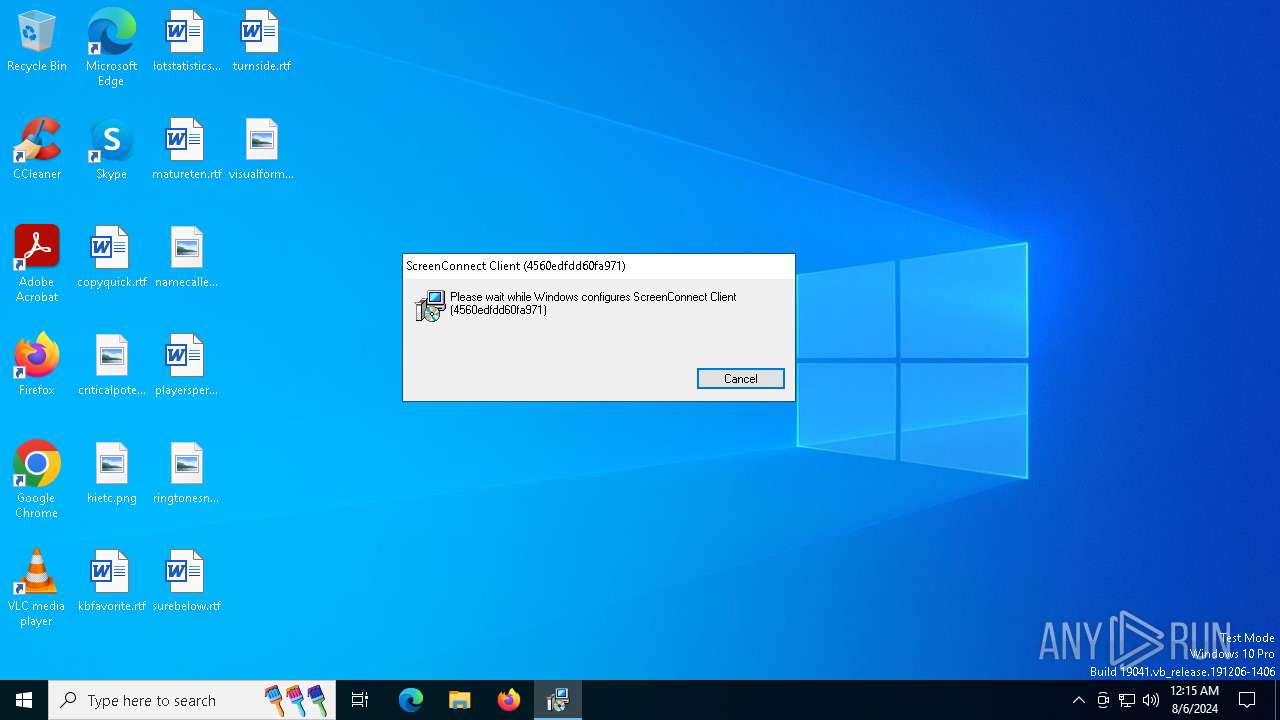
| 6496 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\4560edfdd60fa971\setup.msi" | C:\Windows\SysWOW64\msiexec.exe | ScreenConnect.ClientSetup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6612 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 885
Read events
13 563
Write events
303
Delete events
19
Modification events
| (PID) Process: | (6408) ScreenConnect.ClientSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6408) ScreenConnect.ClientSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6408) ScreenConnect.ClientSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6408) ScreenConnect.ClientSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000027C61BBF95E7DA01D4190000941A0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000003A2A1EBF95E7DA01D4190000941A0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000FE426FBF95E7DA01D4190000941A0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000FE426FBF95E7DA01D4190000941A0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000075A771BF95E7DA01D4190000941A0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6612) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000006E2D7BBF95E7DA01D4190000941A0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
19
Suspicious files
21
Text files
19
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6408 | ScreenConnect.ClientSetup.exe | C:\Users\admin\AppData\Local\Temp\ScreenConnect\4560edfdd60fa971\setup.msi | — | |
MD5:— | SHA256:— | |||
| 6496 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI8289.tmp | executable | |
MD5:FBEB822A9E120144D376522D86F09B1C | SHA256:5FF305D16BA9672D0AD11B0173502BACC877FA2C3C2395932473A88A7E534CB5 | |||
| 6612 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6612 | msiexec.exe | C:\Windows\Installer\ede65.msi | — | |
MD5:— | SHA256:— | |||
| 6760 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI8289.tmp-\ScreenConnect.Windows.dll | executable | |
MD5:AB11C92301BD6B916F51EB3C6BA1F348 | SHA256:EA86C15300B8CC311DE257456EA8B281AB7B5F231A4FCBCFF07E6F300E9ADE14 | |||
| 6760 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI8289.tmp-\TransformSecurityEventTriggerXml.xsl | text | |
MD5:41DFF6114A921D7AC5637B8AC9F04DC4 | SHA256:2CEFD9DB01C7A6F8E33A7DADBF511E963E56FF87D18064BAB2E4FE2D00A95797 | |||
| 6760 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI8289.tmp-\ScreenConnect.InstallerActions.dll | executable | |
MD5:23310F425A59C6D6B7D1814E84789542 | SHA256:0EAE8B0B1467BCF247C415F905FD72AD4A585AA04C9BA0D7FCBB9DB9D22B3BF2 | |||
| 6760 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI8289.tmp-\Microsoft.Deployment.WindowsInstaller.Package.dll | executable | |
MD5:A921A2B83B98F02D003D9139FA6BA3D8 | SHA256:548C551F6EBC5D829158A1E9AD1948D301D7C921906C3D8D6B6D69925FC624A1 | |||
| 6760 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI8289.tmp-\TransformClientOverrideResx.xsl | text | |
MD5:7F75CED83D8C263A88A622A1E089B902 | SHA256:115937C6A57BFC17E1F9EA92C0C146DB44C803A449207FC77DD53CB0824DAA29 | |||
| 6760 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSI8289.tmp-\Microsoft.Deployment.Compression.dll | executable | |
MD5:4717BCC62EB45D12FFBED3A35BA20E25 | SHA256:E04DE7988A2A39931831977FA22D2A4C39CF3F70211B77B618CAE9243170F1A7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
47
DNS requests
22
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1948 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7060 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
7032 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1420 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3164 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1420 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5336 | SearchApp.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1948 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Misc activity | ET INFO Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
6764 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |