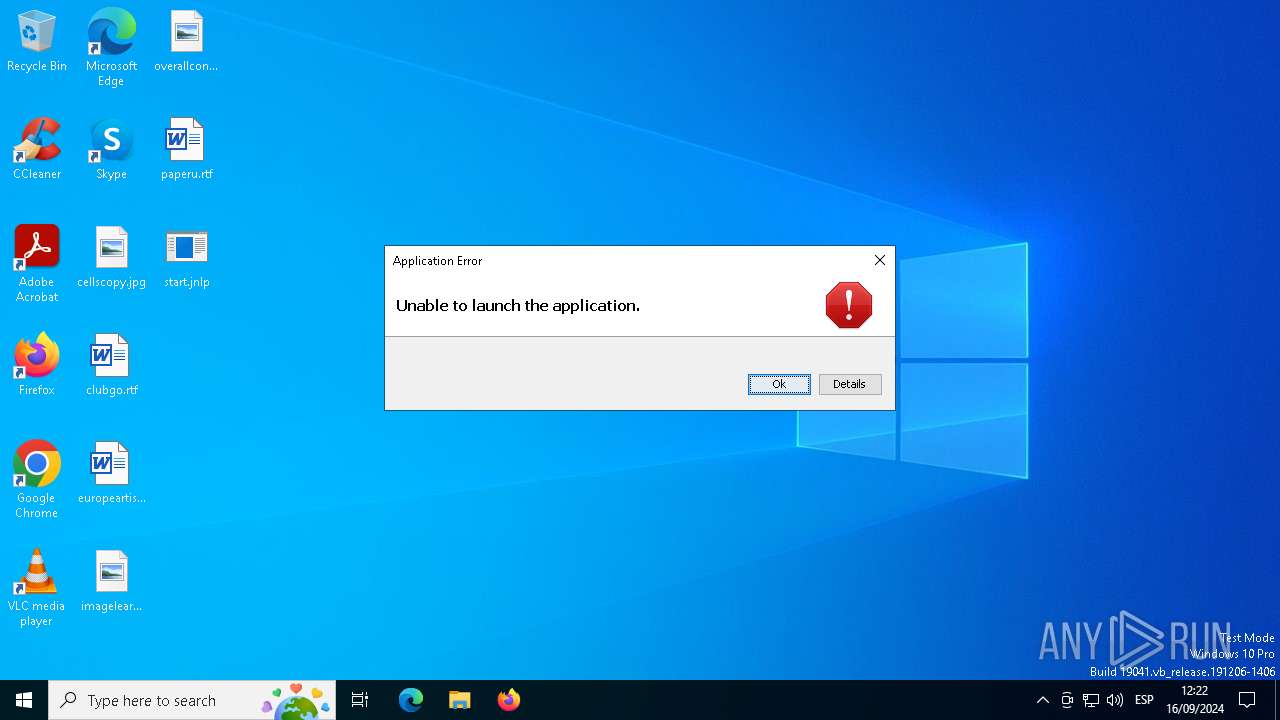
| File name: | start.jnlp |
| Full analysis: | https://app.any.run/tasks/ec4b9d83-bdb2-4a67-af9b-3660ecb8f86c |
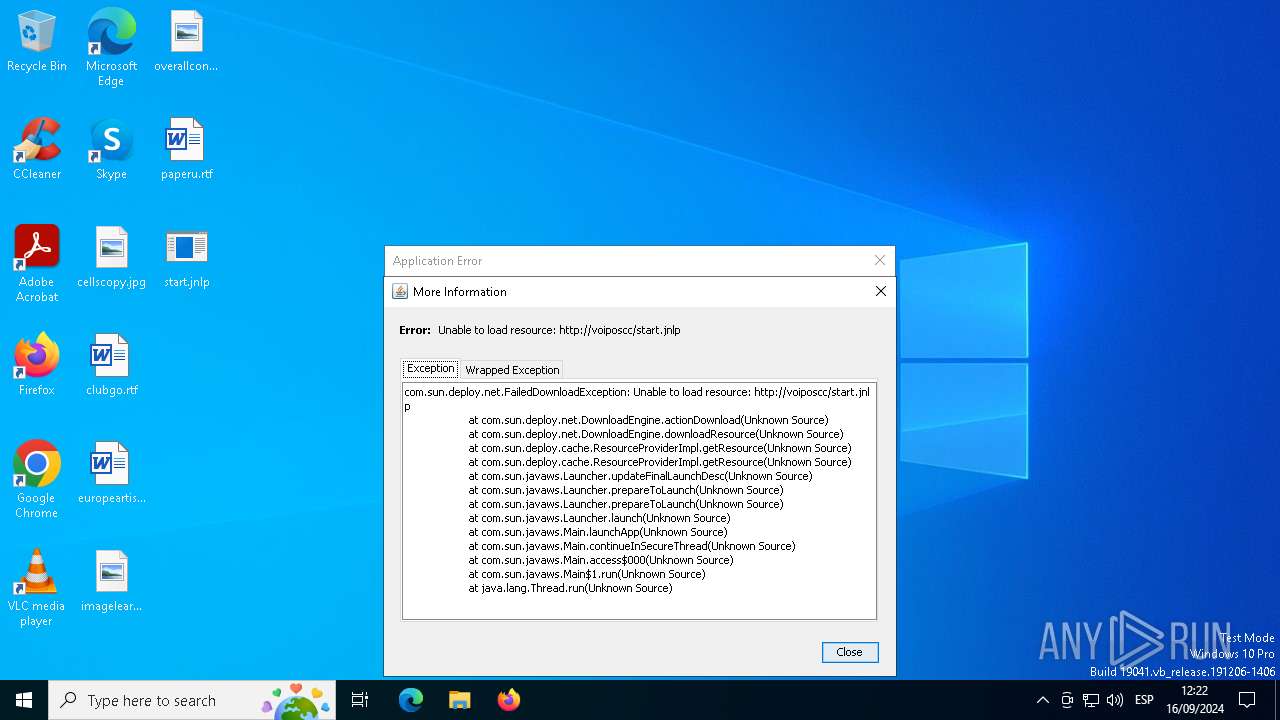
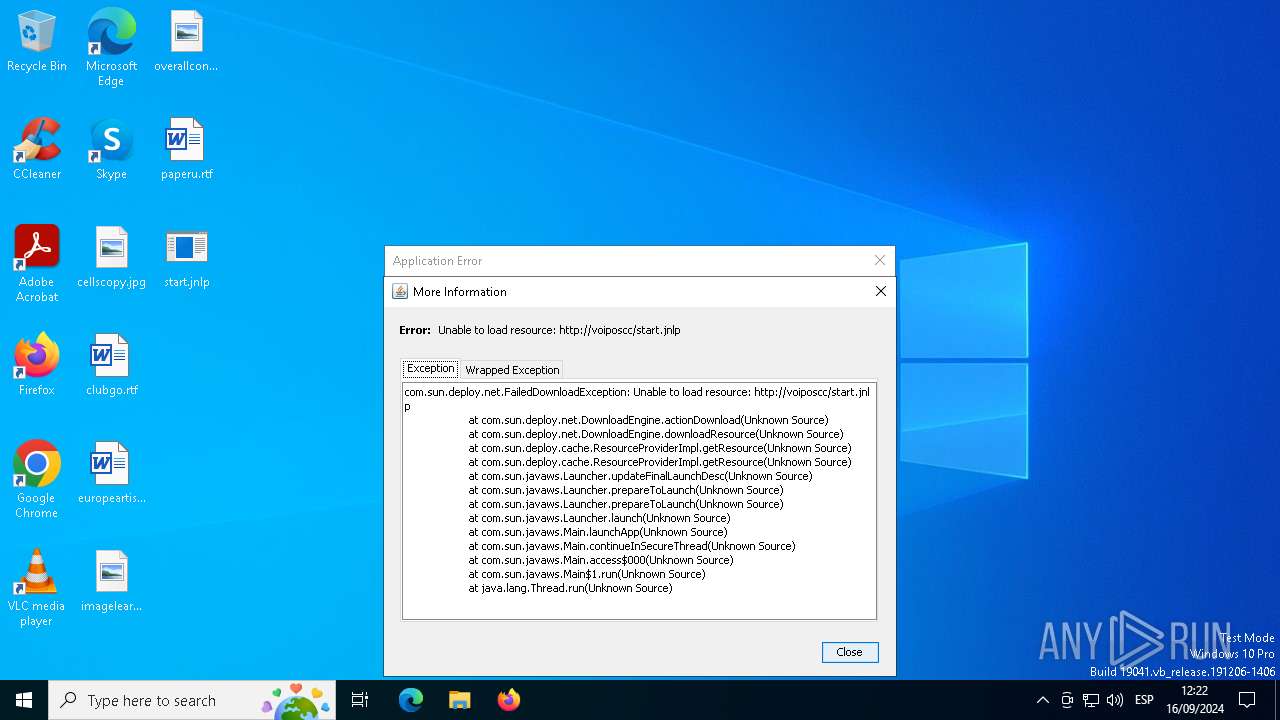
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2024, 10:21:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/xml |
| File info: | XML 1.0 document, ASCII text, with CRLF line terminators |
| MD5: | 727D00B60C231AB7058581171BD0D303 |
| SHA1: | 3C992C13CD0905968E239019748EABECC0F6A539 |
| SHA256: | 3167111F3D0BAF1FCE4CB5D2763B93AF66A2A2C02A77456131E071BE4225E9D2 |
| SSDEEP: | 48:cQa2ebsoMeCdN/lbj74V4+404B49H4V4M4Y4N4s4I41+4n4tQ4Ss4q4D484XX4AG:k2iRC3Zyc5licic95 |
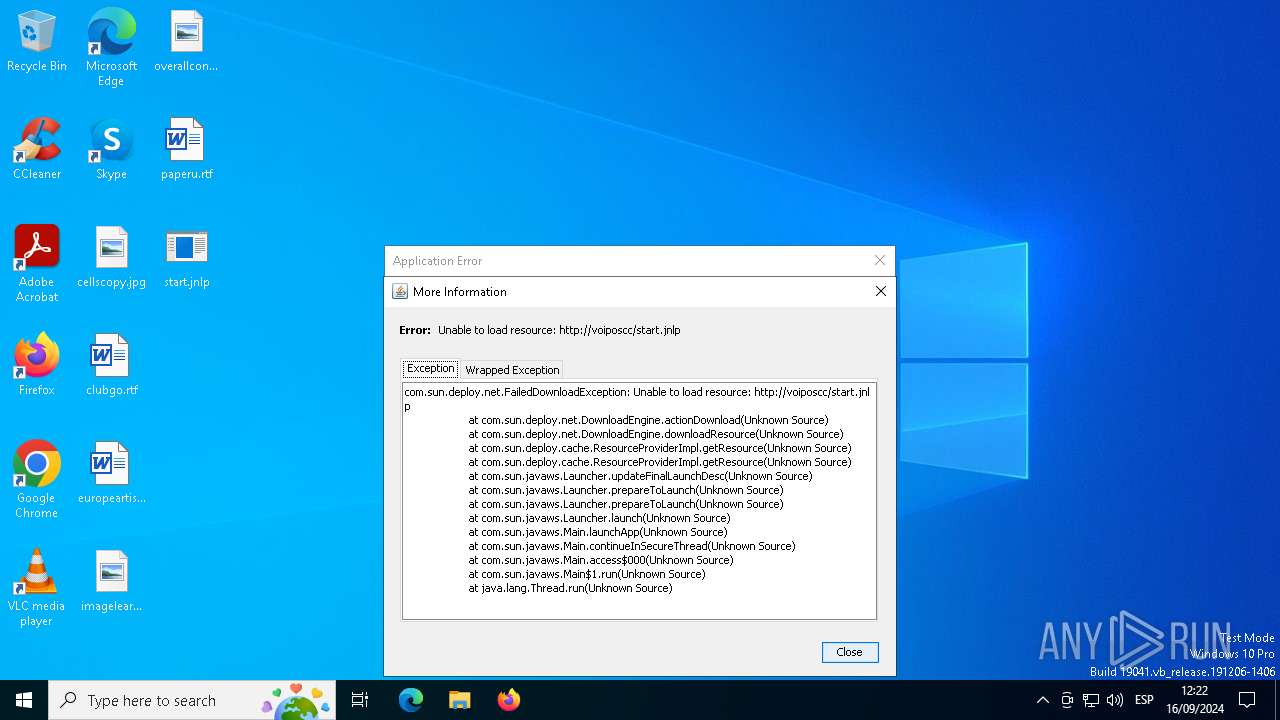
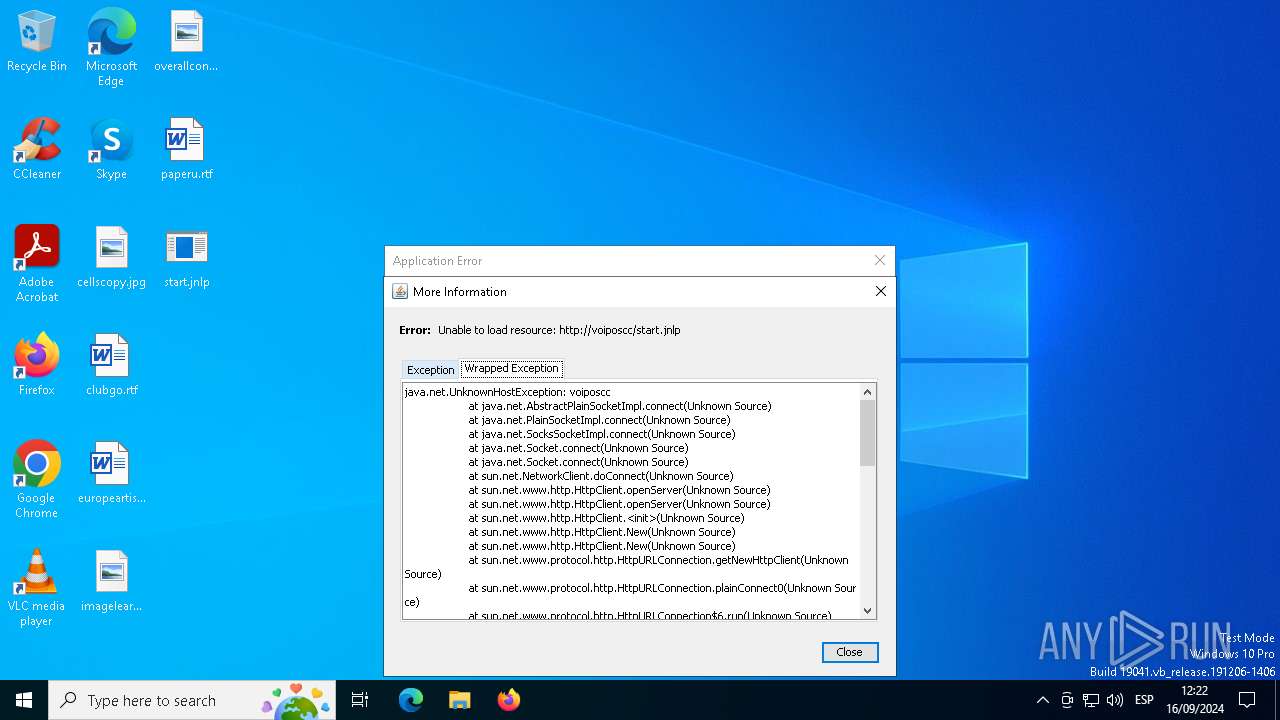
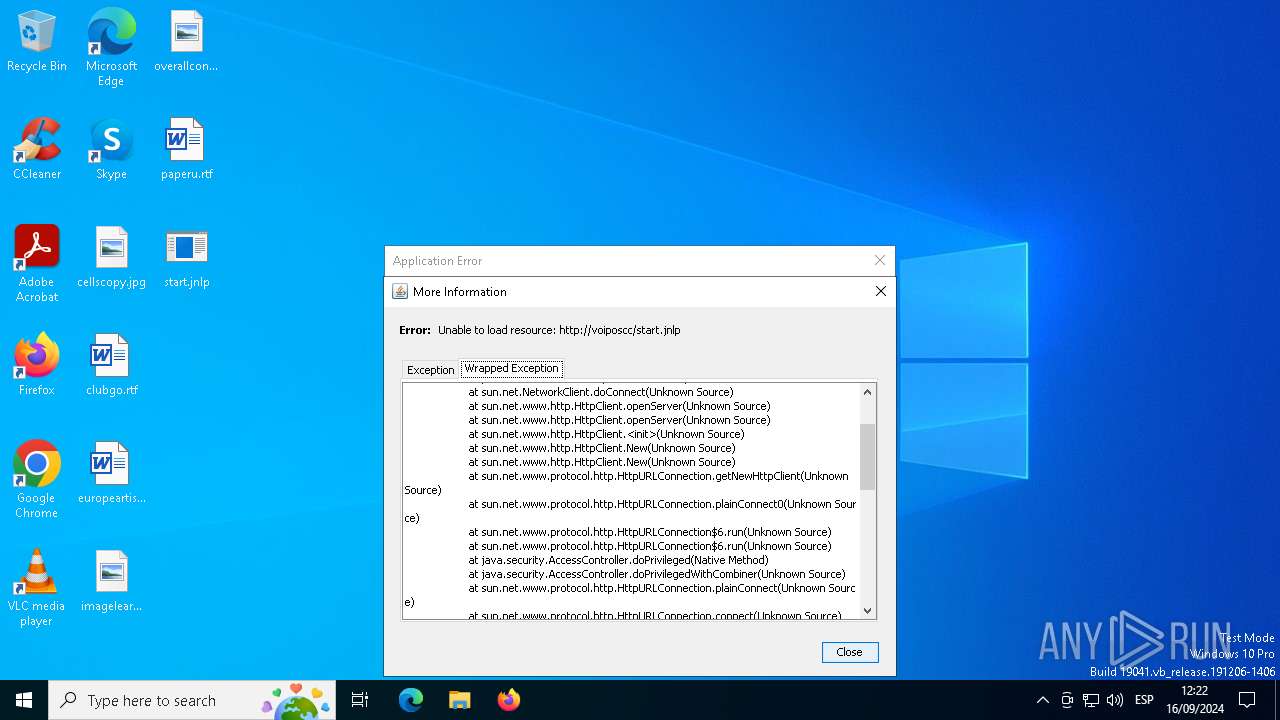
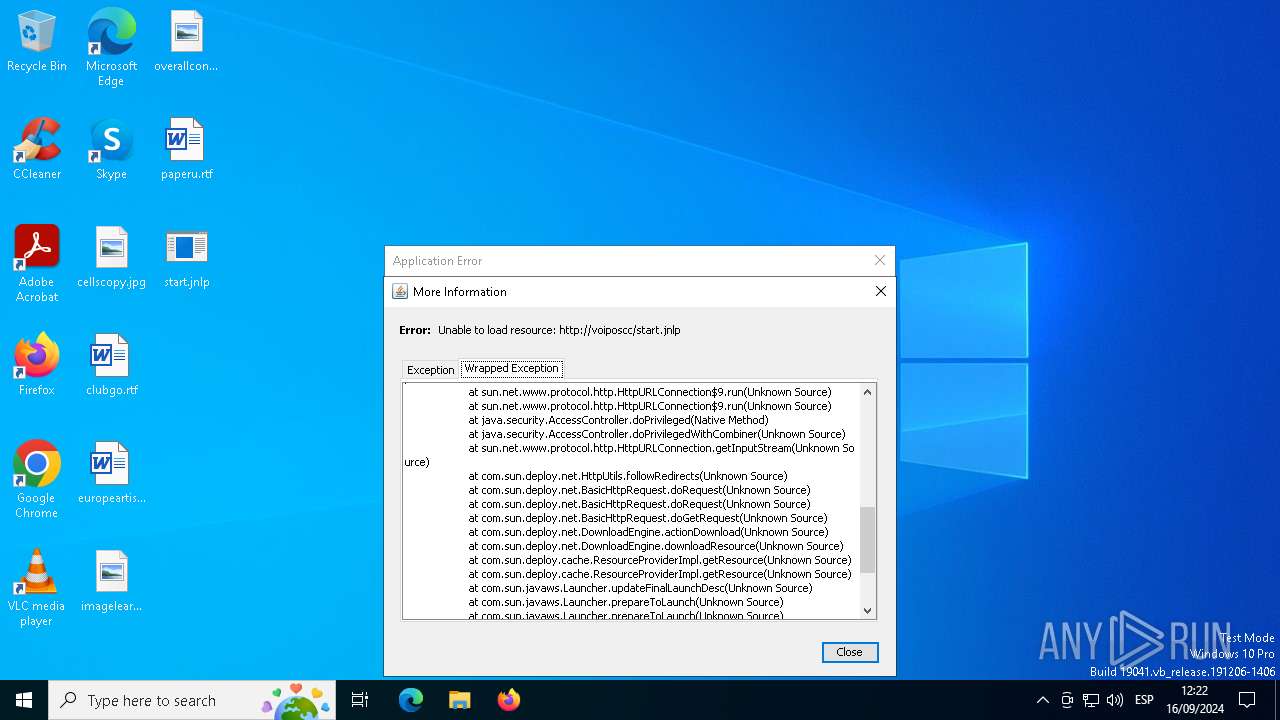
MALICIOUS
No malicious indicators.SUSPICIOUS
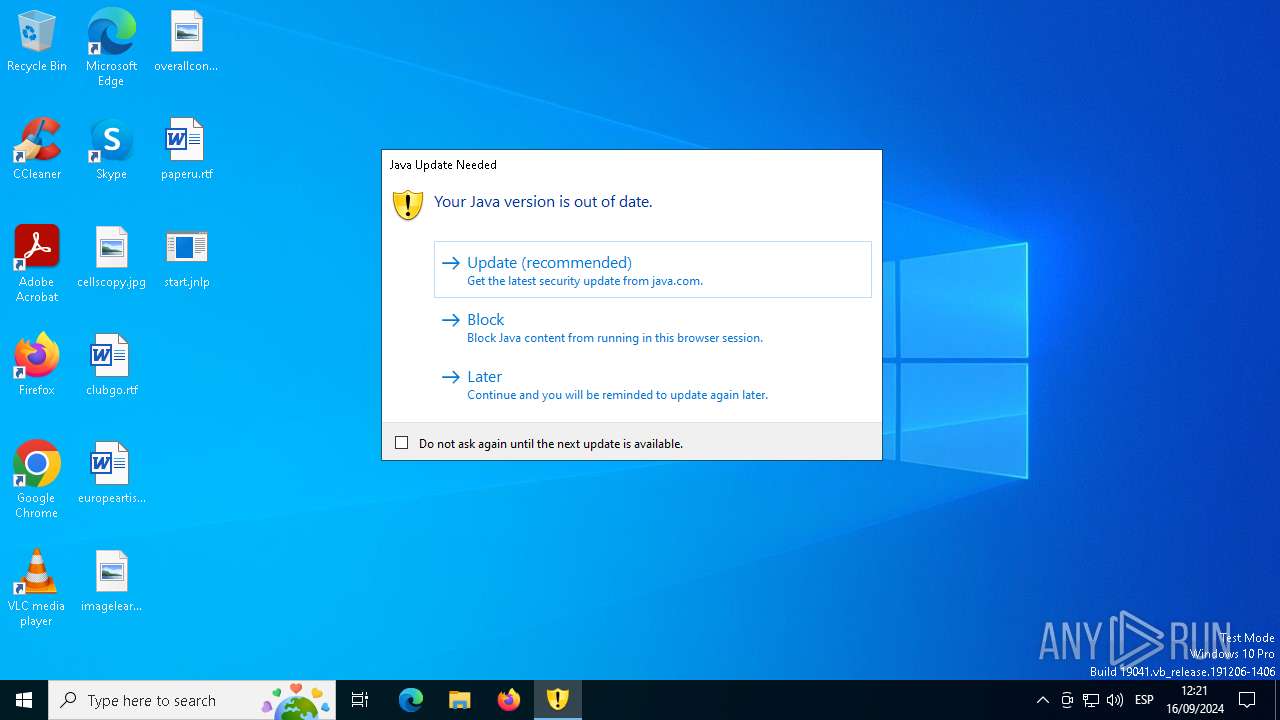
Checks for Java to be installed
- javaws.exe (PID: 3316)
- javaw.exe (PID: 1164)
- javaw.exe (PID: 6276)
- javaw.exe (PID: 3908)
- jp2launcher.exe (PID: 1568)
Application launched itself
- javaws.exe (PID: 3316)
Reads security settings of Internet Explorer
- jp2launcher.exe (PID: 1568)
INFO
Checks supported languages
- javaws.exe (PID: 3316)
- jp2launcher.exe (PID: 6352)
- javaw.exe (PID: 1164)
- javaw.exe (PID: 6276)
- javaw.exe (PID: 3908)
- javaws.exe (PID: 6568)
- jp2launcher.exe (PID: 1568)
Creates files in the program directory
- javaw.exe (PID: 1164)
Create files in a temporary directory
- javaw.exe (PID: 1164)
- javaw.exe (PID: 6276)
- javaw.exe (PID: 3908)
- jp2launcher.exe (PID: 1568)
Reads the computer name
- javaw.exe (PID: 1164)
- javaws.exe (PID: 3316)
- javaw.exe (PID: 6276)
- javaw.exe (PID: 3908)
- jp2launcher.exe (PID: 1568)
Checks proxy server information
- jp2launcher.exe (PID: 1568)
Reads the machine GUID from the registry
- jp2launcher.exe (PID: 1568)
Creates files or folders in the user directory
- jp2launcher.exe (PID: 1568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jnlp | | | Java Web Start application descriptor (82.6) |
|---|---|---|
| .xml | | | Generic XML (ASCII) (10.8) |
| .html | | | HyperText Markup Language (6.5) |
EXIF
XMP
| JnlpSpec: | 1 |
|---|---|
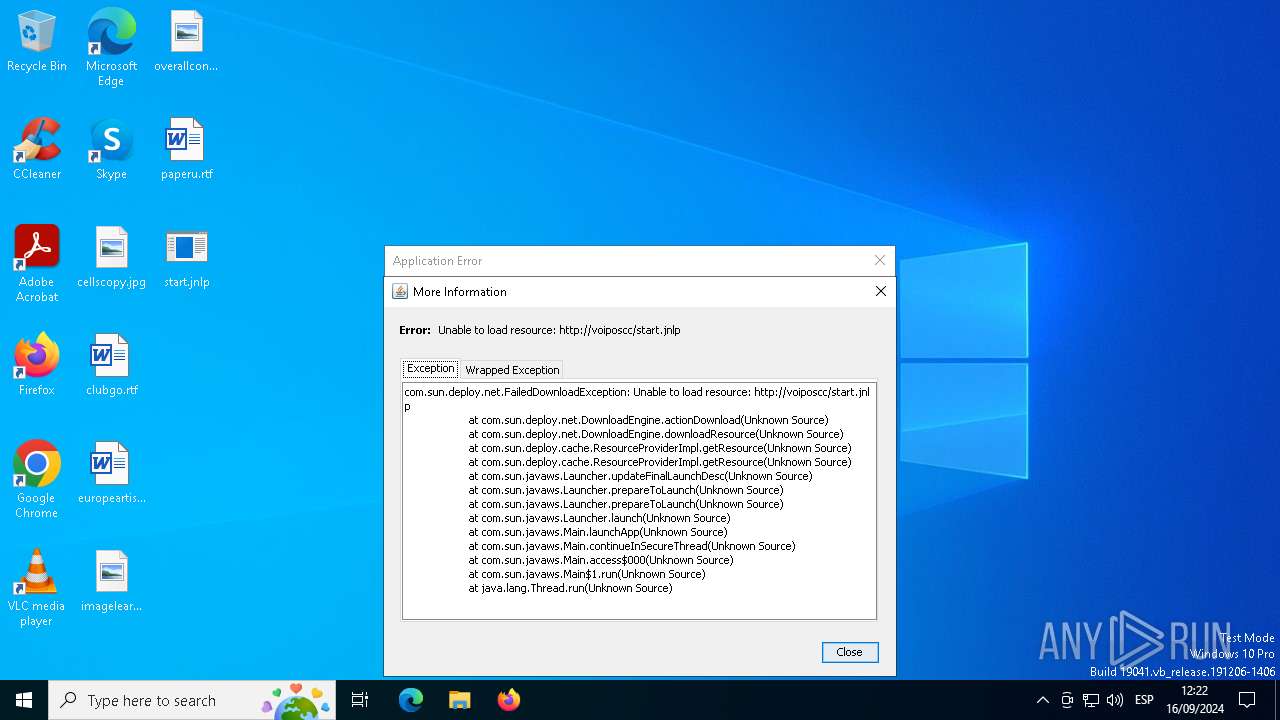
| JnlpCodebase: | http://voiposcc/ |
| JnlpHref: | start.jnlp |
| JnlpInformationTitle: | Agent Portal |
| JnlpInformationVendor: | Unify Software and Solutions GmbH & Co. KG |
| JnlpInformationHomepageHref: | docs/help.html |
| JnlpInformationDescription: | Agent Portal |
| JnlpInformationDescriptionKind: | short |
| JnlpInformationIconHref: | ./images/logo.png |
| JnlpInformationIconWidth: | 64 |
| JnlpInformationIconHeight: | 64 |
| JnlpInformationIconKind: | splash |
| JnlpInformationOffline-allowed: | - |
| JnlpInformationShortcutOnline: | |
| JnlpInformationShortcutDesktop: | - |
| JnlpSecurityAll-permissions: | - |
| JnlpUpdateCheck: | always |
| JnlpUpdatePolicy: | always |
| JnlpResourcesJ2seVersion: | 1.8.0+ |
| JnlpResourcesJ2seInitial-heap-size: | 128m |
| JnlpResourcesJ2seMax-heap-size: | 512m |
| JnlpResourcesJarHref: | ./jar/agentPortalSigned.jar |
| JnlpResourcesNativelibHref: | ./jar/ApplicationBarSigned.dll.jar |
| JnlpResourcesJarDownload: | lazy |
| JnlpApplication-descMain-class: | com.unify.oscc.ap.view.MainApp |
| JnlpApplication-descArgument: | -noswing |
Total processes
133
Monitored processes
11
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1164 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.11.271.2" "later" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -secure -javaws -jre "C:\Program Files\Java\jre1.8.0_271" -vma LWNsYXNzcGF0aABDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxkZXBsb3kuamFyAC1EamF2YS5zZWN1cml0eS5wb2xpY3k9ZmlsZTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxzZWN1cml0eVxqYXZhd3MucG9saWN5AC1EdHJ1c3RQcm94eT10cnVlAC1YdmVyaWZ5OnJlbW90ZQAtRGpubHB4LmhvbWU9QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW4ALURqYXZhLnNlY3VyaXR5Lm1hbmFnZXIALURqbmxweC5vcmlnRmlsZW5hbWVBcmc9QzpcVXNlcnNcYWRtaW5cRGVza3RvcFxzdGFydC5qbmxwAC1Eam5scHgucmVtb3ZlPWZhbHNlAC1Ec3VuLmF3dC53YXJtdXA9dHJ1ZQAtWGJvb3RjbGFzc3BhdGgvYTpDOlxQcm9ncmFtIEZpbGVzXEphdmFcanJlMS44LjBfMjcxXGxpYlxqYXZhd3MuamFyO0M6XFByb2dyYW0gRmlsZXNcSmF2YVxqcmUxLjguMF8yNzFcbGliXGRlcGxveS5qYXI7QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxsaWJccGx1Z2luLmphcgAtWG1zMTI4bQAtWG14NTEybQAtRGpubHB4LmhlYXBzaXplPTEyOG0sNTEybQAtRGpubHB4LnNwbGFzaHBvcnQ9NDk3OTQALURqbmxweC5qdm09QzpcUHJvZ3JhbSBGaWxlc1xKYXZhXGpyZTEuOC4wXzI3MVxiaW5camF2YXcuZXhl -ma QzpcVXNlcnNcYWRtaW5cRGVza3RvcFxzdGFydC5qbmxw | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | javaws.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Version: 11.271.2.09 Modules
| |||||||||||||||
| 3316 | "C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe" "C:\Users\admin\Desktop\start.jnlp" | C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe | — | jp2launcher.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 3908 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.suppression.11.271.2" "false" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 4680 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5708 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6256 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6276 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -cp "C:\PROGRA~1\Java\JRE18~1.0_2\lib\deploy.jar" com.sun.deploy.panel.ControlPanel -userConfig "deployment.expiration.decision.timestamp.11.271.2" "1726482121" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 6352 | "C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe" -securejws C:\Users\admin\Desktop\start.jnlp | C:\Program Files\Java\jre1.8.0_271\bin\jp2launcher.exe | — | explorer.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
| 6568 | JavaWSSplashScreen -splash 49793 "C:\Program Files\Java\jre1.8.0_271\lib\deploy\splash.gif" | C:\Program Files\Java\jre1.8.0_271\bin\javaws.exe | — | javaws.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Web Start Launcher Exit code: 0 Version: 11.271.2.09 Modules
| |||||||||||||||
Total events
6 280
Read events
6 213
Write events
60
Delete events
7
Modification events
| (PID) Process: | (1164) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1675955855080 | |||
| (PID) Process: | (1164) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.roaming.profile |
Value: false | |||
| (PID) Process: | (1164) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.version |
Value: 8 | |||
| (PID) Process: | (1164) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expired.version |
Value: 11.271.2 | |||
| (PID) Process: | (1164) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.browser.path |
Value: C:\Program Files\Internet Explorer\IEXPLORE.EXE | |||
| (PID) Process: | (1164) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1164) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.11.271.2 |
Value: later | |||
| (PID) Process: | (6276) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6276) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.expiration.decision.11.271.2 |
Value: later | |||
| (PID) Process: | (6276) javaw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\JavaSoft\DeploymentProperties |
| Operation: | write | Name: | deployment.modified.timestamp |
Value: 1726482121559 | |||
Executable files
1
Suspicious files
1
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1568 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\baseline.versions | text | |
MD5:74798BE1F4CA6115228214925061CF9E | SHA256:FF22C45E4DE806EC2C8CF165CA956D5AD343DD209F9193DD48BFFC4340C5A5B0 | |||
| 1568 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\blacklist.dynamic | text | |
MD5:B2C6EAE6382150192EA3912393747180 | SHA256:6C73C877B36D4ABD086CB691959B180513AC5ABC0C87FE9070D2D5426D3DBF71 | |||
| 1568 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\update.securitypack.timestamp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1568 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\blacklisted.certs | text | |
MD5:8273F70416F494F7FA5B6C70A101E00E | SHA256:583500B76965EB54B03493372989AB4D3426F85462D1DB232C5AE6706A4D6C58 | |||
| 1568 | jp2launcher.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\83aa4cc77f591dfc2374580bbd95f6ba_bb926e54-e3ca-40fd-ae90-2764341e7792 | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 1164 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:BEE2DA326FF44D93CAF9F070B06363CA | SHA256:F977E15CC07CD0D9920E2CC2DE06D7D58F9ADAD332AC56BB3B3AF7F73026DA68 | |||
| 1164 | javaw.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\deployment.properties | text | |
MD5:BA132B66AE98FD74A4E2508AFC6D3D89 | SHA256:98625760AC751A697F6578D5555E004FE0AB36A4DBE25EAAF268717F90663CDD | |||
| 1568 | jp2launcher.exe | C:\Users\admin\AppData\LocalLow\Sun\Java\Deployment\security\securitypack.jar | java | |
MD5:00E5F72258E6C602E6841BBF4C30B136 | SHA256:905A454FCB15E9F2A469A9A7E6E42B8C6425D20B33A59BE5B84818DAAE964807 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
32
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5816 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1568 | jp2launcher.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | unknown |
1568 | jp2launcher.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | unknown |
1568 | jp2launcher.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | unknown |
5612 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5612 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1568 | jp2launcher.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5816 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5816 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6656 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2256 | svchost.exe | 224.0.0.251:5353 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
javadl-esd-secure.oracle.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1568 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
1568 | jp2launcher.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |