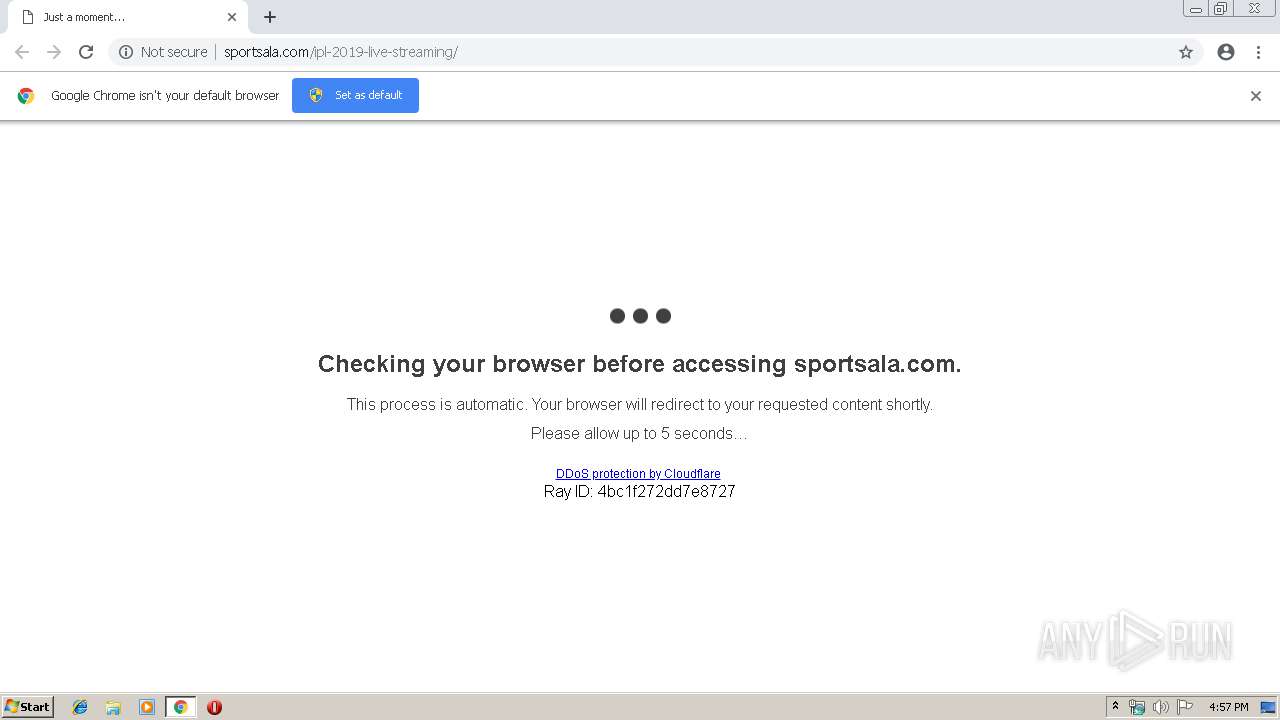
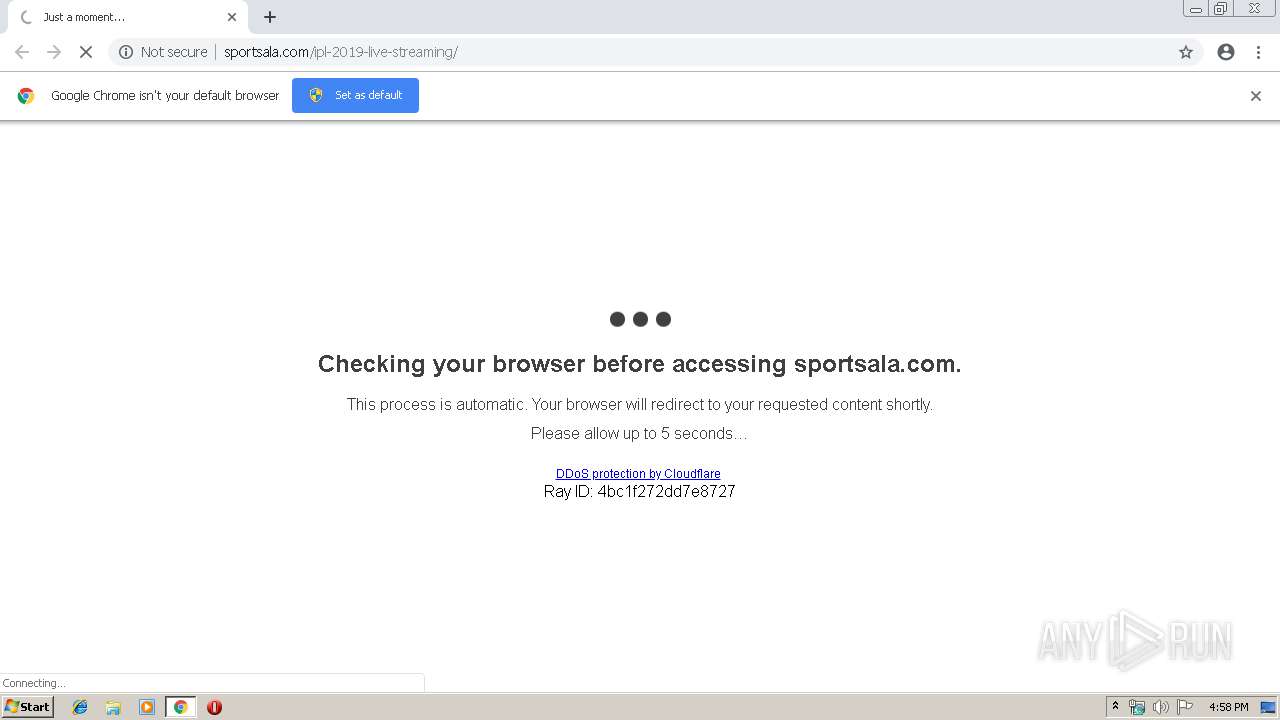
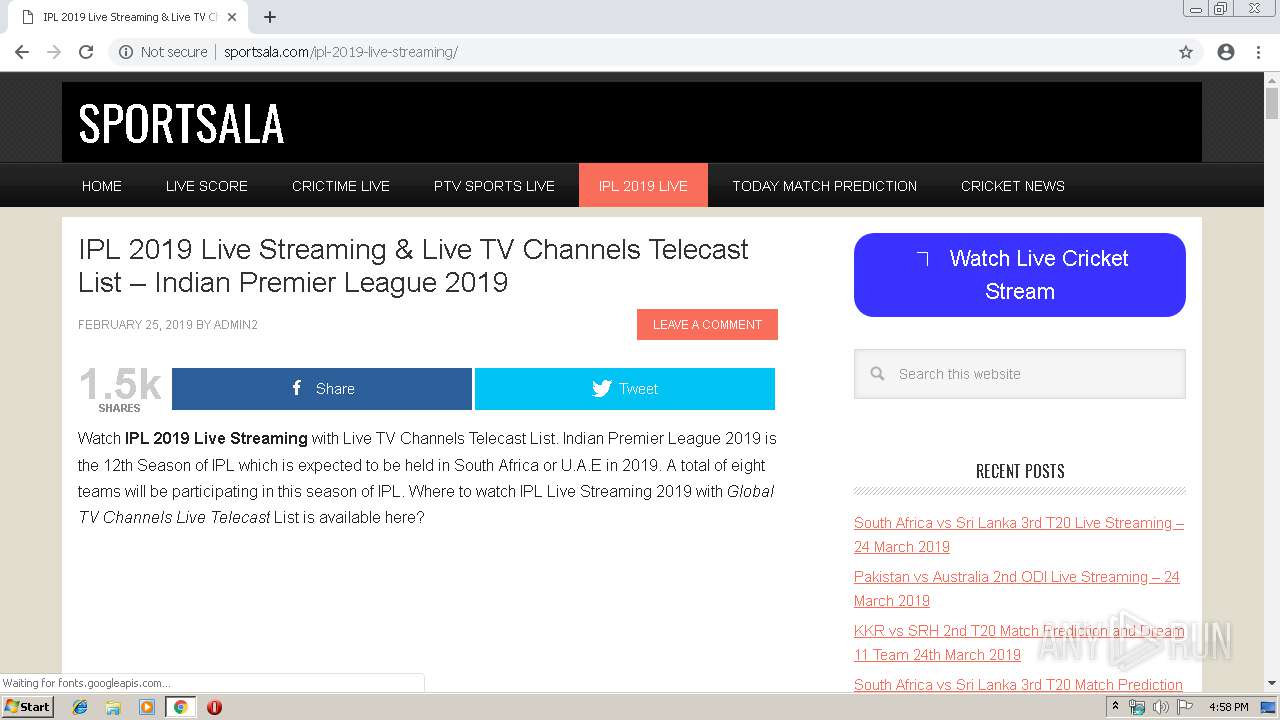
| URL: | http://sportsala.com/ipl-2019-live-streaming/ |
| Full analysis: | https://app.any.run/tasks/603bfe59-608c-49a5-98da-e3451b5fa7c4 |
| Verdict: | No threats detected |
| Analysis date: | March 23, 2019, 16:57:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 23D8914ADE8FDC6F56326E21980E20EC |
| SHA1: | 9517B45772915FF85D138A69330244638B14663D |
| SHA256: | 3160093F995B308C9E0C9C6179D449710CBC47A0E118E1BB68F3B63AAFEC3FFC |
| SSDEEP: | 3:N1KNVNbu0WQhKJ:CNyQh0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 264)
INFO
Application launched itself
- chrome.exe (PID: 264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://sportsala.com/ipl-2019-live-streaming/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3138125441939728111 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3138125441939728111 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3673191694531655871 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3673191694531655871 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f660f18,0x6f660f28,0x6f660f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12773518152701935814 --mojo-platform-channel-handle=3268 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=12012519685214646603 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12012519685214646603 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3652 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=908,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --service-pipe-token=3846888620255093940 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3846888620255093940 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17547277964865557855 --mojo-platform-channel-handle=4192 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1016 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=908,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13612770800869481310 --mojo-platform-channel-handle=3380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
619
Read events
512
Write events
102
Delete events
5
Modification events
| (PID) Process: | (264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1756) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 264-13197833871656875 |
Value: 259 | |||
| (PID) Process: | (264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (264) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
Executable files
0
Suspicious files
157
Text files
155
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFf8c29.TMP | — | |
MD5:— | SHA256:— | |||
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8fe7cf77-d824-4df9-bb32-50f751bf0c32.tmp | — | |
MD5:— | SHA256:— | |||
| 264 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
163
DNS requests
110
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3524 | chrome.exe | GET | 503 | 104.28.4.171:80 | http://sportsala.com/ipl-2019-live-streaming/ | US | html | 5.09 Kb | suspicious |
3524 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
3524 | chrome.exe | GET | 302 | 104.28.5.171:80 | http://sportsala.com/cdn-cgi/l/chk_jschl?s=05f91b0365b99032fa5b3b225ec73980e1655623-1553360274-1800-AQArpxlUFMh7U833PhrI%2FNMG%2BilKD7so801RigP1bo7IGYbBhNZ8OYc9OqGorERDFDq6%2BFpQOiiB%2F5Zbw%2BeNROmkg%2Fr%2B2827LFhbCponngwL9AS7DtAD12xne7D5EqOr3KjC1G7NZKemaNQssryTwgk%3D&jschl_vc=03e153afca188d1741b1b79f13abe41f&pass=1553360278.376-PsgzW29XGm&jschl_answer=25.4446088615 | US | html | 159 b | suspicious |
3524 | chrome.exe | GET | 200 | 104.28.4.171:80 | http://sportsala.com/ipl-2019-live-streaming/ | US | html | 22.3 Kb | suspicious |
3524 | chrome.exe | GET | 200 | 104.28.5.171:80 | http://sportsala.com/favicon.ico | US | html | 159 b | suspicious |
3524 | chrome.exe | GET | 200 | 172.217.22.66:80 | http://pagead2.googlesyndication.com/pagead/js/adsbygoogle.js | US | text | 31.0 Kb | whitelisted |
3524 | chrome.exe | GET | 200 | 151.101.2.2:80 | http://cdn.taboola.com/libtrc/sportsala/loader.js | US | text | 17.9 Kb | whitelisted |
3524 | chrome.exe | GET | 204 | 2.16.186.80:80 | http://b.scorecardresearch.com/b2?c1=7&c2=13739933&c3=20121515121&ns__t=1553360297280&ns_c=UTF-8&cv=3.1&c8=IPL%202019%20Live%20Streaming%20%26%20Live%20TV%20Channels%20Telecast%20List%20-%20Indian%20Premier%20League%202019&c7=http%3A%2F%2Fsportsala.com%2Fipl-2019-live-streaming%2F&c9=http%3A%2F%2Fsportsala.com%2Fipl-2019-live-streaming%2F | unknown | compressed | 901 b | whitelisted |
3524 | chrome.exe | GET | 200 | 205.185.216.42:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3524 | chrome.exe | GET | 200 | 172.217.22.66:80 | http://pagead2.googlesyndication.com/pagead/js/r20190320/r20190131/show_ads_impl.js | US | text | 74.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3524 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3524 | chrome.exe | 104.28.4.171:80 | sportsala.com | Cloudflare Inc | US | shared |
3524 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3524 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3524 | chrome.exe | 172.217.18.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
3524 | chrome.exe | 172.217.21.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3524 | chrome.exe | 104.28.5.171:80 | sportsala.com | Cloudflare Inc | US | shared |
3524 | chrome.exe | 173.194.150.219:80 | r5---sn-5goeen7r.gvt1.com | Google Inc. | US | whitelisted |
3524 | chrome.exe | 104.28.4.171:443 | sportsala.com | Cloudflare Inc | US | shared |
3524 | chrome.exe | 172.217.22.42:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sportsala.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.cloudflare.com |
| whitelisted |
davidcdaniel.us |
| suspicious |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-5goeen7r.gvt1.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1072 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
3524 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
3524 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |