| File name: | 01669485_2 |
| Full analysis: | https://app.any.run/tasks/fdfdad52-7182-4356-b719-1edaf26f9227 |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2019, 03:35:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 388D3D38CDFA133E271527C9009D7196 |
| SHA1: | 4E27AE15474DE649D7EA2C93C71A47351E576AD2 |
| SHA256: | 315DF86C8D9524694162A712902C28C1608150E2E8704C61B0DEEA049C57FE67 |
| SSDEEP: | 49152:mE+if2ezQCgbDUWL1Z5//hv/2/rFM6R3OFgUeO6GfB3qsR:5+ieezQCWBZb3ER+FOHGZ |
MALICIOUS
Changes the autorun value in the registry
- 01669485_2.exe (PID: 1560)
Loads dropped or rewritten executable
- svcrsc.exe (PID: 2104)
- unrscVista.exe (PID: 3008)
- rscmgr.exe (PID: 2812)
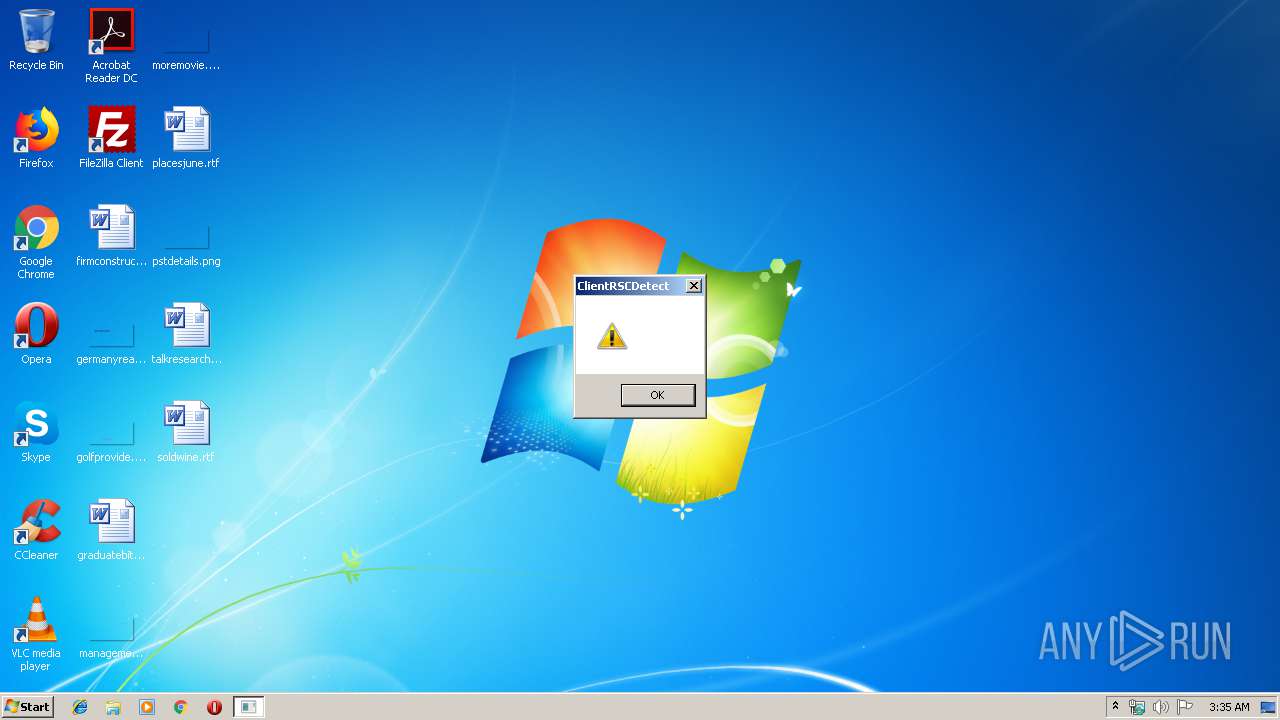
- ClientRSCDetect.exe (PID: 2144)
Application was dropped or rewritten from another process
- rscmgr.exe (PID: 2812)
- svcrsc.exe (PID: 2104)
- ClientRSCDetect.exe (PID: 2144)
- rscdetect.exe (PID: 720)
- unrscVista.exe (PID: 3008)
- RSClientSetupD.exe (PID: 3756)
- Unstsvcrsc.exe (PID: 388)
SUSPICIOUS
Executable content was dropped or overwritten
- 01669485_2.exe (PID: 1560)
- RSClientSetupD.exe (PID: 3756)
- rscmgr.exe (PID: 2812)
- svcrsc.exe (PID: 2104)
Creates files in the Windows directory
- RSClientSetupD.exe (PID: 3756)
- svcrsc.exe (PID: 2104)
- rscmgr.exe (PID: 2812)
- ClientRSCDetect.exe (PID: 2144)
Creates or modifies windows services
- unrscVista.exe (PID: 3008)
- ClientRSCDetect.exe (PID: 2144)
- rscmgr.exe (PID: 2812)
Creates files in the driver directory
- RSClientSetupD.exe (PID: 3756)
Uses ICACLS.EXE to modify access control list
- svcrsc.exe (PID: 2104)
- rscmgr.exe (PID: 2812)
Executed as Windows Service
- svcrsc.exe (PID: 2104)
- Unstsvcrsc.exe (PID: 388)
Removes files from Windows directory
- ClientRSCDetect.exe (PID: 2144)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2068:06:21 08:07:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.15 |
| CodeSize: | 25600 |
| InitializedDataSize: | 2542080 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6a00 |
| OSVersion: | 10 |
| ImageVersion: | 10 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.18362.1 |
| ProductVersionNumber: | 11.0.18362.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.18362.1 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | WEXTRACT.EXE |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.18362.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-May-1932 23:38:46 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Win32 Cabinet Self-Extractor |
| FileVersion: | 11.00.18362.291 (WinBuild.160101.0800) |
| InternalName: | Wextract |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | WEXTRACT.EXE .MUI |
| ProductName: | Internet Explorer |
| ProductVersion: | 11.00.18362.291 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-May-1932 23:38:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000062C4 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.30395 |
.data | 0x00008000 | 0x00001A48 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97064 |
.idata | 0x0000A000 | 0x00001052 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0209 |
.rsrc | 0x0000C000 | 0x0026B000 | 0x0026AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99175 |
.reloc | 0x00277000 | 0x00000888 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.27286 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01344 | 2018 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.15864 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.07737 | 488 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.50949 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.56662 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.94251 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.99361 | 1736 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 3.37828 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 7.98515 | 55762 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.33023 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
Cabinet.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
msvcrt.dll |
Total processes
62
Monitored processes
17
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Unstsvcrsc.exe del | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Unstsvcrsc.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 444 | "C:\Windows\System32\icacls.exe" "C:\Windows\system32\ClientRSCDetect.exe" /grant Administrators:F | C:\Windows\System32\icacls.exe | — | rscmgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 720 | "C:\Windows\system32\rscdetect.exe" | C:\Windows\system32\rscdetect.exe | rscmgr.exe | ||||||||||||
User: admin Company: nTracksystem Co., Ltd. Integrity Level: MEDIUM Description: RSC Media Detect Exit code: 0 Version: 5, 0, 2, 3 Modules
| |||||||||||||||
| 928 | "C:\Windows\System32\icacls.exe" "C:\Windows\system32\rscPtCtrl.exe" /grant SYSTEM:F | C:\Windows\System32\icacls.exe | — | svcrsc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1316 | "C:\Windows\System32\icacls.exe" "C:\Windows\system32\rscmgr.exe" /grant SYSTEM:F | C:\Windows\System32\icacls.exe | — | svcrsc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1560 | "C:\Users\admin\AppData\Local\Temp\01669485_2.exe" | C:\Users\admin\AppData\Local\Temp\01669485_2.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 11.00.18362.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1992 | "C:\Windows\System32\icacls.exe" "C:\Windows\system32\ClientRSCDetect.exe" /grant SYSTEM:F | C:\Windows\System32\icacls.exe | — | rscmgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | C:\Windows\system32\svcrsc.exe | C:\Windows\system32\svcrsc.exe | services.exe | ||||||||||||
User: SYSTEM Company: nTracksystem Co., Ltd. Integrity Level: SYSTEM Description: svcrsc Exit code: 0 Version: 5, 0, 2, 8 Modules
| |||||||||||||||
| 2144 | "C:\Windows\system32\ClientRSCDetect.exe" moonsy | C:\Windows\system32\ClientRSCDetect.exe | rscmgr.exe | ||||||||||||
User: SYSTEM Company: nTracksystem Co., Ltd. Integrity Level: SYSTEM Description: ClientRSCDetect Exit code: 0 Version: 5, 3, 2, 1 Modules
| |||||||||||||||
| 2160 | "C:\Users\admin\AppData\Local\Temp\01669485_2.exe" | C:\Users\admin\AppData\Local\Temp\01669485_2.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Win32 Cabinet Self-Extractor Exit code: 3221226540 Version: 11.00.18362.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
497
Read events
125
Write events
371
Delete events
1
Modification events
| (PID) Process: | (1560) 01669485_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (3008) unrscVista.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\BTHPORT |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (1560) 01669485_2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (2104) svcrsc.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2104) svcrsc.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2812) rscmgr.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2812) rscmgr.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2812) rscmgr.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Minimal\svcrsc |
| Operation: | write | Name: | |
Value: Service | |||
| (PID) Process: | (2812) rscmgr.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\SafeBoot\Network\svcrsc |
| Operation: | write | Name: | |
Value: Service | |||
| (PID) Process: | (2144) ClientRSCDetect.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ntrack |
| Operation: | write | Name: | ConnectInfo |
Value: 1158952660cfff9e85fa460b96d4e00e5155952c5b124f15e9c80acf9e47fc3d5ef18491e143eaa20b1a5e8cebb0fab2 | |||
Executable files
53
Suspicious files
1
Text files
46
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ntrbufd.sys | executable | |
MD5:— | SHA256:— | |||
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ClientRSCDetect.exe | executable | |
MD5:— | SHA256:— | |||
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\NtrMptpfd.sys | executable | |
MD5:— | SHA256:— | |||
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ntrrscfd.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\ClientRSCDetect_USres.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\NtrMptpfd.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ntrrscfd64.sys | executable | |
MD5:— | SHA256:— | |||
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\Ntrrscfd.sys | executable | |
MD5:— | SHA256:— | |||
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\NtrSafefd.dll | executable | |
MD5:— | SHA256:— | |||
| 1560 | 01669485_2.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\NtrMptpfd64.sys | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
RSClientSetupD.exe | [NTRRSC] (RSClientSetup_D) RSC ¼³Ä¡ ÀÛ¾÷ ½ÃÀÛ.
|
RSClientSetupD.exe | [NTRRSC] (RSClientSetup) setup path : C:\Users\admin\AppData\Local\Temp\IXP000.TMP
|
RSClientSetupD.exe | [NTRRSC] Windows 7 32bit ¿î¿µÃ¼Á¦ÀÔ´Ï´Ù.
|
RSClientSetupD.exe | [NTRRSC] Fltmgr driver Service Open
|
RSClientSetupD.exe | [NTRRSC] Fltmgr is found
|
RSClientSetupD.exe | [NTRRSC] (RSClientSetup) Main process [Start]
|
RSClientSetupD.exe | [NTRRSC] (_SetUninstServiceStart) StartService success.
|
unrscVista.exe | [NTR_UnRSCVista] (UninstRSC service) service start.
|
unrscVista.exe | [NTR_UnRSCVista] (UninstRSC service) OS version check. [610][32]
|
unrscVista.exe | [NTR_UnRSCVista] (UninstRSC service) UninstallRSClient process not find.
|