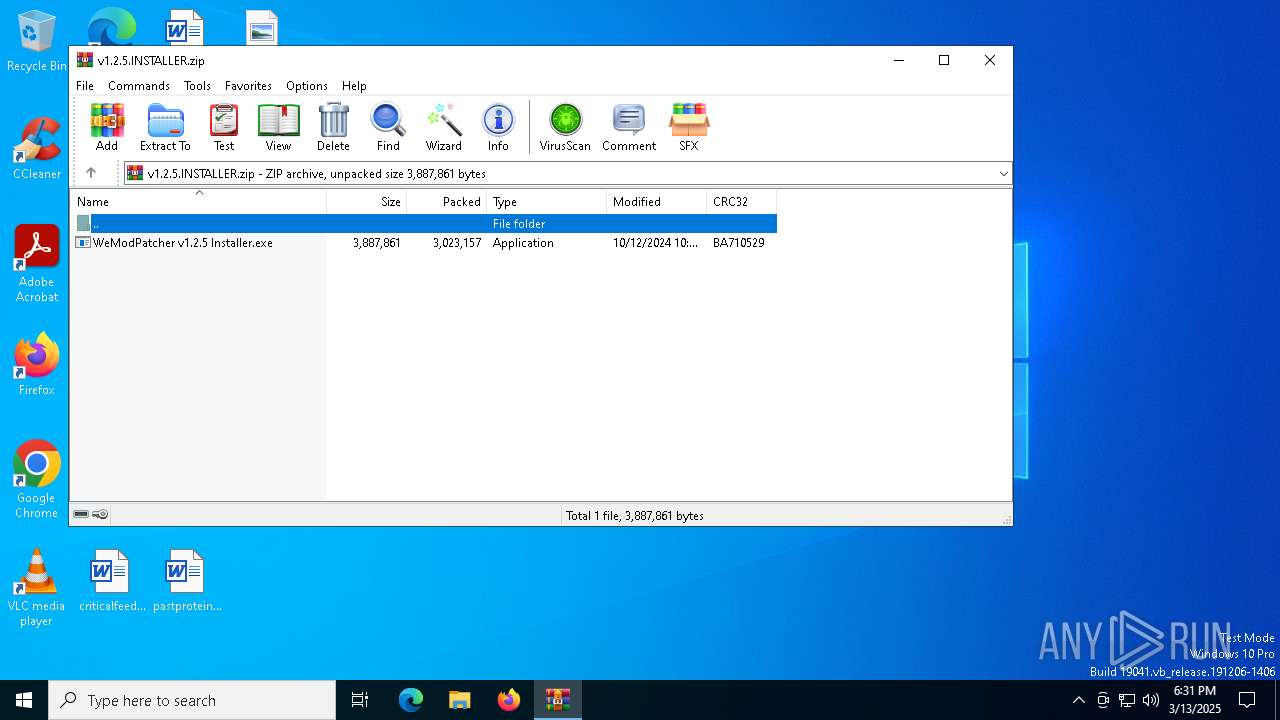
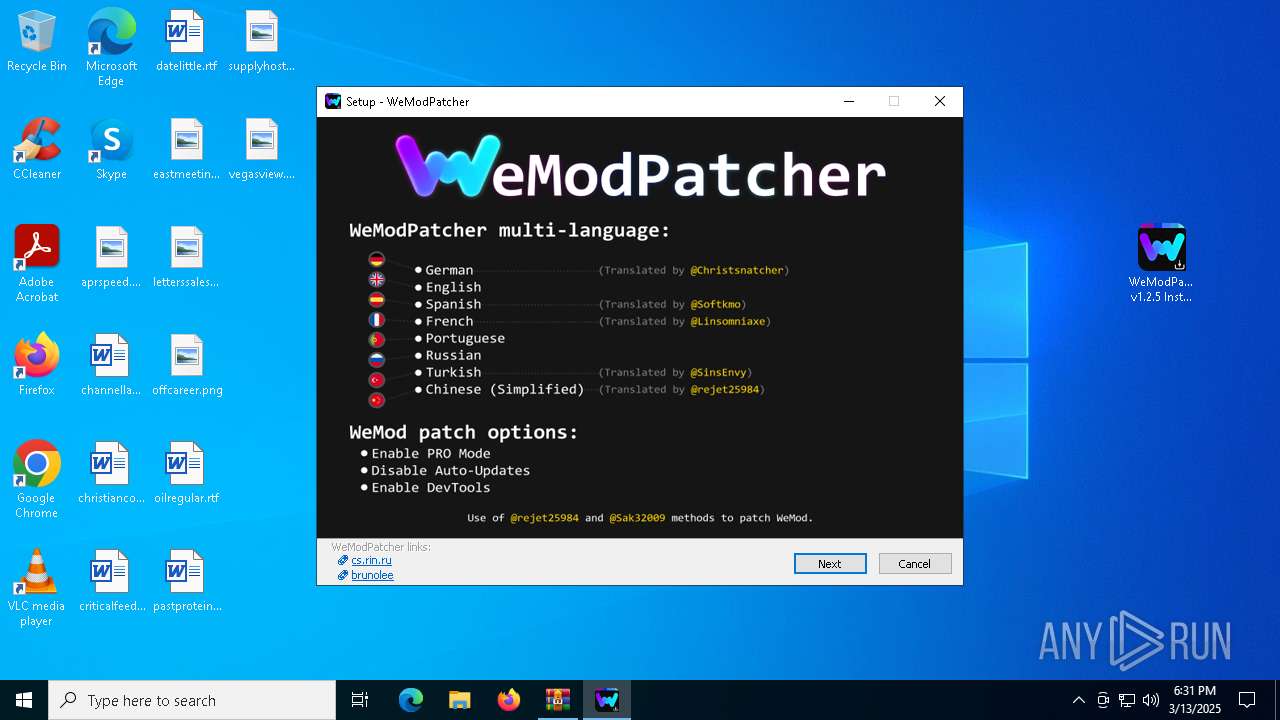
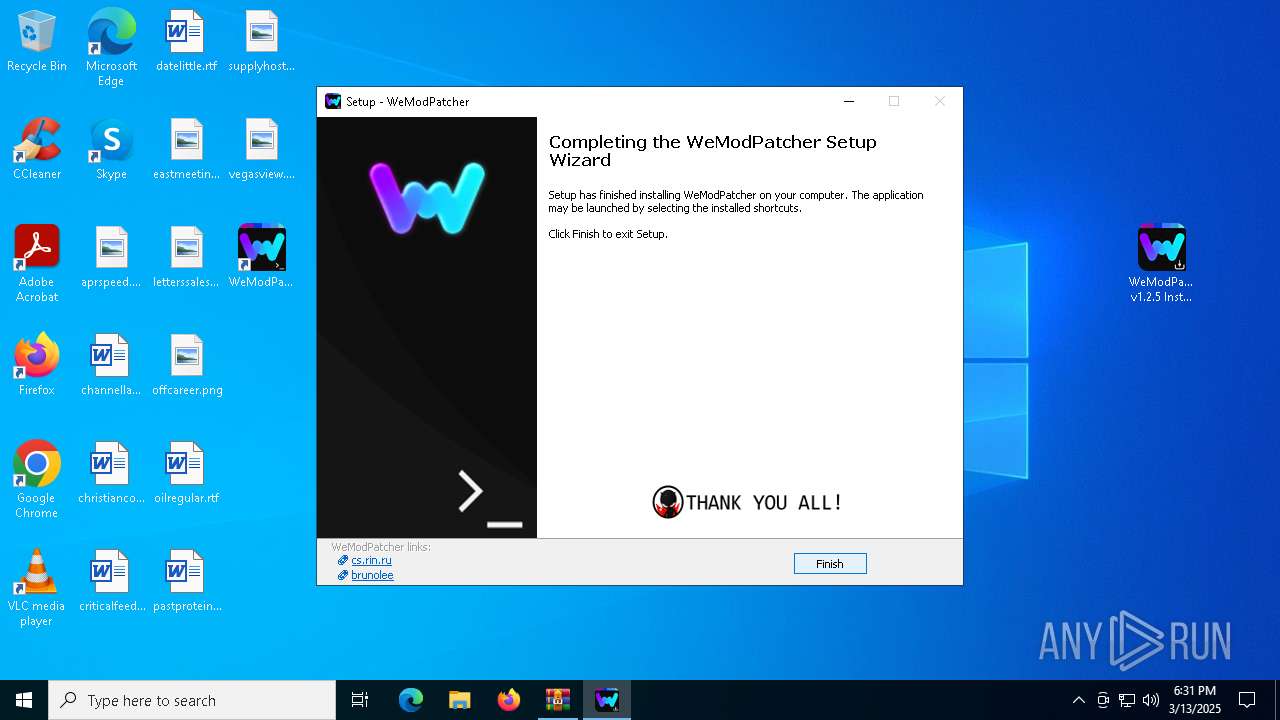
| download: | /brunolee-GIT/W3M0dP4tch32/releases/download/v1.2.5/v1.2.5.INSTALLER.zip |
| Full analysis: | https://app.any.run/tasks/c18c40f2-fdde-4dfd-86d9-8281b79f8ef1 |
| Verdict: | Malicious activity |
| Analysis date: | March 13, 2025, 18:31:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 54F08D8813F9222CE1844456F8B2F2CA |
| SHA1: | 682DF8ABD664E0DAA167E7538C5D834261233425 |
| SHA256: | 314A74A443DFAD1CFC6EF472656C45377D56BB0BCBB62E12D5DE219BDE4949F0 |
| SSDEEP: | 98304:pFJaN/xTinJkY0SOQRYETkyywjuLftNu9pHVRR7SEbDax89dePzi6AwScZBnRoSy:Y0u+R |
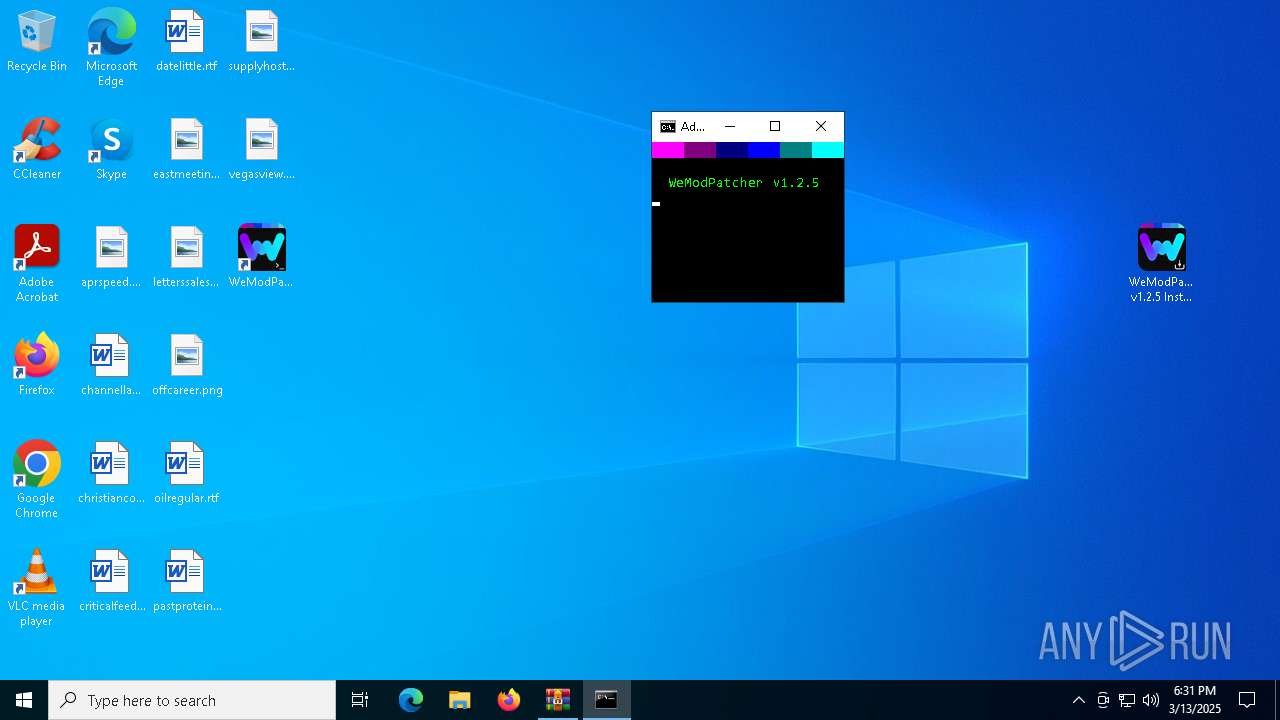
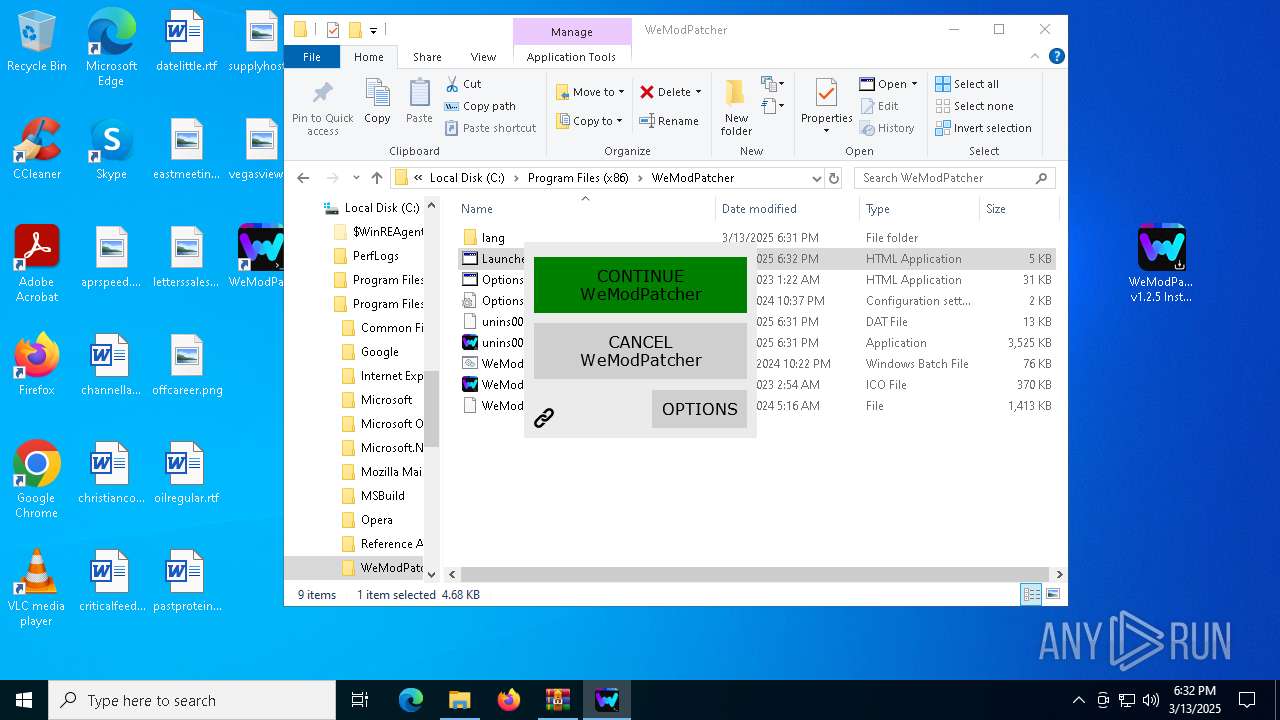
MALICIOUS
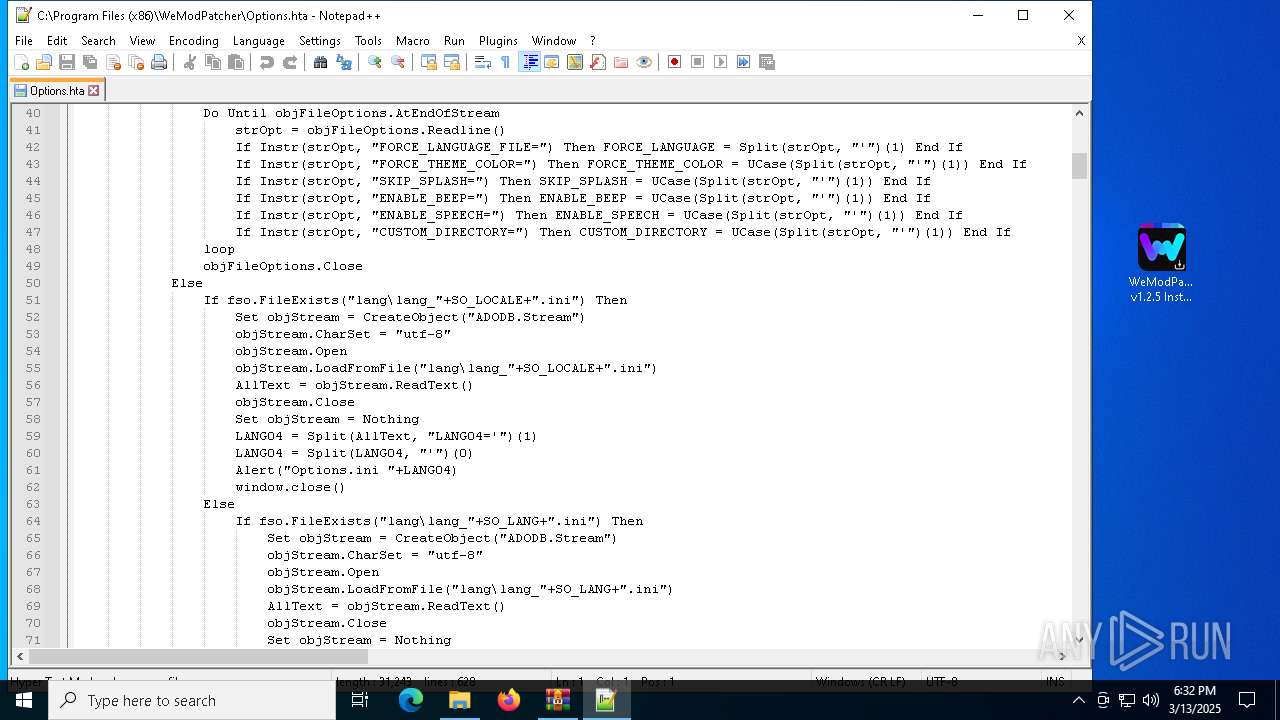
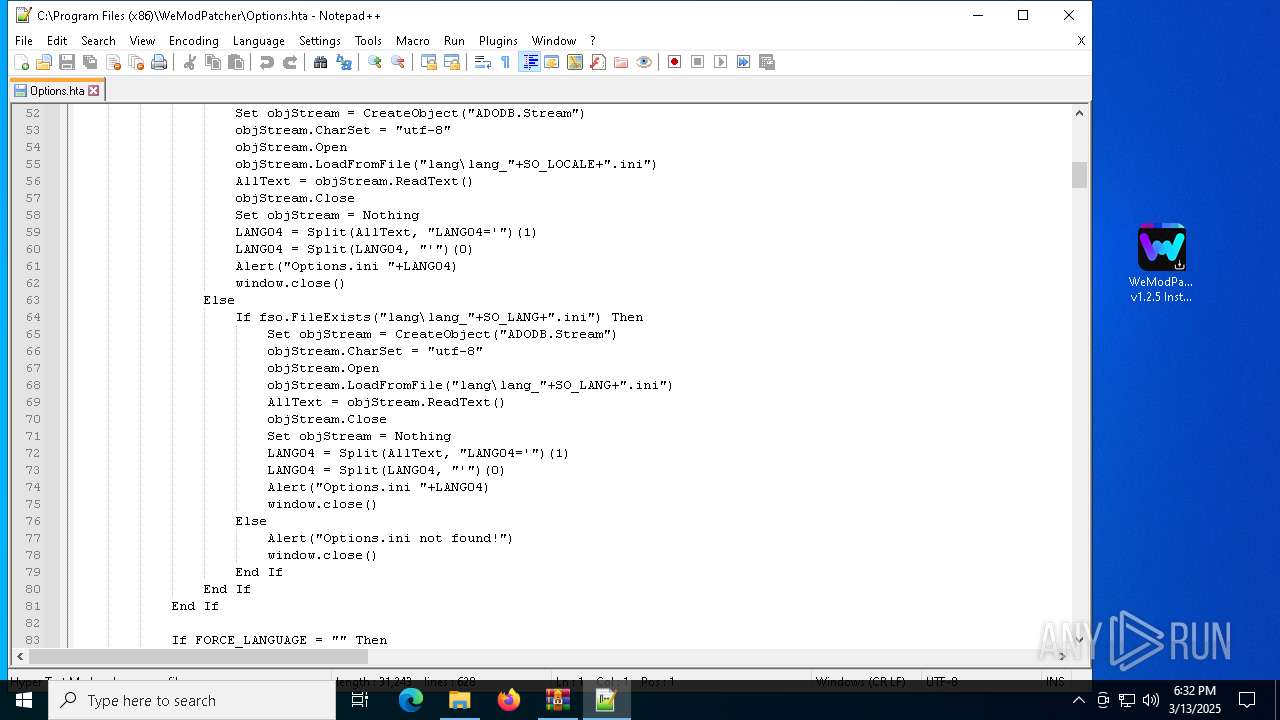
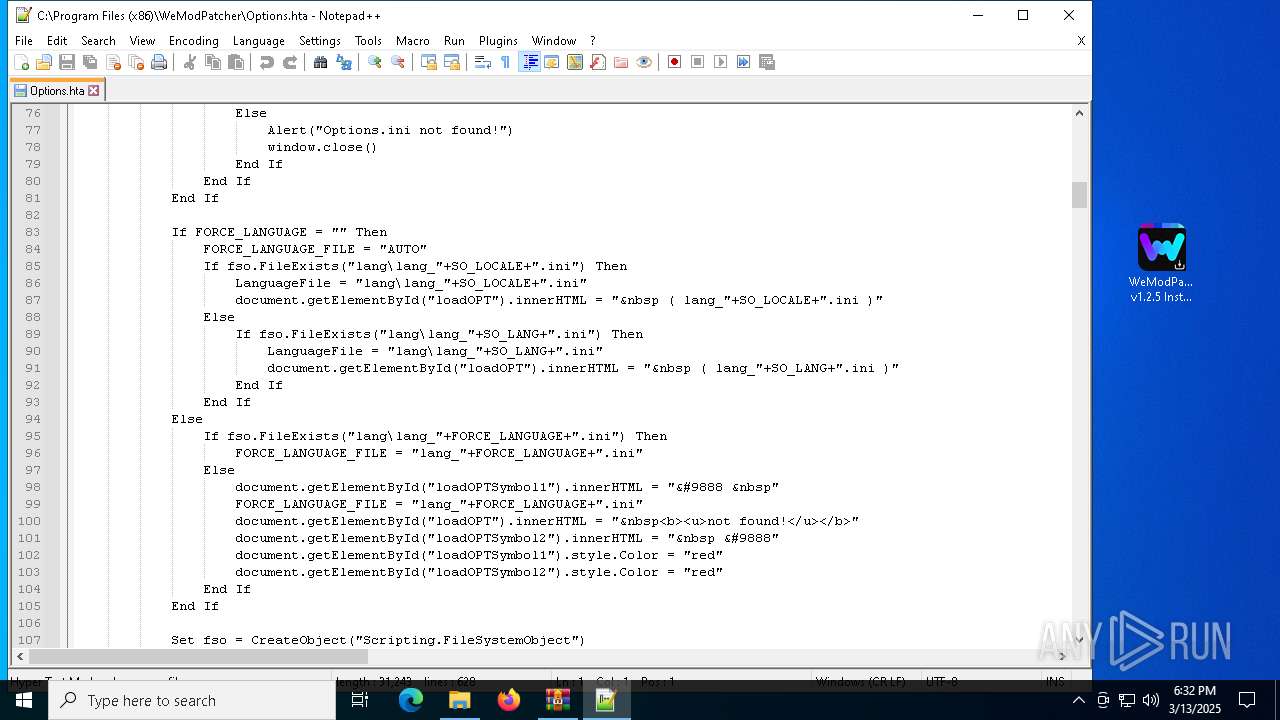
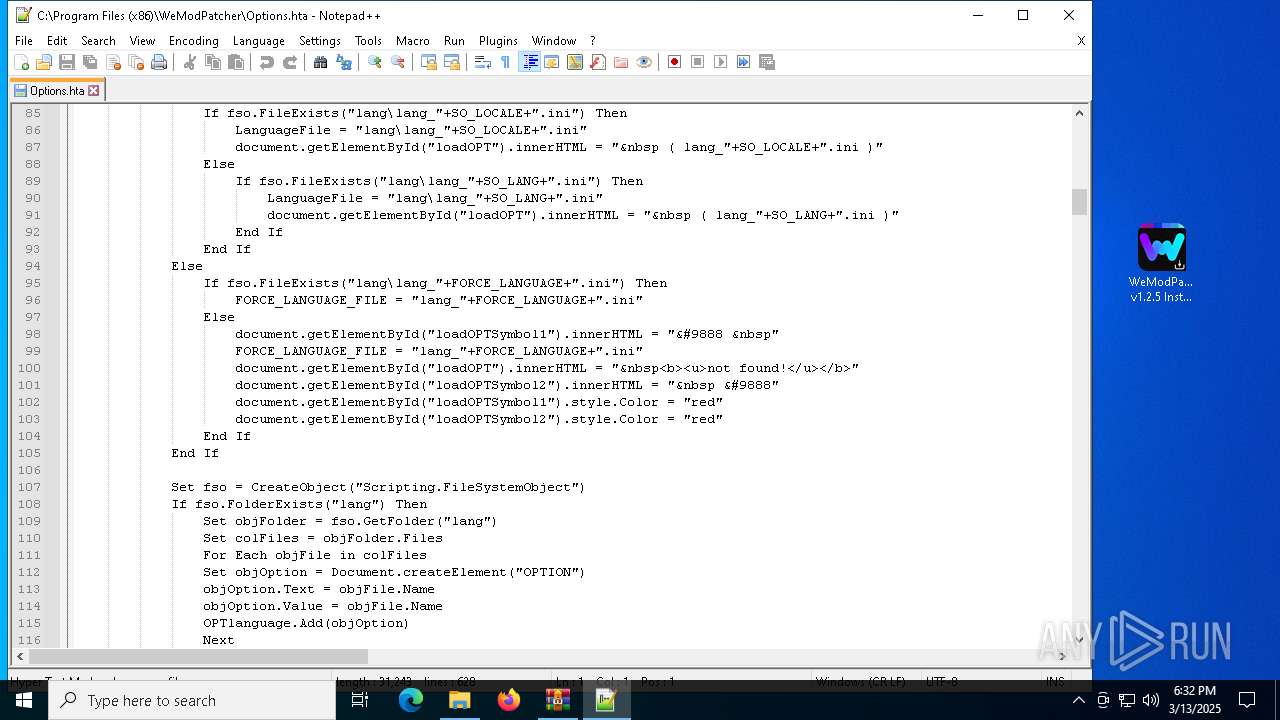
Opens a text file (SCRIPT)
- mshta.exe (PID: 5232)
- mshta.exe (PID: 7592)
Checks whether a specified folder exists (SCRIPT)
- mshta.exe (PID: 5232)
- mshta.exe (PID: 7592)
SUSPICIOUS
Reads security settings of Internet Explorer
- WeModPatcher v1.2.5 Installer.tmp (PID: 7448)
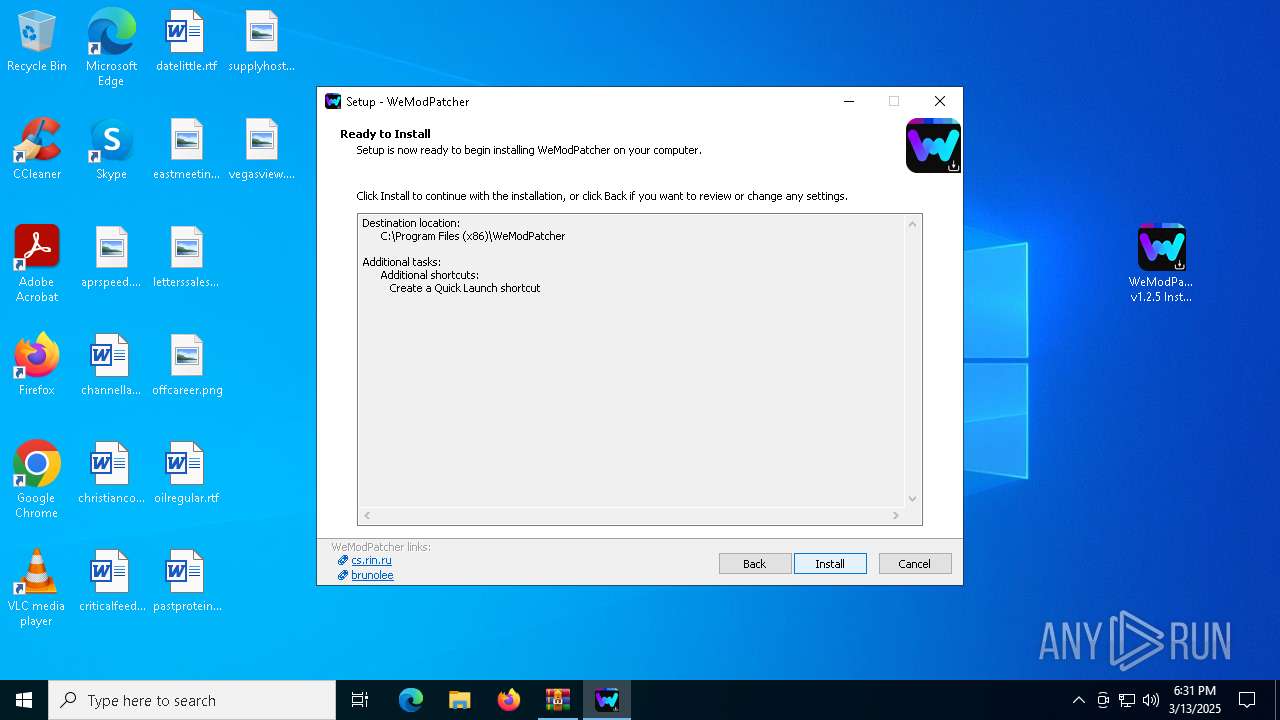
Executable content was dropped or overwritten
- WeModPatcher v1.2.5 Installer.exe (PID: 7428)
- WeModPatcher v1.2.5 Installer.exe (PID: 7584)
- WeModPatcher v1.2.5 Installer.tmp (PID: 7672)
Reads the Windows owner or organization settings
- WeModPatcher v1.2.5 Installer.tmp (PID: 7672)
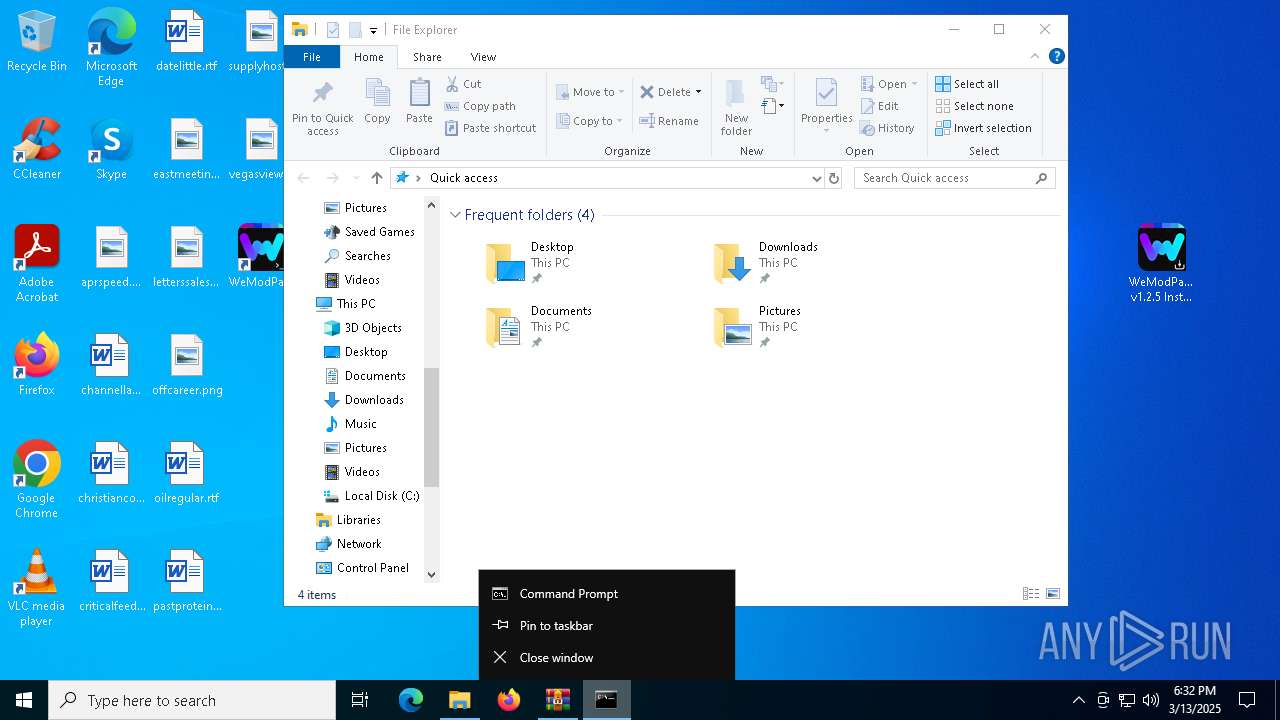
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7992)
- powershell.exe (PID: 5008)
- cmd.exe (PID: 1532)
Execution of CURL command
- cmd.exe (PID: 7992)
- cmd.exe (PID: 1532)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 7992)
- net.exe (PID: 7200)
- net.exe (PID: 7864)
- cmd.exe (PID: 1532)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6988)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 7280)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 3896)
- cmd.exe (PID: 7448)
- cmd.exe (PID: 6652)
- cmd.exe (PID: 7148)
- cmd.exe (PID: 7656)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 6132)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 8036)
- cmd.exe (PID: 728)
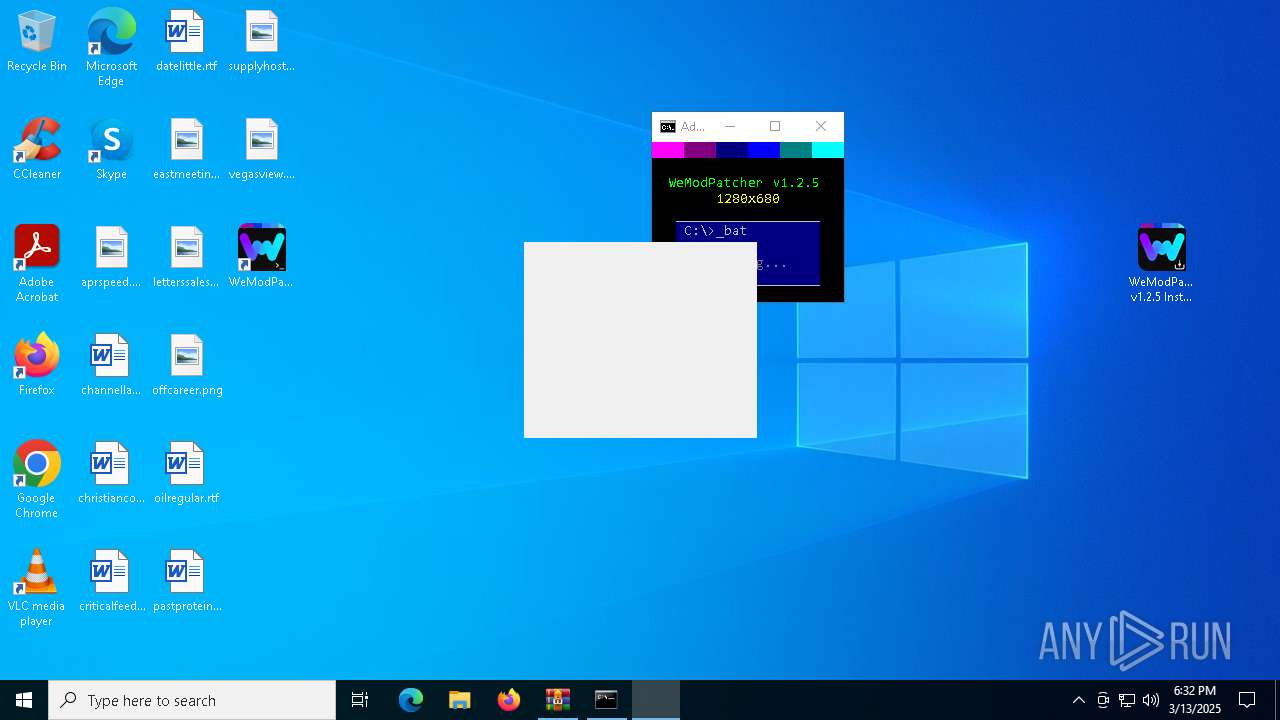
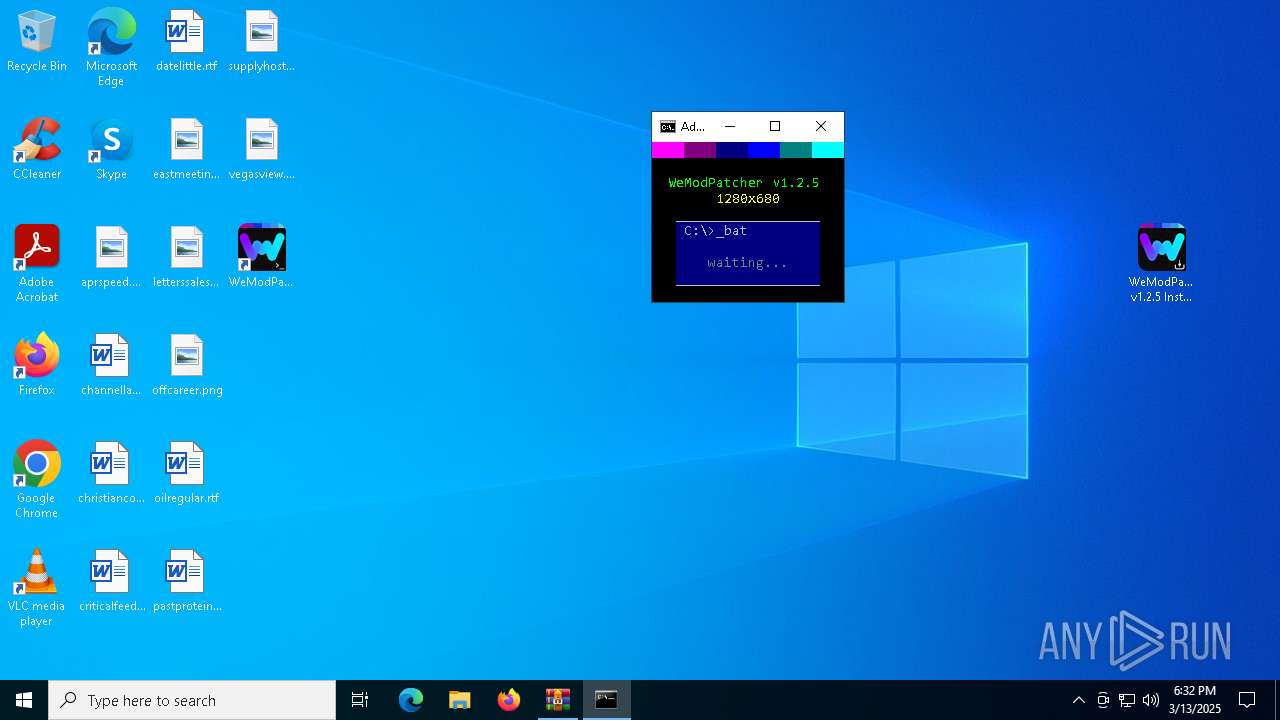
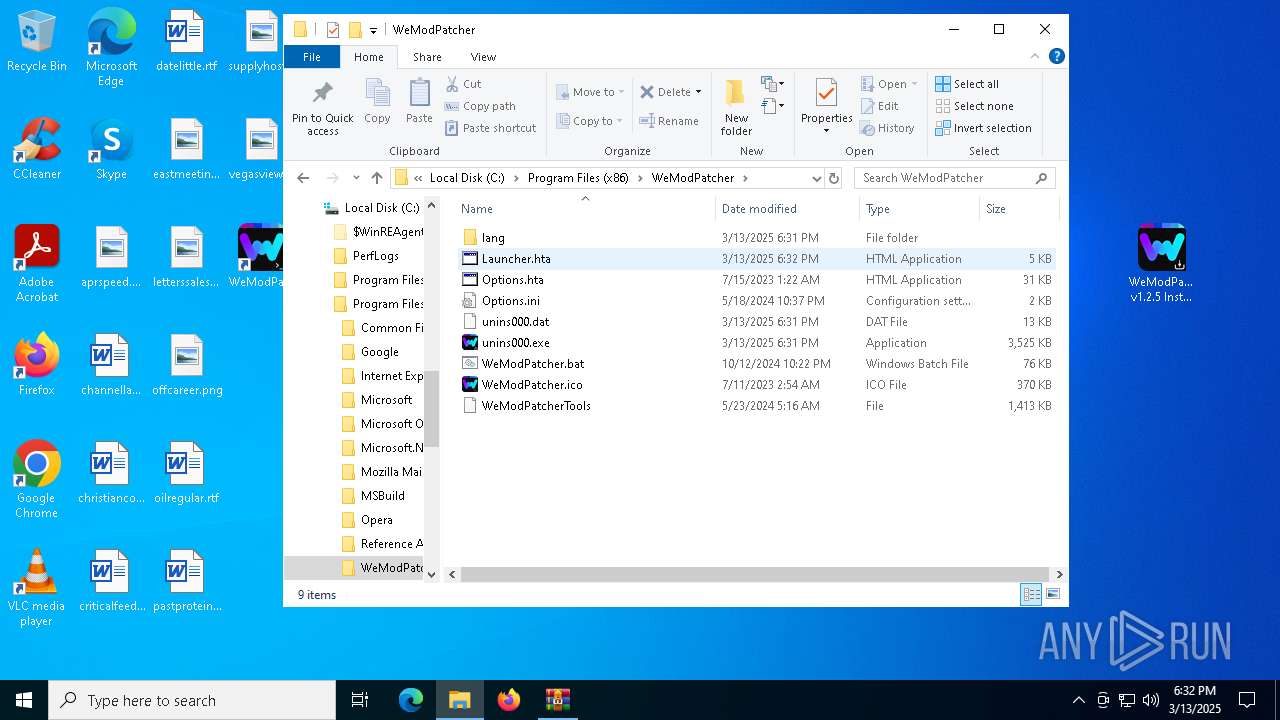
Executing commands from a ".bat" file
- powershell.exe (PID: 5008)
Drops 7-zip archiver for unpacking
- WeModPatcher v1.2.5 Installer.tmp (PID: 7672)
Application launched itself
- cmd.exe (PID: 7992)
- cmd.exe (PID: 1532)
- mshta.exe (PID: 2240)
Get information on the list of running processes
- cmd.exe (PID: 3896)
- cmd.exe (PID: 1532)
- cmd.exe (PID: 4164)
- cmd.exe (PID: 8036)
Starts application with an unusual extension
- cmd.exe (PID: 1532)
- cmd.exe (PID: 7476)
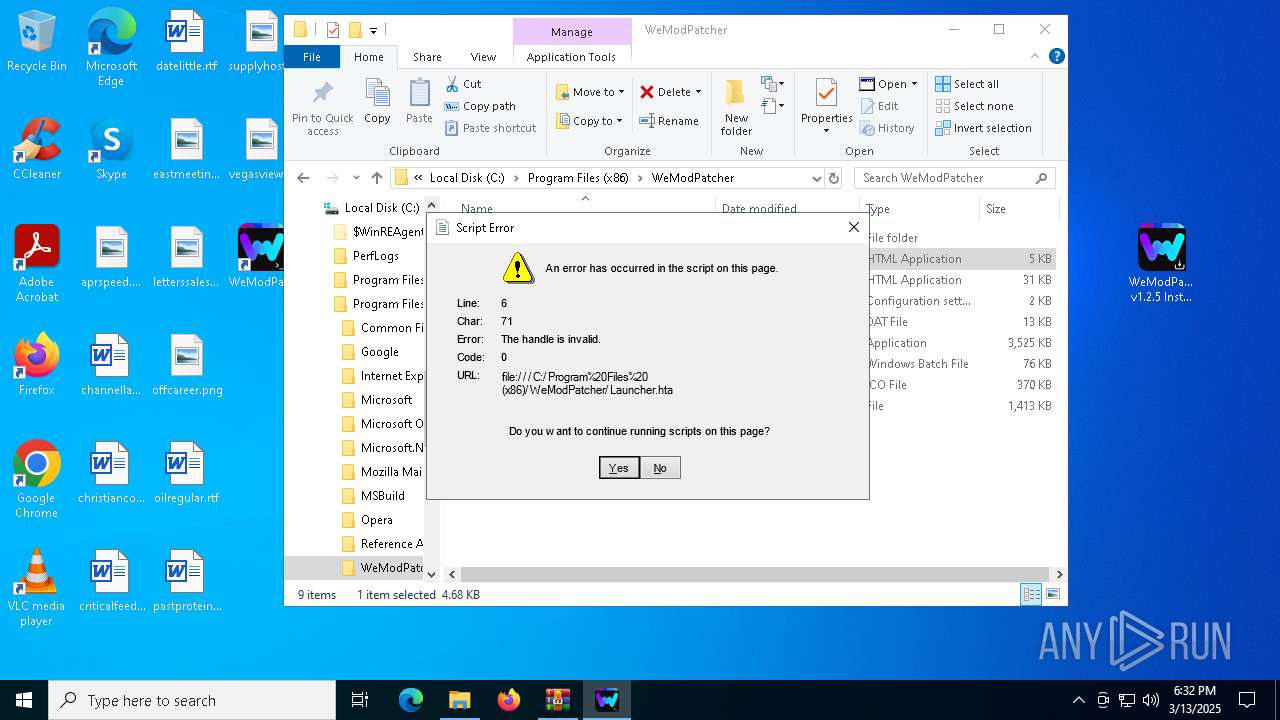
Executes application which crashes
- mshta.exe (PID: 7800)
- mshta.exe (PID: 680)
- mshta.exe (PID: 5408)
- mshta.exe (PID: 5232)
- mshta.exe (PID: 7592)
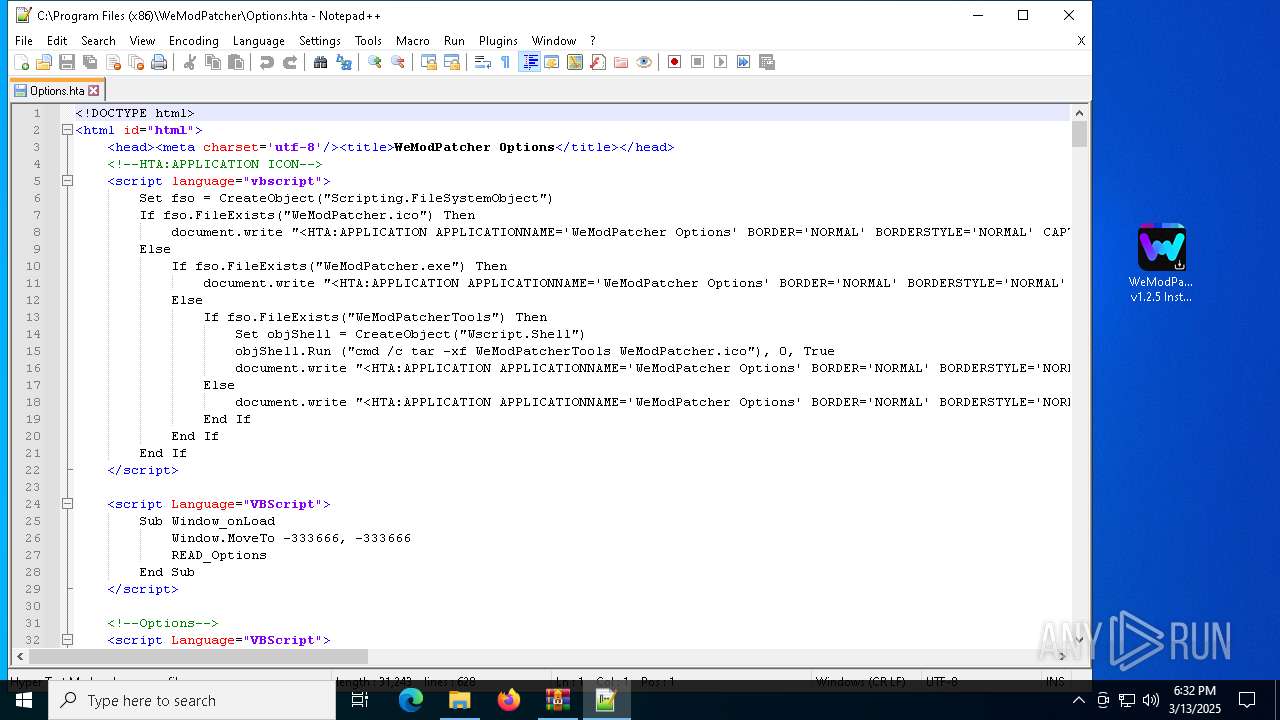
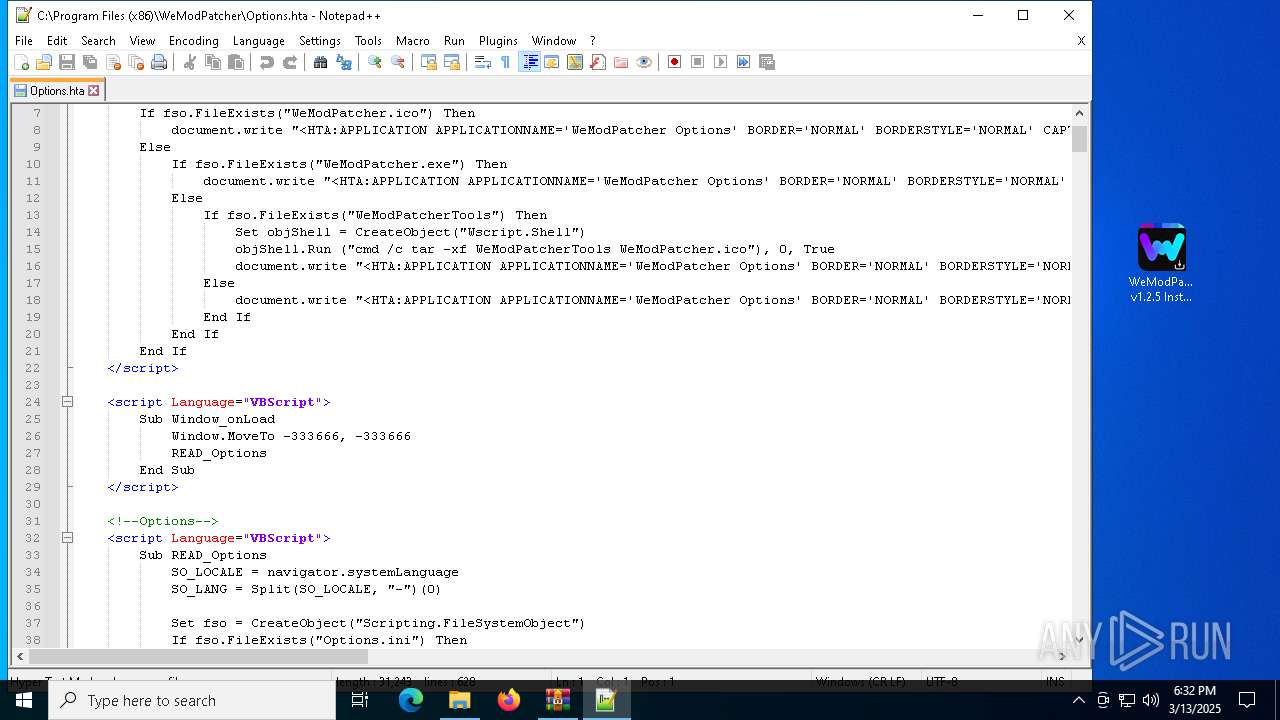
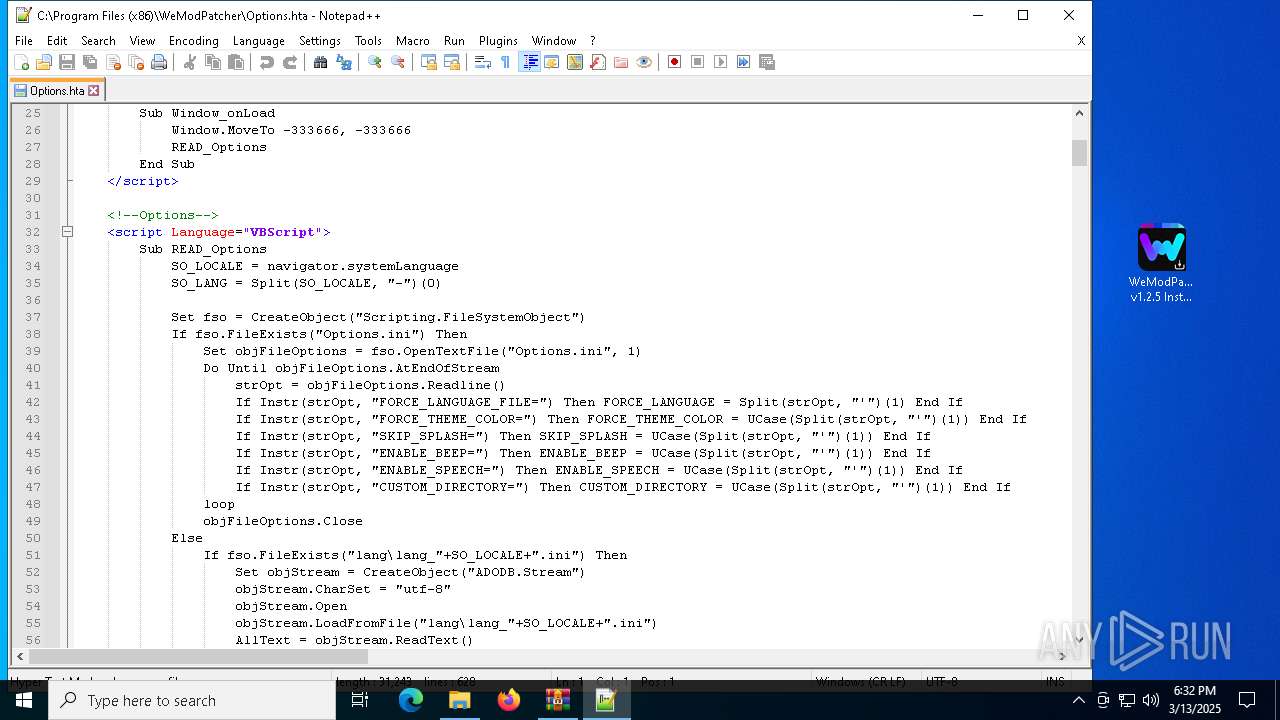
Creates FileSystem object to access computer's file system (SCRIPT)
- mshta.exe (PID: 7800)
- mshta.exe (PID: 2240)
- mshta.exe (PID: 680)
- mshta.exe (PID: 5408)
- mshta.exe (PID: 5232)
- mshta.exe (PID: 7592)
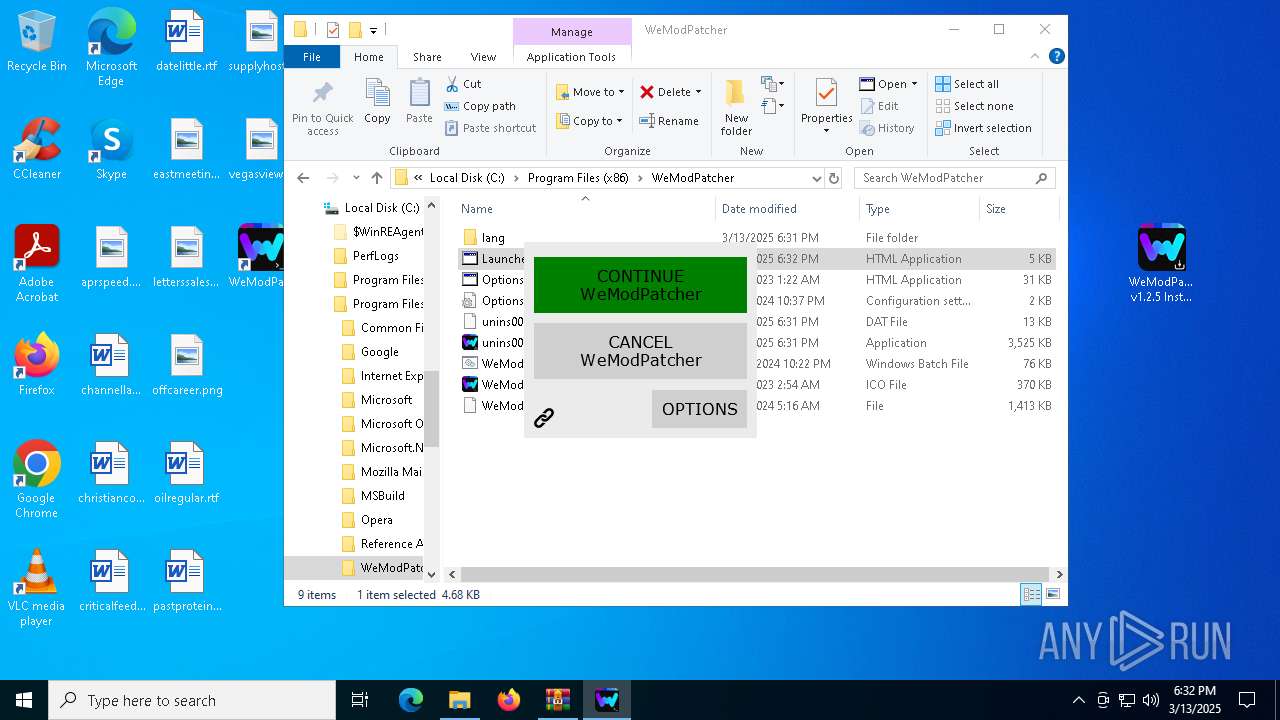
Writes binary data to a Stream object (SCRIPT)
- mshta.exe (PID: 2240)
Checks whether a specific file exists (SCRIPT)
- mshta.exe (PID: 2240)
- mshta.exe (PID: 7592)
- mshta.exe (PID: 5232)
Reads data from a binary Stream object (SCRIPT)
- mshta.exe (PID: 5232)
- mshta.exe (PID: 7592)
Runs shell command (SCRIPT)
- mshta.exe (PID: 2240)
INFO
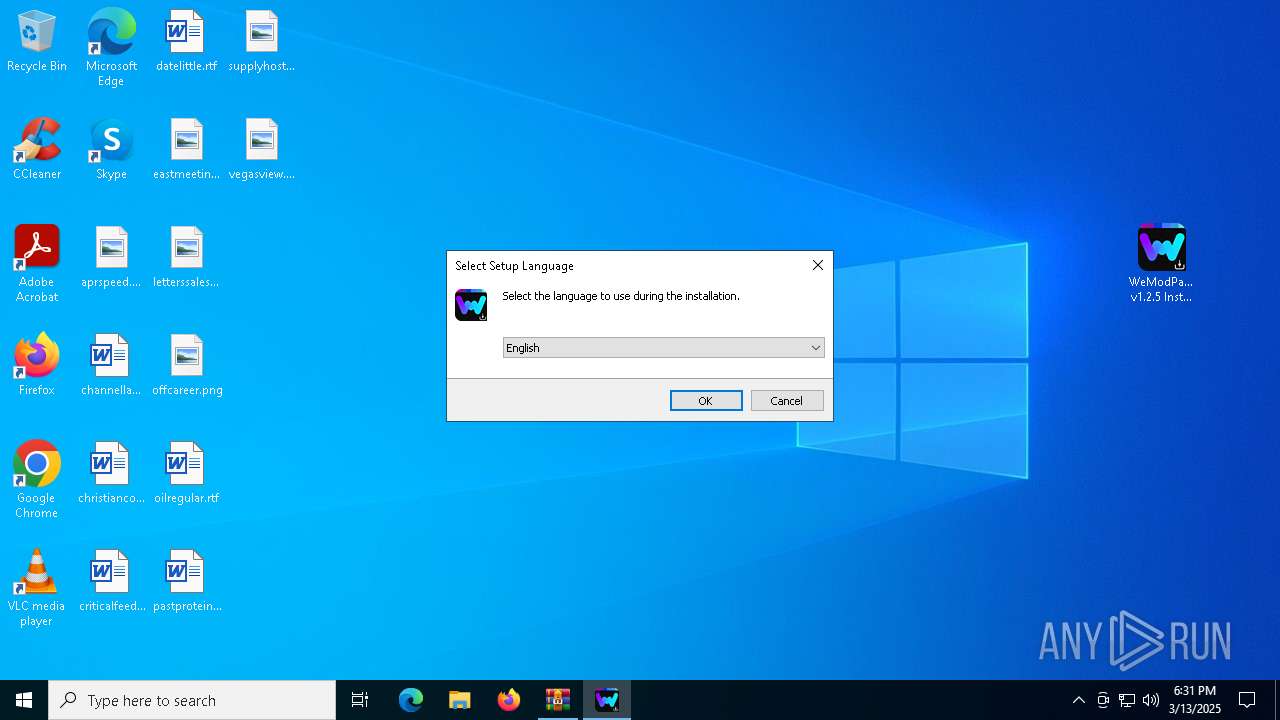
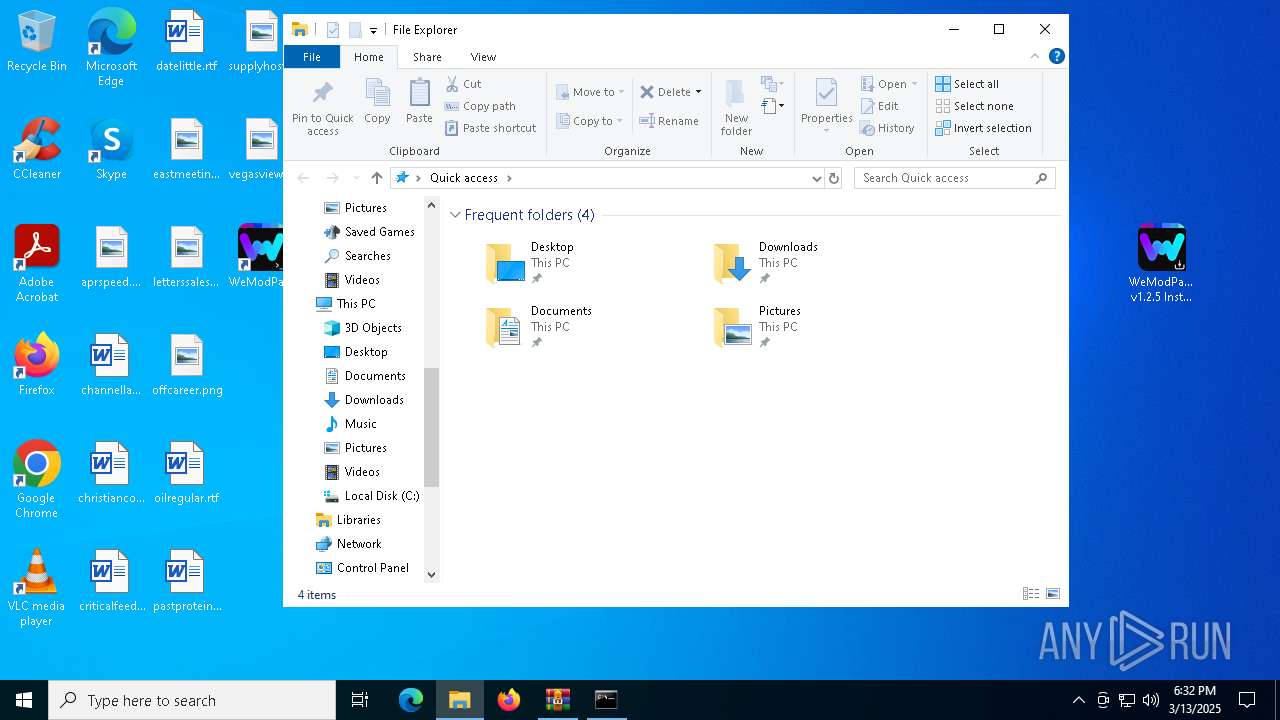
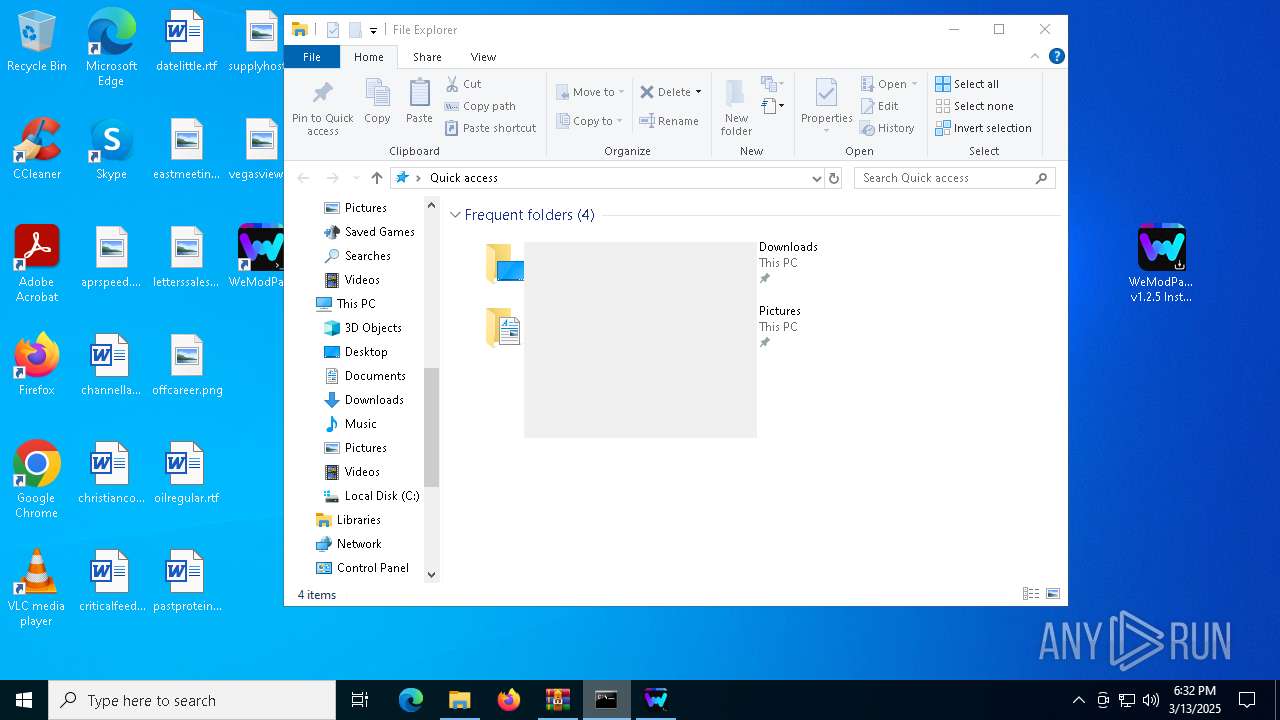
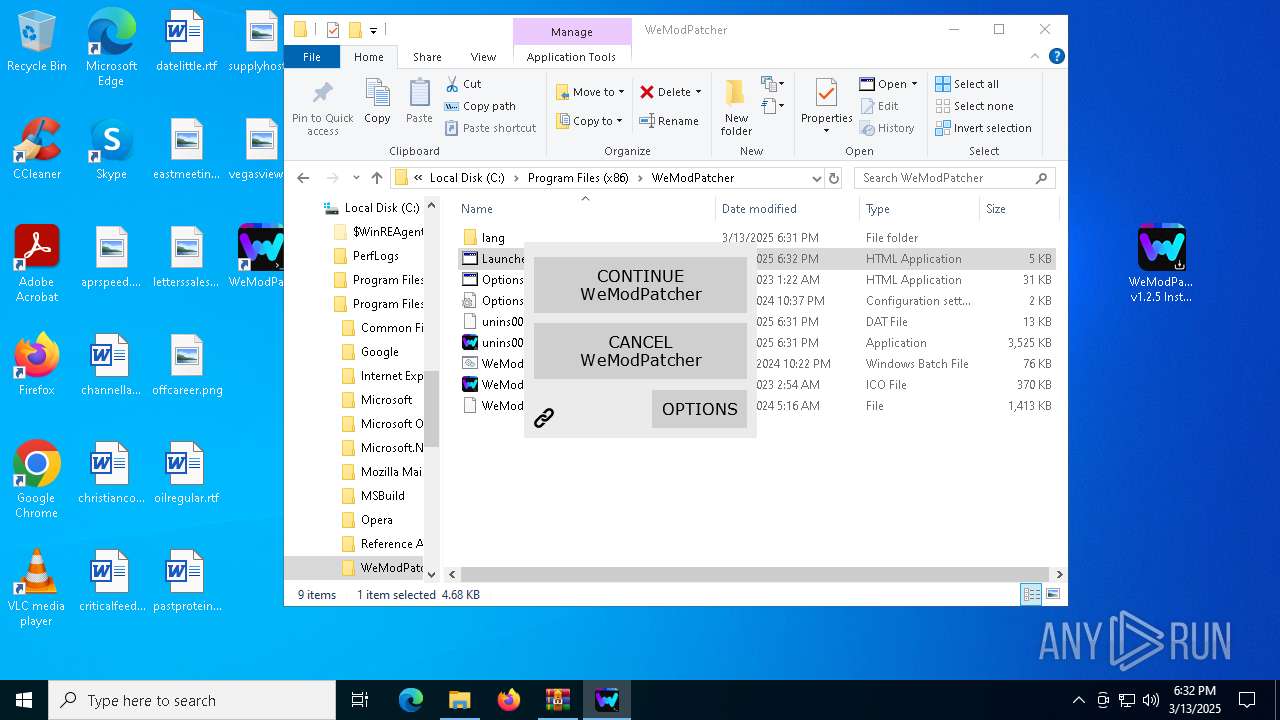
Manual execution by a user
- WeModPatcher v1.2.5 Installer.exe (PID: 7428)
- cmd.exe (PID: 7992)
- mshta.exe (PID: 2240)
- notepad++.exe (PID: 660)
- mshta.exe (PID: 7592)
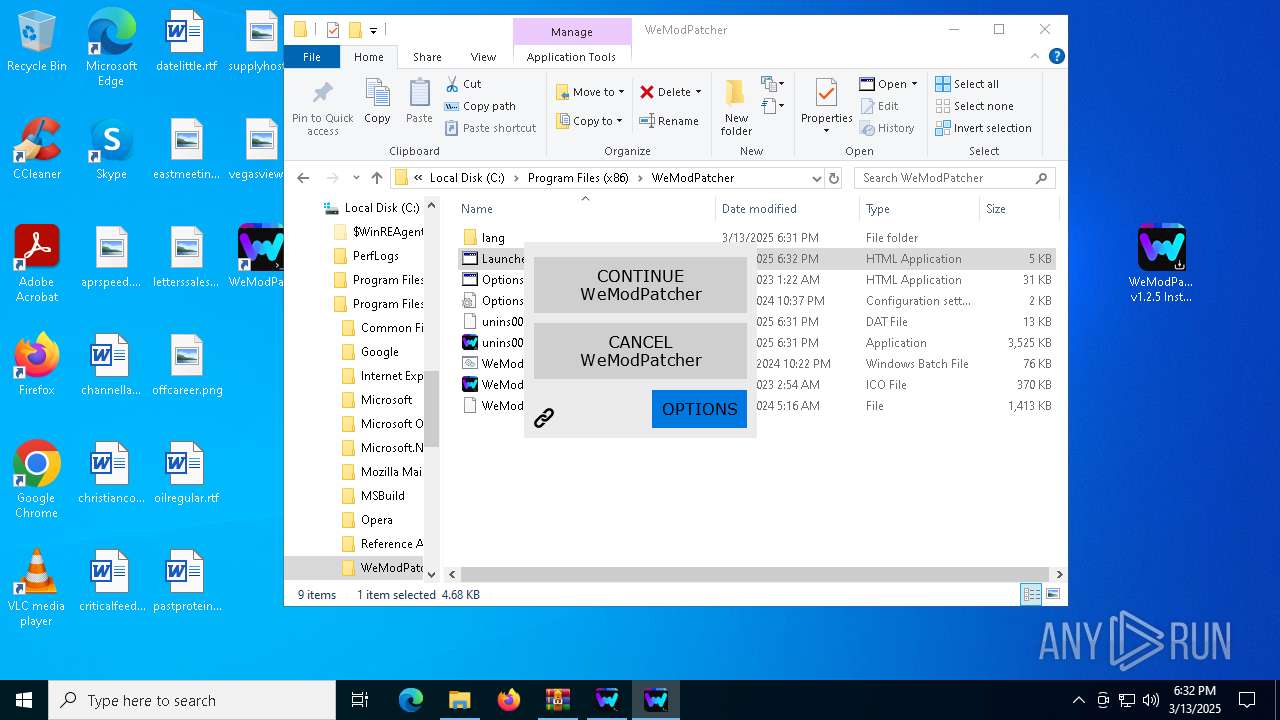
Reads the computer name
- WeModPatcher v1.2.5 Installer.tmp (PID: 7448)
- WeModPatcher v1.2.5 Installer.tmp (PID: 7672)
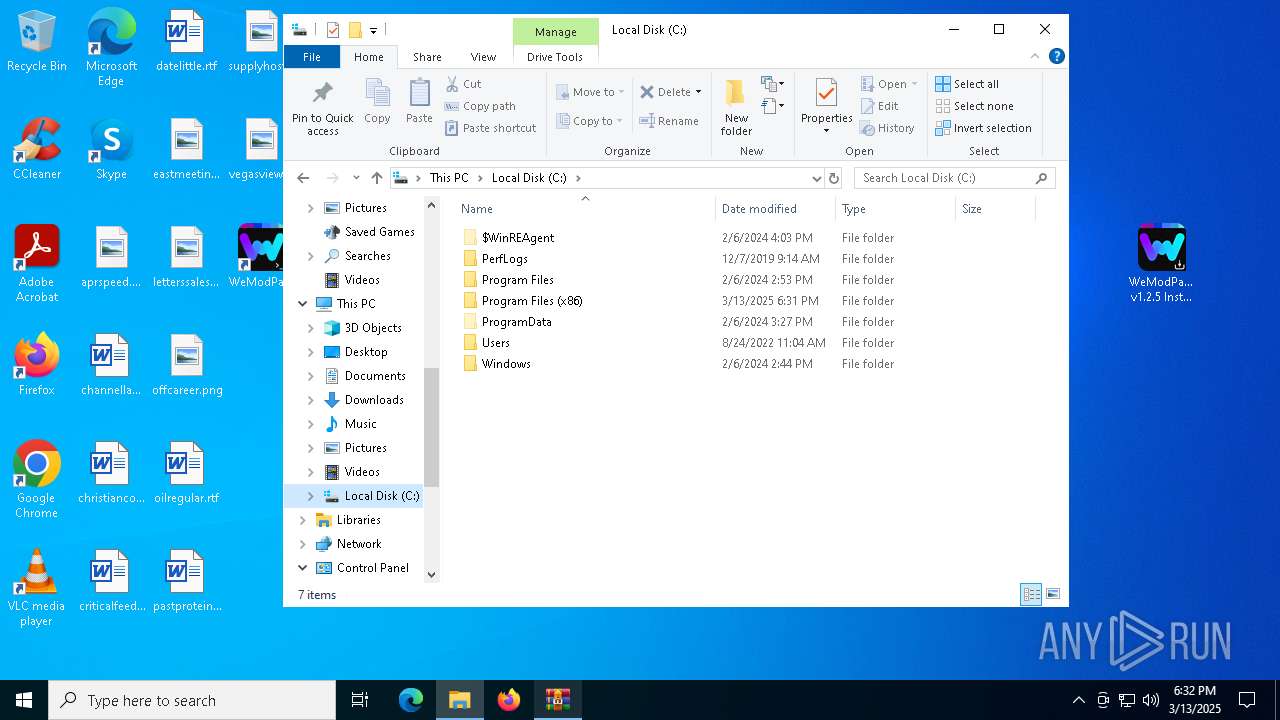
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1852)
Create files in a temporary directory
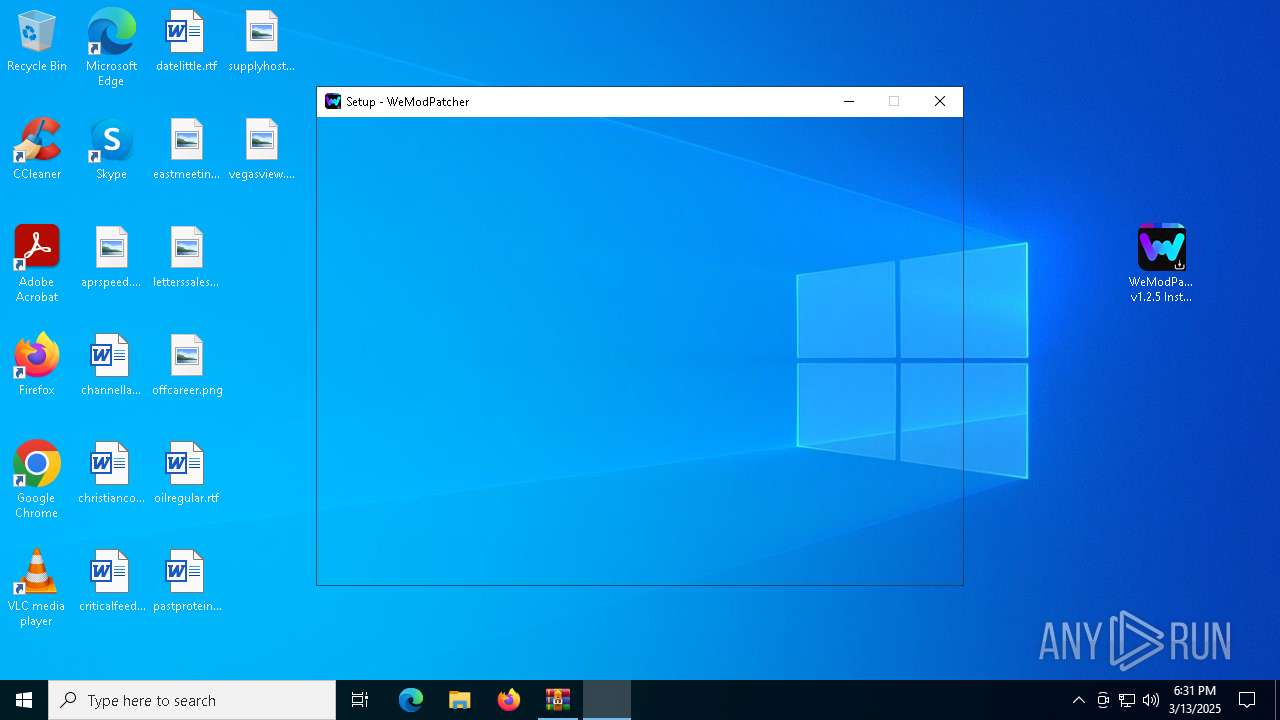
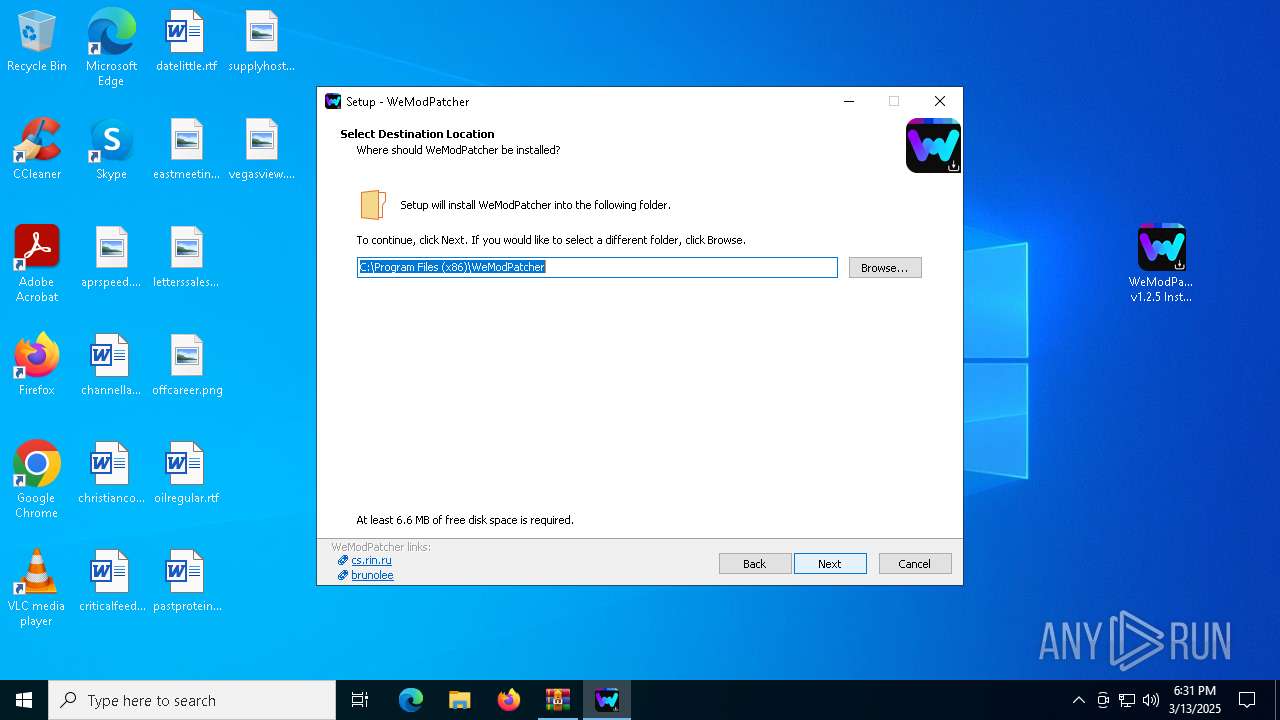
- WeModPatcher v1.2.5 Installer.exe (PID: 7428)
- WeModPatcher v1.2.5 Installer.tmp (PID: 7672)
Checks supported languages
- WeModPatcher v1.2.5 Installer.tmp (PID: 7448)
- WeModPatcher v1.2.5 Installer.exe (PID: 7428)
- WeModPatcher v1.2.5 Installer.exe (PID: 7584)
- WeModPatcher v1.2.5 Installer.tmp (PID: 7672)
Process checks computer location settings
- WeModPatcher v1.2.5 Installer.tmp (PID: 7448)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 5116)
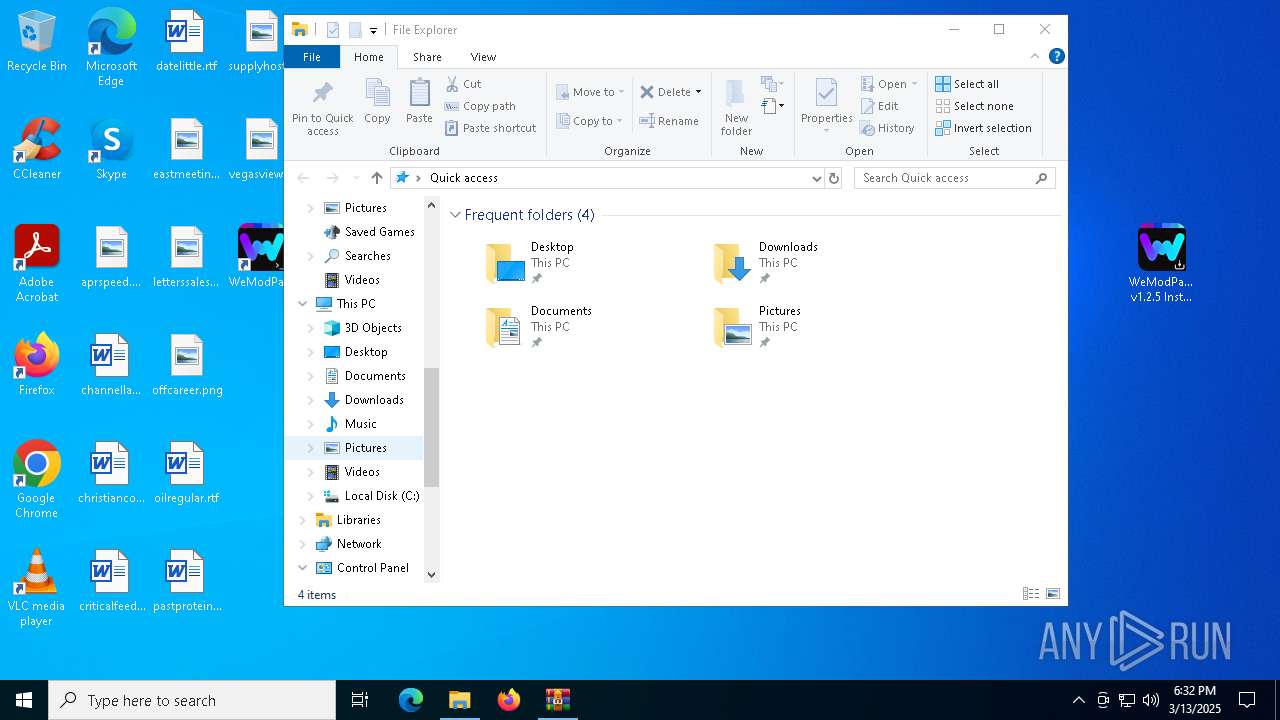
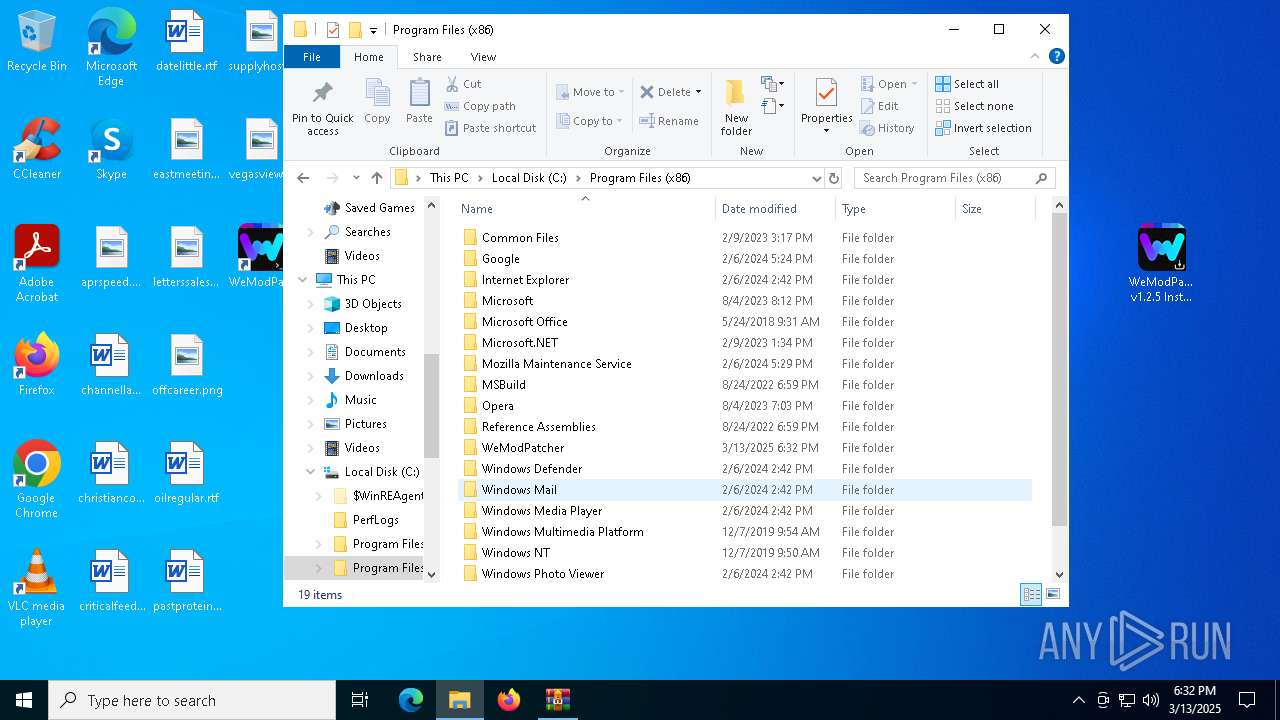
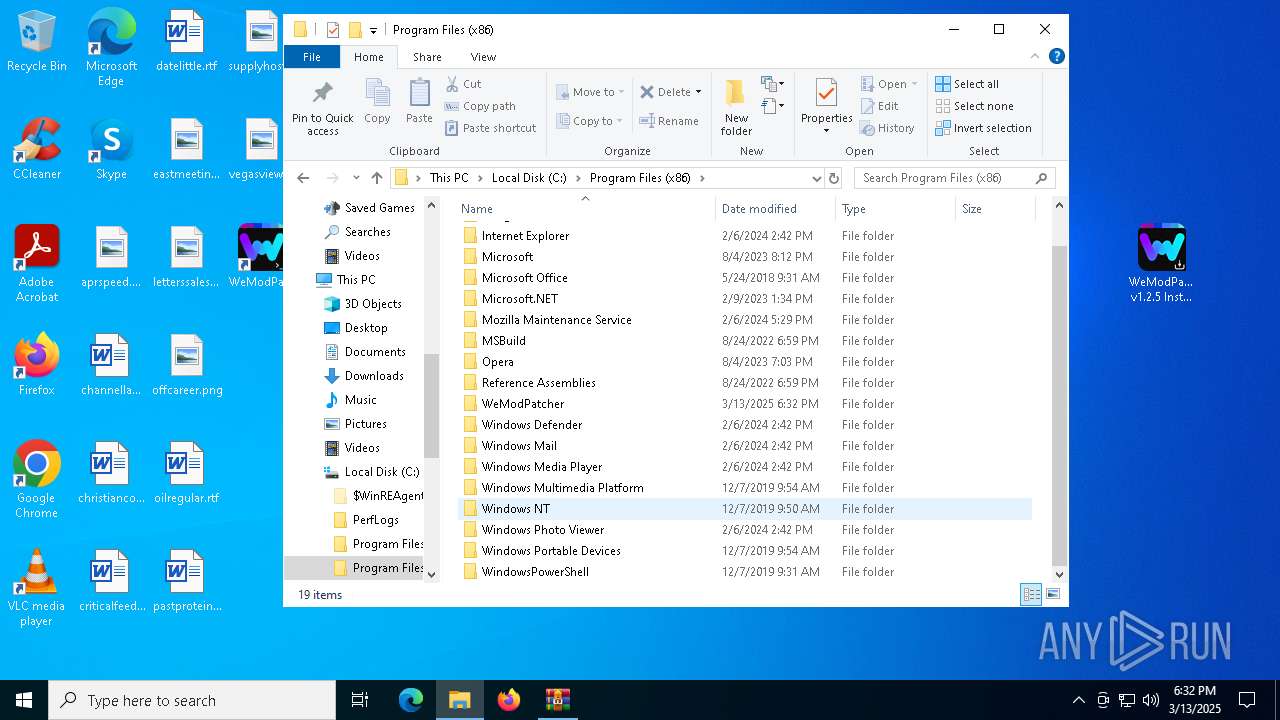
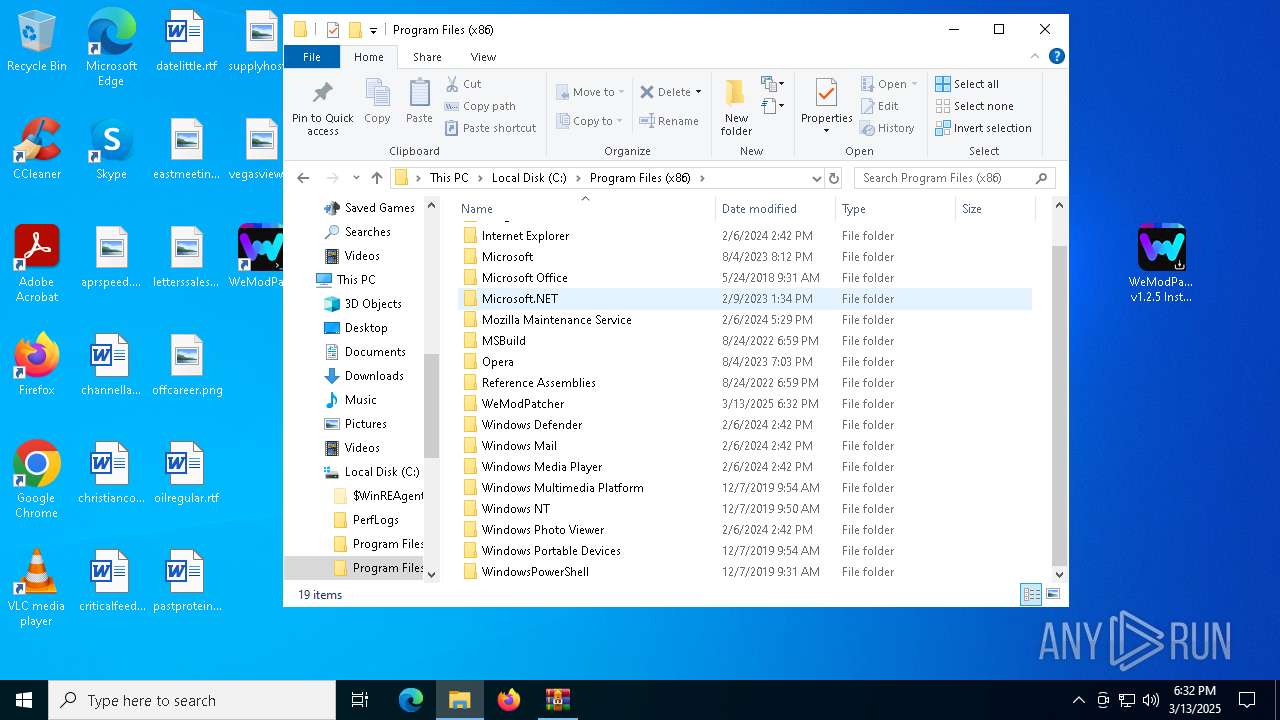
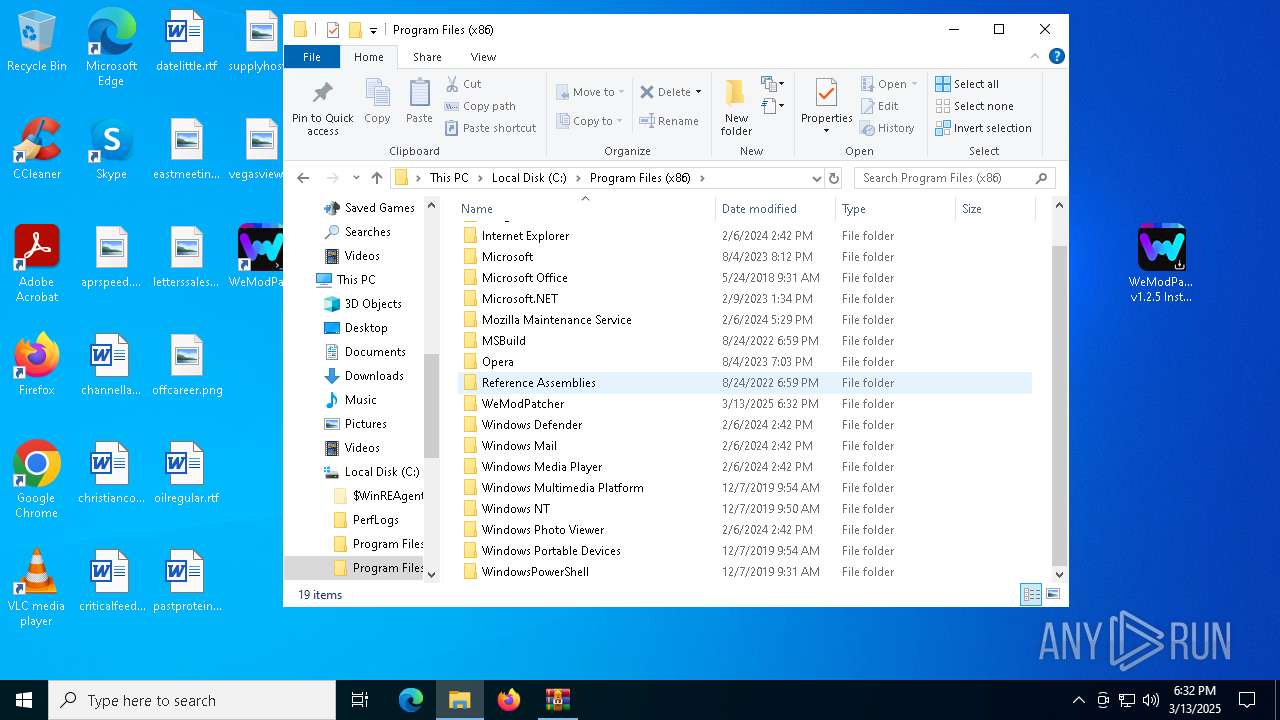
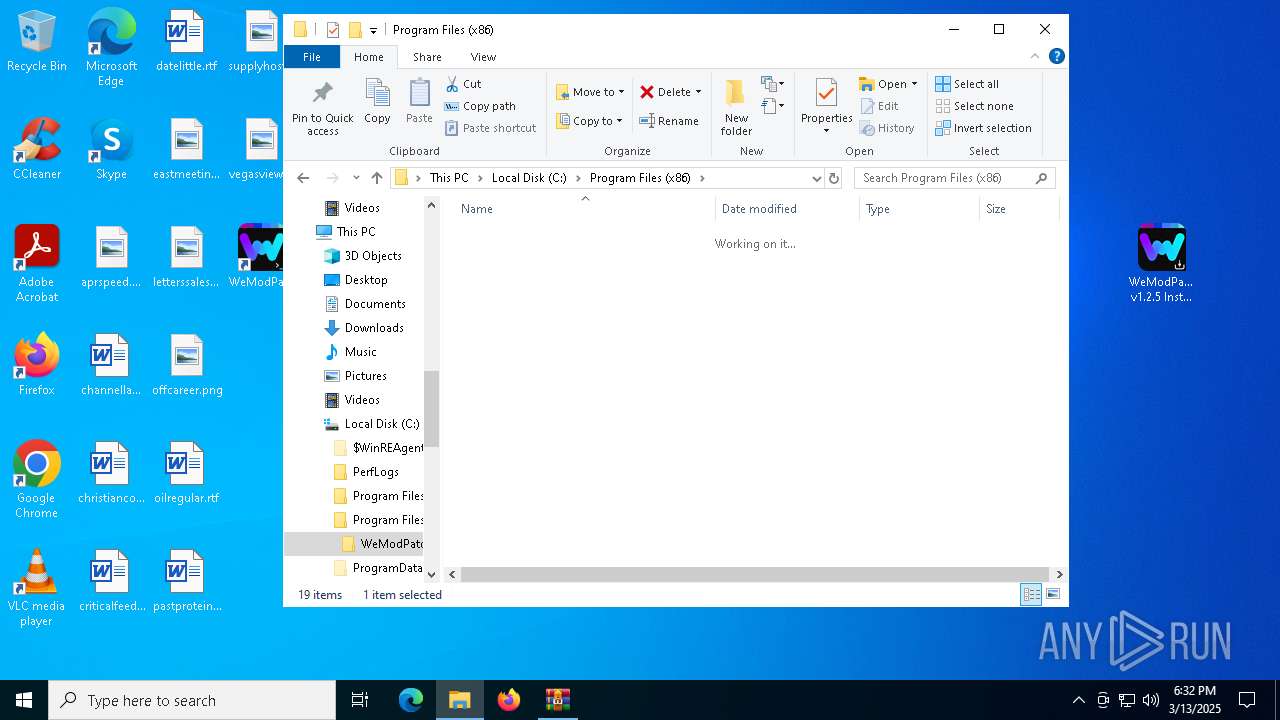
Creates files in the program directory
- WeModPatcher v1.2.5 Installer.tmp (PID: 7672)
- cmd.exe (PID: 1532)
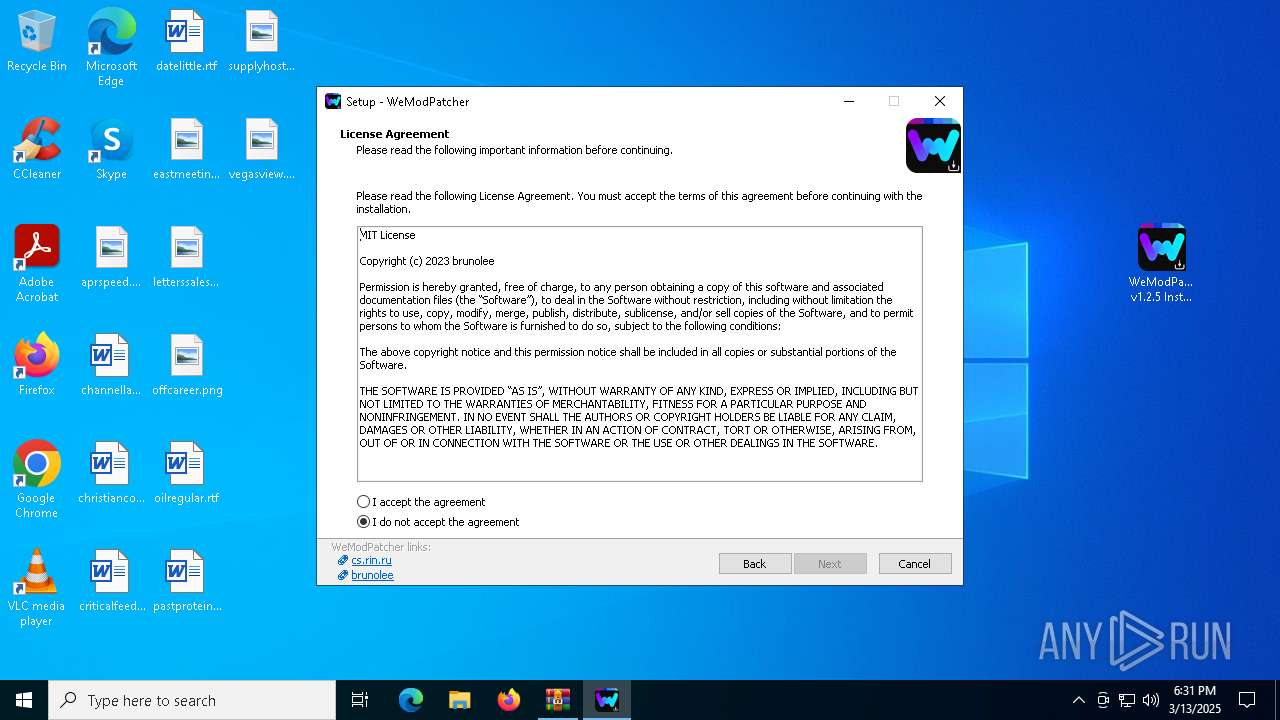
Detects InnoSetup installer (YARA)
- WeModPatcher v1.2.5 Installer.exe (PID: 7428)
Compiled with Borland Delphi (YARA)
- WeModPatcher v1.2.5 Installer.exe (PID: 7428)
Execution of CURL command
- cmd.exe (PID: 8132)
- cmd.exe (PID: 2392)
The sample compiled with english language support
- WeModPatcher v1.2.5 Installer.tmp (PID: 7672)
Changes the display of characters in the console
- cmd.exe (PID: 7476)
- cmd.exe (PID: 1532)
Starts MODE.COM to configure console settings
- mode.com (PID: 5416)
Gets data length (POWERSHELL)
- powershell.exe (PID: 5116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:10:12 22:26:28 |
| ZipCRC: | 0xba710529 |
| ZipCompressedSize: | 3023157 |
| ZipUncompressedSize: | 3887861 |
| ZipFileName: | WeModPatcher v1.2.5 Installer.exe |
Total processes
236
Monitored processes
85
Malicious processes
6
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
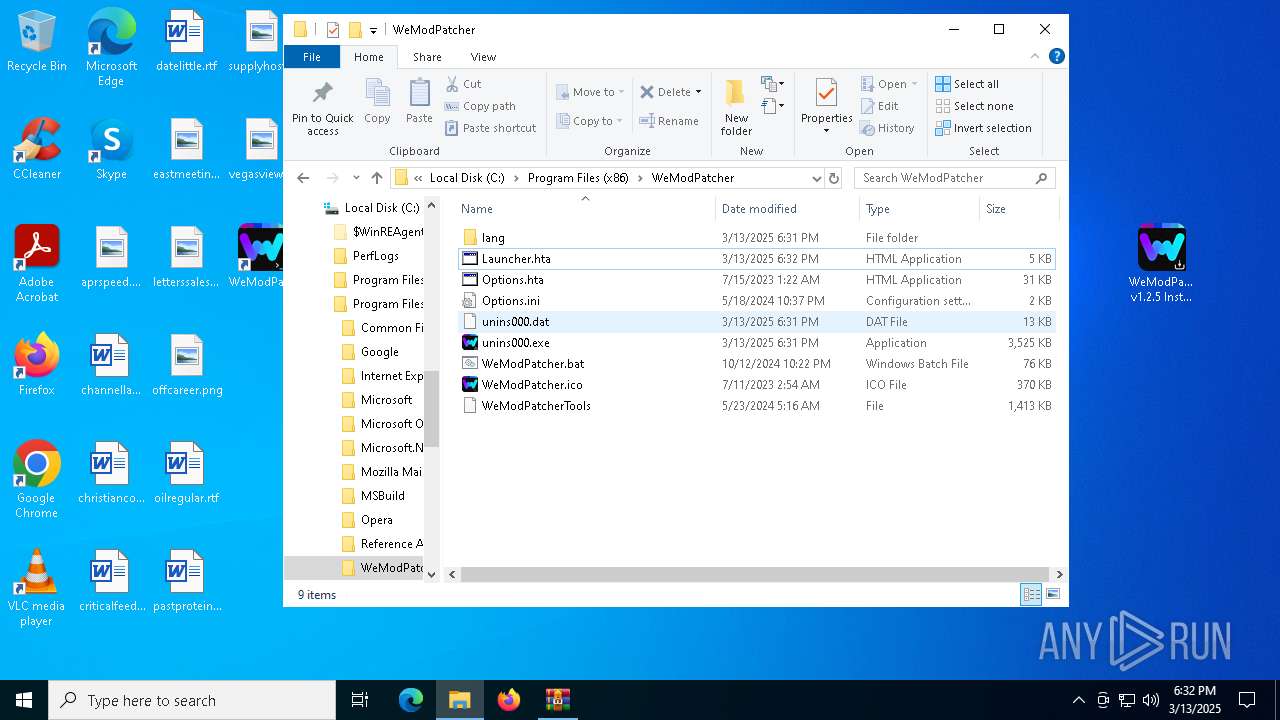
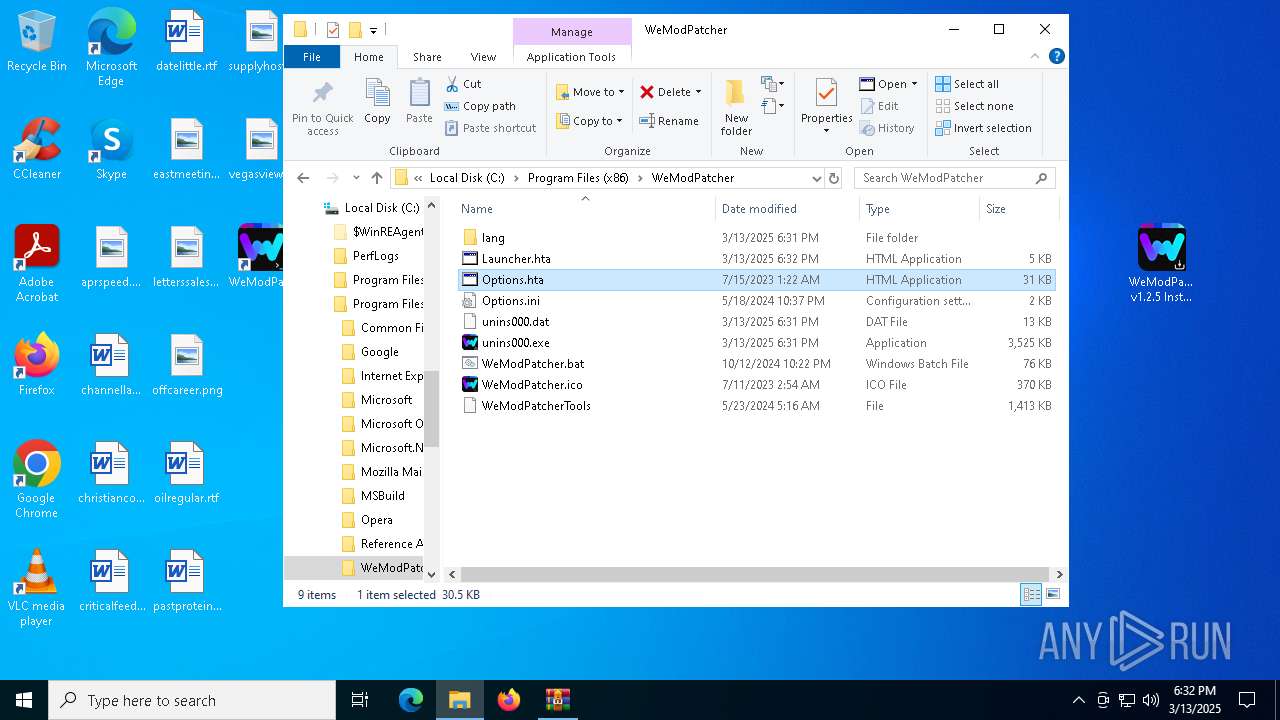
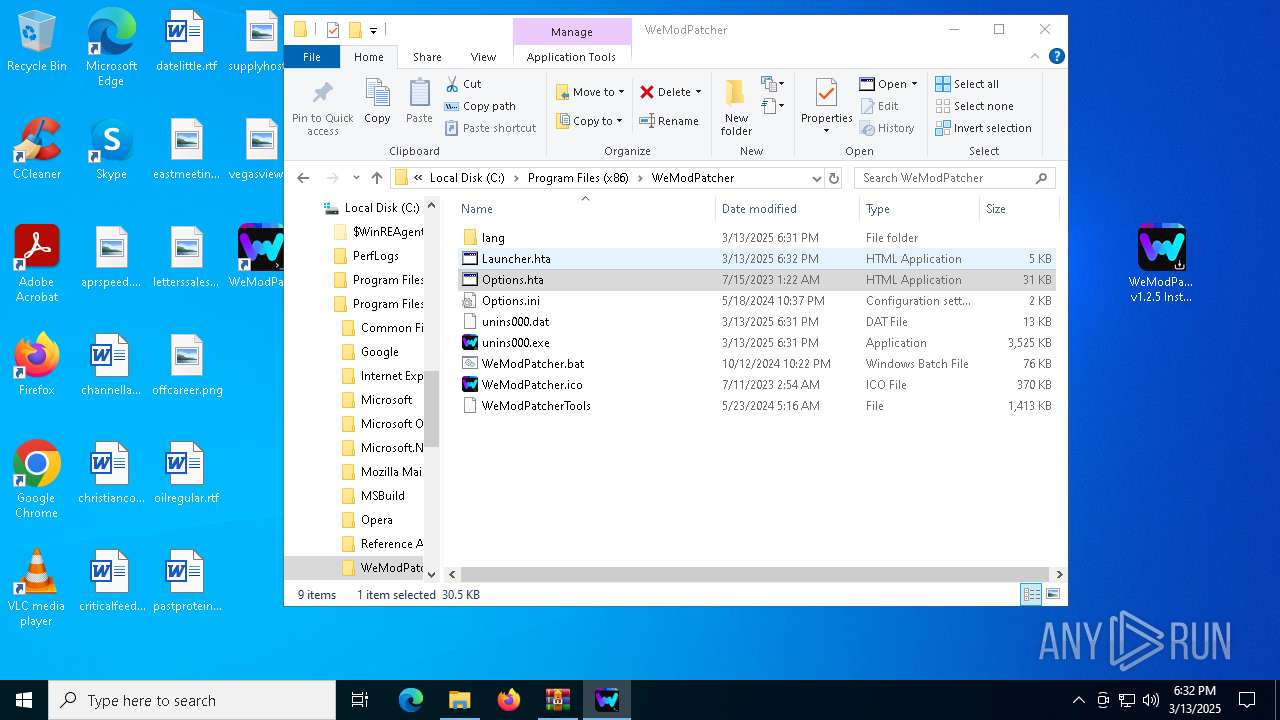
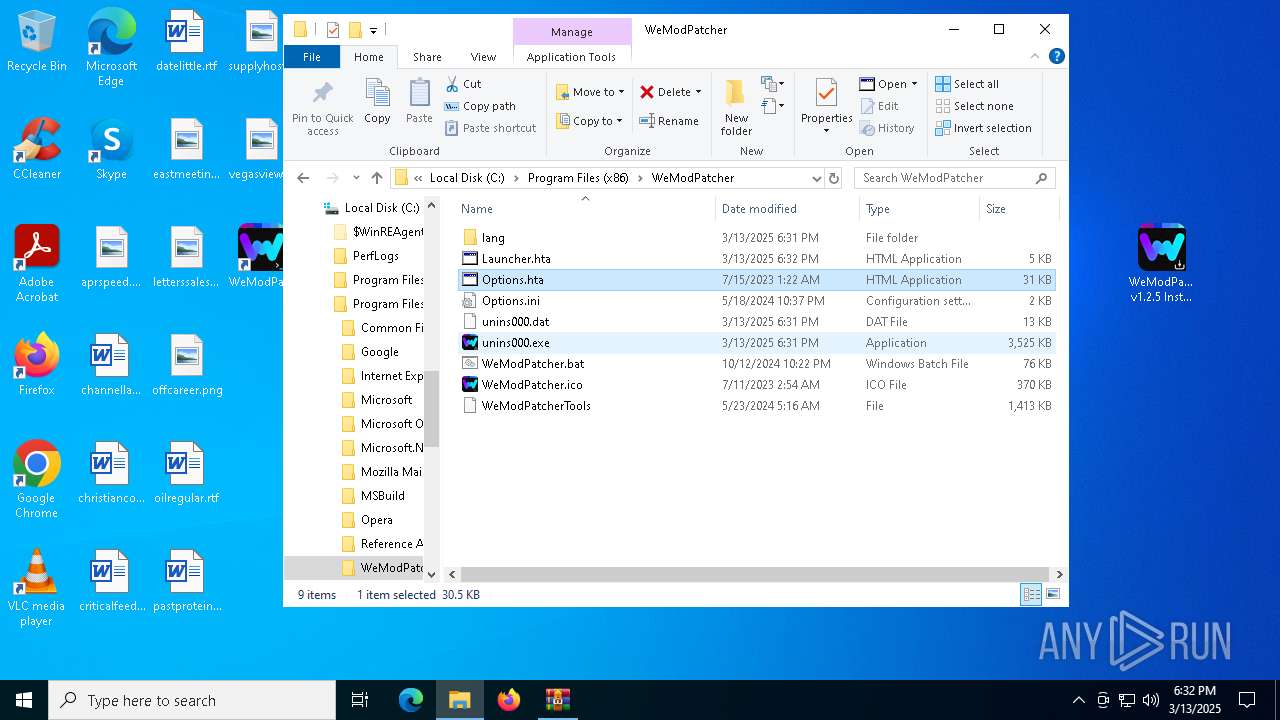
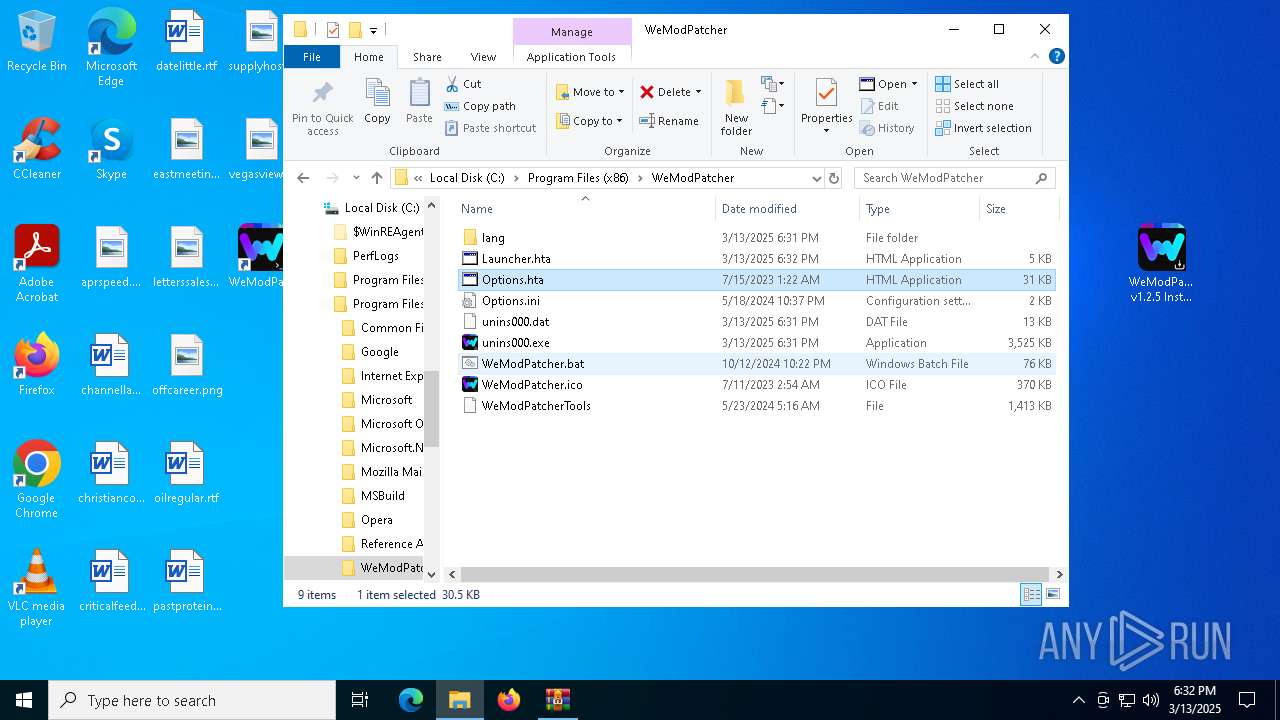
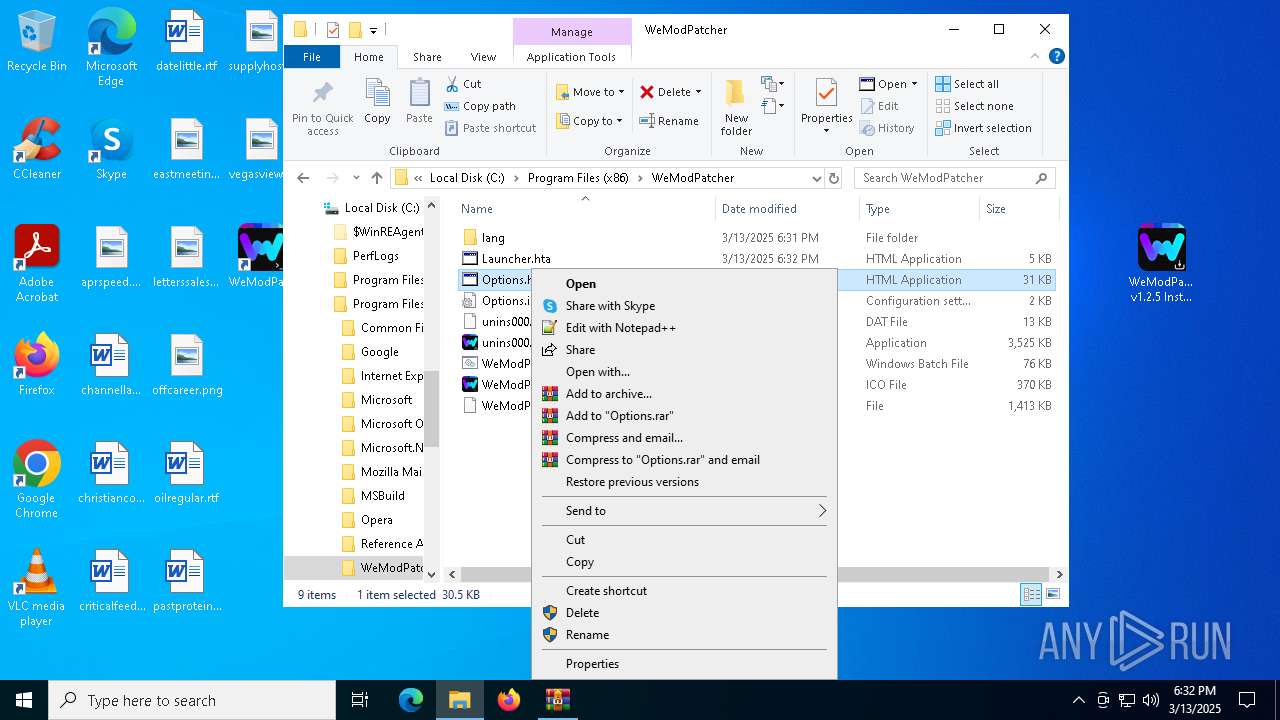
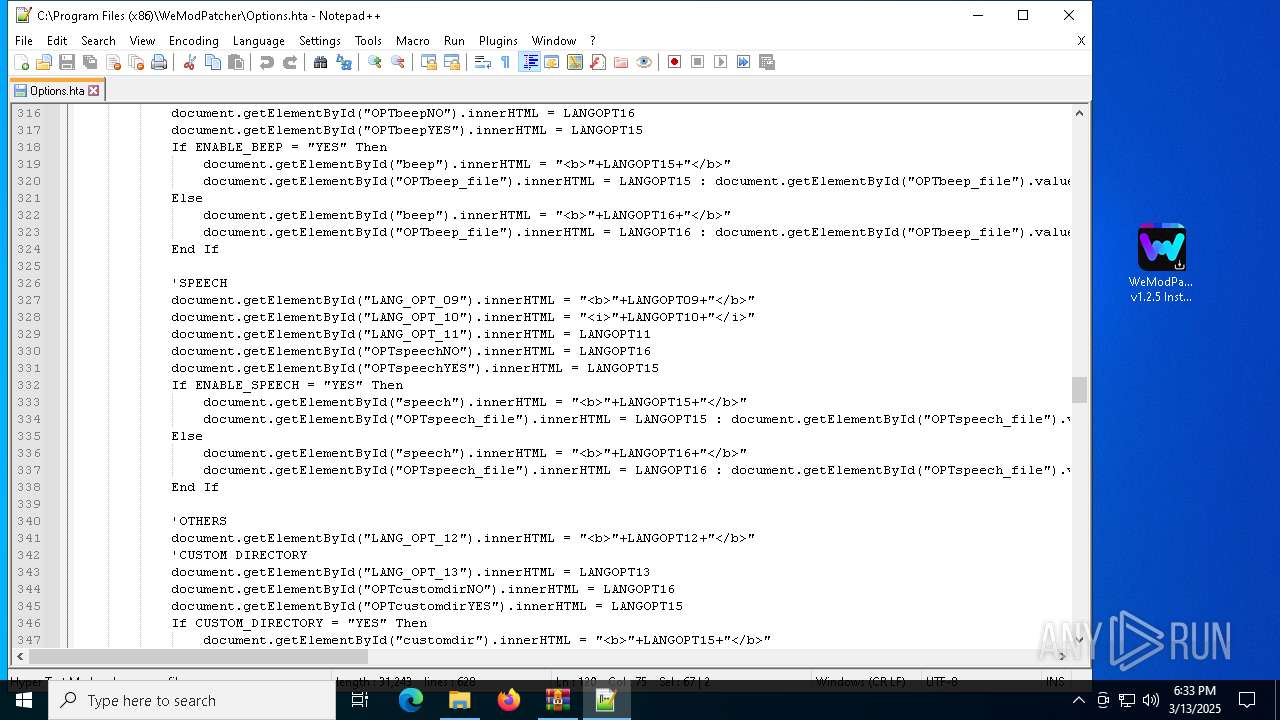
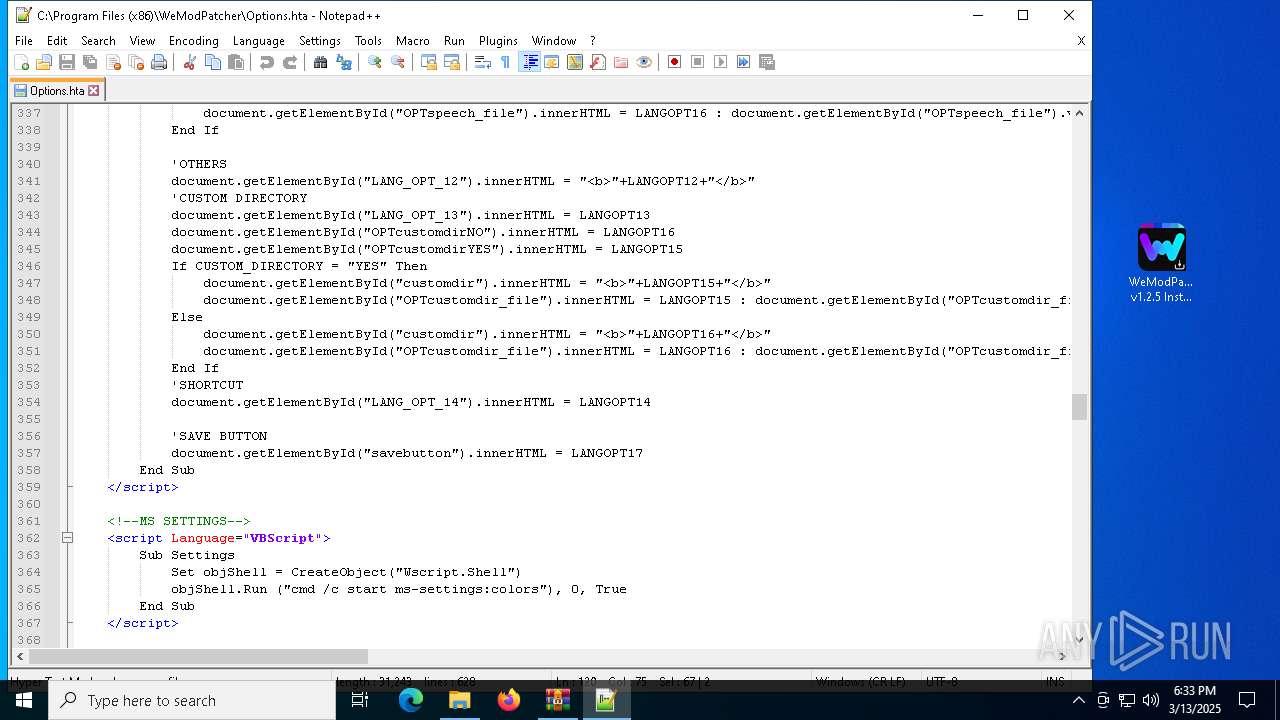
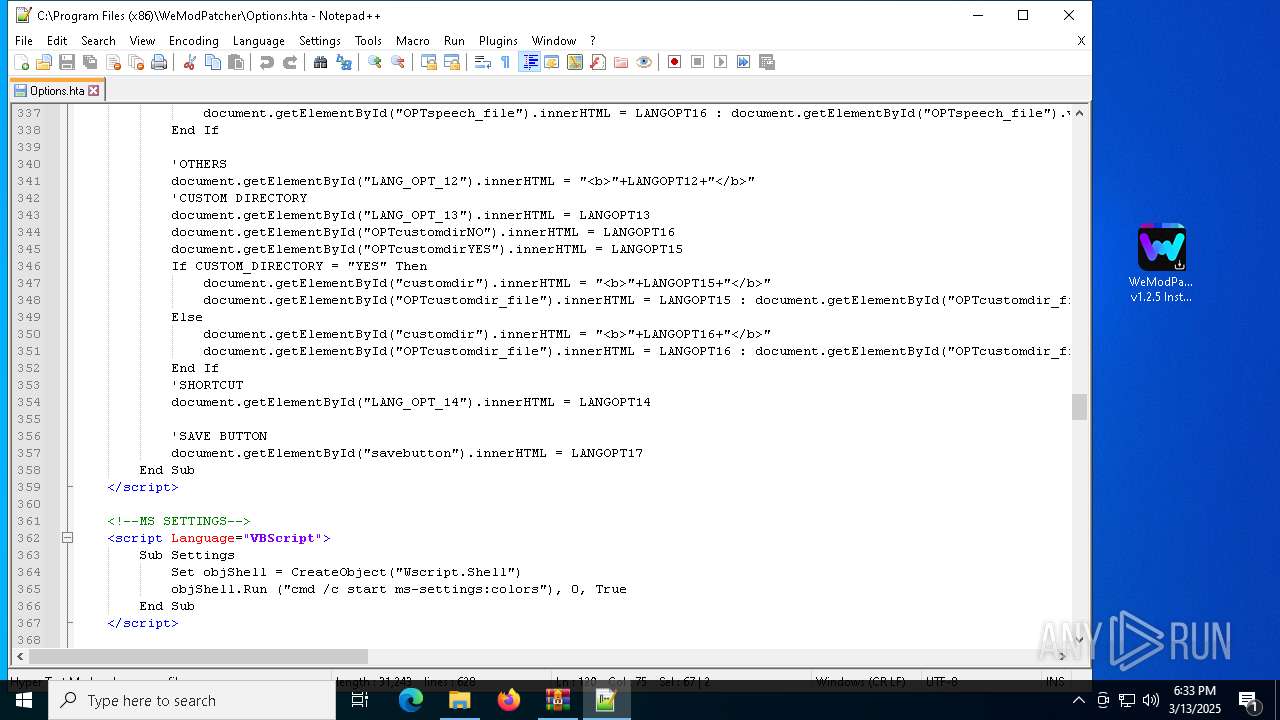
| 660 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Program Files (x86)\WeModPatcher\Options.hta" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 680 | mshta.exe "C:\Program Files (x86)\WeModPatcher\Launcher.hta" | C:\Windows\System32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 3221225477 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\system32\cmd.exe /c mshta.exe "C:\Program Files (x86)\WeModPatcher\Launcher.hta" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225477 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7592 -s 1736 | C:\Windows\SysWOW64\WerFault.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Program Files (x86)\WeModPatcher\WeModPatcher.bat" | C:\Windows\System32\cmd.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
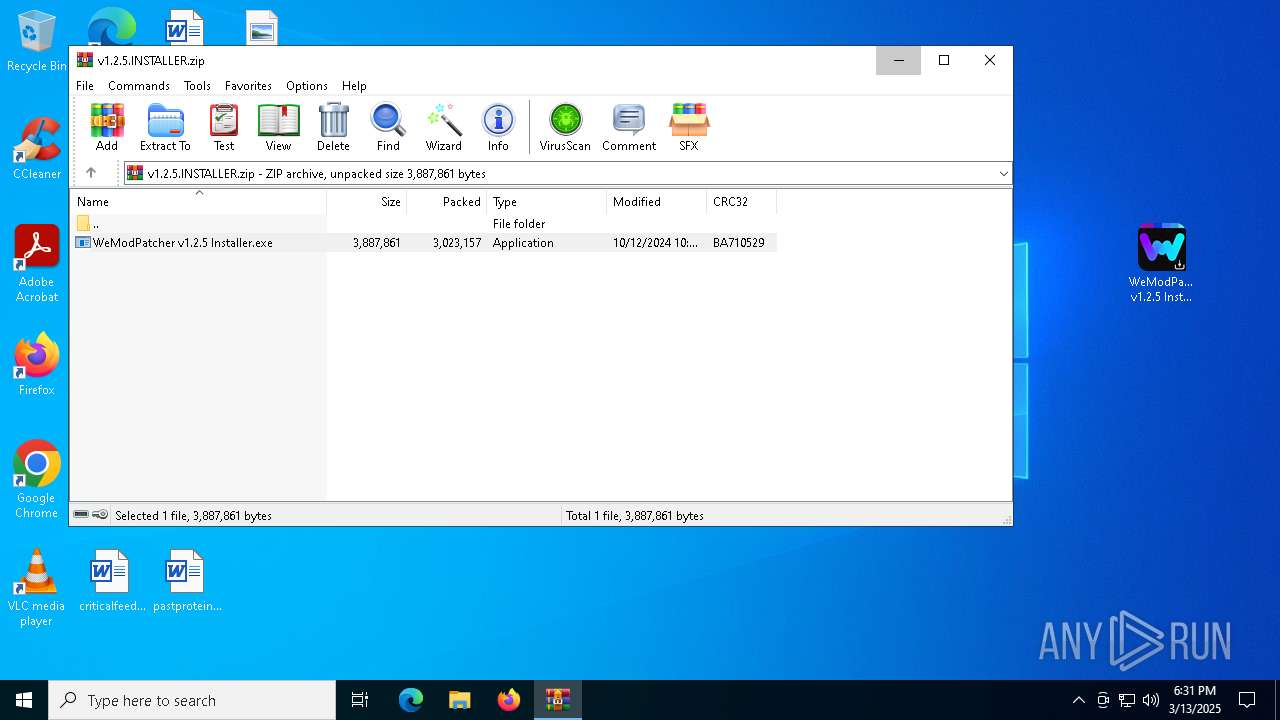
| 1852 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Downloads\v1.2.5.INSTALLER.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2240 | "C:\Windows\SysWOW64\mshta.exe" "C:\Program Files (x86)\WeModPatcher\Launcher.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
90 242
Read events
90 152
Write events
81
Delete events
9
Modification events
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\v1.2.5.INSTALLER.zip | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1852) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8012) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8012) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
6
Suspicious files
26
Text files
71
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5116 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\903efa31-4df4-47b6-b45e-2fbe7bc03228.down_data | — | |
MD5:— | SHA256:— | |||
| 7672 | WeModPatcher v1.2.5 Installer.tmp | C:\Program Files (x86)\WeModPatcher\is-OEF8H.tmp | text | |
MD5:83503A2A8B9F78CFFA4ED444885C4959 | SHA256:E217B87EA4F57FA0FBF70BED27EDA1DA7FF3A4D3B7A989BF15B1261E6735387A | |||
| 5116 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:9FA7CCABC494A5328612D36DD19B8E46 | SHA256:0D0B2B024CD660B45A6646F77B717CCD34A8C0D3EC4D5451D53DD436E87F531D | |||
| 7672 | WeModPatcher v1.2.5 Installer.tmp | C:\Users\admin\AppData\Local\Temp\is-47R2A.tmp\Finished.bmp | image | |
MD5:E53CD7CB8B9F88D2DC9569C3A2A10416 | SHA256:CC0872802A1D2487913BAC918941FDCCA9E96DBDBDFECB0802C1AC6EDFF5A641 | |||
| 7584 | WeModPatcher v1.2.5 Installer.exe | C:\Users\admin\AppData\Local\Temp\is-7S07K.tmp\WeModPatcher v1.2.5 Installer.tmp | executable | |
MD5:FFDD8A3AE61571DBBB2BA95F5EE3D3C6 | SHA256:39C79FE06B2BA133432D8814078F00ED92411BC565613AE35F1DAA0E755DCAF0 | |||
| 7672 | WeModPatcher v1.2.5 Installer.tmp | C:\Program Files (x86)\WeModPatcher\is-1JPK9.tmp | image | |
MD5:CCB4F0739B87DF9D7C9D0BEF63014E53 | SHA256:1F7DDFDA33CC1FF03F897AACAEDFB33A97B6430811089B96C136F362E90073F6 | |||
| 7428 | WeModPatcher v1.2.5 Installer.exe | C:\Users\admin\AppData\Local\Temp\is-7TNLJ.tmp\WeModPatcher v1.2.5 Installer.tmp | executable | |
MD5:FFDD8A3AE61571DBBB2BA95F5EE3D3C6 | SHA256:39C79FE06B2BA133432D8814078F00ED92411BC565613AE35F1DAA0E755DCAF0 | |||
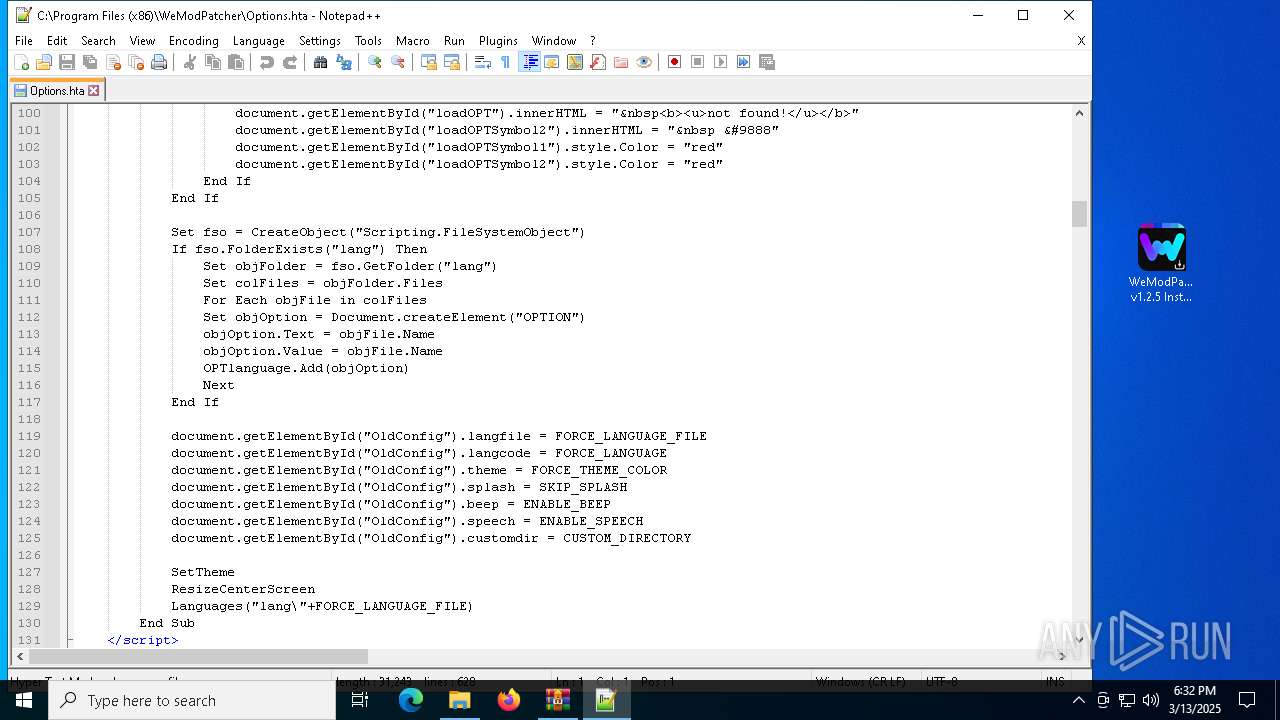
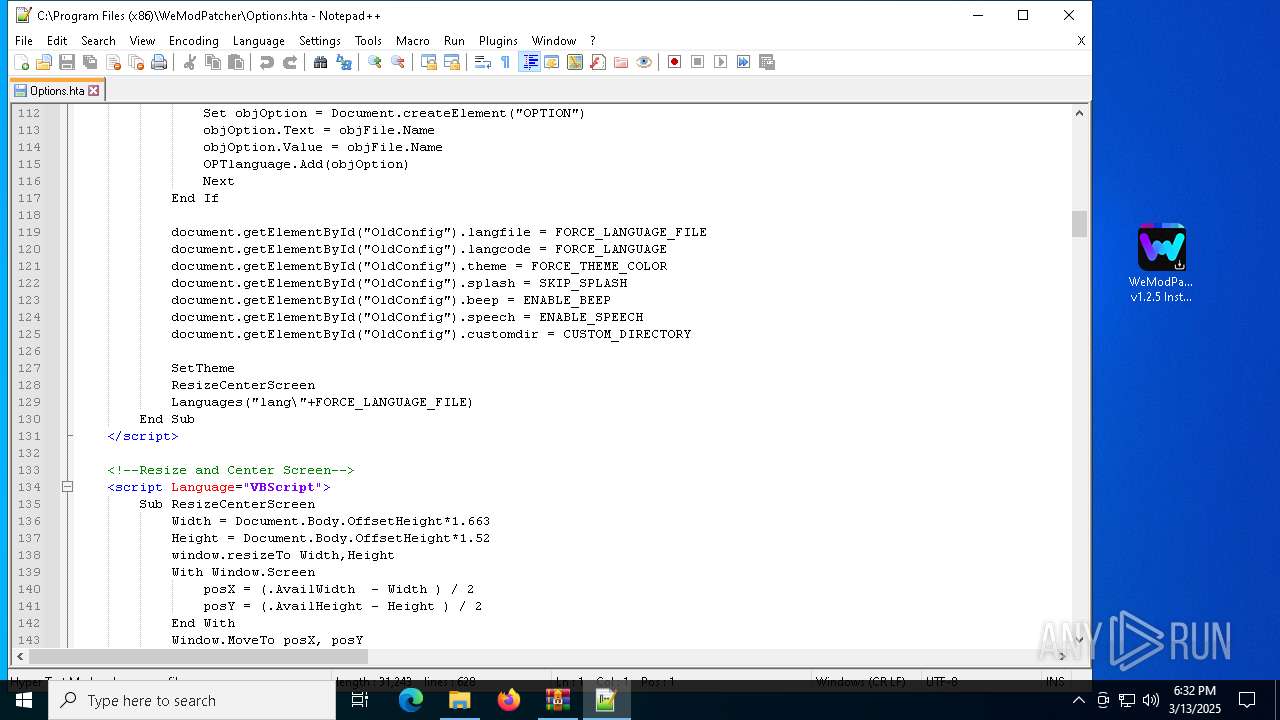
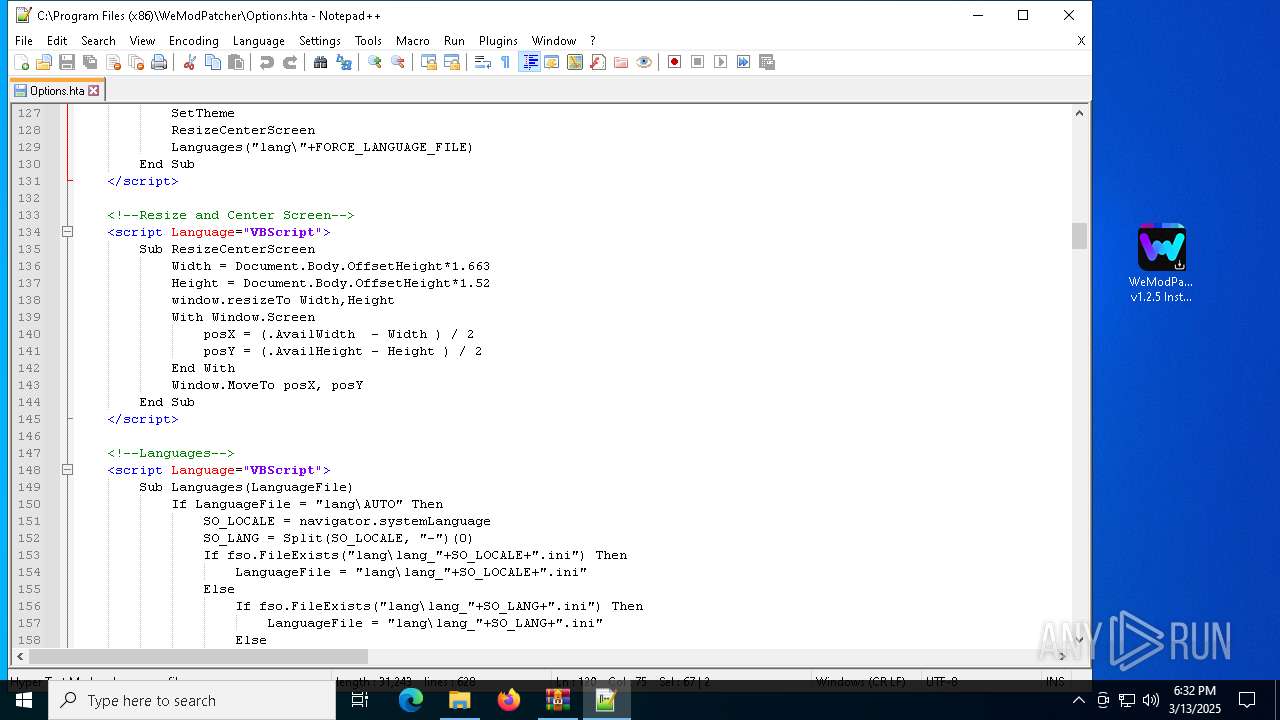
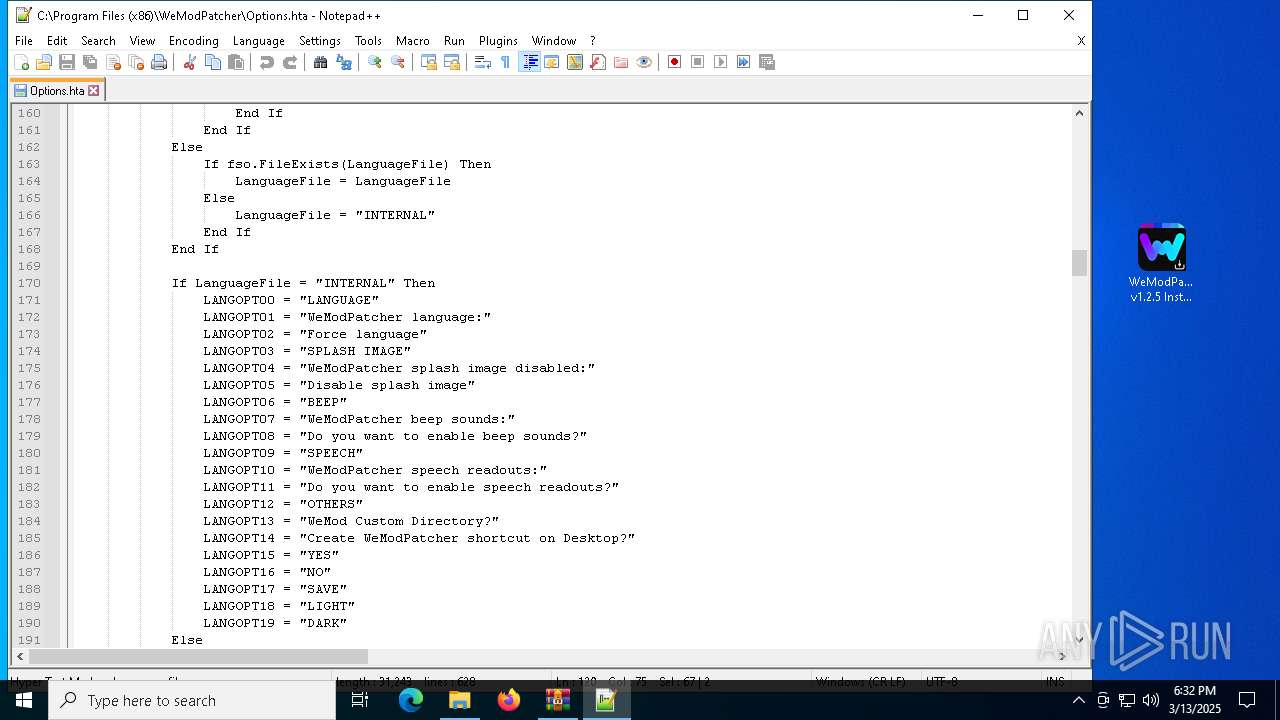
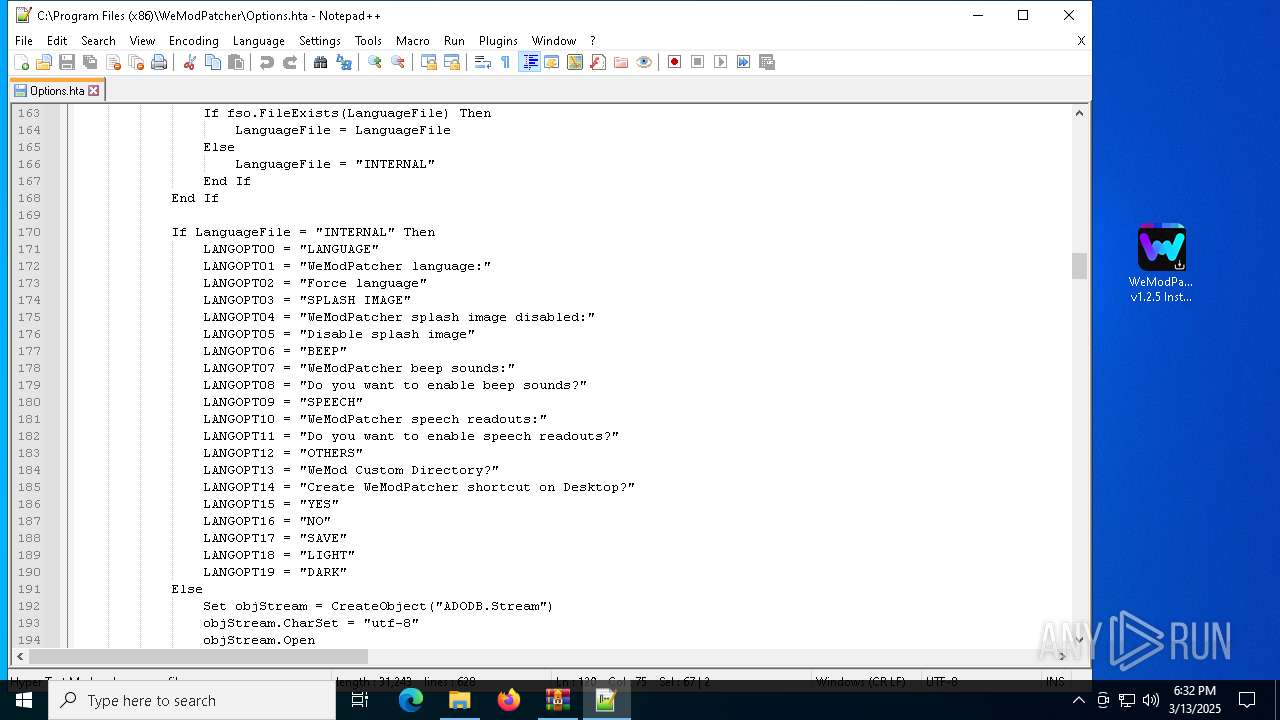
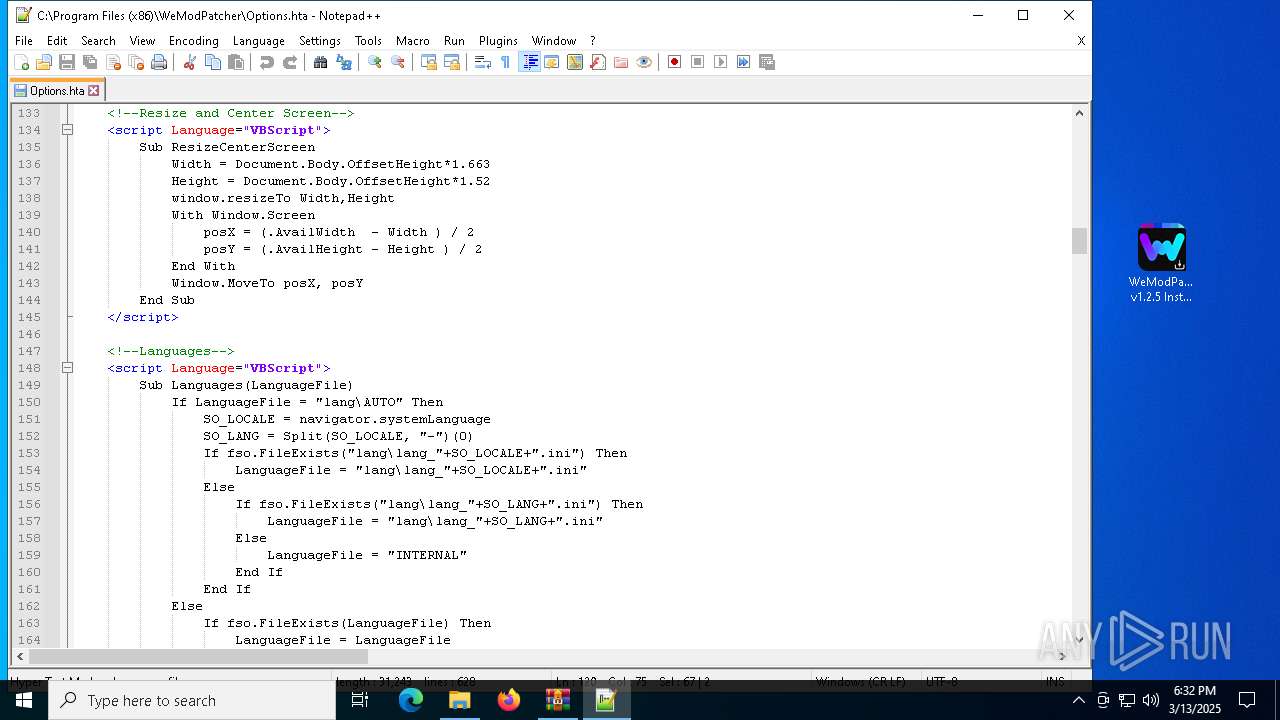
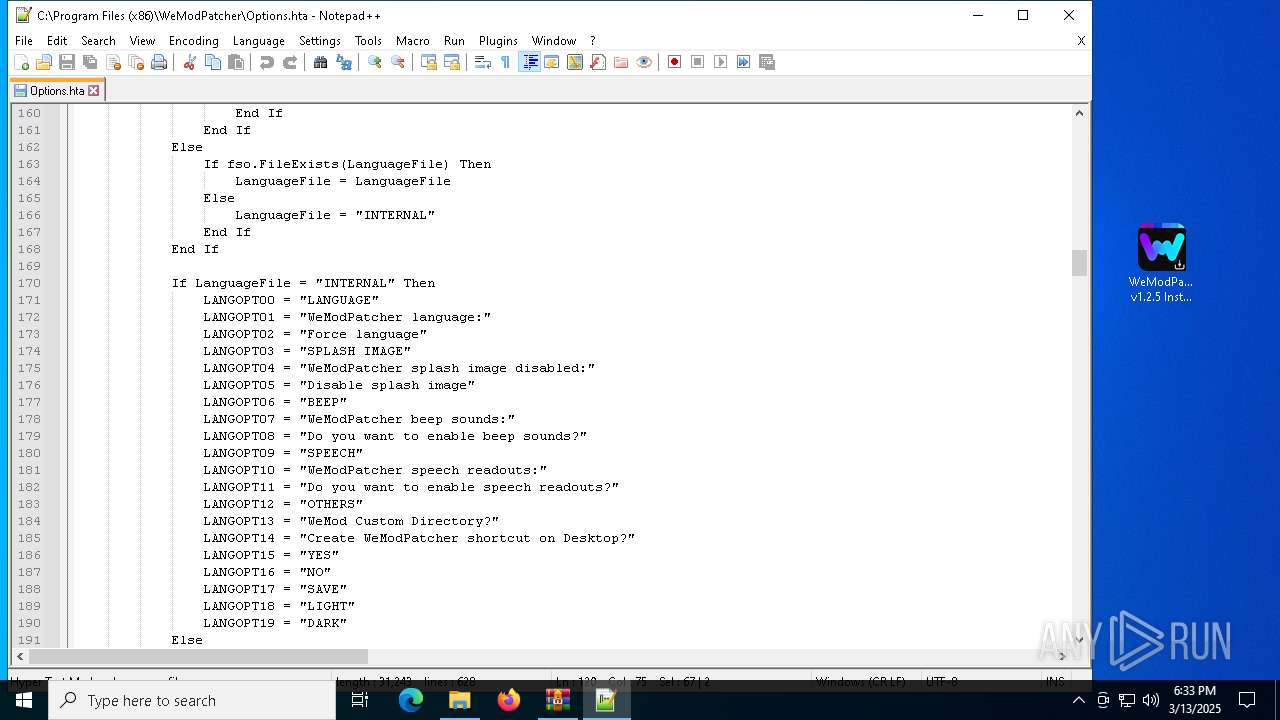
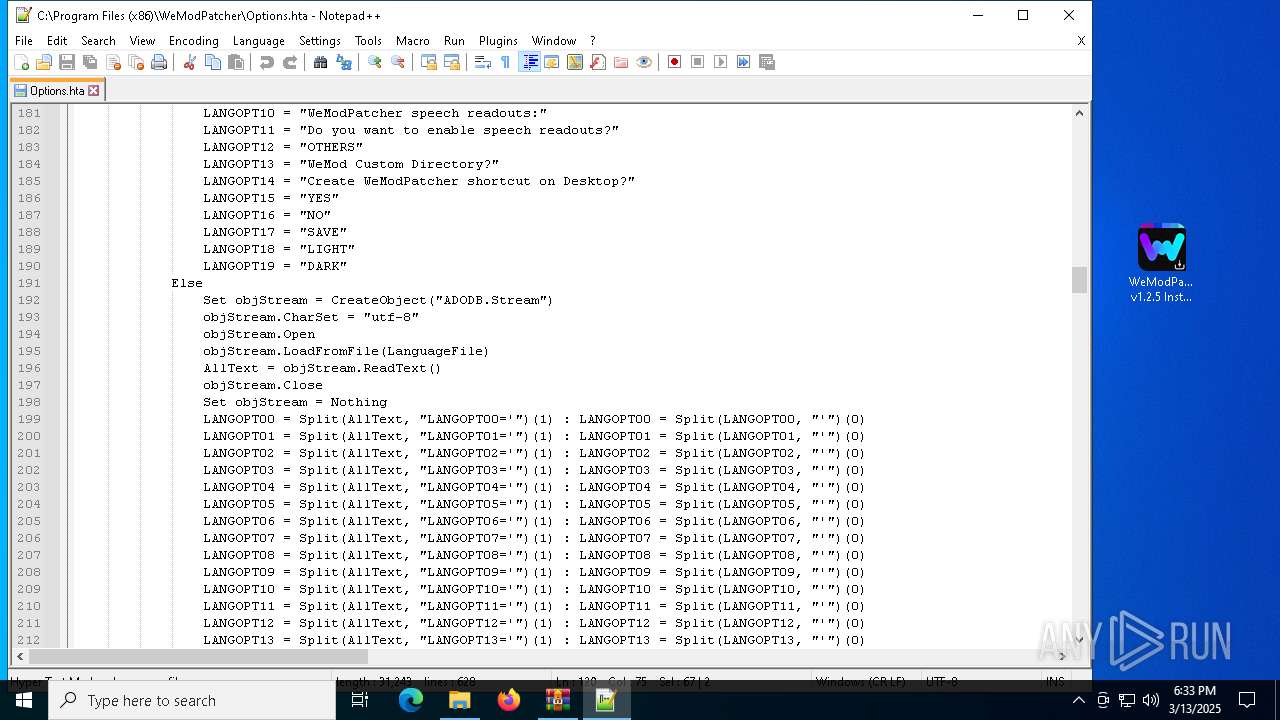
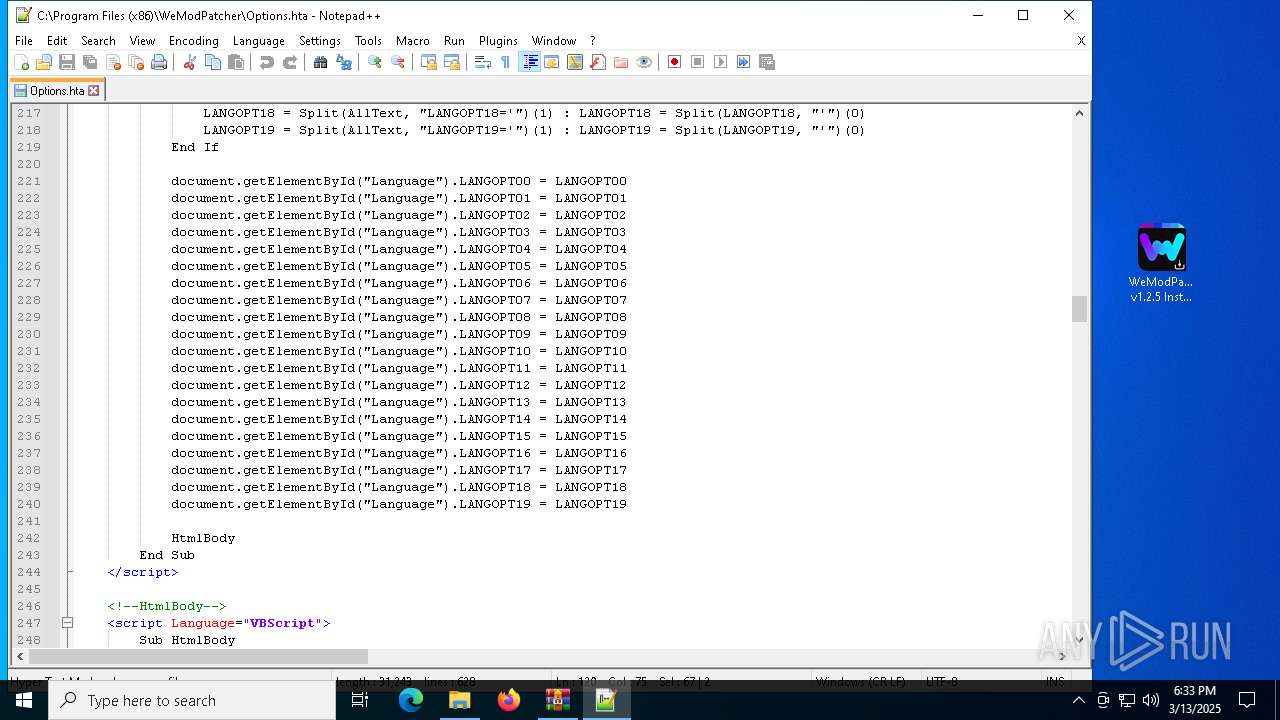
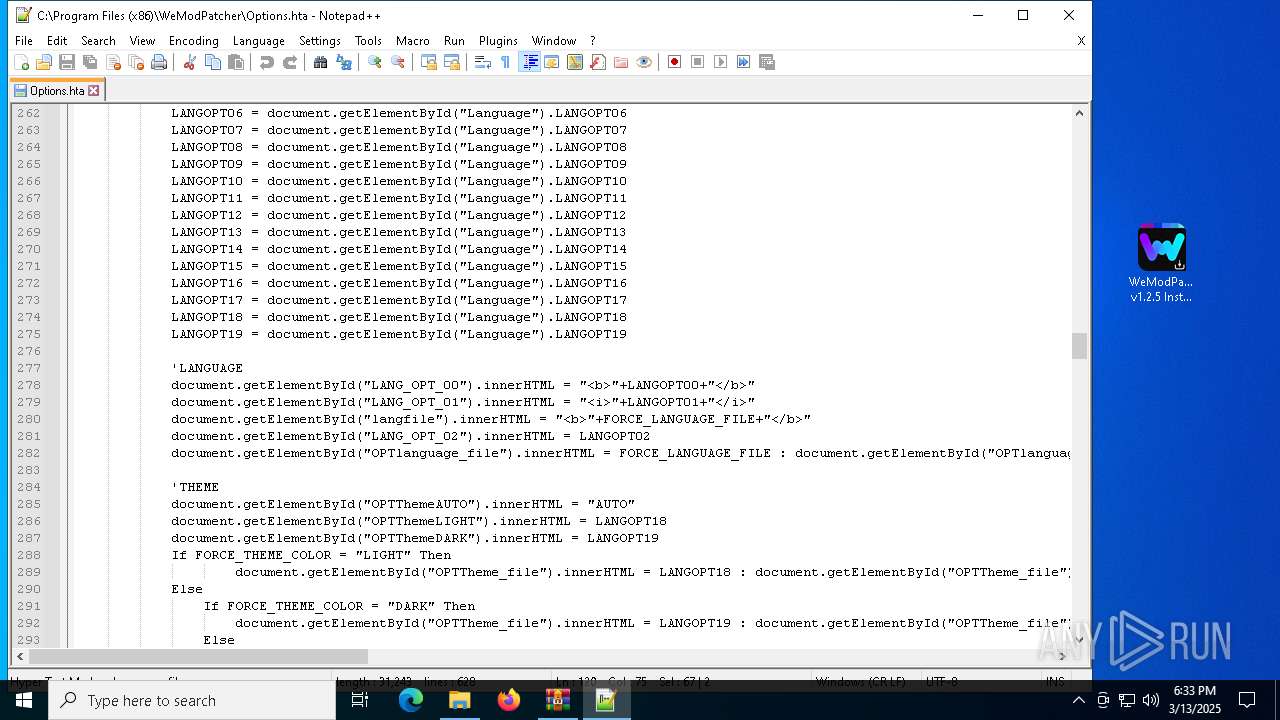
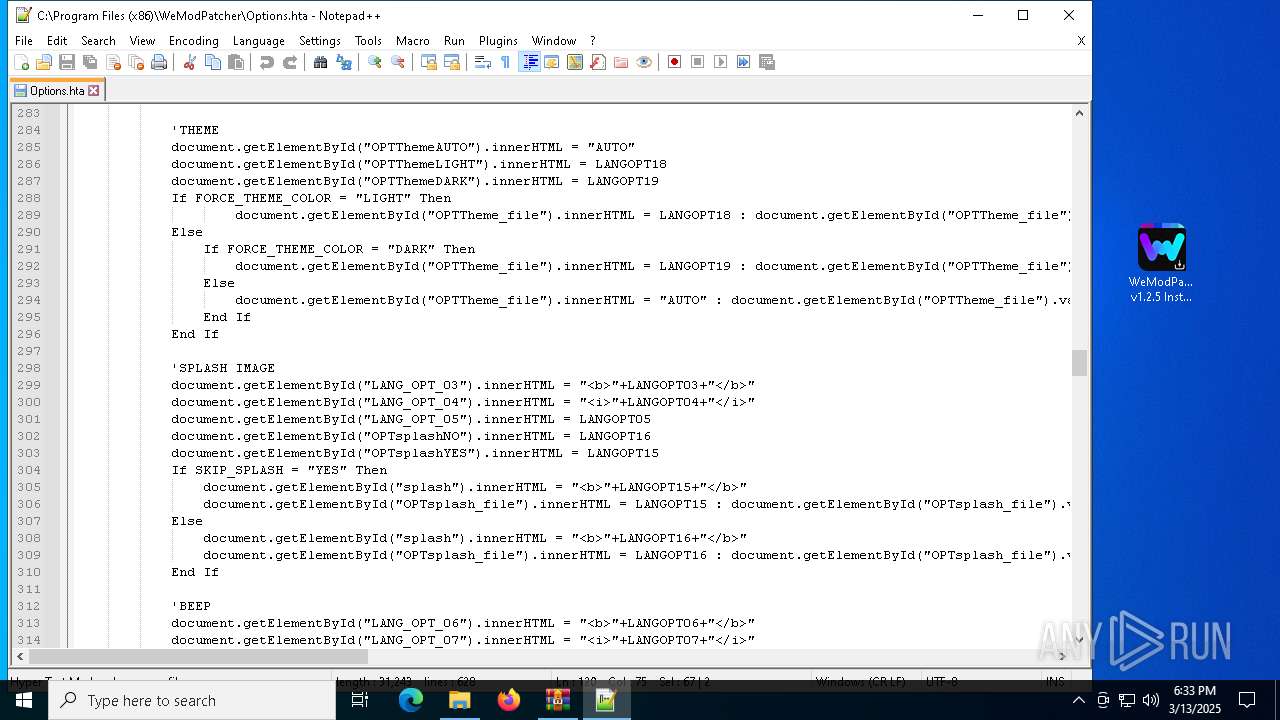
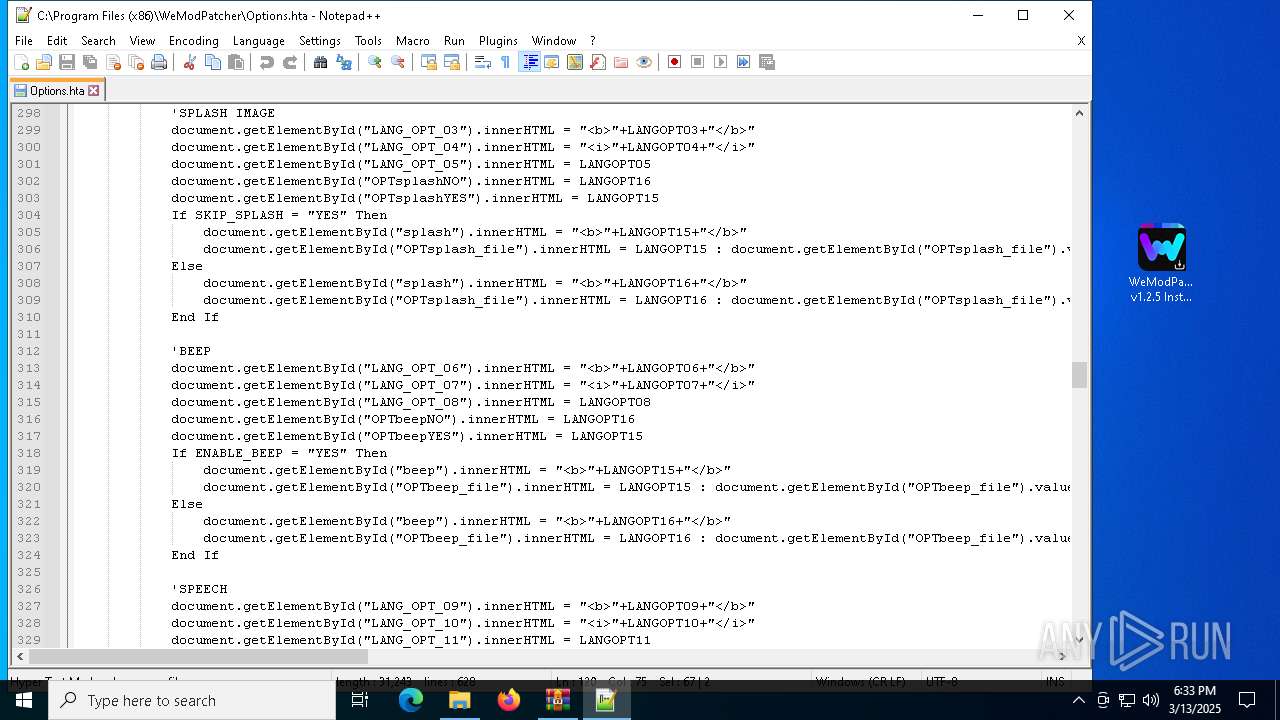
| 7672 | WeModPatcher v1.2.5 Installer.tmp | C:\Program Files (x86)\WeModPatcher\Options.hta | html | |
MD5:C0826786D1B58B03C4C134865CD0A0A6 | SHA256:E4CDEA4433591103E4C416165B9B7EEBFF79C30B011EEE839064C0621FE0B209 | |||
| 7672 | WeModPatcher v1.2.5 Installer.tmp | C:\Users\admin\AppData\Local\Temp\is-47R2A.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 5116 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\903efa31-4df4-47b6-b45e-2fbe7bc03228.a2ff51ba-a5e7-4de8-af5e-f4f1776186d8.down_meta | binary | |
MD5:316D72F5BCB0124C5A3673EEBF5BADDC | SHA256:3349DA5539DF69DB2EE90C21919E1A8A8644C42FADE6B58A1BEC44DF08647E93 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
32
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7500 | backgroundTaskHost.exe | GET | 200 | 104.78.173.167:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 104.78.173.167:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 104.78.173.167:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
5116 | BackgroundTransferHost.exe | GET | 200 | 104.78.173.167:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3272 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
3272 | SIHClient.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6392 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 20.197.71.89:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 104.78.173.167:80 | ocsp.digicert.com | AKAMAI-AS | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |