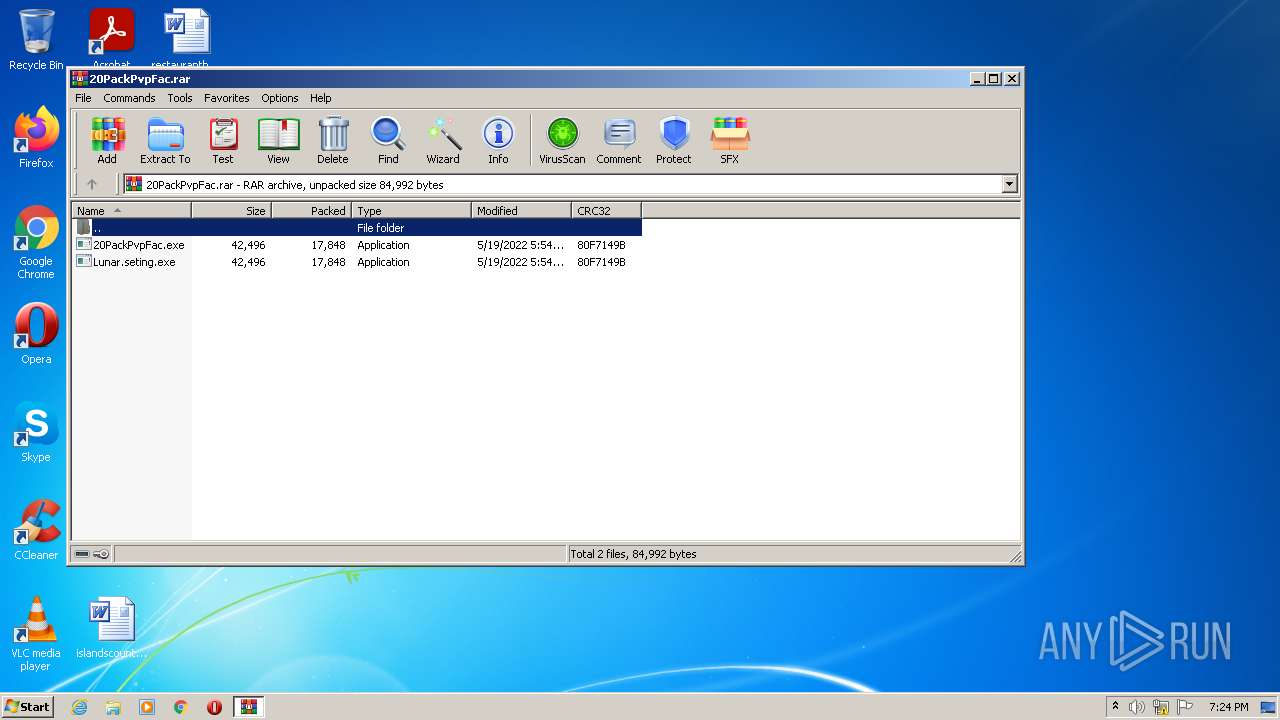
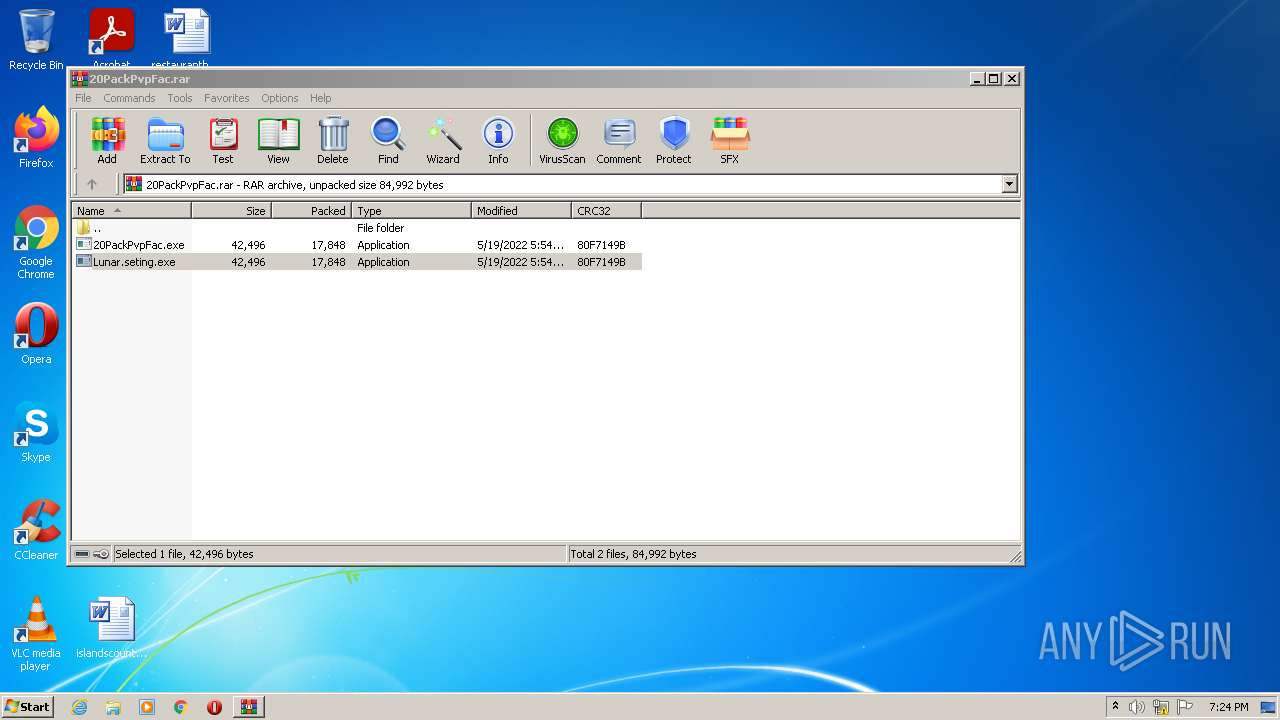
| File name: | 20PackPvpFac.rar |
| Full analysis: | https://app.any.run/tasks/d50e4838-4078-4757-86e2-fe679063387a |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 18:24:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 5701DDB51C8D475BCECDADF416005207 |
| SHA1: | D285B1C03569E8775D3B8522873F9DCC88FA1746 |
| SHA256: | 313FA3E3B56E26386FDC1CA310B4BB7C6CF7B6E3CCF578A53500B68B36F7DFA1 |
| SSDEEP: | 768:UIx4yve9N+lMytAOHotMvOIx4yve9N+lMytAOHotMva:UIx5e9uMytAOHjvOIx5e9uMytAOHjva |
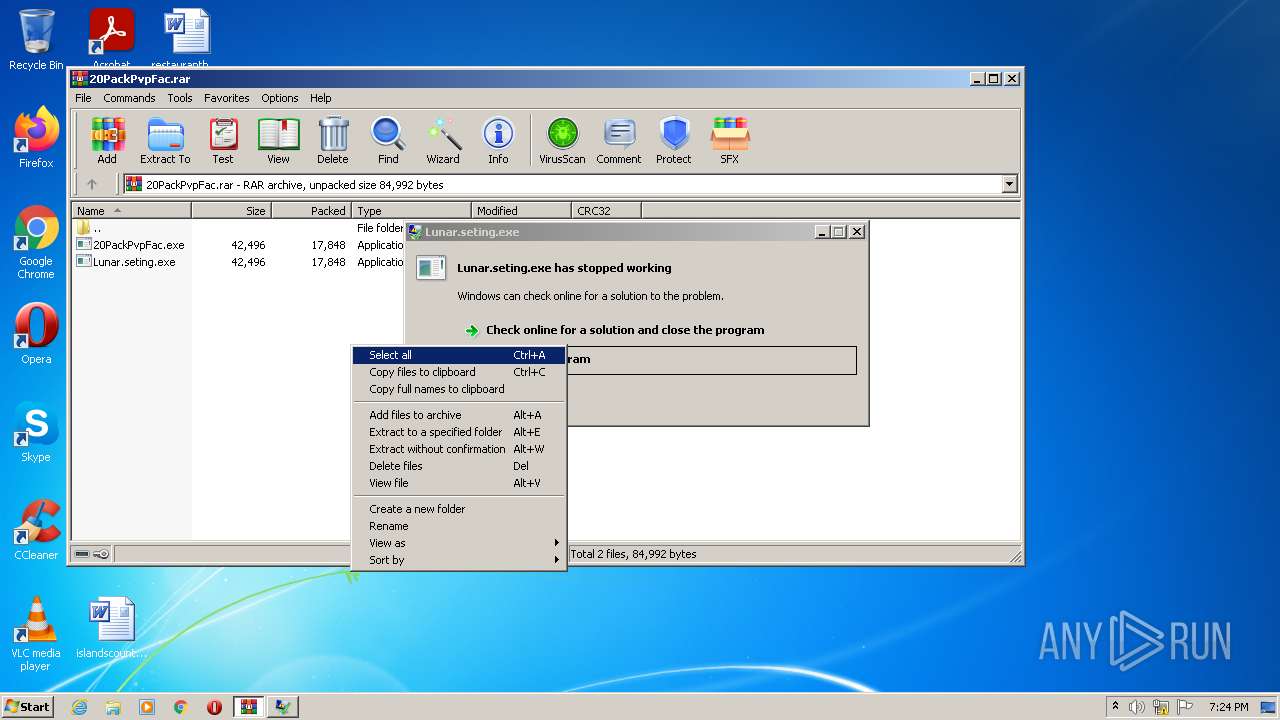
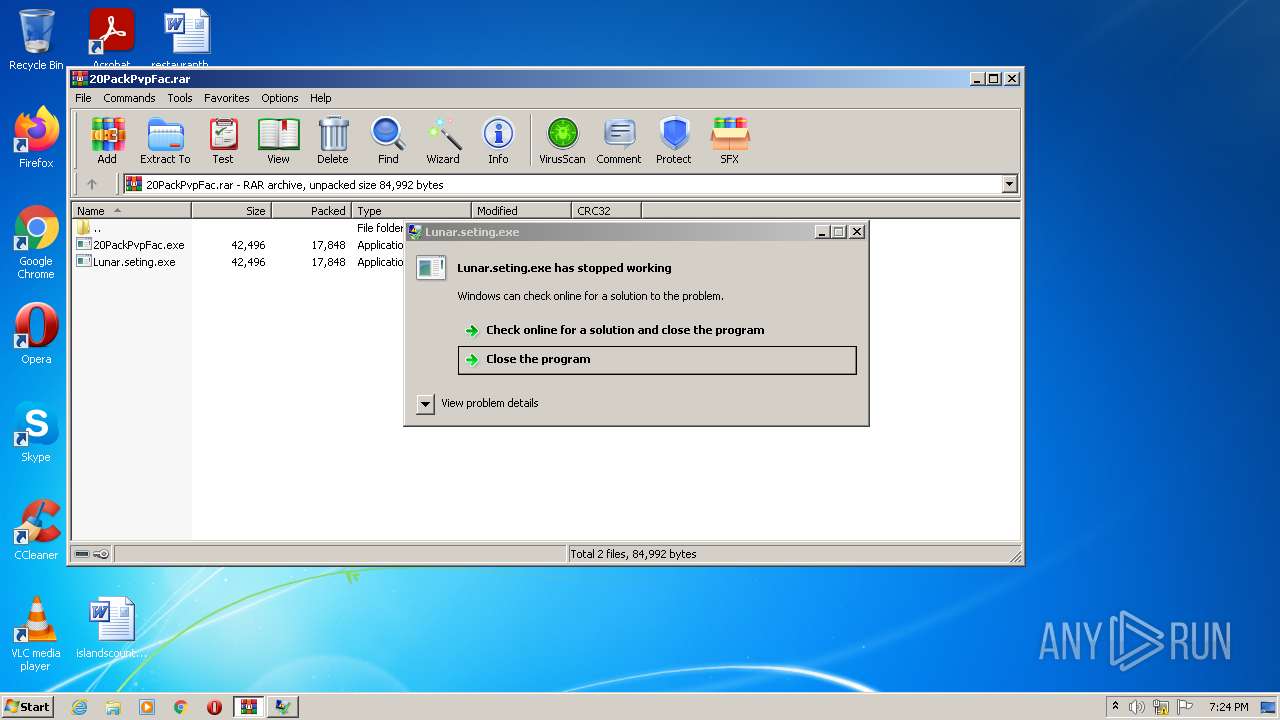
MALICIOUS
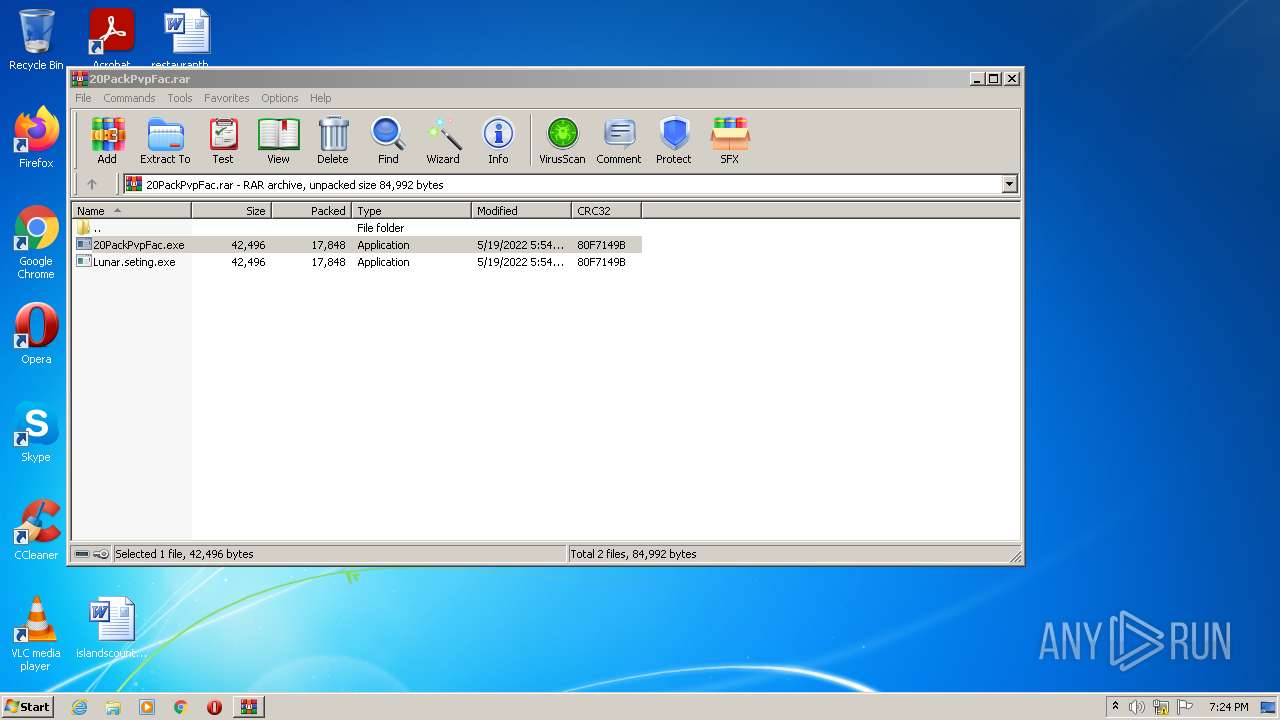
Application was dropped or rewritten from another process
- 20PackPvpFac.exe (PID: 1836)
- Lunar.seting.exe (PID: 3940)
Drops executable file immediately after starts
- WinRAR.exe (PID: 2924)
MERCURIALGRABBER detected by memory dumps
- 20PackPvpFac.exe (PID: 1836)
Actions looks like stealing of personal data
- 20PackPvpFac.exe (PID: 1836)
- Lunar.seting.exe (PID: 3940)
SUSPICIOUS
Checks supported languages
- 20PackPvpFac.exe (PID: 1836)
- WinRAR.exe (PID: 2924)
- Lunar.seting.exe (PID: 3940)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2924)
Reads the computer name
- WinRAR.exe (PID: 2924)
- 20PackPvpFac.exe (PID: 1836)
- Lunar.seting.exe (PID: 3940)
Reads Environment values
- 20PackPvpFac.exe (PID: 1836)
- Lunar.seting.exe (PID: 3940)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2924)
Reads CPU info
- 20PackPvpFac.exe (PID: 1836)
- Lunar.seting.exe (PID: 3940)
Checks for external IP
- 20PackPvpFac.exe (PID: 1836)
- Lunar.seting.exe (PID: 3940)
INFO
Reads settings of System Certificates
- 20PackPvpFac.exe (PID: 1836)
- Lunar.seting.exe (PID: 3940)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
MercurialGrabber
(PID) Process(1836) 20PackPvpFac.exe
C2https://discord.com/api/webhooks/976886781041586236/rro04rr4QUrcsUe2-Pv0FuHd7X6PWEerlf7t9k4jCAReFBSiV93Awtm2Dz95X3cLJH7I
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
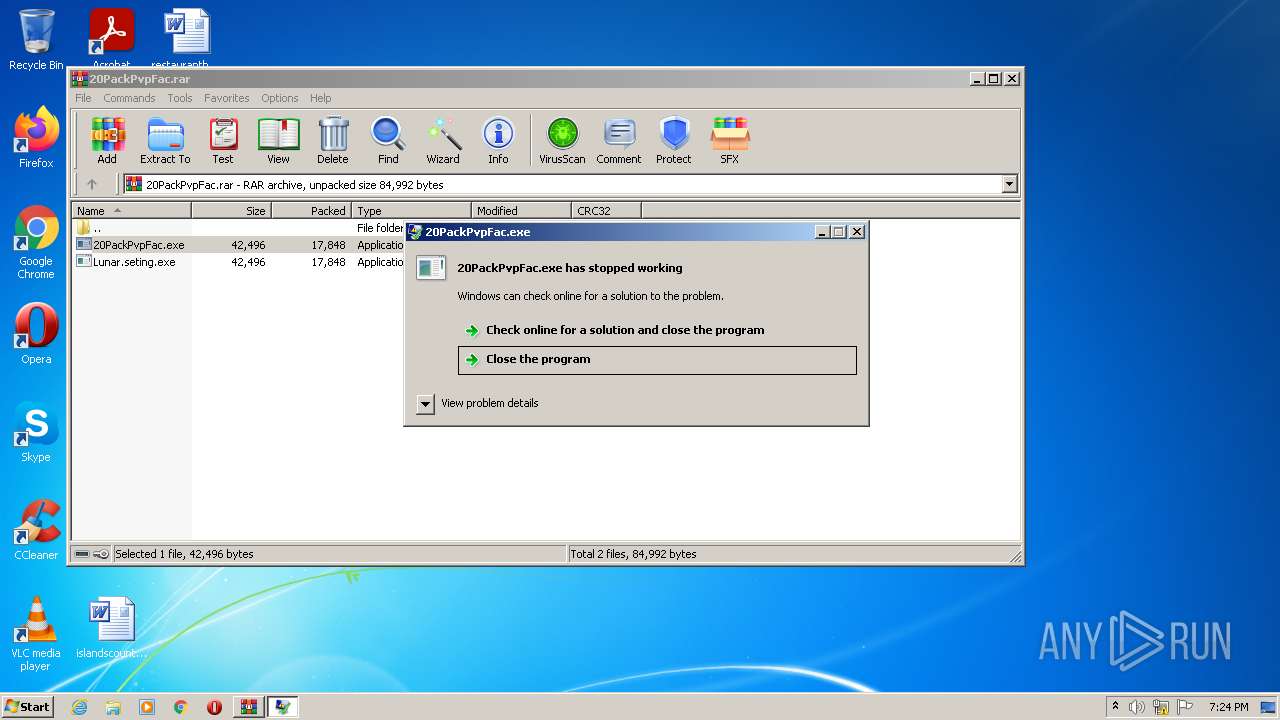
| 1836 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.23007\20PackPvpFac.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.23007\20PackPvpFac.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221225477 Version: 0.0.0.0 Modules
MercurialGrabber(PID) Process(1836) 20PackPvpFac.exe C2https://discord.com/api/webhooks/976886781041586236/rro04rr4QUrcsUe2-Pv0FuHd7X6PWEerlf7t9k4jCAReFBSiV93Awtm2Dz95X3cLJH7I | |||||||||||||||
| 2924 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\20PackPvpFac.rar" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3940 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.24238\Lunar.seting.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.24238\Lunar.seting.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 3221225477 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
8 511
Read events
8 430
Write events
81
Delete events
0
Modification events
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\20PackPvpFac.rar | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
3
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.23007\20PackPvpFac.exe | executable | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.24238\20PackPvpFac.exe | executable | |
MD5:— | SHA256:— | |||
| 1836 | 20PackPvpFac.exe | C:\Users\admin\AppData\Local\Temp\TarF1DA.tmp | cat | |
MD5:— | SHA256:— | |||
| 1836 | 20PackPvpFac.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
| 1836 | 20PackPvpFac.exe | C:\Users\admin\AppData\Local\Temp\CabF1D9.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.24238\Lunar.seting.exe | executable | |
MD5:— | SHA256:— | |||
| 1836 | 20PackPvpFac.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2924 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2924.23007\Lunar.seting.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
4
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1836 | 20PackPvpFac.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com//json/82.118.29.68 | unknown | binary | 278 b | malicious |
3940 | Lunar.seting.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com//json/82.118.29.68 | unknown | binary | 278 b | malicious |
1836 | 20PackPvpFac.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?398237e9f1ef0b5b | US | compressed | 60.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1836 | 20PackPvpFac.exe | 23.128.64.141:443 | ip4.seeip.org | Joe's Datacenter, LLC | US | suspicious |
1836 | 20PackPvpFac.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
1836 | 20PackPvpFac.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3940 | Lunar.seting.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
1836 | 20PackPvpFac.exe | 162.159.137.232:443 | discord.com | Cloudflare Inc | — | malicious |
3940 | Lunar.seting.exe | 23.128.64.141:443 | ip4.seeip.org | Joe's Datacenter, LLC | US | suspicious |
3940 | Lunar.seting.exe | 162.159.137.232:443 | discord.com | Cloudflare Inc | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip4.seeip.org |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ip-api.com |
| malicious |
discord.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1836 | 20PackPvpFac.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
1836 | 20PackPvpFac.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1836 | 20PackPvpFac.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
3940 | Lunar.seting.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
3940 | Lunar.seting.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3940 | Lunar.seting.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2 ETPRO signatures available at the full report