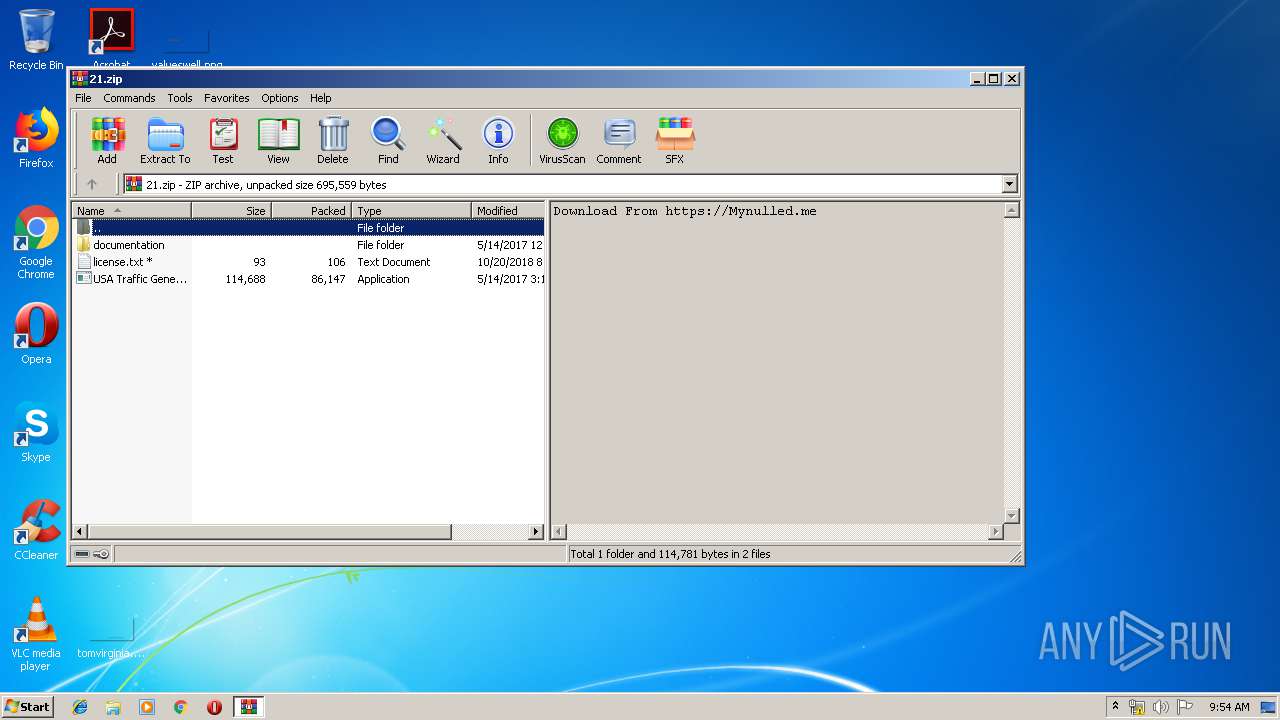
| File name: | 21.zip |
| Full analysis: | https://app.any.run/tasks/fe46ac72-b4c5-4637-9499-597e61f72143 |
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2019, 08:53:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 2AFF2E35AB502C164C57F92BD66A4A31 |
| SHA1: | 400873F8B2651A2807D26F682CCAD97539E605E0 |
| SHA256: | 31171E11E99066088BC2A7C5EE4C8D1AA1FD0EACAFBFD542A39C2ADBB8E4C553 |
| SSDEEP: | 12288:cjkytEmpWSliE6f+6MzhHqrhNstSPJsZZEy41PN4lsp:+kytEmp9l826GHChxOEXPNUC |
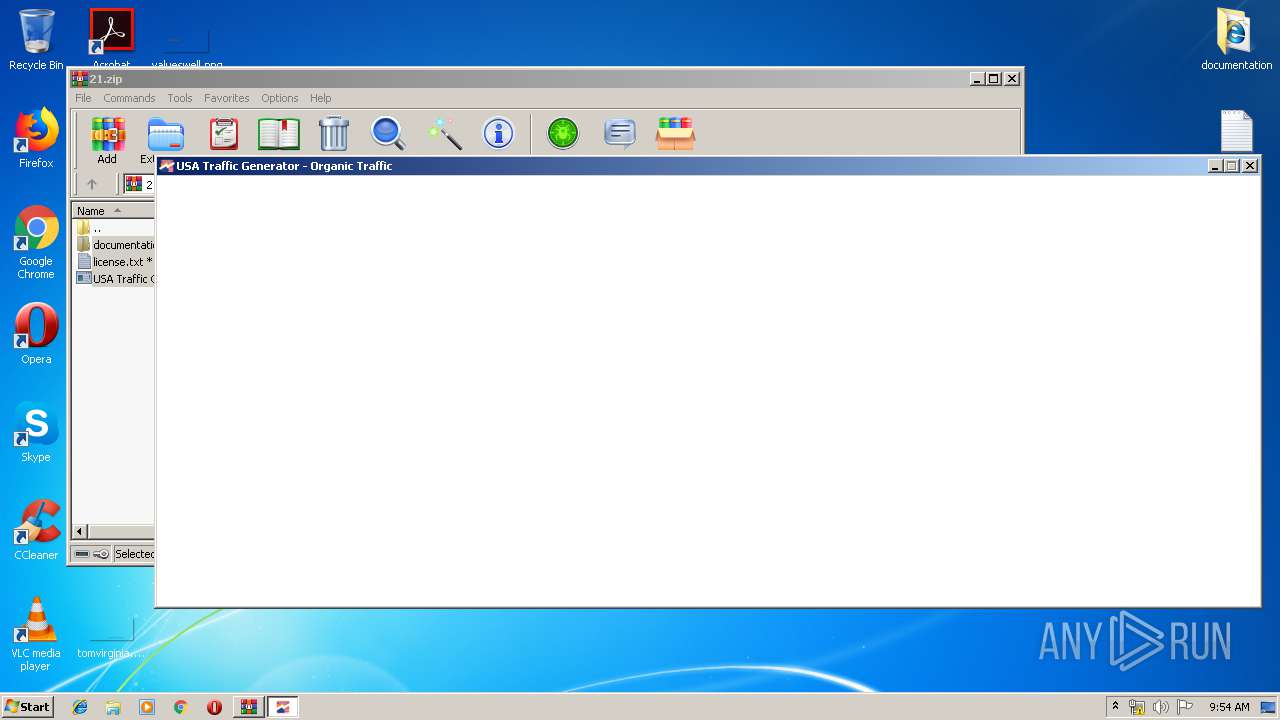
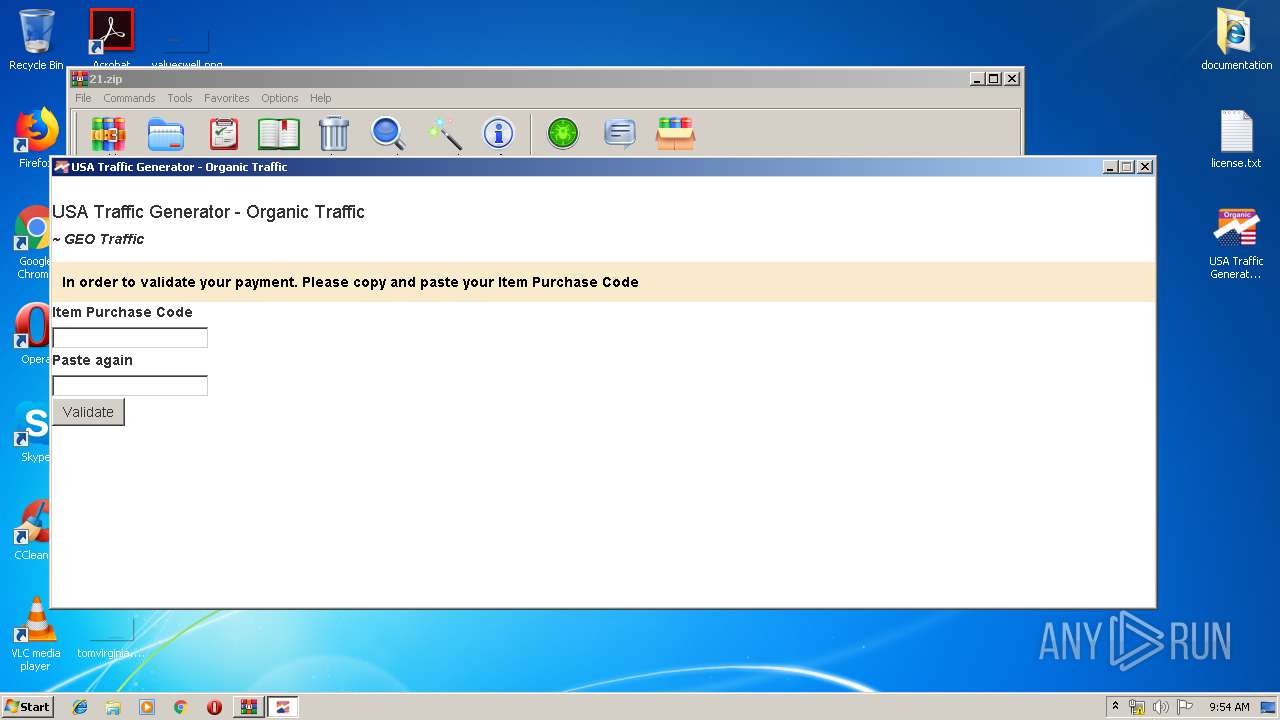
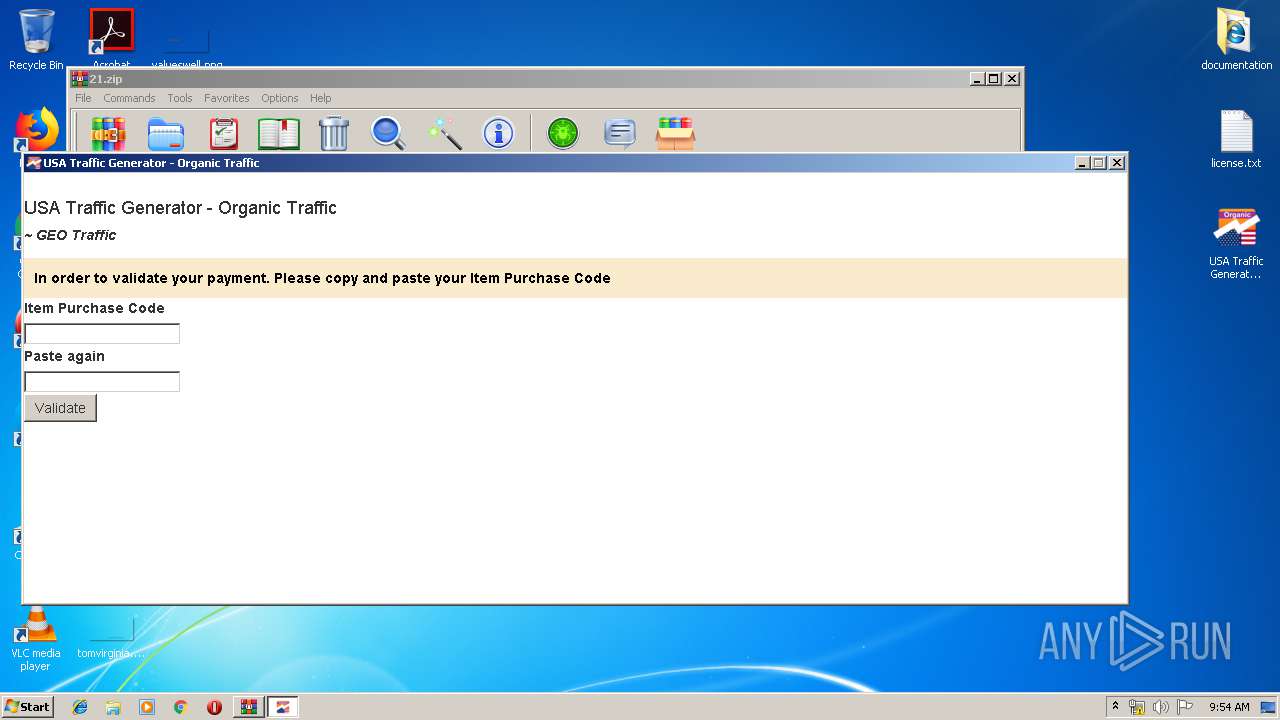
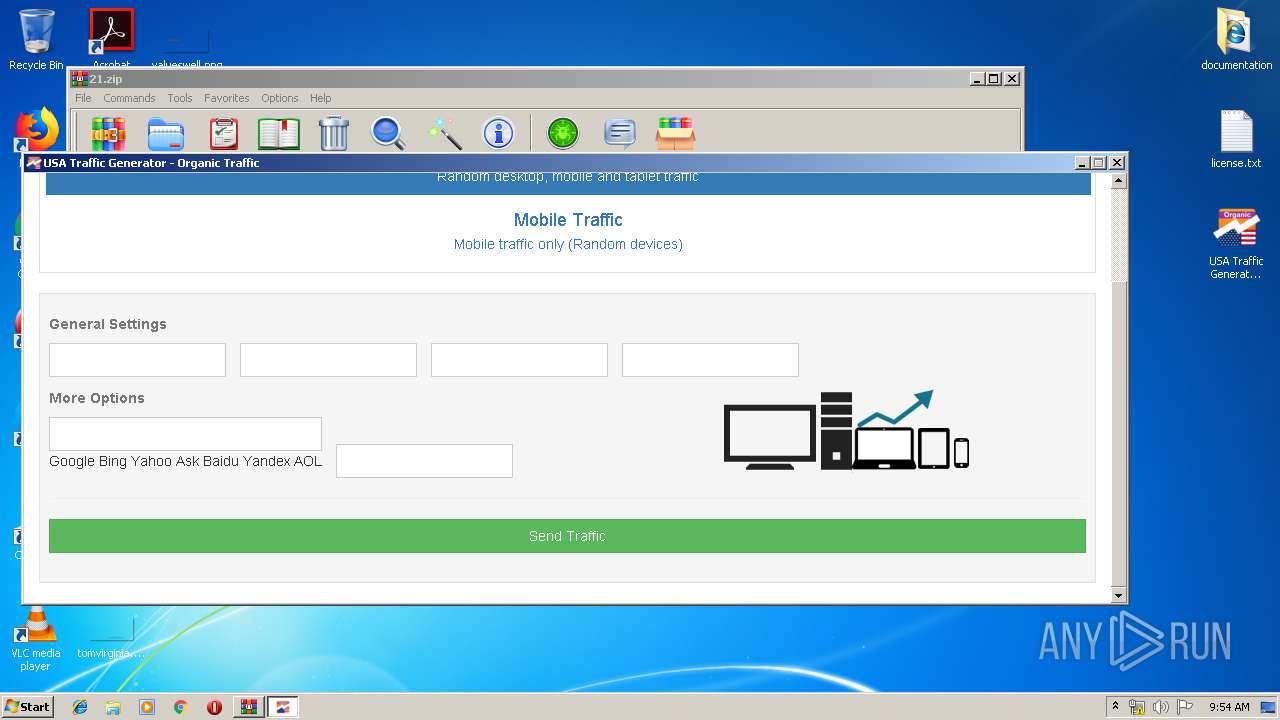
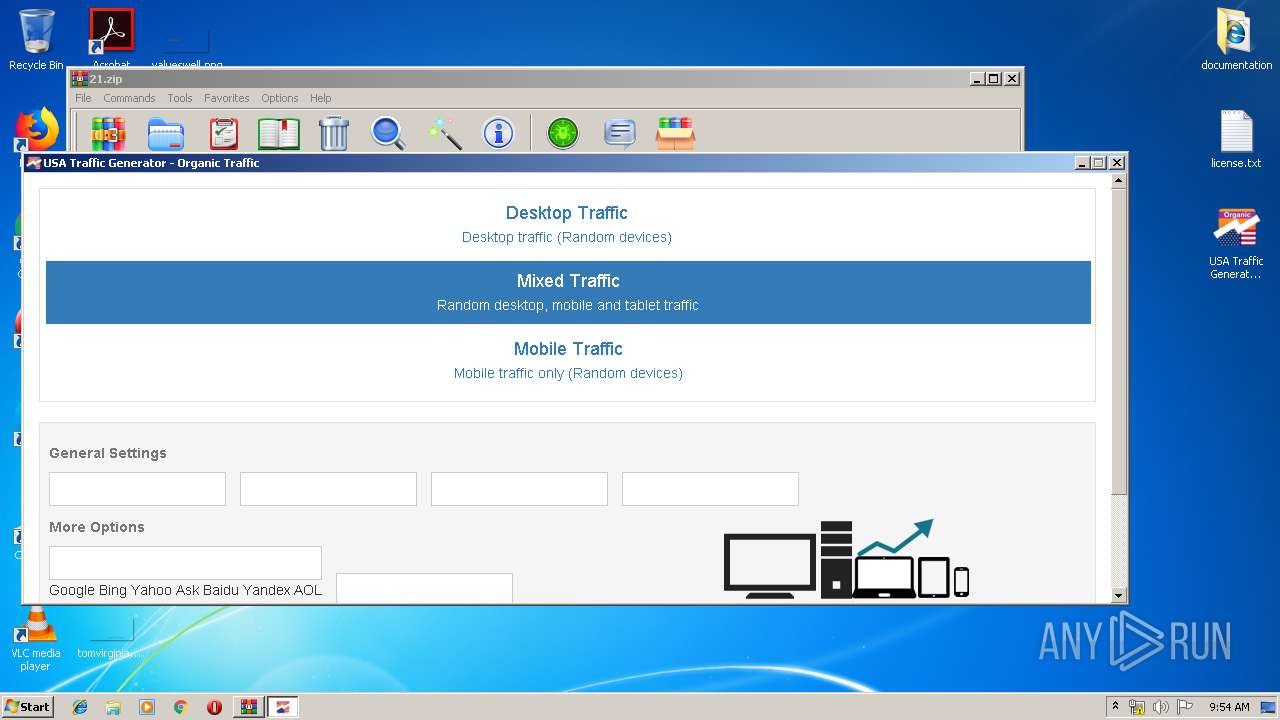
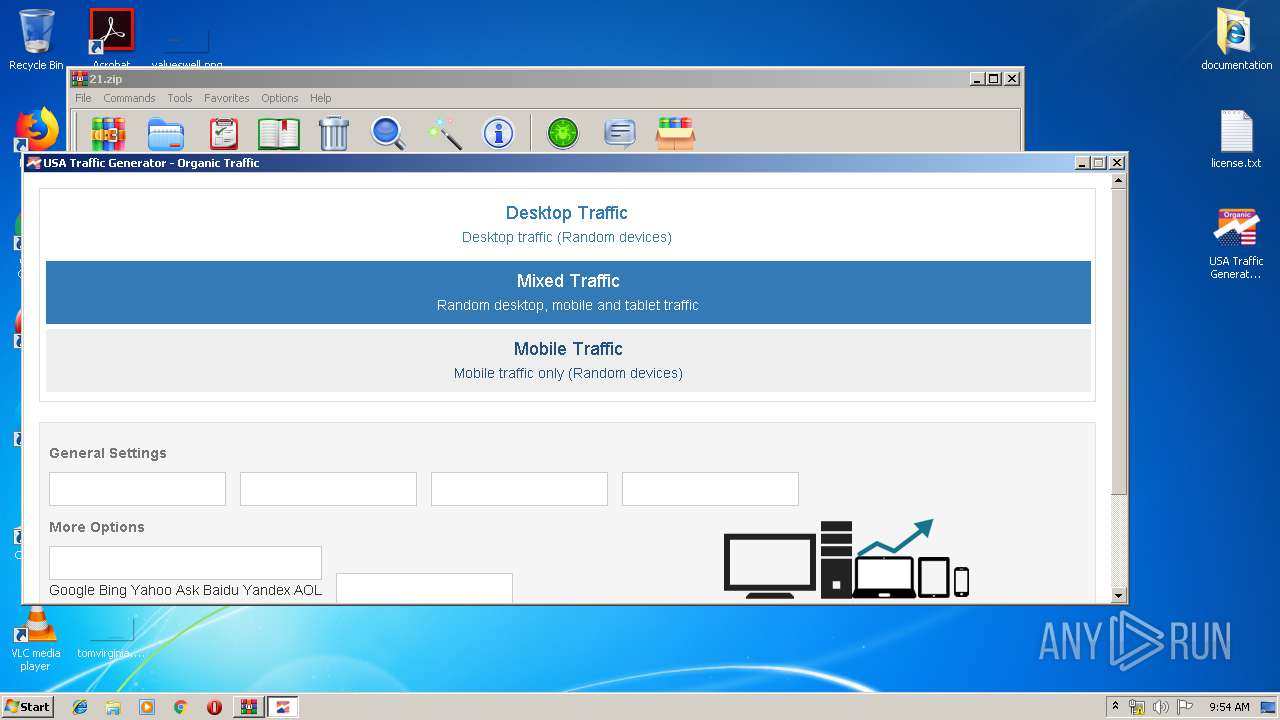
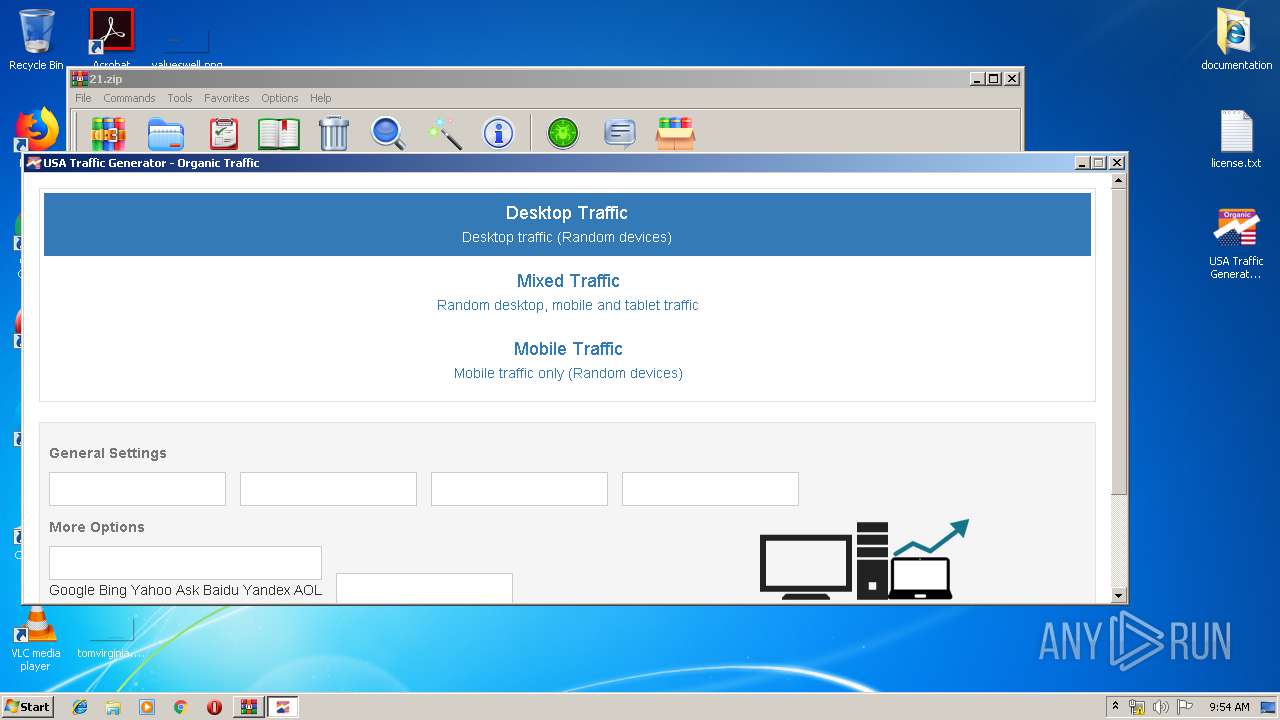
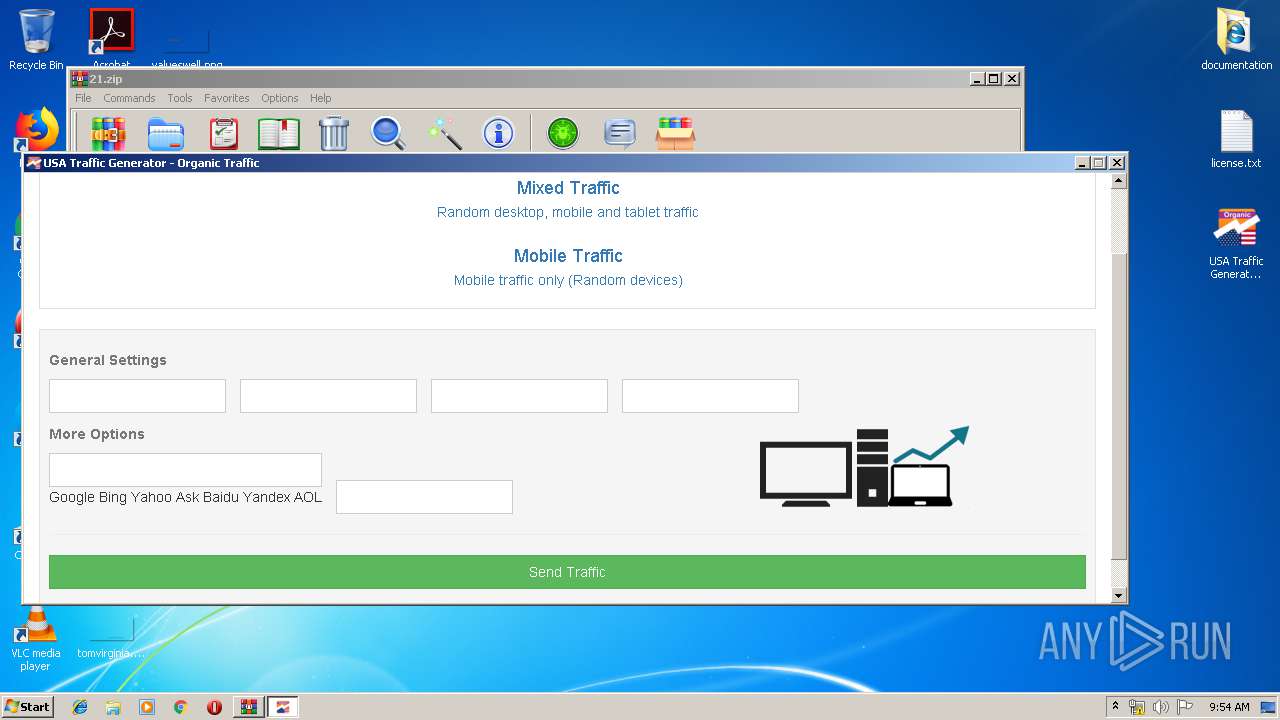
MALICIOUS
Application was dropped or rewritten from another process
- USA Traffic Generator - Organic Traffic.exe (PID: 3140)
Changes settings of System certificates
- USA Traffic Generator - Organic Traffic.exe (PID: 3140)
SUSPICIOUS
Reads internet explorer settings
- USA Traffic Generator - Organic Traffic.exe (PID: 3140)
Reads Internet Cache Settings
- USA Traffic Generator - Organic Traffic.exe (PID: 3140)
Adds / modifies Windows certificates
- USA Traffic Generator - Organic Traffic.exe (PID: 3140)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .maff | | | Mozilla Archive Format (gen) (63.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (36.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2017:05:14 18:13:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | documentation/ |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
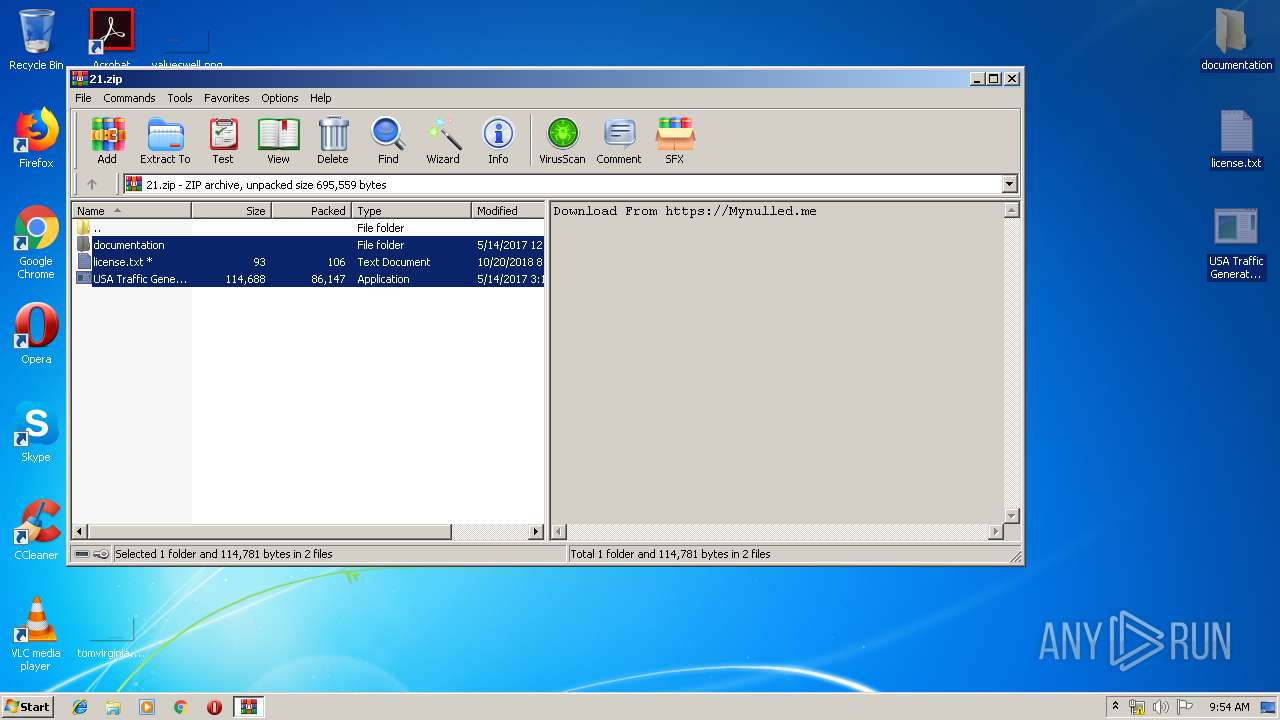
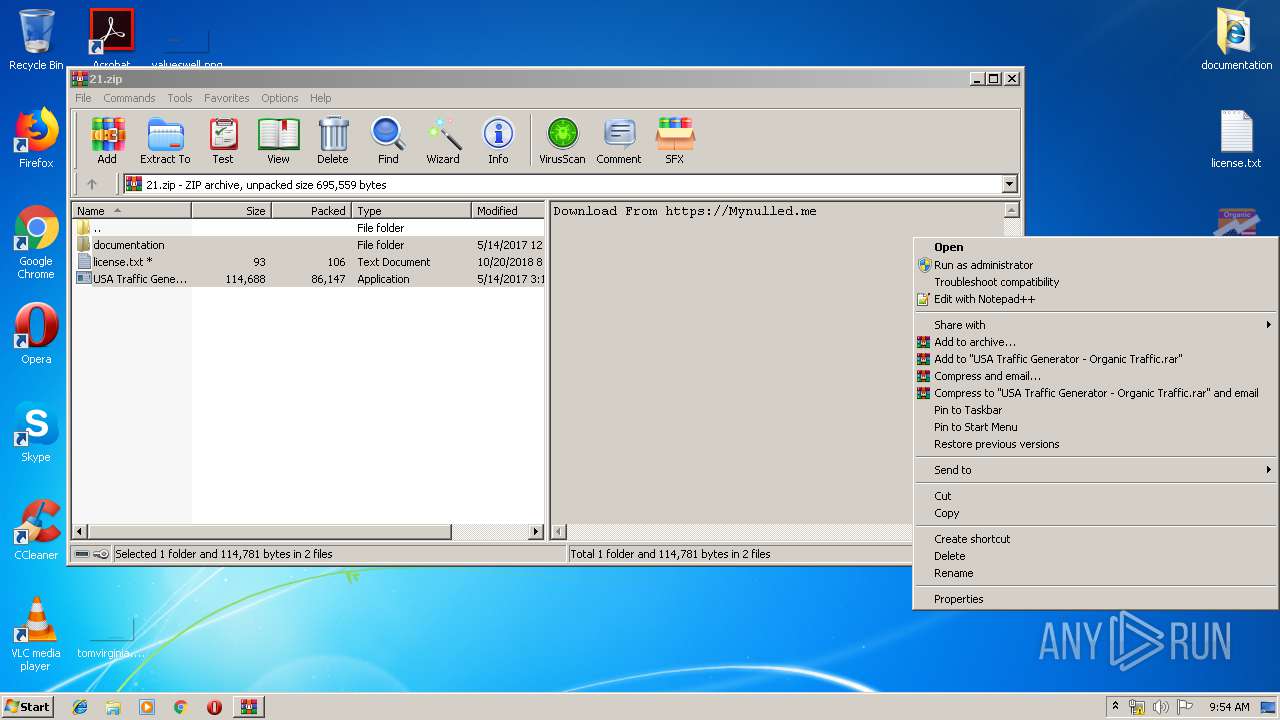
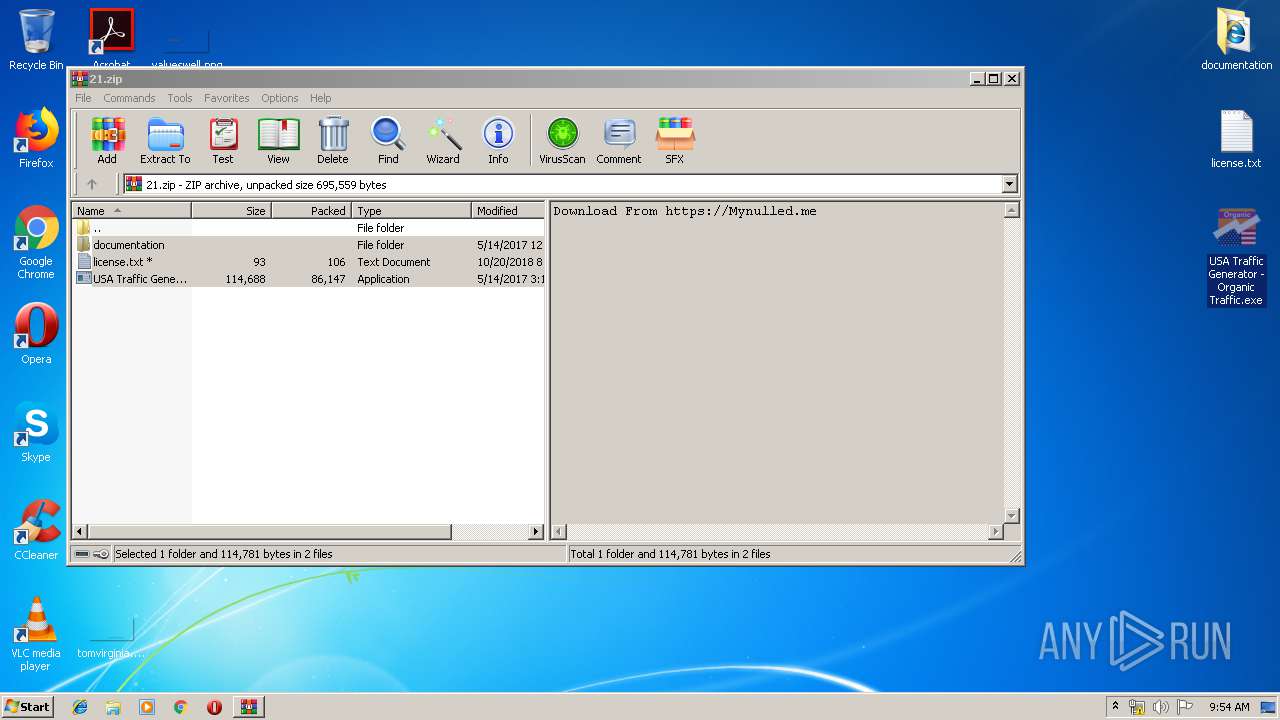
| 2188 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\21.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
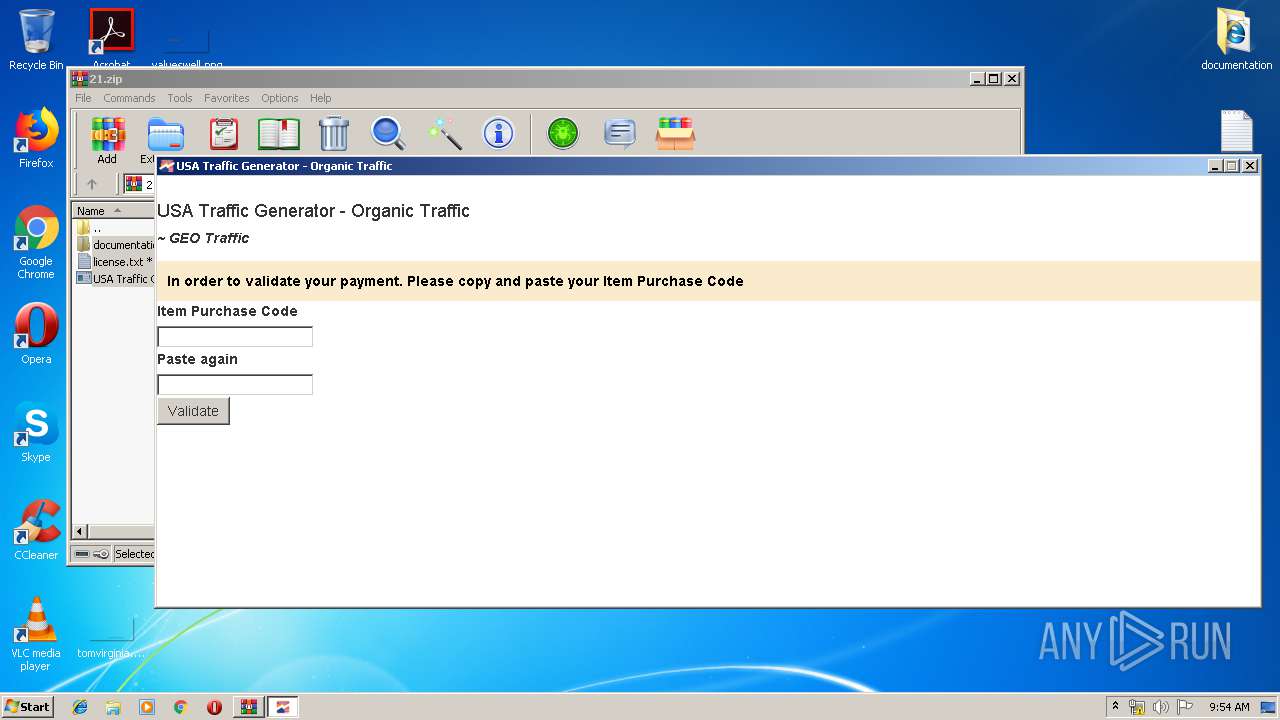
| 3140 | "C:\Users\admin\Desktop\USA Traffic Generator - Organic Traffic.exe" | C:\Users\admin\Desktop\USA Traffic Generator - Organic Traffic.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: BotOrganicUSA Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
607
Read events
559
Write events
48
Delete events
0
Modification events
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\21.zip | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
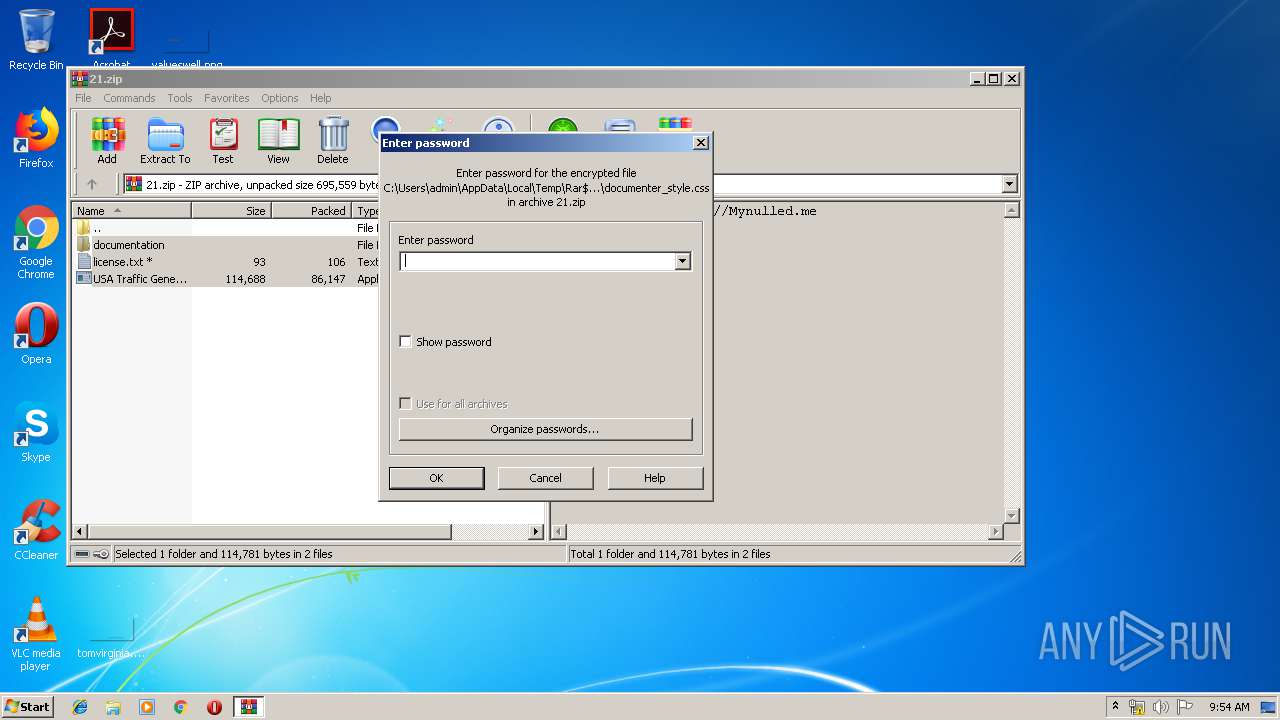
| (PID) Process: | (2188) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\css\documenter_style.css | — | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\css\img\info.png | — | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\css\img\warning.png | — | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\images\image_1.png | — | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\images\image_2.png | — | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\images\image_3.png | — | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\images\image_4.gif | — | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\images\image_5.png | — | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\images\image_6.png | — | |
MD5:— | SHA256:— | |||
| 2188 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2188.15906\documentation\assets\images\image_7.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
5
DNS requests
2
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
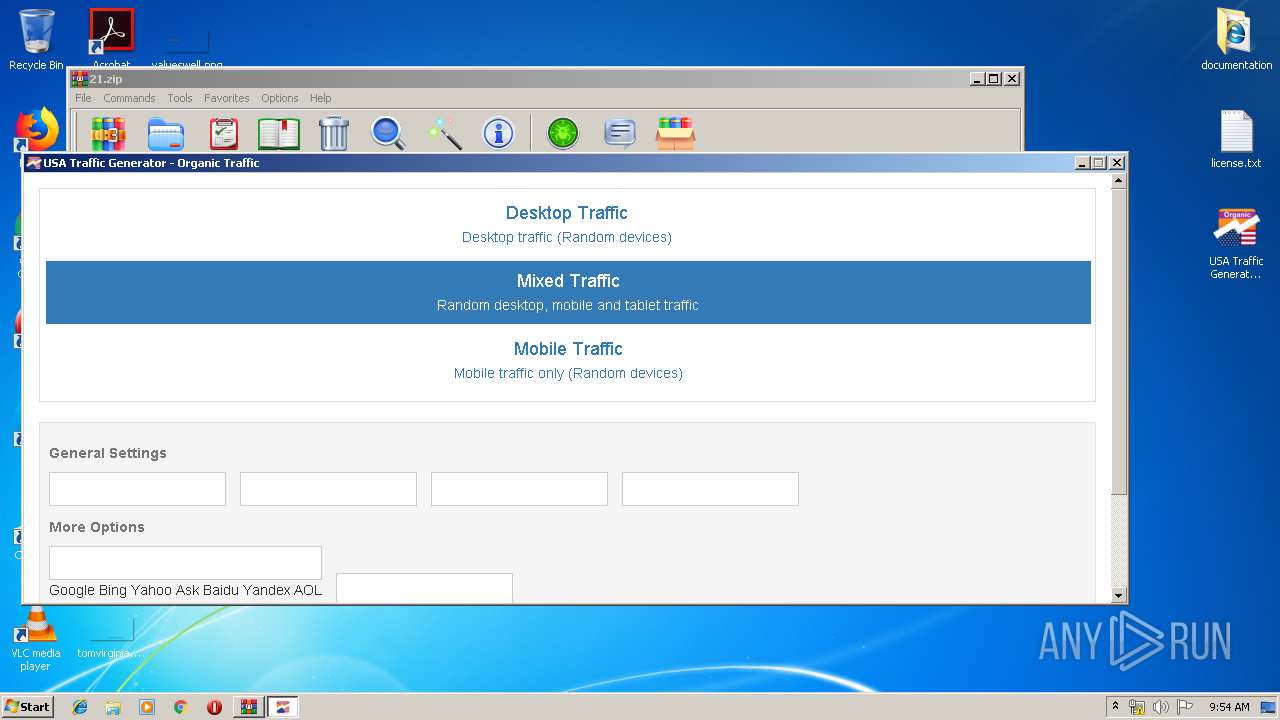
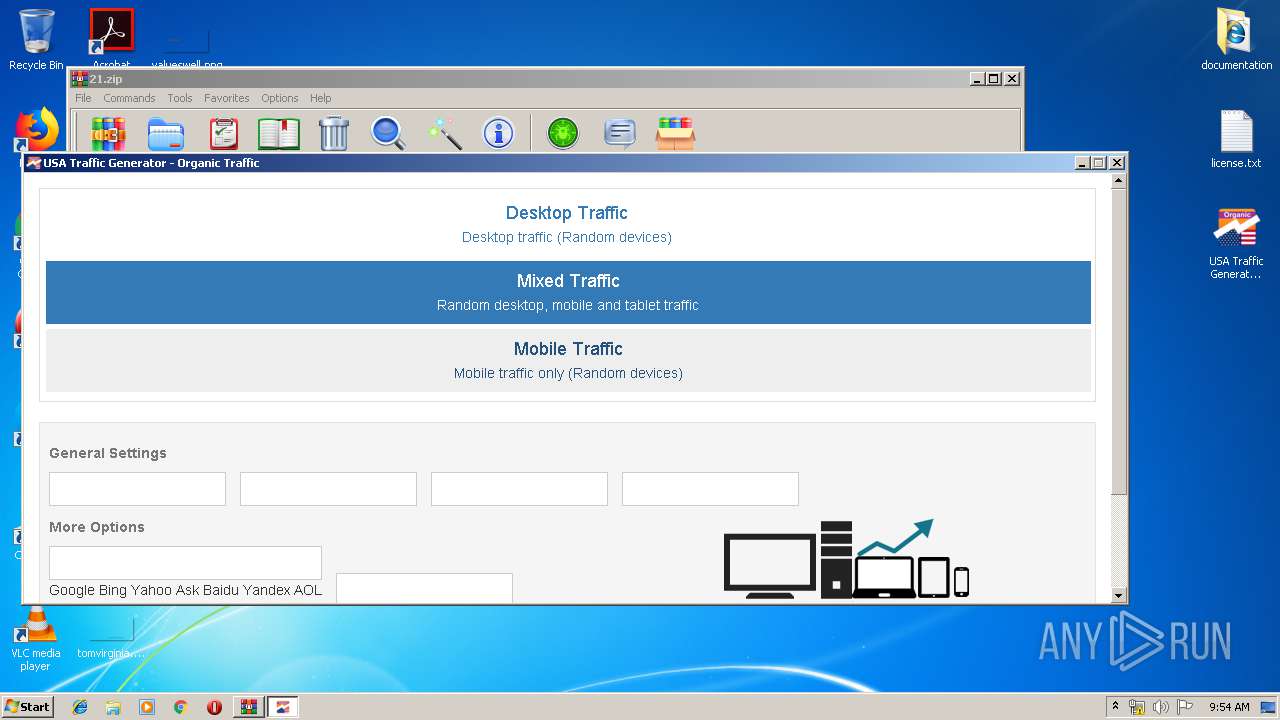
3140 | USA Traffic Generator - Organic Traffic.exe | POST | 302 | 64.37.62.88:80 | http://bunkerlatam.club/countries/organic/organicbasicus/ | US | html | 927 b | suspicious |
3140 | USA Traffic Generator - Organic Traffic.exe | POST | 200 | 64.37.62.88:80 | http://bunkerlatam.club/countries/organic/organicbasicus/pctraffic.php | US | — | — | suspicious |
3140 | USA Traffic Generator - Organic Traffic.exe | GET | 200 | 64.37.62.88:80 | http://bunkerlatam.club/countries/organic/organicbasicus/imgs/sprites.png | US | image | 2.31 Kb | suspicious |
3140 | USA Traffic Generator - Organic Traffic.exe | GET | 200 | 64.37.62.88:80 | http://bunkerlatam.club/countries/organic/organicbasicus/js/bootstrap.min.js | US | text | 11.6 Kb | suspicious |
3140 | USA Traffic Generator - Organic Traffic.exe | GET | 200 | 64.37.62.88:80 | http://bunkerlatam.club/countries/organic/organicbasicus/ | US | html | 927 b | suspicious |
3140 | USA Traffic Generator - Organic Traffic.exe | GET | 200 | 64.37.62.88:80 | http://bunkerlatam.club/countries/organic/organicbasicus/fonts/glyphicons-halflings-regular.eot? | US | eot | 19.6 Kb | suspicious |
3140 | USA Traffic Generator - Organic Traffic.exe | GET | 200 | 64.37.62.88:80 | http://bunkerlatam.club/countries/organic/organicbasicus/css/bootstrap.min.css | US | text | 24.6 Kb | suspicious |
3140 | USA Traffic Generator - Organic Traffic.exe | GET | 200 | 64.37.62.88:80 | http://bunkerlatam.club/countries/organic/organicbasicus/admin.php | US | html | 2.22 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3140 | USA Traffic Generator - Organic Traffic.exe | 172.217.22.106:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3140 | USA Traffic Generator - Organic Traffic.exe | 64.37.62.88:80 | bunkerlatam.club | HostDime.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bunkerlatam.club |
| suspicious |
ajax.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3140 | USA Traffic Generator - Organic Traffic.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |