| File name: | Worm.Klez.E.exe |
| Full analysis: | https://app.any.run/tasks/ef2e4ac1-e95a-4011-92d8-d15a567185ad |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 16:24:46 |
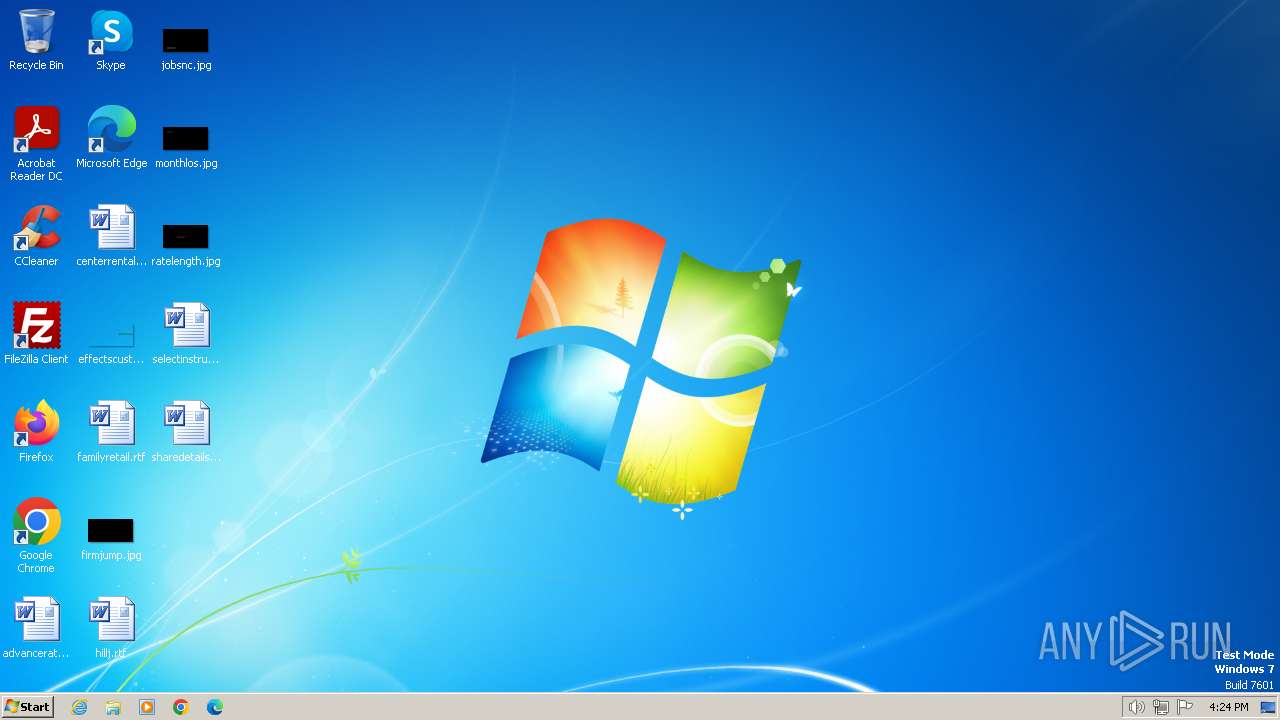
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F2DB87B351770E5995E9FCAAD47D9591 |
| SHA1: | 4C75BD93F458096FBC27FA852E16CE25A602F267 |
| SHA256: | 3113FA9A3CF00ED423A2C686A2FFB19586F6A047747DE65A93436A7DCA8FCFA7 |
| SSDEEP: | 768:zXS6Lnze1gshn5ew/QuBdL/4Ckir4SWeq3HwFdkt+Afs2DBnoLK6KcgMvtDv:TSSnze1gsJ55n/4CkOwwF+bho0stD |
MALICIOUS
Drops the executable file immediately after the start
- Worm.Klez.E.exe (PID: 4052)
- Worm.Klez.E.exe (PID: 2572)
- Winkxa.exe (PID: 2692)
Creates a writable file in the system directory
- Worm.Klez.E.exe (PID: 2572)
SUSPICIOUS
Executes as Windows Service
- Winkxa.exe (PID: 2692)
Executable content was dropped or overwritten
- Worm.Klez.E.exe (PID: 2572)
- Winkxa.exe (PID: 2692)
Process drops legitimate windows executable
- Winkxa.exe (PID: 2692)
Detected use of alternative data streams (AltDS)
- Winkxa.exe (PID: 2692)
INFO
Checks supported languages
- Worm.Klez.E.exe (PID: 4052)
- Worm.Klez.E.exe (PID: 2572)
- Winkxa.exe (PID: 2692)
Reads the computer name
- Worm.Klez.E.exe (PID: 2572)
- Worm.Klez.E.exe (PID: 4052)
- Winkxa.exe (PID: 2692)
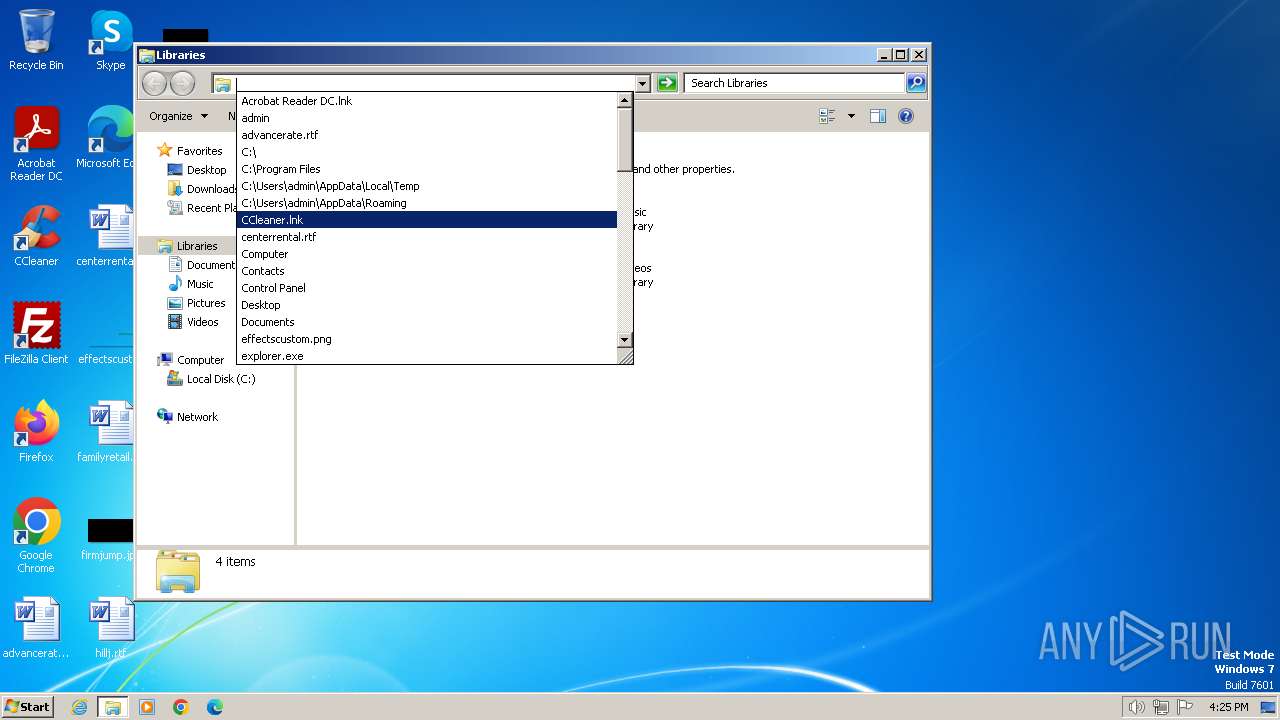
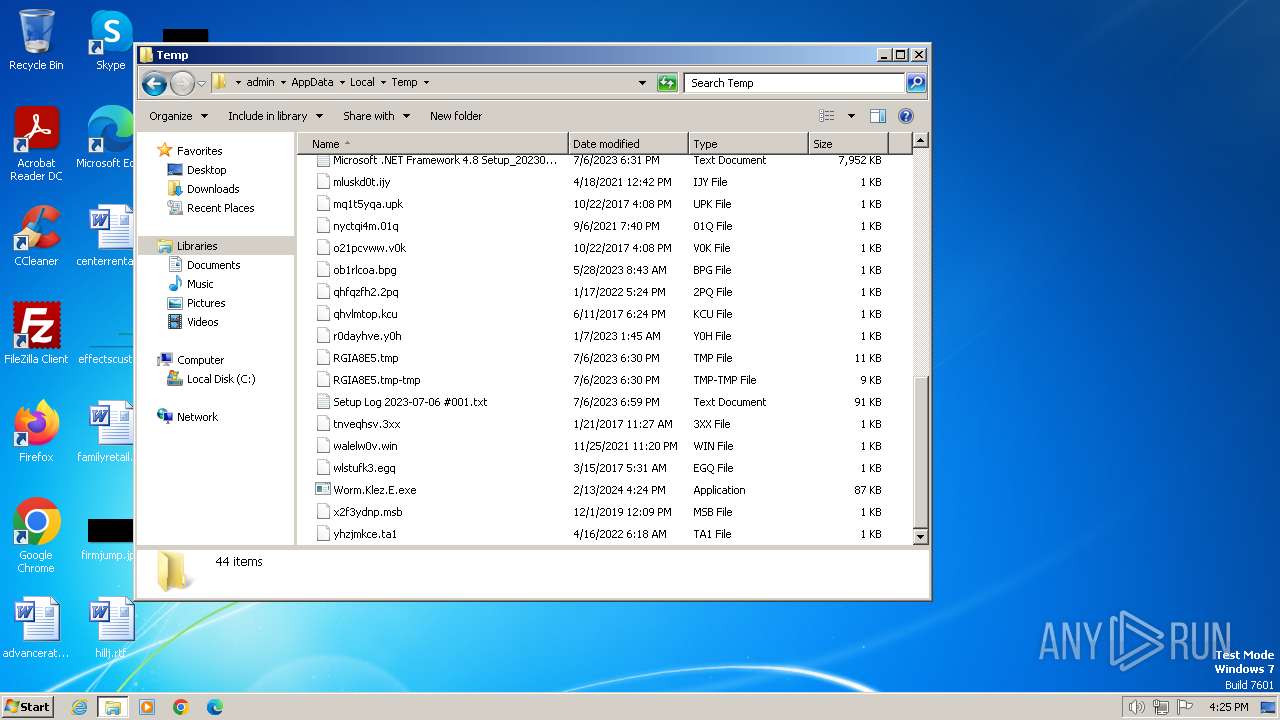
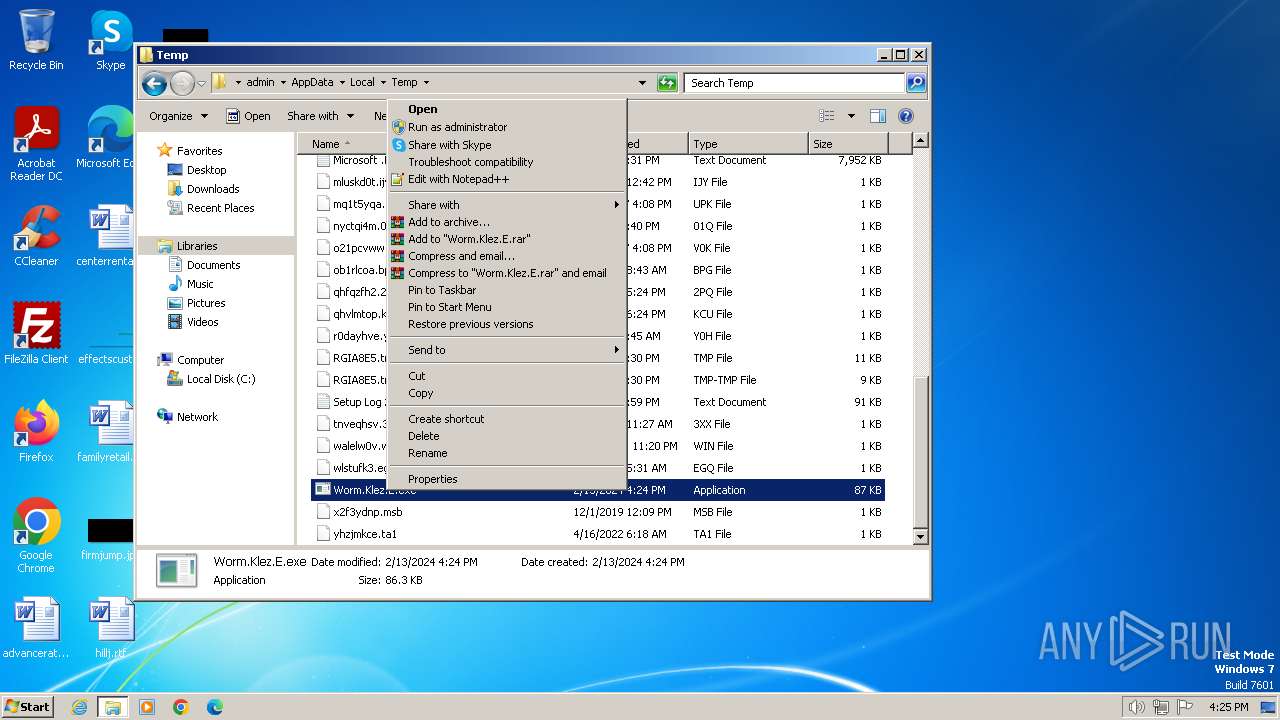
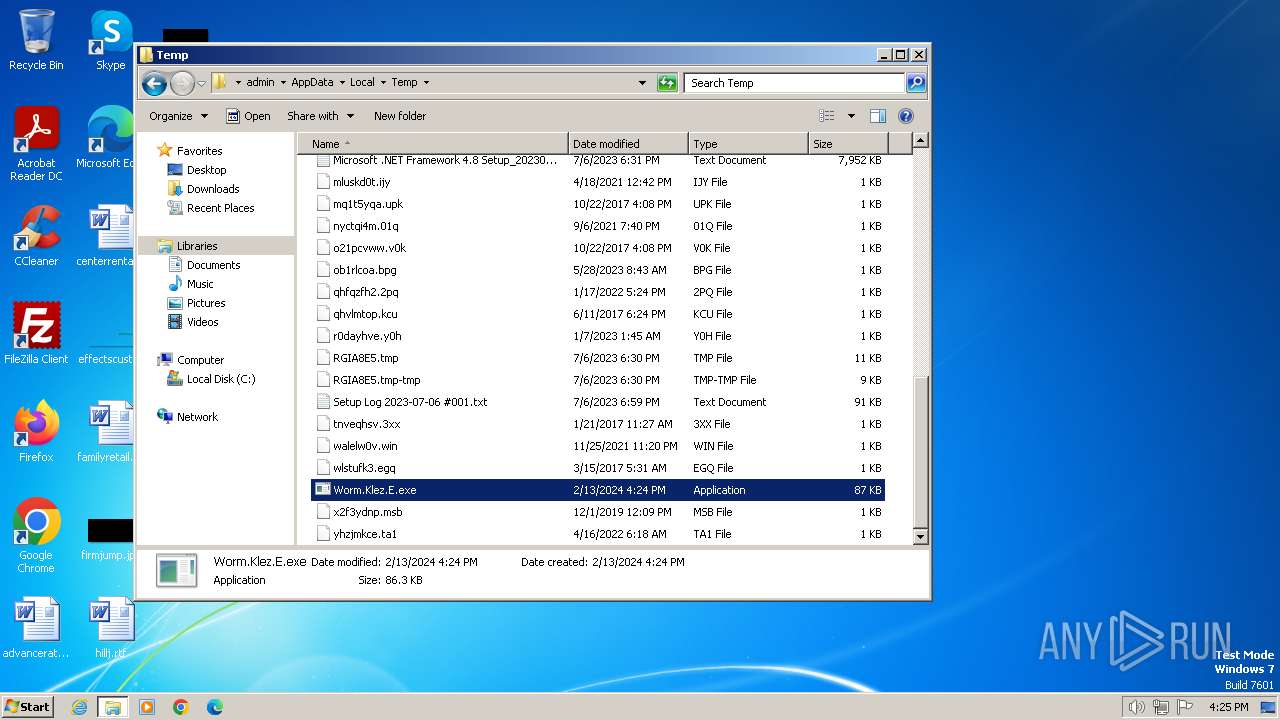
Manual execution by a user
- explorer.exe (PID: 2920)
- Worm.Klez.E.exe (PID: 2572)
Checks proxy server information
- Winkxa.exe (PID: 2692)
Creates files in the program directory
- Winkxa.exe (PID: 2692)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2002:01:14 08:44:12+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 49152 |
| InitializedDataSize: | 557056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8078 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
43
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
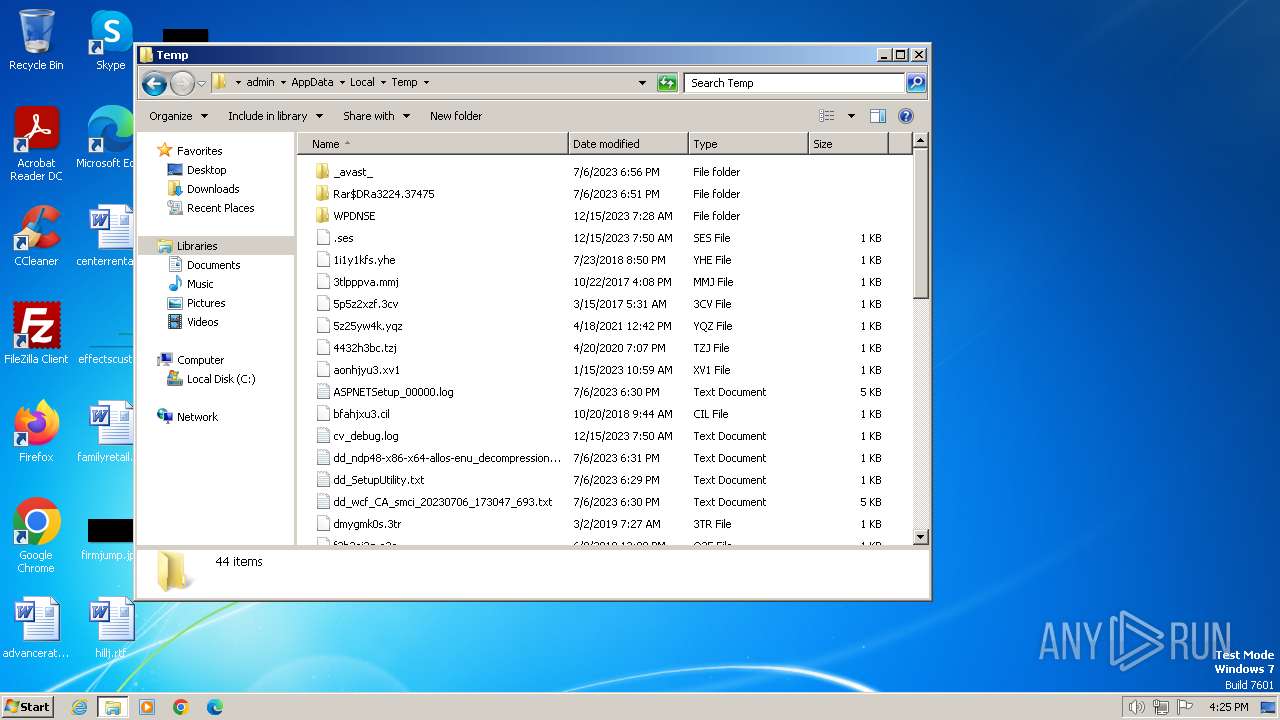
| 2572 | "C:\Users\admin\AppData\Local\Temp\Worm.Klez.E.exe" | C:\Users\admin\AppData\Local\Temp\Worm.Klez.E.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2692 | C:\Windows\system32\Winkxa.exe | C:\Windows\System32\Winkxa.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2920 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4052 | "C:\Users\admin\AppData\Local\Temp\Worm.Klez.E.exe" | C:\Users\admin\AppData\Local\Temp\Worm.Klez.E.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
826
Read events
820
Write events
2
Delete events
4
Modification events
| (PID) Process: | (2692) Winkxa.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2692) Winkxa.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
| (PID) Process: | (2692) Winkxa.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyOverride |
Value: | |||
| (PID) Process: | (2692) Winkxa.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoConfigURL |
Value: | |||
| (PID) Process: | (2692) Winkxa.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | AutoDetect |
Value: | |||
| (PID) Process: | (2692) Winkxa.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000000A00000009000000000000000000000000000000040000000000000000000000000000000000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
23
Suspicious files
8
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2692 | Winkxa.exe | C:\Windows\TEMP\Yay55BF.exe | executable | |
MD5:77710E343790592355AAE4BCBD6EDFC5 | SHA256:A43F27686754294207B3AC3EA0B65648B6A7C4C52BBEE95BF6EDD7AC7F713F9C | |||
| 2692 | Winkxa.exe | C:\Windows\TEMP\Asb5001.exe | executable | |
MD5:77710E343790592355AAE4BCBD6EDFC5 | SHA256:A43F27686754294207B3AC3EA0B65648B6A7C4C52BBEE95BF6EDD7AC7F713F9C | |||
| 2692 | Winkxa.exe | C:\Windows\TEMP\Fr5A06.exe | executable | |
MD5:77710E343790592355AAE4BCBD6EDFC5 | SHA256:A43F27686754294207B3AC3EA0B65648B6A7C4C52BBEE95BF6EDD7AC7F713F9C | |||
| 2692 | Winkxa.exe | C:\Windows\TEMP\Zu4FE1.exe | executable | |
MD5:77710E343790592355AAE4BCBD6EDFC5 | SHA256:A43F27686754294207B3AC3EA0B65648B6A7C4C52BBEE95BF6EDD7AC7F713F9C | |||
| 2692 | Winkxa.exe | C:\Windows\TEMP\Az4FD0.exe | executable | |
MD5:E0A651C8A307C75B988988FDBECCAA99 | SHA256:D407C242B0808C1FB09A3675F61880DA3E80D0805EF39EDC41B500F46F216E41 | |||
| 2692 | Winkxa.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.ynf | binary | |
MD5:34082166B7D60F7BA4FF1BBE6EFCD332 | SHA256:F40CE708B380EBC8DE3F590A574CD829C8F3F6C275B651612C2CE8F47CEA1186 | |||
| 2692 | Winkxa.exe | binary | ||
MD5:— | SHA256:— | |||
| 2572 | Worm.Klez.E.exe | C:\Windows\system32\Winkxa.exe | executable | |
MD5:F2DB87B351770E5995E9FCAAD47D9591 | SHA256:3113FA9A3CF00ED423A2C686A2FFB19586F6A047747DE65A93436A7DCA8FCFA7 | |||
| 2692 | Winkxa.exe | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | executable | |
MD5:EC2002A5F6A7FD75FDFF790B8788A757 | SHA256:DF123CA72BA8A96CB4939F9043E9EE6FCD83A52C2E00FE820BD7579AB8F1C1E6 | |||
| 2692 | Winkxa.exe | C:\Windows\TEMP\Vkr8203.exe | executable | |
MD5:77710E343790592355AAE4BCBD6EDFC5 | SHA256:A43F27686754294207B3AC3EA0B65648B6A7C4C52BBEE95BF6EDD7AC7F713F9C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |