| File name: | è°·æå®è£ å _19.25.13.exe |
| Full analysis: | https://app.any.run/tasks/949c7cd8-27fe-41e5-9793-b86a0dad7cfc |
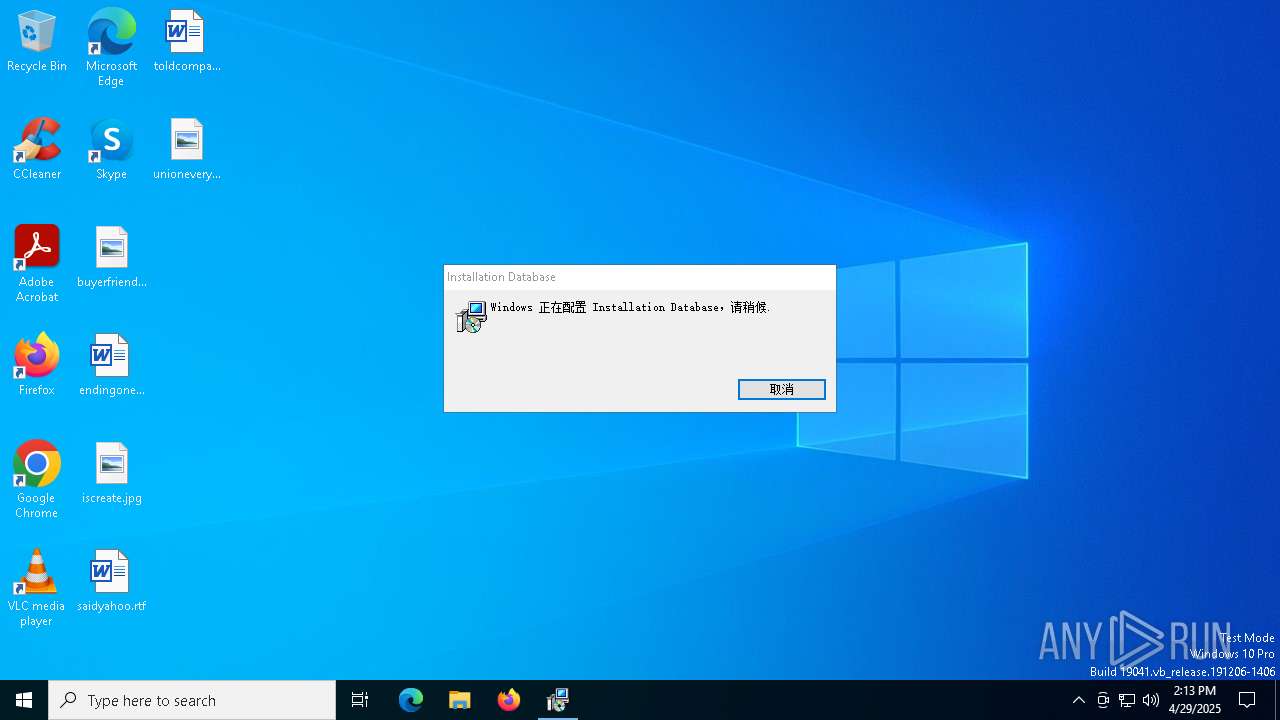
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 14:12:55 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 312774722B2A953142E3D39C464FA9DF |
| SHA1: | 8F97BD42B627D1AAE74C775E78E05D85BD31B4AE |
| SHA256: | 30F1434C85FCBFB70B8C294460EE2F7368F4FF1AEBFB85E06AAC5ED3D5046C47 |
| SSDEEP: | 786432:VCkdXcQjbQerCh1ies8DJsQ+4rjpGuZFOazORU:VCicQjbQACh1ie7DJsr4rjMuZFDzO+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
ADVANCEDINSTALLER mutex has been found
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
Reads the Windows owner or organization settings
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
Process drops legitimate windows executable
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
Executable content was dropped or overwritten
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
Executes as Windows Service
- VSSVC.exe (PID: 2852)
There is functionality for taking screenshot (YARA)
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
Detects AdvancedInstaller (YARA)
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
INFO
The sample compiled with chinese language support
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
Checks supported languages
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
- msiexec.exe (PID: 3240)
- msiexec.exe (PID: 1020)
Reads the computer name
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
- msiexec.exe (PID: 1020)
- msiexec.exe (PID: 3240)
Reads Environment values
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
Create files in a temporary directory
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
The sample compiled with english language support
- è°·æå®è£ å _19.25.13.exe (PID: 1660)
Manages system restore points
- SrTasks.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:05:31 13:15:01+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.36 |
| CodeSize: | 2484736 |
| InitializedDataSize: | 945664 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d6f94 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Debug |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | TargetCommandSwiftUI |
| FileDescription: | Installation Database Installer |
| FileVersion: | 1.0.0 |
| InternalName: | 转接口 |
| LegalCopyright: | Copyright (C) 2025 TargetCommandSwiftUI |
| OriginalFileName: | 转接口.exe |
| ProductName: | Installation Database |
| ProductVersion: | 1.0.0 |
Total processes
137
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Users\admin\AppData\Local\Temp\è°·æå®è£ å _19.25.13.exe" | C:\Users\admin\AppData\Local\Temp\è°·æå®è£ å _19.25.13.exe | — | explorer.exe | |||||||||||
User: admin Company: TargetCommandSwiftUI Integrity Level: MEDIUM Description: Installation Database Installer Exit code: 3221226540 Version: 1.0.0 Modules
| |||||||||||||||
| 1020 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Users\admin\AppData\Local\Temp\è°·æå®è£ å _19.25.13.exe" | C:\Users\admin\AppData\Local\Temp\è°·æå®è£ å _19.25.13.exe | explorer.exe | ||||||||||||
User: admin Company: TargetCommandSwiftUI Integrity Level: HIGH Description: Installation Database Installer Exit code: 1602 Version: 1.0.0 Modules
| |||||||||||||||
| 2560 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2852 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3240 | C:\Windows\syswow64\MsiExec.exe -Embedding 4364393A5D7A0ADDCDA4457D11EE8ADD C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4464 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5376 | "C:\WINDOWS\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\TargetCommandSwiftUI\Installation Database 1.0.0\install\5DE3BAC\转接口.msi" AI_SETUPEXEPATH=C:\Users\admin\AppData\Local\Temp\è°·æå®è£ å _19.25.13.exe SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1745934891 " ALLUSERS="1" | C:\Windows\SysWOW64\msiexec.exe | — | è°·æå®è£ å _19.25.13.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 1602 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6136 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 301
Read events
2 122
Write events
167
Delete events
12
Modification events
| (PID) Process: | (1020) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000F2C7F0DA10B9DB01FC03000068080000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1020) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000F2C7F0DA10B9DB01FC03000068080000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1020) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000009596ADB10B9DB01FC03000068080000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1020) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000C7BC6CDB10B9DB01FC03000068080000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1020) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000DCF367DB10B9DB01FC03000068080000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1020) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000DCF367DB10B9DB01FC03000068080000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1020) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (1020) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000000C52FDDB10B9DB01FC0300003C0C0000E803000001000000000000000000000044E46E3FB0A11F40B146ACFA4734693A00000000000000000000000000000000 | |||
| (PID) Process: | (2852) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000044651DDC10B9DB01240B0000E8140000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2852) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 480000000000000044651DDC10B9DB01240B0000F8040000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1660 | è°·æå®è£ å _19.25.13.exe | C:\Users\admin\AppData\Roaming\TargetCommandSwiftUI\Installation Database 1.0.0\install\holder0.aiph | — | |
MD5:— | SHA256:— | |||
| 1660 | è°·æå®è£ å _19.25.13.exe | C:\Users\admin\AppData\Roaming\TargetCommandSwiftUI\Installation Database 1.0.0\install\5DE3BAC\转接口.msi | — | |
MD5:— | SHA256:— | |||
| 1020 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 1020 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:161C96DAABE041185FDC37B0605B830E | SHA256:E2C043E68A4AA242B7922A0F16630C1BD7FDE64979E62B6107472D3616FE644C | |||
| 1020 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{3f6ee444-a1b0-401f-b146-acfa4734693a}_OnDiskSnapshotProp | binary | |
MD5:161C96DAABE041185FDC37B0605B830E | SHA256:E2C043E68A4AA242B7922A0F16630C1BD7FDE64979E62B6107472D3616FE644C | |||
| 1660 | è°·æå®è£ å _19.25.13.exe | C:\Users\admin\AppData\Local\Temp\MSIDEAB.tmp | executable | |
MD5:C7FBD5EE98E32A77EDF1156DB3FCA622 | SHA256:E140990B509DD6884A5742BDE64F2CDAA10012D472B0B32DE43EBECBC83242B6 | |||
| 1660 | è°·æå®è£ å _19.25.13.exe | C:\Users\admin\AppData\Local\Temp\shiDE5C.tmp | executable | |
MD5:84A34BF3486F7B9B7035DB78D78BDD1E | SHA256:F85911C910B660E528D2CF291BAA40A92D09961996D6D84E7A53A7095C7CD96E | |||
| 1660 | è°·æå®è£ å _19.25.13.exe | C:\Users\admin\AppData\Local\Temp\MSIDFE5.tmp | executable | |
MD5:AE463676775A1DD0B7A28DDB265B4065 | SHA256:83FBFCAFF3DA3EB89F9AEC29E6574CF15502FD670CBB2AB0C8A84451B2598B22 | |||
| 1660 | è°·æå®è£ å _19.25.13.exe | C:\Users\admin\AppData\Local\Temp\MSIDFC5.tmp | executable | |
MD5:C7FBD5EE98E32A77EDF1156DB3FCA622 | SHA256:E140990B509DD6884A5742BDE64F2CDAA10012D472B0B32DE43EBECBC83242B6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
29
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6576 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6576 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.69:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6576 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |