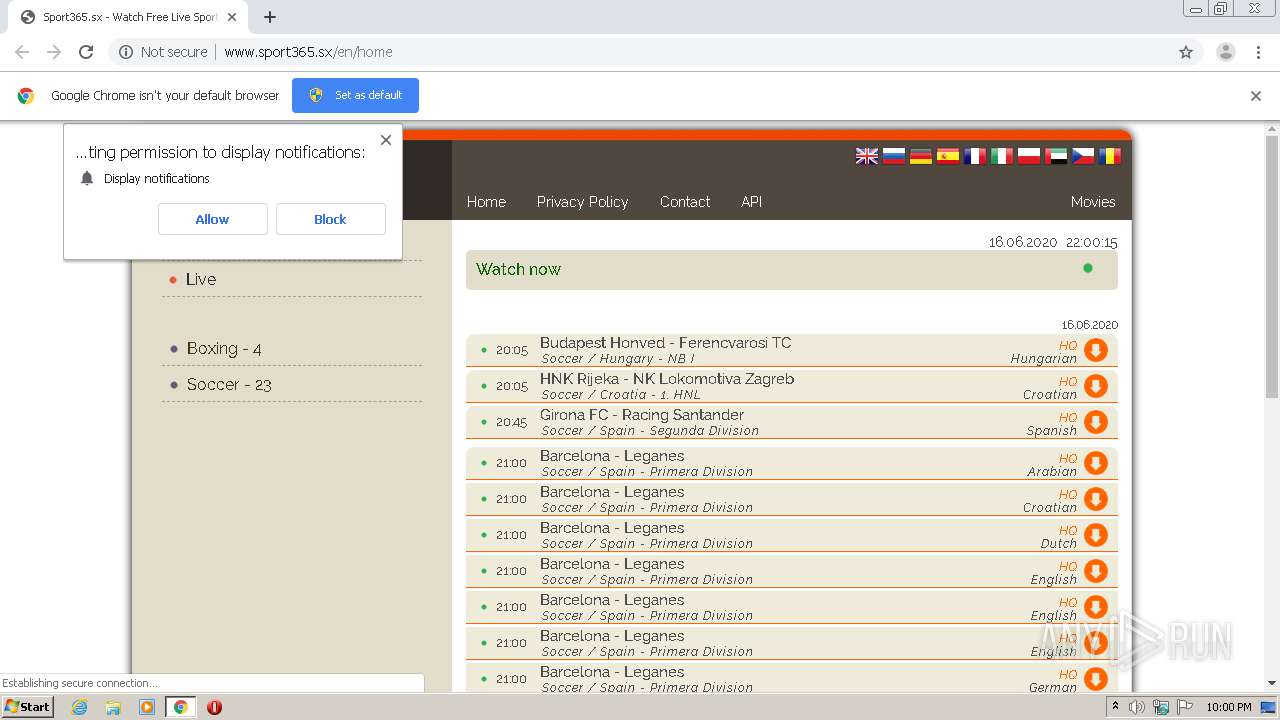
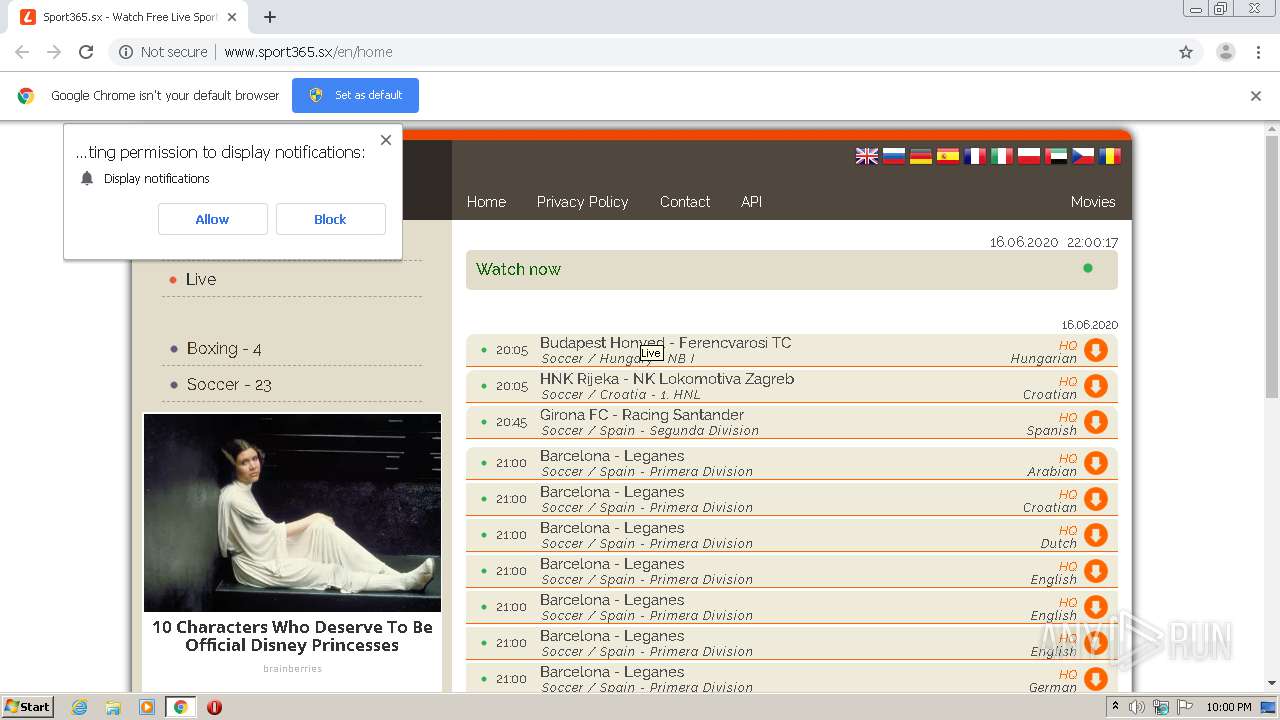
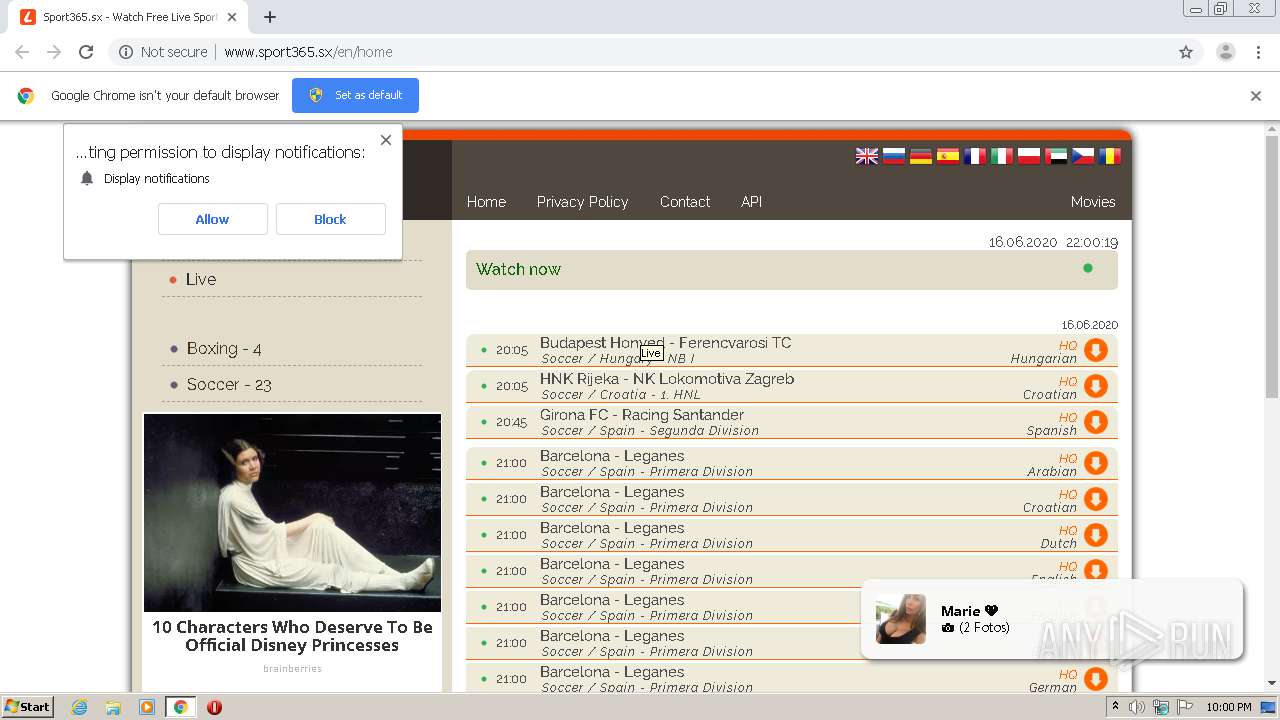
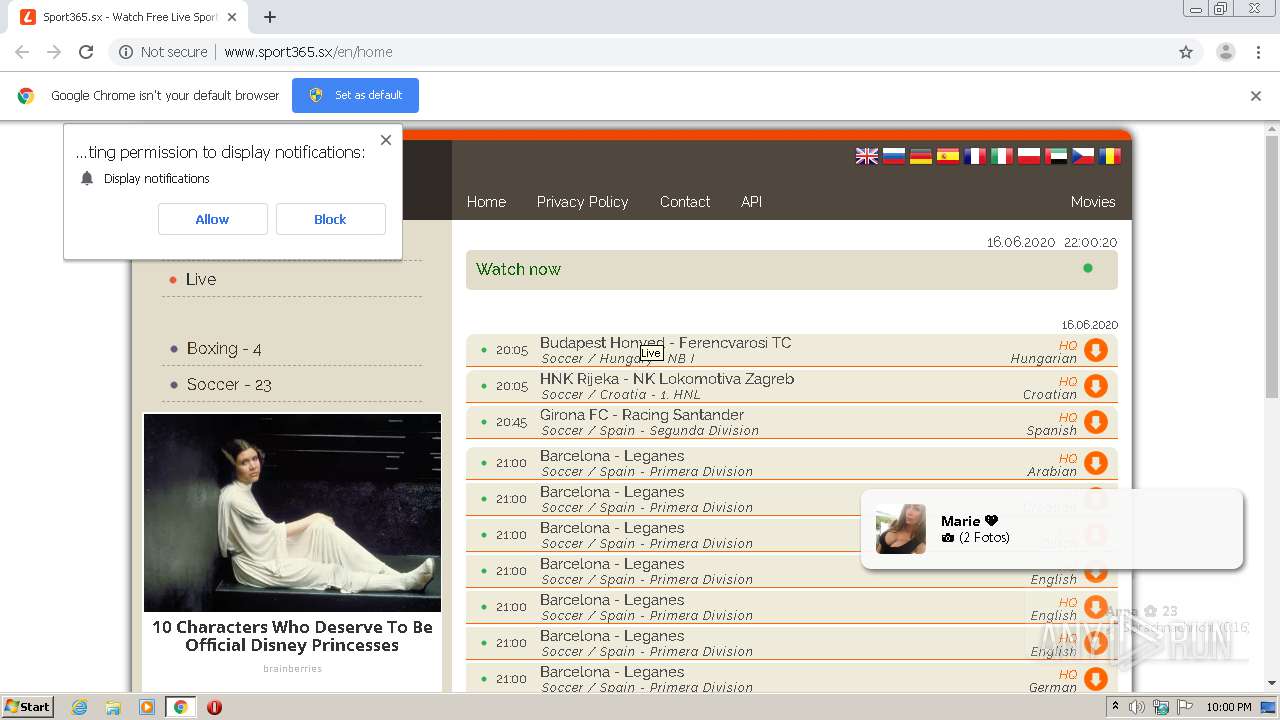
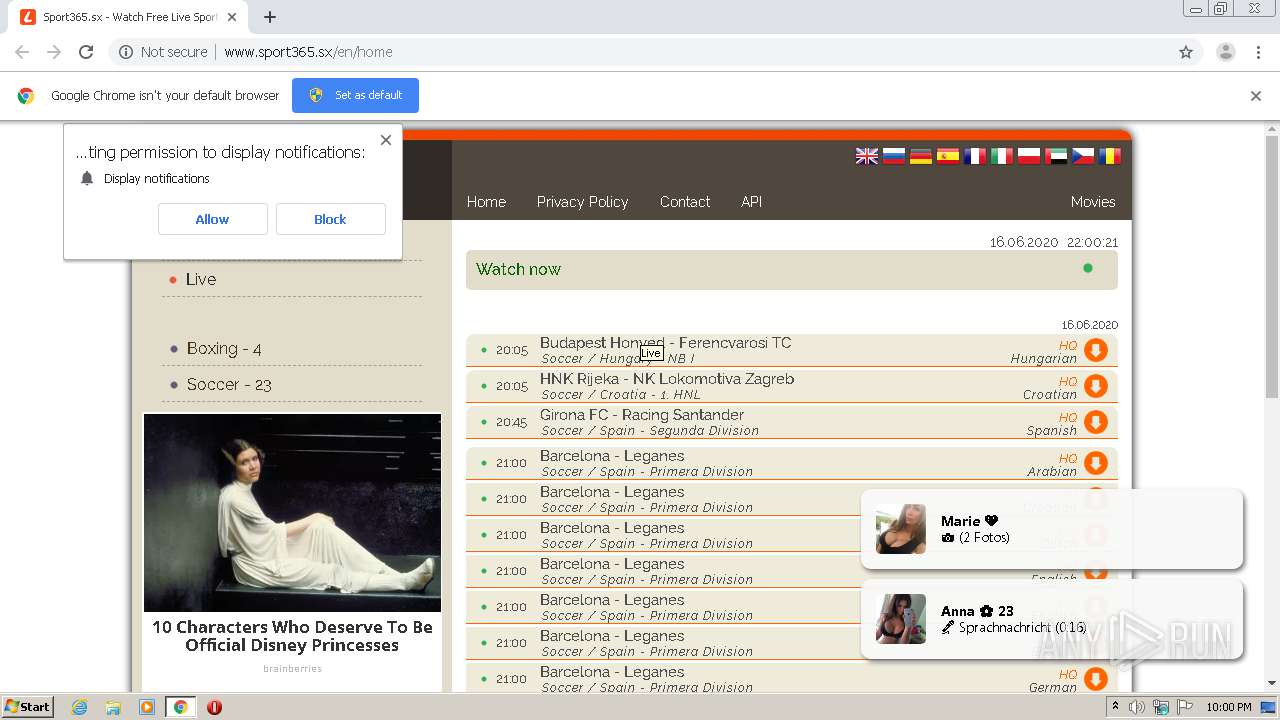
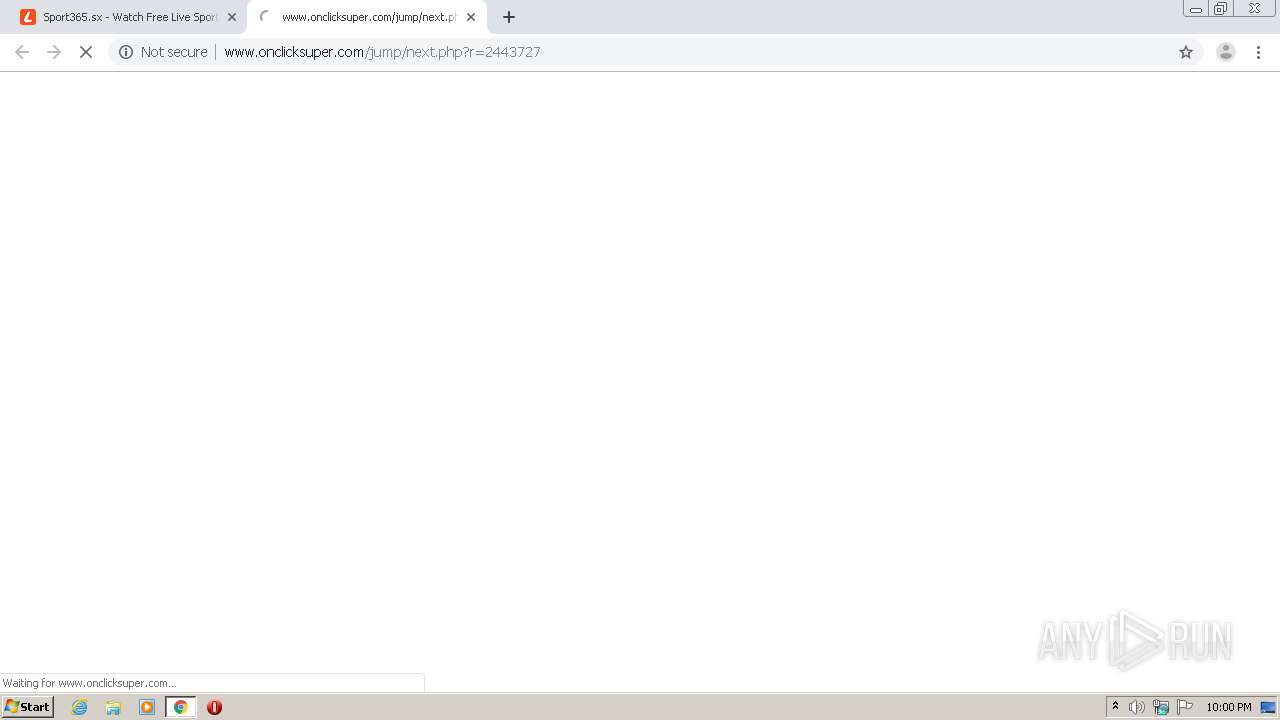
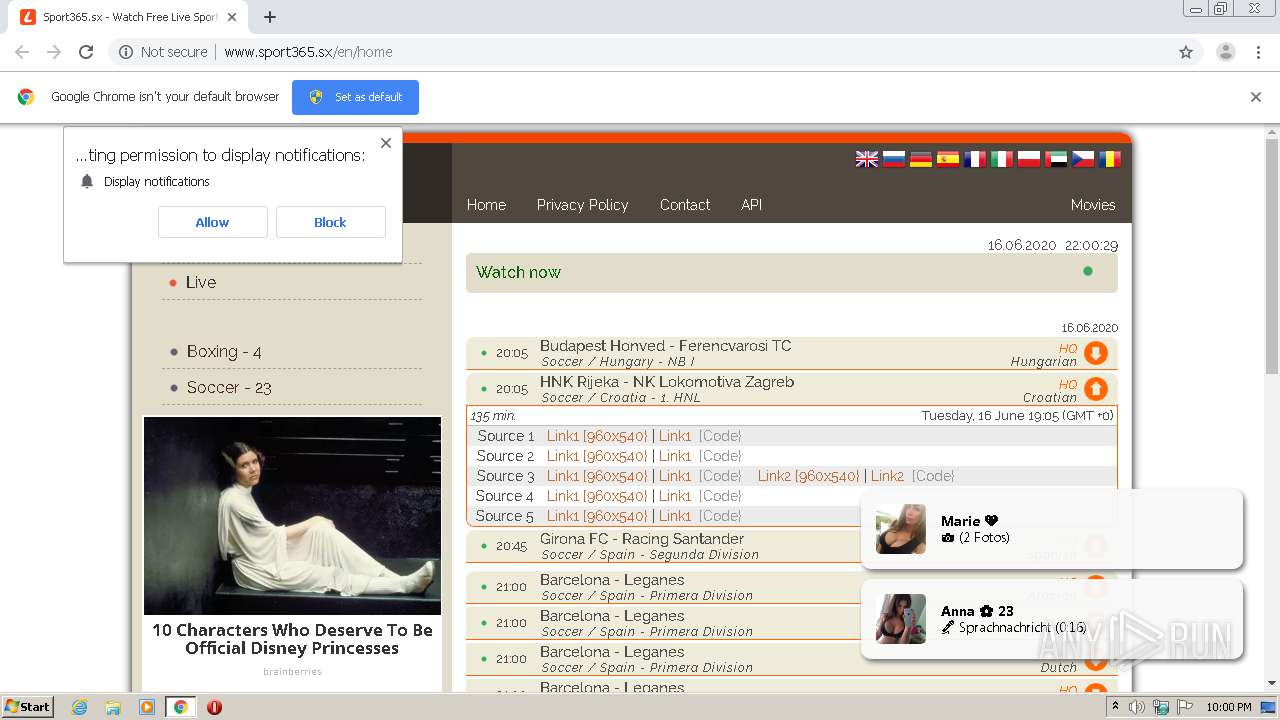
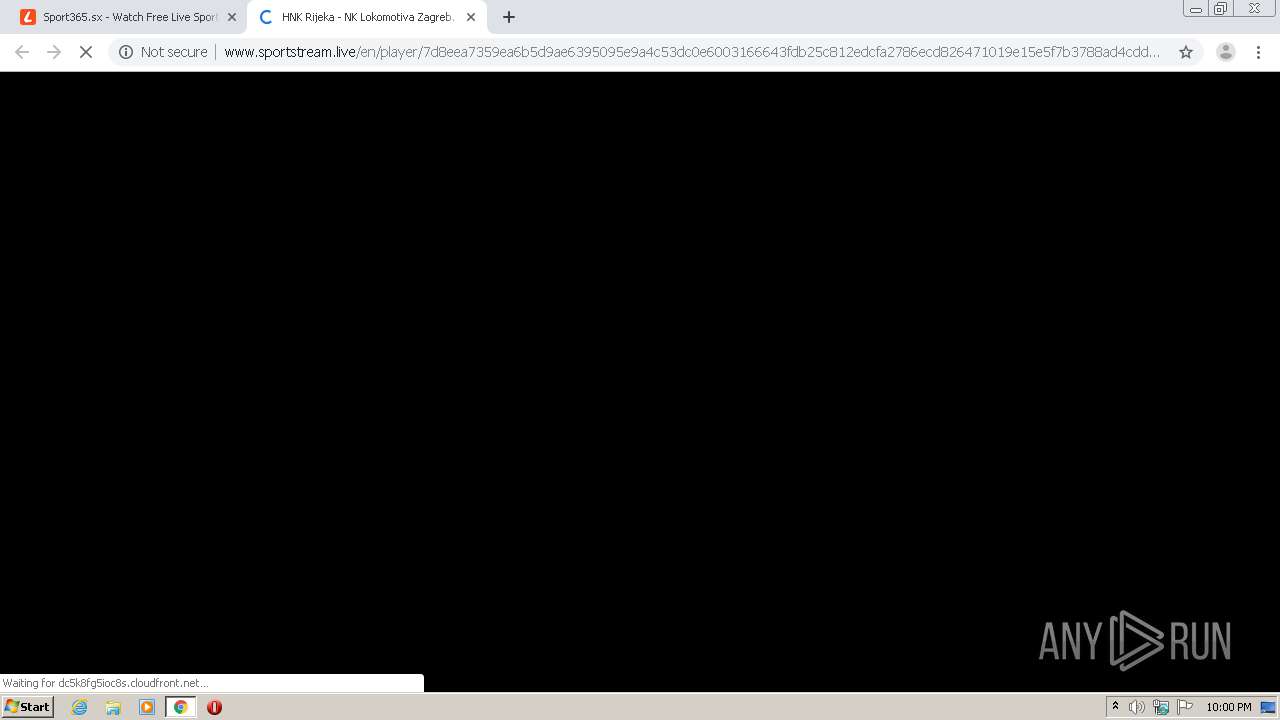
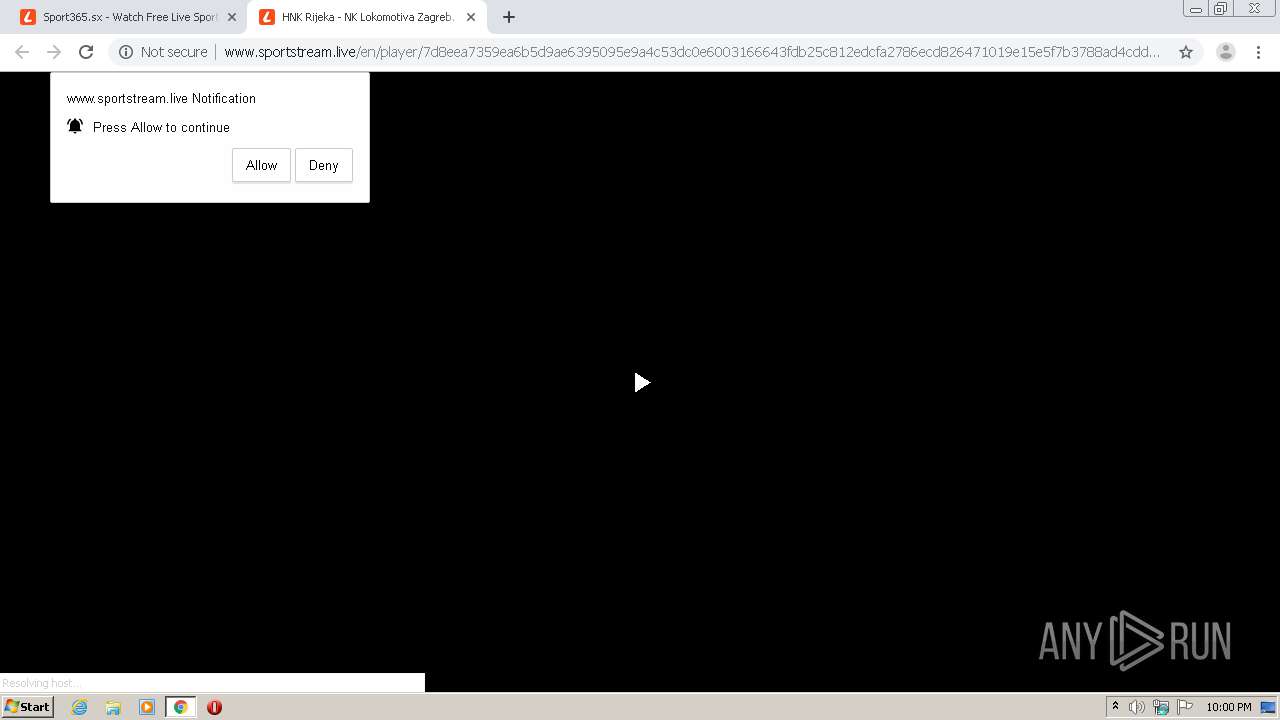
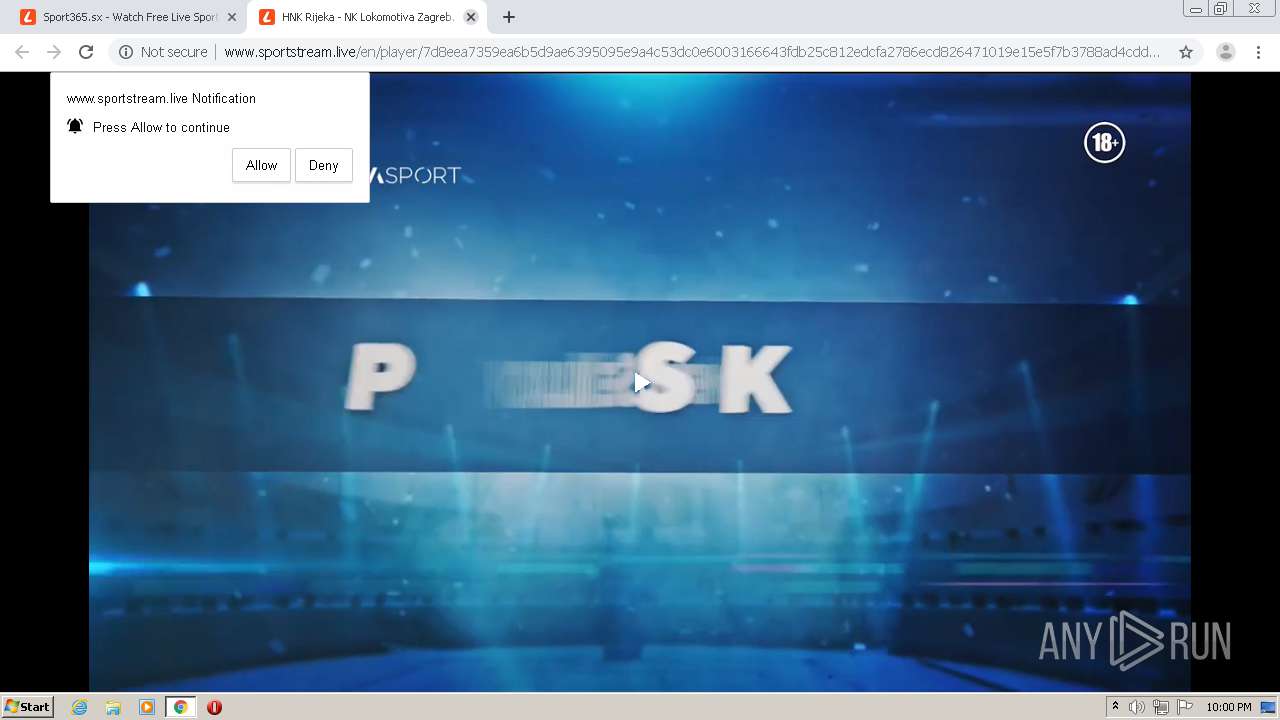
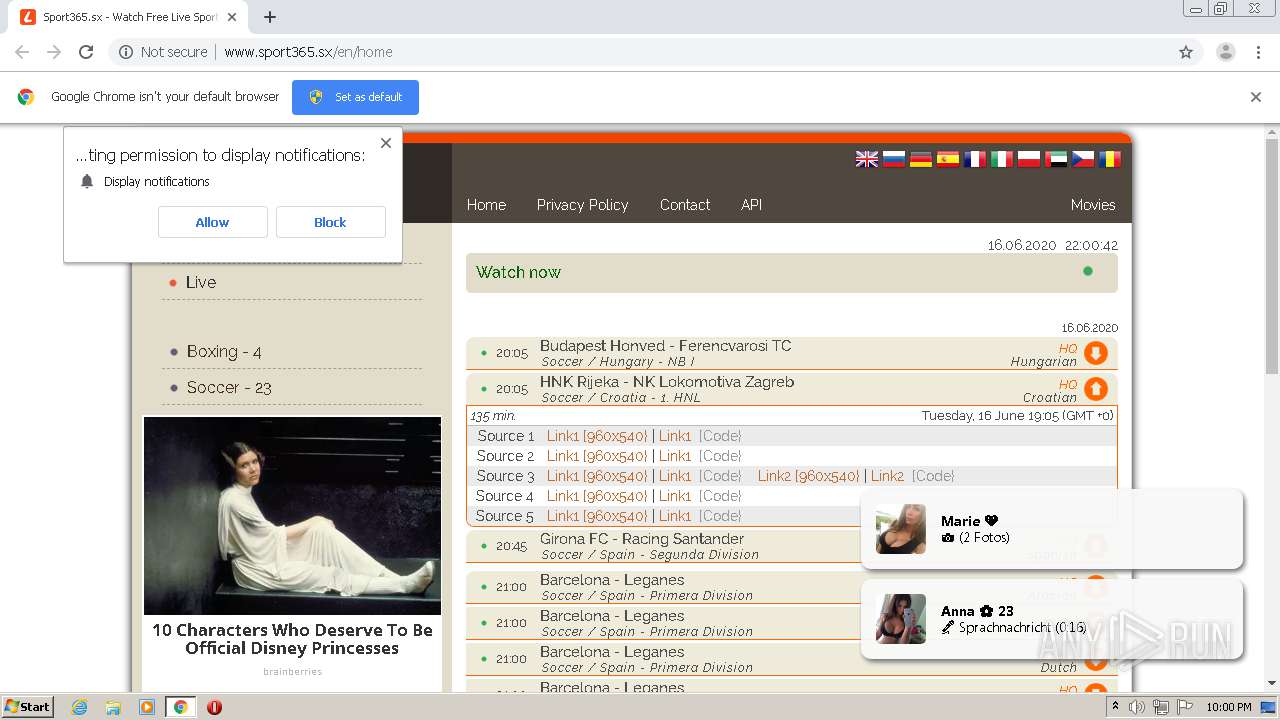
| URL: | http://www.sport365.sx/ |
| Full analysis: | https://app.any.run/tasks/70f1e036-b288-4ca7-b0fd-b73f8456f14f |
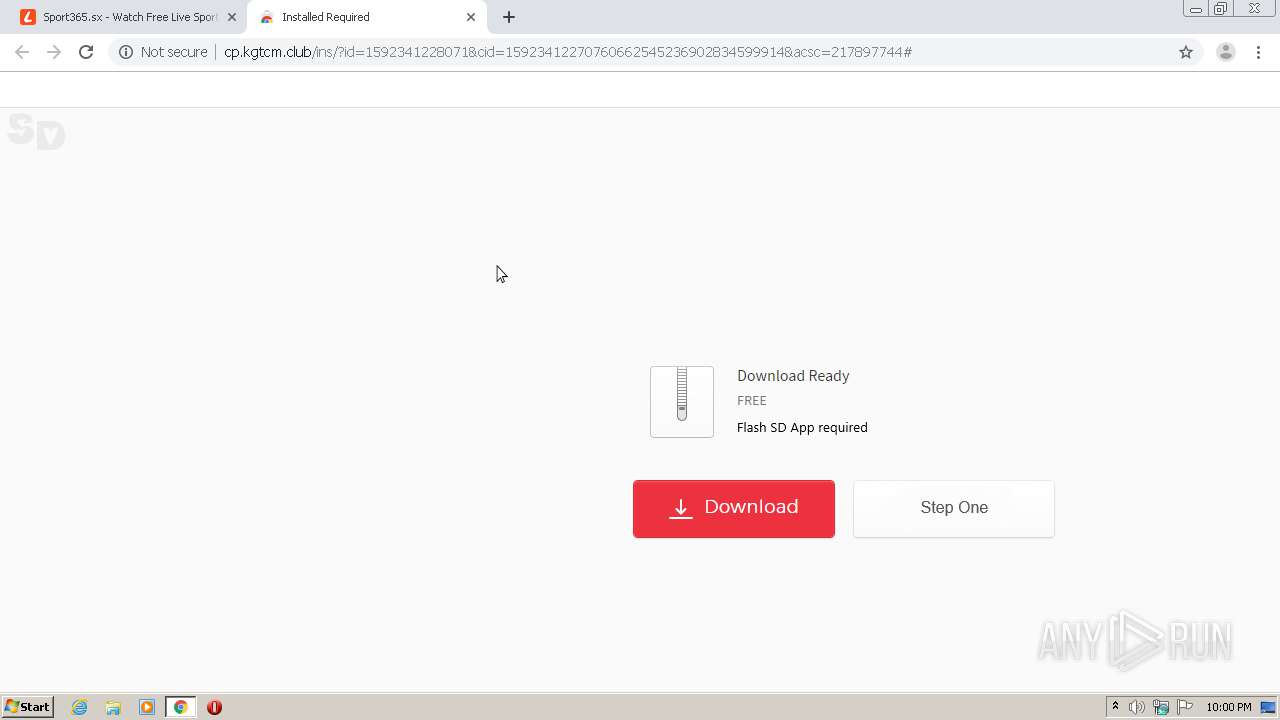
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2020, 20:59:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 146EF961CF1EF2C4815C09E966DBFE60 |
| SHA1: | 9BB4D3561D351B047970969095BB93BDDA0DB4EC |
| SHA256: | 30EB1B77D513459797D503995062E013798259DE899F3B3E6D3434EA0FB1E26F |
| SSDEEP: | 3:N1KJS4z:Cc4z |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1044)
INFO
Application launched itself
- chrome.exe (PID: 1044)
Reads the hosts file
- chrome.exe (PID: 1044)
- chrome.exe (PID: 4024)
Creates files in the user directory
- chrome.exe (PID: 1044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
32
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,9129514211403449998,6476524187030522547,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7959841789710883938 --mojo-platform-channel-handle=4616 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,9129514211403449998,6476524187030522547,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17207108097185772811 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.sport365.sx/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,9129514211403449998,6476524187030522547,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12037938058456912353 --mojo-platform-channel-handle=4672 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,9129514211403449998,6476524187030522547,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16101396304353568966 --mojo-platform-channel-handle=4000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,9129514211403449998,6476524187030522547,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10269050950391151613 --mojo-platform-channel-handle=4664 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,9129514211403449998,6476524187030522547,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2923683982780302790 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4700 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,9129514211403449998,6476524187030522547,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=7020639608914586908 --mojo-platform-channel-handle=2960 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,9129514211403449998,6476524187030522547,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17651311527068437926 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,9129514211403449998,6476524187030522547,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9072265942854651937 --mojo-platform-channel-handle=5044 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
632
Read events
537
Write events
90
Delete events
5
Modification events
| (PID) Process: | (3732) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1044-13236814812626125 |
Value: 259 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
71
Text files
234
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5EE932DD-414.pma | — | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d4481410-d6e5-43f6-b060-c6f52ac72633.tmp | — | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DA692BE42E4EF2668AE7499A7D5DA720 | SHA256:EB865CAF59002C092F5FDBE22D01935866BC1277108B29E897052CB2439630ED | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF168ad0.TMP | text | |
MD5:F69C20D5B552B8D973FB1CBA5FDD7D87 | SHA256:48799968D50E2D74E625A0AB18E93C6792AF20010334C6BB4E935C8D26F7026A | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF168adf.TMP | text | |
MD5:33B05E8AC9C178C58ED3321F496588C0 | SHA256:2CDF6A09638A0B563EA2672D6926210771902E0A9203FE15D2857FC4EB954CDE | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF168cb4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
112
TCP/UDP connections
147
DNS requests
61
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4024 | chrome.exe | GET | 200 | 37.1.202.42:80 | http://www.sport365.sx/en/home | NL | html | 10.5 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.162.52:80 | http://s1.sport365.cloud/css/m.css?1592337903 | US | text | 2.11 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.162.52:80 | http://s1.sport365.cloud/js/jquery.min.js | US | text | 33.0 Kb | suspicious |
4024 | chrome.exe | GET | 302 | 37.1.202.42:80 | http://www.sport365.sx/ | NL | text | 2 b | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.162.52:80 | http://s1.sport365.cloud/js/forge.min.js | US | binary | 74.5 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.162.52:80 | http://s1.sport365.cloud/js/jquery.cookie.js | US | text | 1.33 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.162.52:80 | http://s1.sport365.cloud/js/b500097693fab5f37bd969456c9c1e77.js?1592337903 | US | text | 61.0 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 104.27.162.52:80 | http://s1.sport365.cloud/js/advertisement.js?1592337903 | US | text | 22.5 Kb | suspicious |
4024 | chrome.exe | GET | 200 | 143.204.101.177:80 | http://dc5k8fg5ioc8s.cloudfront.net/?gfkcd=825597 | US | text | 28.5 Kb | shared |
4024 | chrome.exe | GET | 200 | 104.27.162.52:80 | http://s1.sport365.cloud/js/35878370c7a61850d100018cc4197c96.js?1592337903 | US | text | 24.6 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4024 | chrome.exe | 37.1.202.42:80 | www.sport365.sx | Serverius Holding B.V. | NL | suspicious |
4024 | chrome.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4024 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
4024 | chrome.exe | 104.27.162.52:80 | s1.sport365.cloud | Cloudflare Inc | US | shared |
4024 | chrome.exe | 143.204.101.177:80 | dc5k8fg5ioc8s.cloudfront.net | — | US | suspicious |
4024 | chrome.exe | 163.172.253.2:80 | tags2.adshell.net | Online S.a.s. | FR | unknown |
4024 | chrome.exe | 52.222.147.193:443 | matekernes.fun | Amazon.com, Inc. | US | whitelisted |
4024 | chrome.exe | 216.58.207.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
4024 | chrome.exe | 52.222.147.193:80 | matekernes.fun | Amazon.com, Inc. | US | whitelisted |
4024 | chrome.exe | 82.202.209.179:80 | cdn.trafficdok.com | OOO Network of data-centers Selectel | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.sport365.sx |
| suspicious |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
s1.sport365.cloud |
| suspicious |
dc5k8fg5ioc8s.cloudfront.net |
| shared |
tags2.adshell.net |
| unknown |
fonts.gstatic.com |
| whitelisted |
matekernes.fun |
| whitelisted |
cdn.trafficdok.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1072 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
4024 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4024 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4024 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4024 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4024 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4024 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4024 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4024 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |
4024 | chrome.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.cloud Domain |