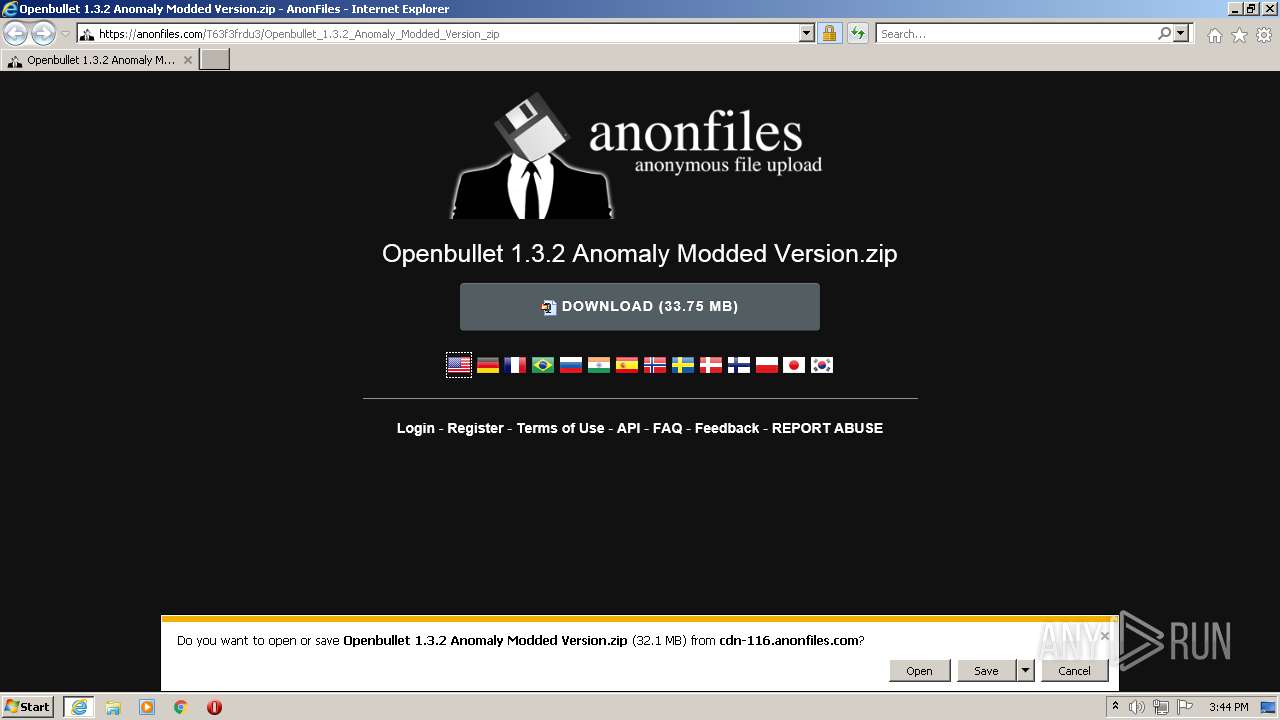
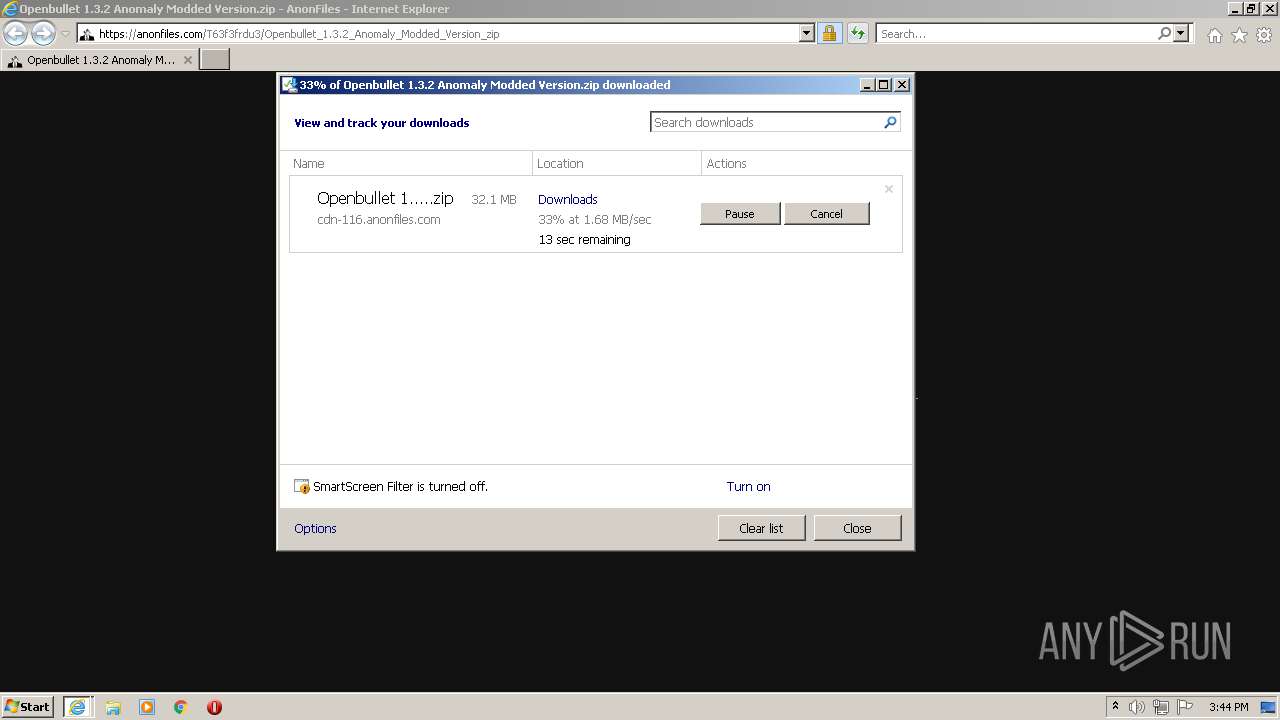
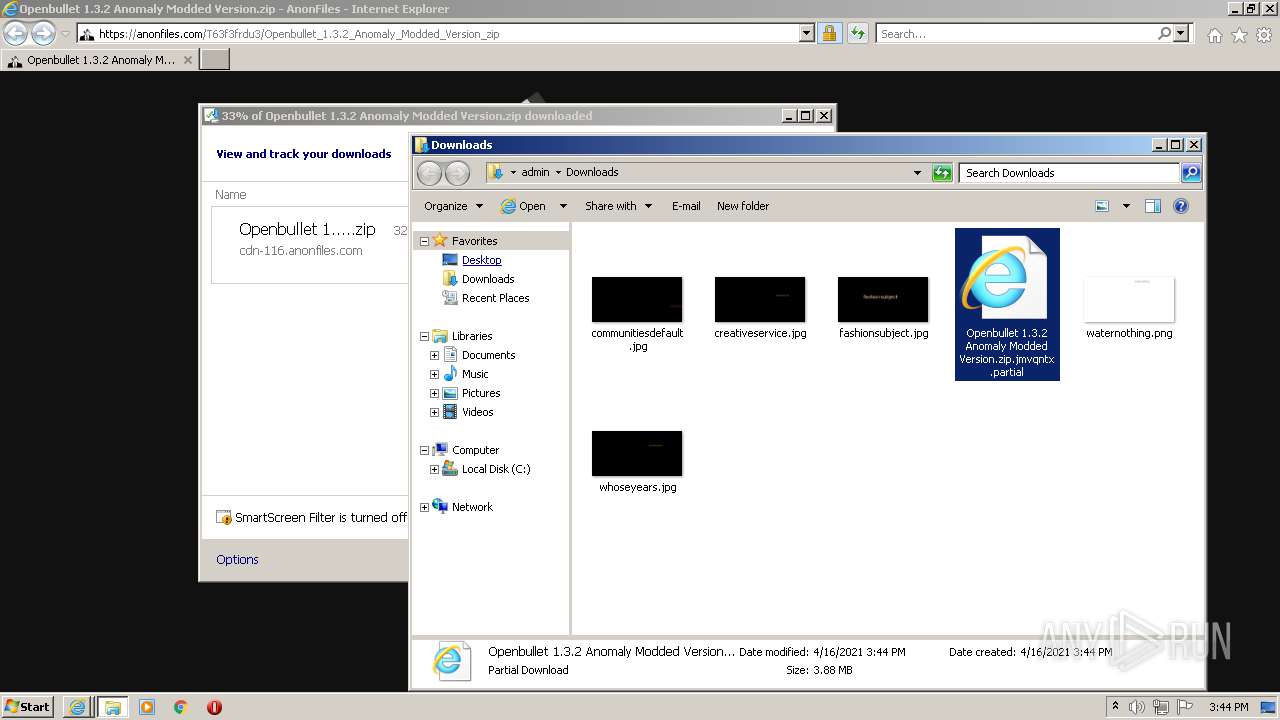
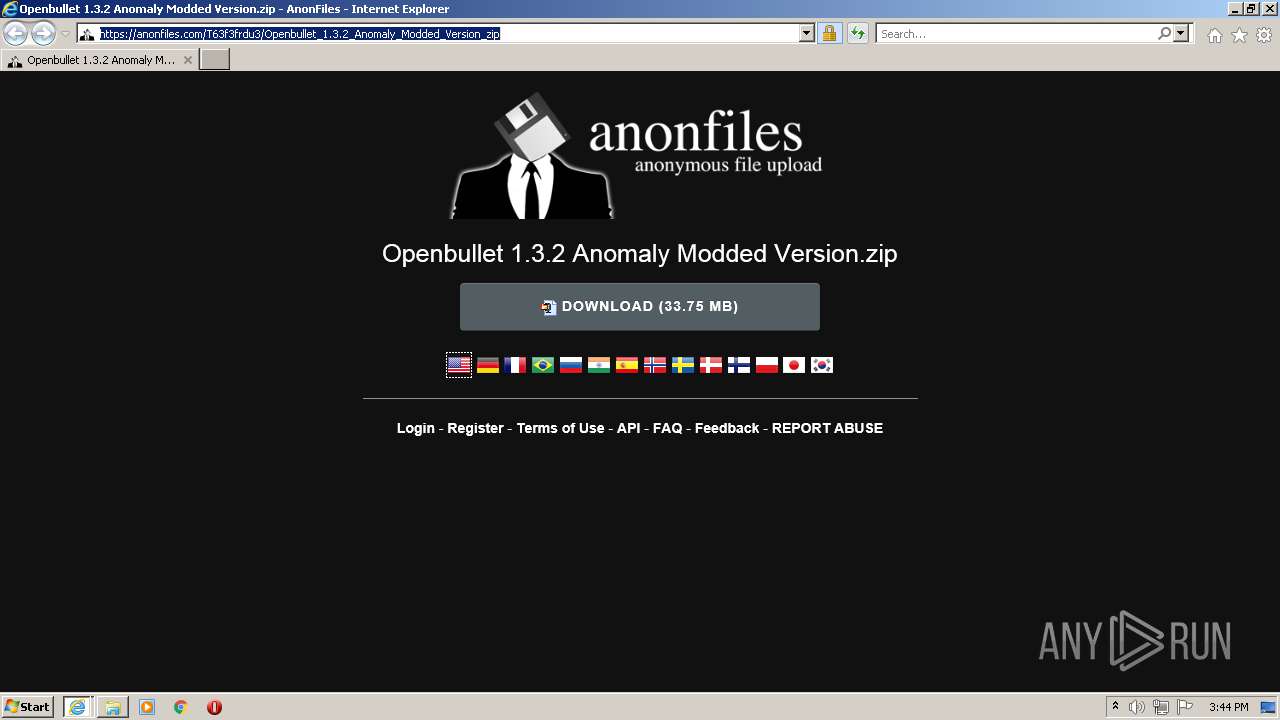
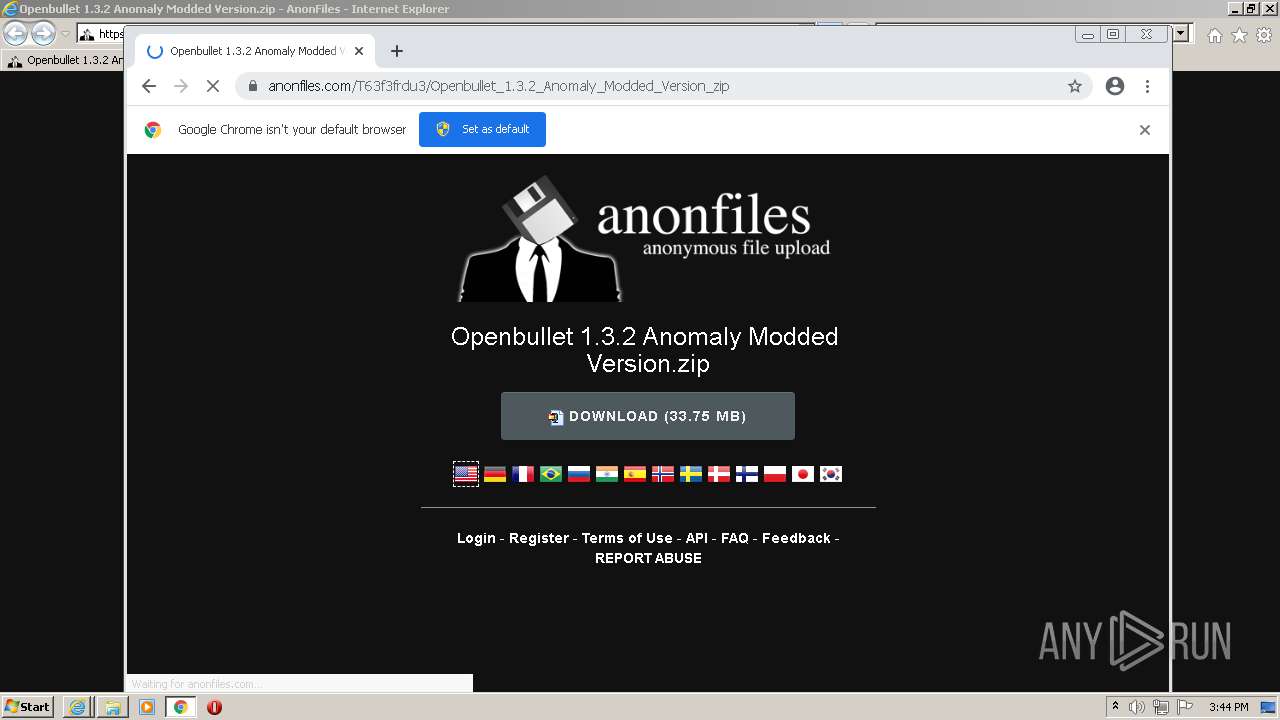
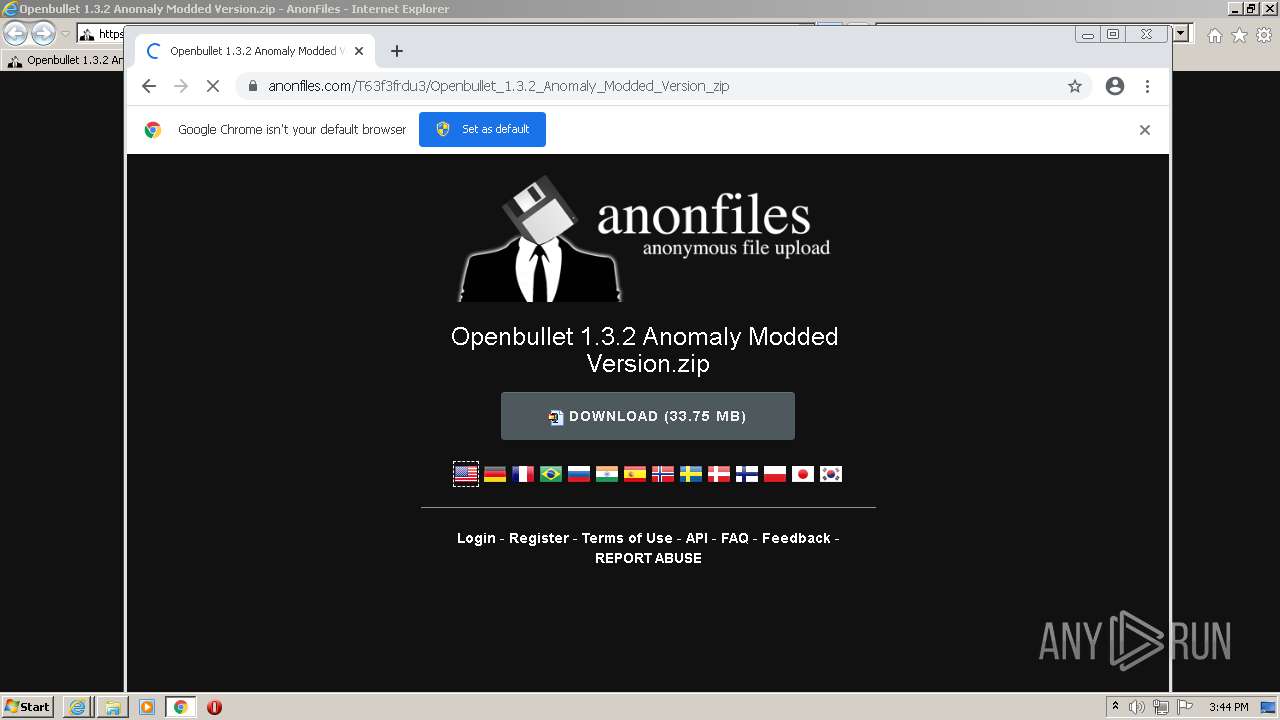
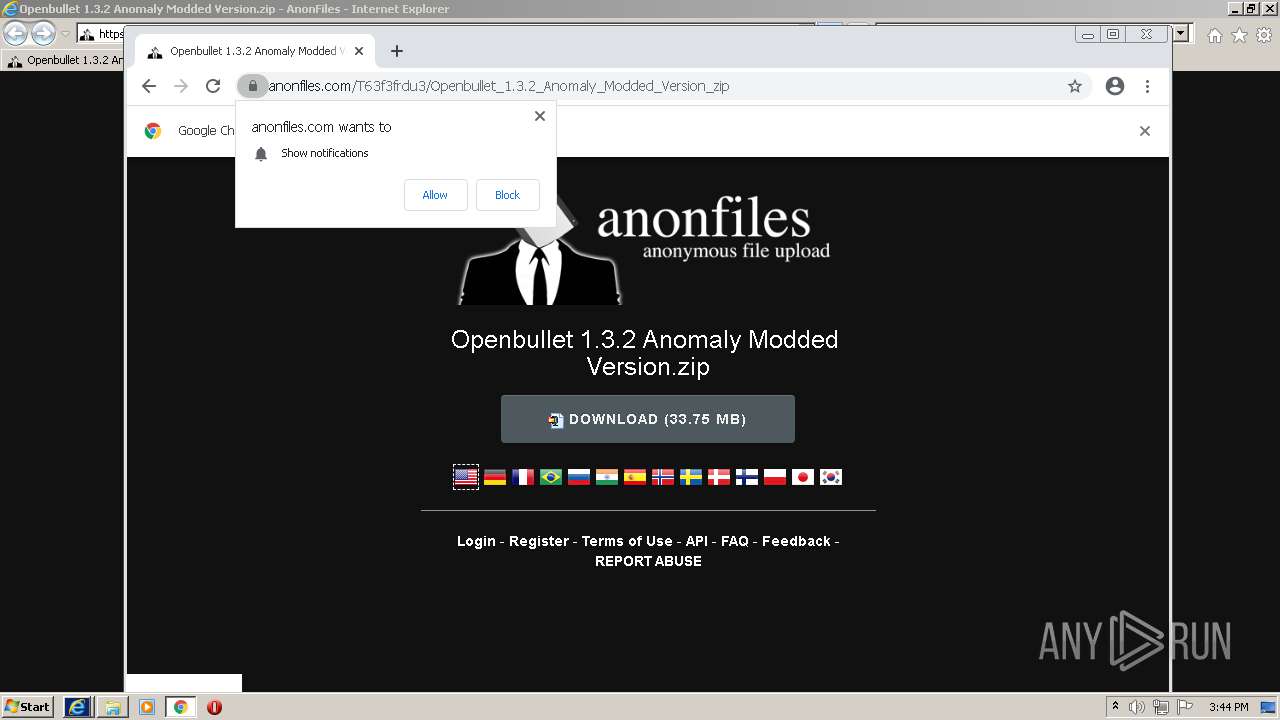
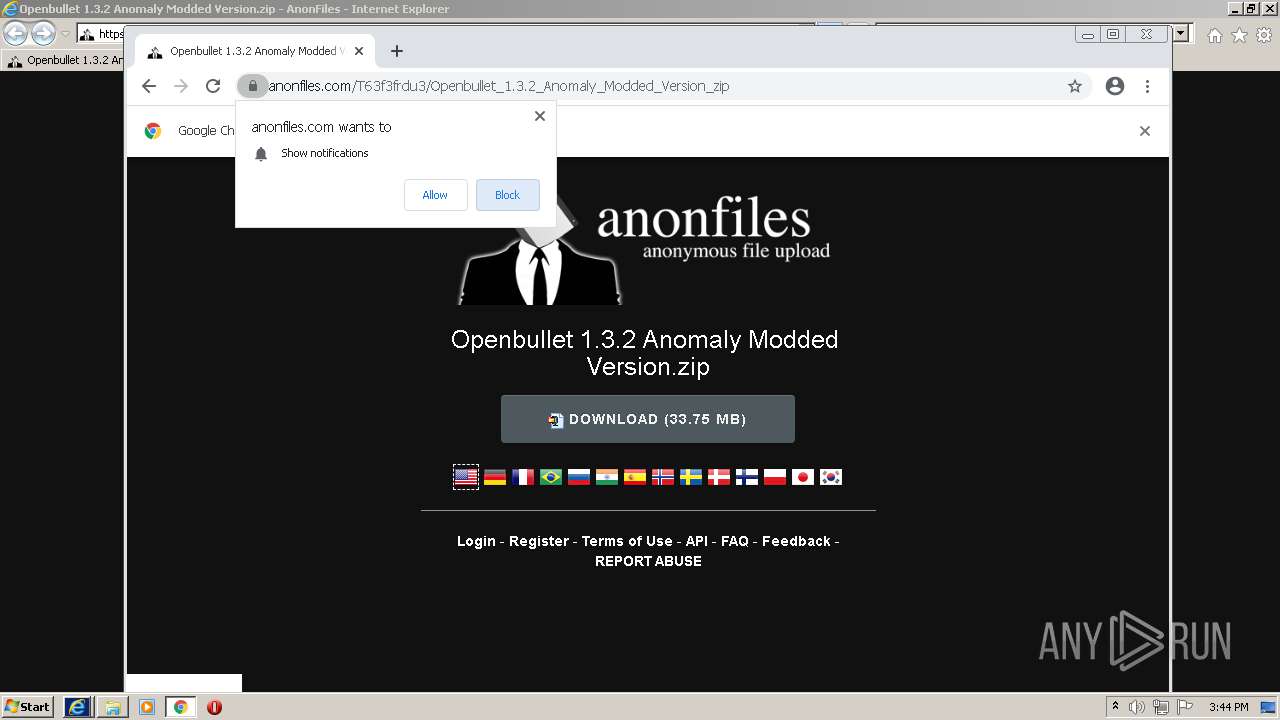
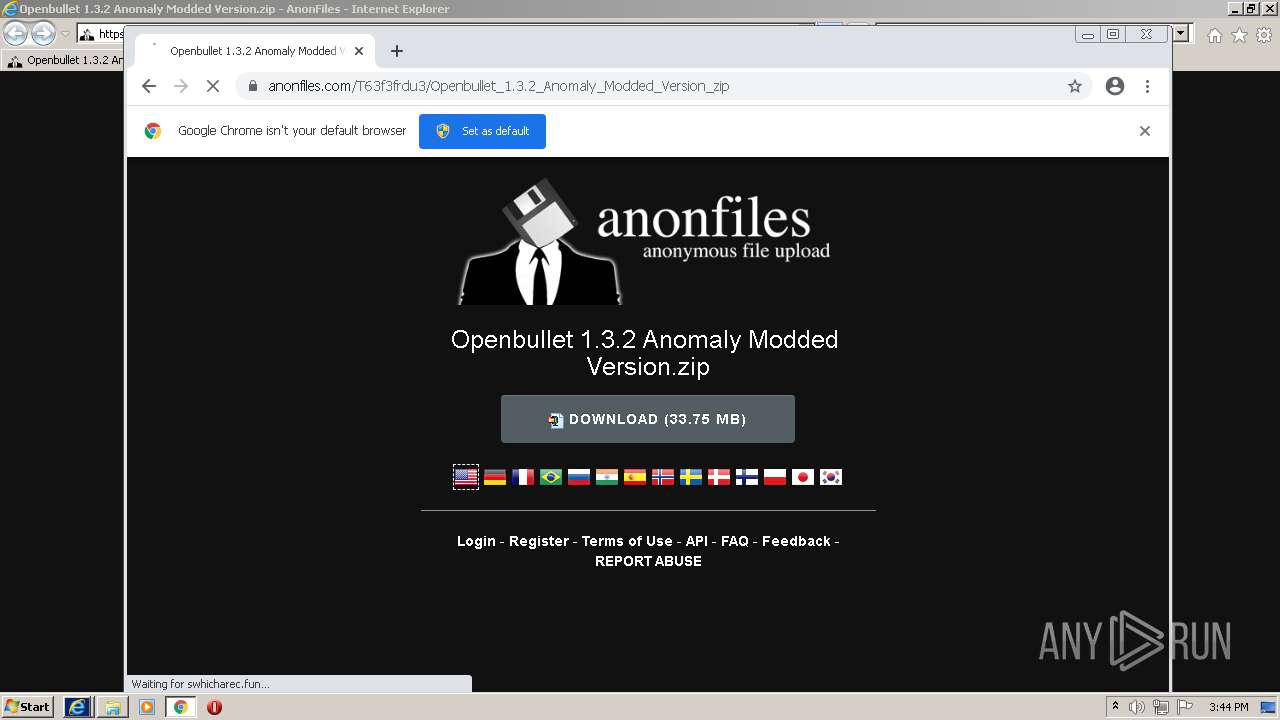
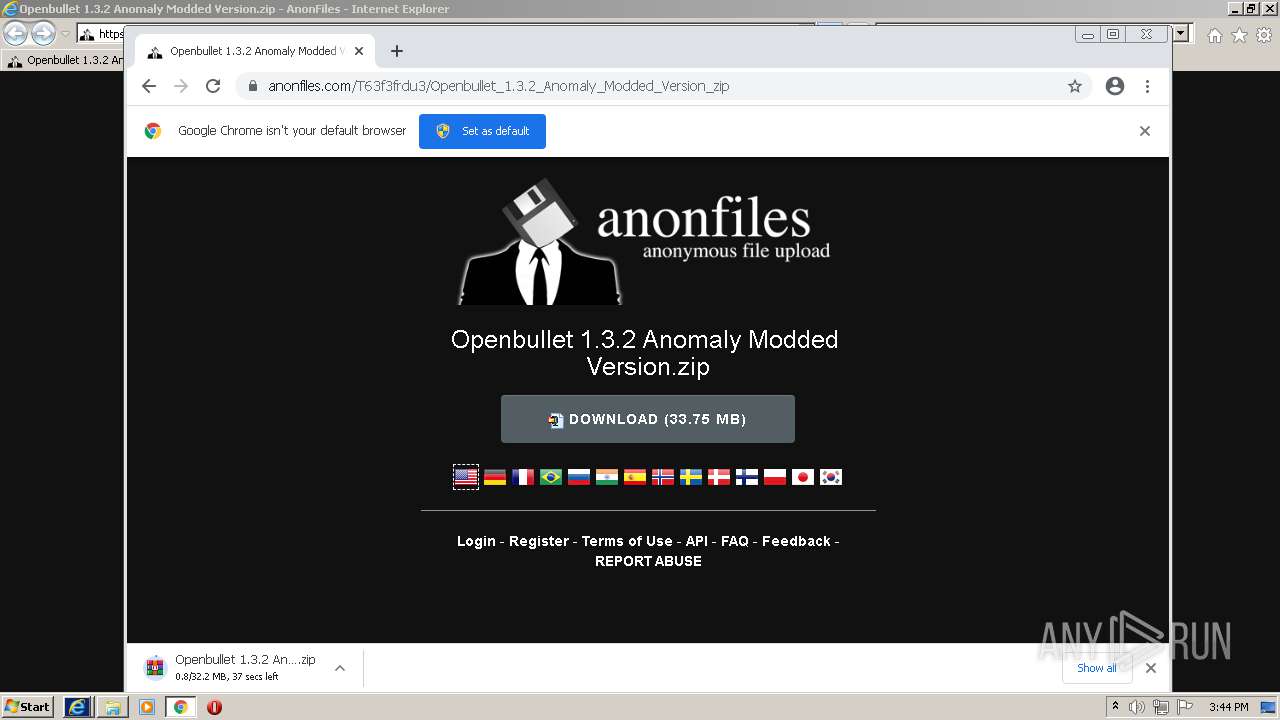
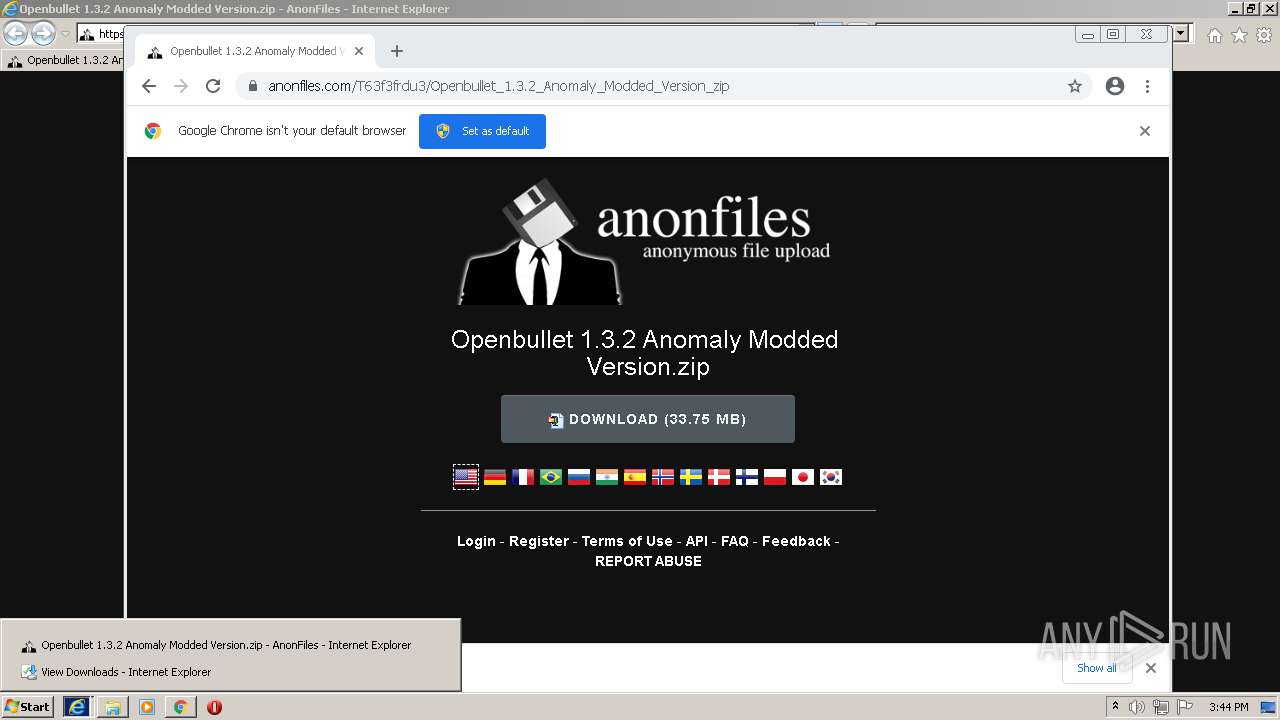
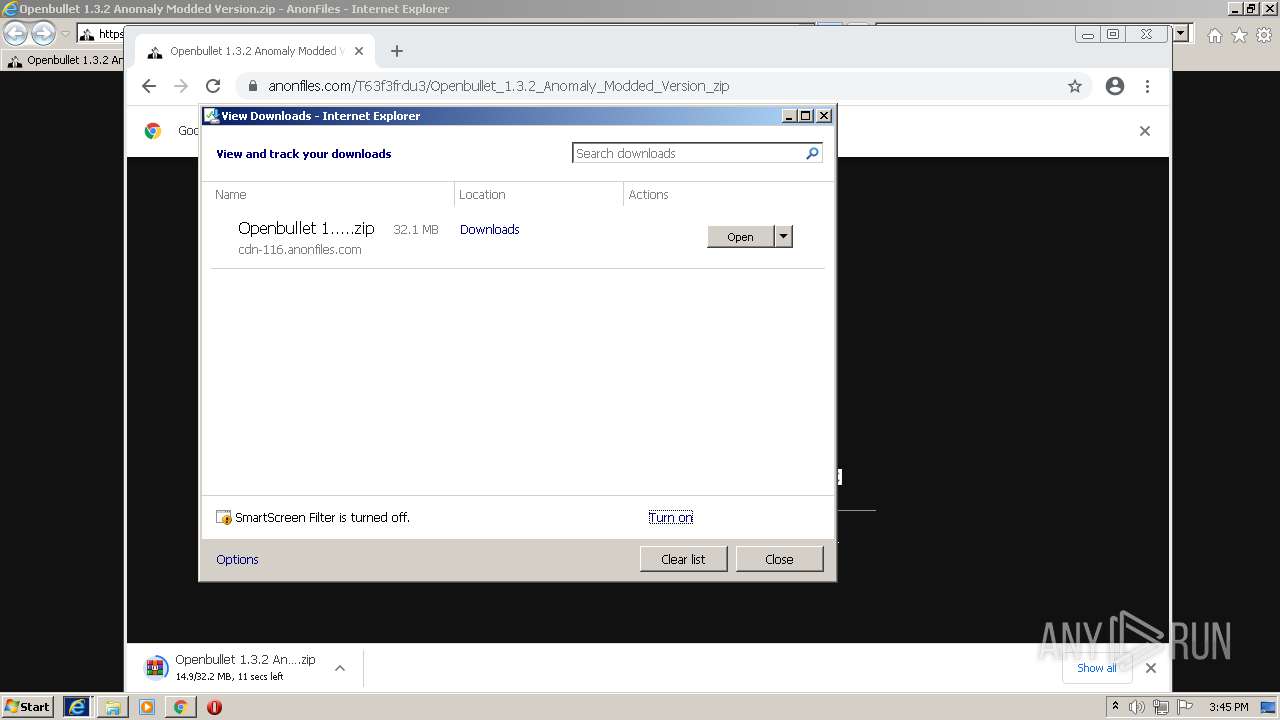
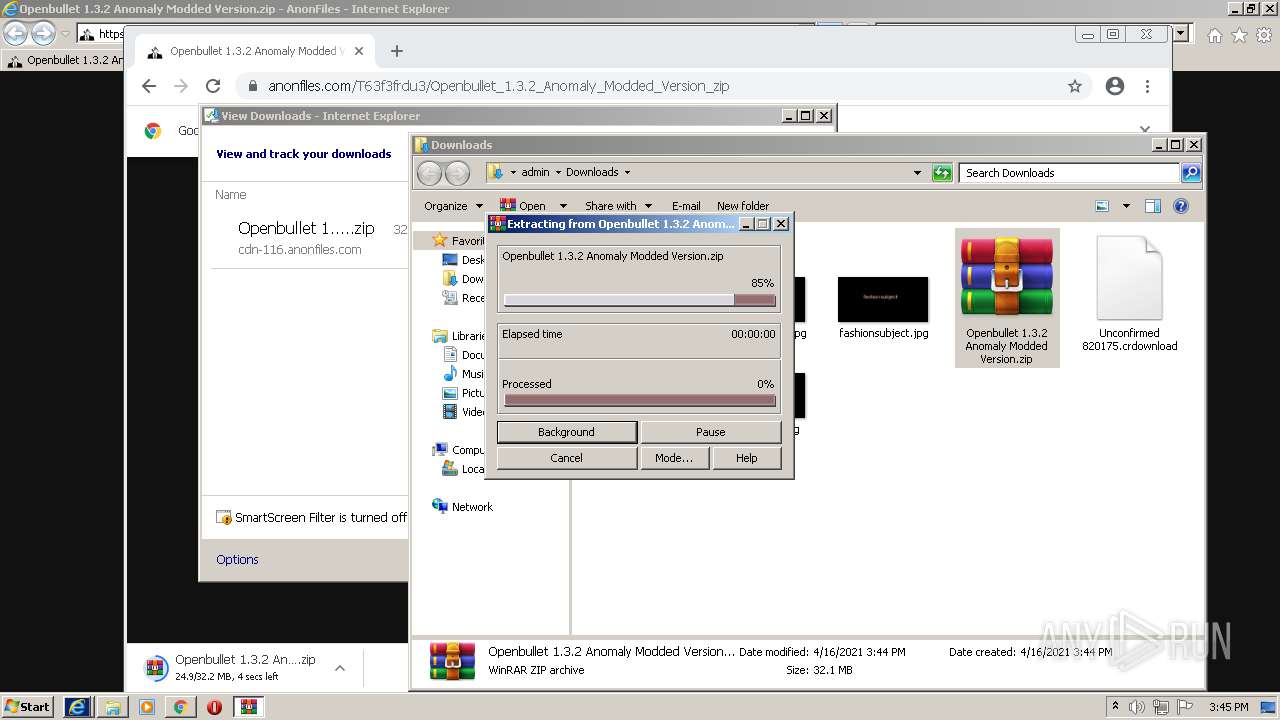
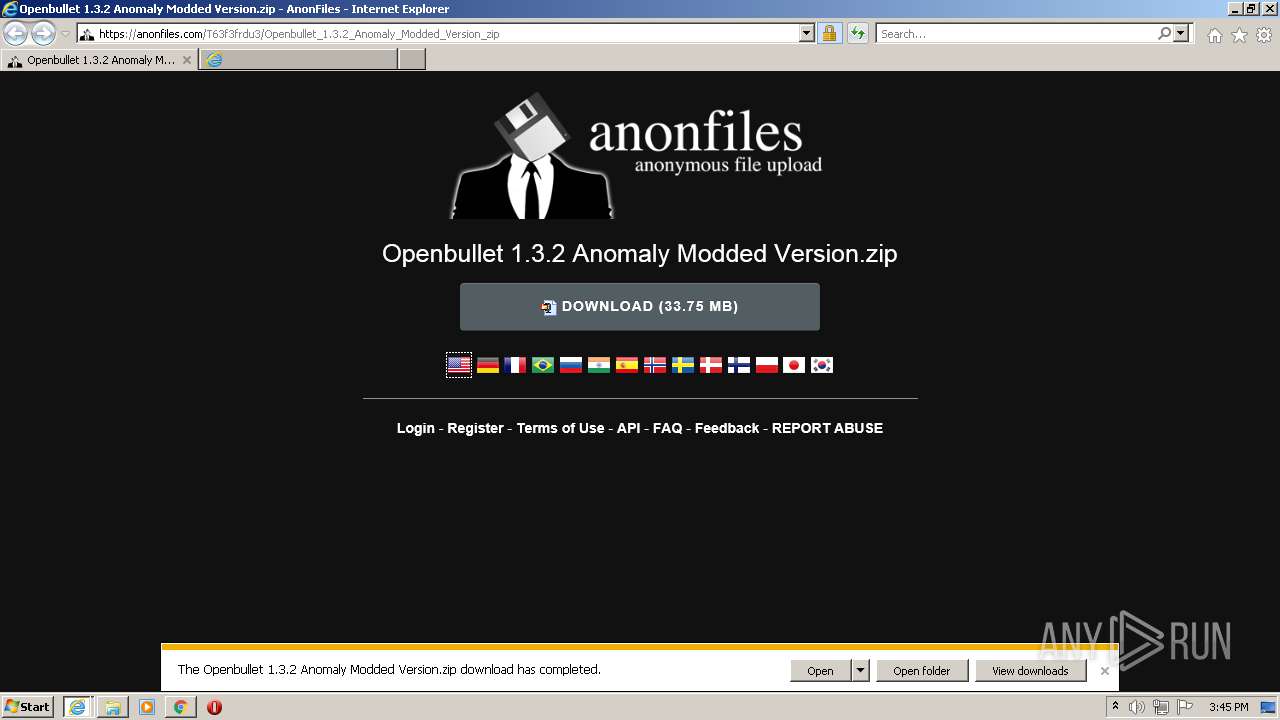
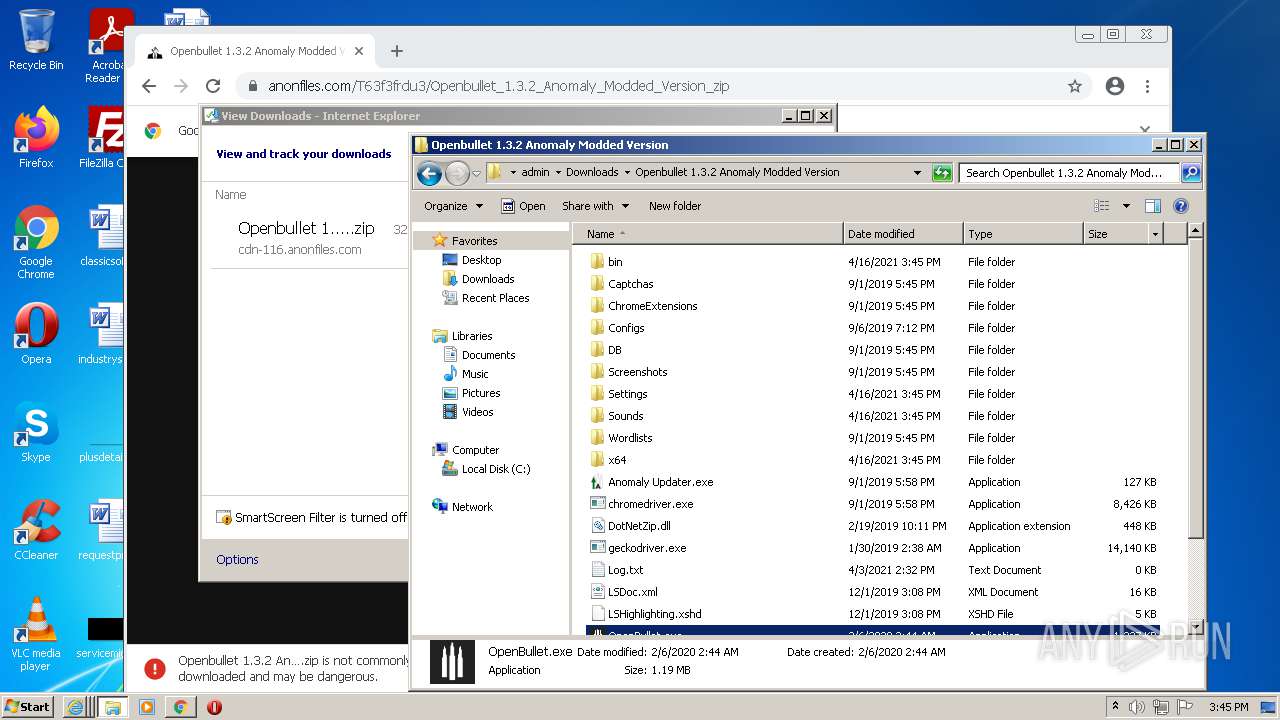
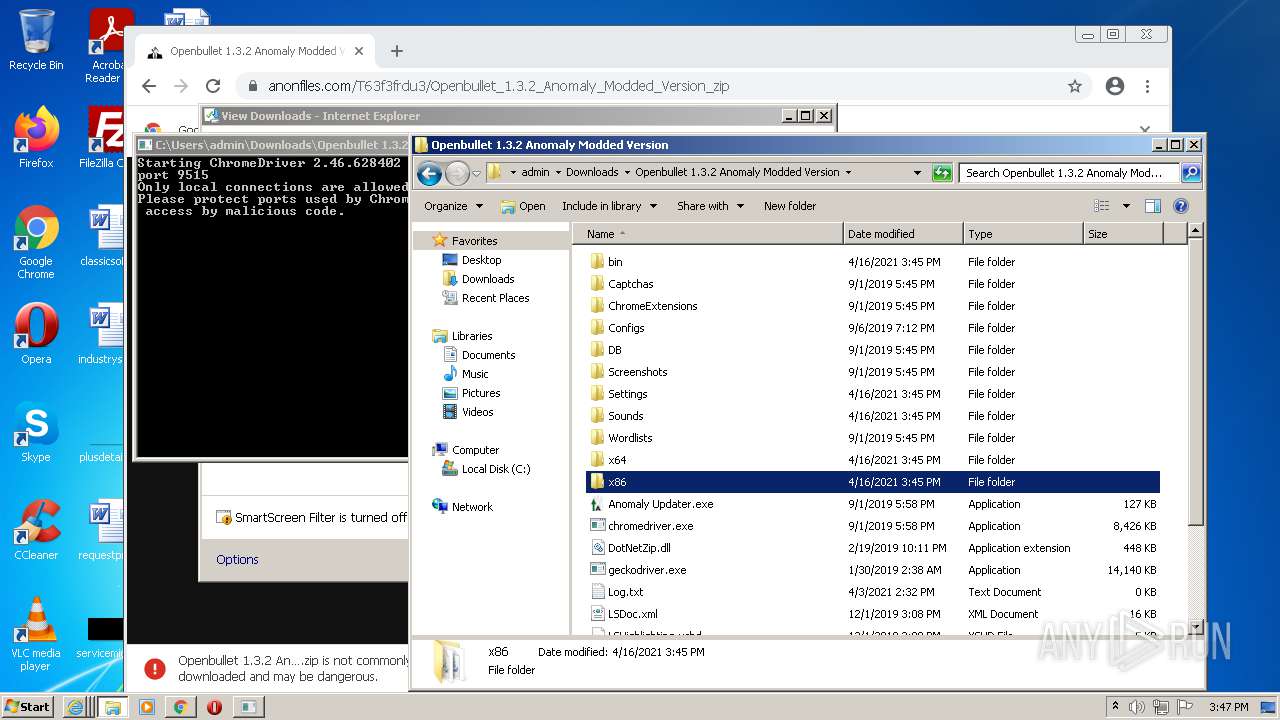
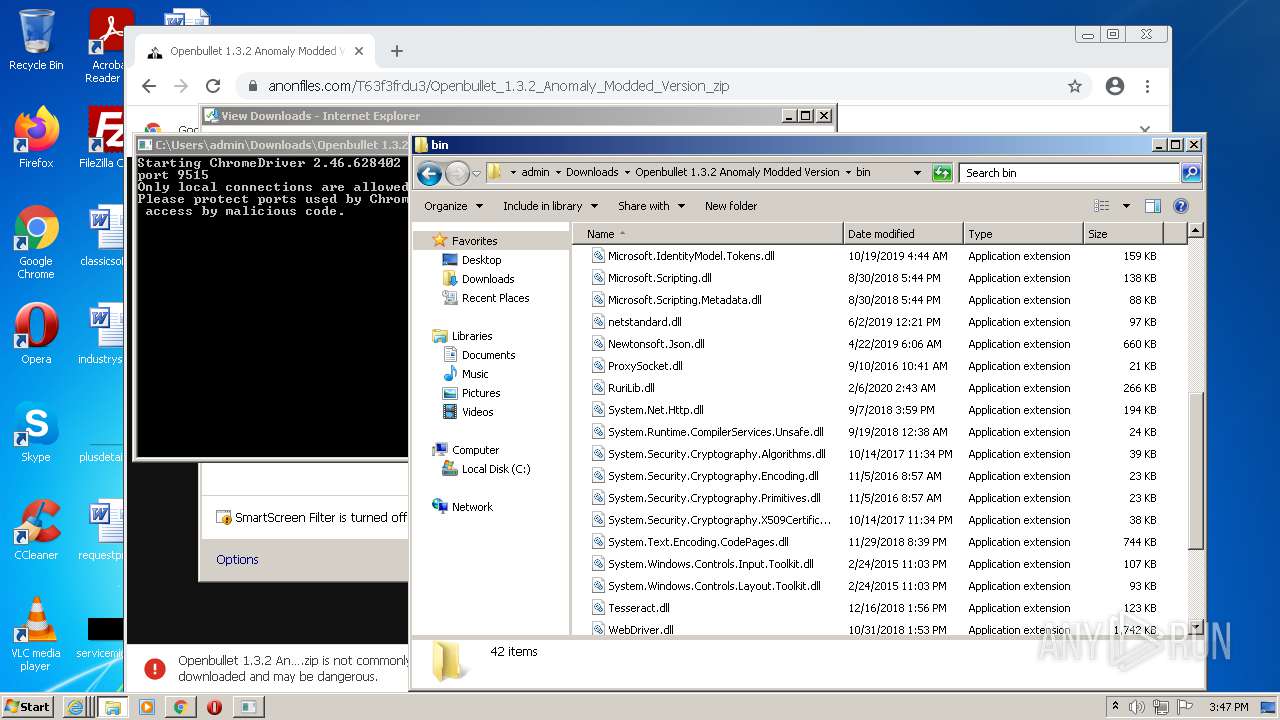
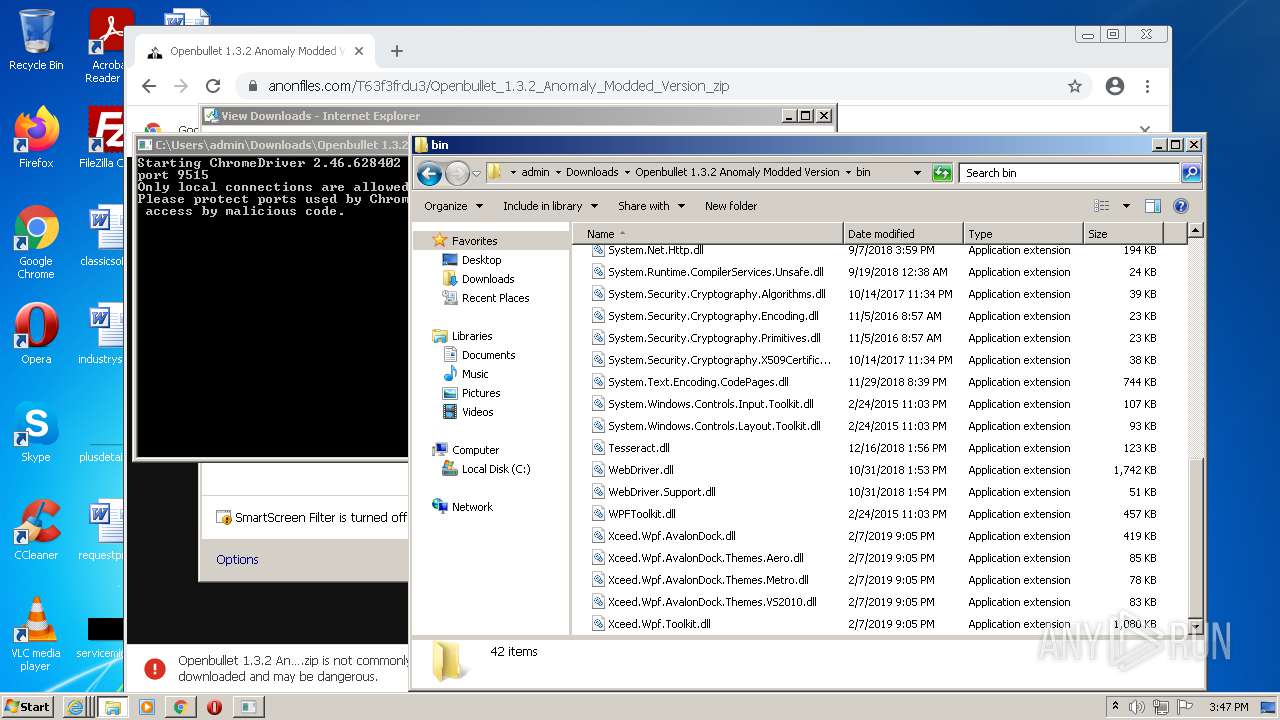
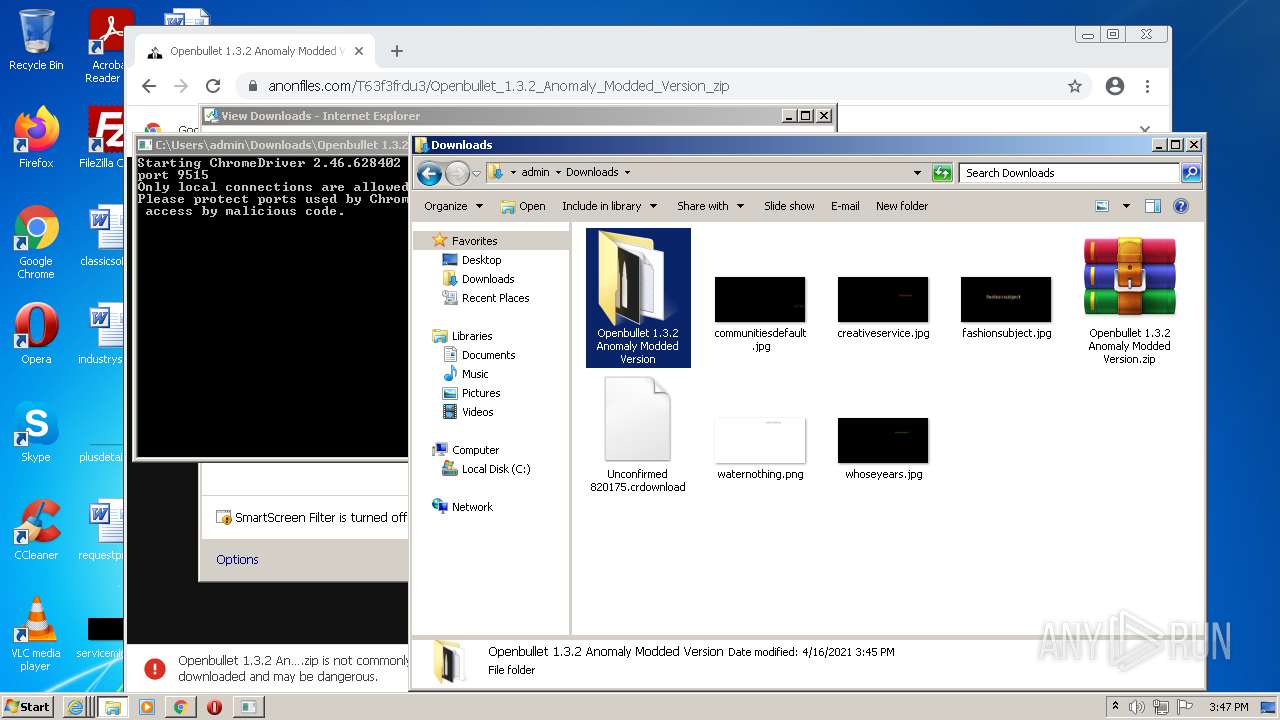
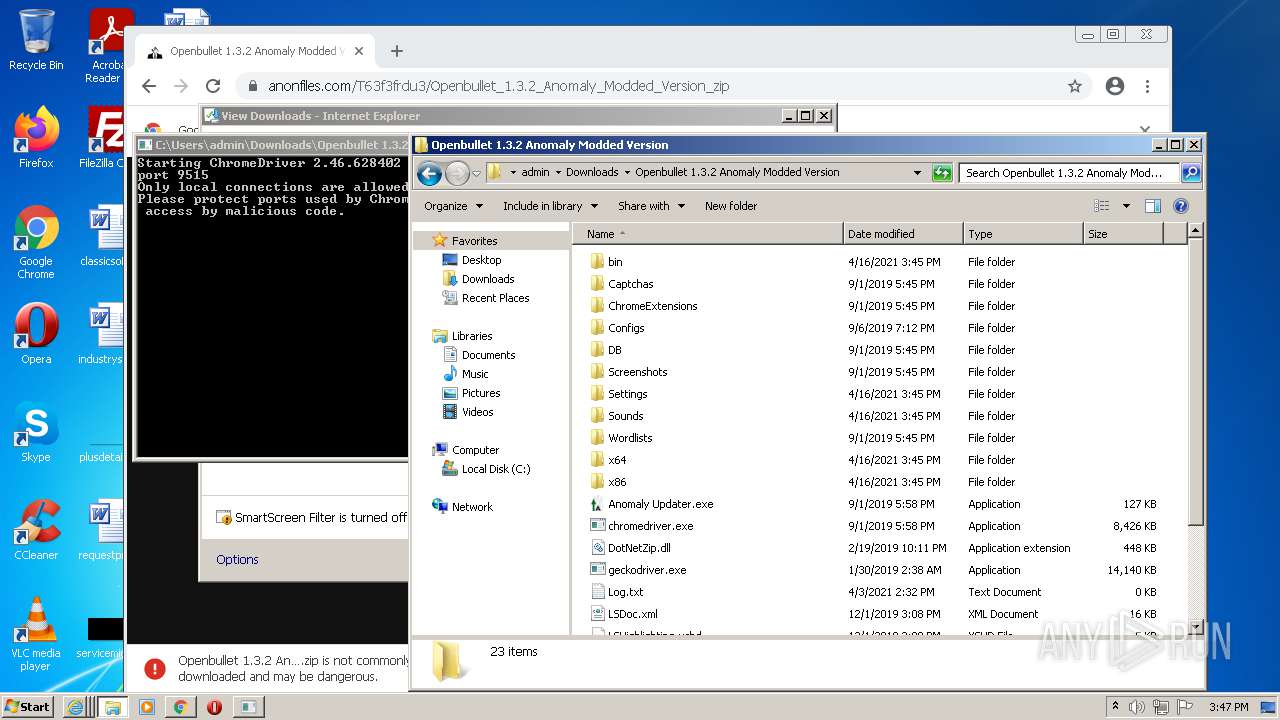
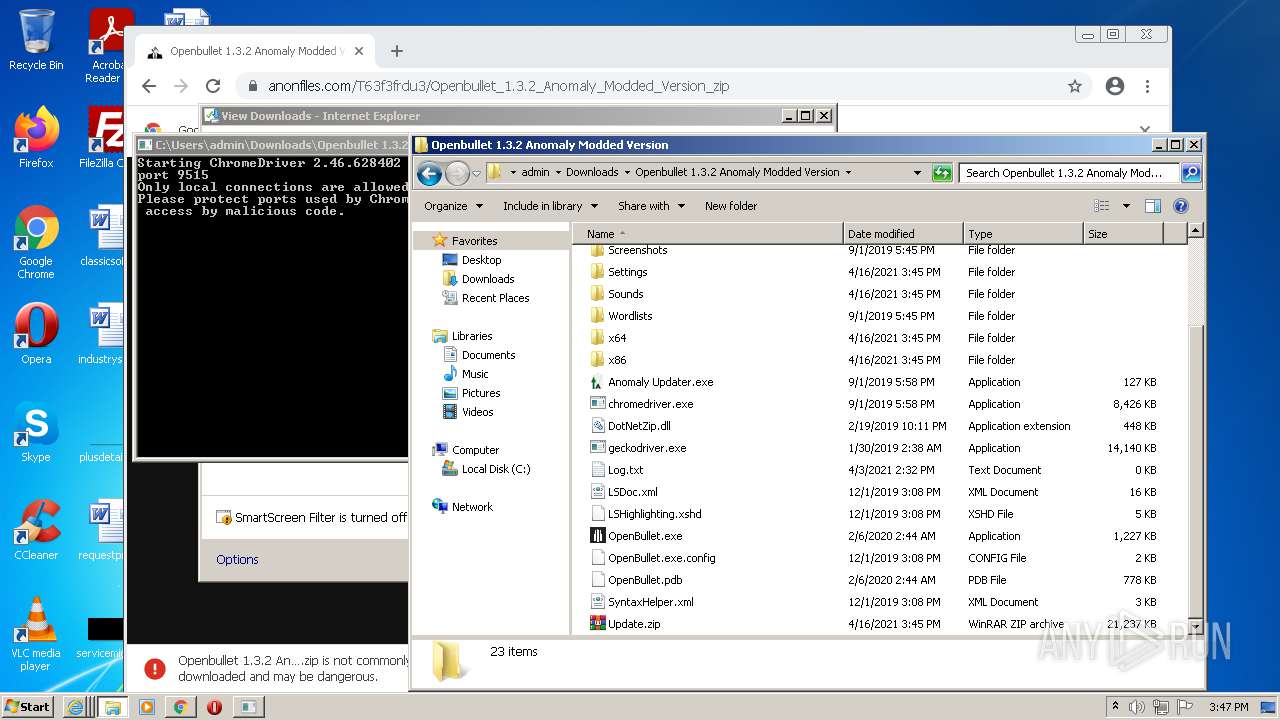
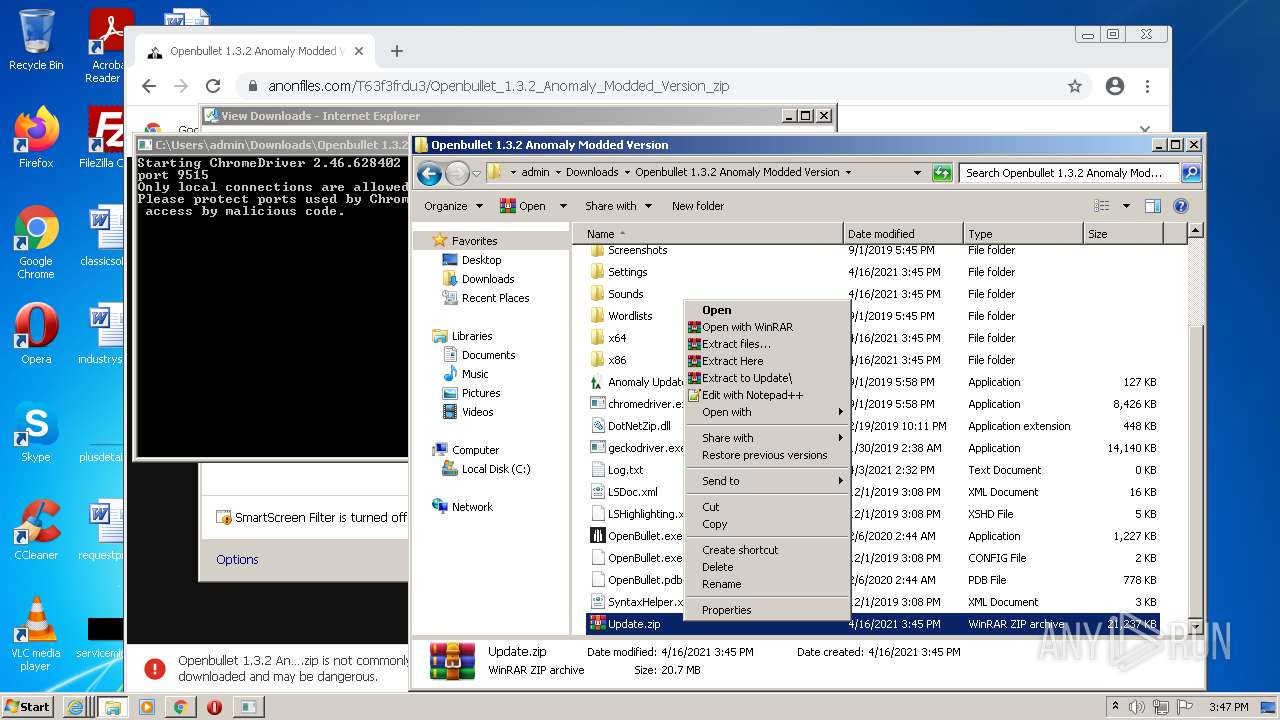
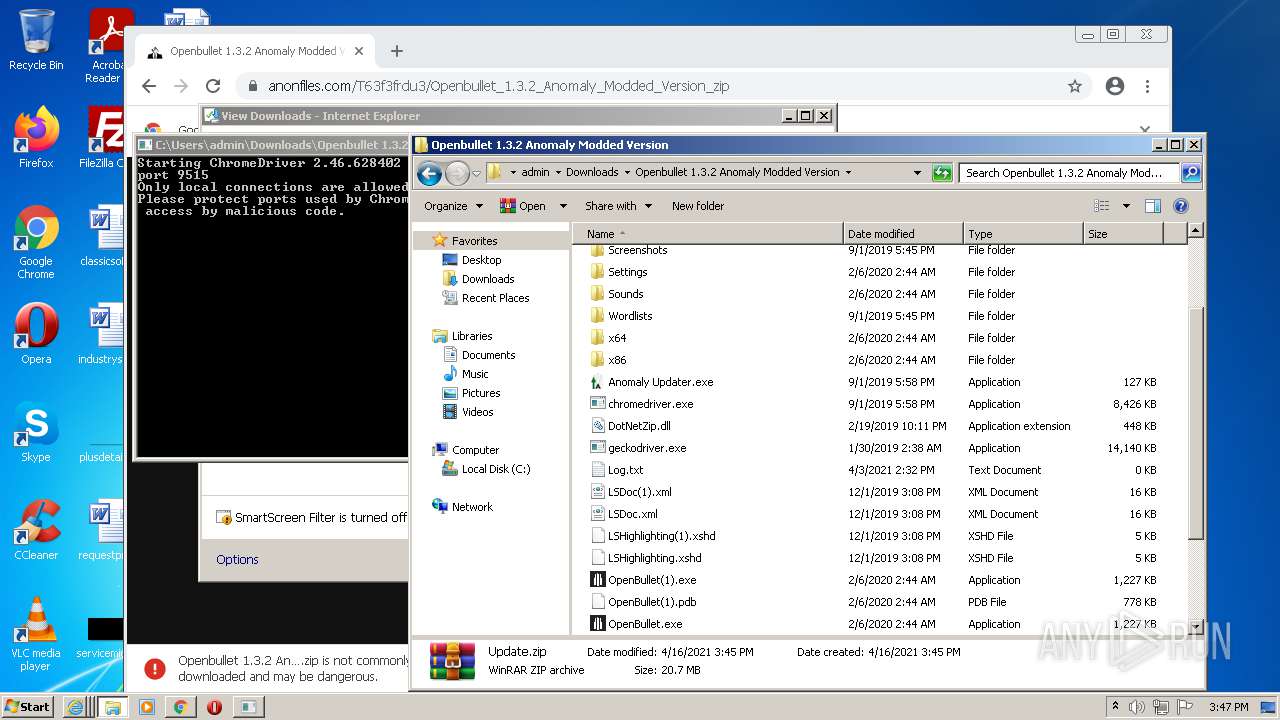
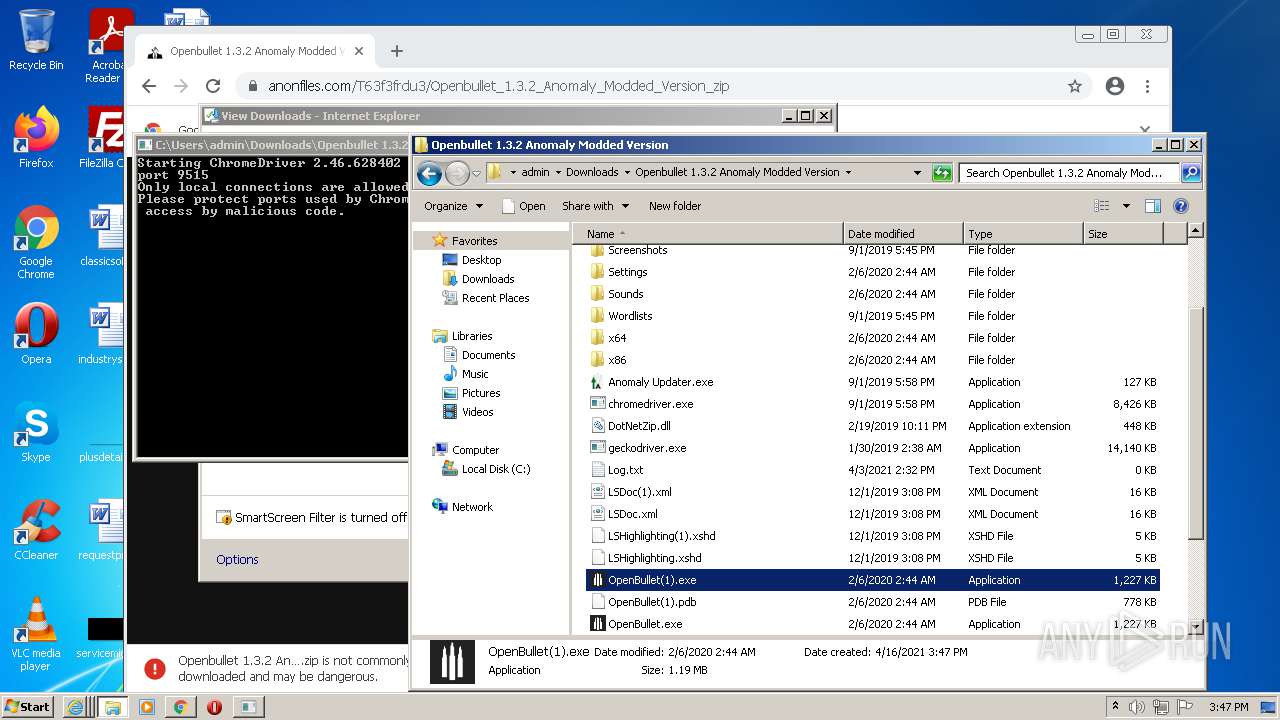
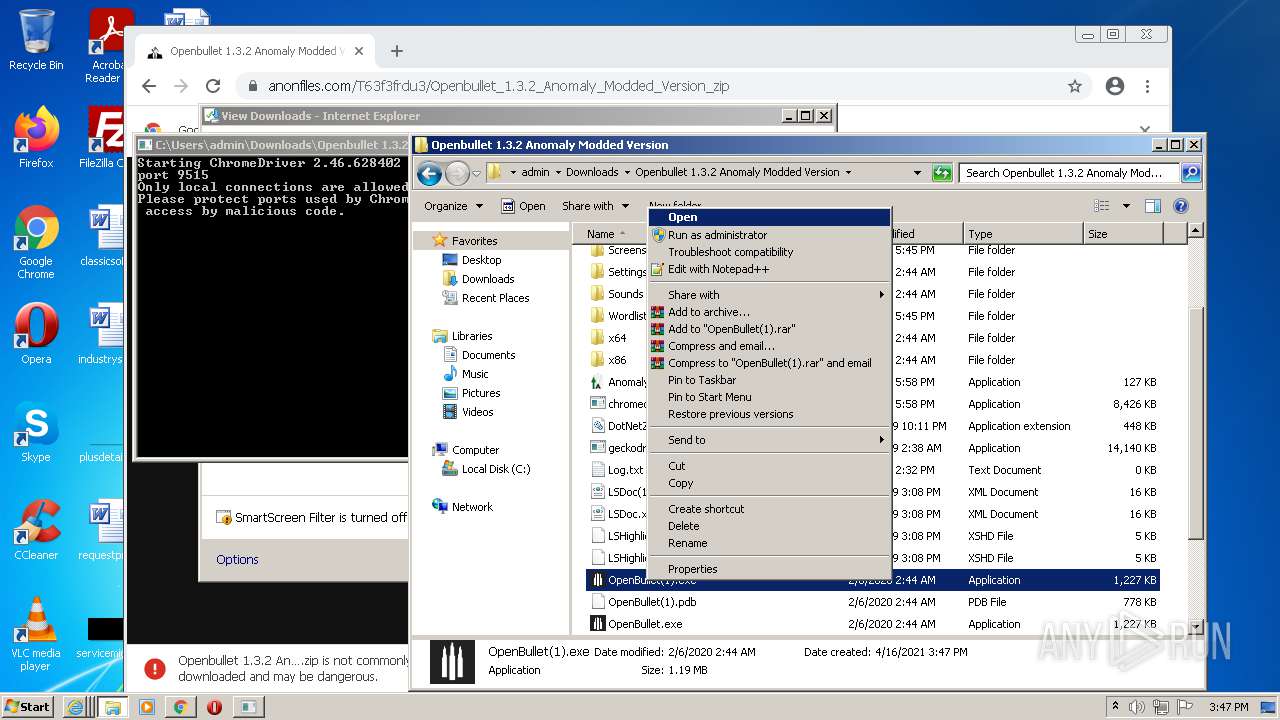
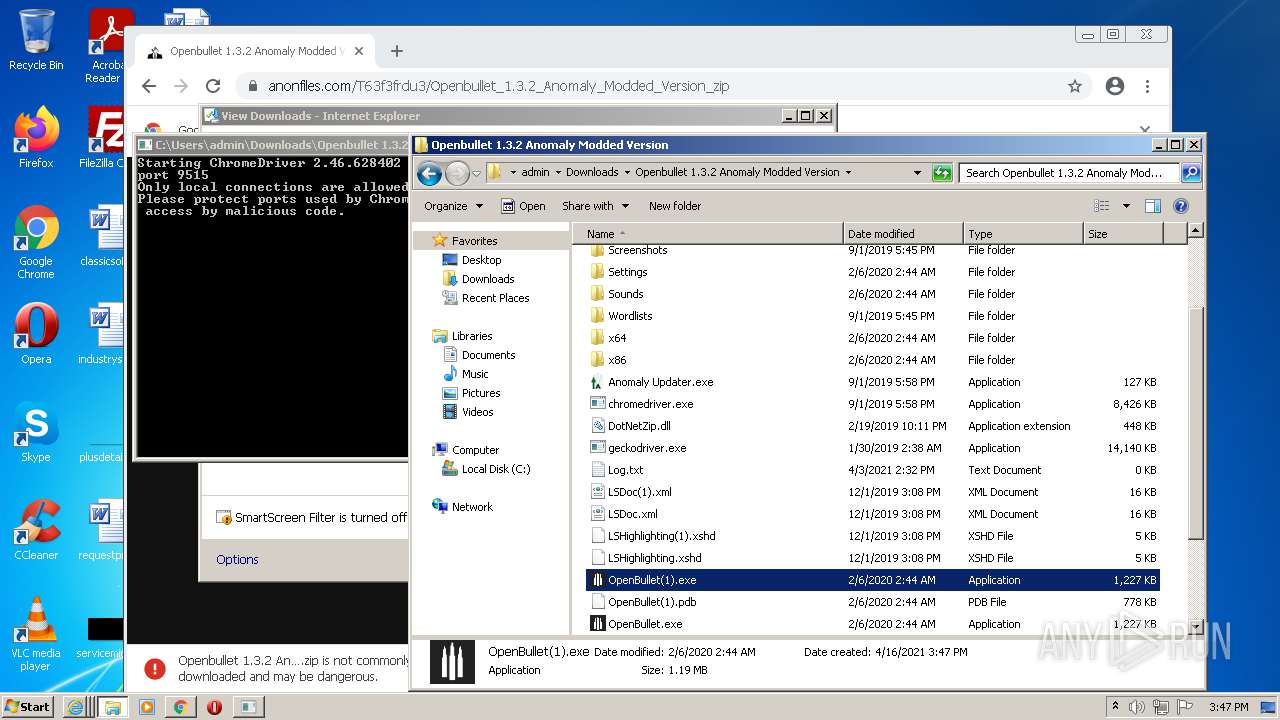
| URL: | https://anonfiles.com/T63f3frdu3/Openbullet_1.3.2_Anomaly_Modded_Version_zip |
| Full analysis: | https://app.any.run/tasks/572da83a-5b54-449c-9798-77860b7ae770 |
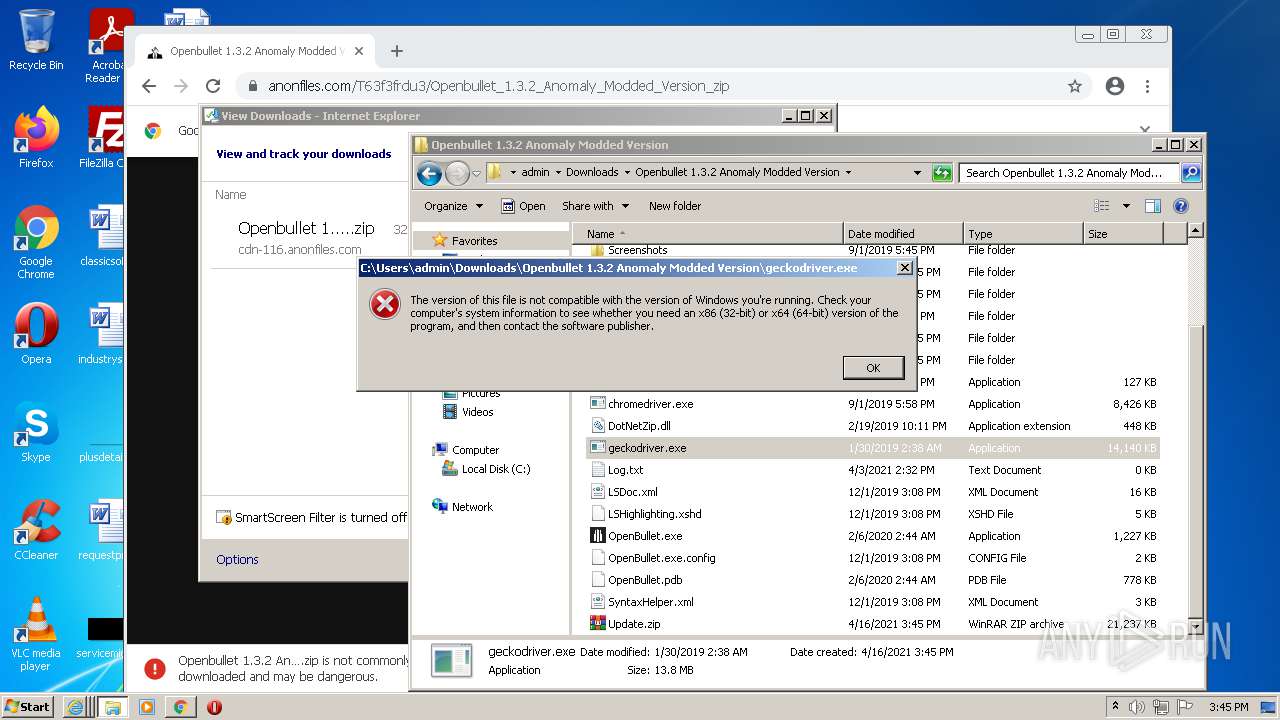
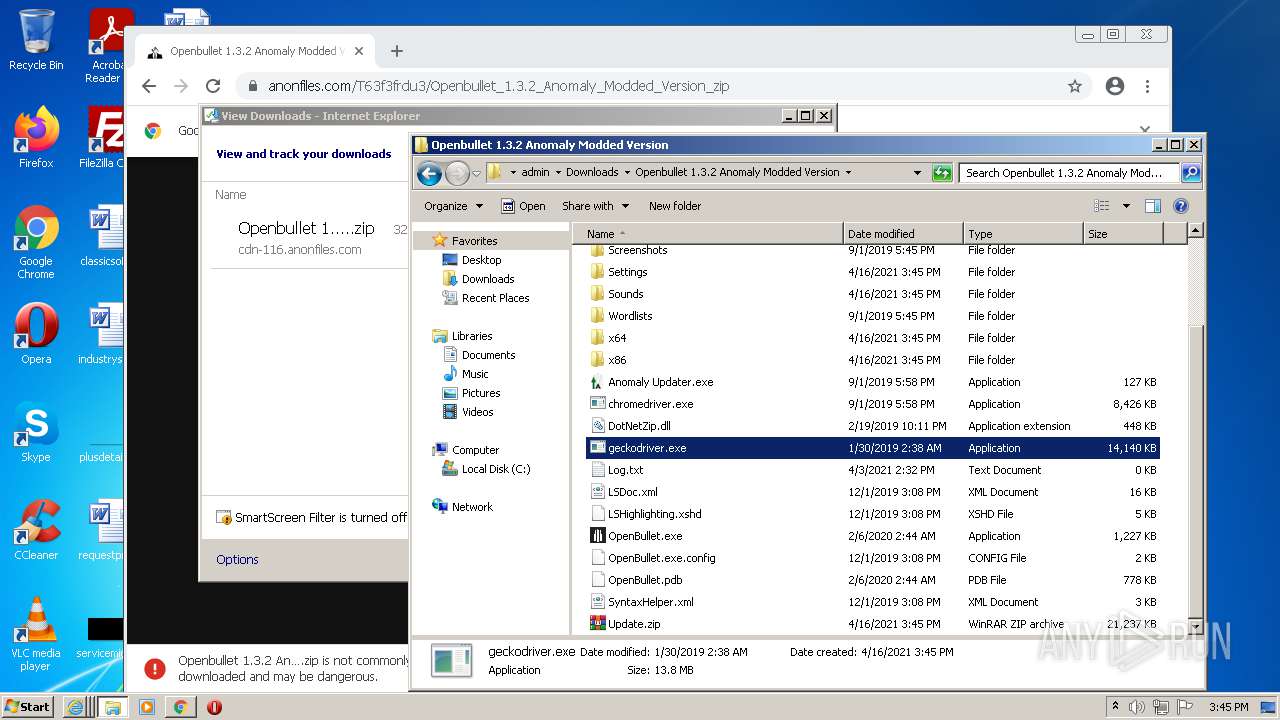
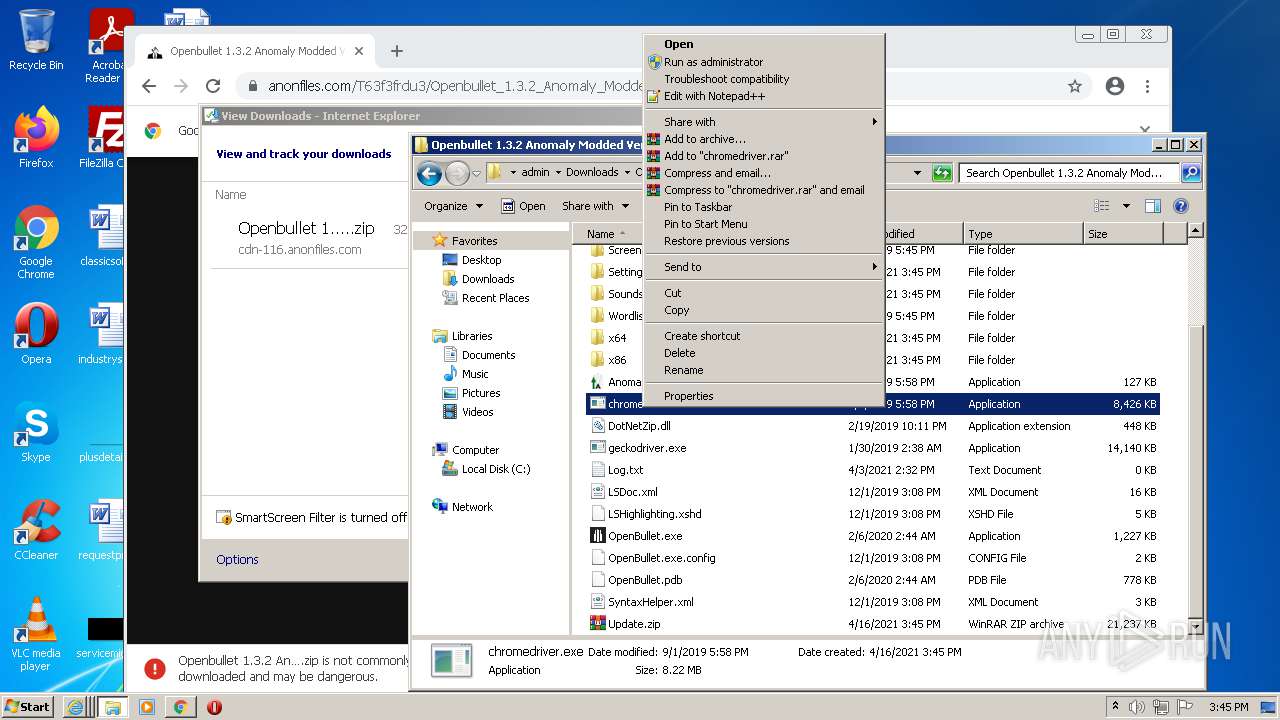
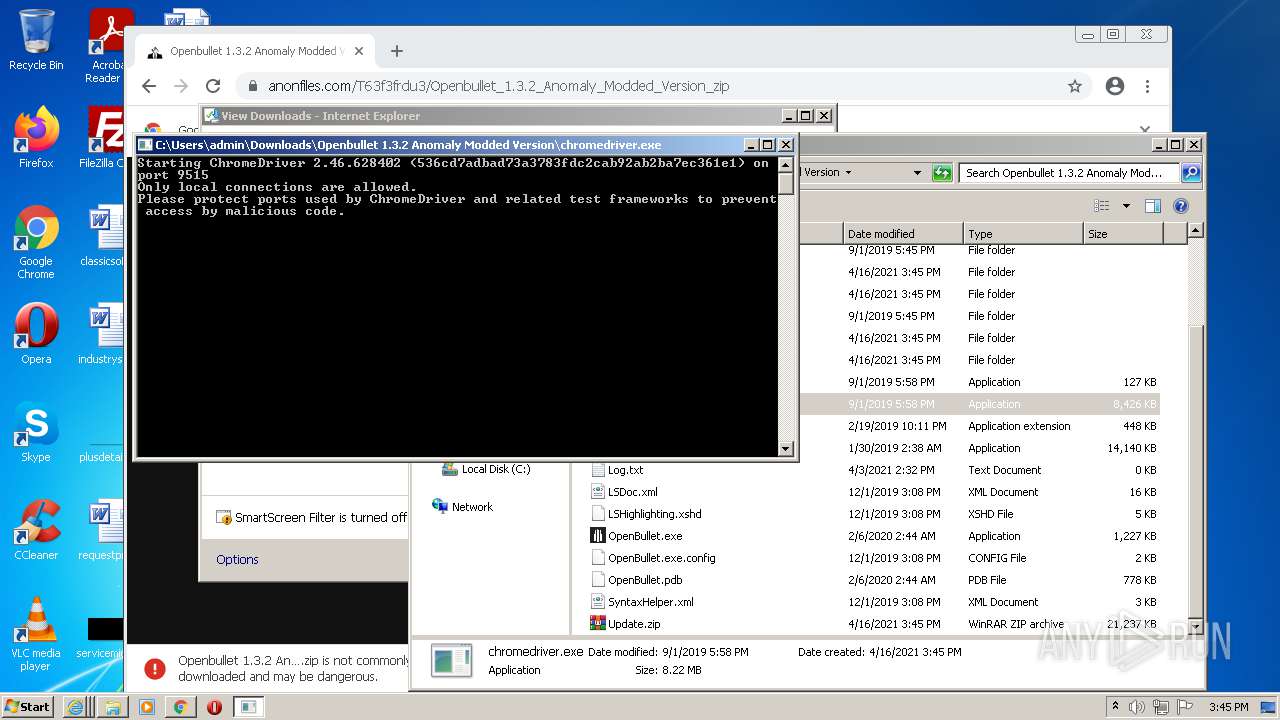
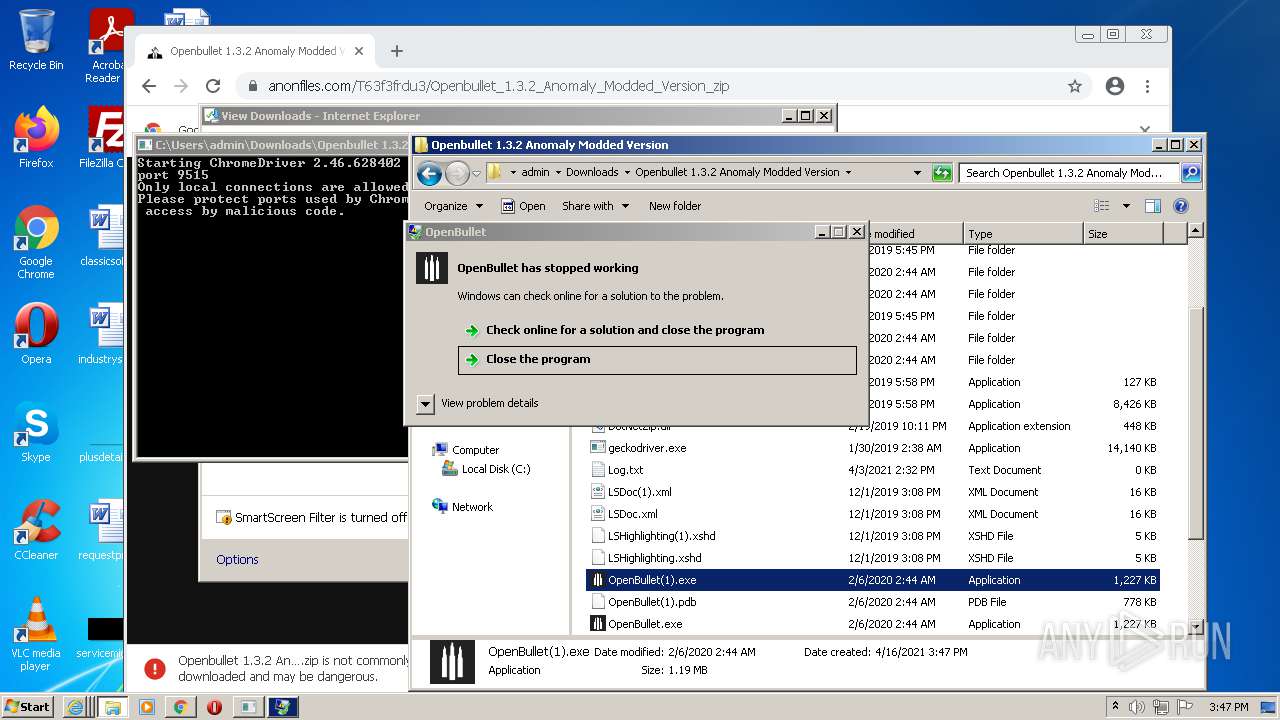
| Verdict: | Malicious activity |
| Analysis date: | April 16, 2021, 14:43:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 87D316916F8450CCDD85E11030E3ECF1 |
| SHA1: | 8B9BA51413901371C93FDC8F72DBC3AB7768E591 |
| SHA256: | 30D319BFE0F56D63873A6D716FCA21C0FD80D167BB6A3805EE6CCCF0A81C5604 |
| SSDEEP: | 3:N8M2ODxwsTEJAiwU:2M2exwcEifU |
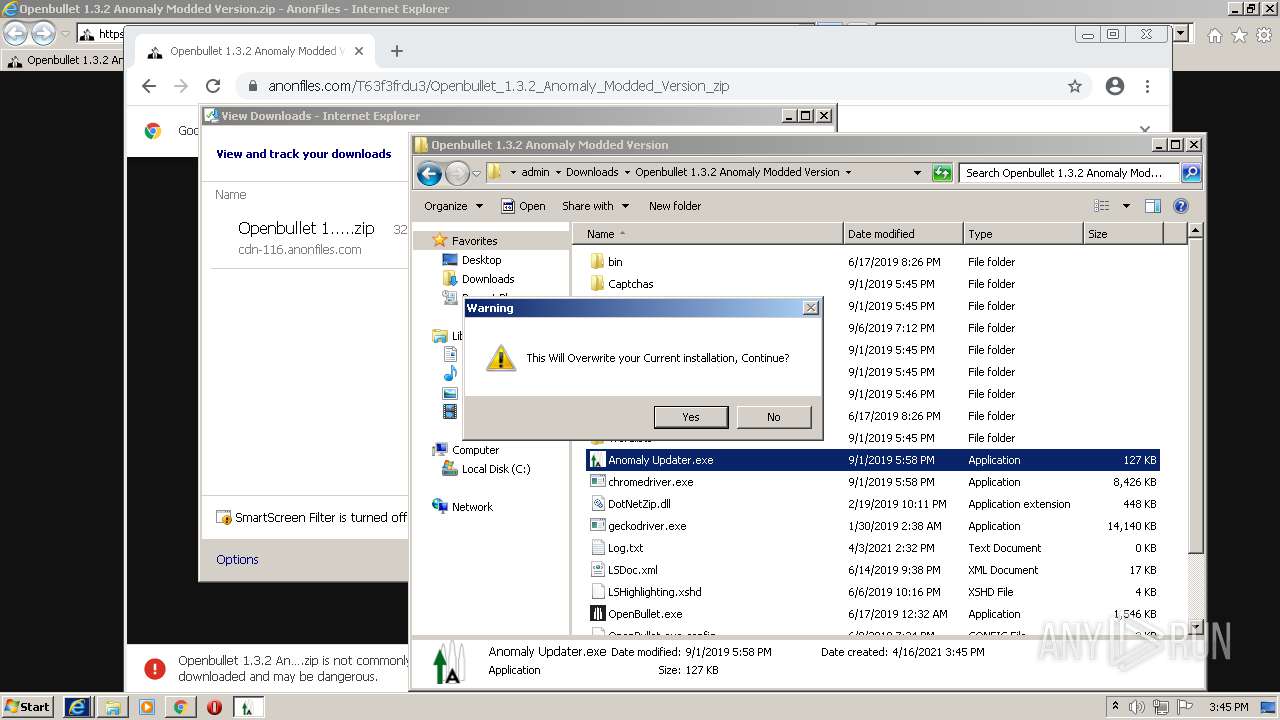
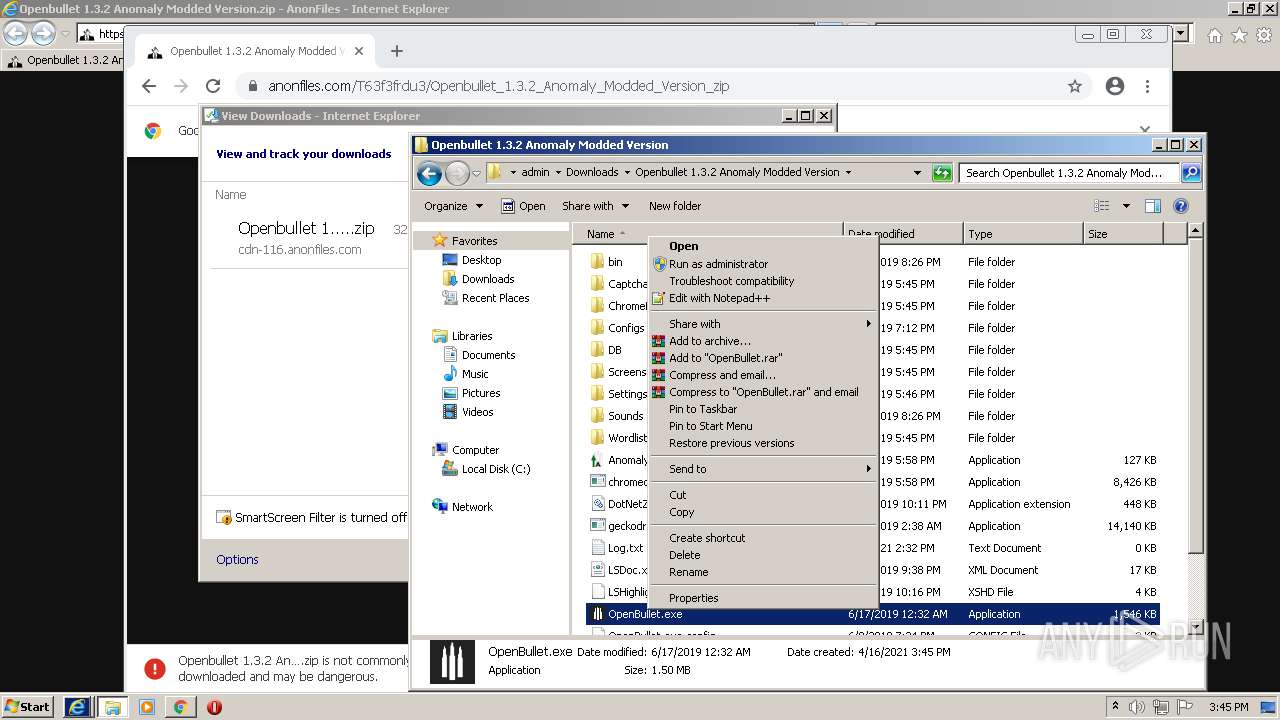
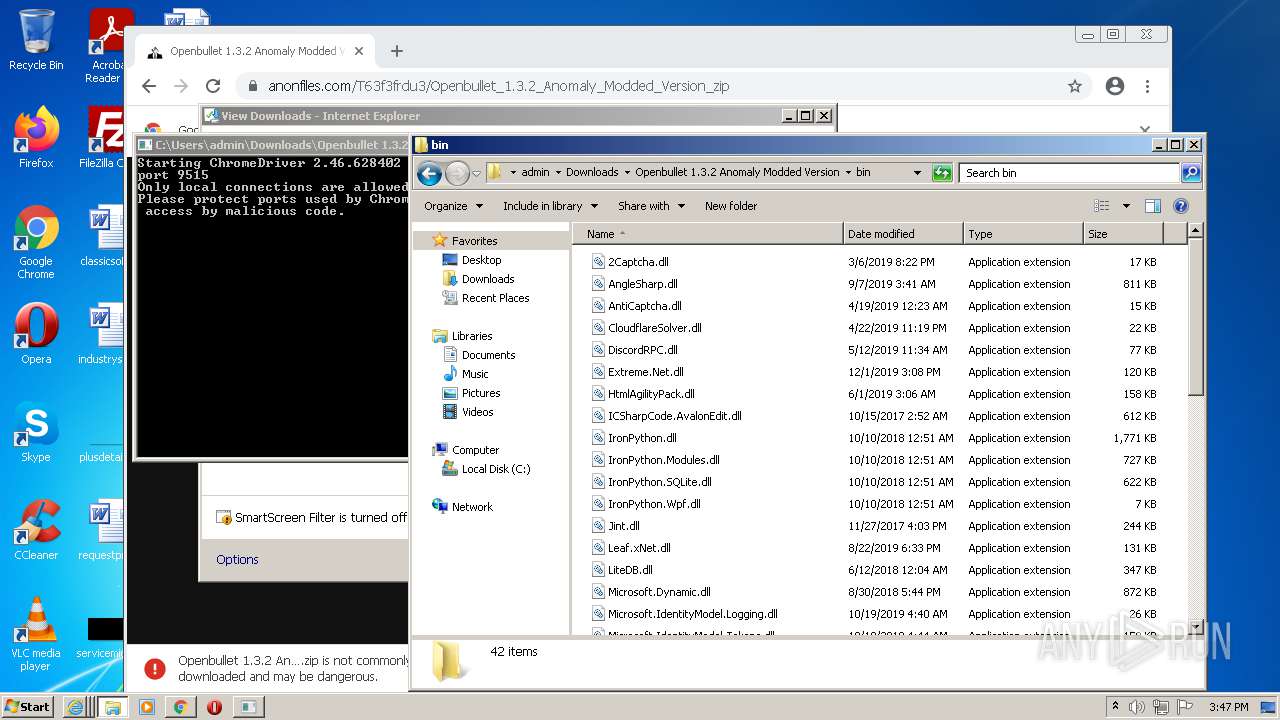
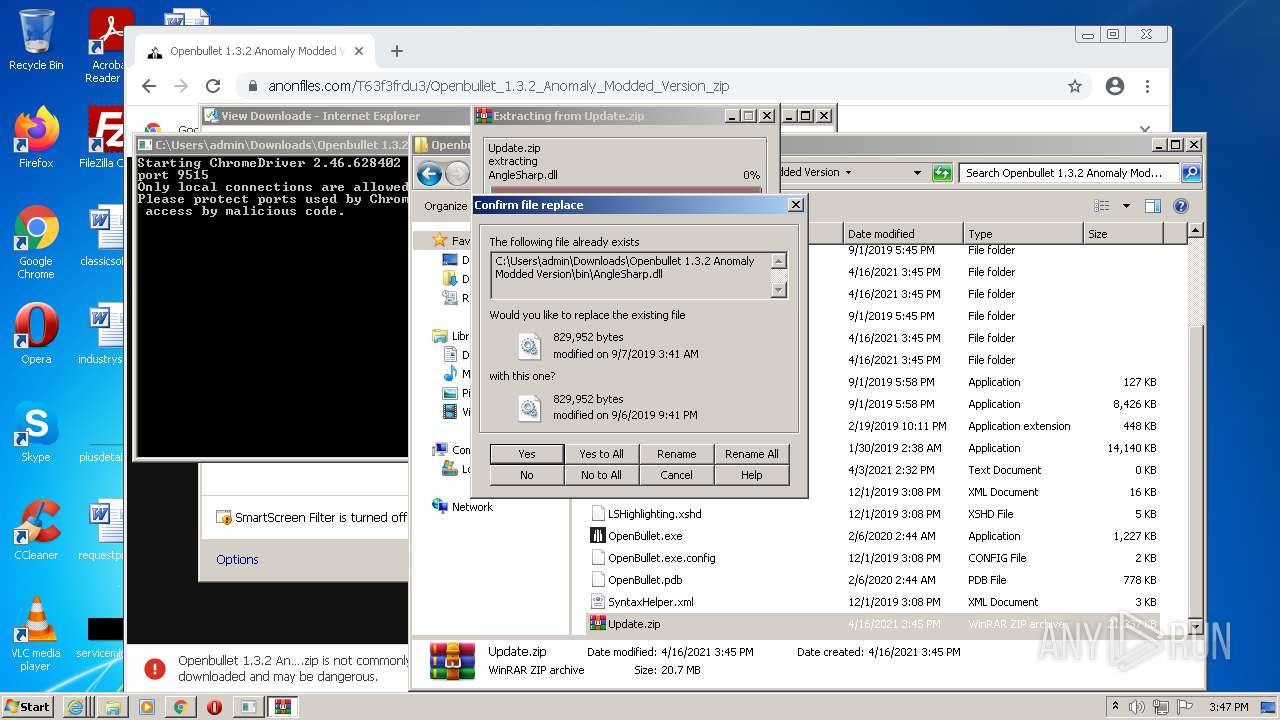
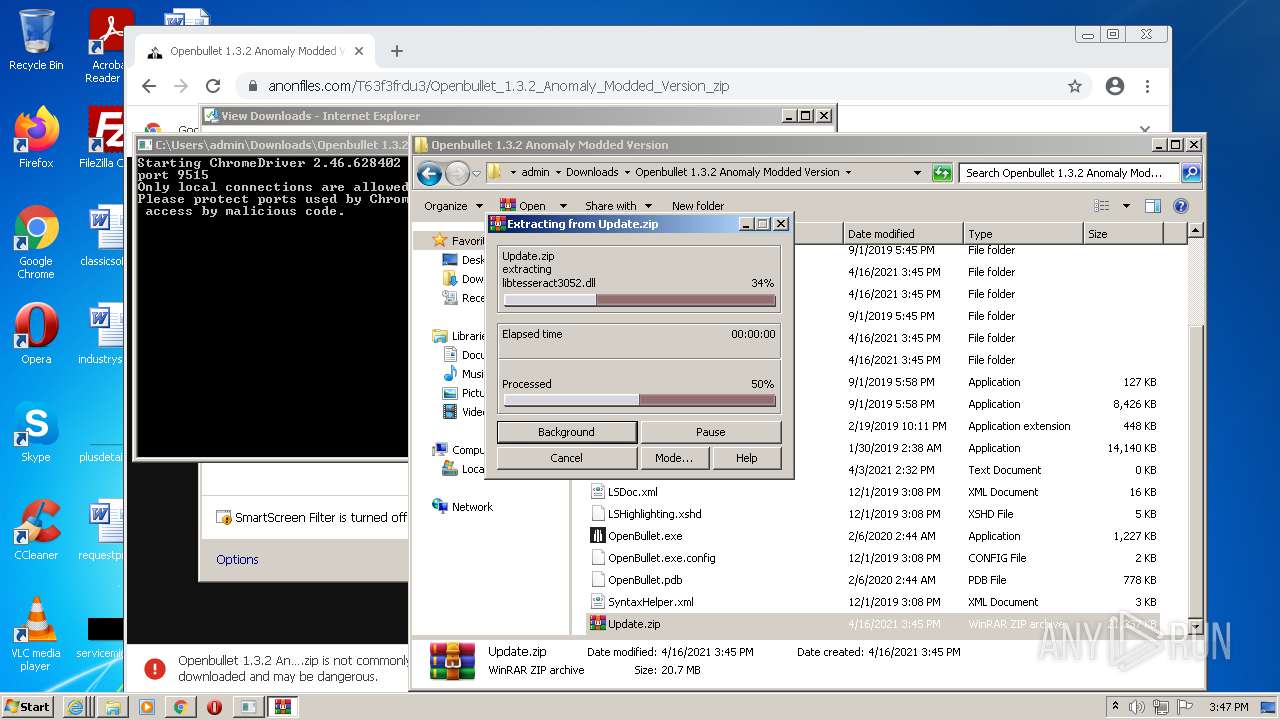
MALICIOUS
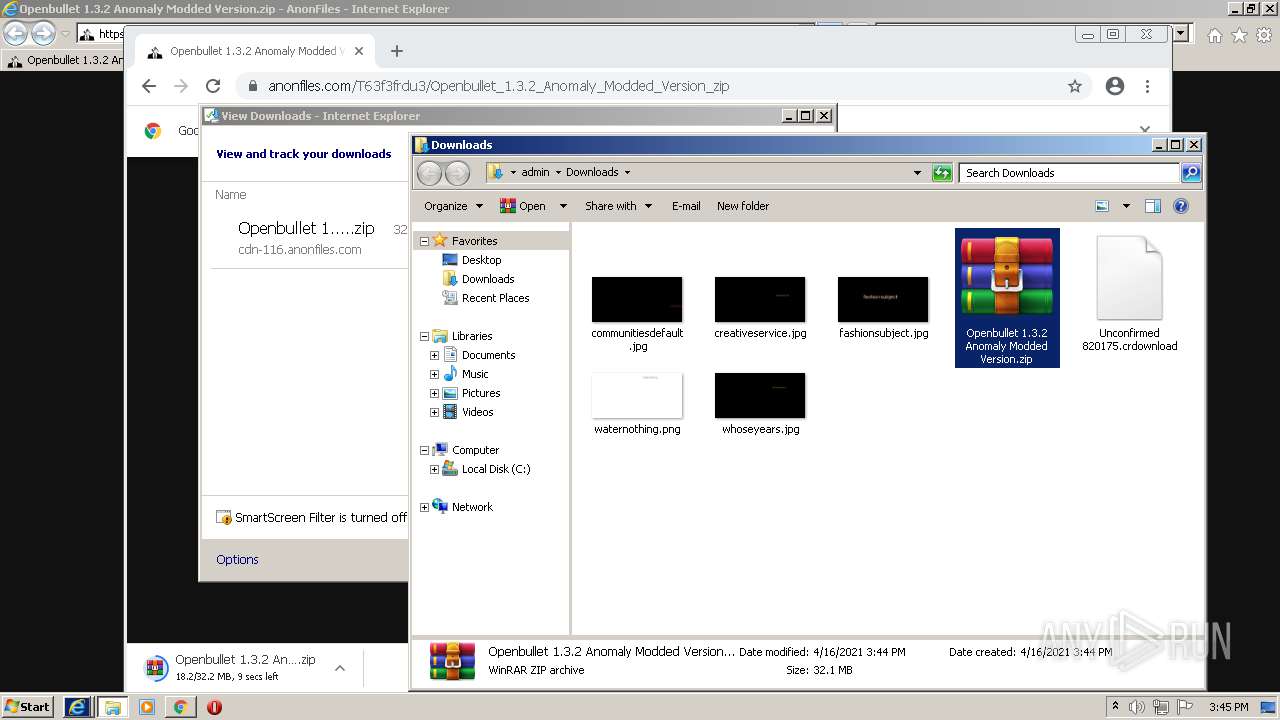
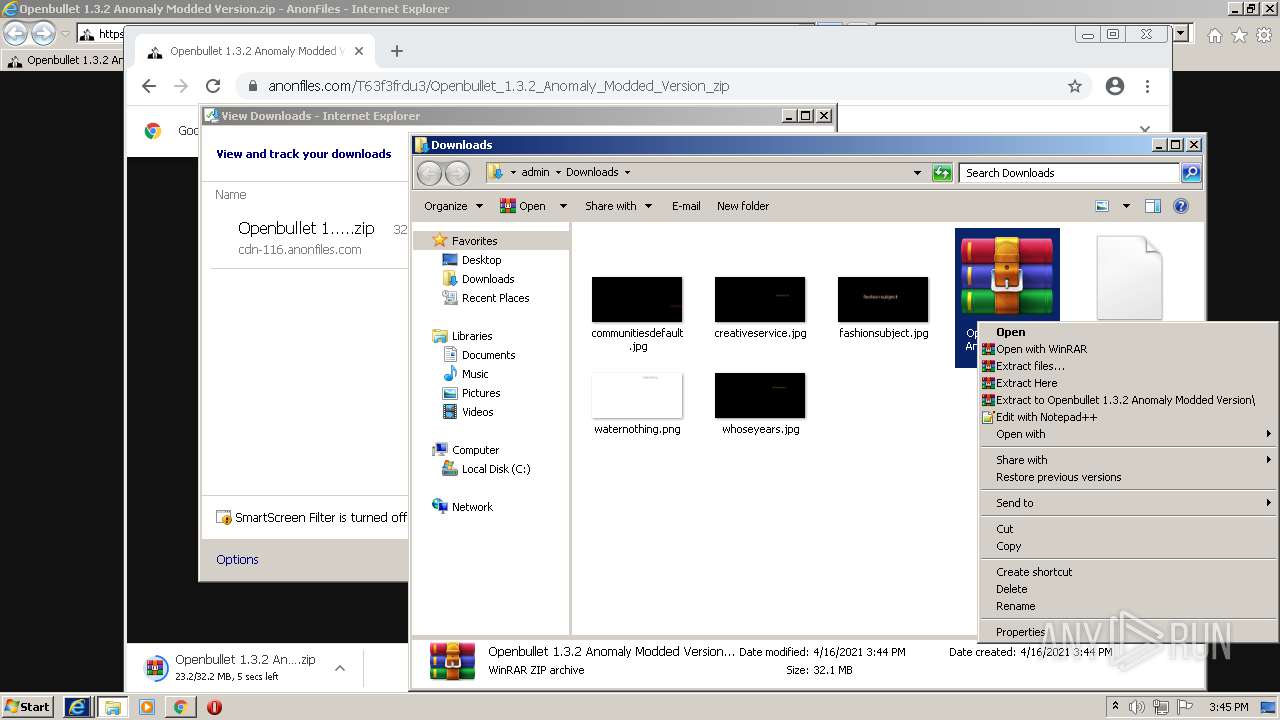
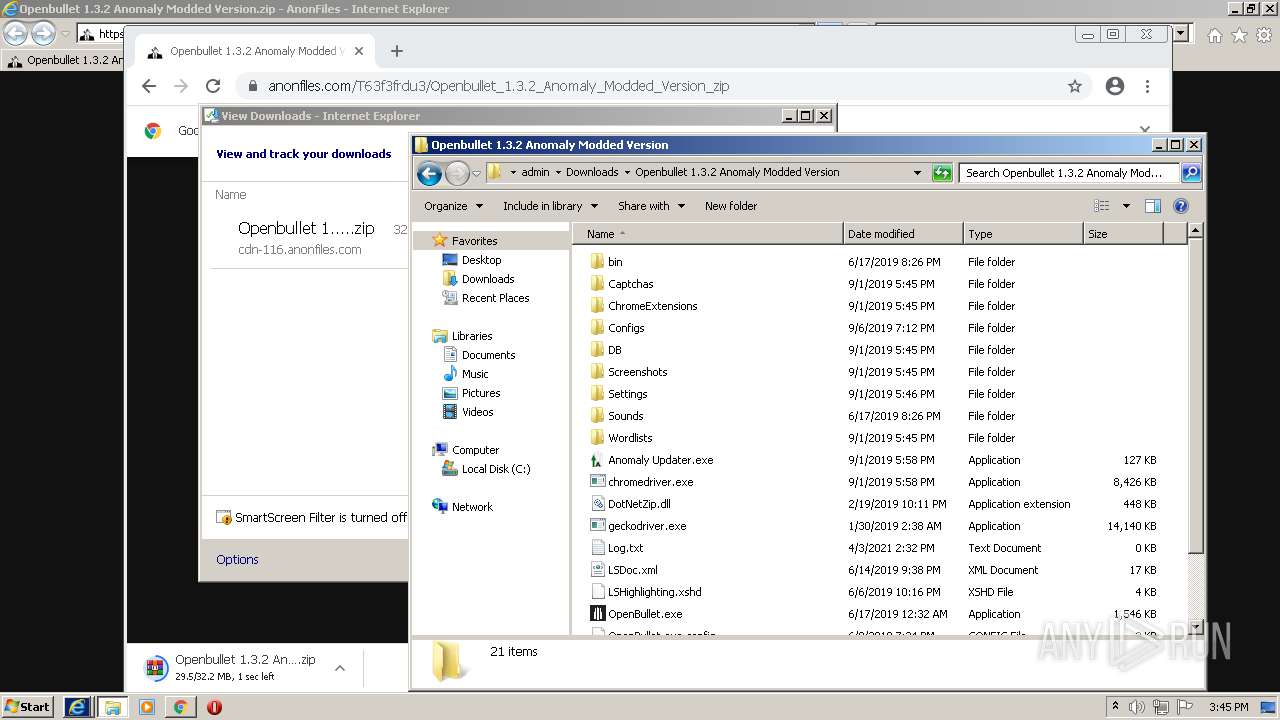
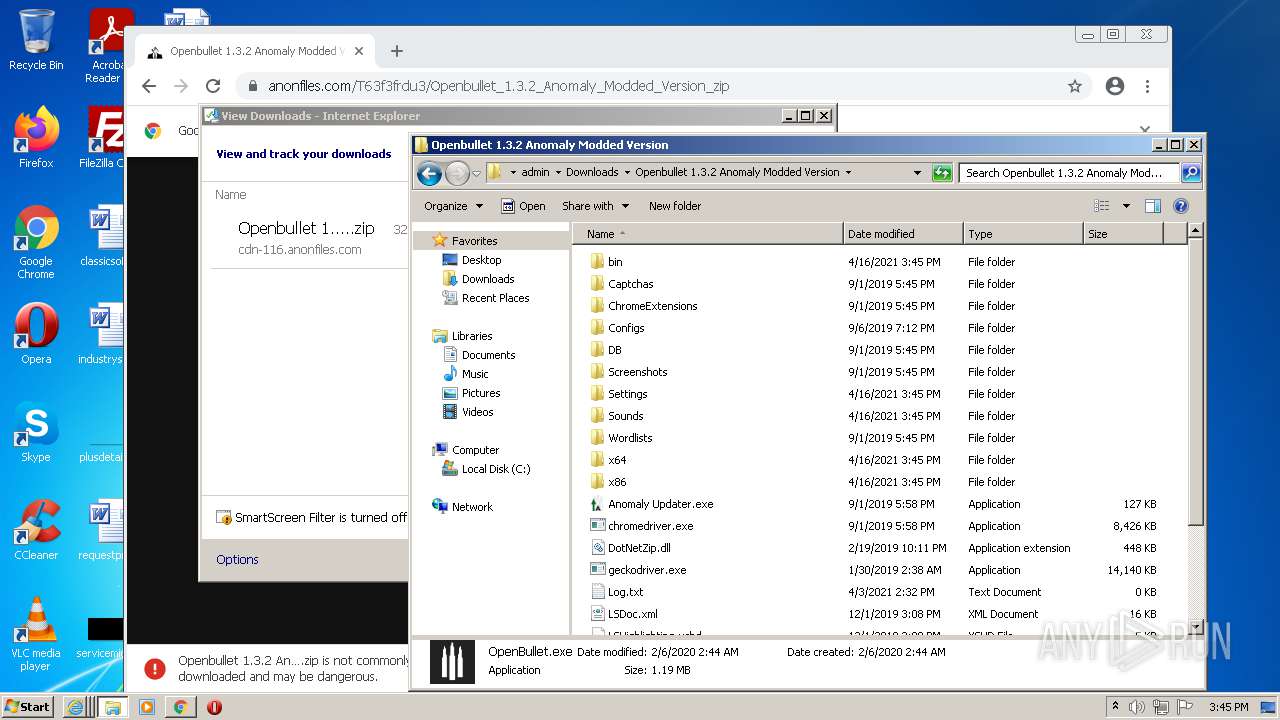
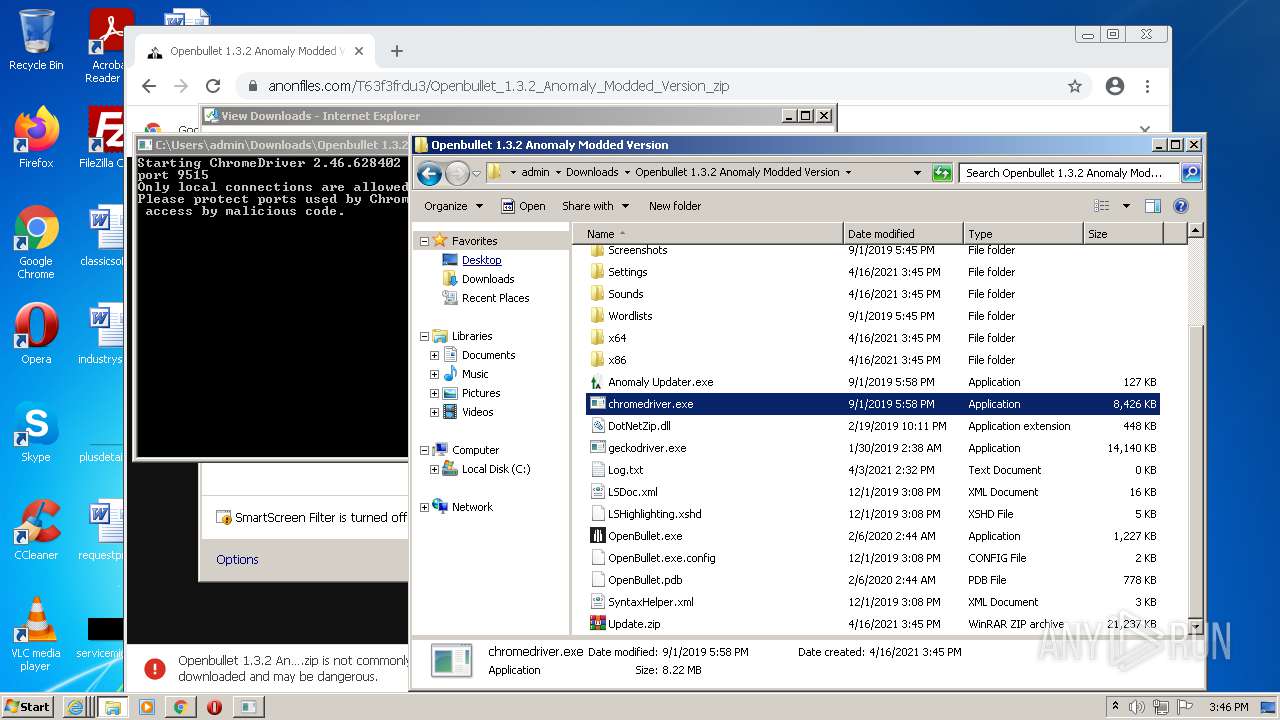
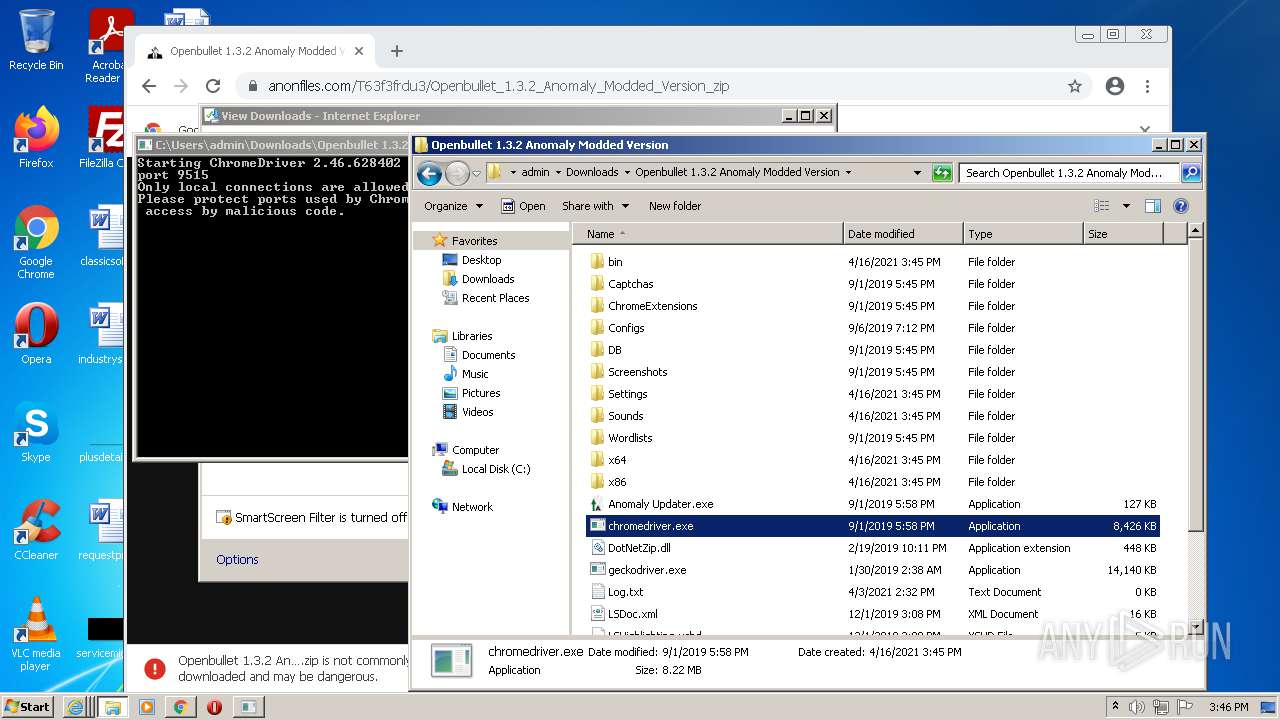
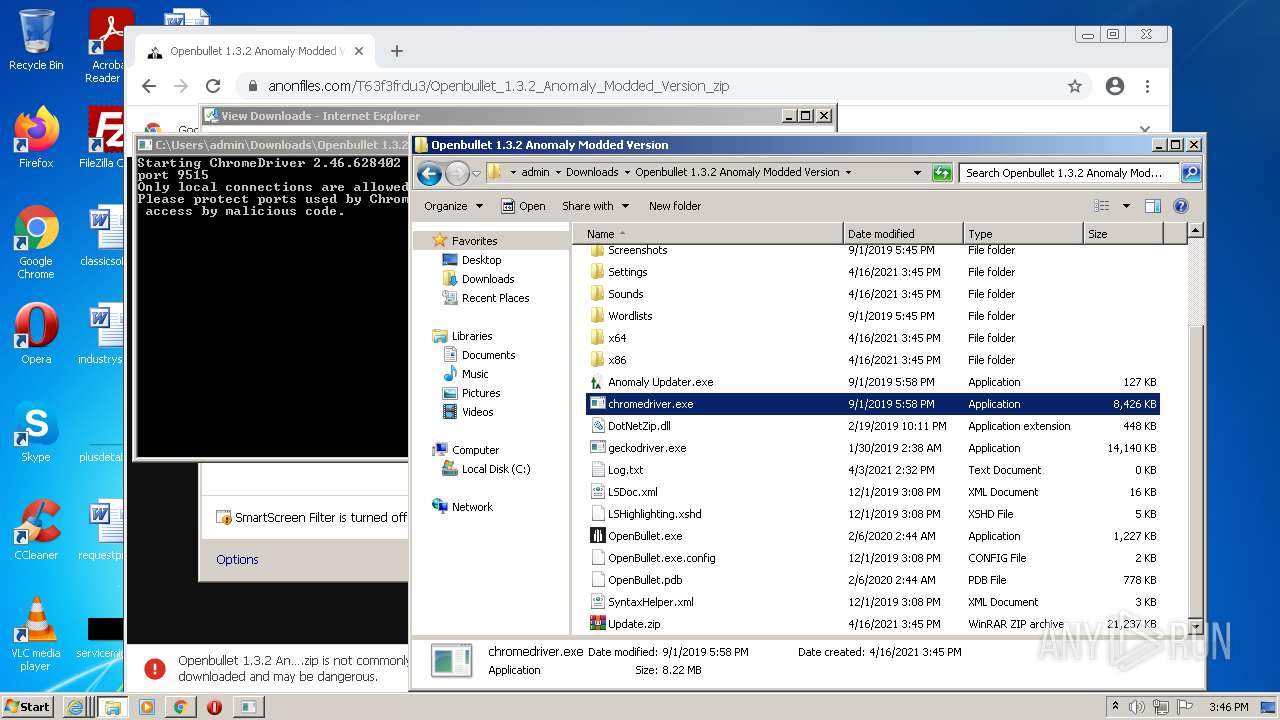
Drops executable file immediately after starts
- WinRAR.exe (PID: 2104)
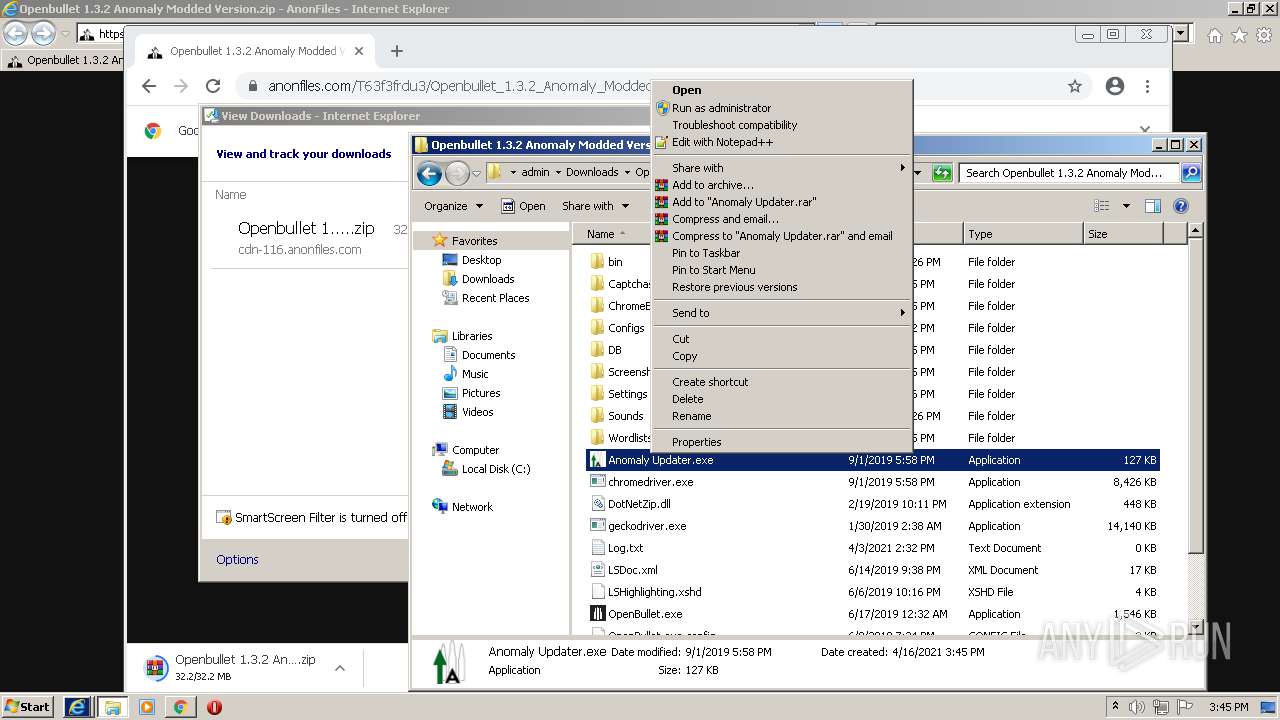
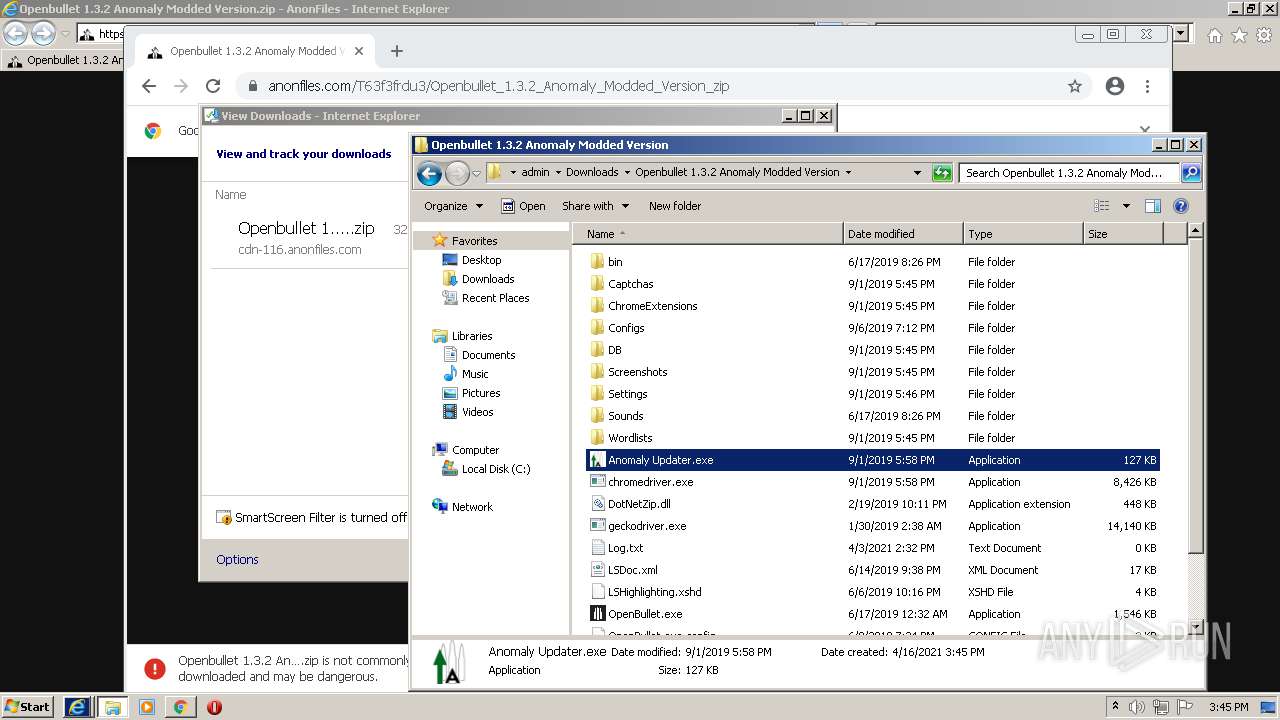
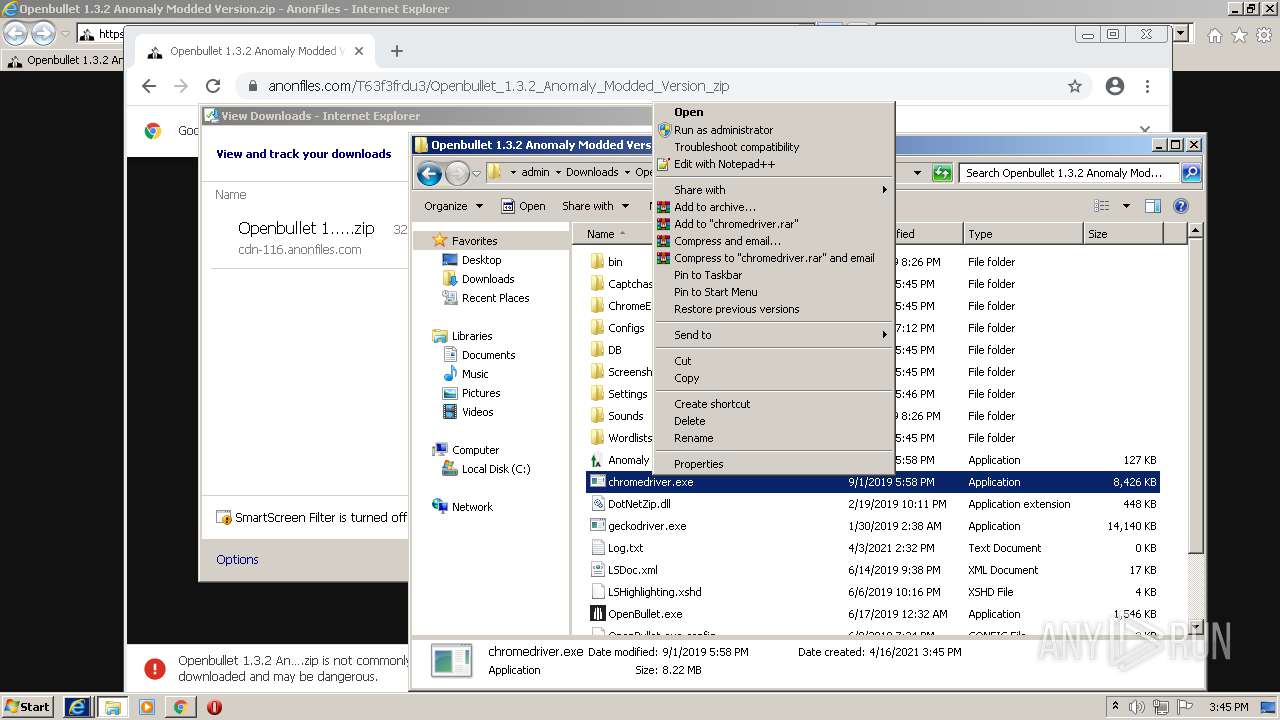
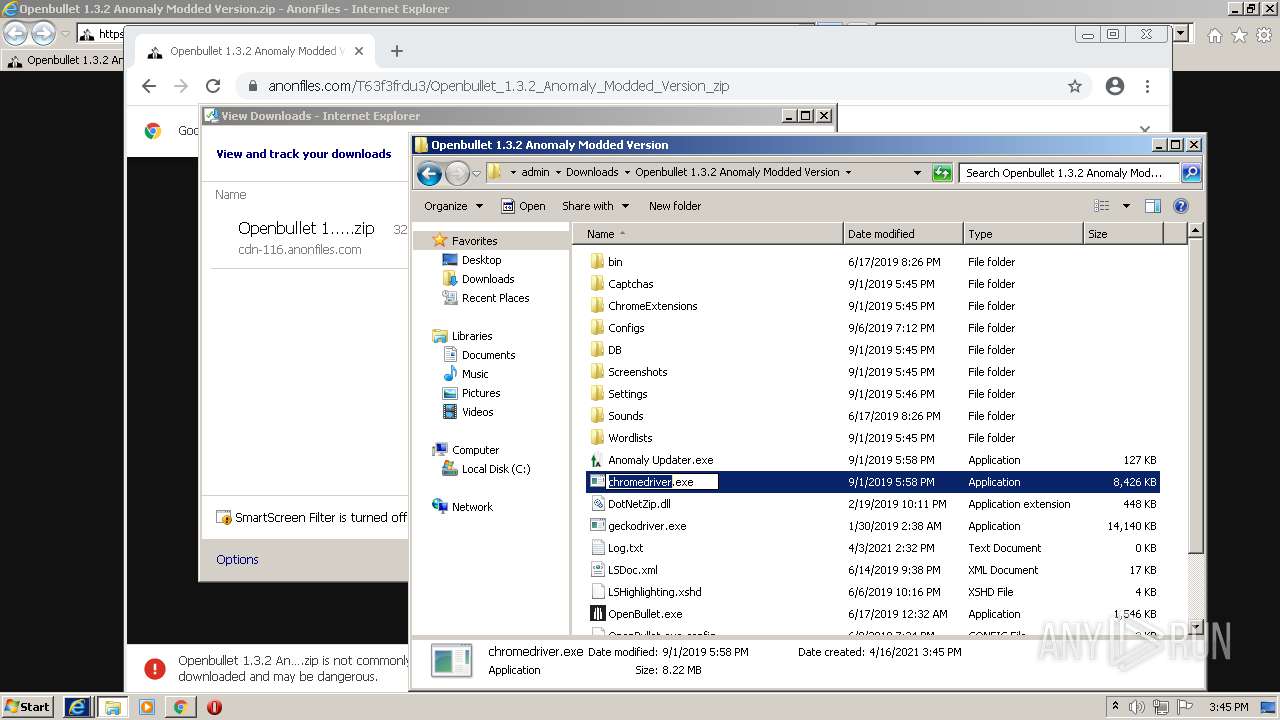
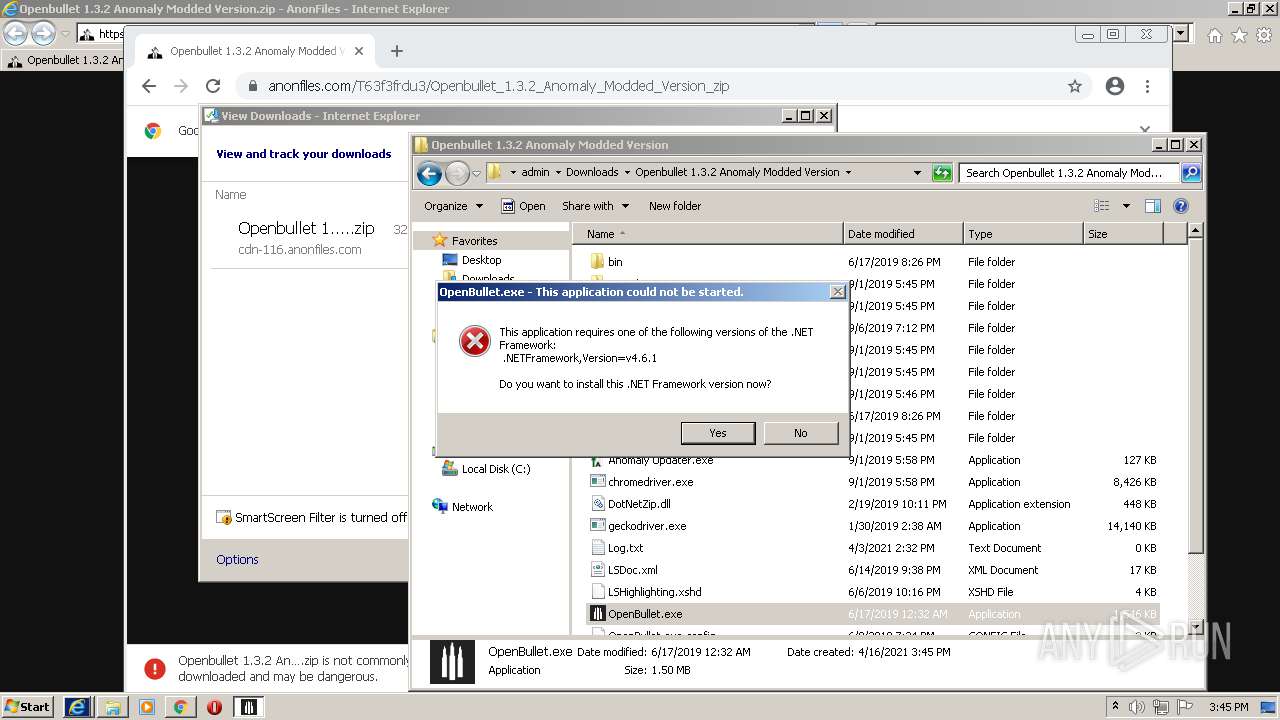
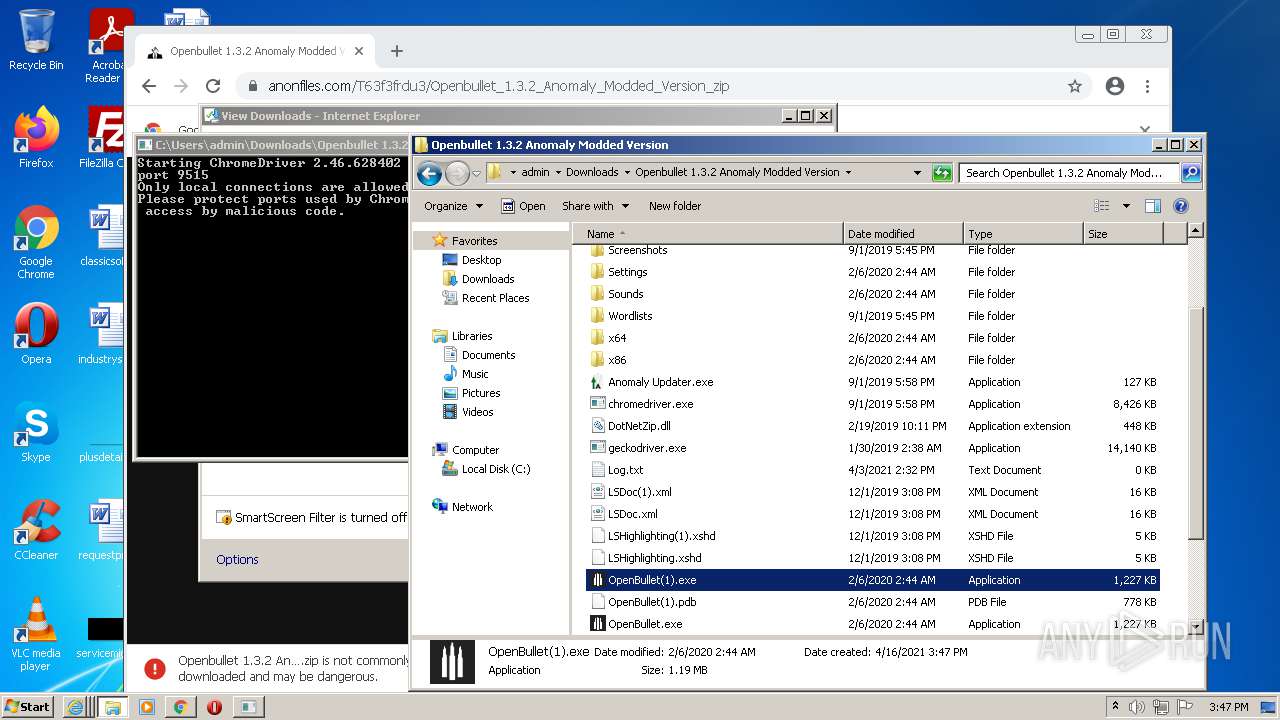
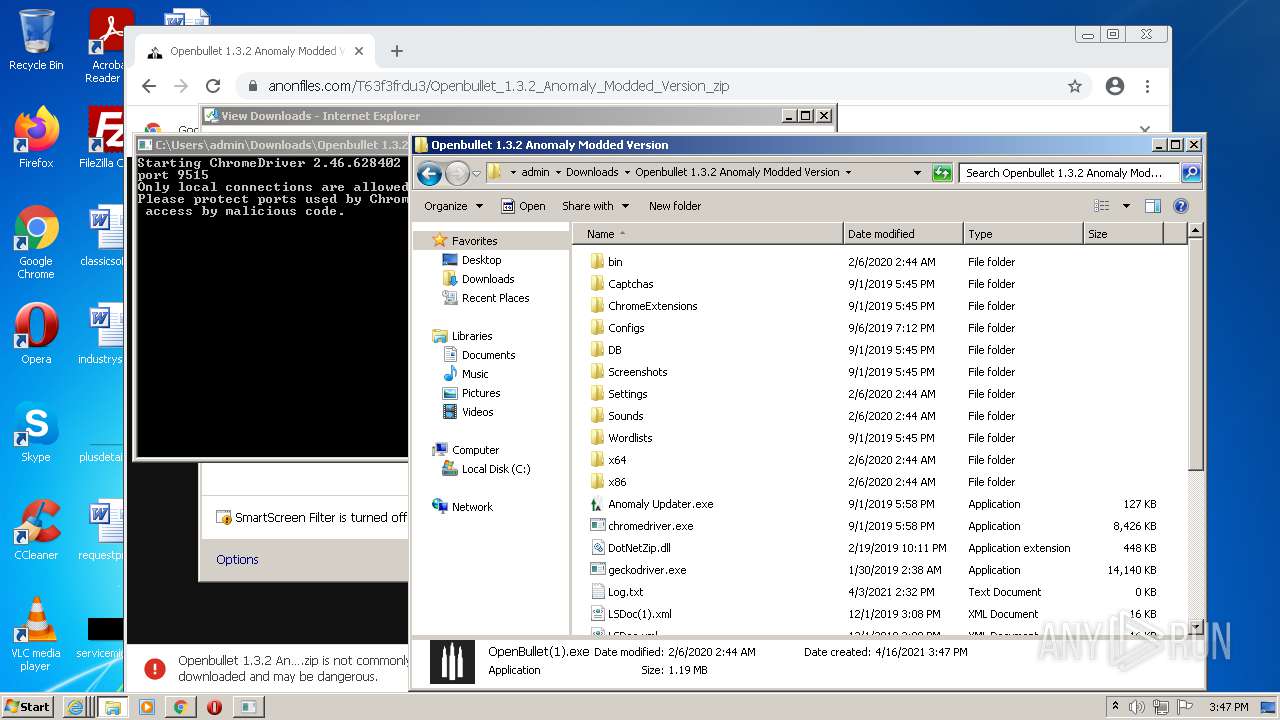
Application was dropped or rewritten from another process
- Anomaly Updater.exe (PID: 2112)
- OpenBullet.exe (PID: 1372)
- chromedriver.exe (PID: 2560)
- OpenBullet(1).exe (PID: 2792)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 304)
- Anomaly Updater.exe (PID: 2112)
- SearchProtocolHost.exe (PID: 648)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1292)
- iexplore.exe (PID: 3696)
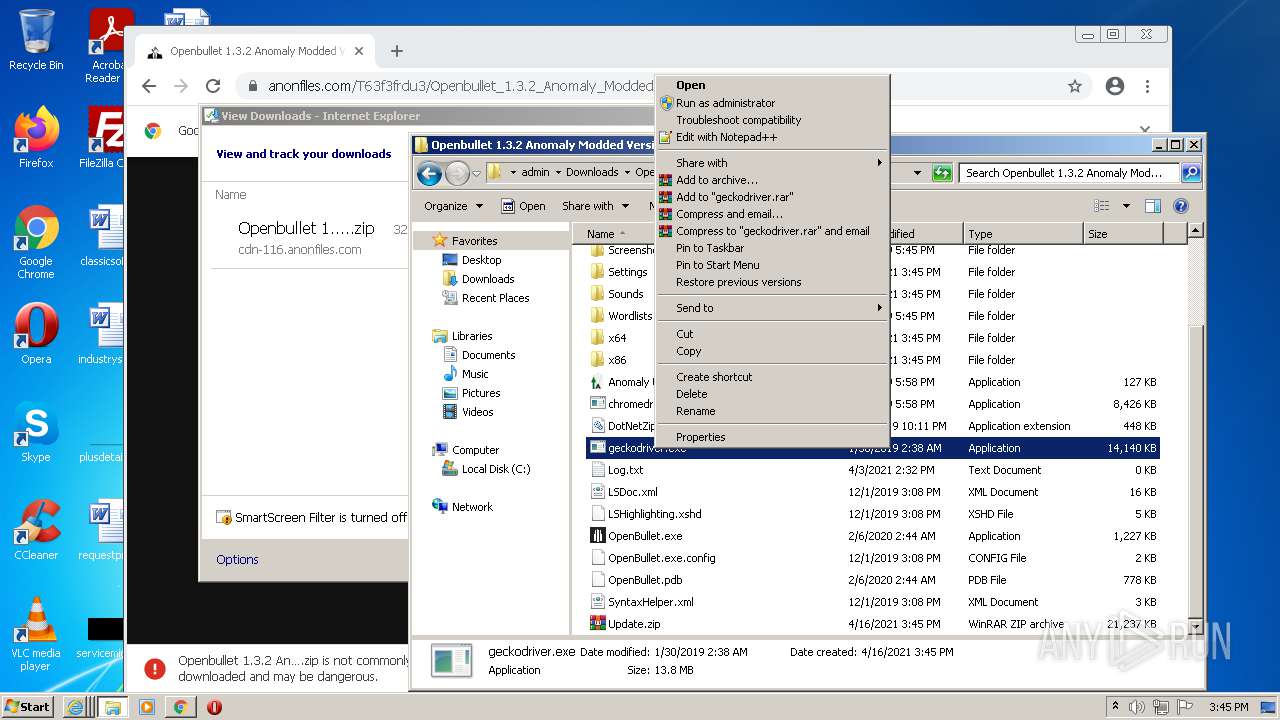
Modifies files in Chrome extension folder
- chrome.exe (PID: 3508)
Checks supported languages
- WinRAR.exe (PID: 2104)
- Anomaly Updater.exe (PID: 2112)
- OpenBullet.exe (PID: 1372)
- chromedriver.exe (PID: 2560)
- WinRAR.exe (PID: 2588)
- OpenBullet(1).exe (PID: 2792)
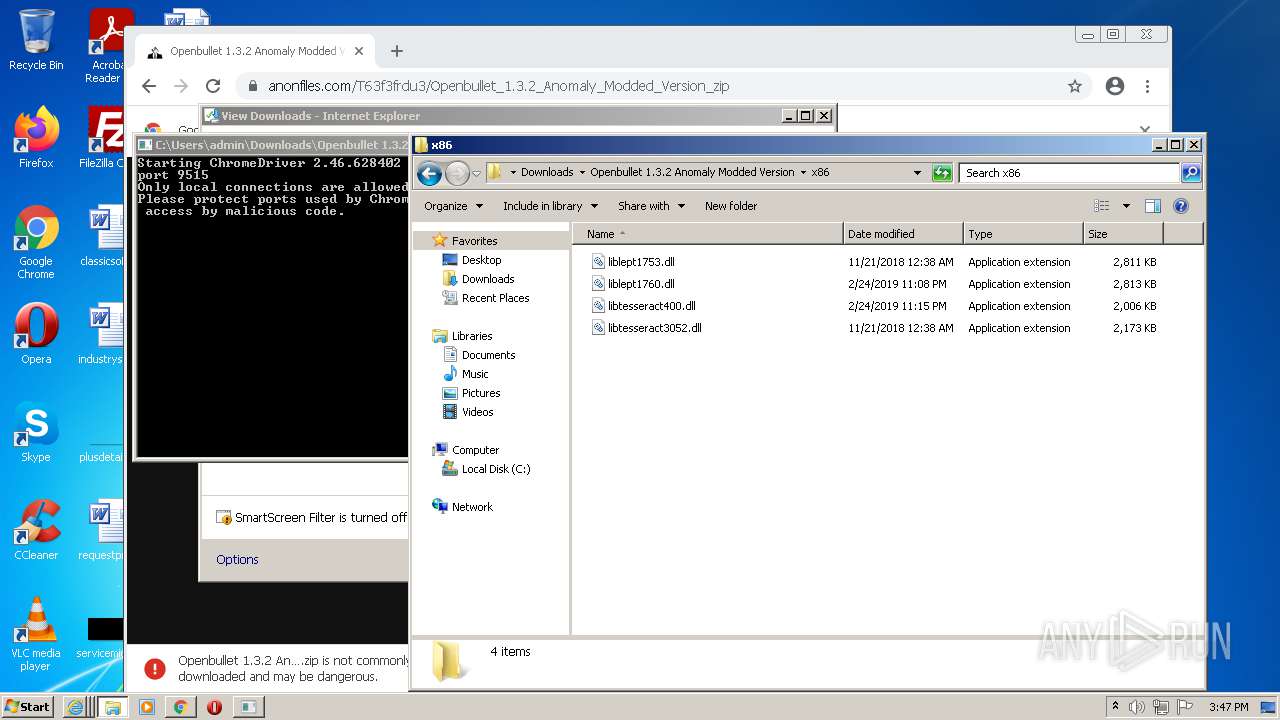
Drops a file with too old compile date
- WinRAR.exe (PID: 2104)
- Anomaly Updater.exe (PID: 2112)
- WinRAR.exe (PID: 2588)
Reads the computer name
- WinRAR.exe (PID: 2104)
- Anomaly Updater.exe (PID: 2112)
- chromedriver.exe (PID: 2560)
- WinRAR.exe (PID: 2588)
- OpenBullet(1).exe (PID: 2792)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2104)
- chrome.exe (PID: 3688)
- Anomaly Updater.exe (PID: 2112)
- WinRAR.exe (PID: 2588)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2104)
- Anomaly Updater.exe (PID: 2112)
- WinRAR.exe (PID: 2588)
- chrome.exe (PID: 3688)
Reads Environment values
- Anomaly Updater.exe (PID: 2112)
INFO
Checks supported languages
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 1292)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 3776)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 2528)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 572)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 2968)
- chrome.exe (PID: 1400)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 3208)
- chrome.exe (PID: 968)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 1772)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 284)
- chrome.exe (PID: 1900)
- chrome.exe (PID: 2492)
- iexplore.exe (PID: 3696)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 2280)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 980)
- chrome.exe (PID: 1816)
- chrome.exe (PID: 668)
- SearchProtocolHost.exe (PID: 648)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 3264)
Application launched itself
- iexplore.exe (PID: 3632)
- chrome.exe (PID: 3508)
Reads the computer name
- iexplore.exe (PID: 1292)
- iexplore.exe (PID: 3632)
- chrome.exe (PID: 3508)
- chrome.exe (PID: 3412)
- chrome.exe (PID: 2456)
- chrome.exe (PID: 572)
- chrome.exe (PID: 968)
- chrome.exe (PID: 1900)
- chrome.exe (PID: 2492)
- iexplore.exe (PID: 3696)
- chrome.exe (PID: 3564)
- SearchProtocolHost.exe (PID: 648)
Changes internet zones settings
- iexplore.exe (PID: 3632)
Reads settings of System Certificates
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 1292)
- chrome.exe (PID: 3412)
- Anomaly Updater.exe (PID: 2112)
- iexplore.exe (PID: 3696)
Checks Windows Trust Settings
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 1292)
- iexplore.exe (PID: 3696)
Creates files in the user directory
- iexplore.exe (PID: 1292)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3696)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3632)
Reads internet explorer settings
- iexplore.exe (PID: 1292)
- iexplore.exe (PID: 3696)
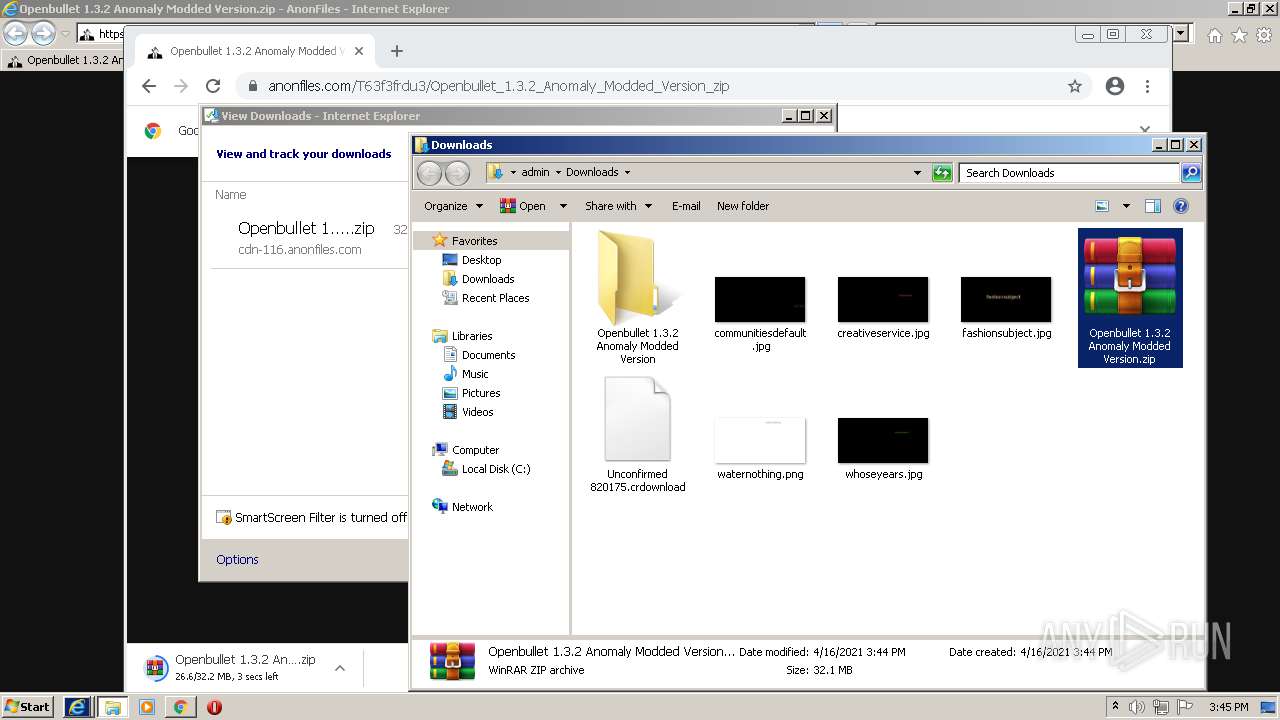
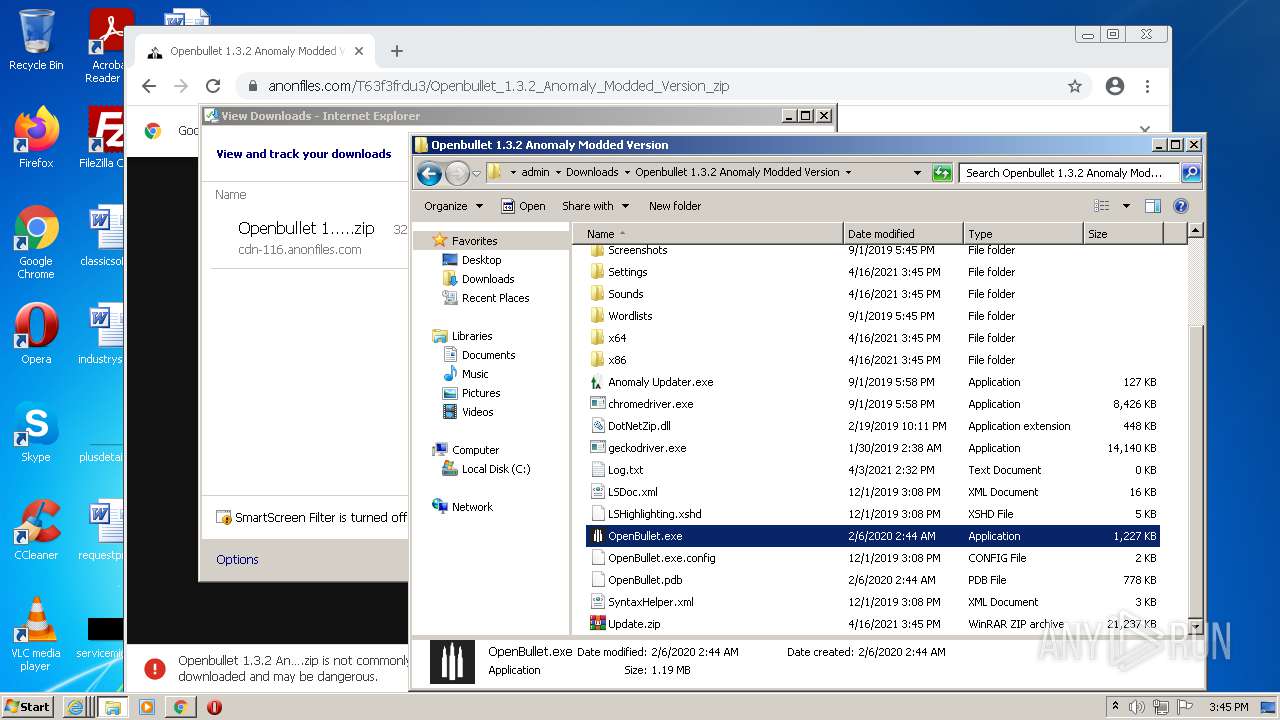
Manual execution by user
- chrome.exe (PID: 3508)
- WinRAR.exe (PID: 2104)
- Anomaly Updater.exe (PID: 2112)
- OpenBullet.exe (PID: 1372)
- chromedriver.exe (PID: 2560)
- WinRAR.exe (PID: 2588)
- OpenBullet(1).exe (PID: 2792)
Reads the hosts file
- chrome.exe (PID: 3508)
- chrome.exe (PID: 3412)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3632)
Changes settings of System certificates
- iexplore.exe (PID: 3632)
Reads the date of Windows installation
- chrome.exe (PID: 2492)
Dropped object may contain Bitcoin addresses
- Anomaly Updater.exe (PID: 2112)
- WinRAR.exe (PID: 2588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
104
Monitored processes
40
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,18229018541471866697,11243884708663524644,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3564 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 304 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,18229018541471866697,11243884708663524644,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 648 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe7_ Global\UsGthrCtrlFltPipeMssGthrPipe7 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,18229018541471866697,11243884708663524644,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,18229018541471866697,11243884708663524644,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3152 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,18229018541471866697,11243884708663524644,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3632 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1372 | "C:\Users\admin\Downloads\Openbullet 1.3.2 Anomaly Modded Version\OpenBullet.exe" | C:\Users\admin\Downloads\Openbullet 1.3.2 Anomaly Modded Version\OpenBullet.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Description: OpenBullet Exit code: 2148734720 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,18229018541471866697,11243884708663524644,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2844 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
42 197
Read events
41 847
Write events
340
Delete events
10
Modification events
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30880462 | |||
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30880462 | |||
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3632) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
208
Suspicious files
98
Text files
329
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\E4292U1R.txt | text | |
MD5:— | SHA256:— | |||
| 3632 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\anonfiles[1].css | text | |
MD5:— | SHA256:— | |||
| 1292 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Openbullet_1.3[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
124
DNS requests
71
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 142.250.34.2:80 | http://edgedl.gvt1.com/edgedl/release2/chrome_component/PV1PFhY4Cc1AJf3I3rnvqg_1.3.36.31/AMTLN8DcC4lzlwQm0P1dJdQ | US | — | — | whitelisted |
3632 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3632 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3632 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
1292 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGCDPAjbzpoUYuu%2B39wE%3D | US | der | 1.48 Kb | whitelisted |
1292 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.49 Kb | whitelisted |
3412 | chrome.exe | GET | 302 | 142.250.74.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 538 b | whitelisted |
1292 | iexplore.exe | GET | 200 | 23.55.163.73:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.16 Kb | whitelisted |
3696 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1292 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAyO4MkNaokViAQGHuJB%2Ba8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
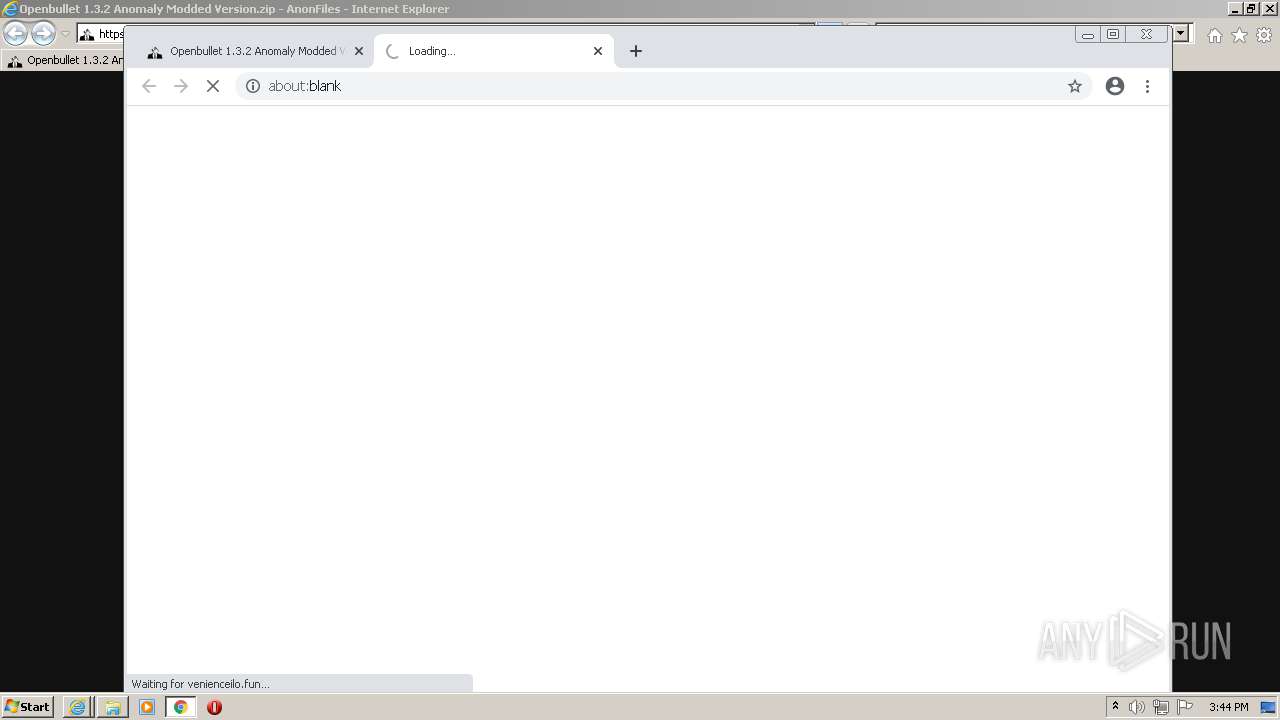
3632 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1292 | iexplore.exe | 104.21.19.216:443 | anonfiles.com | Cloudflare Inc | US | unknown |
3632 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3632 | iexplore.exe | 67.26.139.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1292 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1292 | iexplore.exe | 172.67.190.59:443 | anonfiles.com | — | US | suspicious |
1292 | iexplore.exe | 67.26.139.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3632 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3632 | iexplore.exe | 8.248.139.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3632 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anonfiles.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
dns.msftncsi.com |
| shared |
ocsp.digicert.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
vjs.zencdn.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |