| File name: | 2020.doc |
| Full analysis: | https://app.any.run/tasks/98a62604-ec8b-4e38-aa35-00f90e90762c |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 10:20:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, unknown version |
| MD5: | E68AD11B43A56F8F51582BE826A70D4E |
| SHA1: | FEB1592CEB69B45B2541C391C067F75D49BC1515 |
| SHA256: | 30CCF018AF3C244424561ECB303CD8843975A1920300B9FDB6EAB5DC36C8E2D6 |
| SSDEEP: | 12288:zbFWirip7Jc077WK4wDfRSXVH1bzfuTtf+FH3tQmOx6AXOmg:HFreJp7DfoV5zfxdQmOxk |
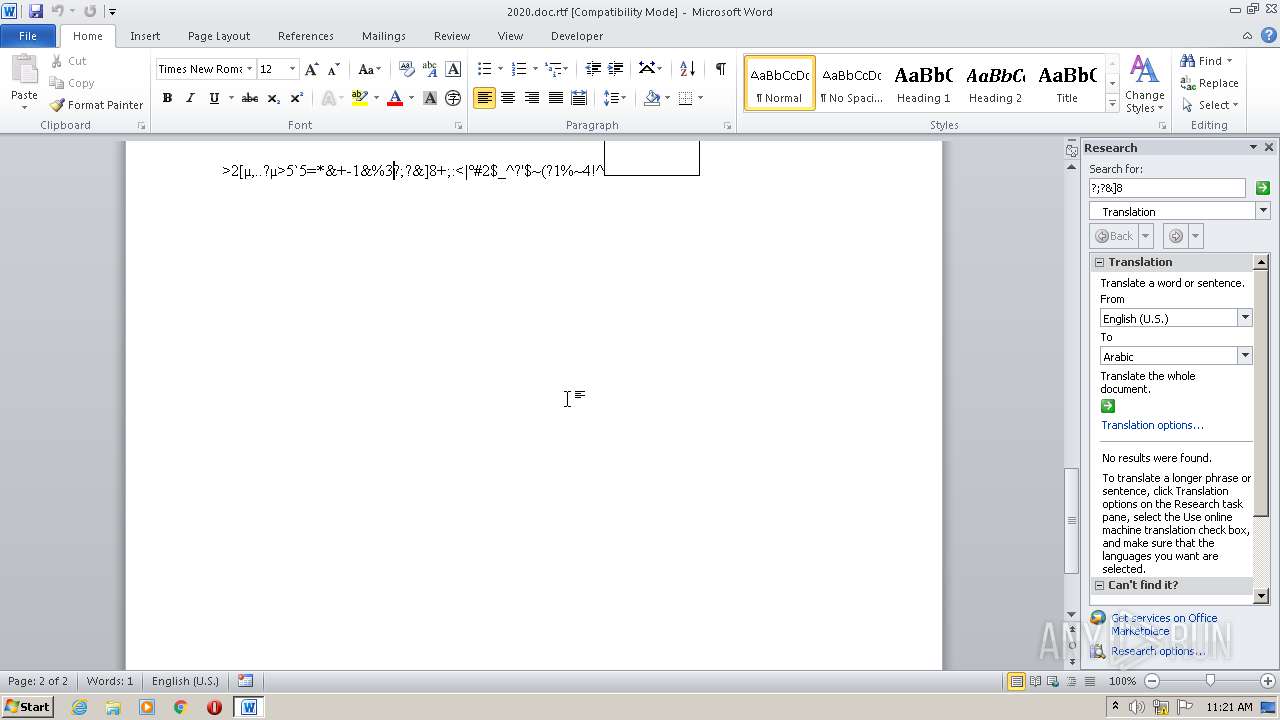
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3808)
Application was dropped or rewritten from another process
- ndaboski38547.exe (PID: 2908)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3520)
Uses Task Scheduler to run other applications
- ndaboski38547.exe (PID: 2908)
SUSPICIOUS
Creates files in the user directory
- EQNEDT32.EXE (PID: 3808)
- ndaboski38547.exe (PID: 2908)
Reads Internet Cache Settings
- EQNEDT32.EXE (PID: 3808)
Executed via COM
- EQNEDT32.EXE (PID: 3808)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 3808)
- ndaboski38547.exe (PID: 2908)
Reads the BIOS version
- ndaboski38547.exe (PID: 2908)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2652)
Reads settings of System Certificates
- WINWORD.EXE (PID: 2652)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 2652)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
Total processes
41
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2136 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | ndaboski38547.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\2020.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2908 | "C:\Users\admin\AppData\Roaming\ndaboski38547.exe" | C:\Users\admin\AppData\Roaming\ndaboski38547.exe | EQNEDT32.EXE | ||||||||||||
User: admin Company: theHTPC.net Integrity Level: MEDIUM Description: Folder GUI Exit code: 0 Version: 1.4.4.0 Modules
| |||||||||||||||
| 3520 | "C:\Windows\System32\schtasks.exe" /Create /TN "Updates\rTGTNzjEvF" /XML "C:\Users\admin\AppData\Local\Temp\tmp606C.tmp" | C:\Windows\System32\schtasks.exe | — | ndaboski38547.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3808 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
16 009
Read events
7 778
Write events
8 095
Delete events
136
Modification events
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2)$ |
Value: 322924005C0A0000010000000000000000000000 | |||
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2652) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
3
Suspicious files
8
Text files
3
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB1A3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3808 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Temp\CabCCEB.tmp | — | |
MD5:— | SHA256:— | |||
| 3808 | EQNEDT32.EXE | C:\Users\admin\AppData\Local\Temp\TarCCEC.tmp | — | |
MD5:— | SHA256:— | |||
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\config14[1].xml | — | |
MD5:— | SHA256:— | |||
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Cab4B34.tmp | — | |
MD5:— | SHA256:— | |||
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Tar4B35.tmp | — | |
MD5:— | SHA256:— | |||
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2652 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$20.doc.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3808 | EQNEDT32.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
| 3808 | EQNEDT32.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
16
DNS requests
8
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3808 | EQNEDT32.EXE | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA7yTSbUNi7CXXtef0luXqk%3D | US | der | 279 b | whitelisted |
2652 | WINWORD.EXE | GET | 200 | 52.109.88.8:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={019C826E-445A-4649-A5B0-0BF08FCC4EEE}&build=14.0.6023 | NL | xml | 1.99 Kb | whitelisted |
1052 | svchost.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3808 | EQNEDT32.EXE | GET | 301 | 92.119.113.140:80 | http://miratechs.ga/gatusall/ndaboski/ndaboski.exe | unknown | html | 121 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3808 | EQNEDT32.EXE | 92.119.113.140:80 | miratechs.ga | — | — | malicious |
3808 | EQNEDT32.EXE | 92.119.113.140:443 | miratechs.ga | — | — | malicious |
3808 | EQNEDT32.EXE | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
2652 | WINWORD.EXE | 52.109.8.27:443 | rr.office.microsoft.com | Microsoft Corporation | US | whitelisted |
2652 | WINWORD.EXE | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1052 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2136 | MSBuild.exe | 178.170.138.163:4554 | — | eTOP sp. z o.o. | MT | malicious |
2652 | WINWORD.EXE | 52.109.88.8:80 | office14client.microsoft.com | Microsoft Corporation | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
miratechs.ga |
| malicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
office14client.microsoft.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
3808 | EQNEDT32.EXE | Potentially Bad Traffic | ET INFO Suspicious Domain (*.ga) in TLS SNI |
3808 | EQNEDT32.EXE | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.ga) |