| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/8f5429a6-d1e5-45a0-8630-33ee0418909d |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2018, 12:59:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1DC1E9152C2B8B24EB16D04A6ACD748E |
| SHA1: | 0D98E078E42ABC9828E4EBABBCCF415C94559510 |
| SHA256: | 30C4A30FD74DDBD9FE3A8EC4427773AF8DE3BB51E3481F0CFCAAC9563807AD21 |
| SSDEEP: | 12288:YXmwRo+mv8QD4+0N463/SQiStn/CC9HNrPIdYl+5VlMmoUCH6XzVRkRRi:YX48QE+UtBt/CC9HNDIdYAVMvUJXhmq |
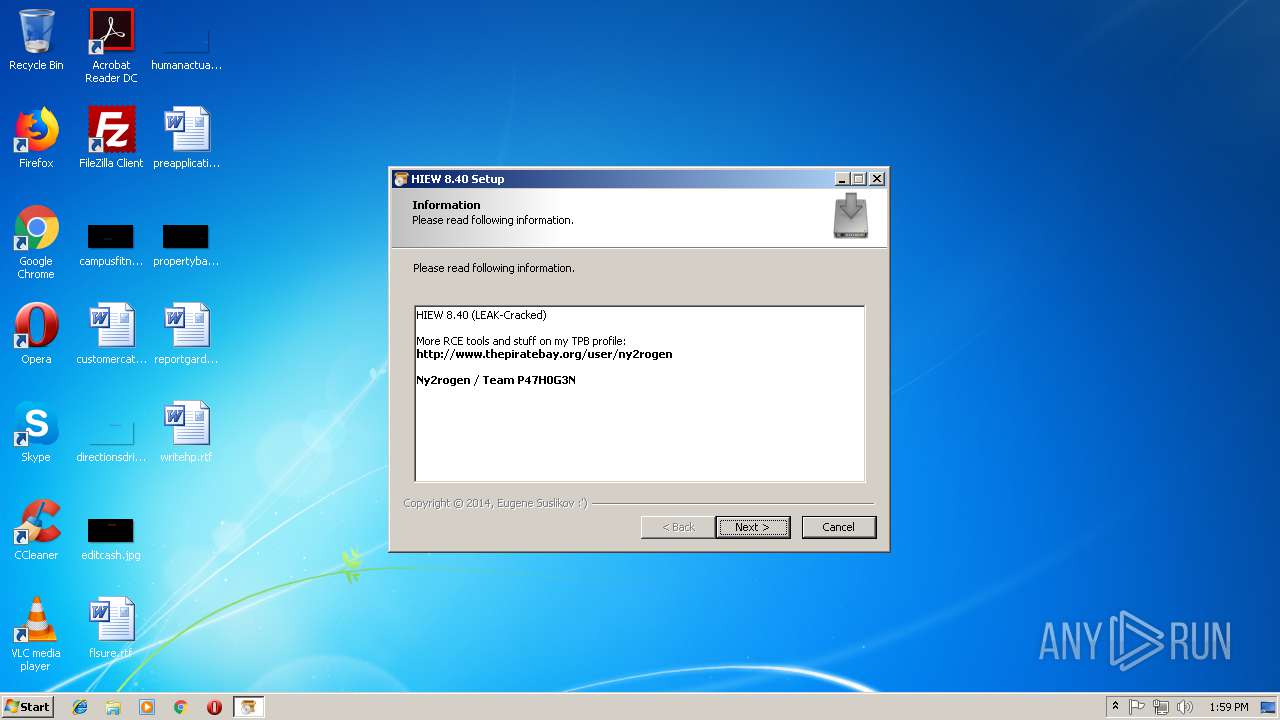
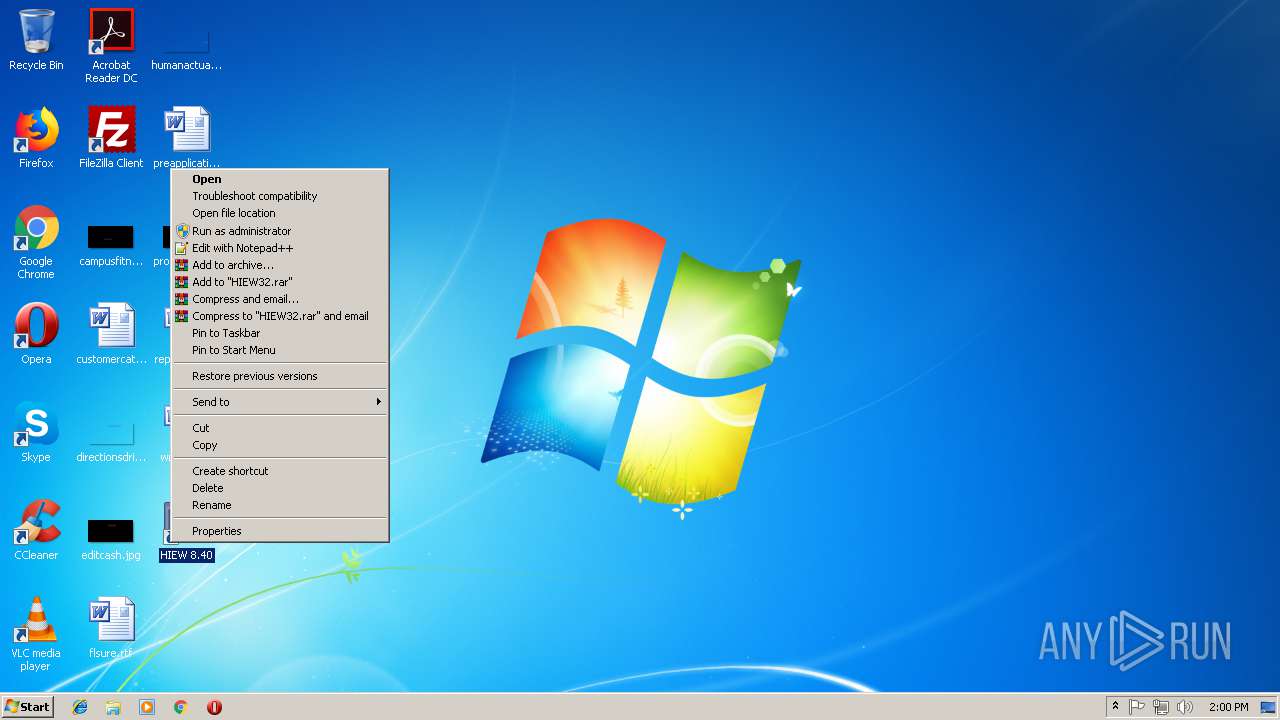
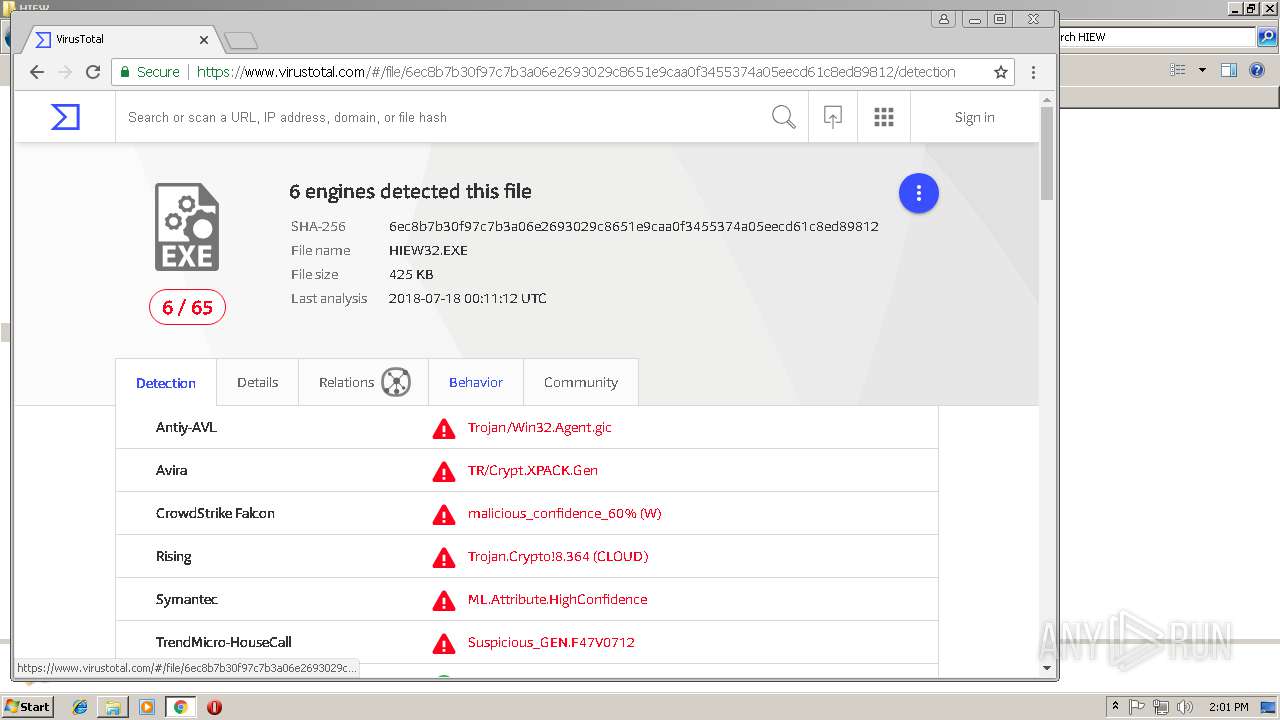
MALICIOUS
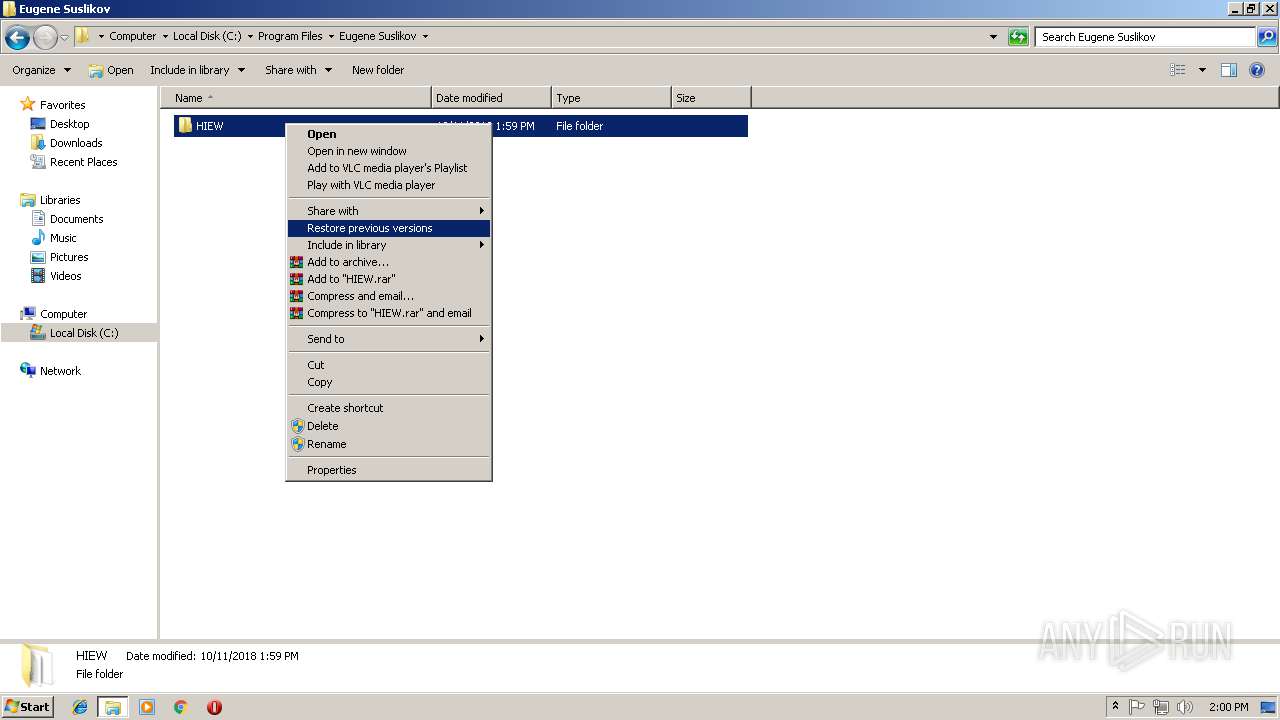
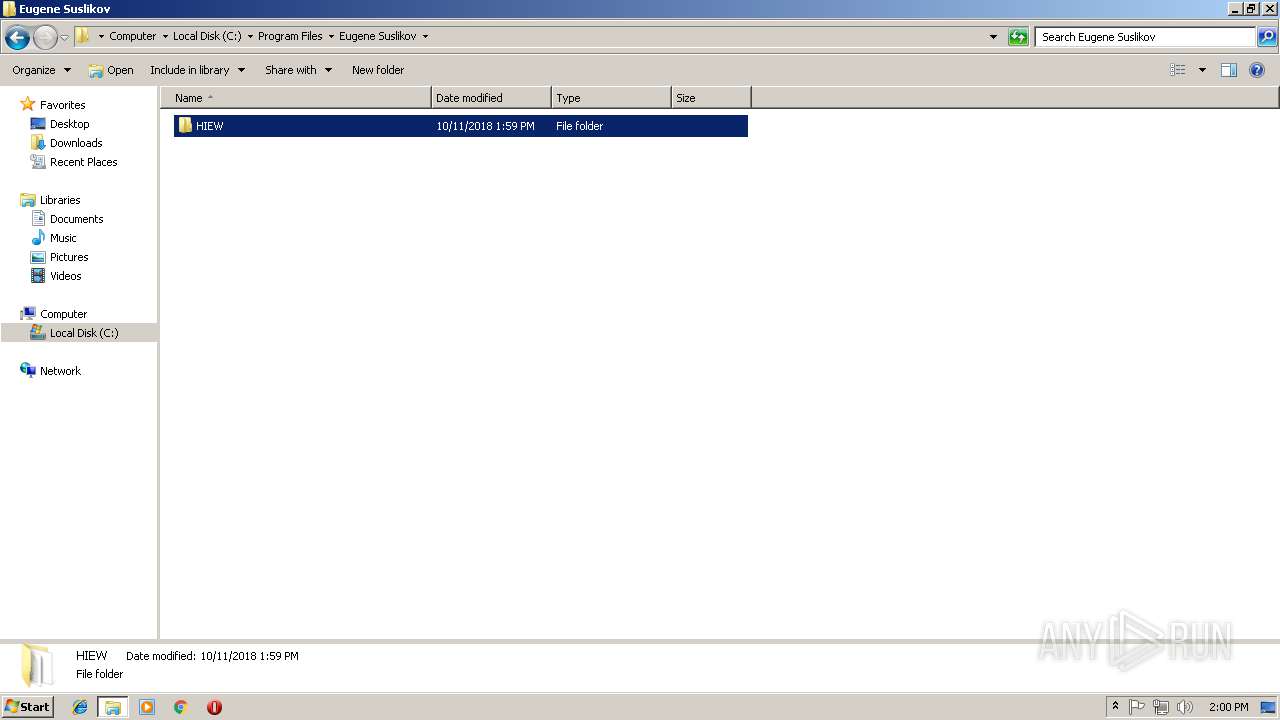
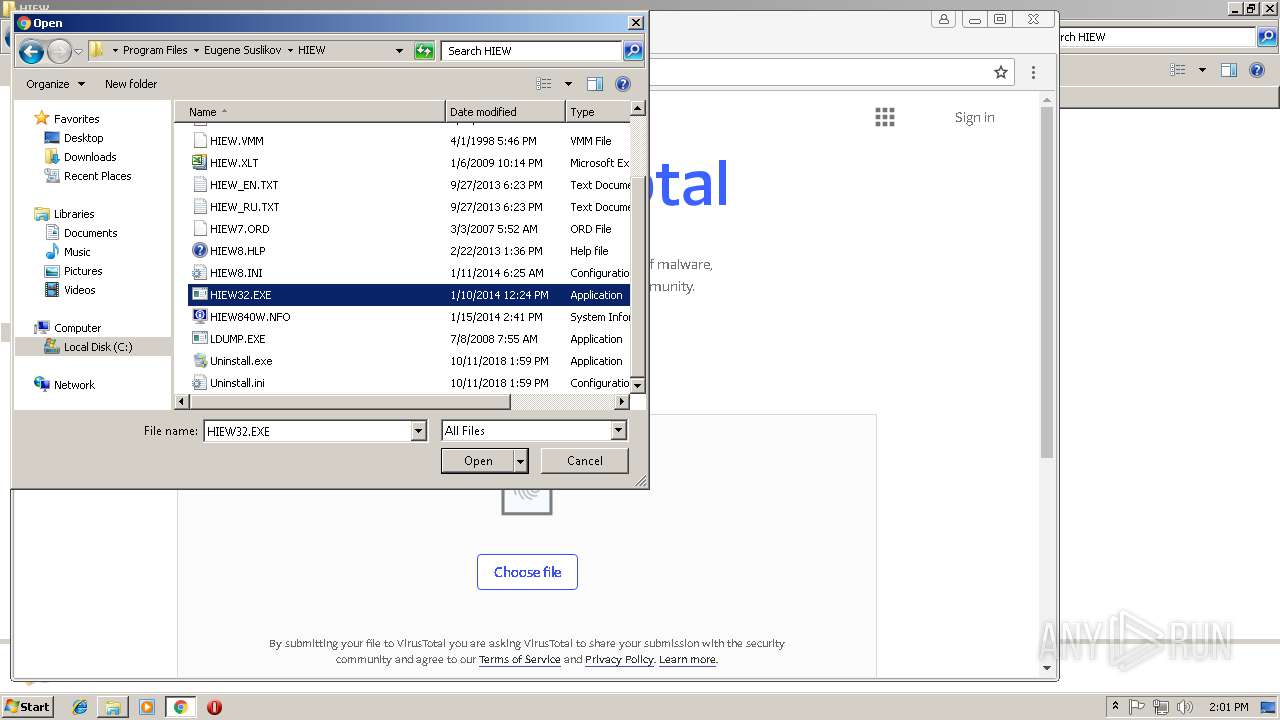
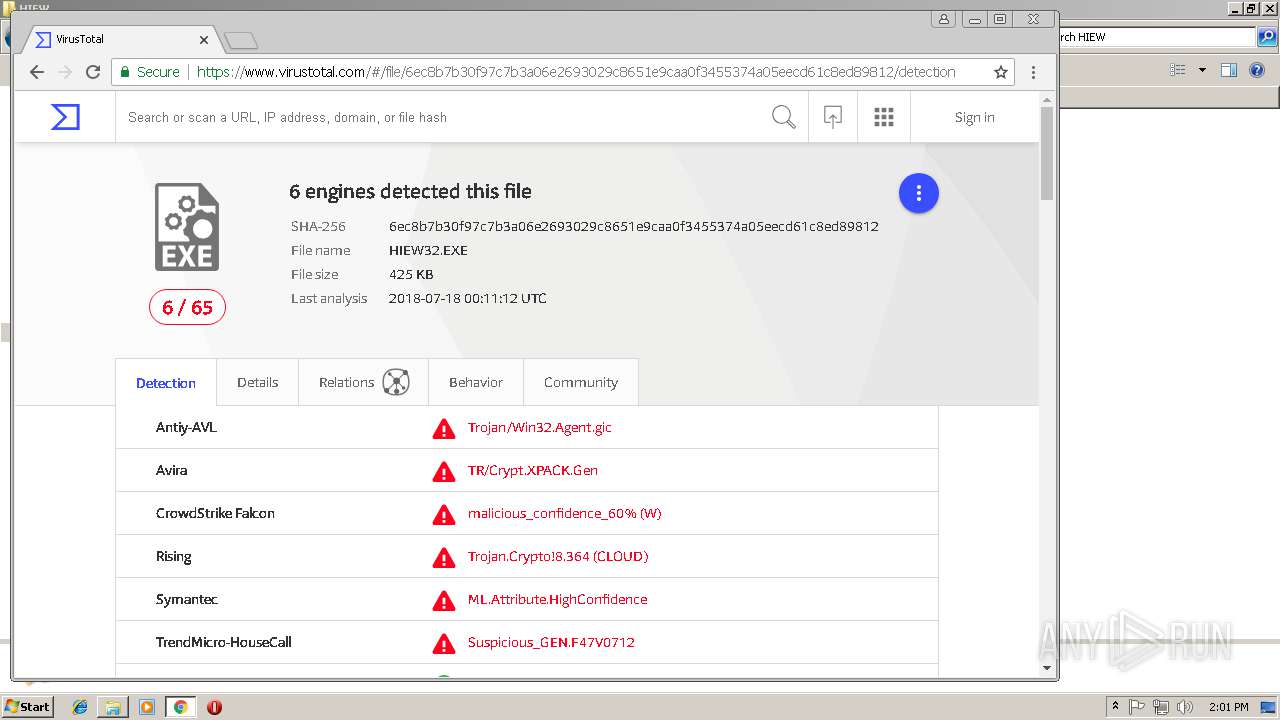
Application was dropped or rewritten from another process
- HIEW32.EXE (PID: 2240)
SUSPICIOUS
Executable content was dropped or overwritten
- Setup.exe (PID: 3704)
Creates a software uninstall entry
- Setup.exe (PID: 3704)
Creates files in the user directory
- Setup.exe (PID: 3704)
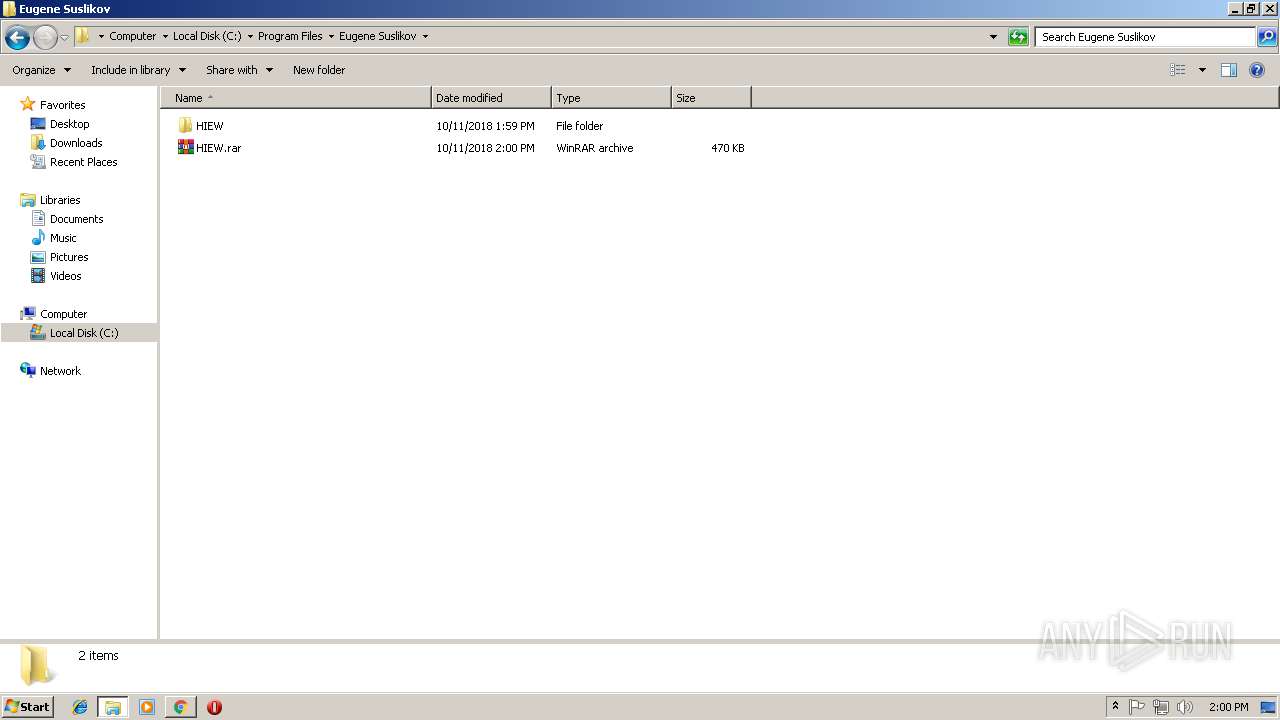
Creates files in the program directory
- Setup.exe (PID: 3704)
- WinRAR.exe (PID: 968)
Application launched itself
- WinRAR.exe (PID: 256)
INFO
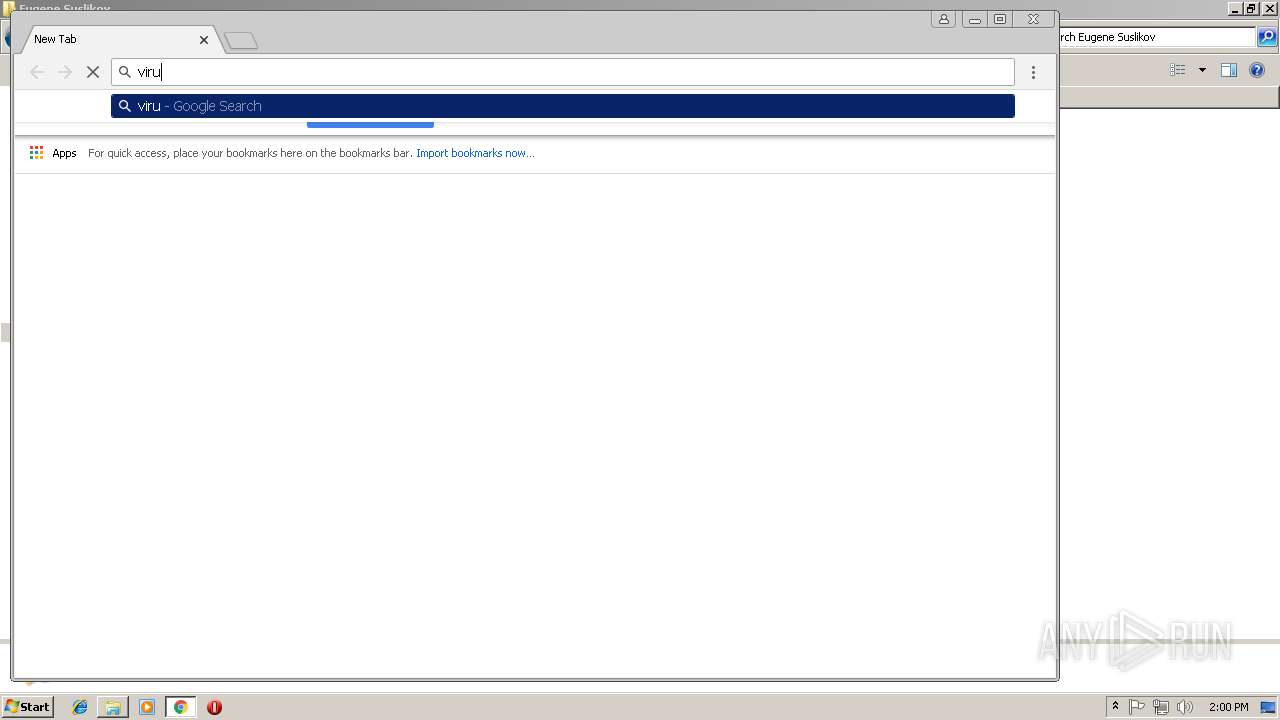
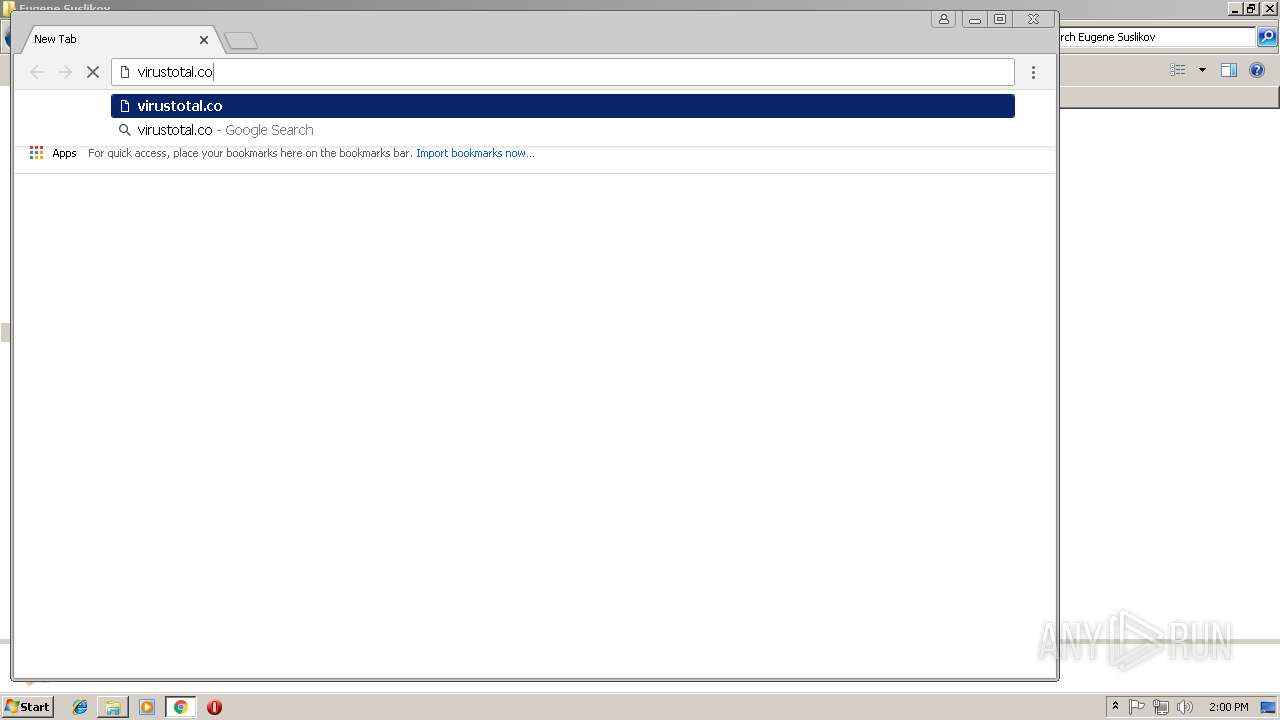
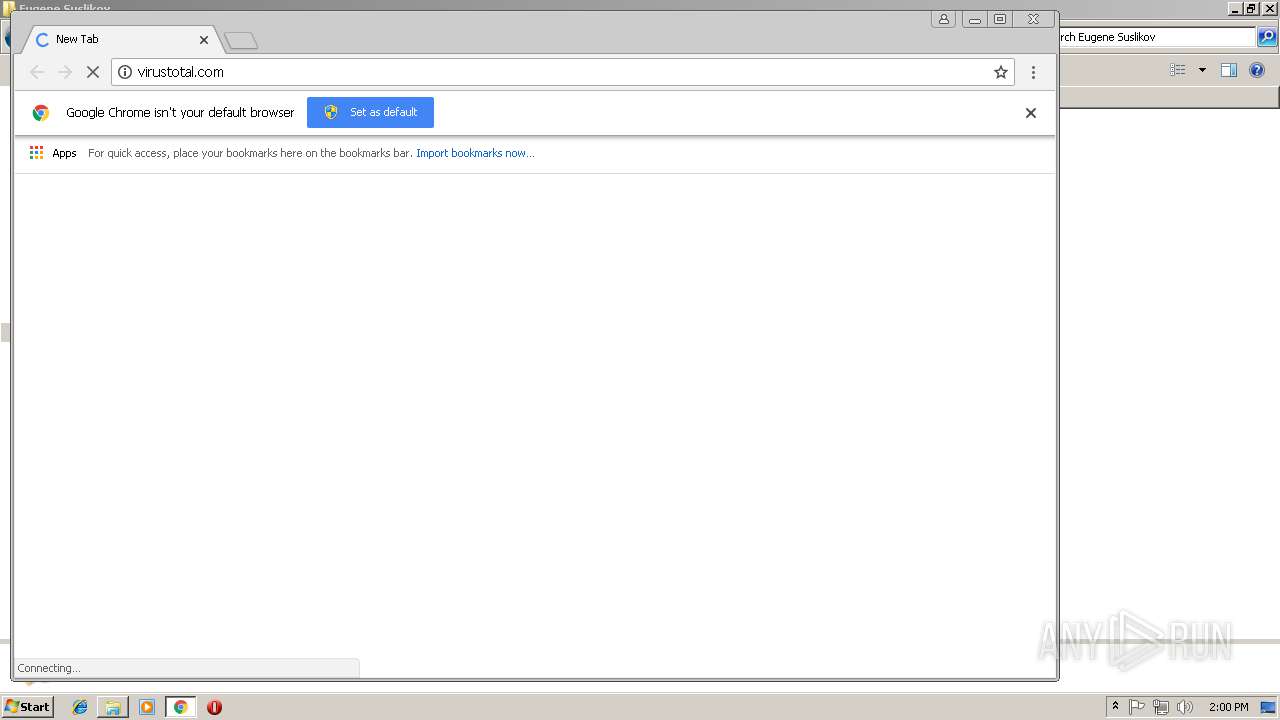
Application launched itself
- chrome.exe (PID: 2848)
Reads Internet Cache Settings
- chrome.exe (PID: 2848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
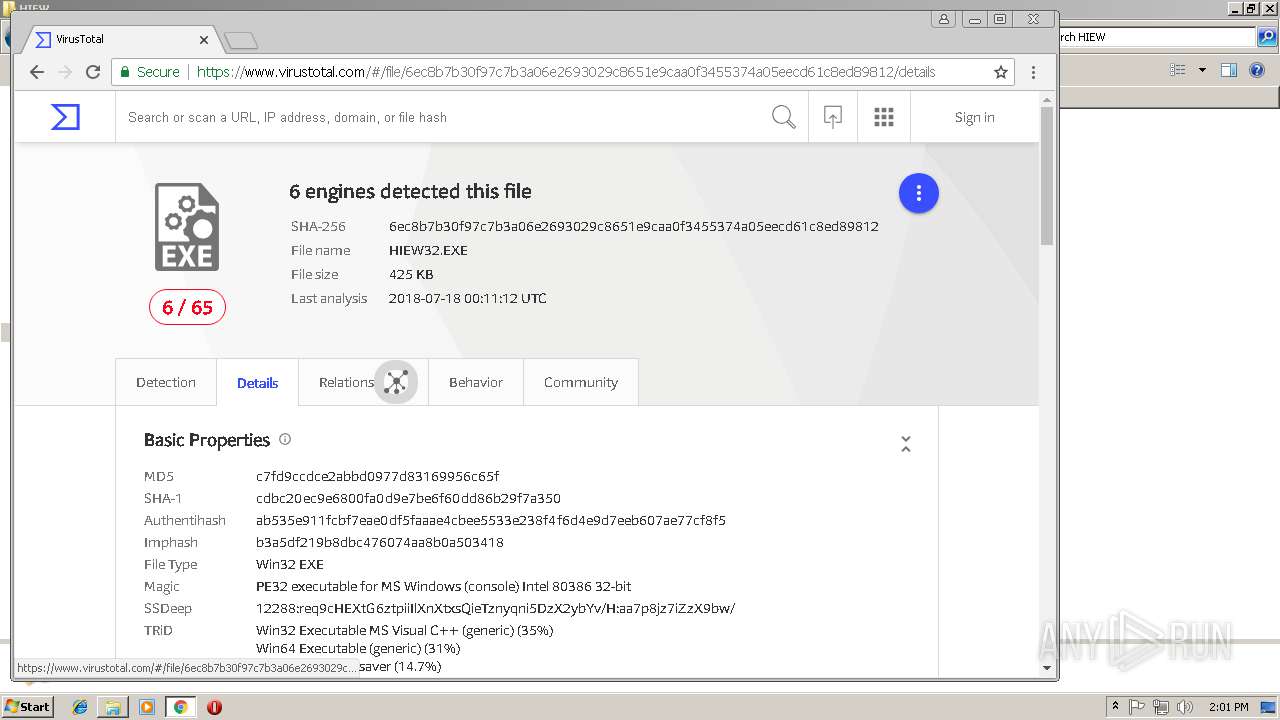
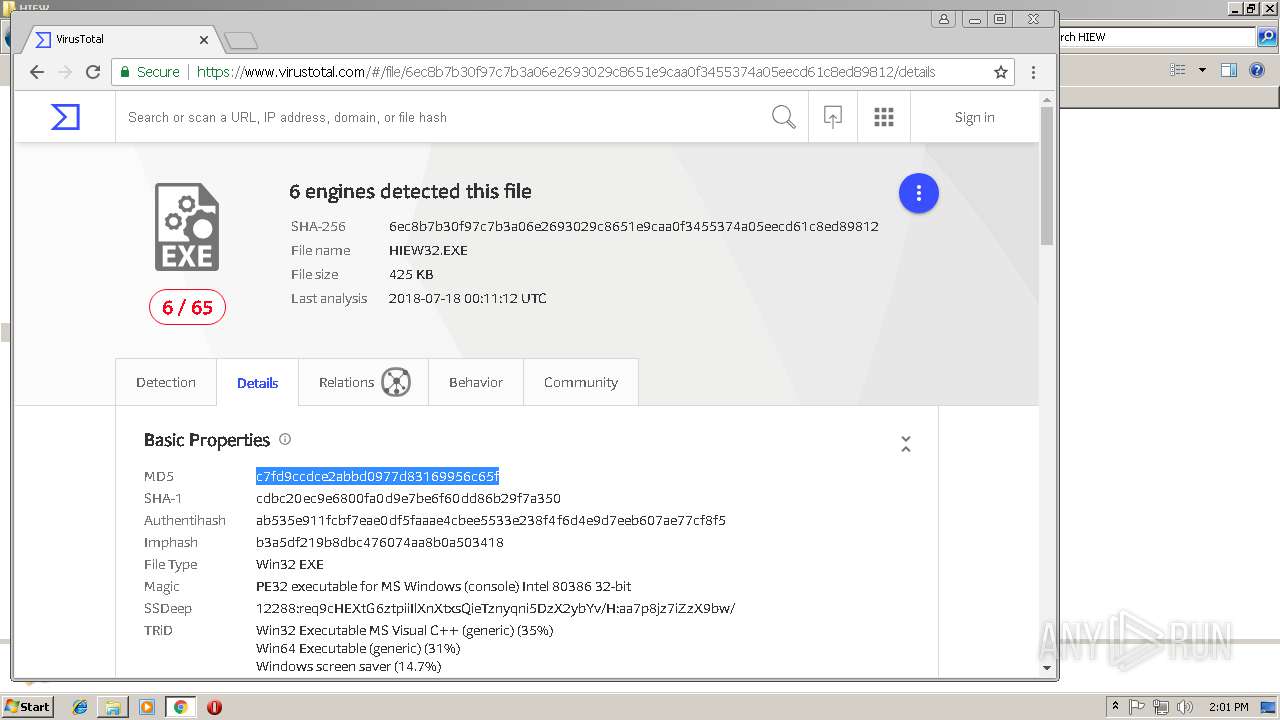
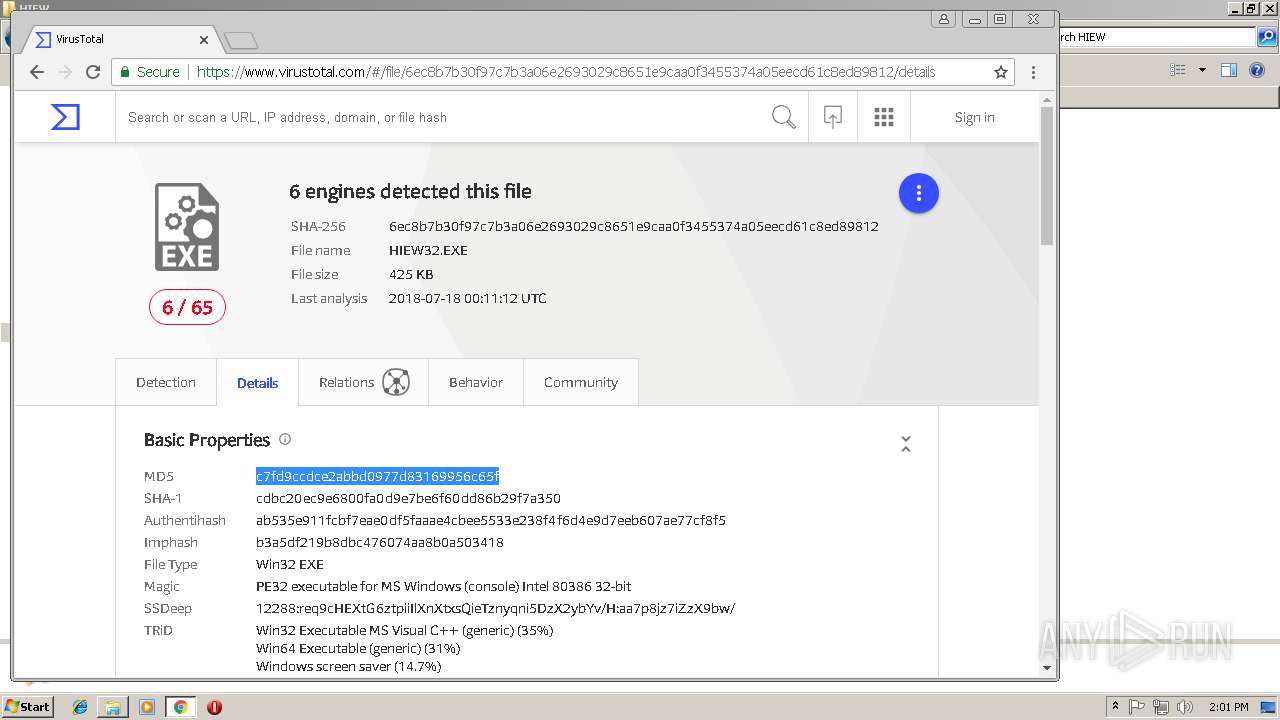
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 148992 |
| InitializedDataSize: | 41984 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25468 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.40.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
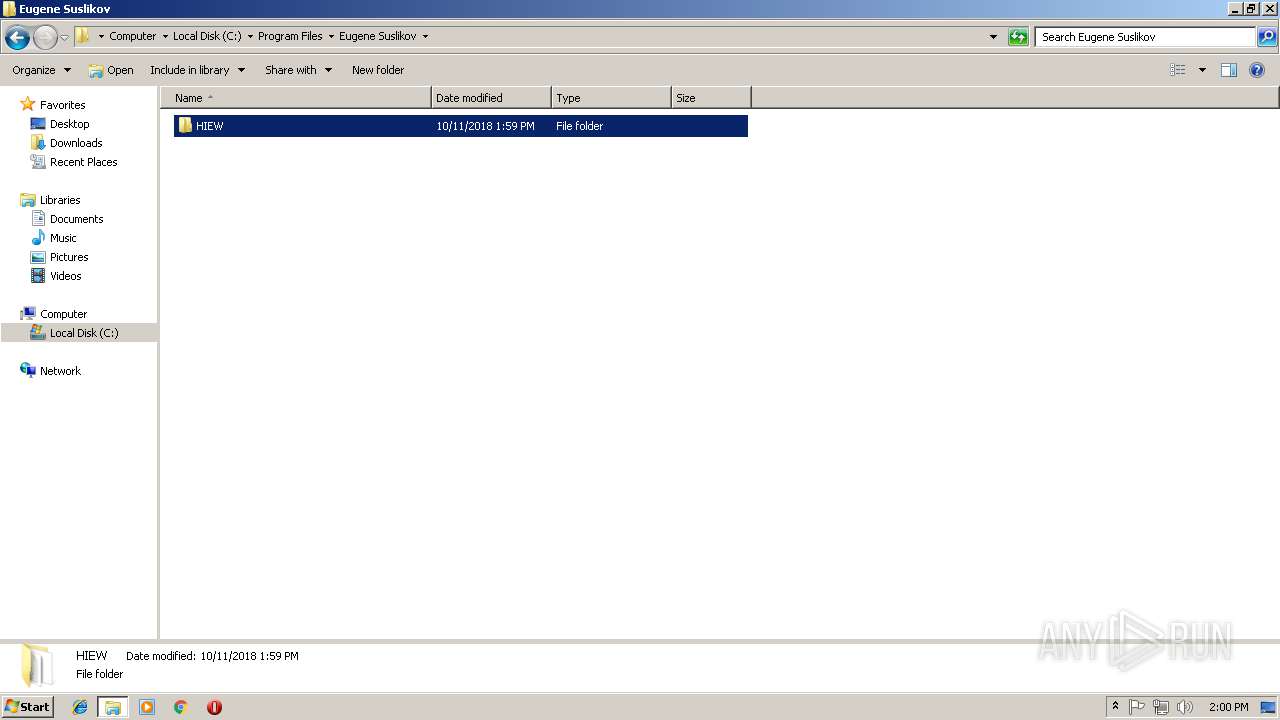
| CompanyName: | Eugene Suslikov |
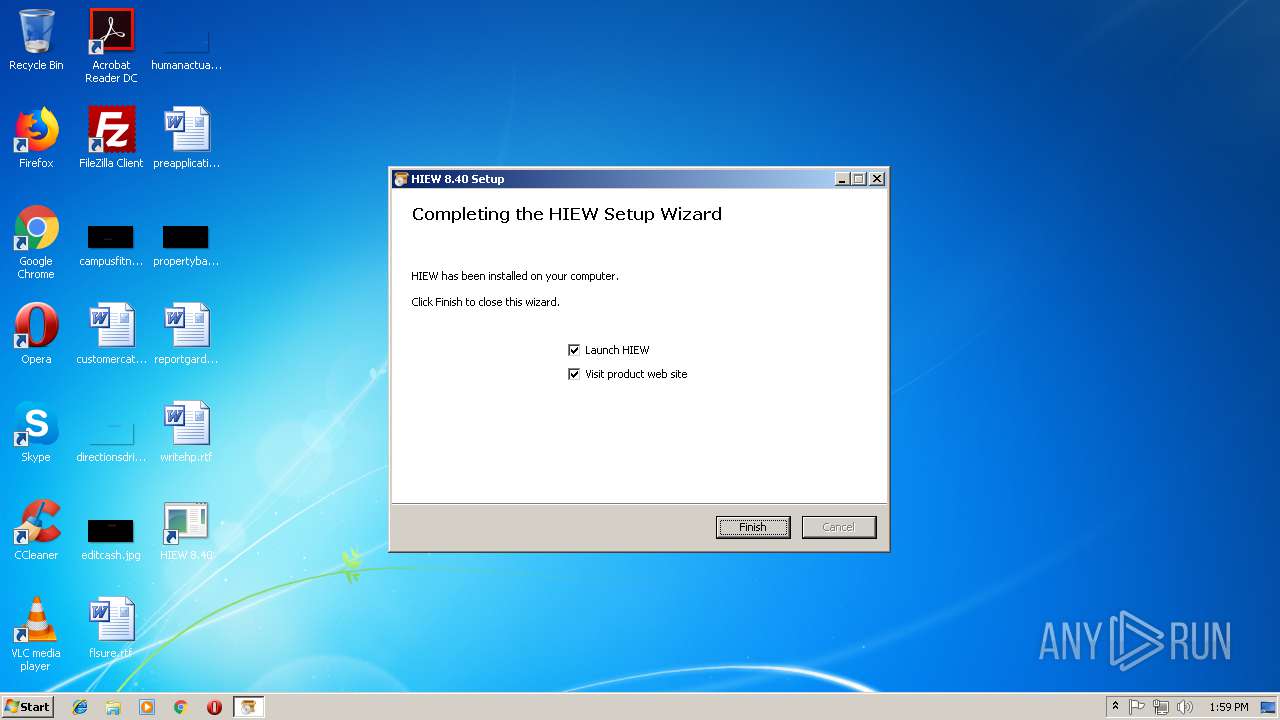
| FileDescription: | HIEW 8.40 Installation |
| FileVersion: | 8.40 |
| LegalCopyright: | Eugene Suslikov |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Eugene Suslikov |
| FileDescription: | HIEW 8.40 Installation |
| FileVersion: | 8.40 |
| LegalCopyright: | Eugene Suslikov |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59438 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88549 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x00004534 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 5.82924 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 5.73501 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 5.87171 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 5.60169 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.35641 | 48 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
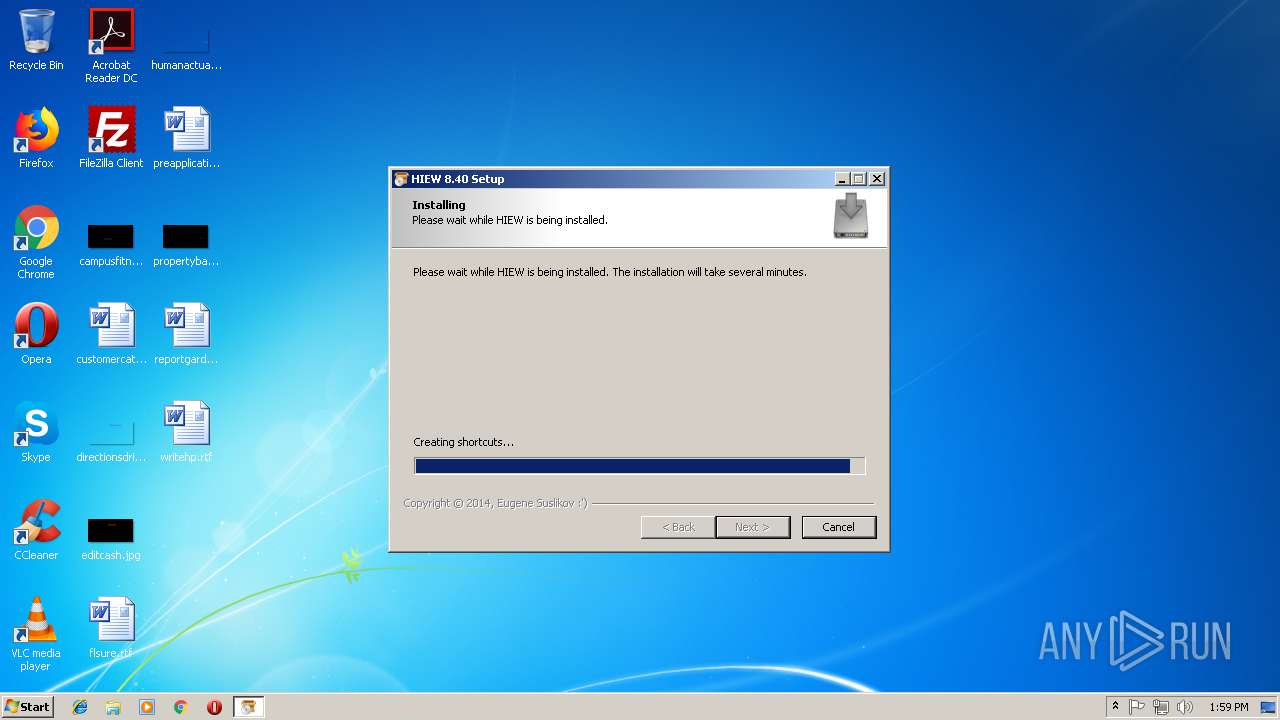
Total processes
60
Monitored processes
18
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
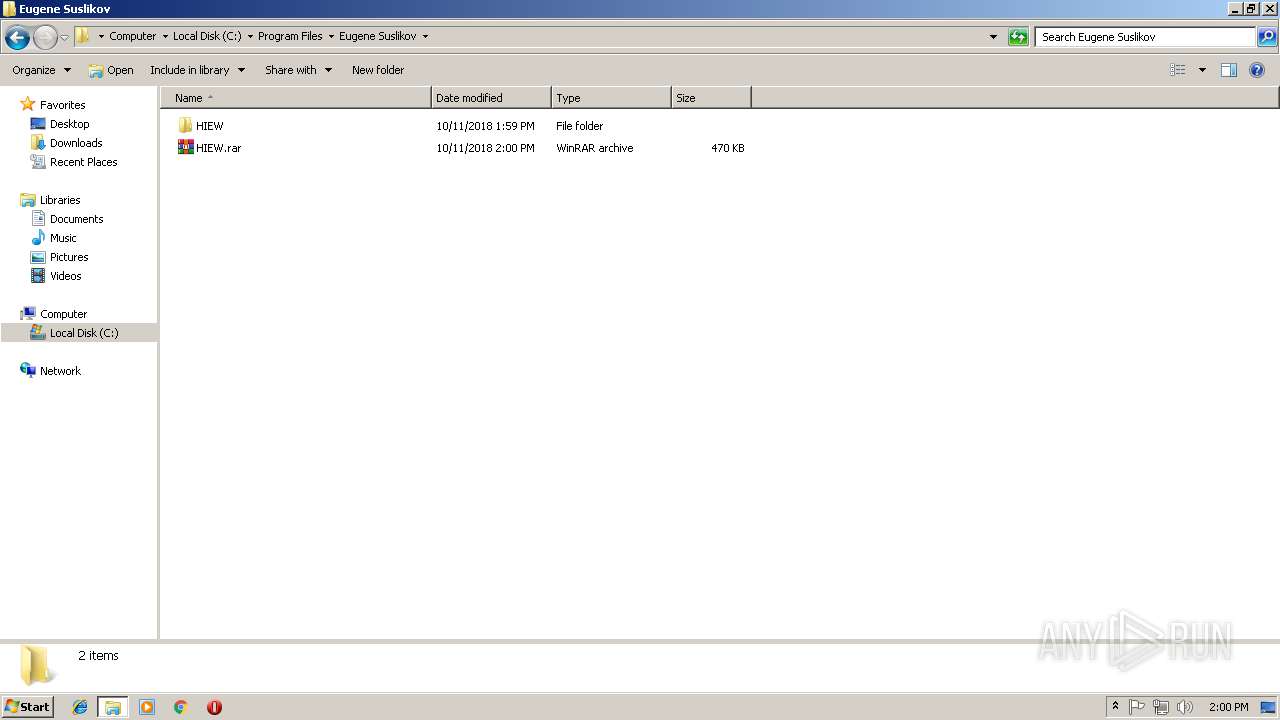
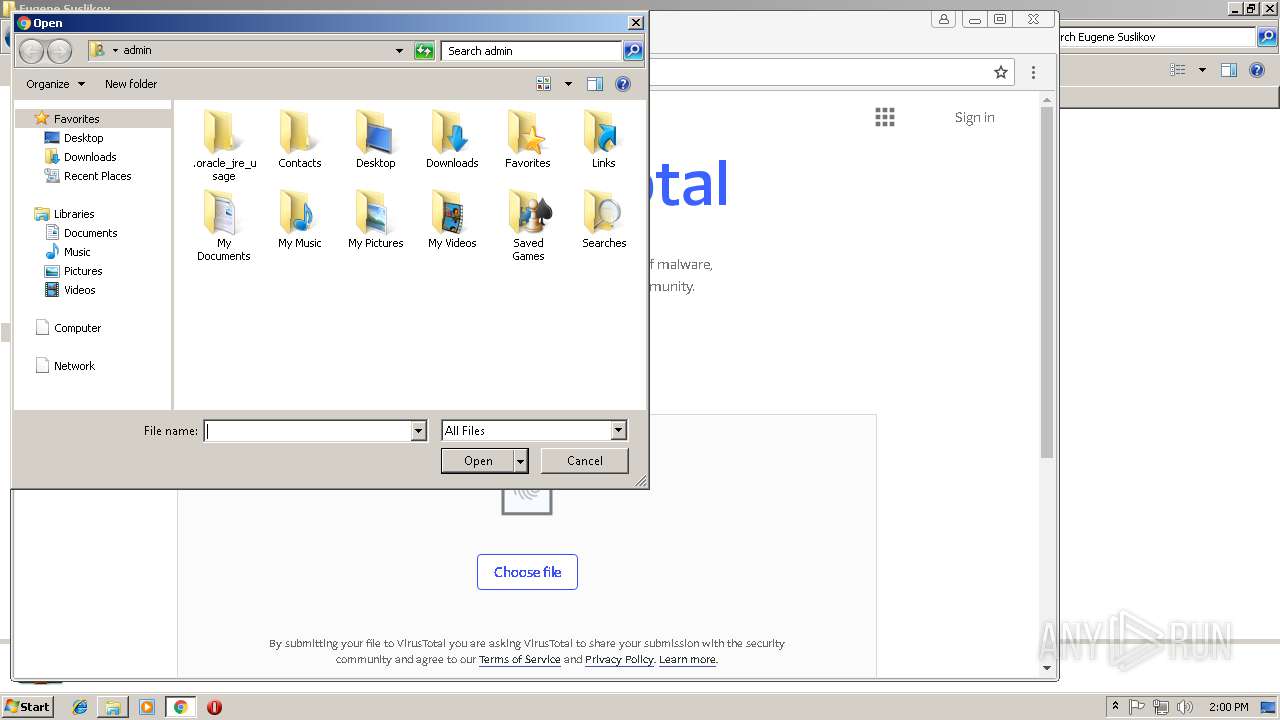
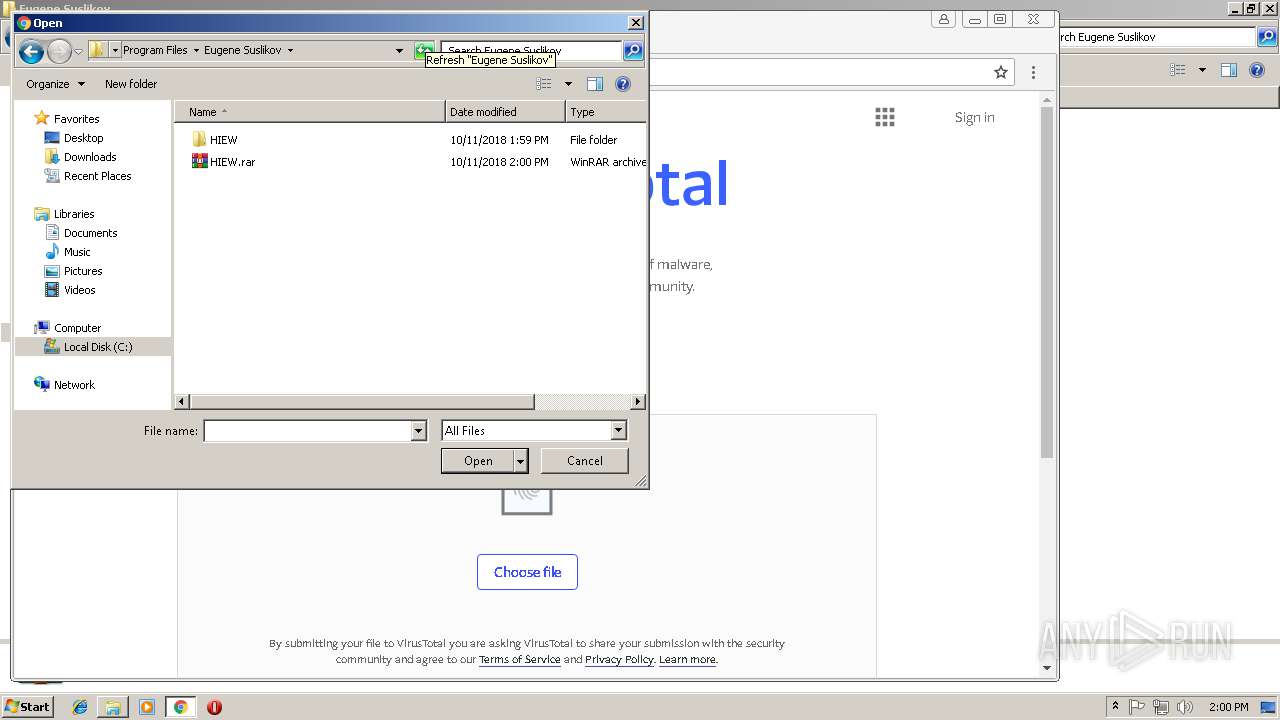
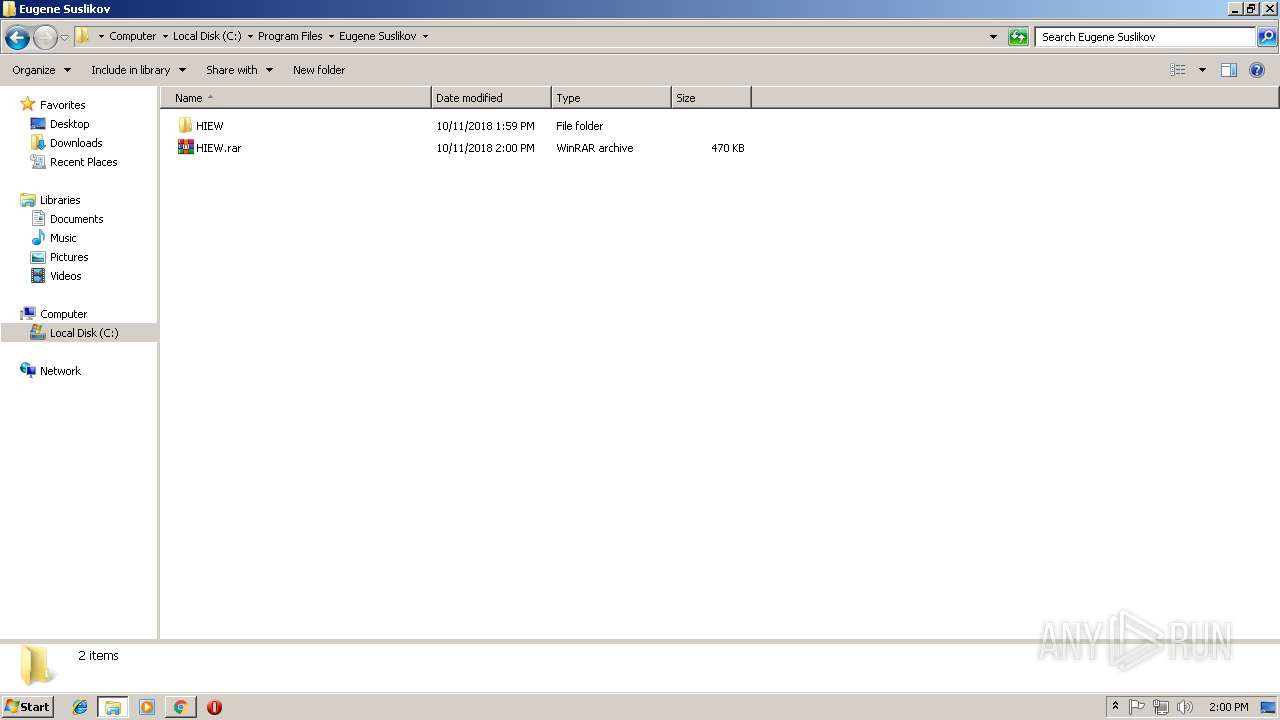
| 256 | "C:\Program Files\WinRAR\WinRAR.exe" a -ep1 -scul -r0 -iext -- HIEW.rar "C:\Program Files\Eugene Suslikov\HIEW" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=848,11859098647633755653,10000072910494700106,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=AA12B36BF10D0926CB33DA01EC0921D5 --mojo-platform-channel-handle=1120 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 968 | "C:\Program Files\WinRAR\WinRAR.exe" -elevate256 | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=848,11859098647633755653,10000072910494700106,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=8F8D64F38E16CB2C87814B64440F256E --mojo-platform-channel-handle=4708 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2620 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
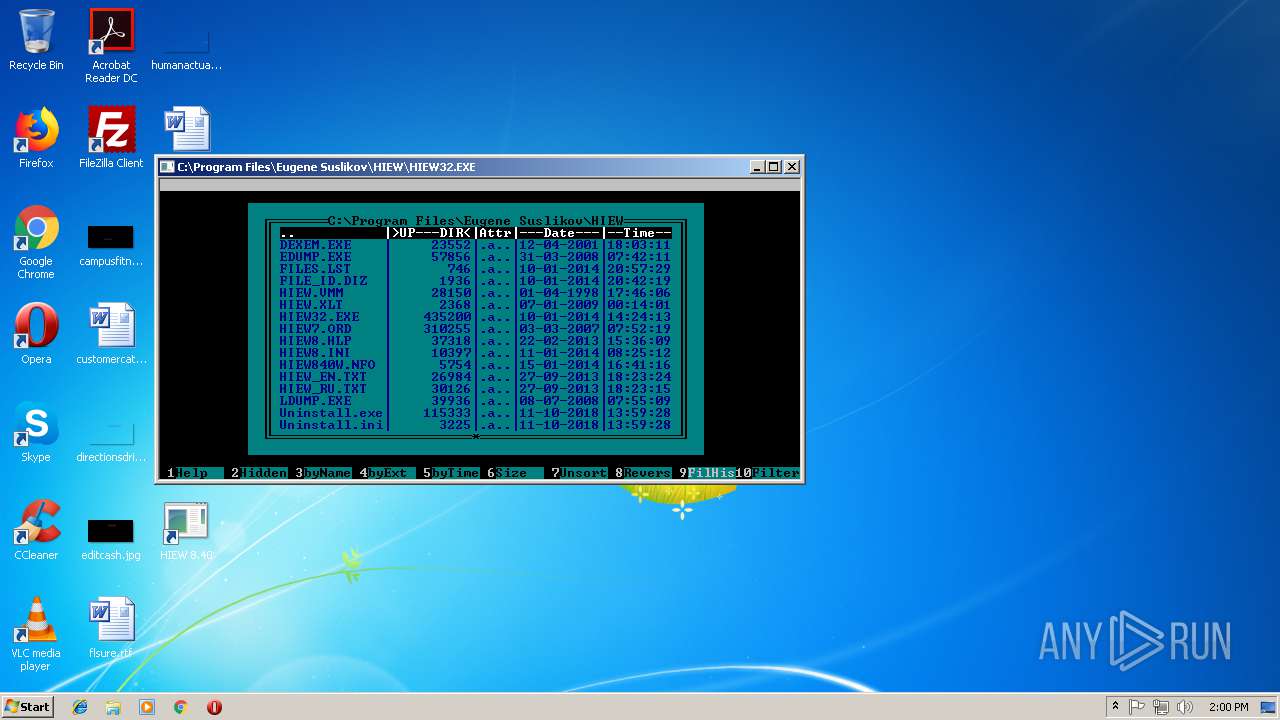
| 2240 | "C:\Program Files\Eugene Suslikov\HIEW\HIEW32.EXE" | C:\Program Files\Eugene Suslikov\HIEW\HIEW32.EXE | — | Setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 3221225786 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=848,11859098647633755653,10000072910494700106,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=BA9BFD9ED0CE65AC022032F16DDCAA2E --mojo-platform-channel-handle=900 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=848,11859098647633755653,10000072910494700106,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4D4642E17B80F05E654FB95E1B83F536 --mojo-platform-channel-handle=2248 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=848,11859098647633755653,10000072910494700106,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=CABE56ECA32E68BA3AFBC1B91A4CE20C --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CABE56ECA32E68BA3AFBC1B91A4CE20C --renderer-client-id=7 --mojo-platform-channel-handle=3780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 690
Read events
1 432
Write events
249
Delete events
9
Modification events
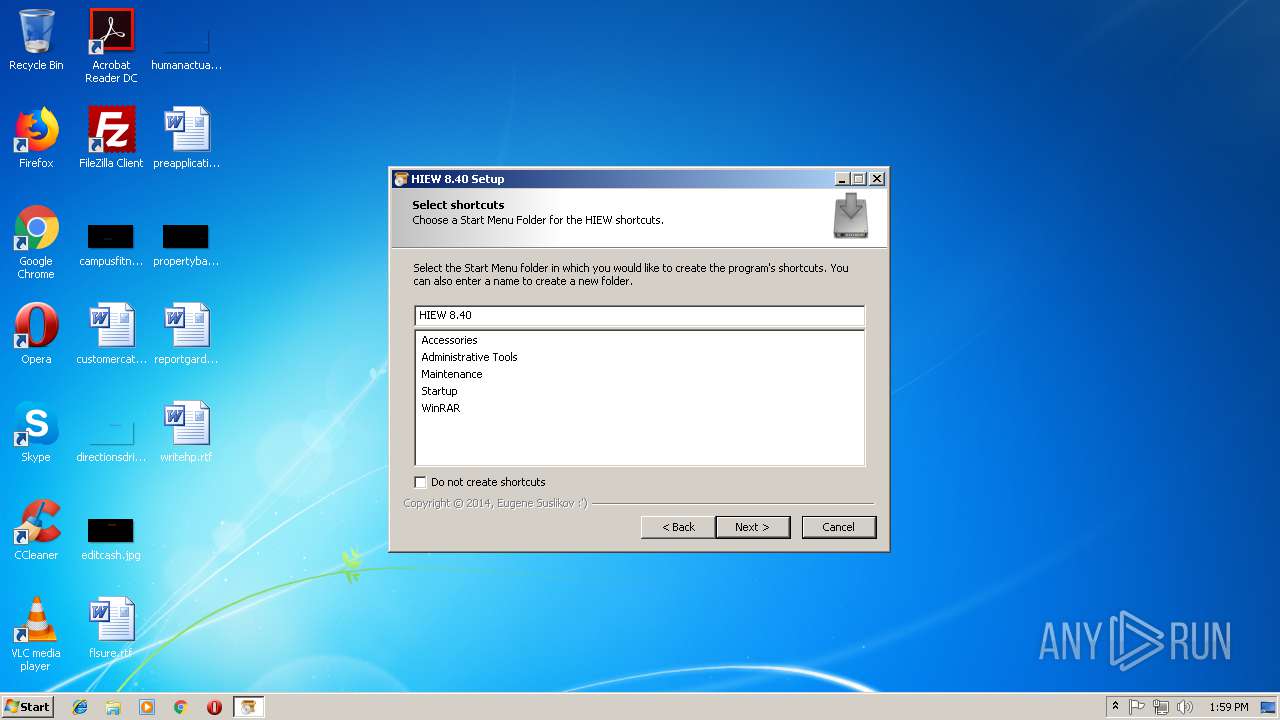
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | DisplayName |
Value: HIEW 8.40 | |||
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | DisplayVersion |
Value: 8.40 | |||
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | VersionMajor |
Value: 8 | |||
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | VersionMinor |
Value: 40 | |||
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | Publisher |
Value: Eugene Suslikov | |||
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Eugene Suslikov\HIEW\Uninstall.exe | |||
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Eugene Suslikov\HIEW\Uninstall.exe | |||
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.thepiratebay.org/user/ny2rogen | |||
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Eugene Suslikov\HIEW\ | |||
| (PID) Process: | (3704) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HIEW 8.40 |
| Operation: | write | Name: | InstallSource |
Value: C:\Users\admin\AppData\Local\Temp\ | |||
Executable files
6
Suspicious files
63
Text files
92
Unknown types
3
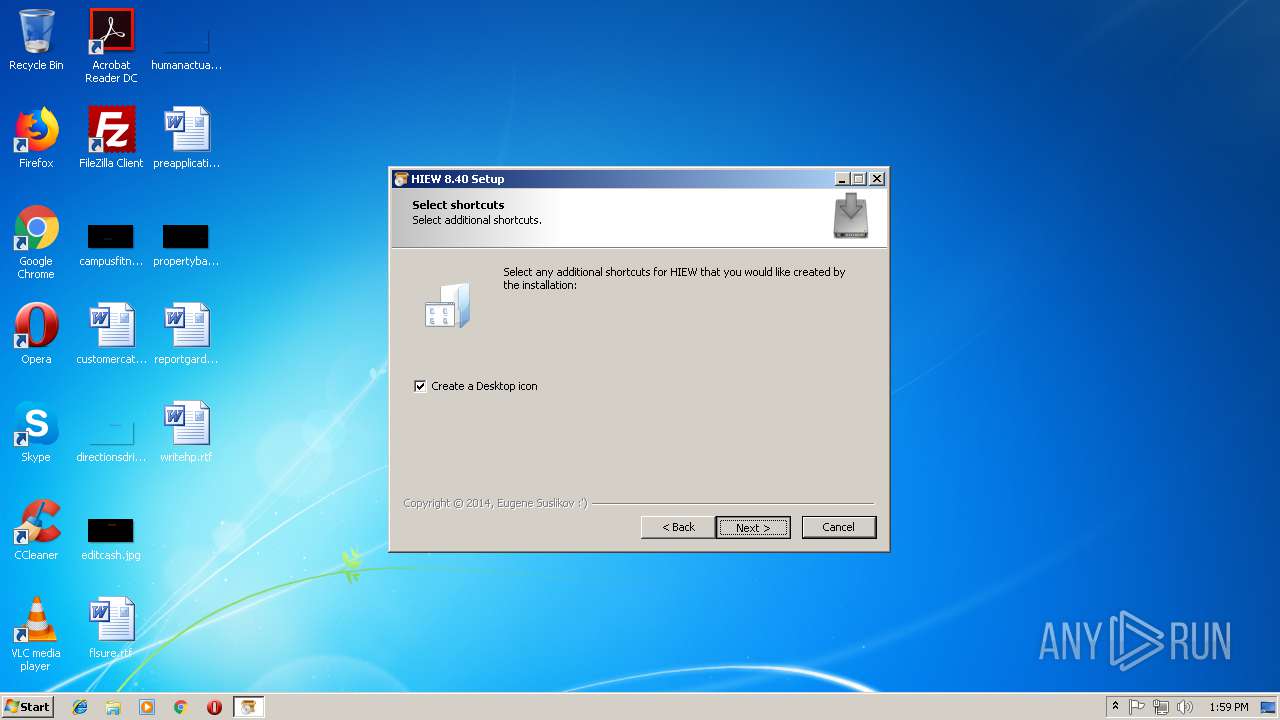
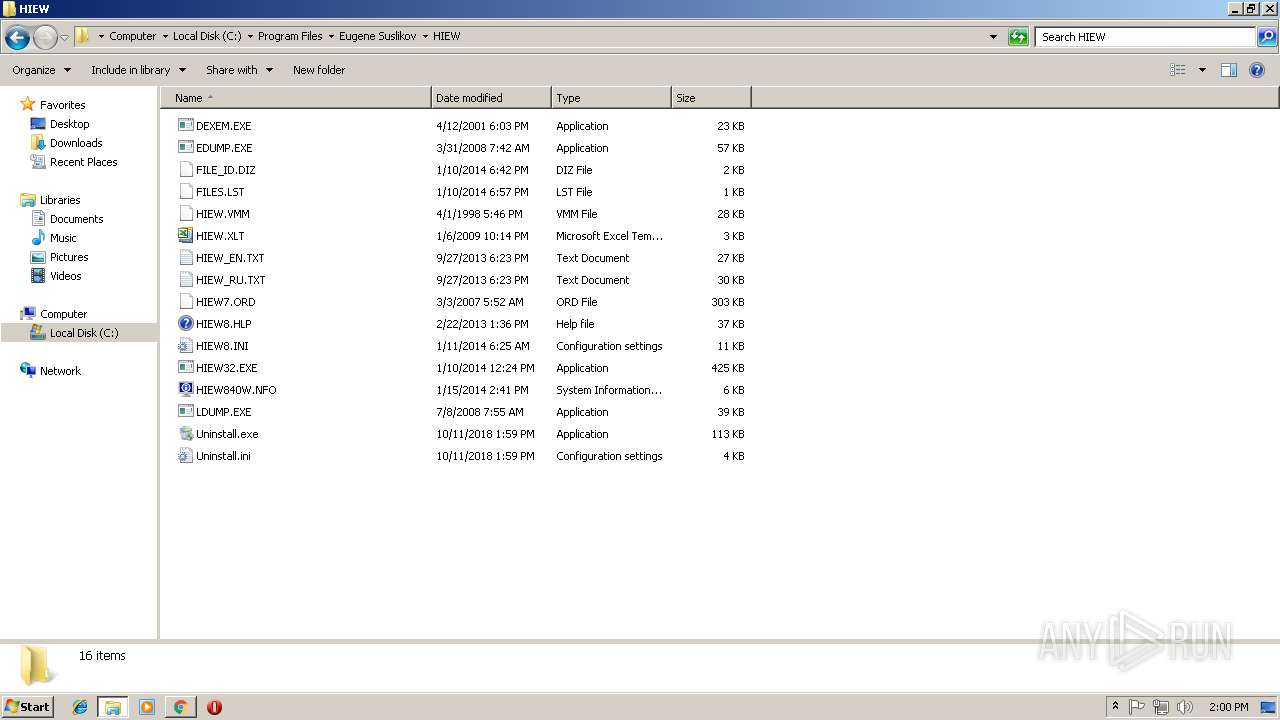
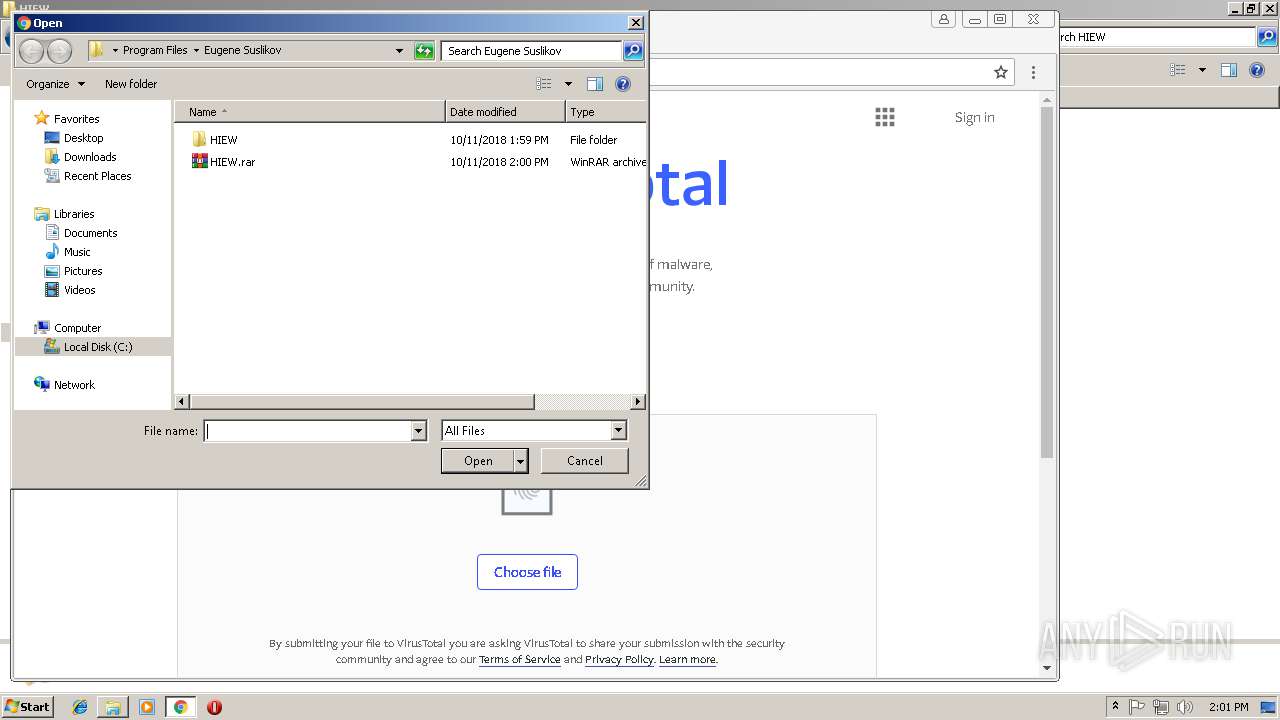
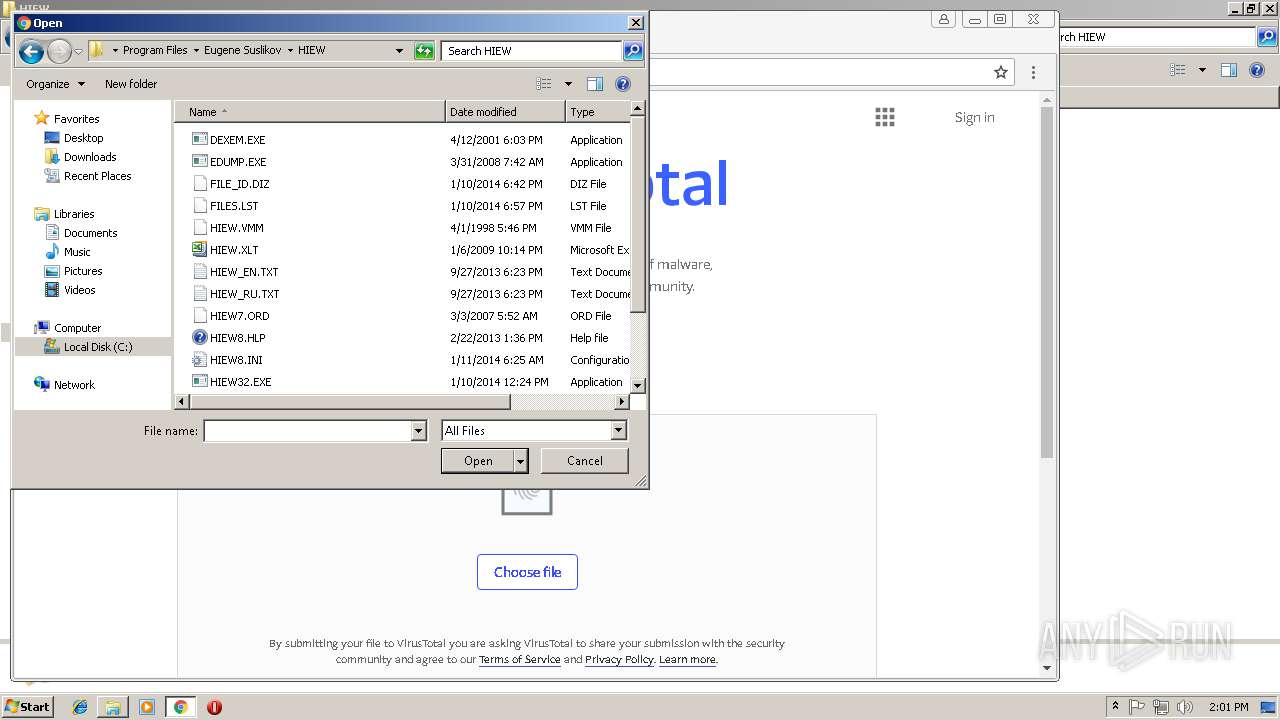
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3704 | Setup.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 3704 | Setup.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:— | SHA256:— | |||
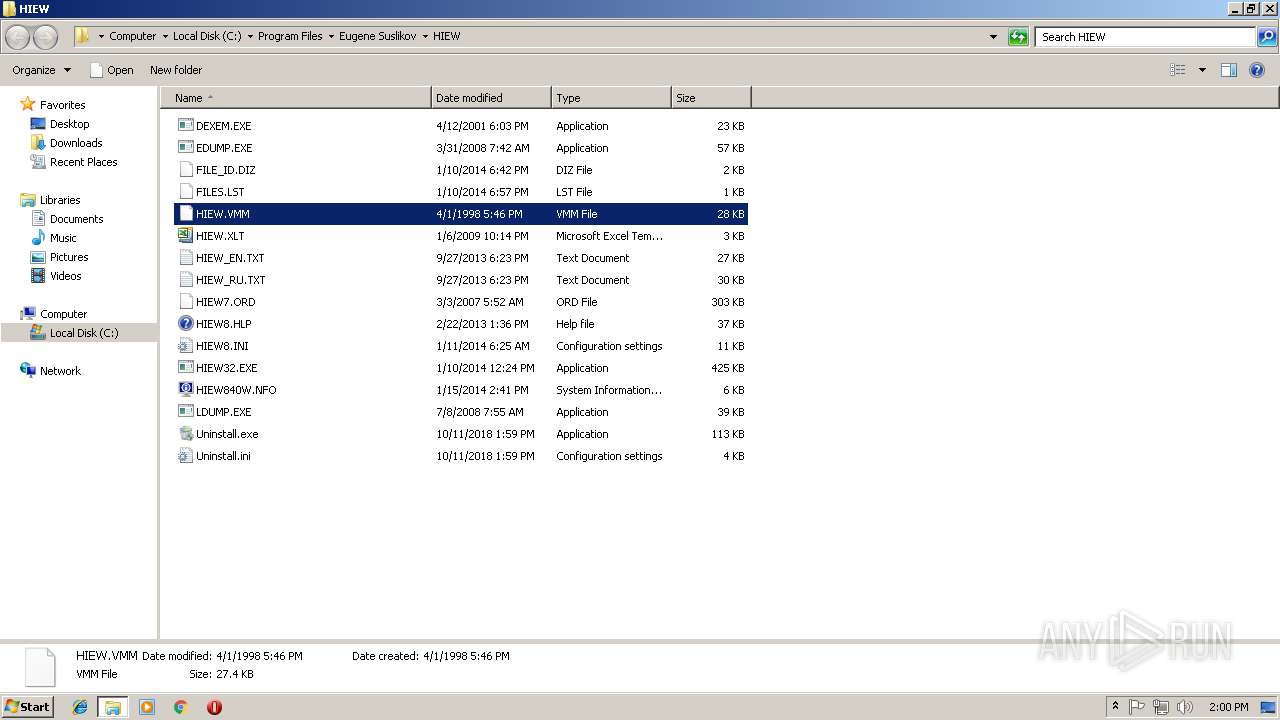
| 3704 | Setup.exe | C:\Program Files\Eugene Suslikov\HIEW\HIEW8.HLP | text | |
MD5:— | SHA256:— | |||
| 3704 | Setup.exe | C:\Program Files\Eugene Suslikov\HIEW\EDUMP.EXE | executable | |
MD5:— | SHA256:— | |||
| 3704 | Setup.exe | C:\Program Files\Eugene Suslikov\HIEW\HIEW32.EXE | executable | |
MD5:— | SHA256:— | |||
| 3704 | Setup.exe | C:\Program Files\Eugene Suslikov\HIEW\HIEW840W.NFO | text | |
MD5:— | SHA256:— | |||
| 3704 | Setup.exe | C:\Users\admin\AppData\Local\Temp\$inst\8.tmp | image | |
MD5:BAC172B887BC7D09DB5E14CE26A4943E | SHA256:AAA3BEE9EBD3640C05B8A70F22C9FBDB8EA0E61CA3762DB5A4583E94D46A5C79 | |||
| 3704 | Setup.exe | C:\Program Files\Eugene Suslikov\HIEW\HIEW_RU.TXT | text | |
MD5:— | SHA256:— | |||
| 3704 | Setup.exe | C:\Program Files\Eugene Suslikov\HIEW\FILES.LST | text | |
MD5:— | SHA256:— | |||
| 3704 | Setup.exe | C:\Program Files\Eugene Suslikov\HIEW\FILE_ID.DIZ | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
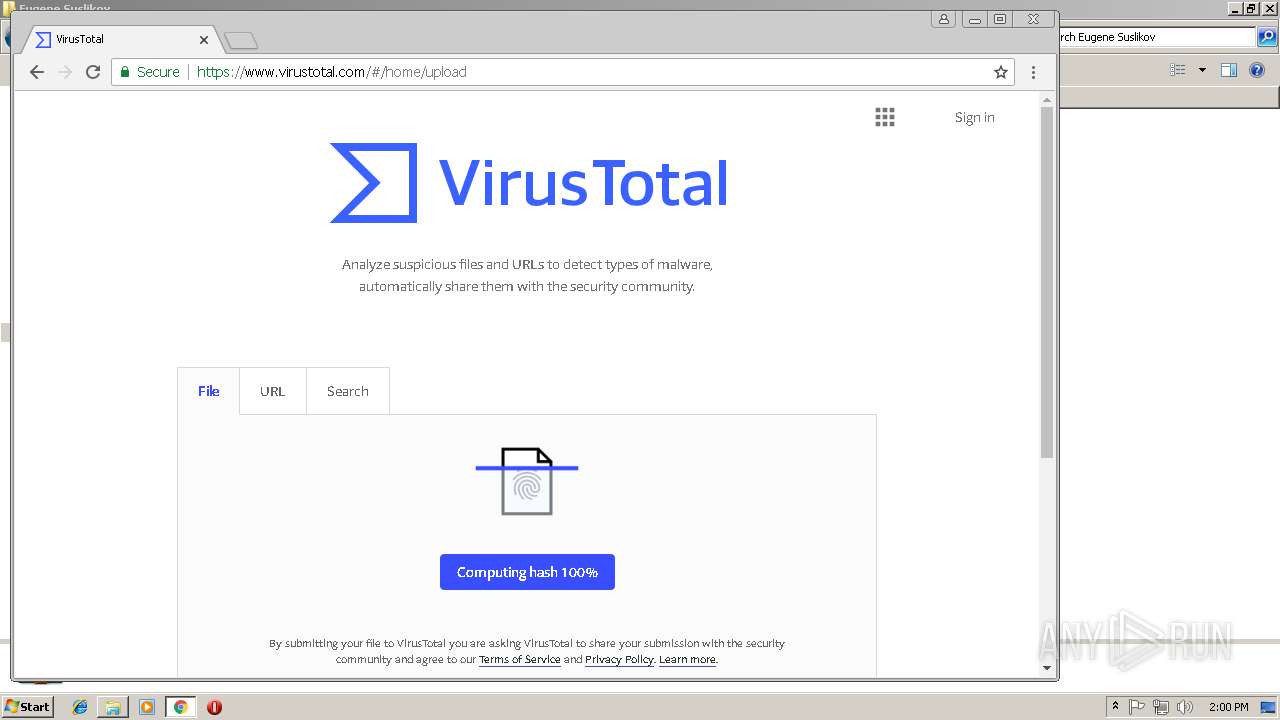
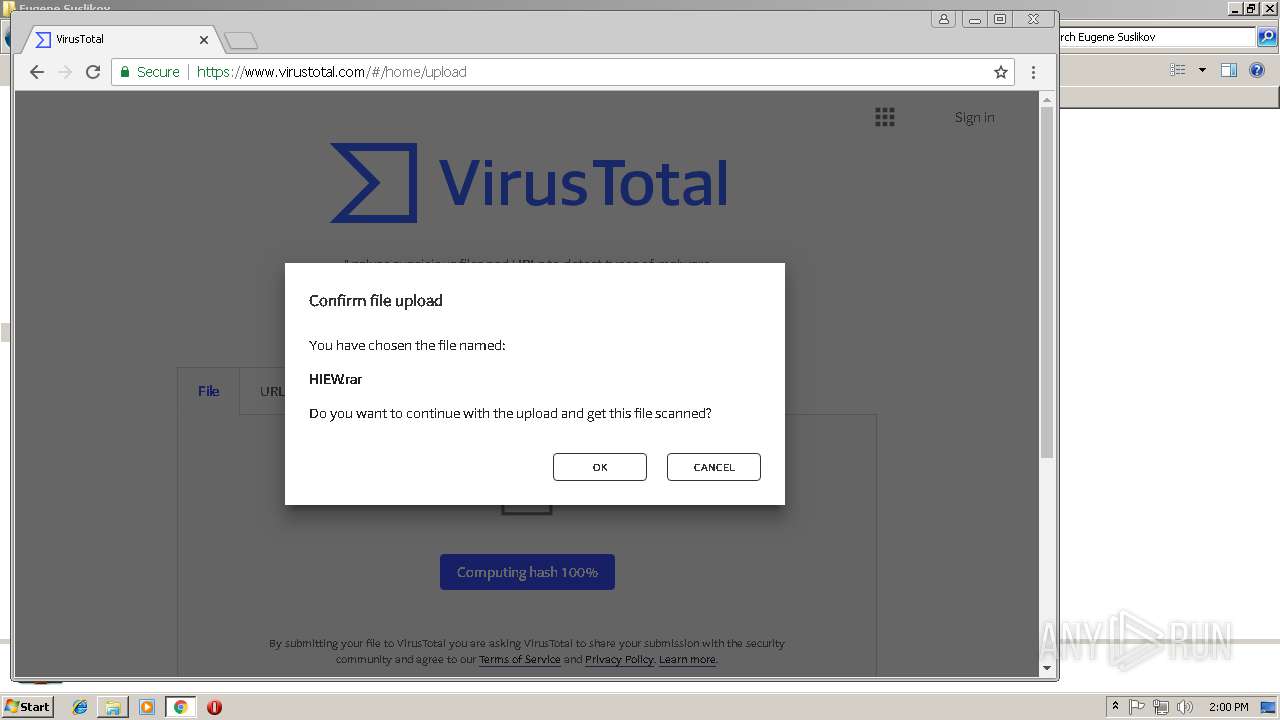
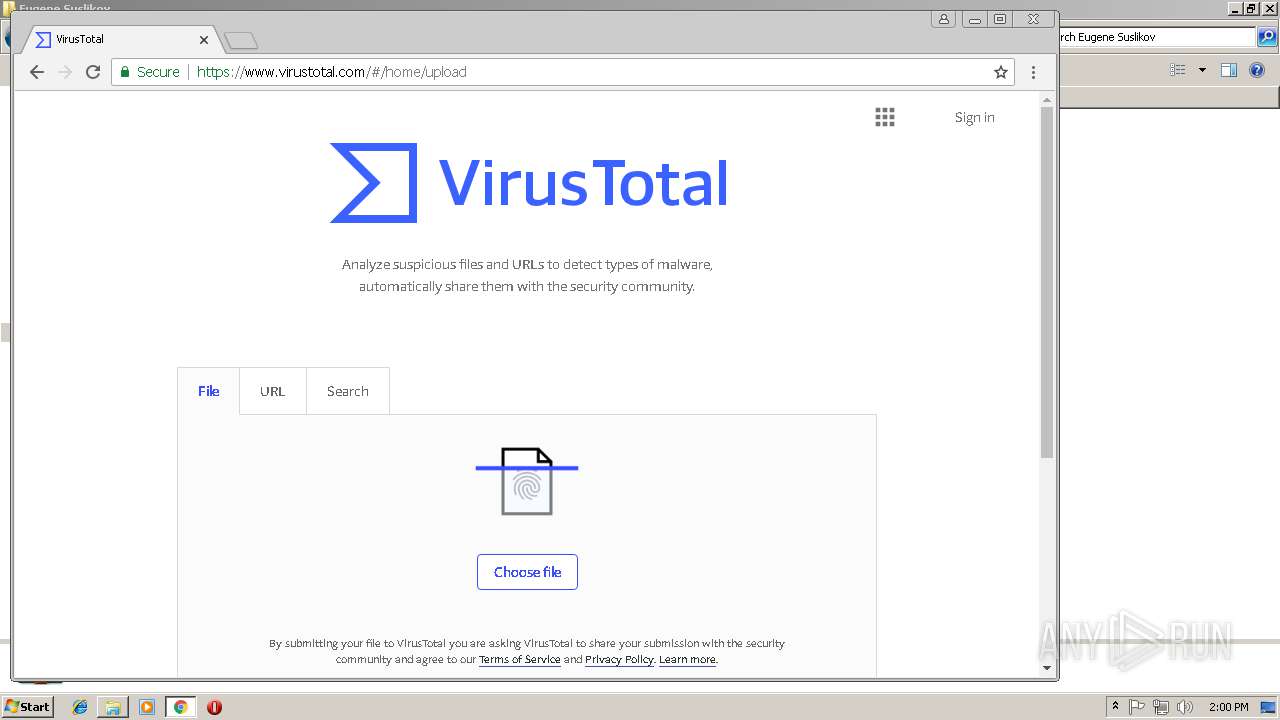
HTTP(S) requests
1
TCP/UDP connections
34
DNS requests
15
Threats
0
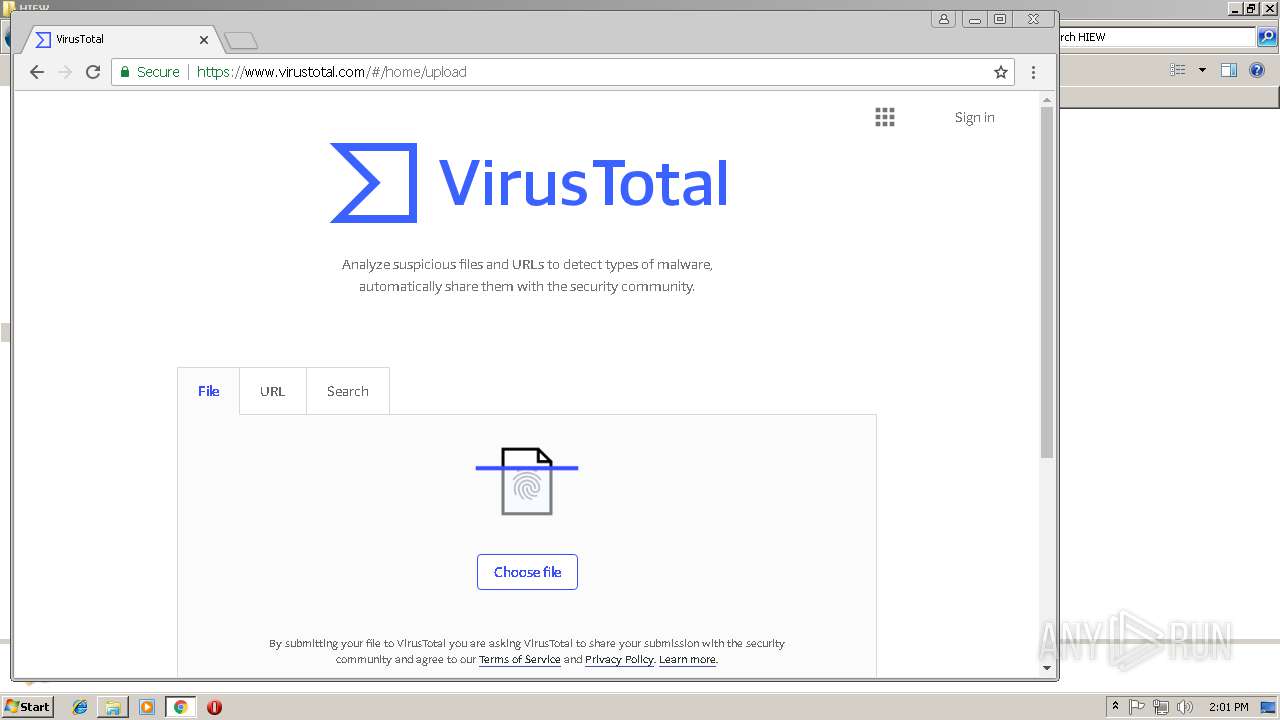
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
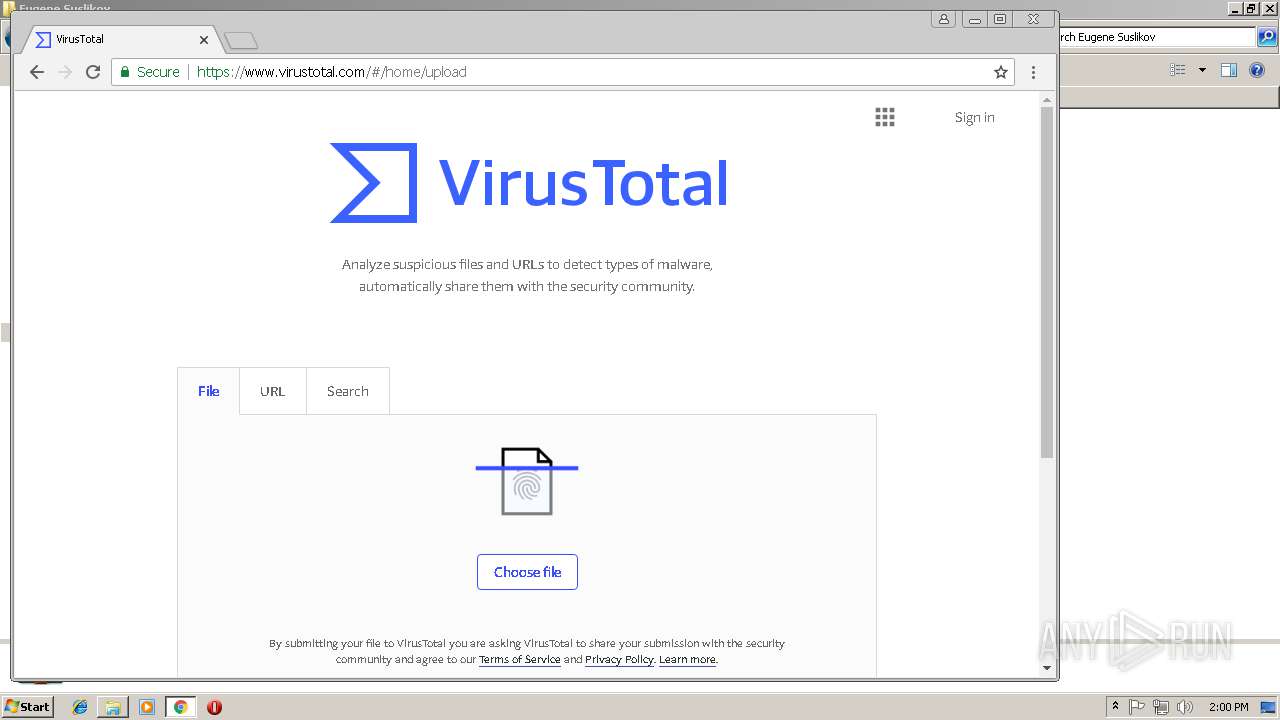
2848 | chrome.exe | GET | 302 | 216.239.38.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2848 | chrome.exe | 172.217.20.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.20.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.19.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.17.35:443 | www.google.de | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.239.38.21:80 | virustotal.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.19.196:443 | www.google.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 216.239.38.21:443 | virustotal.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 74.125.34.46:443 | www.virustotal.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.20.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2848 | chrome.exe | 172.217.17.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
virustotal.com |
| whitelisted |
www.virustotal.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |