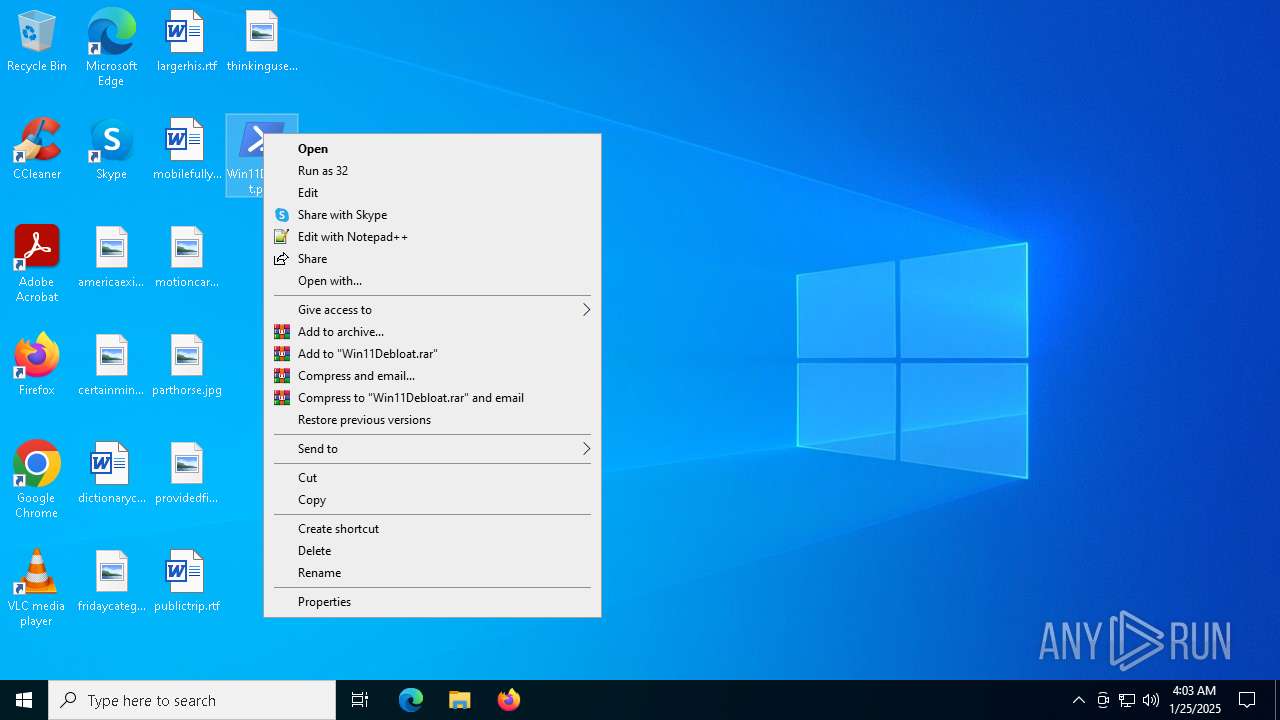
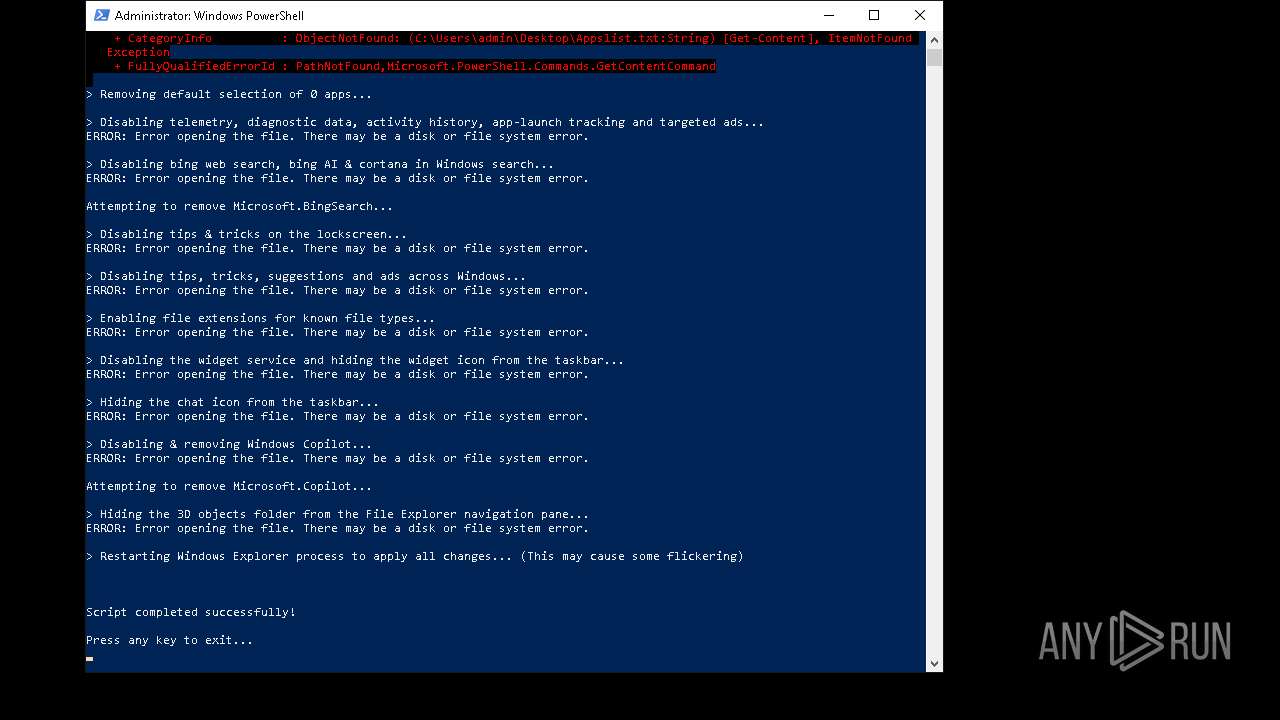
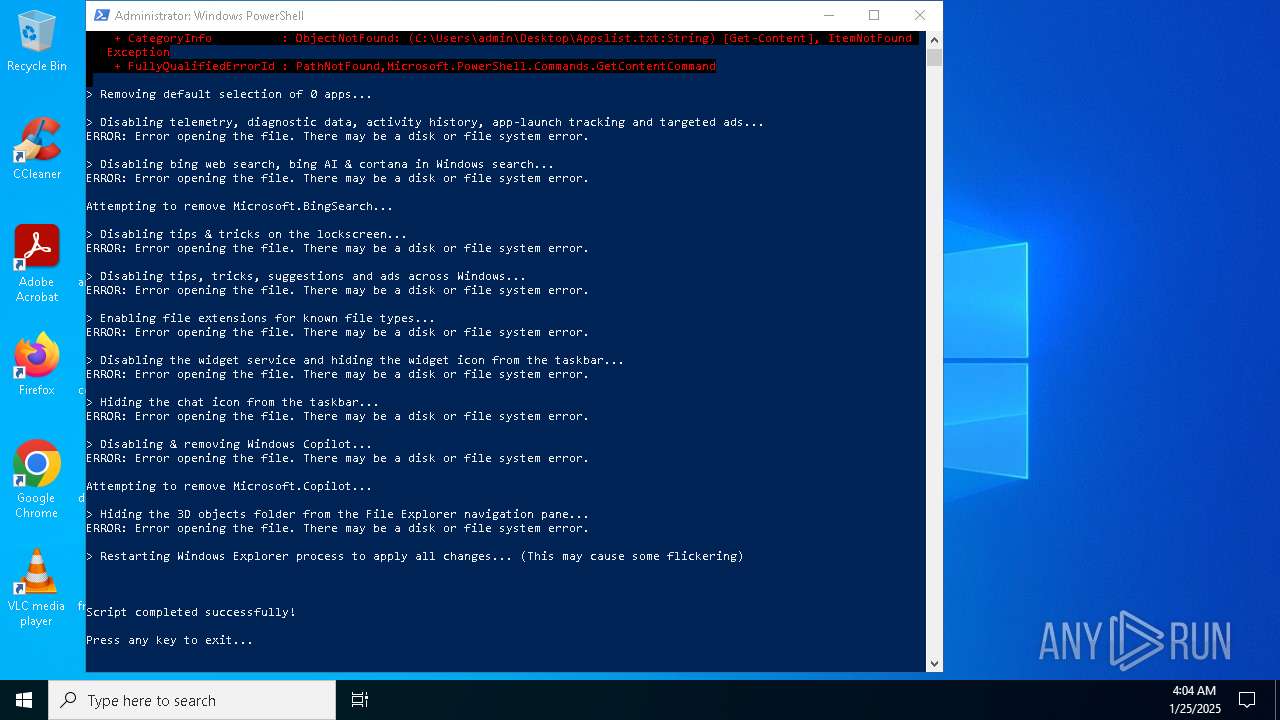
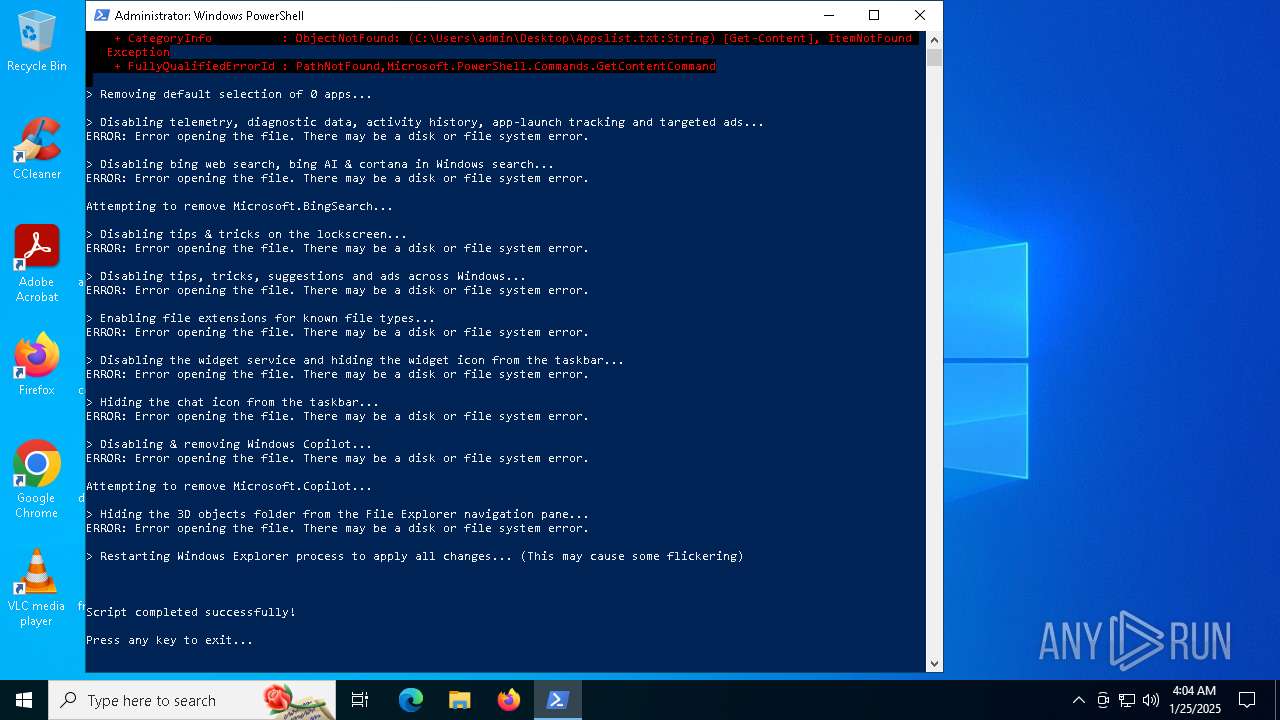
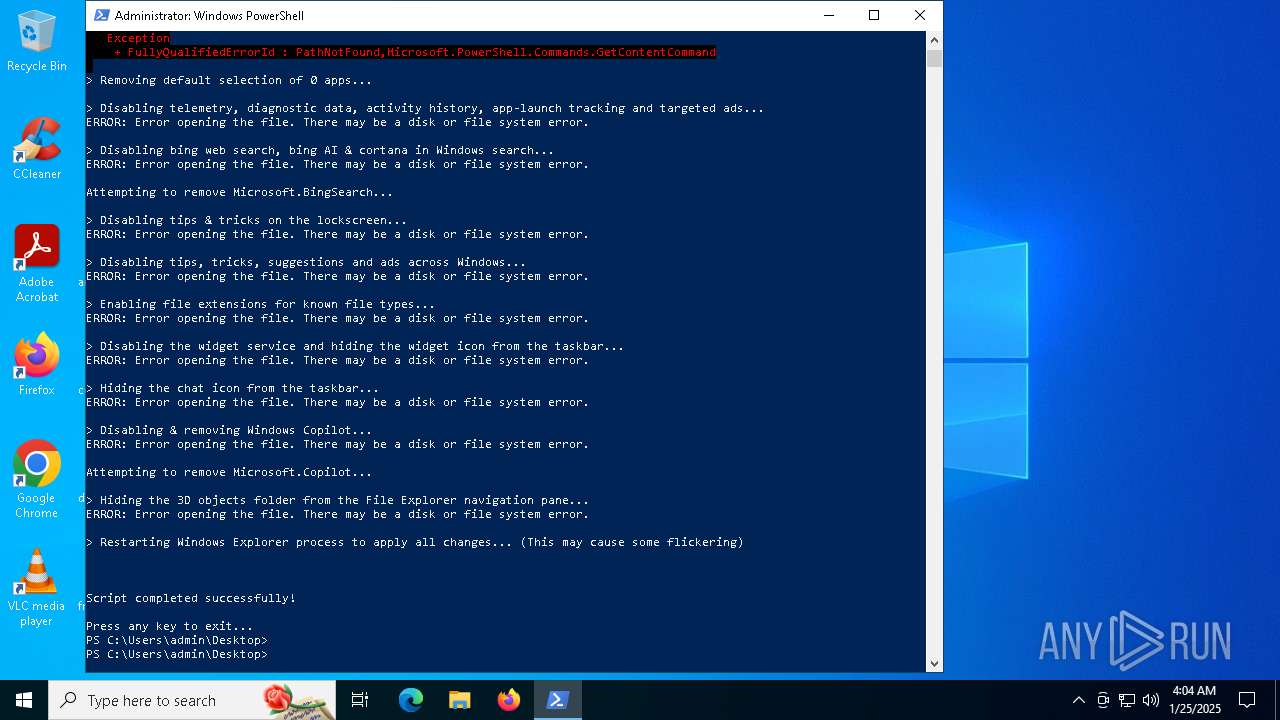
| File name: | Win11Debloat.ps1 |
| Full analysis: | https://app.any.run/tasks/18c3e7e9-b697-4117-98b7-931f0afc8a2c |
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2025, 04:02:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text |
| MD5: | 704F93FAD4179ACDE68B18B21E1643C3 |
| SHA1: | 8884885F91B0F43EFB930F37EDC1DAE34B003507 |
| SHA256: | 30C43D823809F4EDDD3ED7CEDA7A6720A326B1C8279B875A900D7E9232D9CA4B |
| SSDEEP: | 768:UAzvOaIdarHVtPizoRv7l+/wtwAFEZnwyw+LBYTTExfc:UwvOaUGPiEv71nExk |
MALICIOUS
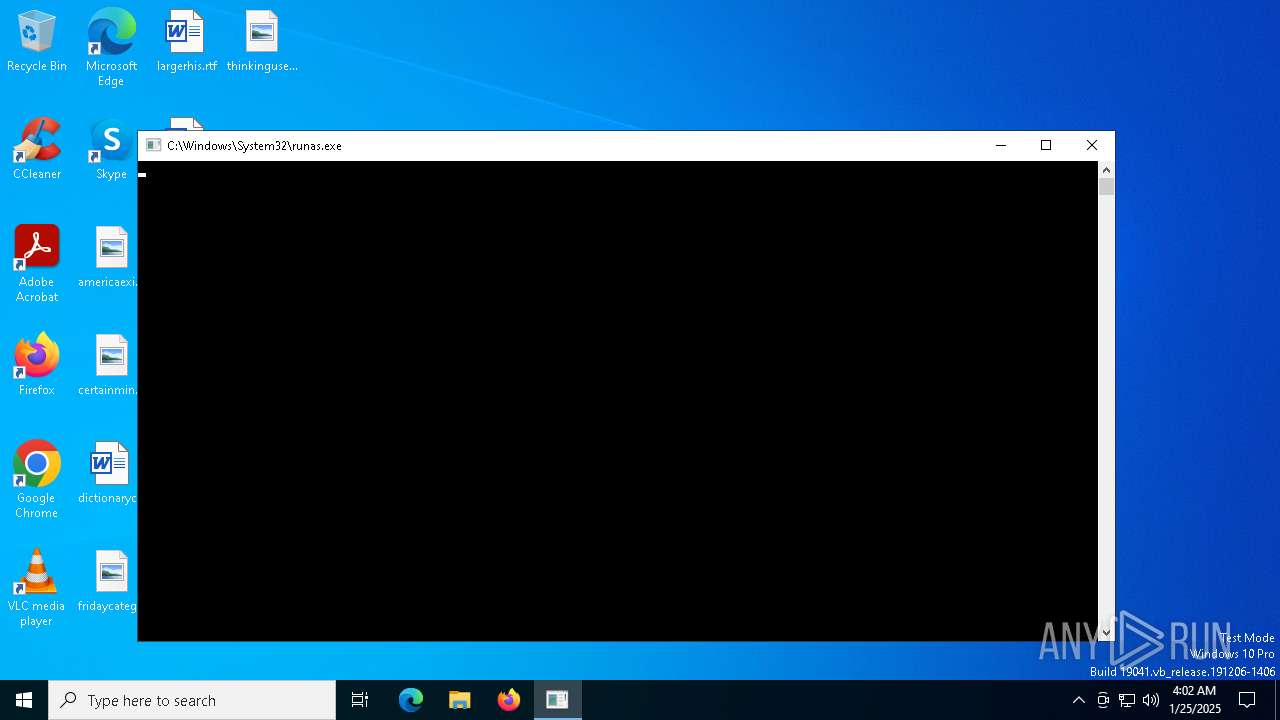
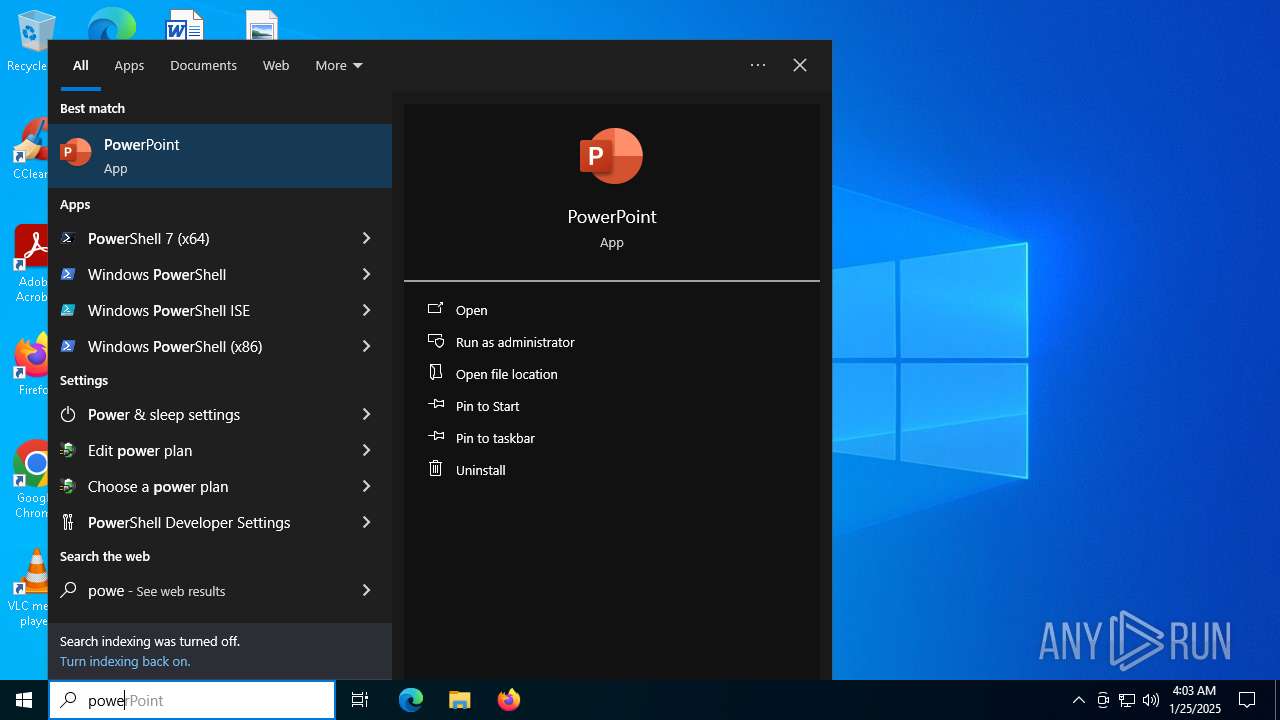
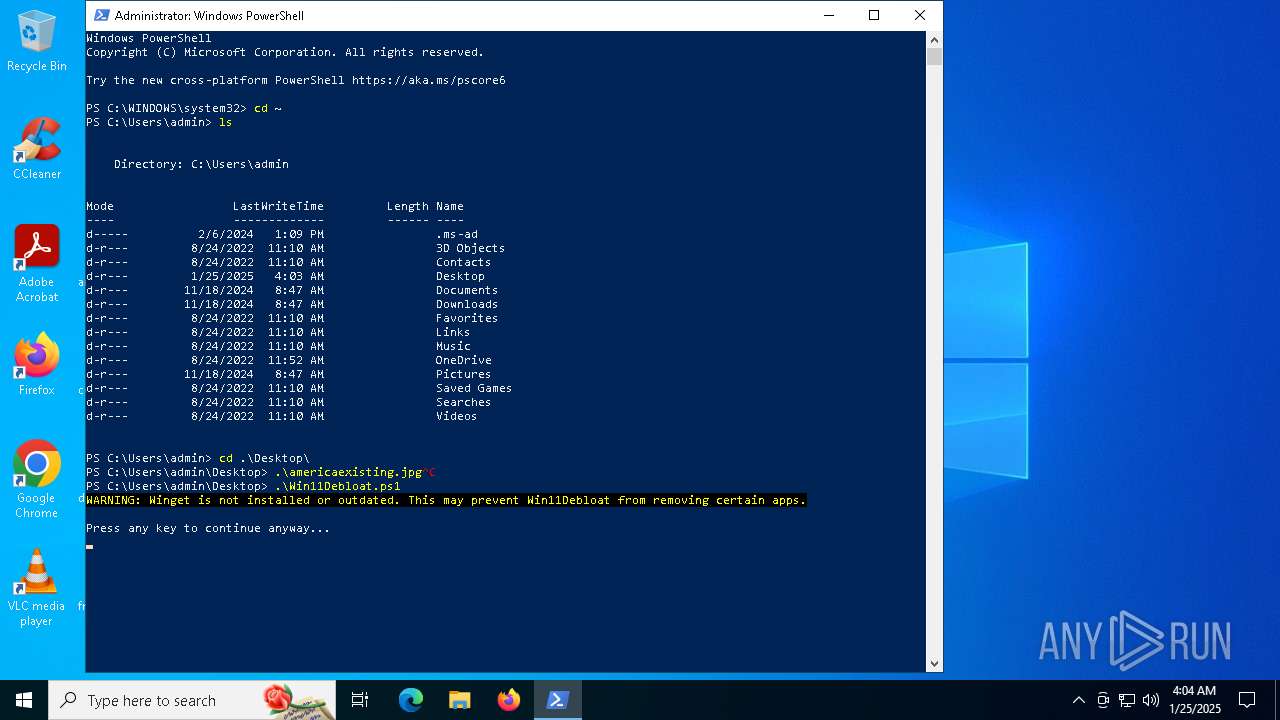
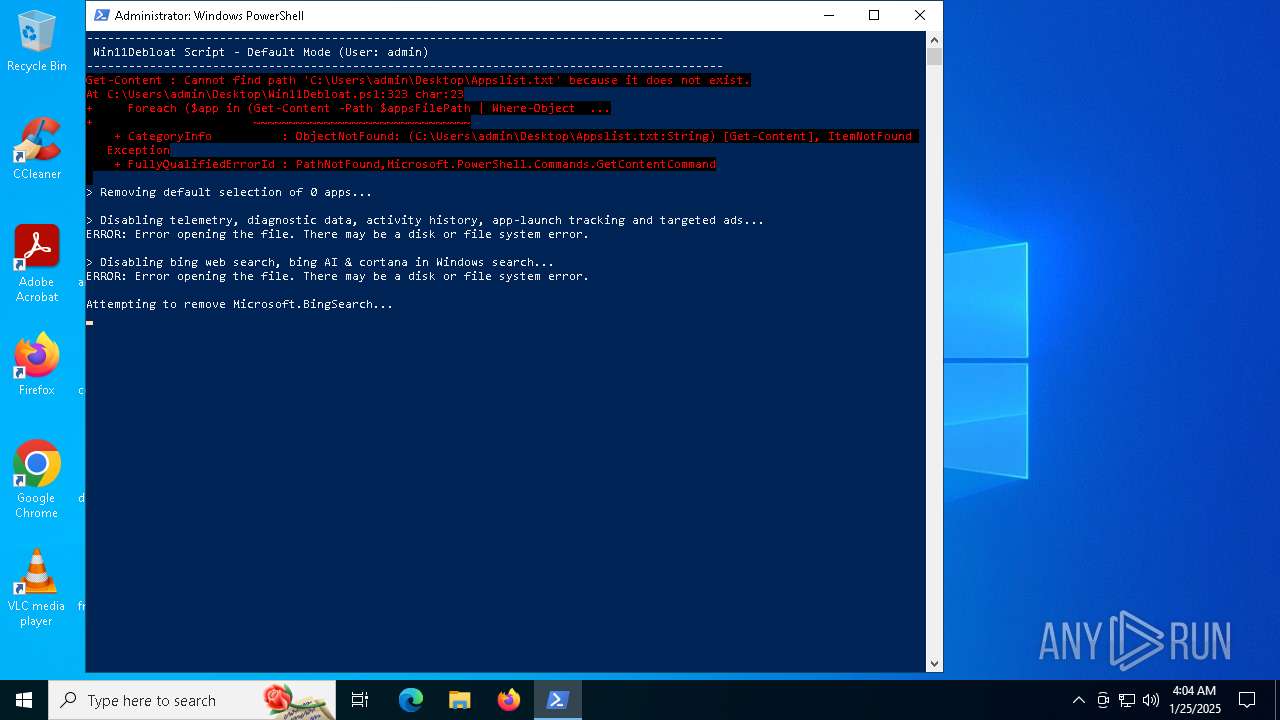
Bypass execution policy to execute commands
- powershell.exe (PID: 2008)
- powershell.exe (PID: 5244)
SUSPICIOUS
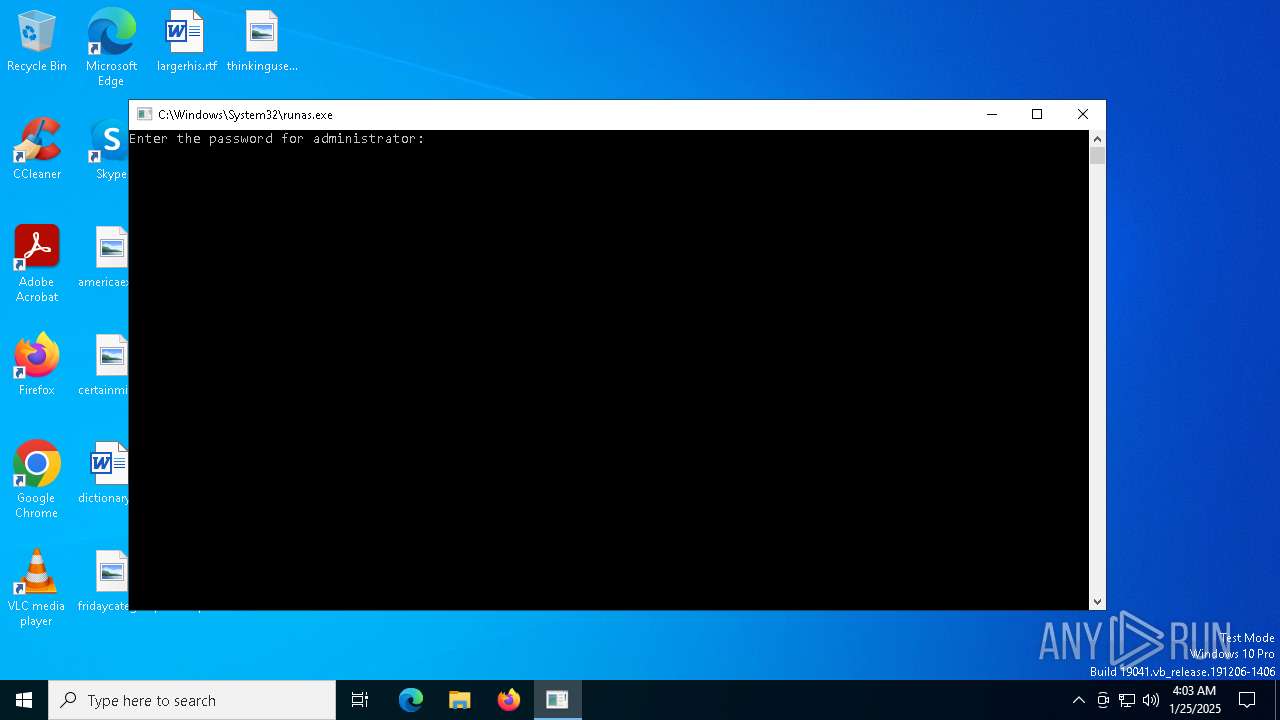
Starts another process probably with elevated privileges via RUNAS.EXE
- runas.exe (PID: 6520)
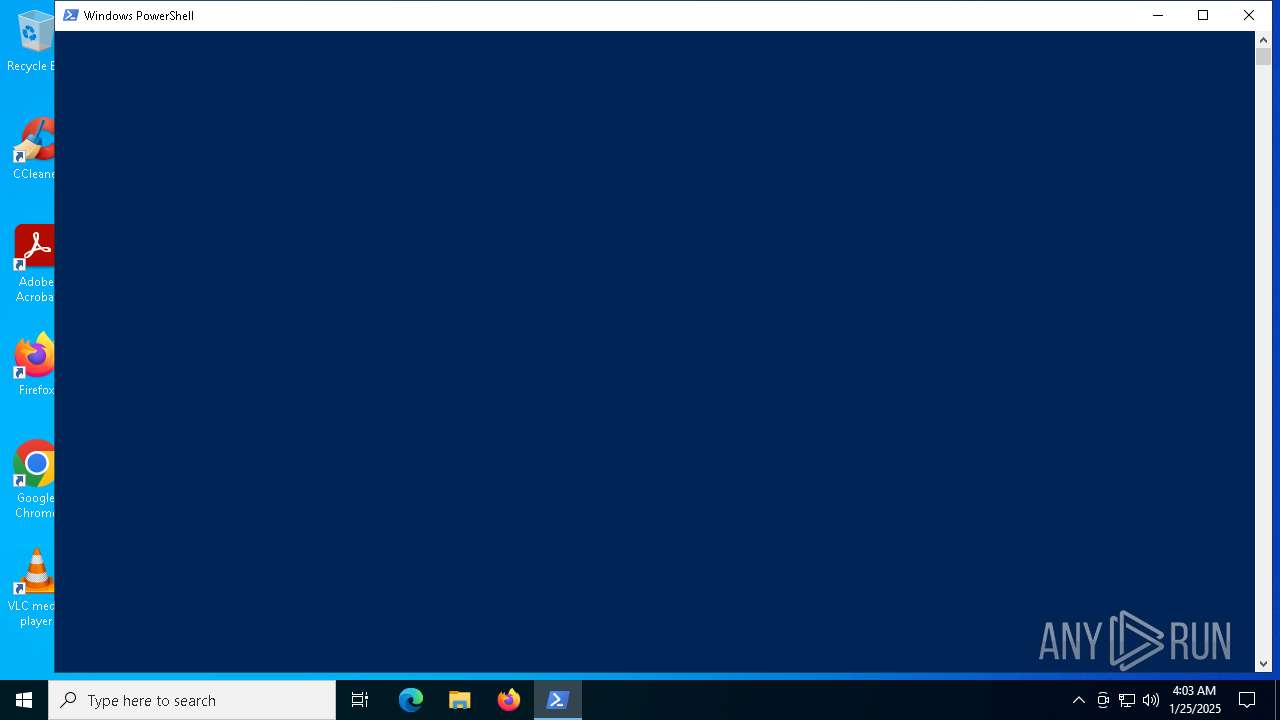
The process executes via Task Scheduler
- powershell.exe (PID: 3564)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 3564)
Uses REG/REGEDIT.EXE to modify registry
- powershell.exe (PID: 3564)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 3564)
The process creates files with name similar to system file names
- powershell.exe (PID: 3564)
Executable content was dropped or overwritten
- powershell.exe (PID: 3564)
Process drops legitimate windows executable
- powershell.exe (PID: 3564)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 5036)
- DismHost.exe (PID: 6056)
Reads security settings of Internet Explorer
- StartMenuExperienceHost.exe (PID: 6668)
Reads the date of Windows installation
- StartMenuExperienceHost.exe (PID: 6668)
- SearchApp.exe (PID: 6956)
INFO
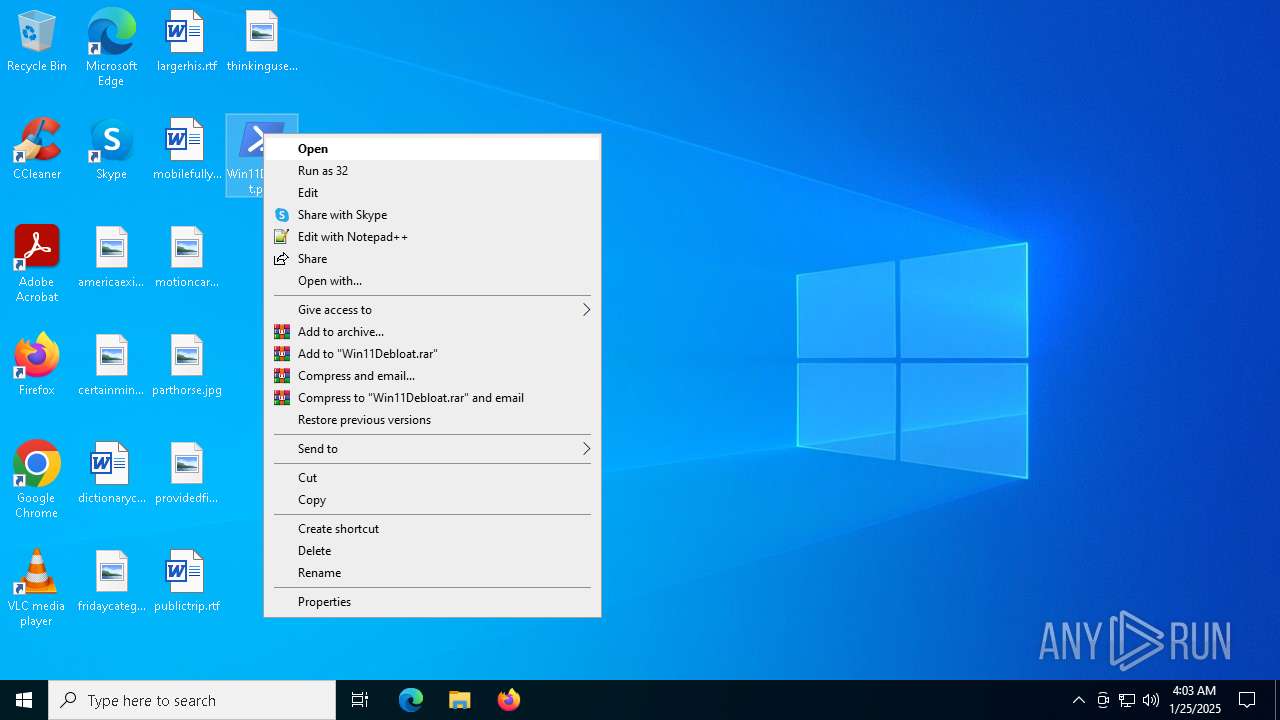
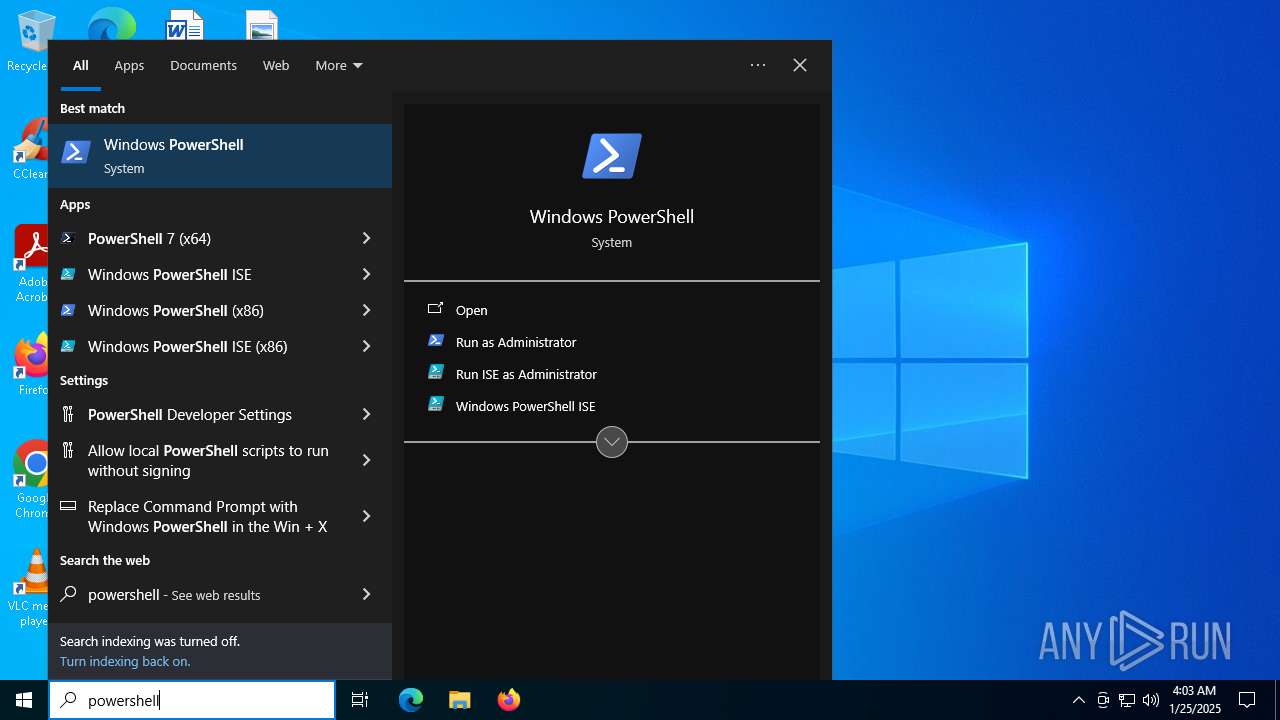
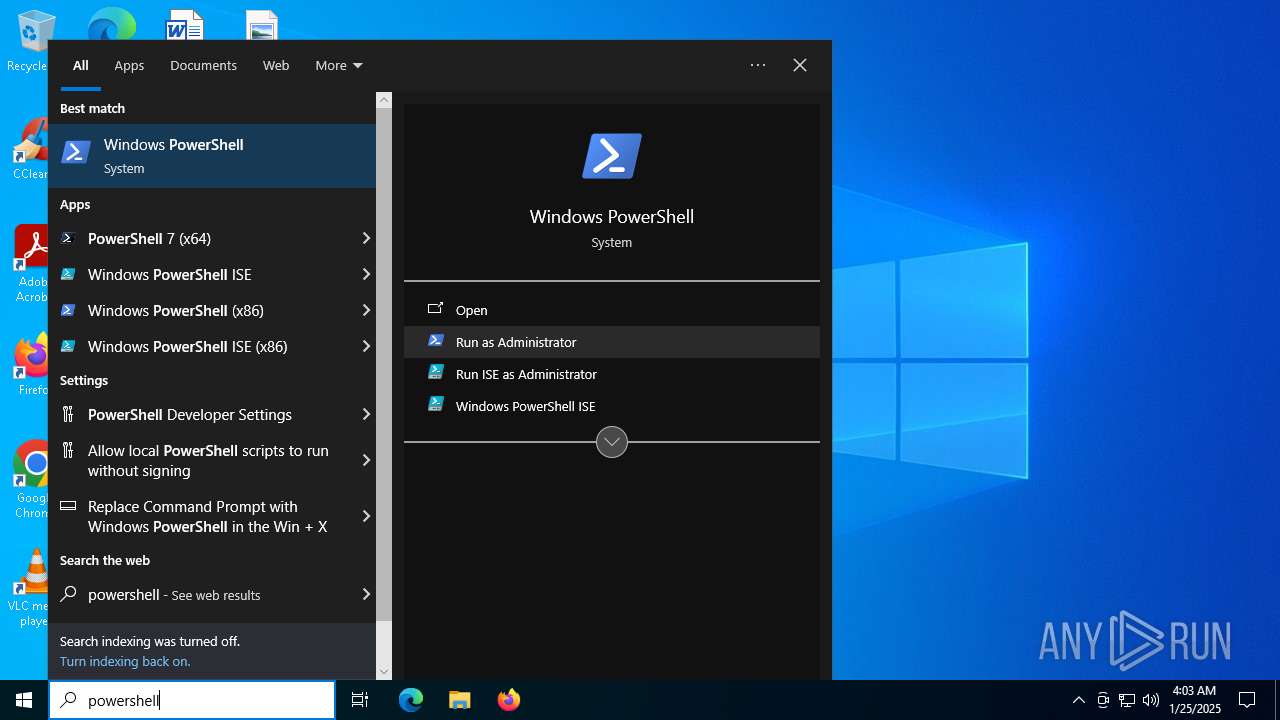
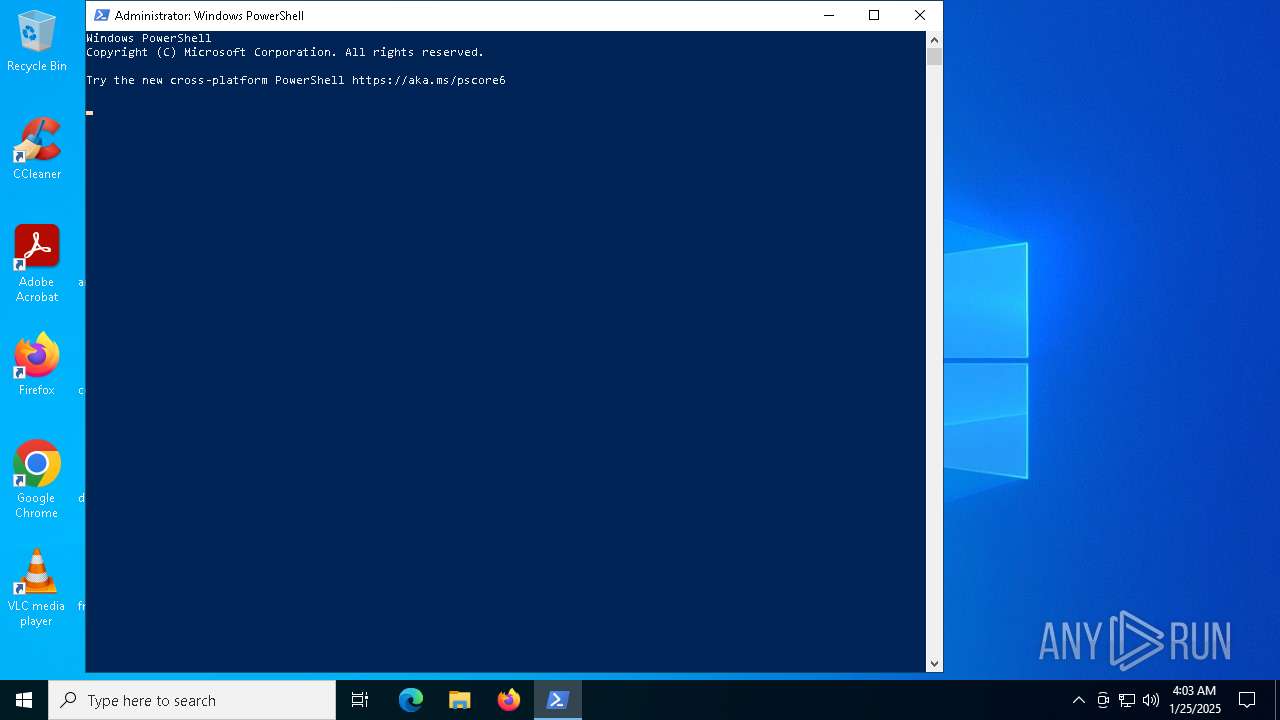
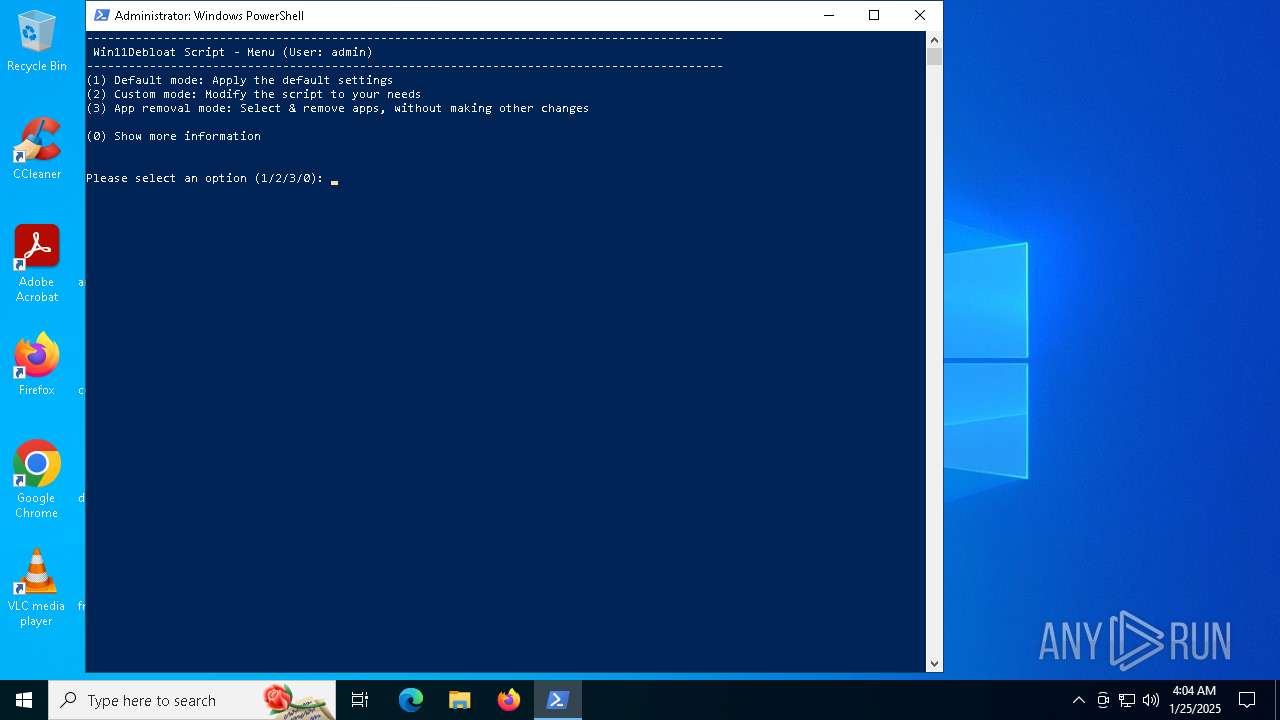
Manual execution by a user
- powershell.exe (PID: 2008)
- powershell.exe (PID: 5244)
Checks current location (POWERSHELL)
- powershell.exe (PID: 3564)
Gets or sets the time when the file was last written to (POWERSHELL)
- powershell.exe (PID: 3564)
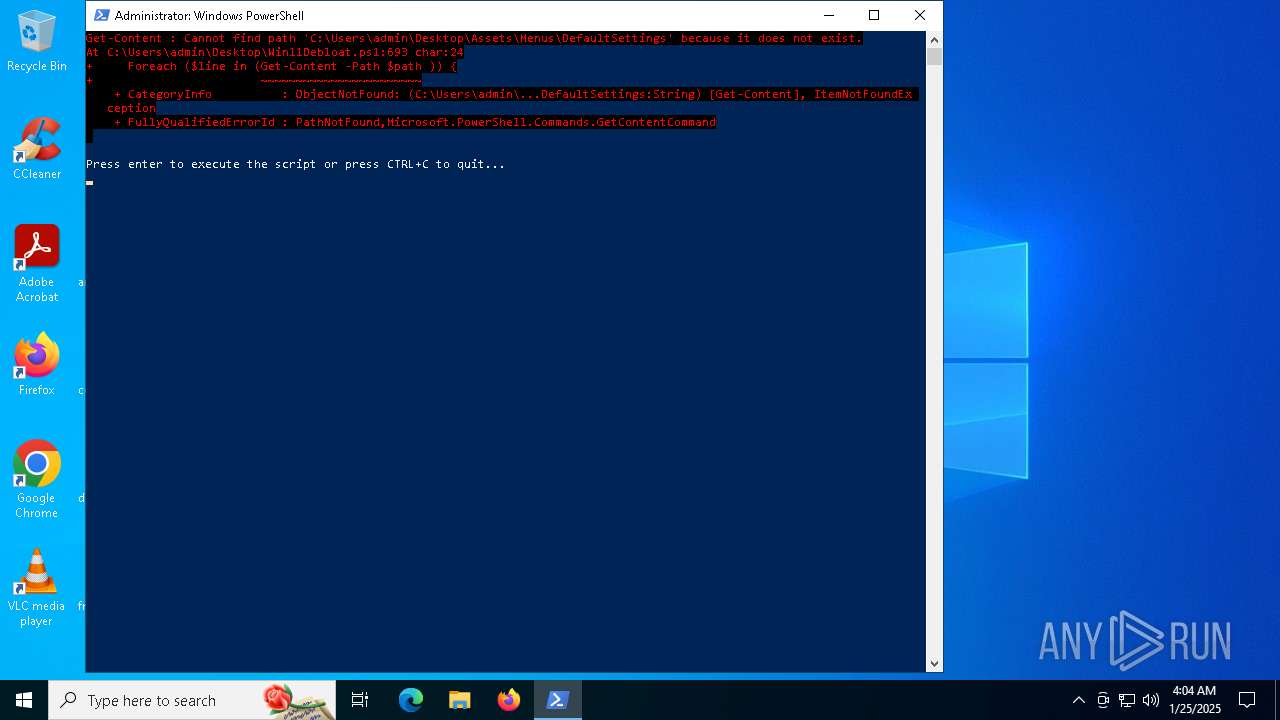
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 2008)
- powershell.exe (PID: 3564)
- powershell.exe (PID: 5244)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3564)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3564)
The sample compiled with english language support
- powershell.exe (PID: 3564)
Reads Environment values
- DismHost.exe (PID: 6056)
- DismHost.exe (PID: 5036)
- SearchApp.exe (PID: 6956)
Checks supported languages
- DismHost.exe (PID: 6056)
- DismHost.exe (PID: 5036)
- TextInputHost.exe (PID: 6428)
- StartMenuExperienceHost.exe (PID: 6668)
- SearchApp.exe (PID: 6956)
Reads the computer name
- DismHost.exe (PID: 5036)
- DismHost.exe (PID: 6056)
- StartMenuExperienceHost.exe (PID: 6668)
- TextInputHost.exe (PID: 6428)
- SearchApp.exe (PID: 6956)
Process checks computer location settings
- StartMenuExperienceHost.exe (PID: 6668)
- SearchApp.exe (PID: 6956)
Checks proxy server information
- SearchApp.exe (PID: 6956)
- BackgroundTransferHost.exe (PID: 544)
Reads the software policy settings
- SearchApp.exe (PID: 6956)
- BackgroundTransferHost.exe (PID: 544)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 6956)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 544)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5428)
- BackgroundTransferHost.exe (PID: 544)
- BackgroundTransferHost.exe (PID: 5568)
- BackgroundTransferHost.exe (PID: 6224)
- BackgroundTransferHost.exe (PID: 6292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ovpn | | | OpenVPN profile (with rem) (100) |
|---|
Total processes
175
Monitored processes
29
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\WINDOWS\system32\reg.exe" import C:\Users\admin\Desktop\Regfiles\Disable_Widgets_Taskbar.reg | C:\Windows\System32\reg.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 544 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\Win11Debloat.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\System32\mobsync.exe -Embedding | C:\Windows\System32\mobsync.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Sync Center Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2940 | "C:\WINDOWS\system32\reg.exe" import C:\Users\admin\Desktop\Regfiles\Disable_Copilot.reg | C:\Windows\System32\reg.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2996 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3208 | "C:\WINDOWS\system32\reg.exe" import C:\Users\admin\Desktop\Regfiles\Disable_Windows_Suggestions.reg | C:\Windows\System32\reg.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3564 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | RuntimeBroker.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3688 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4144 | "C:\WINDOWS\system32\reg.exe" import C:\Users\admin\Desktop\Regfiles\Disable_Telemetry.reg | C:\Windows\System32\reg.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 025
Read events
30 939
Write events
83
Delete events
3
Modification events
| (PID) Process: | (6668) StartMenuExperienceHost.exe | Key: | \REGISTRY\A\{97eb8fea-43c7-12f9-d57e-52548fba8251}\LocalState\DataCorruptionRecovery |
| Operation: | write | Name: | InitializationAttemptCount |
Value: 0100000016864D41DE6EDB01 | |||
| (PID) Process: | (6668) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (6668) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_AppUsageData |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (6668) StartMenuExperienceHost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows NT\CurrentVersion\TileDataModel\Migration\StartNonLayoutProperties_TargetedContentTiles |
| Operation: | write | Name: | Completed |
Value: 1 | |||
| (PID) Process: | (6324) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31157982 | |||
| (PID) Process: | (6324) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
| (PID) Process: | (6668) StartMenuExperienceHost.exe | Key: | \REGISTRY\A\{97eb8fea-43c7-12f9-d57e-52548fba8251}\LocalState\DataCorruptionRecovery |
| Operation: | write | Name: | InitializationAttemptCount |
Value: 00000000FAAD7341DE6EDB01 | |||
| (PID) Process: | (6956) SearchApp.exe | Key: | \REGISTRY\A\{d35d79ec-7037-1a31-d0f6-9d4b62296d75}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_USEREMAIL |
Value: 0000087E8B41DE6EDB01 | |||
| (PID) Process: | (6956) SearchApp.exe | Key: | \REGISTRY\A\{d35d79ec-7037-1a31-d0f6-9d4b62296d75}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPETEXT |
Value: 000017E28D41DE6EDB01 | |||
| (PID) Process: | (6956) SearchApp.exe | Key: | \REGISTRY\A\{d35d79ec-7037-1a31-d0f6-9d4b62296d75}\LocalState |
| Operation: | write | Name: | BINGIDENTITY_PROP_ACCOUNTTYPE |
Value: 000017E28D41DE6EDB01 | |||
Executable files
102
Suspicious files
16
Text files
106
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_asw5fqdz.5w5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5zmzhuh5.dru.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:9701896F442F99A756462EB9710BDD22 | SHA256:A98F5FD6F6A35B0E319C0740415CA800D7B134347FF74E052E13FD737BD5EE59 | |||
| 2008 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K681I73KGU9LEA2Y0FHA.temp | binary | |
MD5:C1B83A847D36B22B3C6A583AFC8D7059 | SHA256:FF94ABD7C449C7D4251F6BEB127DE12ECB133704823E05D57F0147AE4C045CA3 | |||
| 5244 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:E7E3B5D6B31821DBFBE14A6B774F1E7D | SHA256:9B00DC5FFA3C41ED4A1D340F53E1BDF8E296136B1F8DC784FC1123C59E08DC85 | |||
| 5244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF13fcc2.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 2008 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ejfxtdsm.byd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\A29XO0SLS1CNSGBKTY7U.temp | binary | |
MD5:9701896F442F99A756462EB9710BDD22 | SHA256:A98F5FD6F6A35B0E319C0740415CA800D7B134347FF74E052E13FD737BD5EE59 | |||
| 2008 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:C1B83A847D36B22B3C6A583AFC8D7059 | SHA256:FF94ABD7C449C7D4251F6BEB127DE12ECB133704823E05D57F0147AE4C045CA3 | |||
| 3564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_c5pgnp1w.5mh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
49
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5564 | svchost.exe | GET | 200 | 23.216.77.21:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5564 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6276 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5036 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
544 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5036 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
556 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 104.126.37.128:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5564 | svchost.exe | 23.216.77.21:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5564 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
Threats
Process | Message |
|---|---|
reg.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|
reg.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|
powershell.exe | PID=3564 TID=4944 DismApi.dll: Parent process command line: "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" - DismInitializeInternal
|
powershell.exe | PID=3564 TID=4944 DismApi.dll: Host machine information: OS Version=10.0.19045, Running architecture=amd64, Number of processors=4 - DismInitializeInternal
|
powershell.exe | PID=3564 TID=4944 Input parameters: LogLevel: 2, LogFilePath: C:\WINDOWS\Logs\DISM\dism.log, ScratchDirectory: (null) - DismInitializeInternal
|
powershell.exe | PID=3564 TID=4944 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=3564 TID=4944 DismApi.dll: <----- Starting DismApi.dll session -----> - DismInitializeInternal
|
powershell.exe | PID=3564 TID=4944 DismApi.dll: API Version 10.0.19041.3758 - DismInitializeInternal
|
powershell.exe | PID=3564 TID=4944 Enter DismInitializeInternal - DismInitializeInternal
|
powershell.exe | PID=3564 TID=4944 DismApi.dll: - DismInitializeInternal
|