| File name: | DevExpress.Patch.exe |
| Full analysis: | https://app.any.run/tasks/5db0873e-0784-410e-94e3-03aaab379794 |
| Verdict: | Malicious activity |
| Analysis date: | September 14, 2019, 09:17:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 20A5C68E9A98C0409EAD730DB9891AFD |
| SHA1: | 3F5C8E32430596E217DCB3B4DEB3D0A742268F62 |
| SHA256: | 30B5D731842C1A78E910AEB22BF01A1FECFC9BD5F28DC65F5F6DF0BB32446C90 |
| SSDEEP: | 12288:Lyub3R31Qa6uYMwdWjWzQ5TracRJ2JoQO79B:eub33Z6JMwQj0Q1NvqoQG9B |
MALICIOUS
Loads dropped or rewritten executable
- DevExpress.Patch.exe (PID: 2196)
SUSPICIOUS
Reads internet explorer settings
- DevExpress.Patch.exe (PID: 2196)
Removes files from Windows directory
- DevExpress.Patch.exe (PID: 2196)
Executable content was dropped or overwritten
- DevExpress.Patch.exe (PID: 2196)
Creates files in the Windows directory
- ngen.exe (PID: 2668)
- DevExpress.Patch.exe (PID: 2196)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:06:16 14:17:58+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 630784 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9bf3e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 8.0.0.0 |
| ProductVersionNumber: | 8.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
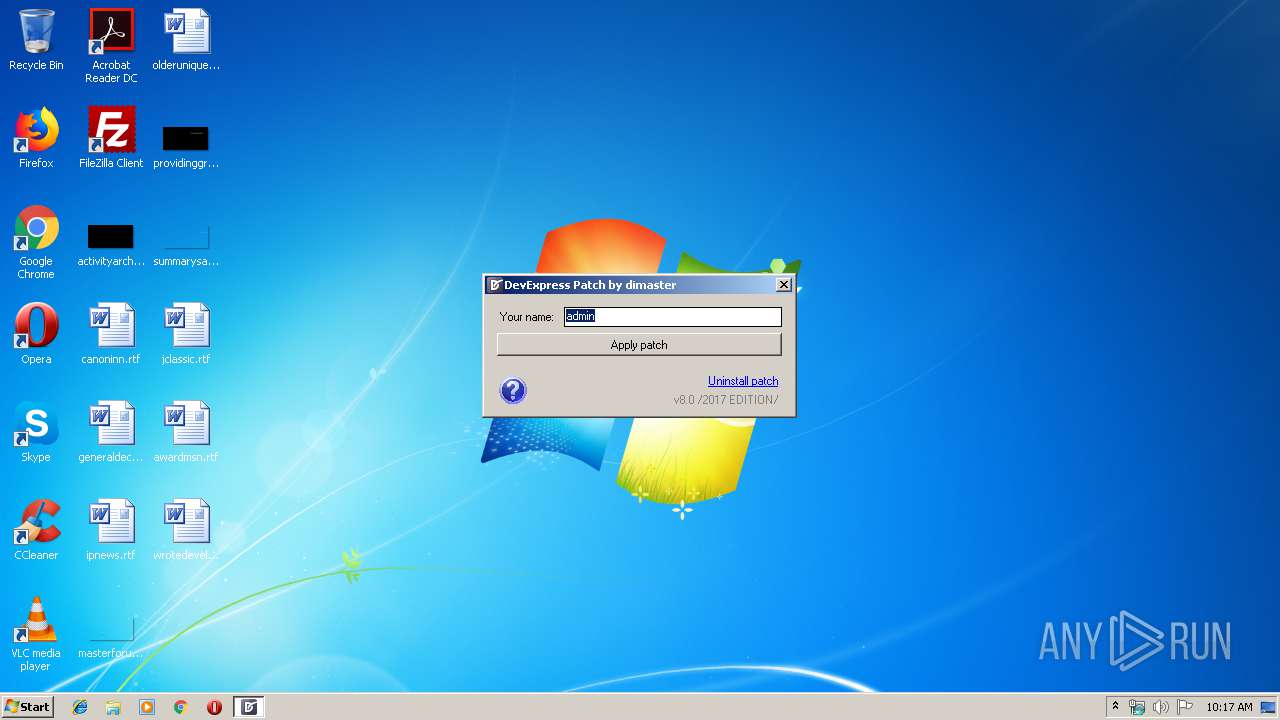
| CompanyName: | dimaster |
| FileDescription: | DevExpress.Patch |
| FileVersion: | 8.0.0.0 |
| InternalName: | DevExpress.Patch.exe |
| LegalCopyright: | Copyright © dimaster 2017 |
| LegalTrademarks: | - |
| OriginalFileName: | DevExpress.Patch.exe |
| ProductName: | DevExpress 2017 Universal Patch by dimaster |
| ProductVersion: | 8.0.0.0 |
| AssemblyVersion: | 8.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 16-Jun-2017 12:17:58 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | dimaster |
| FileDescription: | DevExpress.Patch |
| FileVersion: | 8.0.0.0 |
| InternalName: | DevExpress.Patch.exe |
| LegalCopyright: | Copyright © dimaster 2017 |
| LegalTrademarks: | - |
| OriginalFilename: | DevExpress.Patch.exe |
| ProductName: | DevExpress 2017 Universal Patch by dimaster |
| ProductVersion: | 8.0.0.0 |
| Assembly Version: | 8.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 16-Jun-2017 12:17:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00099F44 | 0x0009A000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.73402 |
.rsrc | 0x0009C000 | 0x00004D1C | 0x00004E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.83786 |
.reloc | 0x000A2000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.42965 | 3312 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.50497 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.35361 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.45849 | 48 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
42
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | "C:\Users\admin\AppData\Local\Temp\DevExpress.Patch.exe" | C:\Users\admin\AppData\Local\Temp\DevExpress.Patch.exe | explorer.exe | ||||||||||||
User: admin Company: dimaster Integrity Level: HIGH Description: DevExpress.Patch Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
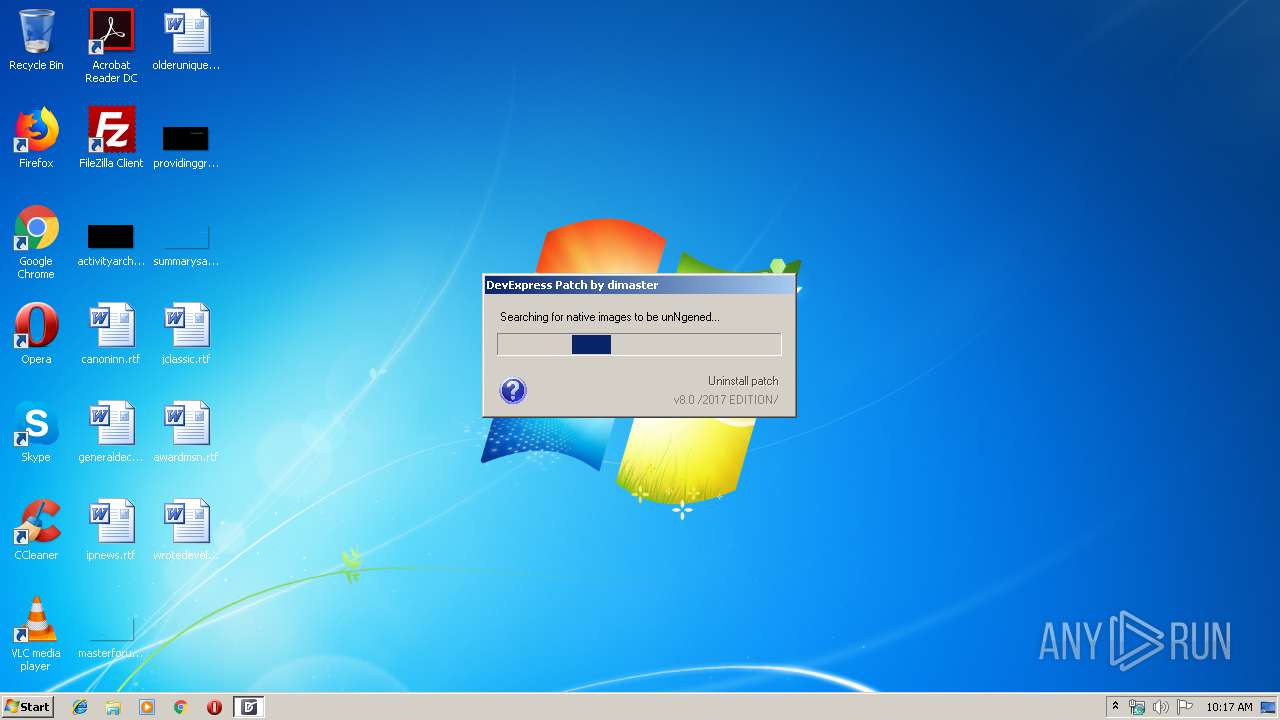
| 2464 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 100 -InterruptEvent 0 -NGENProcess f0 -Pipe fc -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 2668 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe" executeQueuedItems | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | DevExpress.Patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3076 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe -StartupEvent 174 -InterruptEvent 0 -NGENProcess 17c -Pipe 160 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 3584 | "C:\Users\admin\AppData\Local\Temp\DevExpress.Patch.exe" | C:\Users\admin\AppData\Local\Temp\DevExpress.Patch.exe | — | explorer.exe | |||||||||||
User: admin Company: dimaster Integrity Level: MEDIUM Description: DevExpress.Patch Exit code: 3221226540 Version: 8.0.0.0 Modules
| |||||||||||||||
| 3664 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe" display | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.exe | — | DevExpress.Patch.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Common Language Runtime native compiler Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
Total events
1 163
Read events
887
Write events
276
Delete events
0
Modification events
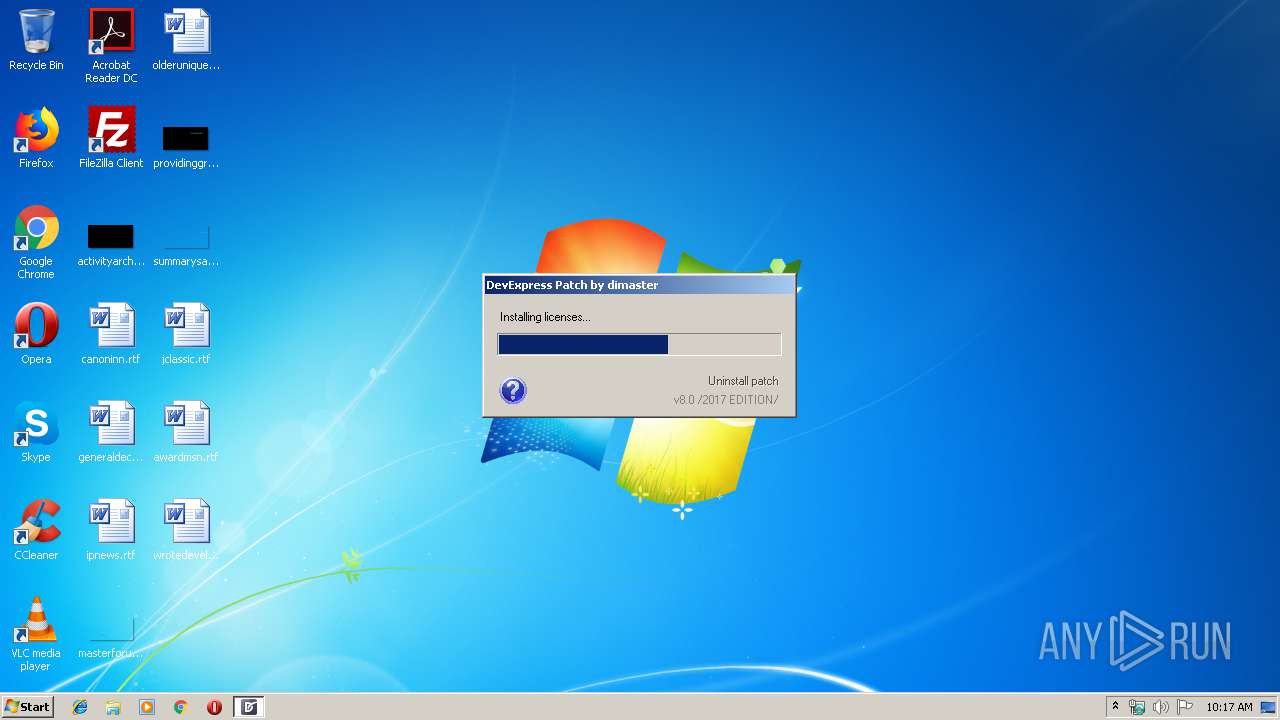
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application |
| Operation: | write | Name: | AutoBackupLogFiles |
Value: 0 | |||
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\COM+ SOAP Services |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Windows\Microsoft.NET\Framework\v4.0.30319\EventLogMessages.dll | |||
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fusion\GACChangeNotification\Default |
| Operation: | write | Name: | StoreChangeID |
Value: 582 | |||
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fusion\GACChangeNotification\Default |
| Operation: | write | Name: | StoreChangeIDFor64BitProcesses |
Value: 73 | |||
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fusion\GACChangeNotification\Default |
| Operation: | write | Name: | StoreChangeIDFor32BitProcesses |
Value: 582 | |||
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Fusion\GACChangeNotification\Default |
| Operation: | write | Name: | DevExpress.Patch.Common,8.0.0.0,,7fc7bfca2443de66,MSIL |
Value: 6CC0E848DD6AD501 | |||
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Licenses\0378852d-d597-4a32-b6d9-680a16a3cda6 |
| Operation: | write | Name: | 70 |
Value: OV+G/CqyE0LrWWQLQrvApSoVZ6Z20mqxAh5/OAGIqWm3g46Y4C5ey0ObYvJyxeXI0PPYfg99t8JEk6z3DwedYLvC1sdYa7dAb8t3yKLq4ZOjgpxKRn1iA+u8yuU+mhqJWm5BuA==AAAAAAAAAAAAAAAAAAAAAAAAAAA3MCwzNjczMzMwOTM5NjQ4NDExMywzNjczMzMwOTM5NjQ4NDExMyxhZG1pbiwxLDEsMQ== | |||
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Licenses\6F0F8269-1516-44C6-BD30-0E90BE27871C |
| Operation: | write | Name: | 70 |
Value: 1309 | |||
| (PID) Process: | (2196) DevExpress.Patch.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Licenses\0378852d-d597-4a32-b6d9-680a16a3cda6 |
| Operation: | write | Name: | 71 |
Value: pwcskkSTFYH4wbr3QYSYZCKUubWmZt6kwcraMMKmUTv3fRc5E6Z+DGGisS1VqNX5VzlWnOY1ot8ScA9/506Nuu5HCFGZmHNjqW1oBBd2dGtBopHZxkUkvIKV8TIH2B4rN0cH6w==AAAAAAAAAAAAAAAAAAAAAAAAAAA3MSwzNjczMzMwOTM5NjQ4NDExMywzNjczMzMwOTM5NjQ4NDExMyxhZG1pbiwxLDEsMQ== | |||
Executable files
5
Suspicious files
0
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2196 | DevExpress.Patch.exe | C:\Windows\tfadxp80.txt | — | |
MD5:— | SHA256:— | |||
| 2196 | DevExpress.Patch.exe | C:\Windows\assembly\tmp\ROV7INQE\DevExpress.Patch.Common.dll | — | |
MD5:— | SHA256:— | |||
| 2196 | DevExpress.Patch.exe | C:\Windows\assembly\GAC_MSIL\DevExpress.Patch.Common\8.0.0.0__7fc7bfca2443de66 | — | |
MD5:— | SHA256:— | |||
| 2196 | DevExpress.Patch.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.log | text | |
MD5:— | SHA256:— | |||
| 3664 | ngen.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.log | text | |
MD5:— | SHA256:— | |||
| 2668 | ngen.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\ngen.log | text | |
MD5:— | SHA256:— | |||
| 2196 | DevExpress.Patch.exe | C:\Users\admin\AppData\Local\Temp\DevExpress.Patch.Common.dll | executable | |
MD5:660BAD0F52FC882539C8A1CA6E3E14E4 | SHA256:F7770C53E7593AB1213E438C33346B42E481EE88F18C1A8B4887248282847E1F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report