| File name: | loader-x86.exe |
| Full analysis: | https://app.any.run/tasks/3d68cf09-d067-45fc-ab9d-91da29ee90de |
| Verdict: | Malicious activity |
| Analysis date: | January 16, 2019, 01:52:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 88AF313256C691C169E0A98E0B848223 |
| SHA1: | A8CA0C24FA760ECC65BF834B29EADD6722688912 |
| SHA256: | 30B0E8E913C3BD374B301F776E3C79109FE4539F589D85ABDA8EBC9D980230BC |
| SSDEEP: | 6144:2DYxpIMAVOw8B2y0WPOitxkUA7JzJ9mMMMMMMMMMMMM2Th:2DwpIMqJ8BPLMMMMMMMMMMMM21 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2404)
- cmd.exe (PID: 3660)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3660)
- loader-x86.exe (PID: 3152)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (63.7) |
|---|---|---|
| .scr | | | Windows screen saver (20) |
| .exe | | | Win32 Executable (generic) (6.9) |
| .exe | | | Win16/32 Executable Delphi generic (3.1) |
| .exe | | | Generic Win/DOS Executable (3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 13:44:34+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 111616 |
| InitializedDataSize: | 521728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c384 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.0.0 |
| ProductVersionNumber: | 3.5.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Mirillis Ltd. |
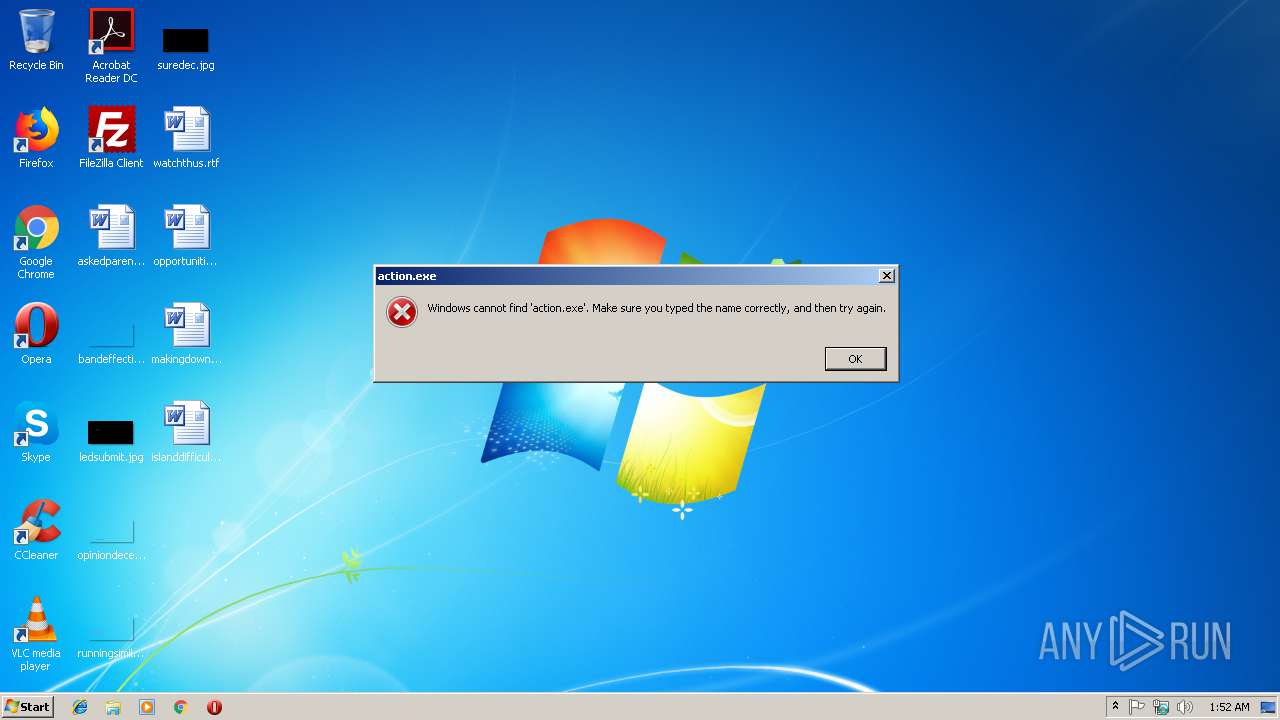
| FileDescription: | Loader For Mirillis Action! |
| FileVersion: | 3. 5. 0. 0 |
| InternalName: | ActionLoader.exe |
| LegalCopyright: | Copyright (C) 2009-2018 Mirillis Ltd. |
| LegalTrademarks: | Mirillis Ltd. |
| OriginalFileName: | ActionLoader.exe |
| ProductName: | Loader For Mirillis Action! |
| ProductVersion: | 3.5.0.0 |
| Comments: | Loader For Mirillis Action! |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Feb-2018 12:44:34 |
| Detected languages: |
|
| CompanyName: | Mirillis Ltd. |
| FileDescription: | Loader For Mirillis Action! |
| FileVersion: | 3. 5. 0. 0 |
| InternalName: | ActionLoader.exe |
| LegalCopyright: | Copyright (C) 2009-2018 Mirillis Ltd. |
| LegalTrademarks: | Mirillis Ltd. |
| OriginalFilename: | ActionLoader.exe |
| ProductName: | Loader For Mirillis Action! |
| ProductVersion: | 3.5.0.0 |
| Comments: | Loader For Mirillis Action! |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 01-Feb-2018 12:44:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001AA58 | 0x0001AC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.92348 |
.itext | 0x0001C000 | 0x00000758 | 0x00000800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.68491 |
.data | 0x0001D000 | 0x0000178C | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70696 |
.bss | 0x0001F000 | 0x00004FC8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00024000 | 0x00000B4A | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.68875 |
.didata | 0x00025000 | 0x000000C8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.44508 |
.tls | 0x00026000 | 0x0000000C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00027000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.210826 |
.reloc | 0x00028000 | 0x0000231C | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.437 |
.rsrc | 0x0002B000 | 0x0007A80C | 0x0007AA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.95945 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07702 | 517 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.84641 | 1720 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.5593 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.70139 | 3760 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.17769 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.29537 | 5512 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 4.83757 | 6760 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.83002 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 4.51423 | 14920 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 4.51634 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
advapi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
oleaut32.dll |
user32.dll |
Total processes
44
Monitored processes
11
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2268 | C:\Windows\system32\reg.exe query "HKU\S-1-5-19" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2404 | C:\Windows\system32\cmd.exe /c REG query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Mirillis Action!" /v InstallLocation | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2596 | reg add "HKEY_CURRENT_USER\Software\Mirillis\Action" /v "LicenseConfig" /t reg_binary /d "8b3a8daabd448deb9956bfc241f7c59dca33174ffc44dbc2cab514da87d234b1" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2612 | REG query "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Mirillis Action!" /v InstallLocation | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2956 | "C:\Users\admin\AppData\Local\Temp\loader-x86.exe" | C:\Users\admin\AppData\Local\Temp\loader-x86.exe | — | explorer.exe | |||||||||||
User: admin Company: Mirillis Ltd. Integrity Level: MEDIUM Description: Loader For Mirillis Action! Exit code: 3221226540 Version: 3. 5. 0. 0 Modules
| |||||||||||||||
| 2984 | reg add "HKEY_CURRENT_USER\Software\Mirillis\Action" /v "config" /t reg_binary /d "002ad0511122f3614ad5108c017e3dd4506db559" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3152 | "C:\Users\admin\AppData\Local\Temp\loader-x86.exe" | C:\Users\admin\AppData\Local\Temp\loader-x86.exe | explorer.exe | ||||||||||||
User: admin Company: Mirillis Ltd. Integrity Level: HIGH Description: Loader For Mirillis Action! Exit code: 0 Version: 3. 5. 0. 0 Modules
| |||||||||||||||
| 3360 | reg add "HKEY_CURRENT_USER\Software\Mirillis\Action" /v "LicenseHolder" /t reg_sz /d "RU-BOARD" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3660 | cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\0RWQT7FP.bat" "C:\Users\admin\AppData\Local\Temp\loader-x86.exe" " | C:\Windows\system32\cmd.exe | — | loader-x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3696 | reg add "HKEY_CURRENT_USER\Software\Mirillis\Action\License" /v "License" /t reg_sz /d "G376M48MAU9MHVNRYHZSQGNDCMDX9UJUF9PDQ8PVA7FNQNE3BLEC" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
50
Read events
45
Write events
5
Delete events
0
Modification events
| (PID) Process: | (2596) reg.exe | Key: | HKEY_CURRENT_USER\Software\Mirillis\Action |
| Operation: | write | Name: | LicenseConfig |
Value: 8B3A8DAABD448DEB9956BFC241F7C59DCA33174FFC44DBC2CAB514DA87D234B1 | |||
| (PID) Process: | (2984) reg.exe | Key: | HKEY_CURRENT_USER\Software\Mirillis\Action |
| Operation: | write | Name: | config |
Value: 002AD0511122F3614AD5108C017E3DD4506DB559 | |||
| (PID) Process: | (3360) reg.exe | Key: | HKEY_CURRENT_USER\Software\Mirillis\Action |
| Operation: | write | Name: | LicenseHolder |
Value: RU-BOARD | |||
| (PID) Process: | (3696) reg.exe | Key: | HKEY_CURRENT_USER\Software\Mirillis\Action\License |
| Operation: | write | Name: | License |
Value: G376M48MAU9MHVNRYHZSQGNDCMDX9UJUF9PDQ8PVA7FNQNE3BLEC | |||
| (PID) Process: | (4076) reg.exe | Key: | HKEY_CURRENT_USER\Software\Mirillis\Action |
| Operation: | write | Name: | CheckForUpdates |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | loader-x86.exe | C:\Users\admin\AppData\Local\Temp\0RWQT7FP.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report