| File name: | productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe |
| Full analysis: | https://app.any.run/tasks/3d5fcf13-619f-44fb-87f8-9f6fb6e09d3b |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 20:18:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 43A864F4A0B4723600BE5AA8EDA46937 |
| SHA1: | CB62A60A015F913A27DD59FF465A31341D27A5BD |
| SHA256: | 30B040107C6934062082DB4DD5E5988E6737F45DD00725065CBFB88B849EC05F |
| SSDEEP: | 6144:0bUTp1zjt/oKNM+/87wBeat1RAAx94DqoJqZ0XPRSDJikrHLAPS7EQRMuOBfQcq5:0IDjJB587wBe2Rf4DqoQ+PRSDskrHMBm |
MALICIOUS
Loads dropped or rewritten executable
- productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe (PID: 3448)
- Rundll32.exe (PID: 3456)
SUSPICIOUS
Executable content was dropped or overwritten
- productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe (PID: 3448)
Reads Internet Cache Settings
- productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe (PID: 3448)
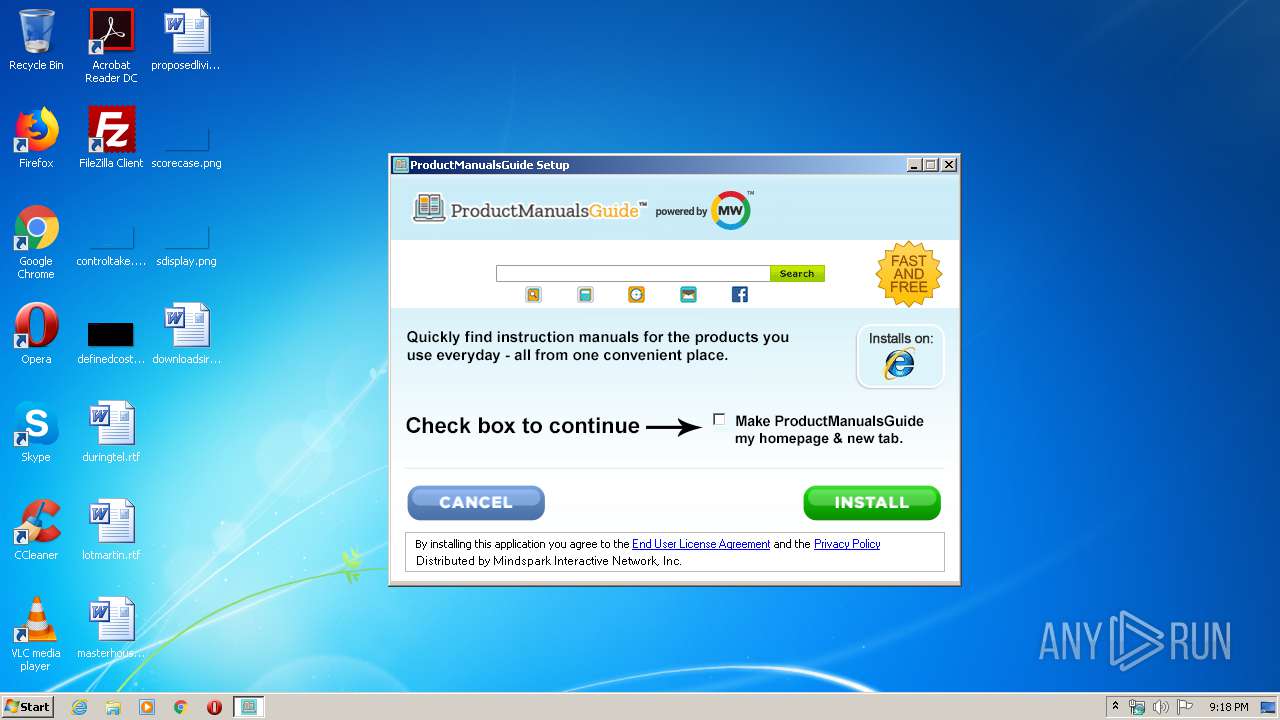
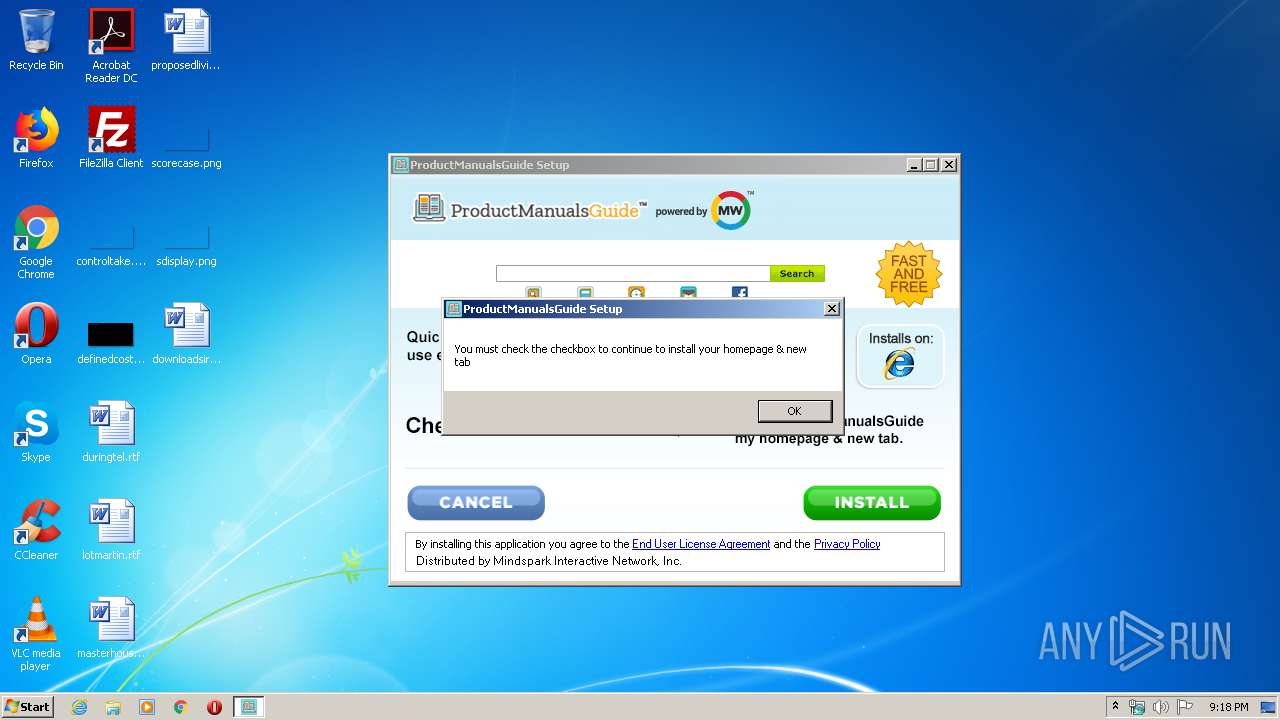
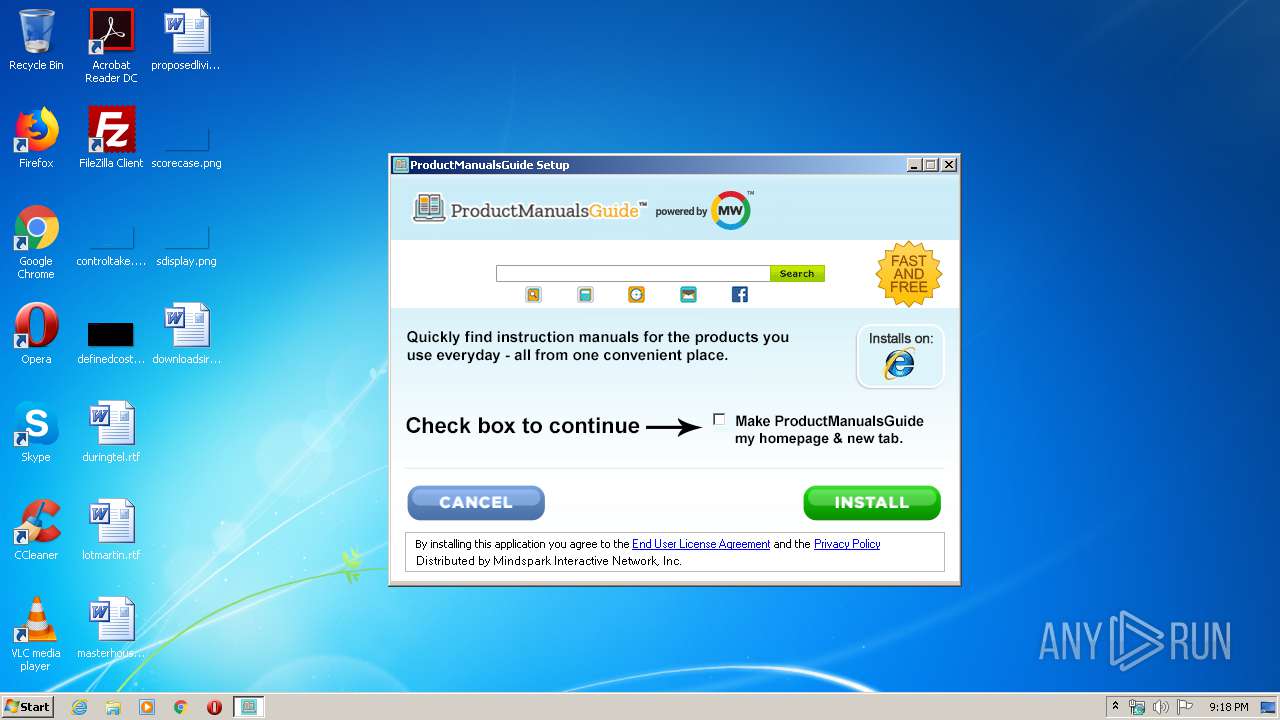
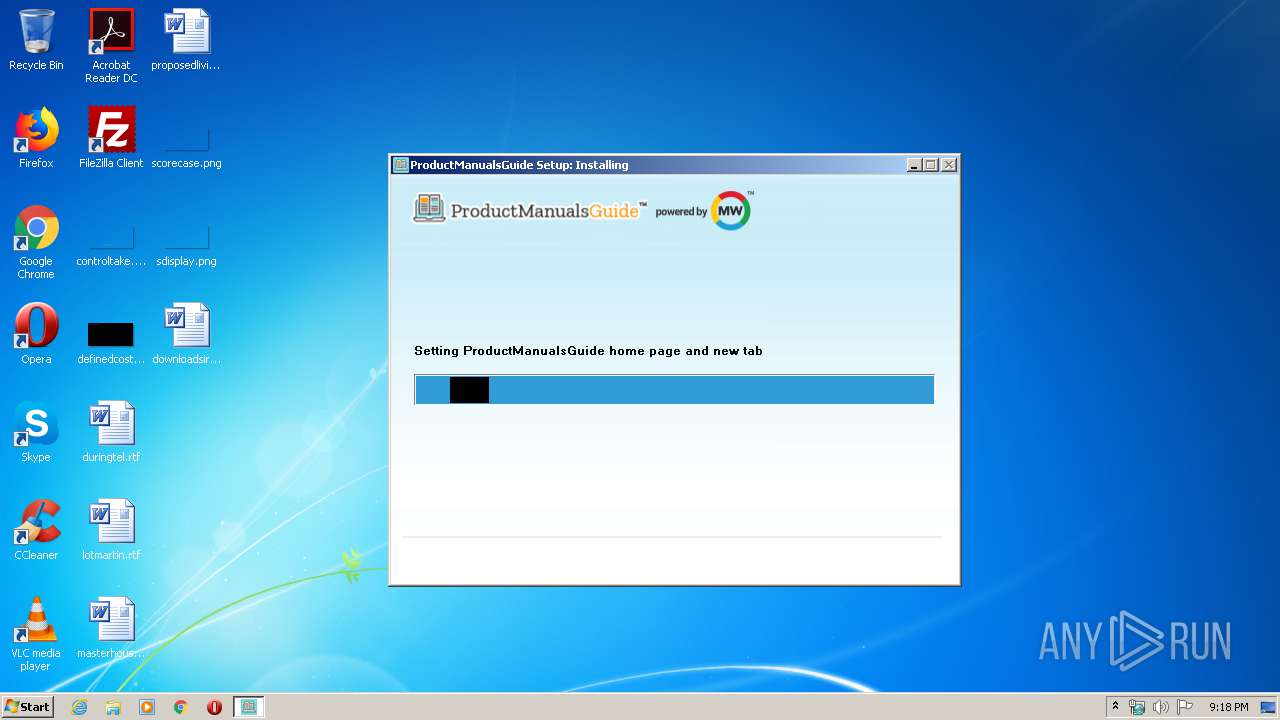
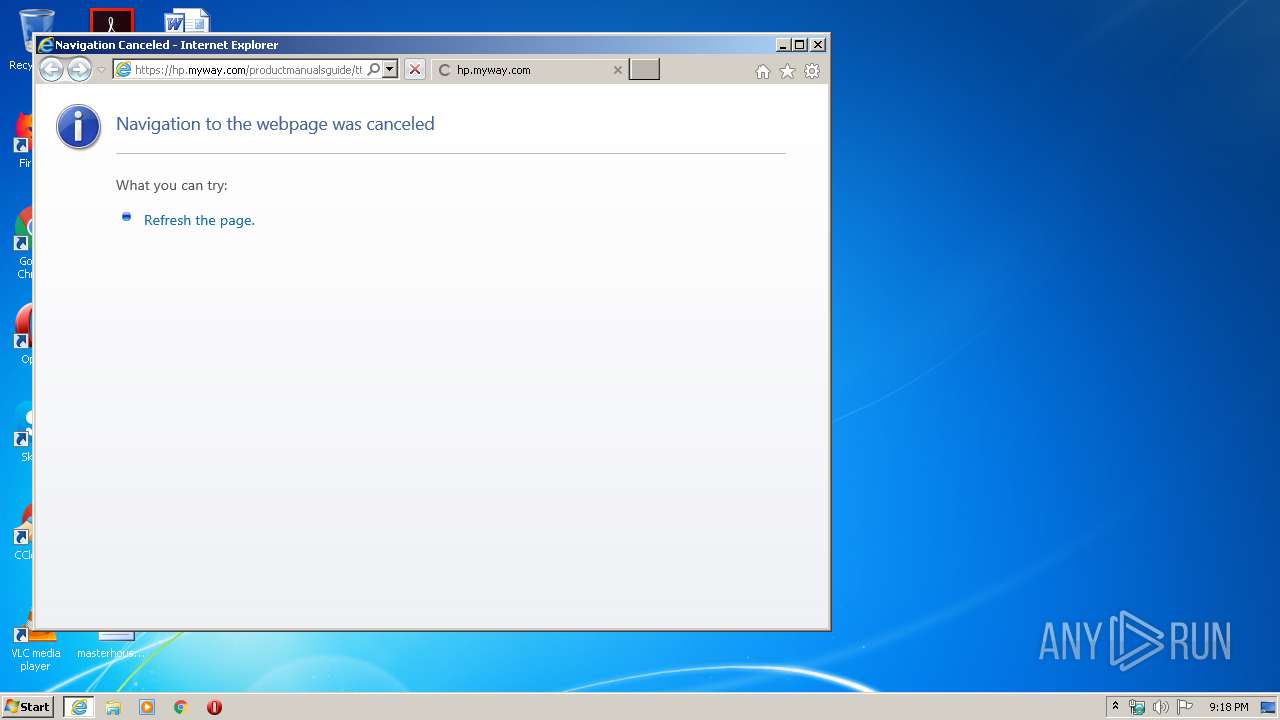
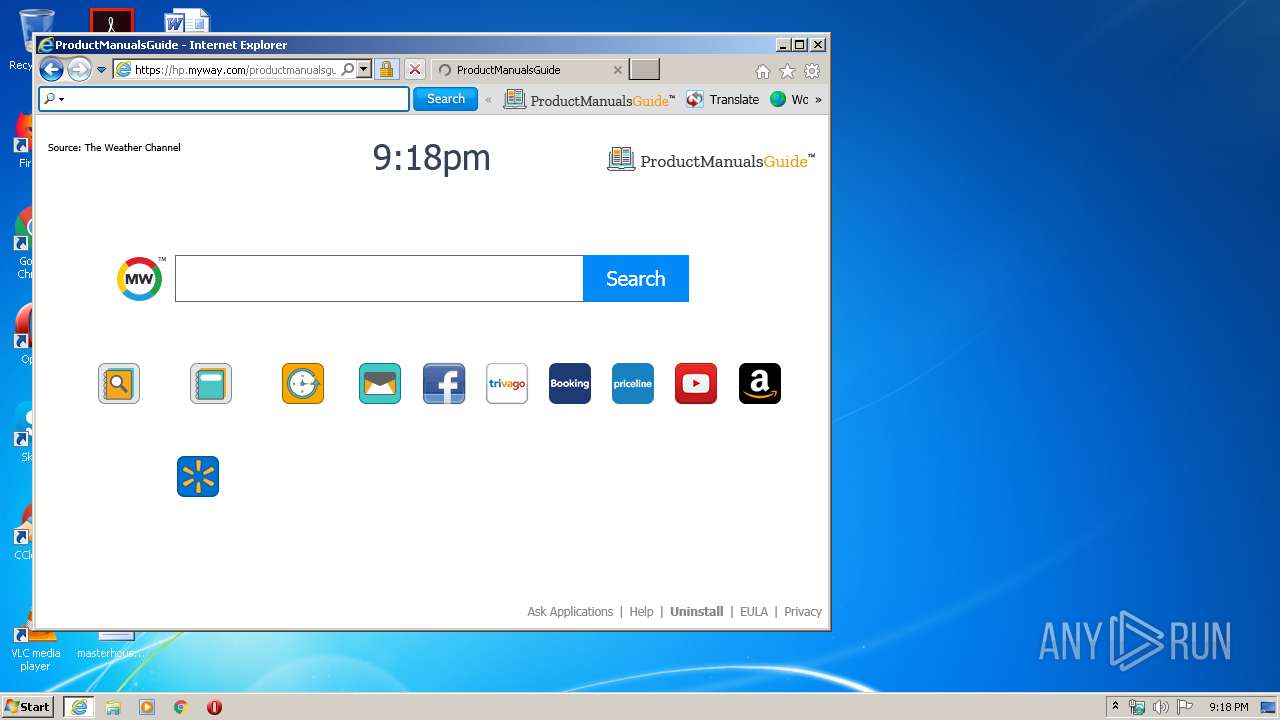
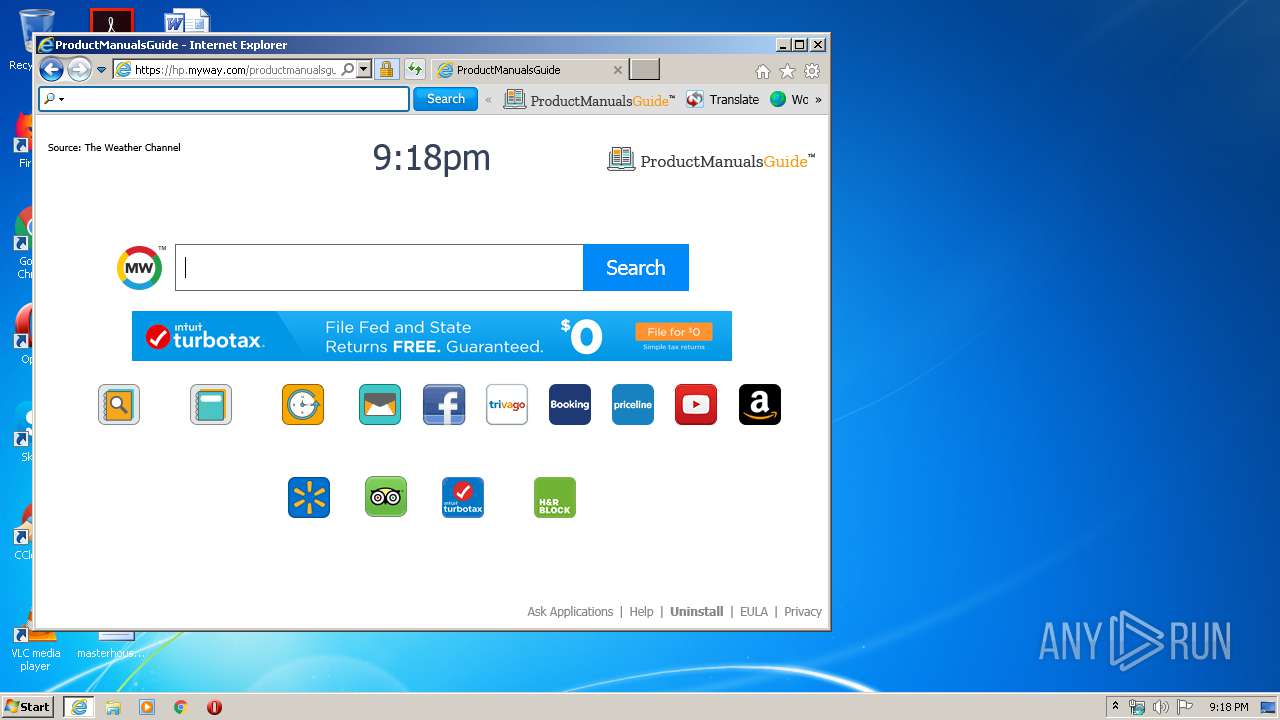
Changes the started page of IE
- productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe (PID: 3448)
Uses RUNDLL32.EXE to load library
- productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe (PID: 3448)
Creates a software uninstall entry
- productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe (PID: 3448)
Executed via COM
- iexplore.exe (PID: 3400)
Creates files in the user directory
- productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe (PID: 3448)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3400)
Reads Internet Cache Settings
- iexplore.exe (PID: 3400)
- iexplore.exe (PID: 4020)
Reads settings of System Certificates
- iexplore.exe (PID: 4020)
- iexplore.exe (PID: 3400)
Creates files in the user directory
- iexplore.exe (PID: 4020)
Reads internet explorer settings
- iexplore.exe (PID: 4020)
Changes settings of System certificates
- iexplore.exe (PID: 3400)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 06:01:44+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.8.1.1000 |
| ProductVersionNumber: | 2.8.1.1000 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | http://www.mindspark.com |
| CompanyName: | Mindspark Interactive Network, Inc. |
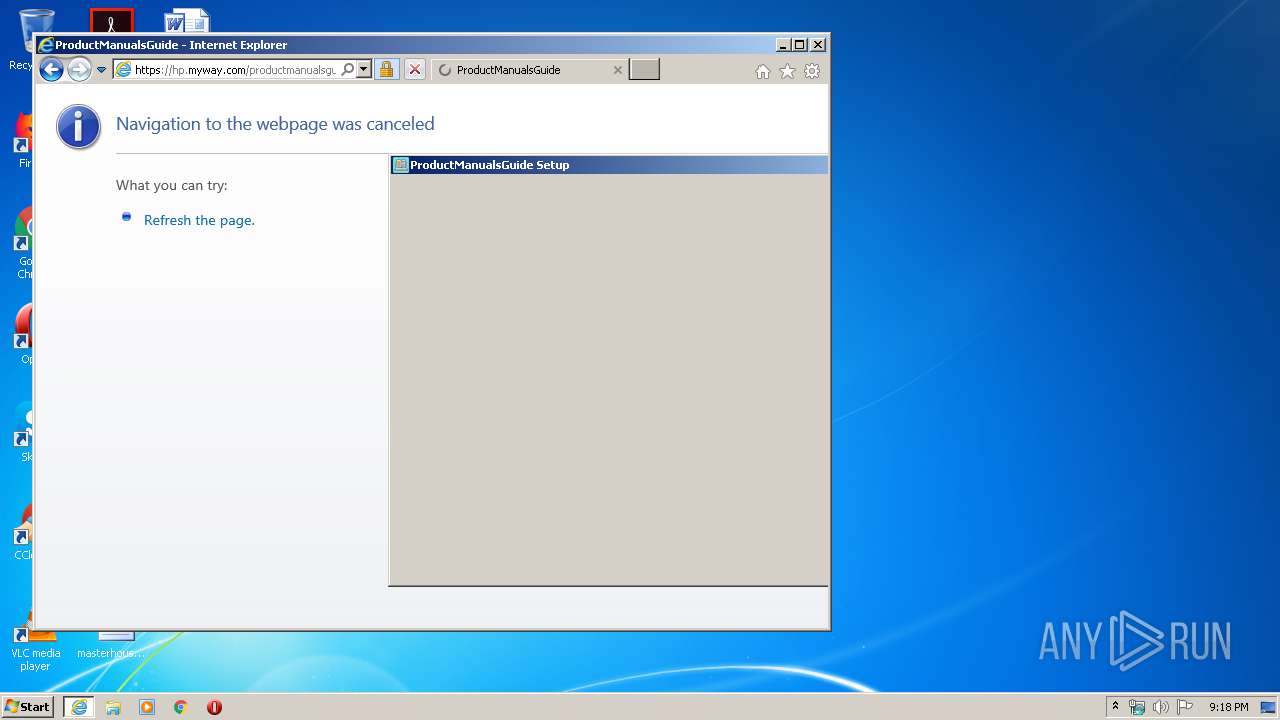
| FileDescription: | ProductManualsGuide Setup |
| FileVersion: | 2.8.1.1000 |
| InternalName: | ProductManualsGuide |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | ProductManualsGuide |
| ProductVersion: | 2.8.1.1000 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Dec-2013 05:01:44 |
| Detected languages: |
|
| Comments: | http://www.mindspark.com |
| CompanyName: | Mindspark Interactive Network, Inc. |
| FileDescription: | ProductManualsGuide Setup |
| FileVersion: | 2.8.1.1000 |
| InternalName: | ProductManualsGuide |
| LegalCopyright: | © 2015 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | ProductManualsGuide |
| ProductVersion: | 2.8.1.1000 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Dec-2013 05:01:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000606C | 0x00006200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45707 |
.rdata | 0x00008000 | 0x00001460 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.94596 |
.data | 0x0000A000 | 0x0002AF98 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79535 |
.ndata | 0x00035000 | 0x00055000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0008A000 | 0x000049F0 | 0x00004A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.66385 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31253 | 1118 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.5441 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.99024 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.27308 | 48 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.89384 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
38
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3400 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\AppData\Local\Temp\productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe" | C:\Users\admin\AppData\Local\Temp\productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | explorer.exe | ||||||||||||
User: admin Company: Mindspark Interactive Network, Inc. Integrity Level: MEDIUM Description: ProductManualsGuide Setup Exit code: 0 Version: 2.8.1.1000 Modules
| |||||||||||||||
| 3456 | "Rundll32.exe" "C:\Users\admin\AppData\Local\ProductManualsGuideTooltab\TooltabExtension.dll",A -hp=https://hp.myway.com/productmanualsguide/ttab02/index.html -ua="(Windows NT 6.1; Win32; MSIE 11.0; Build 7601; SP 1)" -ul=https://anx.mindspark.com/anx.gif?anxa=%251&anxe=%252&anxt=C3496EE8-ED15-4CF6-8F33-49685EAB2FCC&anxtv=2.8.1.1000&anxp=^CQW^mni000^TTAB02&anxsi=&anxv=%253&anxd=2020-03-30&anxr=%254 -hu=SHOW | C:\Windows\system32\Rundll32.exe | — | productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4020 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3400 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
4 117
Read events
675
Write events
2 328
Delete events
1 114
Modification events
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | Start Page |
Value: https://hp.myway.com/productmanualsguide/ttab02/index.html?n=786741FD&p2=^CQW^mni000^TTAB02&ptb=C3496EE8-ED15-4CF6-8F33-49685EAB2FCC&coid=f6fd7f1678944f19864e9b2999e055ce | |||
| (PID) Process: | (3448) productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | Key: | HKEY_CURRENT_USER\Software\ProductManualsGuide |
| Operation: | write | Name: | Start Page |
Value: https://hp.myway.com/productmanualsguide/ttab02/index.html?n=786741FD&p2=^CQW^mni000^TTAB02&ptb=C3496EE8-ED15-4CF6-8F33-49685EAB2FCC&coid=f6fd7f1678944f19864e9b2999e055ce | |||
Executable files
3
Suspicious files
26
Text files
100
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabF8FE.tmp | — | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarF8FF.tmp | — | |
MD5:— | SHA256:— | |||
| 3448 | productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | C:\Users\admin\AppData\Local\Temp\nsp6C9E.tmp\ProductManualsGuide-02_1501261247266.bmp | image | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:— | SHA256:— | |||
| 3448 | productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | C:\Users\admin\AppData\Local\Temp\nsp6C9E.tmp\ProductManualsGuide-01_1501261256538.bmp | image | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | binary | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\errorPageStrings[1] | text | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\index[1].htm | html | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:— | SHA256:— | |||
| 3448 | productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | C:\Users\admin\AppData\Local\Temp\nsp6C9E.tmp\reporting | image | |
MD5:AD4B0F606E0F8465BC4C4C170B37E1A3 | SHA256:CF4724B2F736ED1A0AE6BC28F1EAD963D9CD2C1FD87B6EF32E7799FC1C5C8BDA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
33
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4020 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 2.16.186.11:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | unknown | der | 1.37 Kb | whitelisted |
4020 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJ13zfQMBhkWtuM%3D | US | der | 468 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgMTpiZKu5ZPjufHzmOwcG0K9w%3D%3D | unknown | der | 527 b | whitelisted |
3448 | productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgMX%2Fe0p2X%2FGrZv50DSIlQkDlA%3D%3D | unknown | der | 527 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1d2/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBT4YwNSyUnwC88de5a5l4eUO%2BLQewQUsd0yXei3N3LSzlzOJv5HeeIBCOkCEQD9THeEVm6ehgoAAAAAGFjU | US | der | 472 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJ13zfQMBhkWtuM%3D | US | der | 468 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDy4NKedukSQwgAAAAAMgpY | US | der | 472 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 2.16.186.27:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgMTpiZKu5ZPjufHzmOwcG0K9w%3D%3D | unknown | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3448 | productmanualsguide.f6fd7f1678944f19864e9b2999e055ce.exe | 35.244.218.203:443 | dp.tb.ask.com | — | US | whitelisted |
4020 | iexplore.exe | 104.96.145.33:443 | hp.myway.com | Akamai Technologies, Inc. | NL | unknown |
4020 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4020 | iexplore.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4020 | iexplore.exe | 172.217.21.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
4020 | iexplore.exe | 35.227.202.20:443 | weatherblink.wdgserv.com | — | US | unknown |
4020 | iexplore.exe | 2.16.186.11:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | whitelisted |
4020 | iexplore.exe | 34.102.222.207:443 | anx.mindspark.com | — | US | malicious |
3400 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4020 | iexplore.exe | 2.16.186.27:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
anx.mindspark.com |
| whitelisted |
dns.msftncsi.com |
| shared |
dp.tb.ask.com |
| whitelisted |
hp.myway.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ak.staticimgfarm.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
weatherblink.wdgserv.com |
| unknown |
api.bing.com |
| whitelisted |