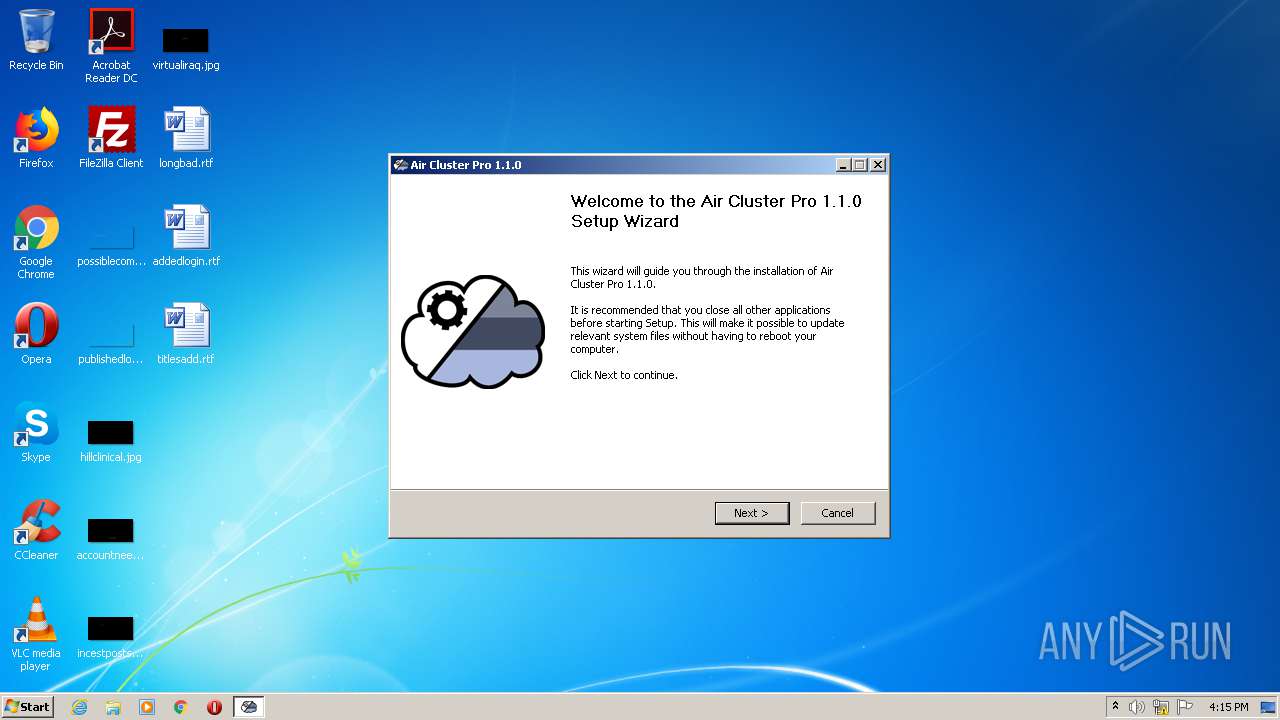
| File name: | Air.Cluster.Pro-1.1.0.exe |
| Full analysis: | https://app.any.run/tasks/ef29c07a-947e-4022-b7b3-9e666ab2517d |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2020, 16:15:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 00E0AA175707CB283B9F62450D8C6291 |
| SHA1: | 4FF2F52CCBA42CD54D1A4ABC97DF3F90CE1FB2B9 |
| SHA256: | 30AF5B18DB49878CF6402669CD67D6BD7C96DE4A23A65D45DDDBDCB6FE3A3F1E |
| SSDEEP: | 49152:iBeeEuqYhs2laMyfmLQt6IMljghvNC0gs6opkJrBD9RzPsvTOsga++:sefPYhnlax6QtDhvojsiJHPQ |
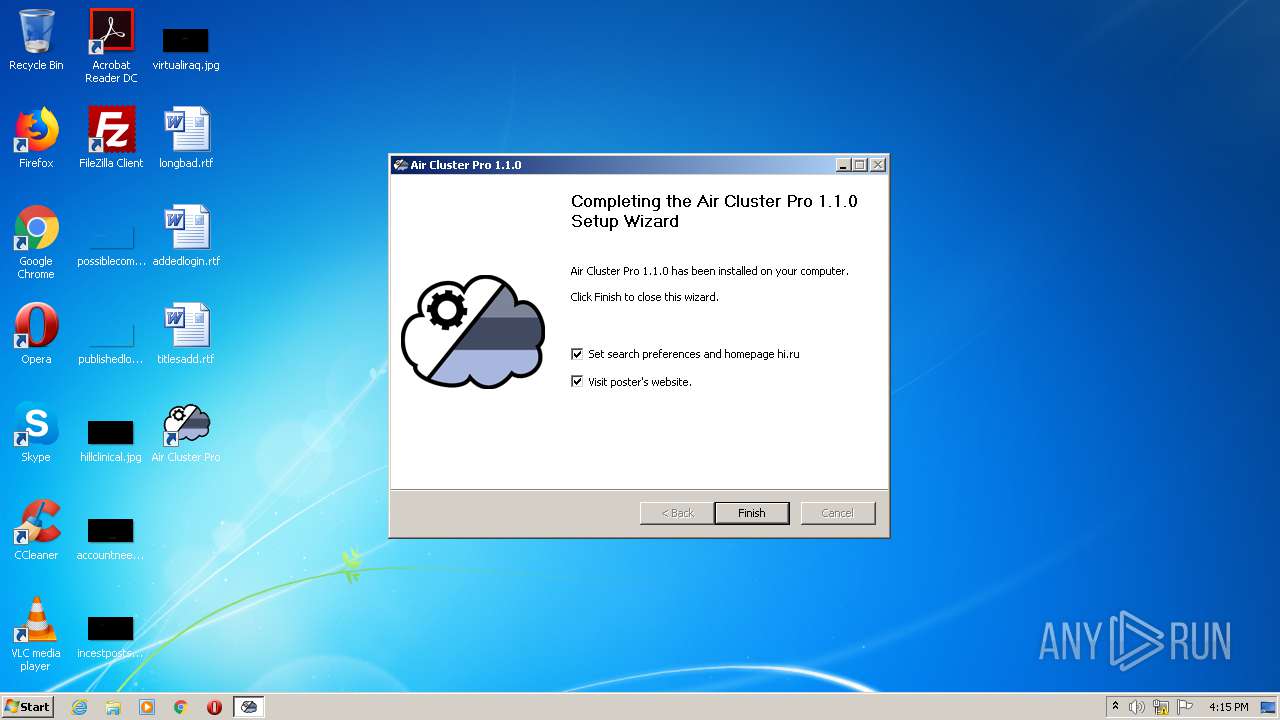
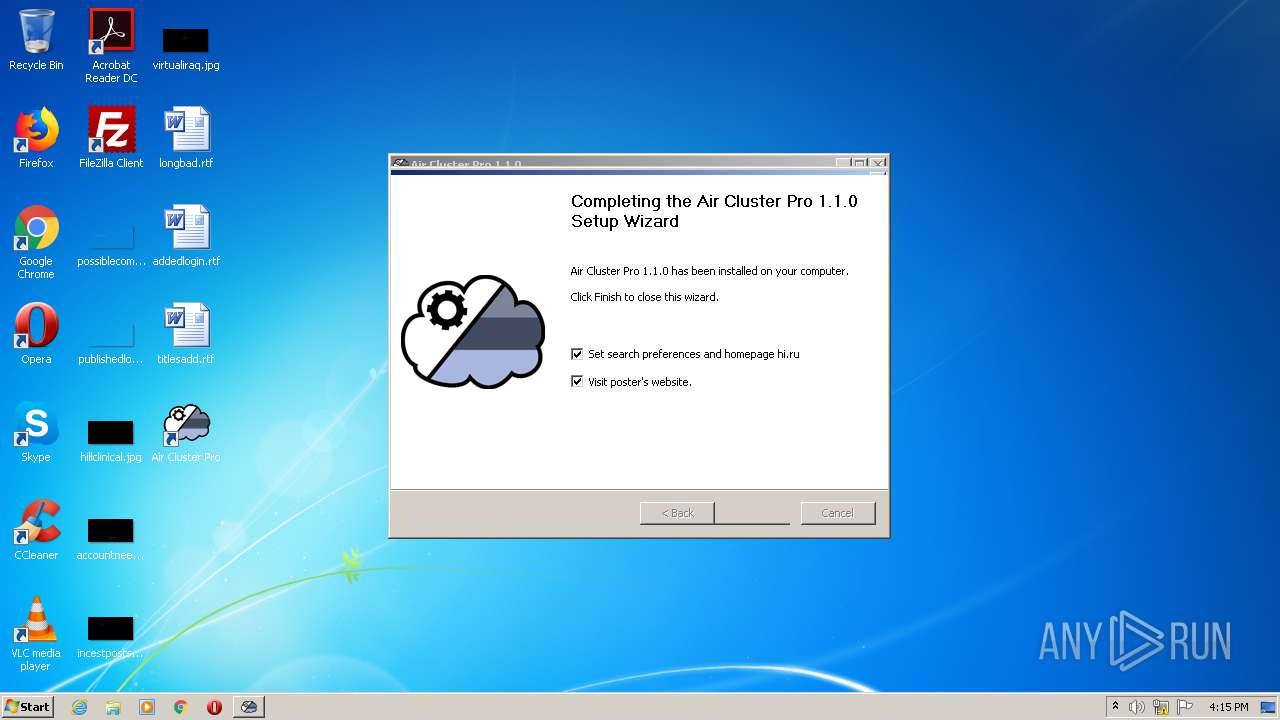
MALICIOUS
Drops executable file immediately after starts
- Air.Cluster.Pro-1.1.0.exe (PID: 3084)
- packeg.exe (PID: 4028)
- install.exe (PID: 2752)
Loads dropped or rewritten executable
- Air.Cluster.Pro-1.1.0.exe (PID: 3084)
- install.exe (PID: 2752)
Application was dropped or rewritten from another process
- packeg.exe (PID: 4028)
- install.exe (PID: 2752)
Actions looks like stealing of personal data
- install.exe (PID: 2752)
SUSPICIOUS
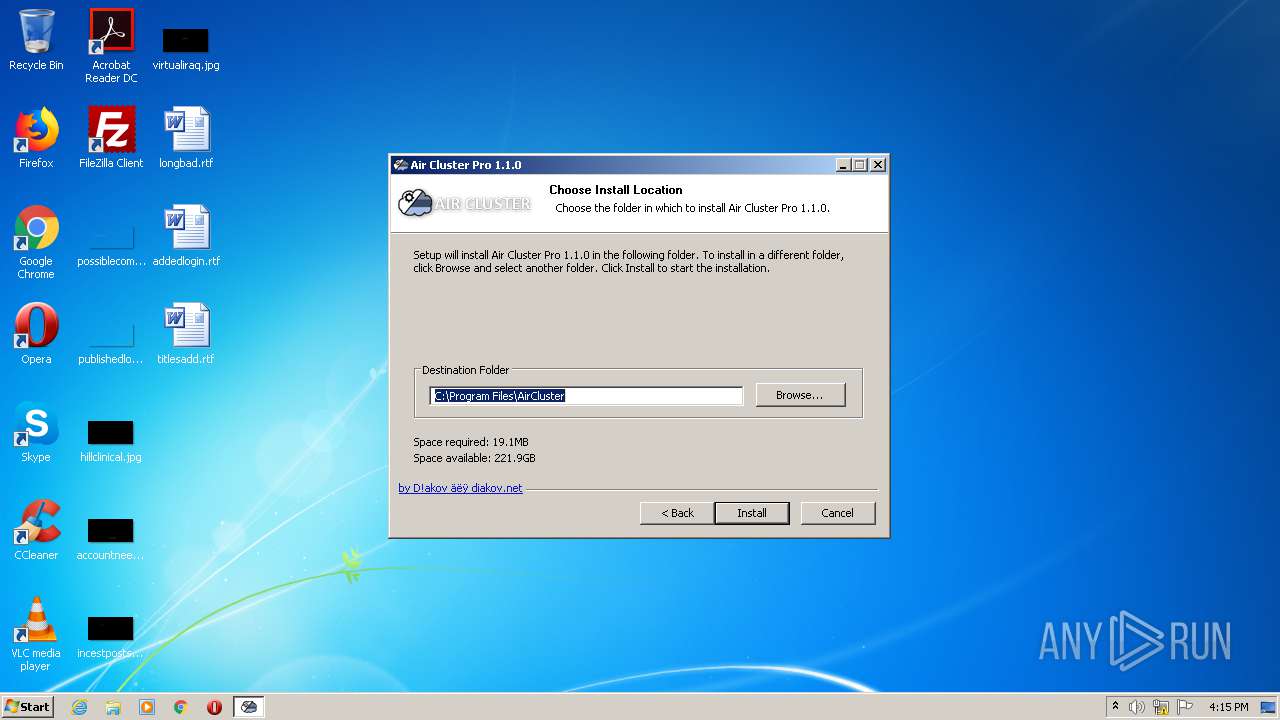
Creates a software uninstall entry
- Air.Cluster.Pro-1.1.0.exe (PID: 3084)
- install.exe (PID: 2752)
Creates a directory in Program Files
- Air.Cluster.Pro-1.1.0.exe (PID: 3084)
- install.exe (PID: 2752)
Executable content was dropped or overwritten
- packeg.exe (PID: 4028)
- install.exe (PID: 2752)
- Air.Cluster.Pro-1.1.0.exe (PID: 3084)
Creates files in the program directory
- install.exe (PID: 2752)
- Air.Cluster.Pro-1.1.0.exe (PID: 3084)
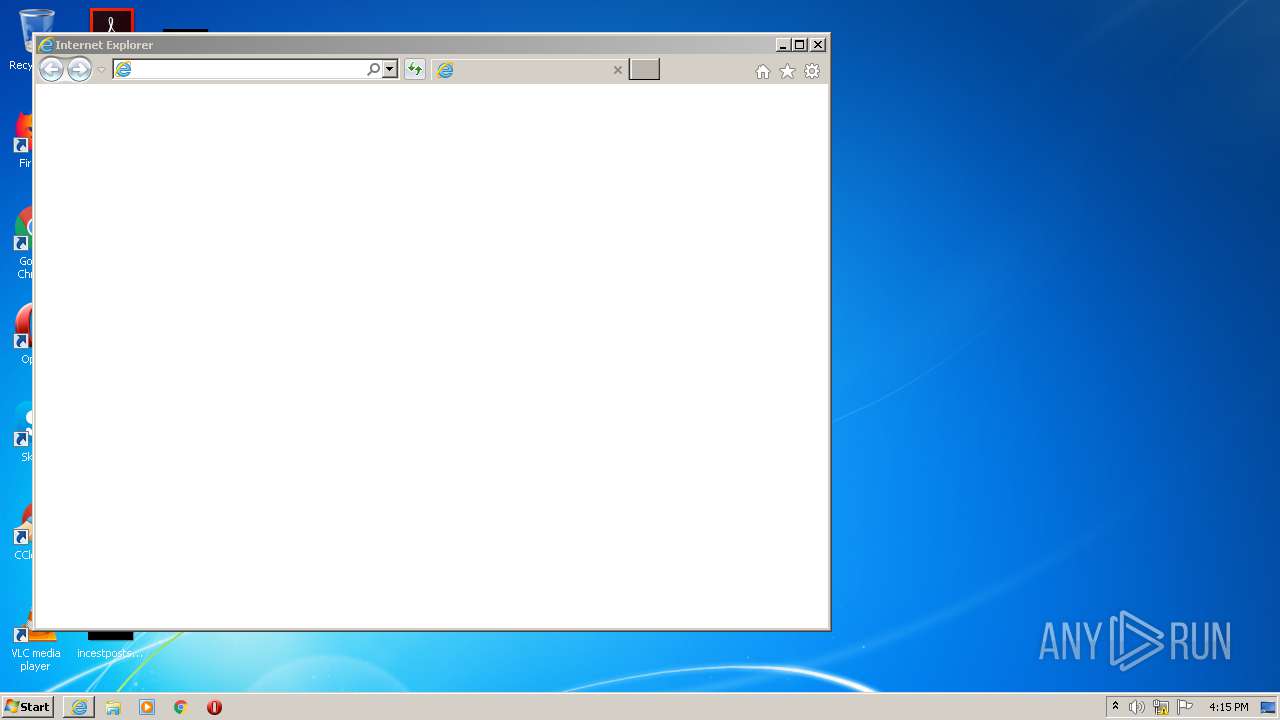
Starts Internet Explorer
- Air.Cluster.Pro-1.1.0.exe (PID: 3084)
Drops a file that was compiled in debug mode
- Air.Cluster.Pro-1.1.0.exe (PID: 3084)
Drops a file with too old compile date
- Air.Cluster.Pro-1.1.0.exe (PID: 3084)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3564)
Reads settings of System Certificates
- iexplore.exe (PID: 2560)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2560)
Creates files in the user directory
- iexplore.exe (PID: 2560)
Changes settings of System certificates
- iexplore.exe (PID: 2560)
Application launched itself
- iexplore.exe (PID: 3564)
Reads internet explorer settings
- iexplore.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.0 |
| ProductVersionNumber: | 1.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Windows, Cyrillic |
| CompanyName: | diakov.net |
| FileDescription: | Air Cluster Pro 1.1.0 |
| FileVersion: | 1.1.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| CompanyName: | diakov.net |
| FileDescription: | Air Cluster Pro 1.1.0 |
| FileVersion: | 1.1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x00016000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x0000F098 | 0x0000F200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.69142 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.38789 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 3.526 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 3.96507 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 3.2609 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 2.8744 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
43
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2560 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3564 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2752 | C:\Users\admin\AppData\Local\Temp\temp\install.exe /S | C:\Users\admin\AppData\Local\Temp\temp\install.exe | Air.Cluster.Pro-1.1.0.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2784 | "C:\Users\admin\AppData\Local\Temp\Air.Cluster.Pro-1.1.0.exe" | C:\Users\admin\AppData\Local\Temp\Air.Cluster.Pro-1.1.0.exe | — | explorer.exe | |||||||||||
User: admin Company: diakov.net Integrity Level: MEDIUM Description: Air Cluster Pro 1.1.0 Exit code: 3221226540 Version: 1.1.0.0 Modules
| |||||||||||||||
| 3084 | "C:\Users\admin\AppData\Local\Temp\Air.Cluster.Pro-1.1.0.exe" | C:\Users\admin\AppData\Local\Temp\Air.Cluster.Pro-1.1.0.exe | explorer.exe | ||||||||||||
User: admin Company: diakov.net Integrity Level: HIGH Description: Air Cluster Pro 1.1.0 Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 3564 | "C:\Program Files\Internet Explorer\iexplore.exe" https://diakov.net/ | C:\Program Files\Internet Explorer\iexplore.exe | Air.Cluster.Pro-1.1.0.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4028 | C:\Users\admin\AppData\Local\Temp\temp\packeg.exe -gm2 -y -pdiakov1 | C:\Users\admin\AppData\Local\Temp\temp\packeg.exe | Air.Cluster.Pro-1.1.0.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z SFX Exit code: 0 Version: 19.00 Modules
| |||||||||||||||
Total events
1 311
Read events
1 192
Write events
119
Delete events
0
Modification events
| (PID) Process: | (3084) Air.Cluster.Pro-1.1.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Air Cluster Pro 1.1.0 |
| Operation: | write | Name: | DisplayName |
Value: Air Cluster Pro | |||
| (PID) Process: | (3084) Air.Cluster.Pro-1.1.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Air Cluster Pro 1.1.0 |
| Operation: | write | Name: | UninstallPath |
Value: C:\Program Files\AirCluster | |||
| (PID) Process: | (3084) Air.Cluster.Pro-1.1.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Air Cluster Pro 1.1.0 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\AirCluster\Óäàëèòü Air Cluster Pro.exe | |||
| (PID) Process: | (3084) Air.Cluster.Pro-1.1.0.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Air Cluster Pro 1.1.0 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\AirCluster\AirCluster.exe | |||
| (PID) Process: | (2752) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Chrome\Extensions\imhlianhlhdicjchlbmbfaefhhjencbe |
| Operation: | write | Name: | version |
Value: 0.4 | |||
| (PID) Process: | (2752) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Chrome\Extensions\imhlianhlhdicjchlbmbfaefhhjencbe |
| Operation: | write | Name: | update_url |
Value: https://clients2.google.com/service/update2/crx | |||
| (PID) Process: | (2752) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Chrome\Extensions\imhlianhlhdicjchlbmbfaefhhjencbe |
| Operation: | write | Name: | version |
Value: 0.4 | |||
| (PID) Process: | (2752) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Chrome\Extensions\imhlianhlhdicjchlbmbfaefhhjencbe |
| Operation: | write | Name: | update_url |
Value: https://clients2.google.com/service/update2/crx | |||
| (PID) Process: | (2752) install.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2752) install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\HStar |
| Operation: | write | Name: | DisplayName |
Value: StartHi uninstall | |||
Executable files
31
Suspicious files
28
Text files
139
Unknown types
25
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Program Files\AirCluster\AirCluster.exe | executable | |
MD5:— | SHA256:— | |||
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsg30B0.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsg30B0.tmp\nsis-r.bmp | image | |
MD5:— | SHA256:— | |||
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsg30B0.tmp\nsDialogs.dll | executable | |
MD5:C10E04DD4AD4277D5ADC951BB331C777 | SHA256:E31AD6C6E82E603378CB6B80E67D0E0DCD9CF384E1199AC5A65CB4935680021A | |||
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsg30B0.tmp\orange-r.bmp | image | |
MD5:— | SHA256:— | |||
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsg30B0.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsg30B0.tmp\Aero.dll | executable | |
MD5:243BF44688B131C3171F2827A93E39DC | SHA256:04A577DF50431EB0FF6FB103566402BF66C50415BCC1F8A86B9C235053131455 | |||
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Program Files\AirCluster\ControlzEx.dll | executable | |
MD5:9577DA08FB416F6737407F01B48F58C0 | SHA256:03D23B095B0576E695127A56B1DCEAE4B45CDEA8EF6082739B81FA4023C833E3 | |||
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsg30B0.tmp\ToolTips.dll | executable | |
MD5:9A0DA2692764BB842411A8B9687EBBB7 | SHA256:28AEAA48C929188A0D169887CC3F16370741467AE49E1DB59763F030710A6BBB | |||
| 3084 | Air.Cluster.Pro-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\nsg30B0.tmp\BrandingURL.dll | executable | |
MD5:71C46B663BAA92AD941388D082AF97E7 | SHA256:BB2B9C272B8B66BC1B414675C2ACBA7AFAD03FFF66A63BABEE3EE57ED163D19E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
27
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2560 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEHF3toefcUDcL07GDkLSO9I%3D | RU | der | 1.48 Kb | whitelisted |
2560 | iexplore.exe | GET | 200 | 23.55.163.68:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgRlyCOuUH1sx0JRzva1VE3w6Q%3D%3D | US | der | 527 b | whitelisted |
2560 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2560 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCKcuDfDBqJ0QIAAAAAgFWT | US | der | 472 b | whitelisted |
2560 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFcLuT0XSrlKAgAAAACAVZE%3D | US | der | 471 b | whitelisted |
3564 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2560 | iexplore.exe | GET | 200 | 216.58.212.131:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDCM7HfIeUYqwUAAAAAfoxq | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2560 | iexplore.exe | 176.57.71.209:443 | diakov.net | — | — | unknown |
2560 | iexplore.exe | 23.55.163.71:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | US | suspicious |
2560 | iexplore.exe | 172.217.22.66:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2560 | iexplore.exe | 23.55.163.61:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | US | unknown |
2560 | iexplore.exe | 88.212.201.216:443 | counter.yadro.ru | United Network LLC | RU | suspicious |
3564 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2560 | iexplore.exe | 172.217.18.162:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
2560 | iexplore.exe | 5.45.205.244:80 | yandex.ocsp-responder.com | YANDEX LLC | RU | whitelisted |
2560 | iexplore.exe | 23.55.163.68:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | US | suspicious |
2560 | iexplore.exe | 216.58.212.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
diakov.net |
| malicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
an.yandex.ru |
| whitelisted |
counter.yadro.ru |
| whitelisted |