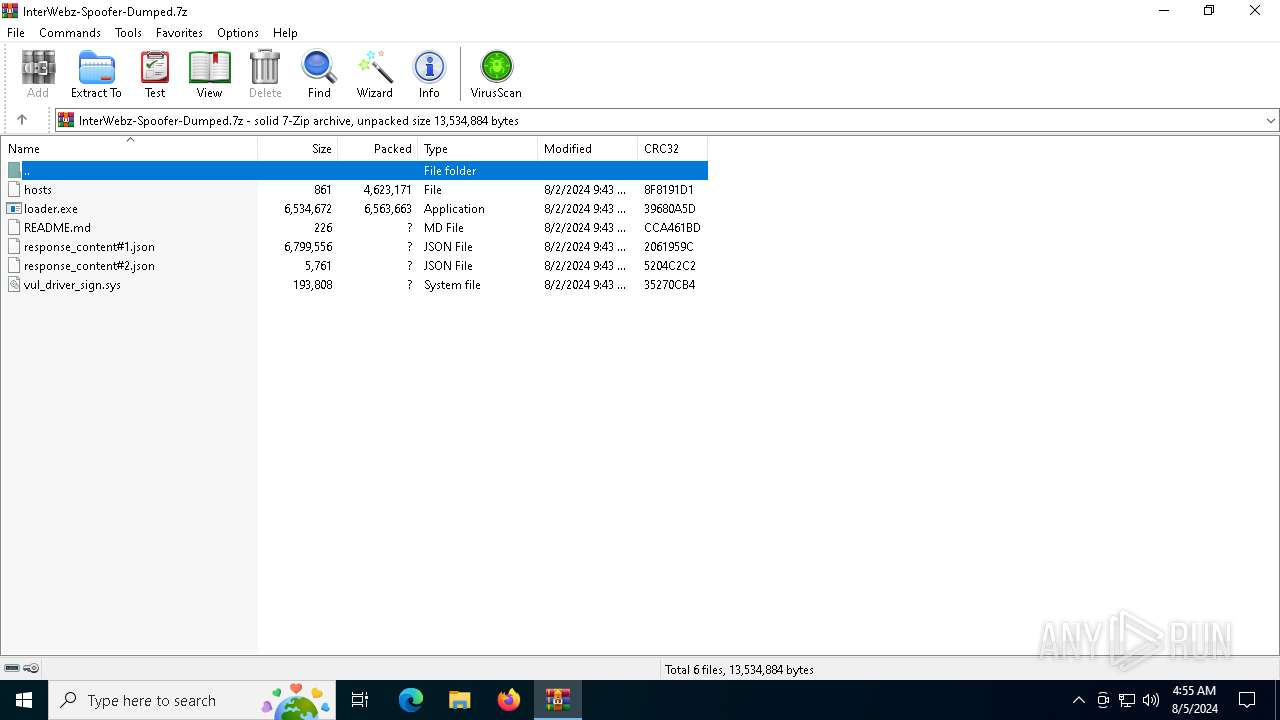
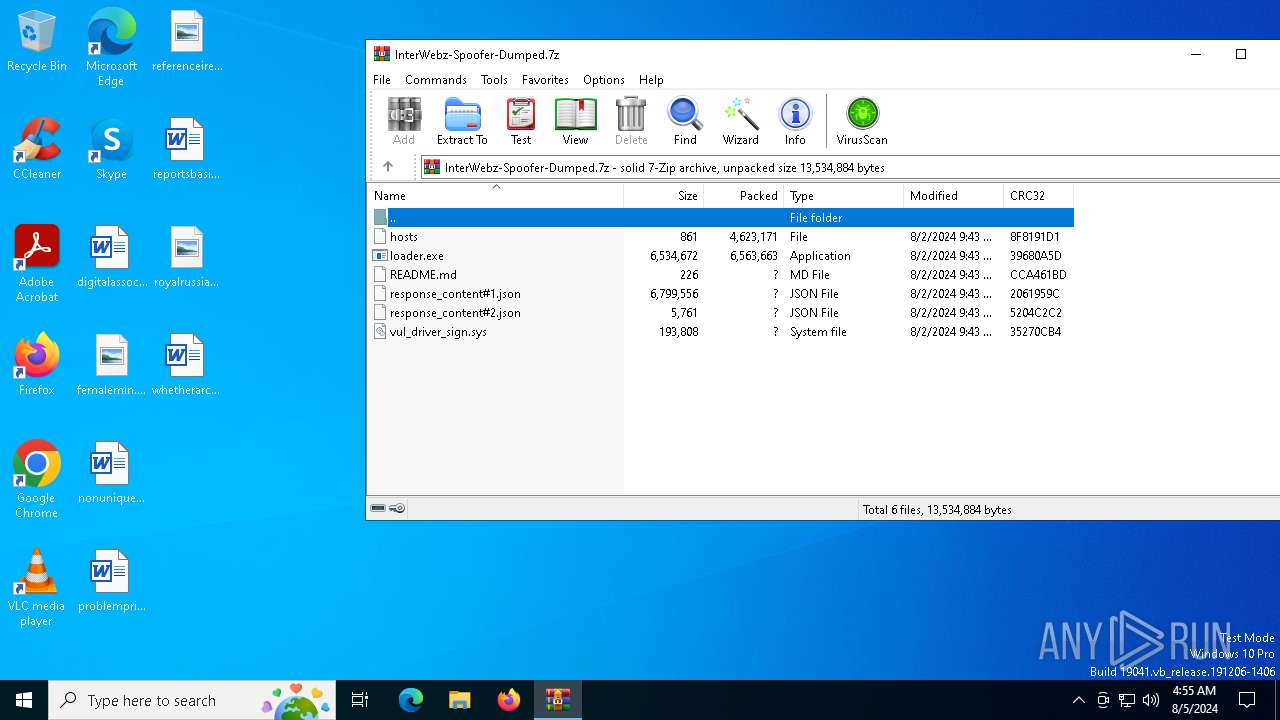
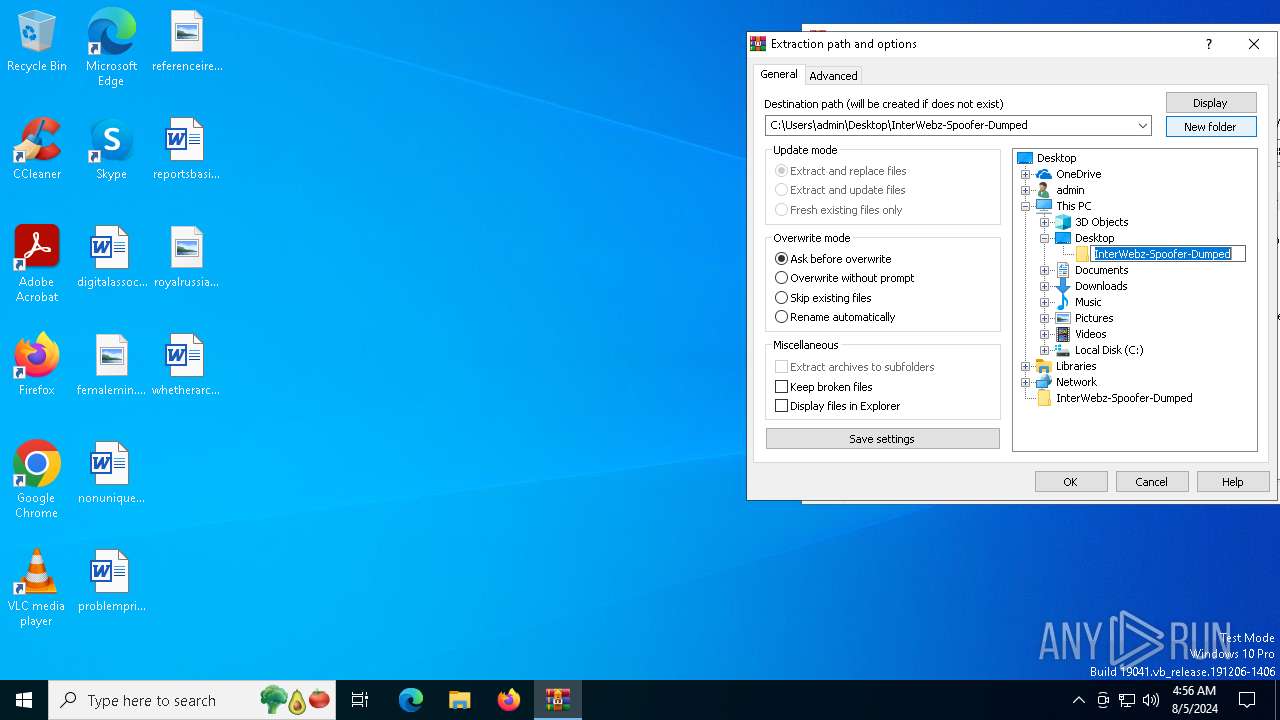
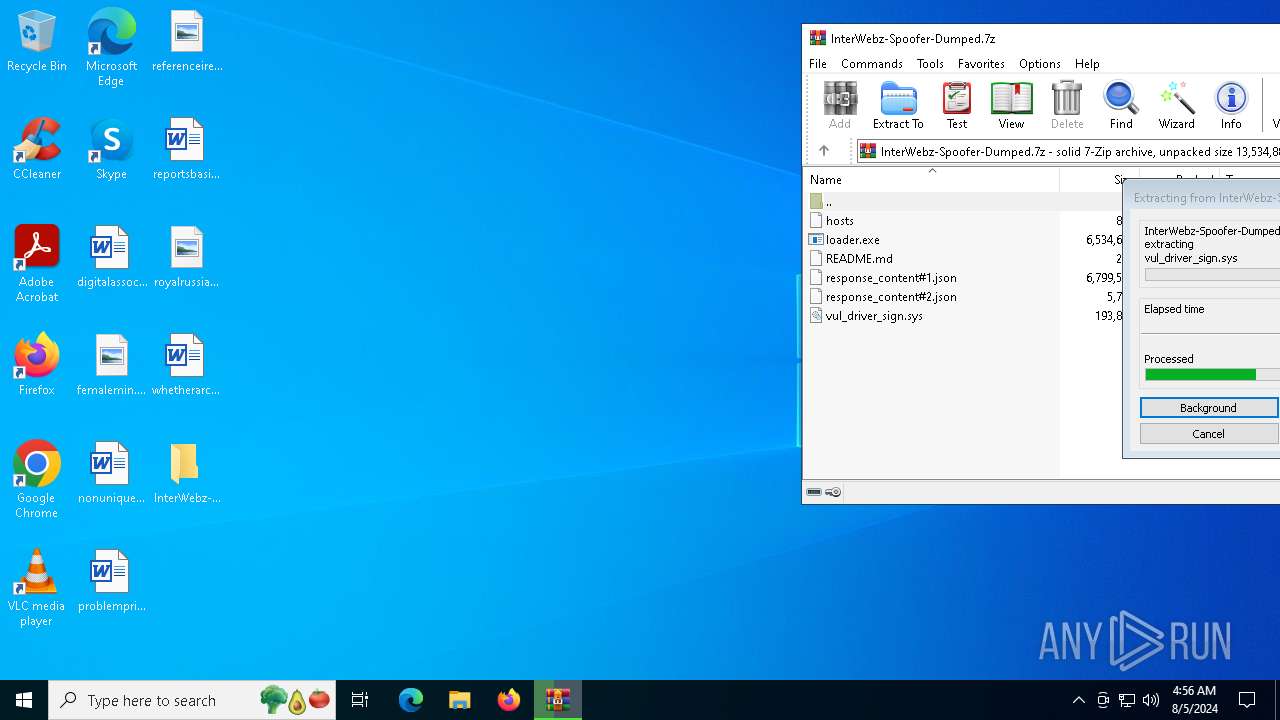
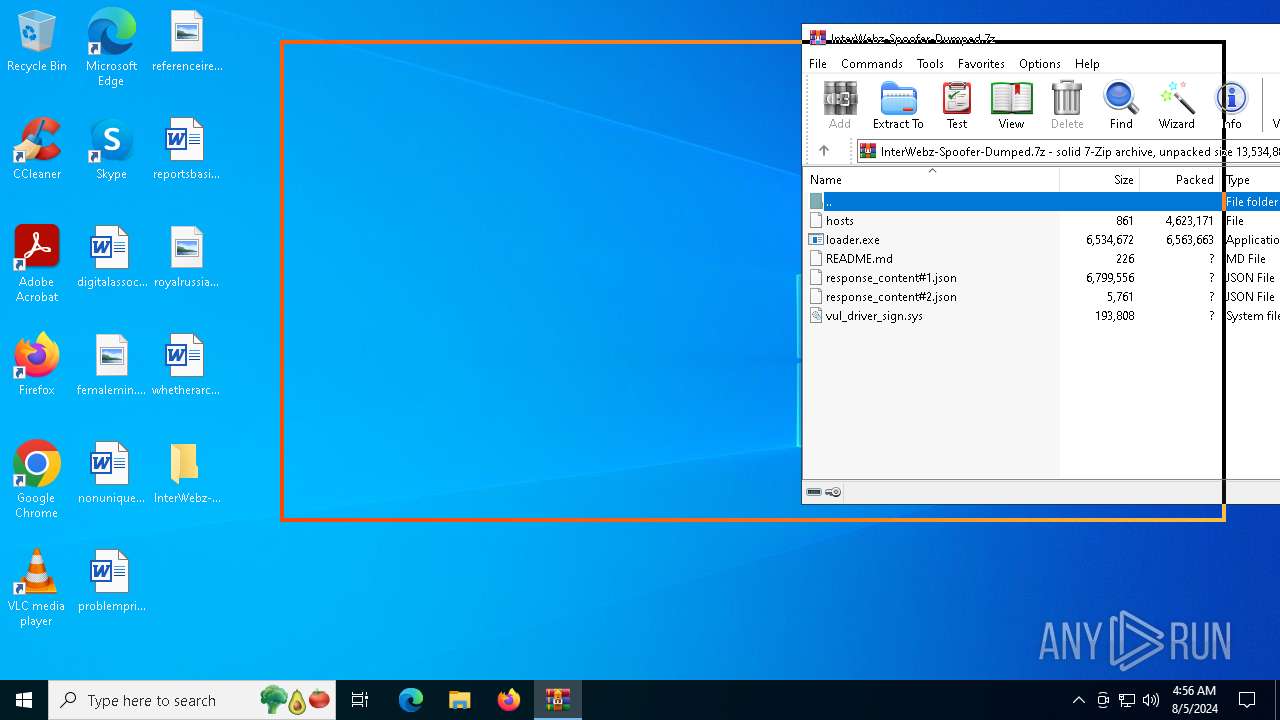
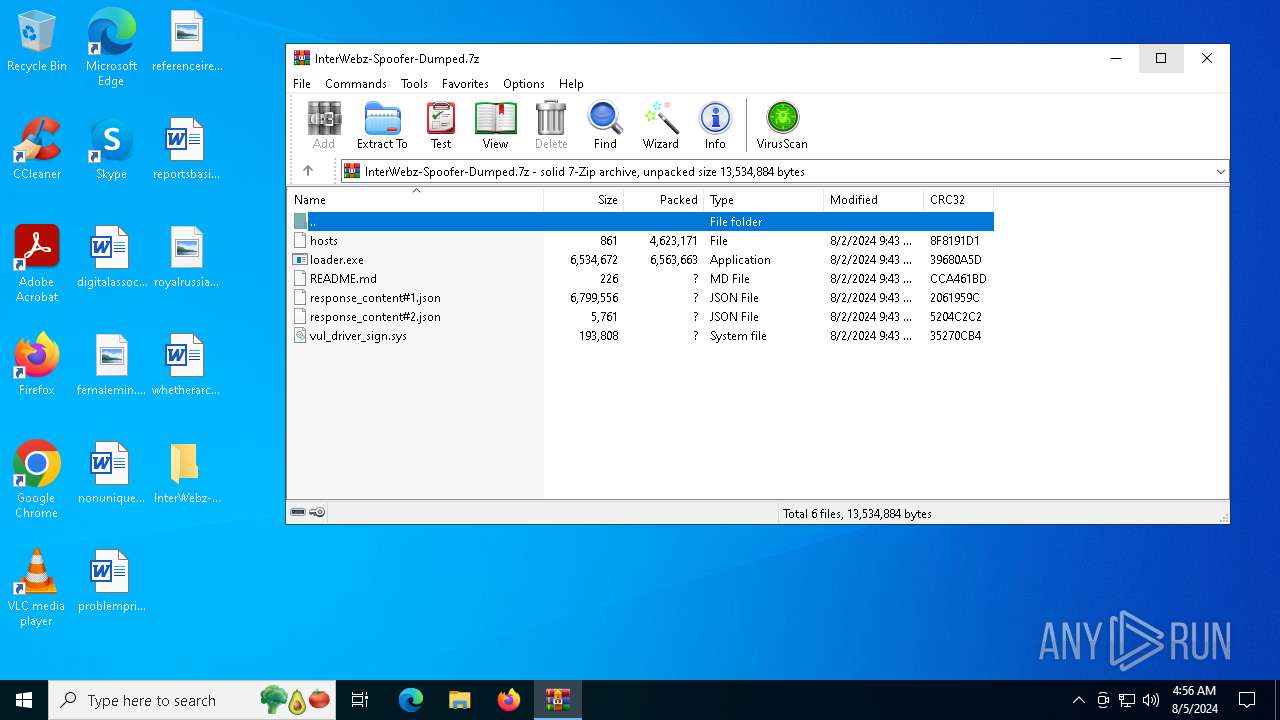
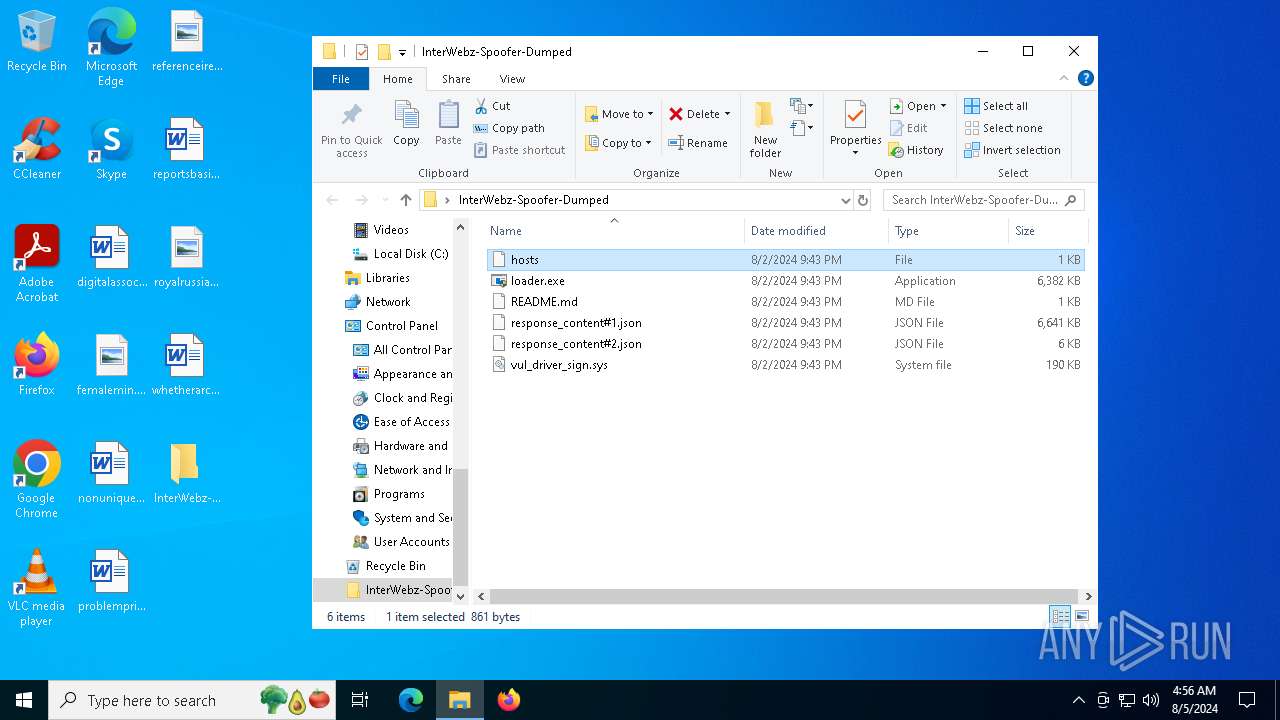
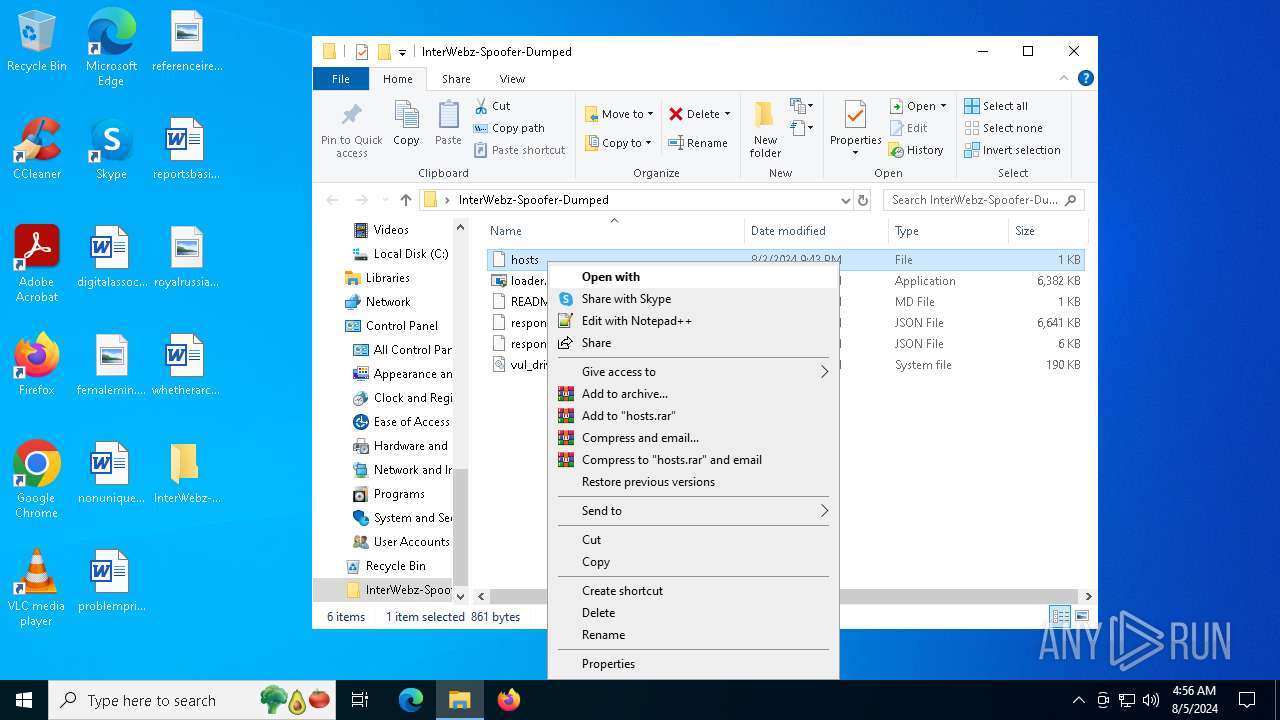
| File name: | InterWebz-Spoofer-Dumped.7z |
| Full analysis: | https://app.any.run/tasks/eaf19a0b-f194-4f33-b4a9-03a794056cdf |
| Verdict: | Malicious activity |
| Analysis date: | August 05, 2024, 04:55:36 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 7A250657E3F1EB1EE7D83A1979FE158C |
| SHA1: | C43C460FBBDD065AADF71720B72E09EC1E91C765 |
| SHA256: | 30ACA83883FC9CE27E8336E781CA44FE3F748E14679F6557BEFF8D5B9C3CD2DA |
| SSDEEP: | 98304:7QPAXx3b9DlrNZ+2mGqykLqF2NzPM+E5daxLbIAG2eWSzwQPLXYu+ltC0+UCsYpX:IMtvi9zaashd/+J2adSyVLU |
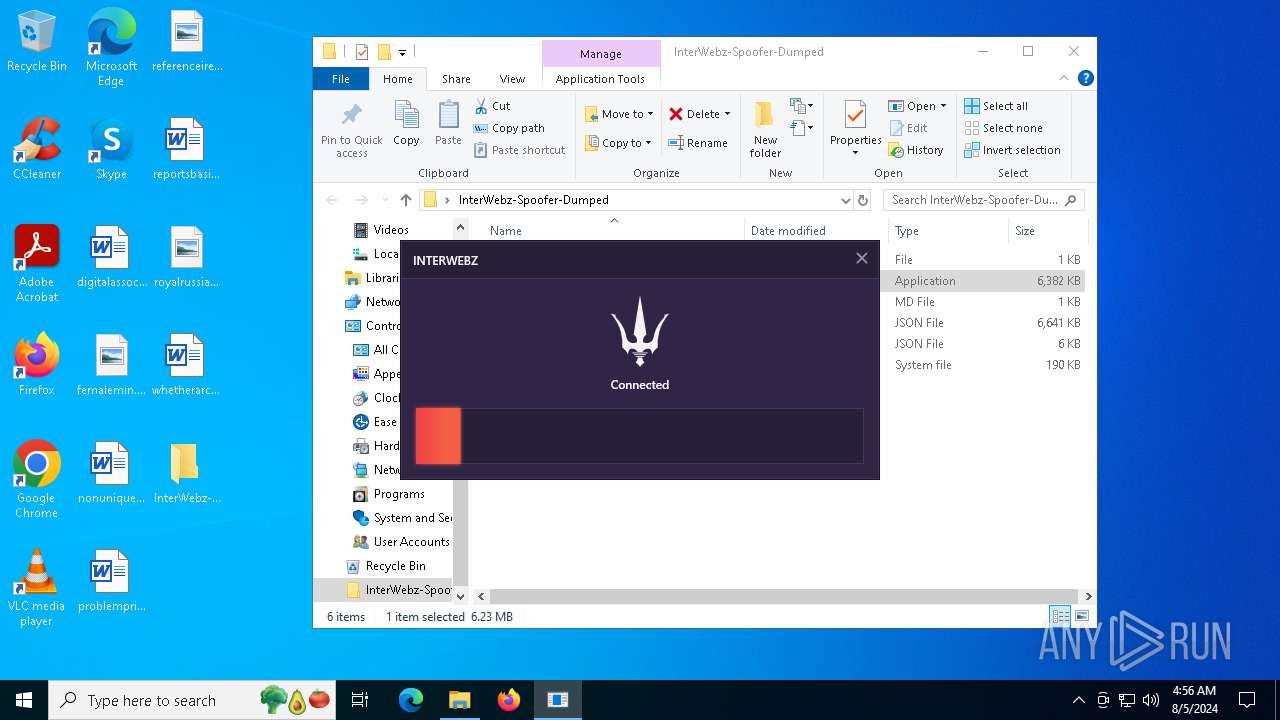
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6484)
SUSPICIOUS
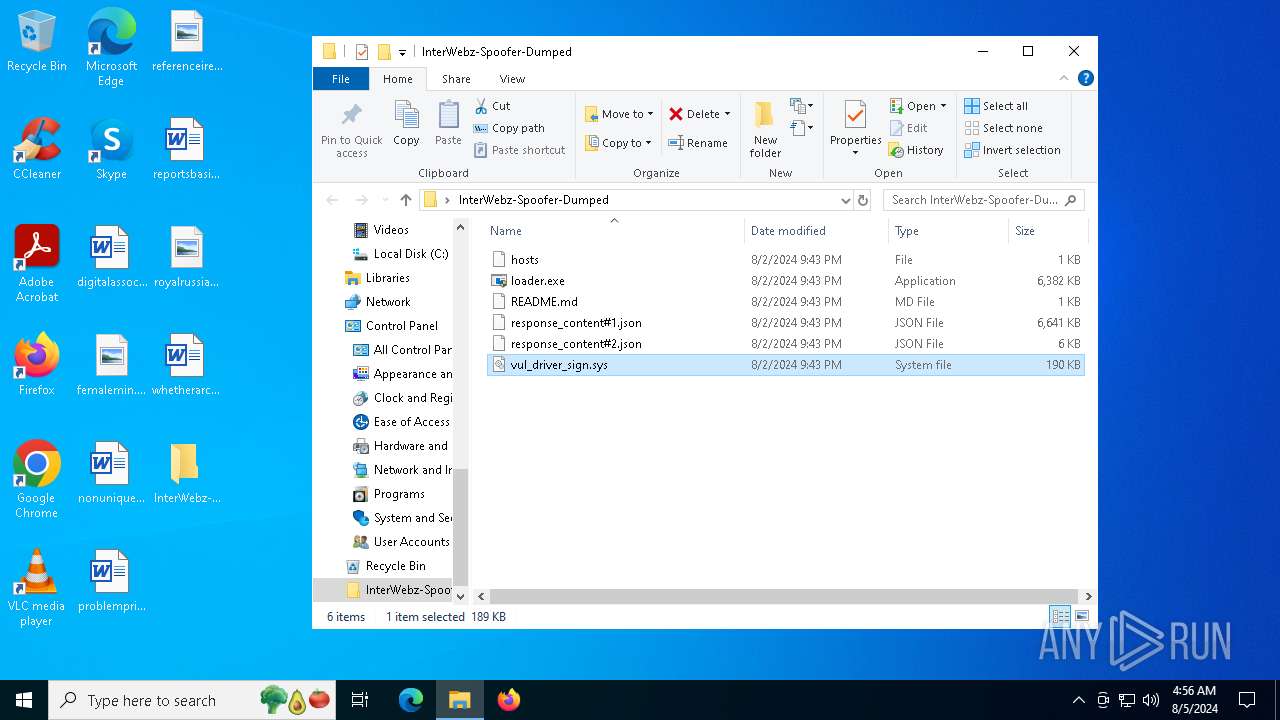
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 6484)
Reads the BIOS version
- loader.exe (PID: 5916)
- loader.exe (PID: 5372)
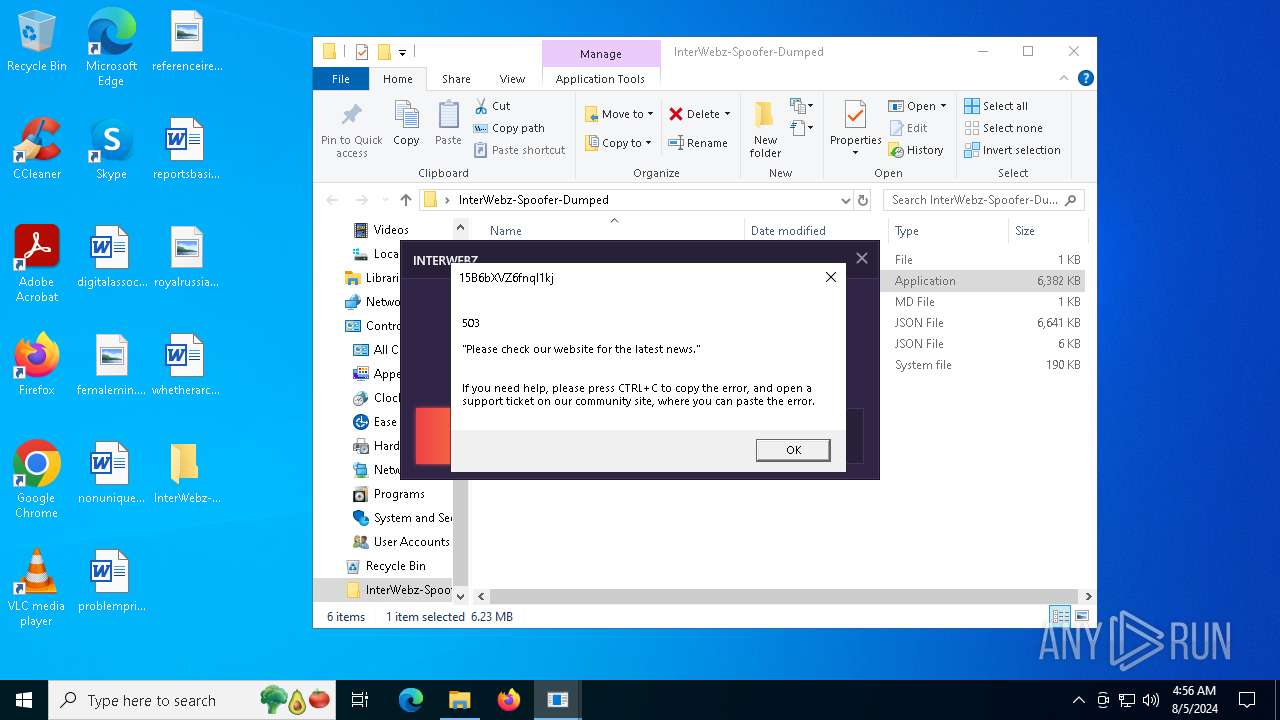
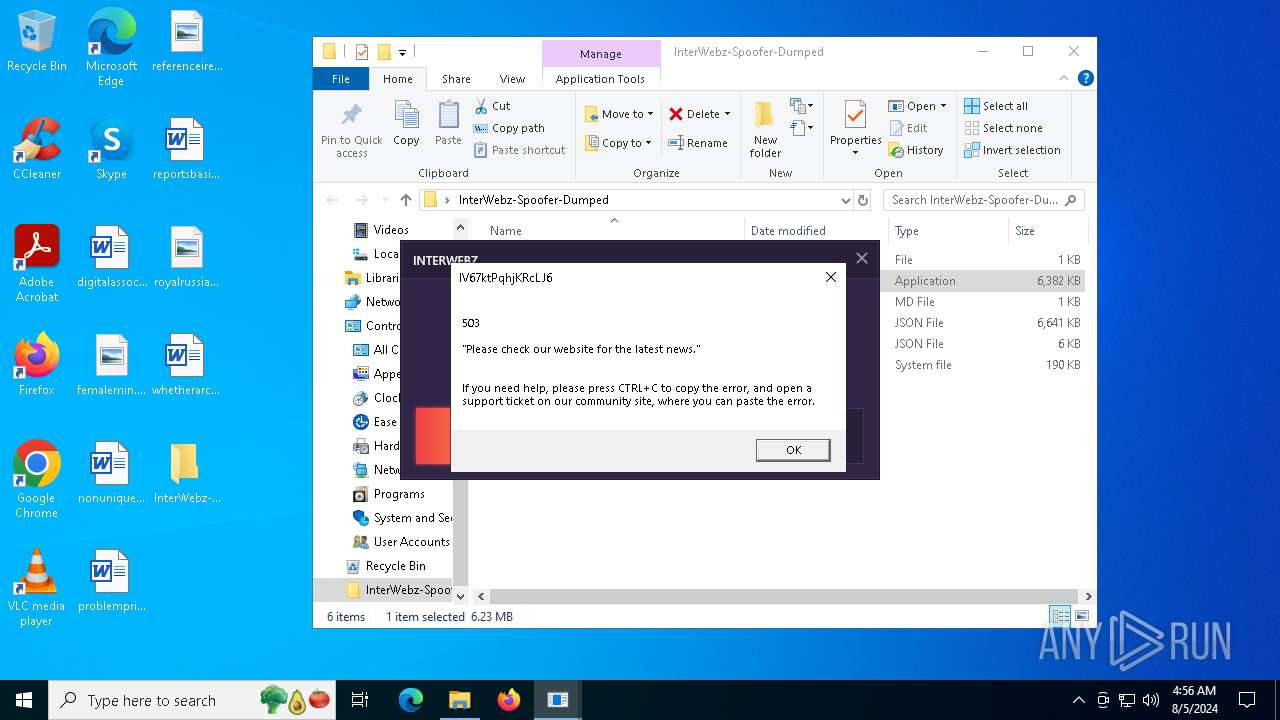
Executes application which crashes
- loader.exe (PID: 5916)
- loader.exe (PID: 5372)
INFO
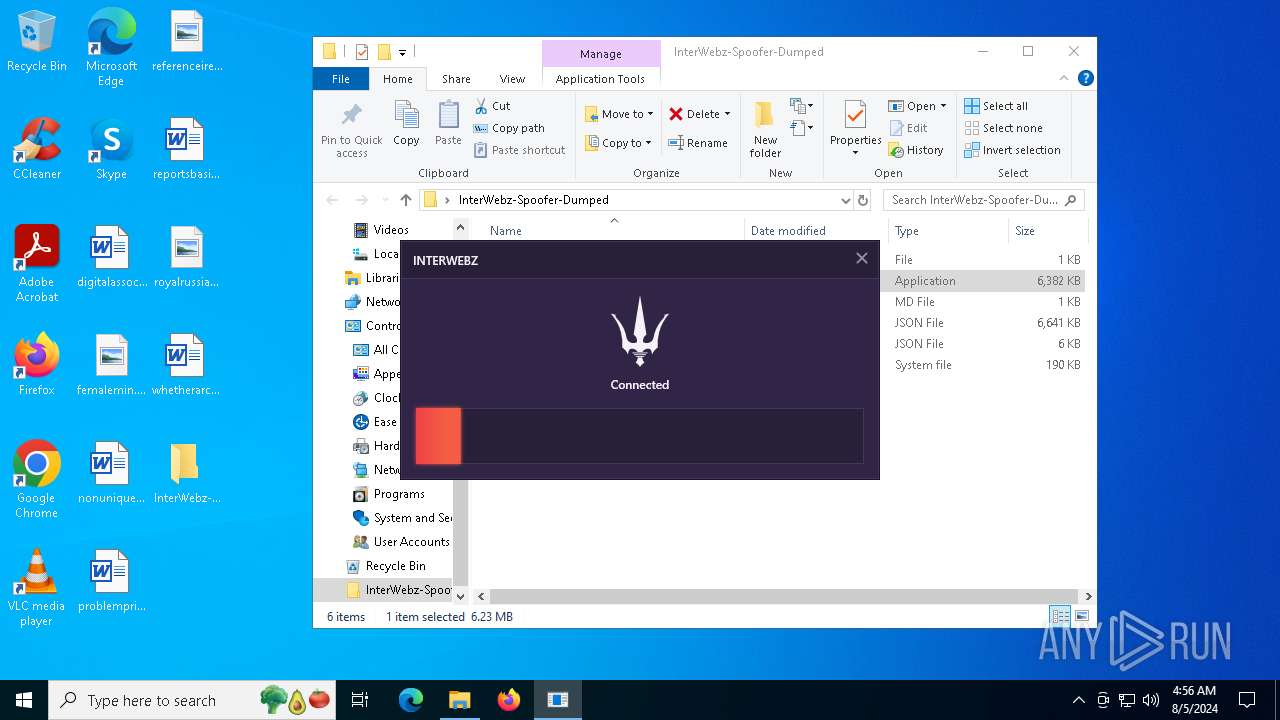
Manual execution by a user
- loader.exe (PID: 6008)
- loader.exe (PID: 5916)
- loader.exe (PID: 5372)
- loader.exe (PID: 6632)
Process checks whether UAC notifications are on
- loader.exe (PID: 5916)
- loader.exe (PID: 5372)
Checks supported languages
- loader.exe (PID: 5916)
- loader.exe (PID: 5372)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6484)
Reads the computer name
- loader.exe (PID: 5916)
- loader.exe (PID: 5372)
Reads the software policy settings
- WerFault.exe (PID: 4692)
- WerFault.exe (PID: 6684)
Checks proxy server information
- WerFault.exe (PID: 4692)
- WerFault.exe (PID: 6684)
Creates files or folders in the user directory
- WerFault.exe (PID: 4692)
- WerFault.exe (PID: 6684)
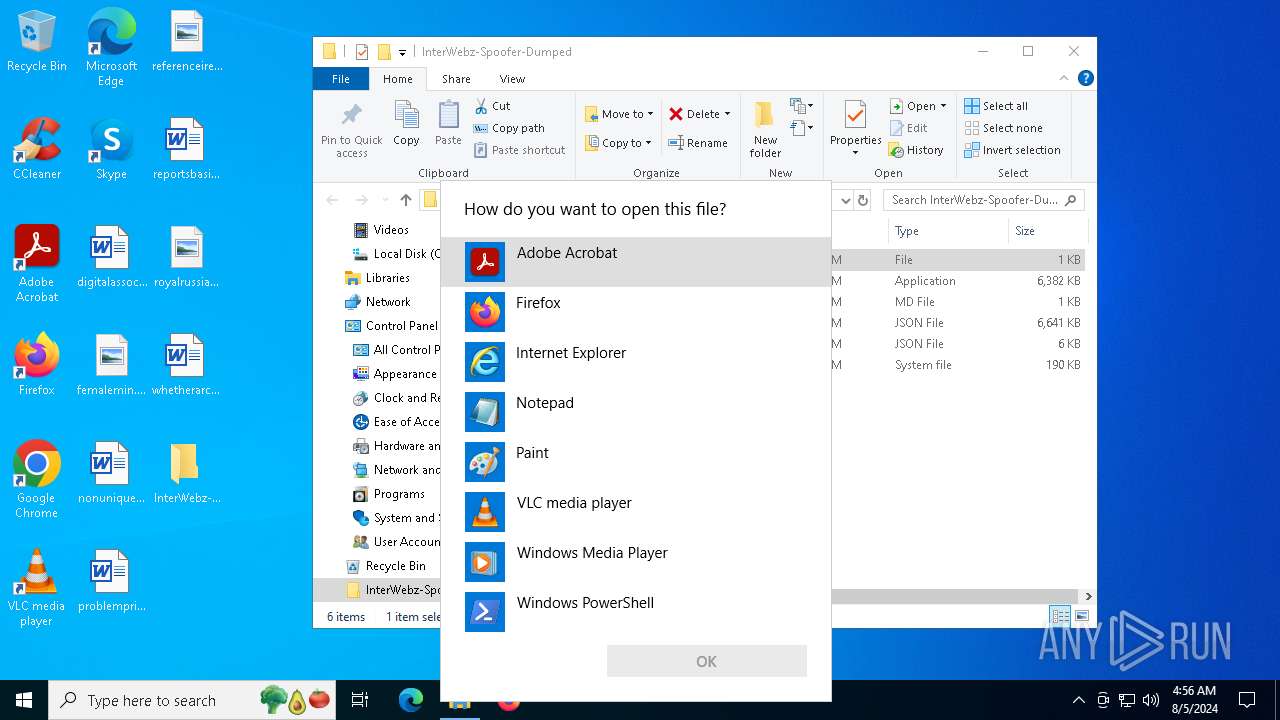
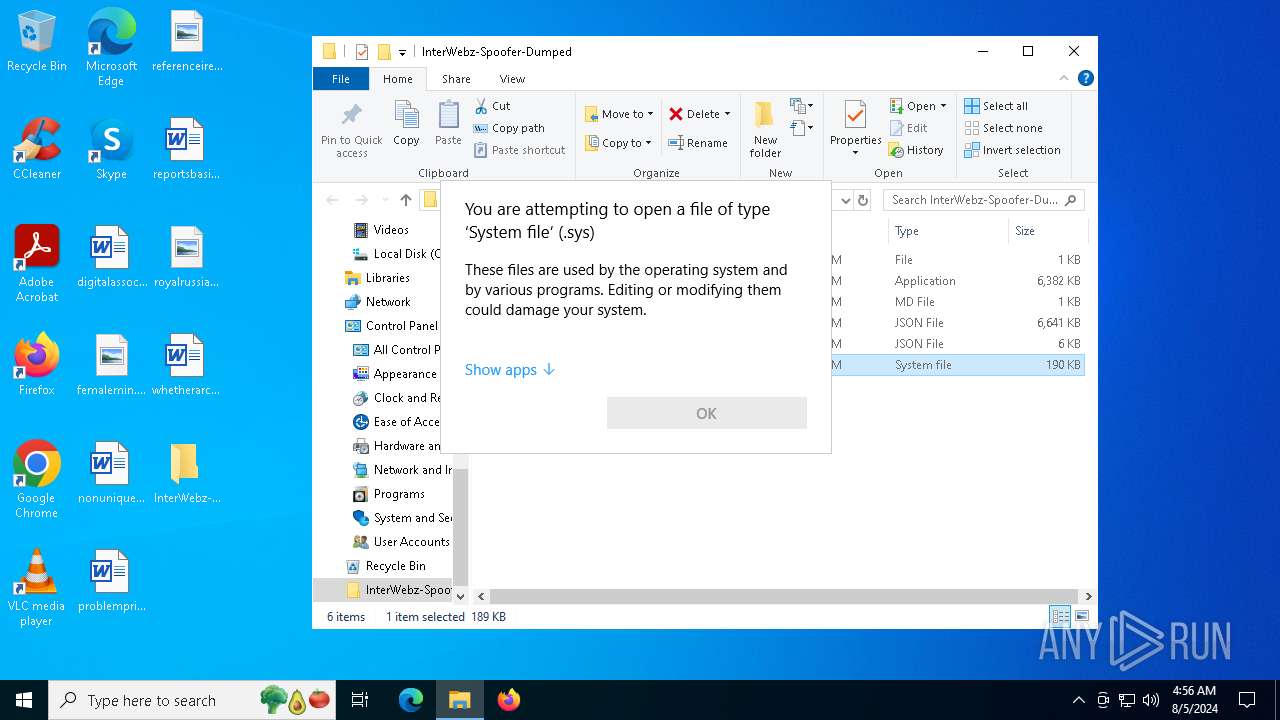
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6360)
- OpenWith.exe (PID: 5292)
- OpenWith.exe (PID: 2616)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
144
Monitored processes
11
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2616 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3276 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4692 | C:\WINDOWS\system32\WerFault.exe -u -p 5916 -s 896 | C:\Windows\System32\WerFault.exe | loader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5292 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
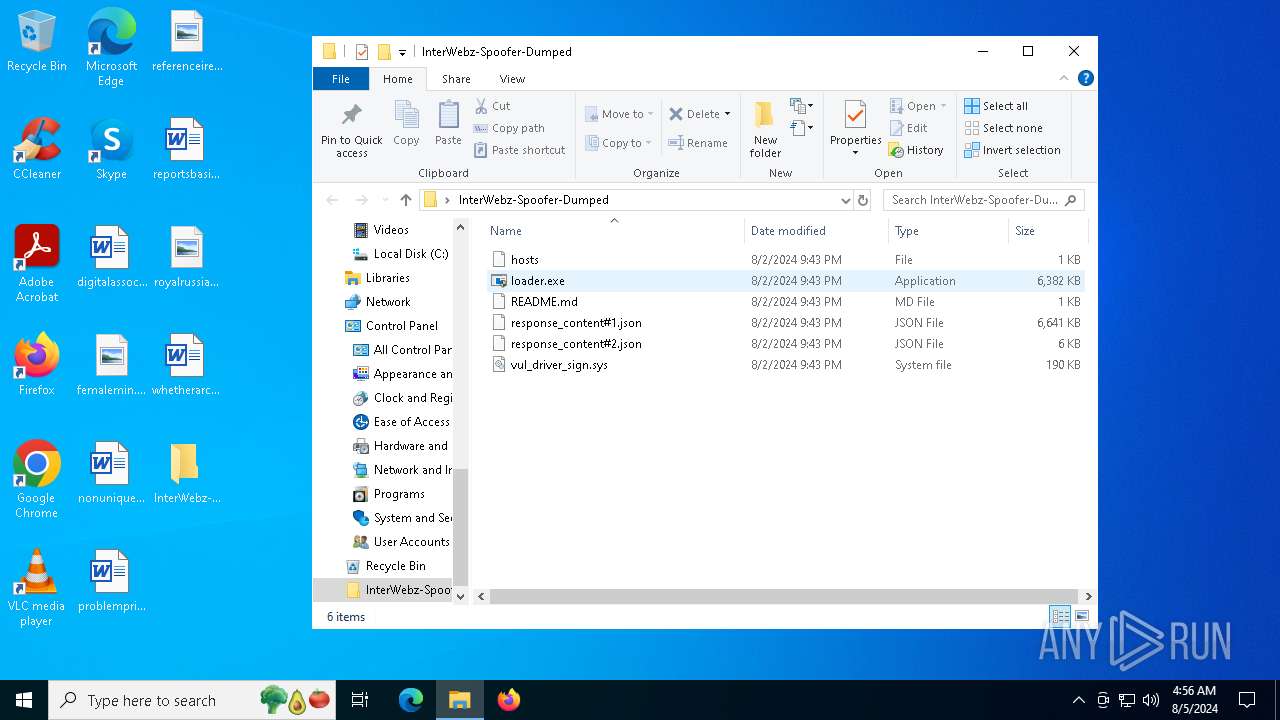
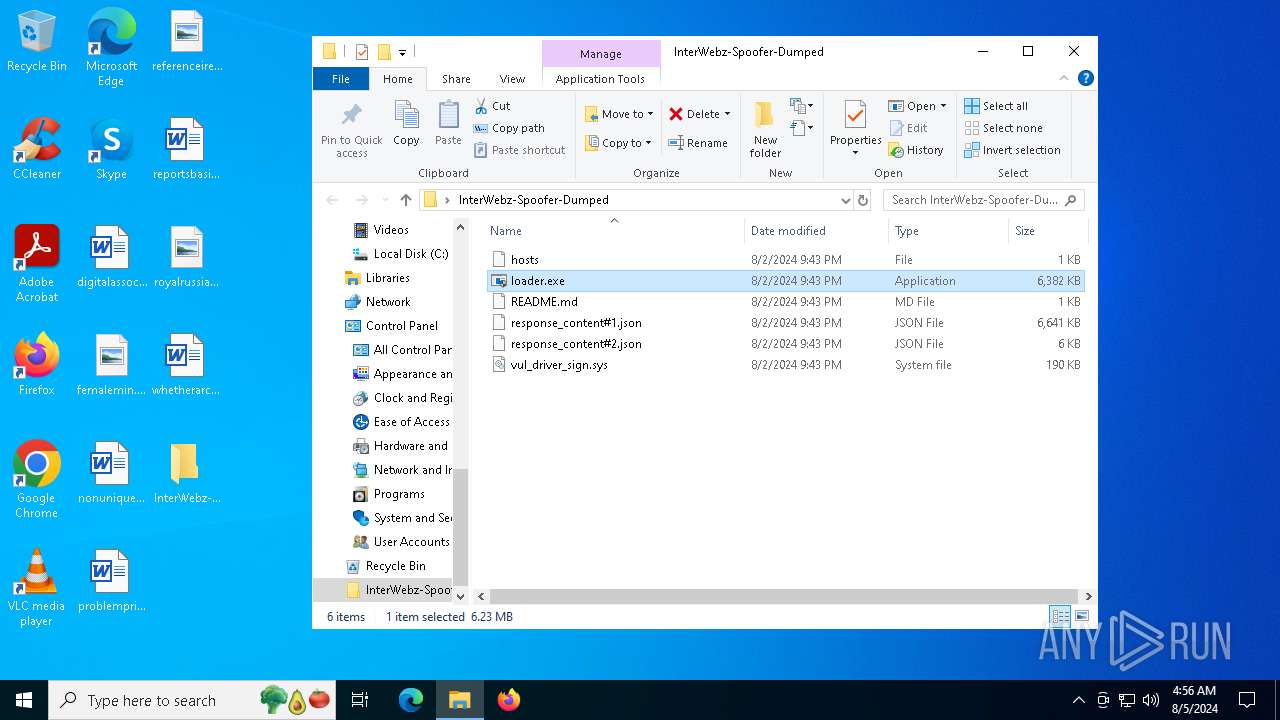
| 5372 | "C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\loader.exe" | C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2147483651 Modules
| |||||||||||||||
| 5916 | "C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\loader.exe" | C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2147483651 Modules
| |||||||||||||||
| 6008 | "C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\loader.exe" | C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6360 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
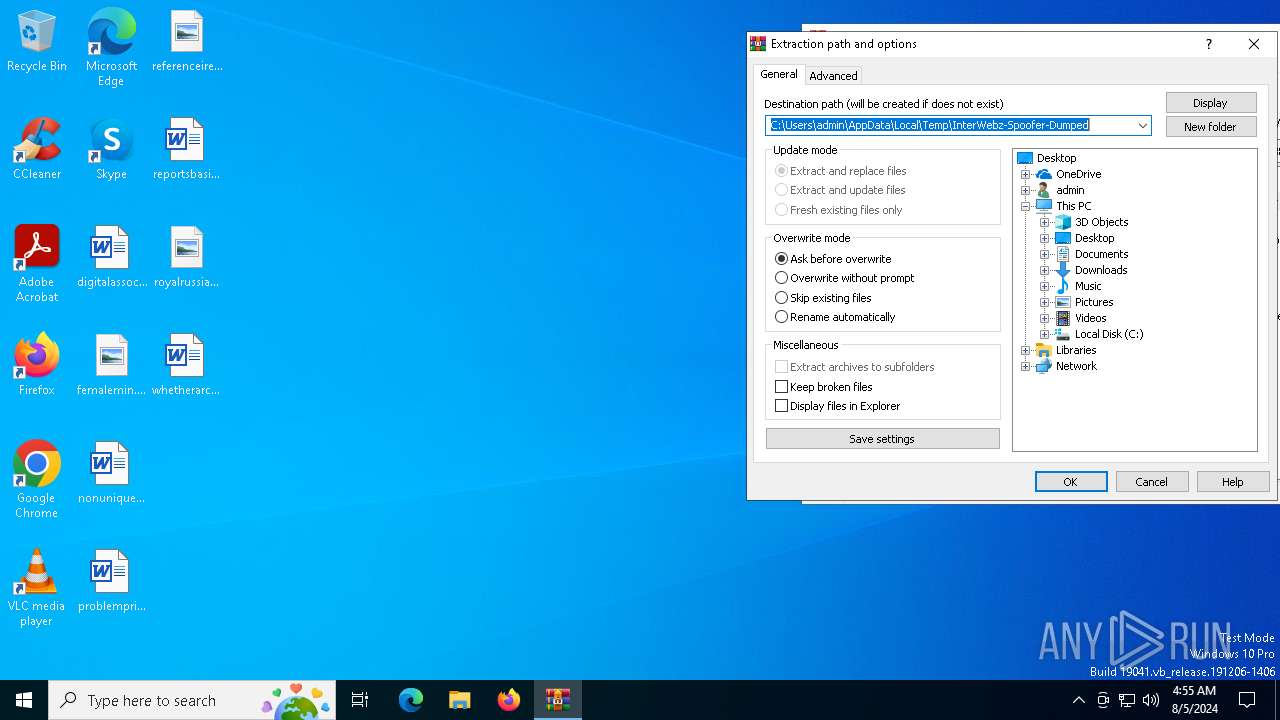
| 6484 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\InterWebz-Spoofer-Dumped.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6632 | "C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\loader.exe" | C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
17 896
Read events
17 851
Write events
33
Delete events
12
Modification events
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\InterWebz-Spoofer-Dumped.7z | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped | |||
| (PID) Process: | (6484) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF160100002B000000D604000014020000 | |||
Executable files
2
Suspicious files
4
Text files
7
Unknown types
1
Dropped files
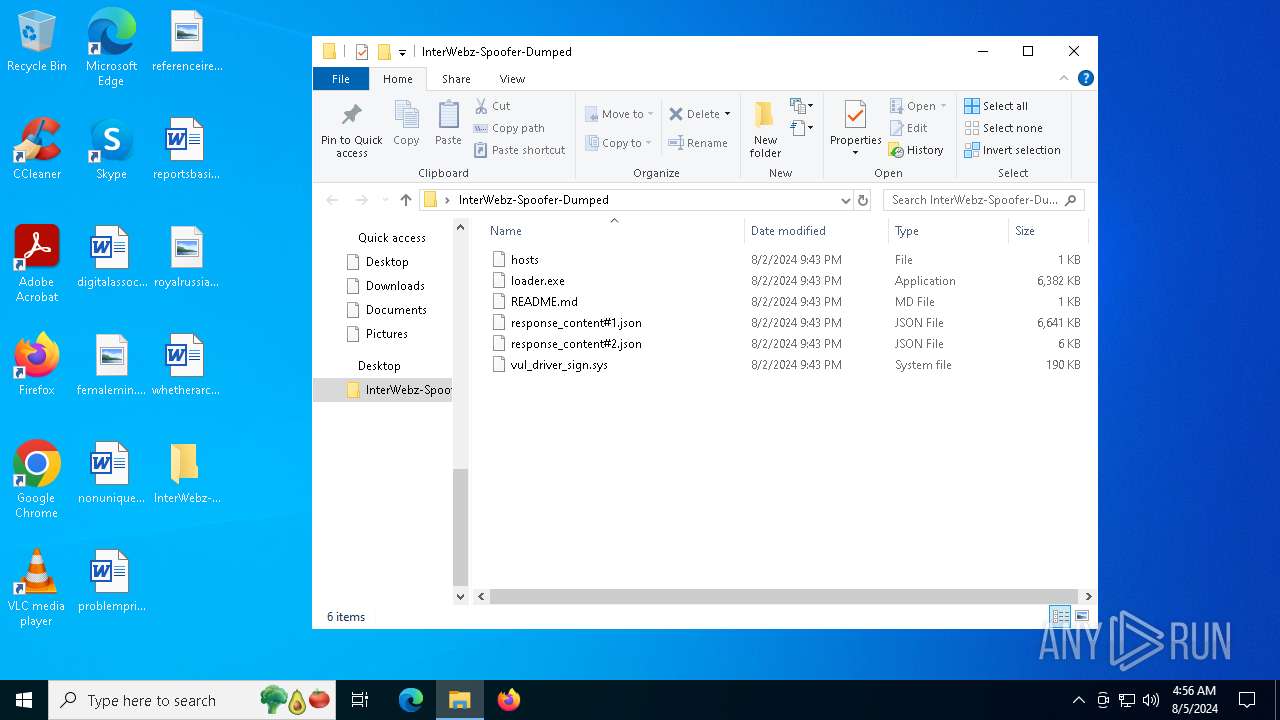
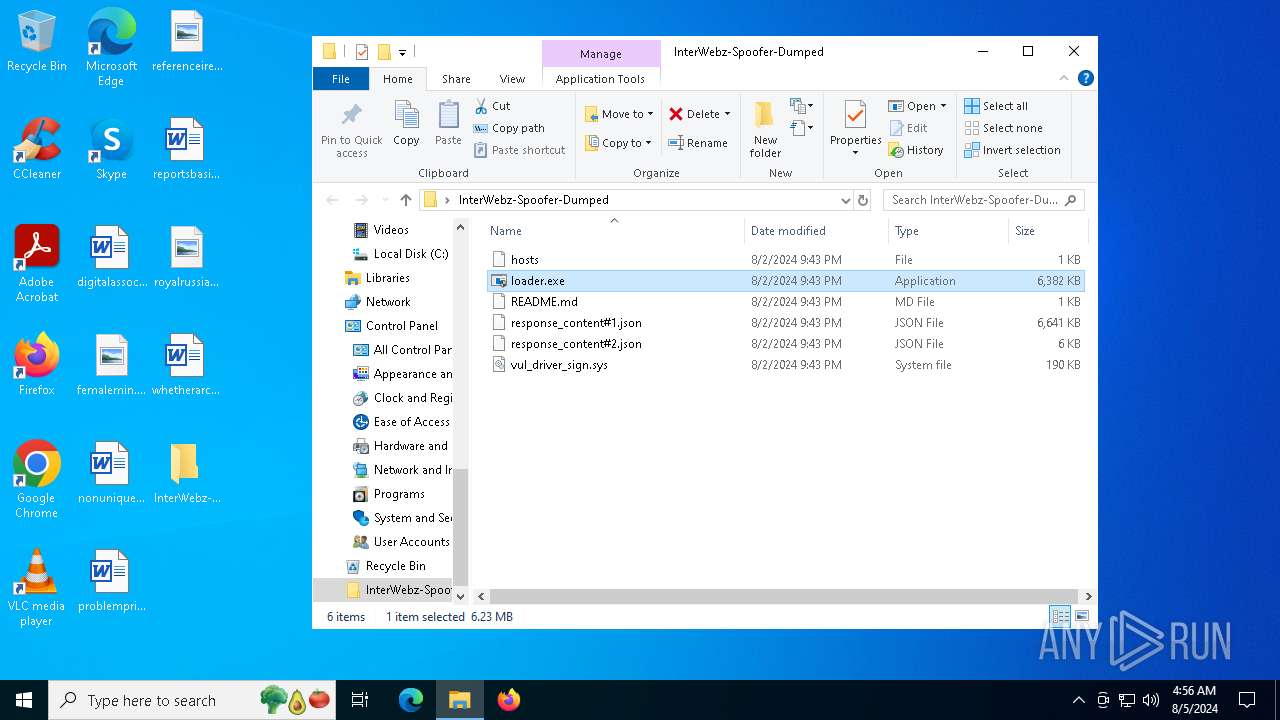
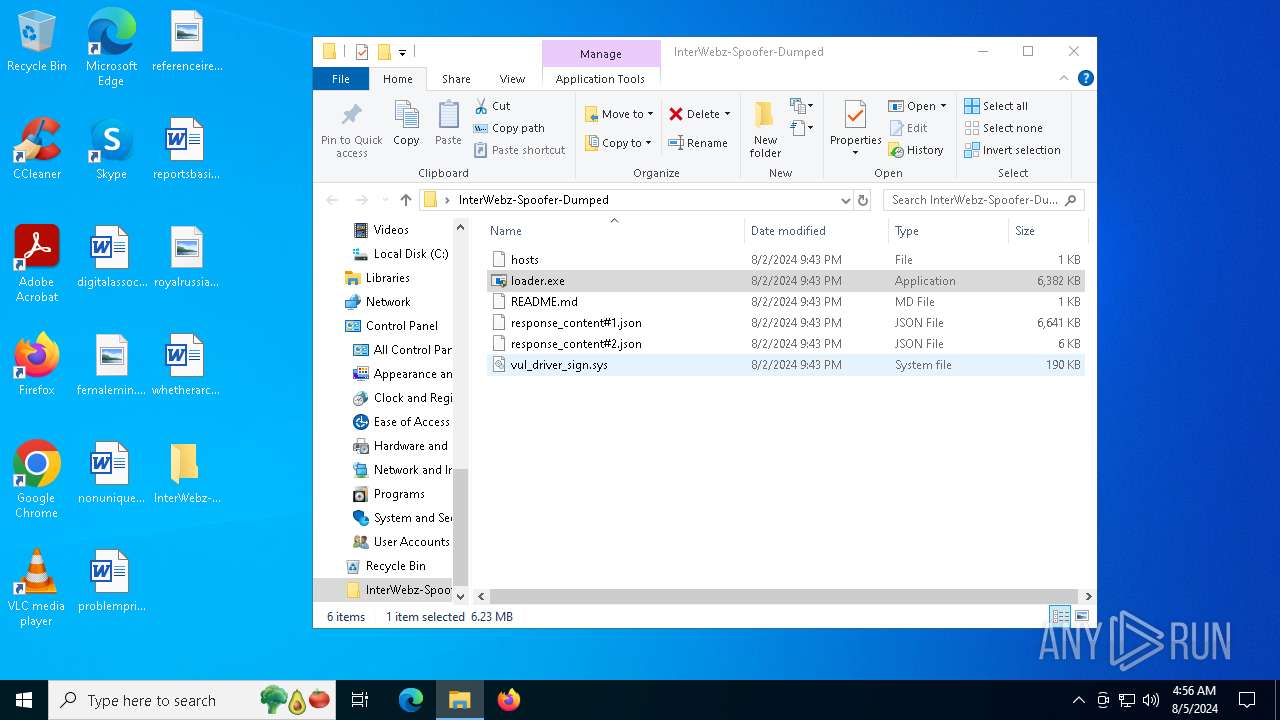
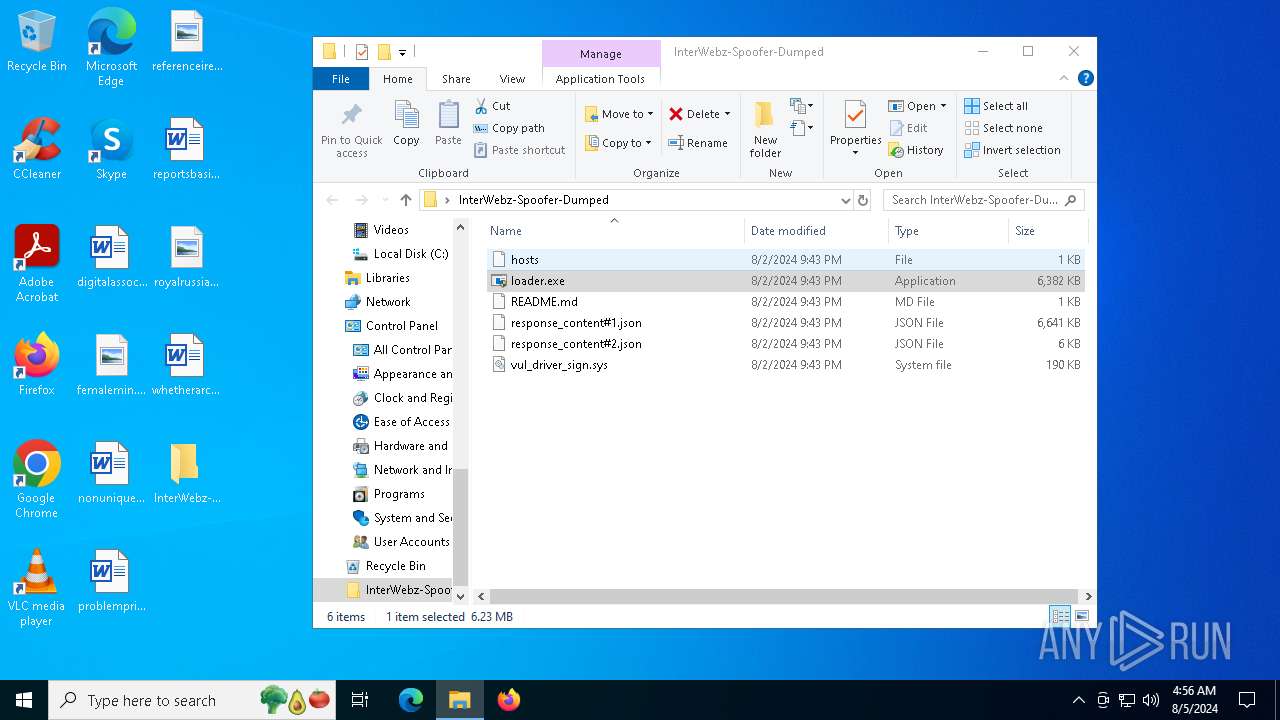
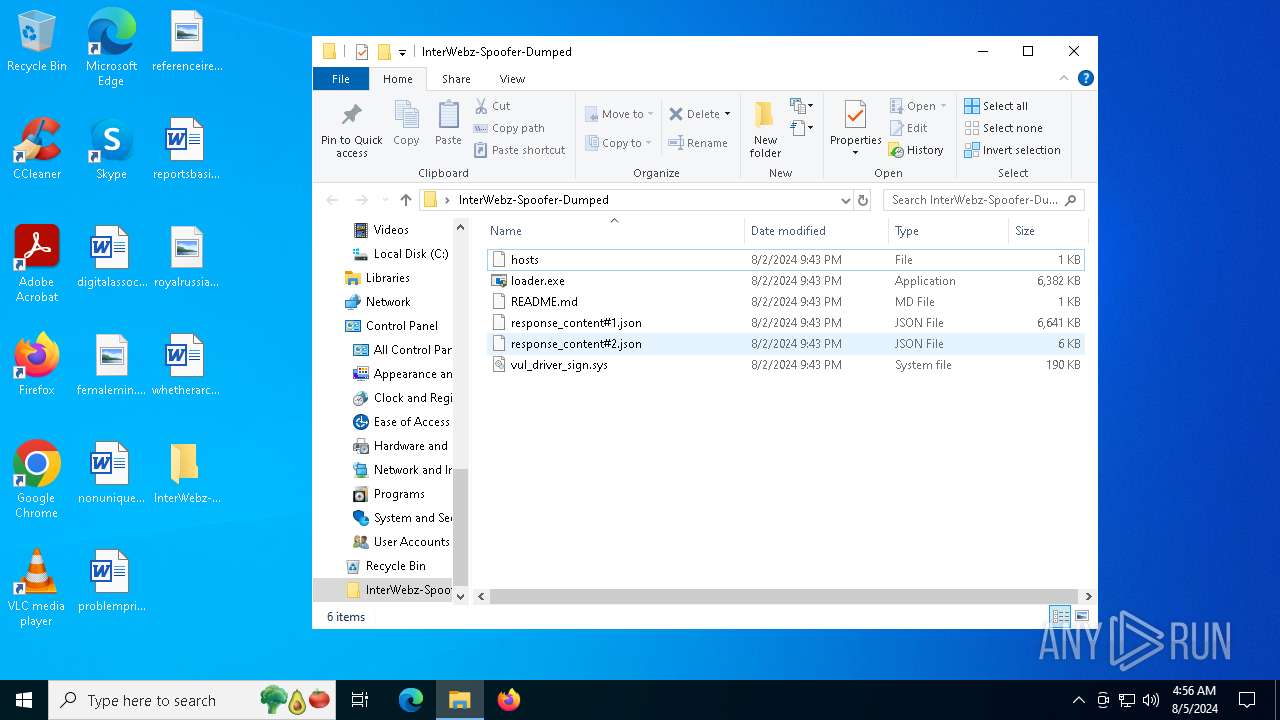
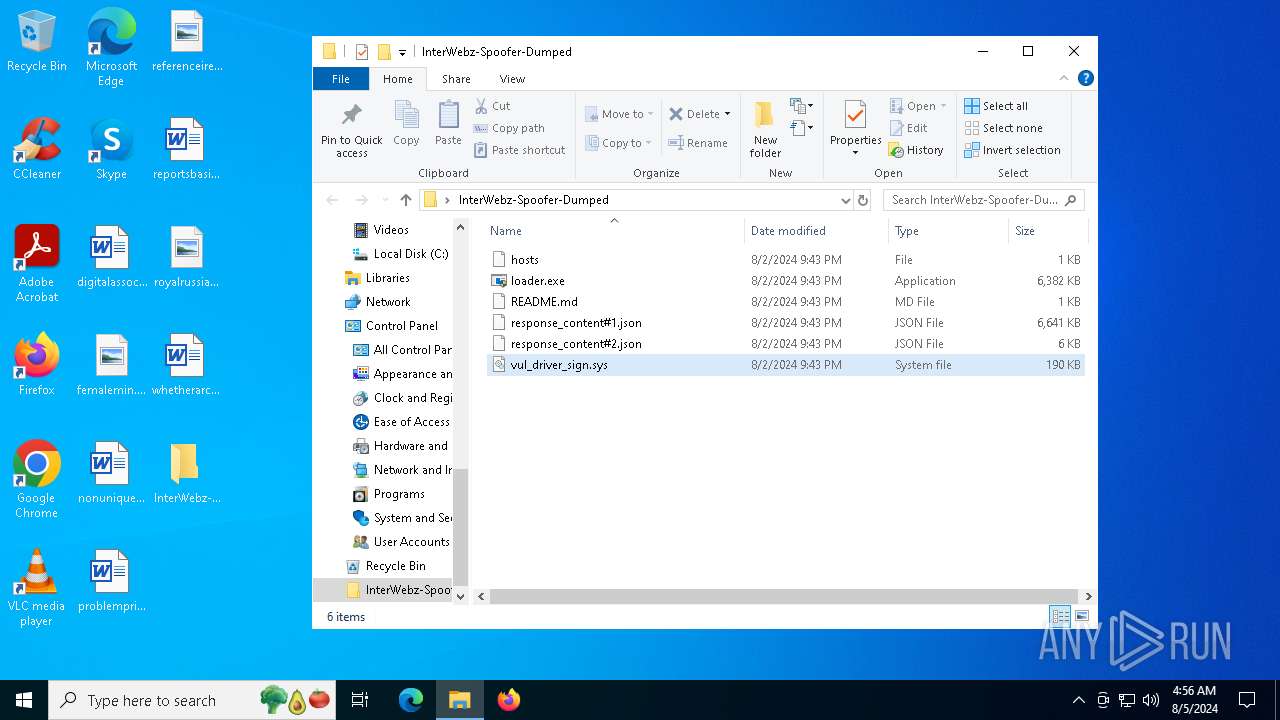
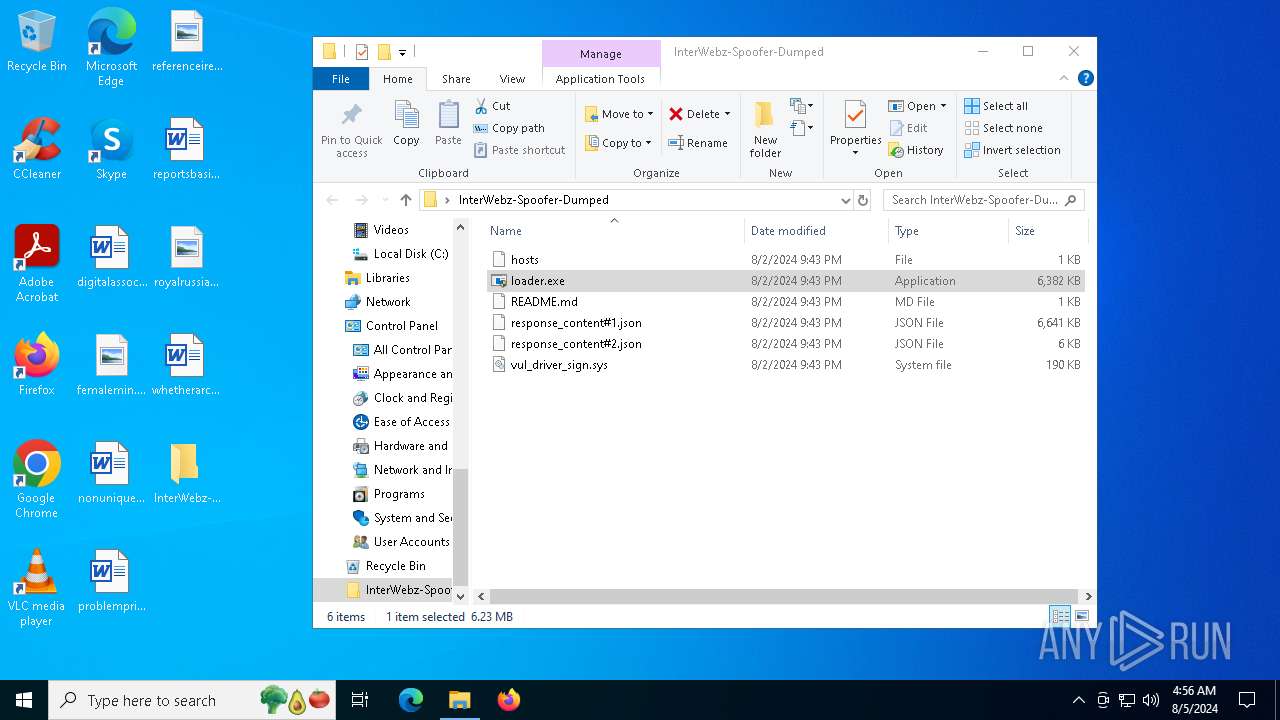
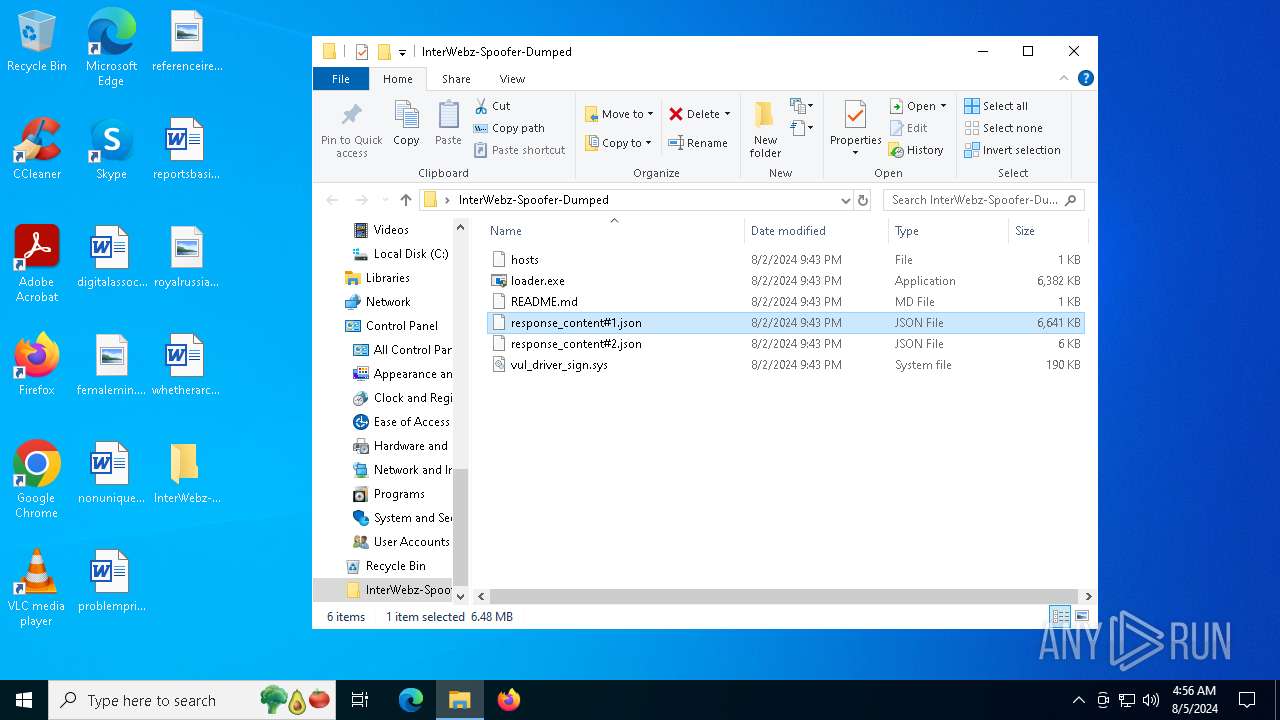
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6484 | WinRAR.exe | C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\response_content#1.json | — | |
MD5:— | SHA256:— | |||
| 4692 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_loader.exe_b3b3a4e71a1eaae95e1157c370b43cbdfca7de2f_16e39ca6_f7aab34f-e401-43bb-a007-dea5702a6397\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4692 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\loader.exe.5916.dmp | — | |
MD5:— | SHA256:— | |||
| 6684 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_loader.exe_b3b3a4e71a1eaae95e1157c370b43cbdfca7de2f_16e39ca6_c221f339-b6b0-43bb-a46d-85f769810413\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6684 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\loader.exe.5372.dmp | — | |
MD5:— | SHA256:— | |||
| 6484 | WinRAR.exe | C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\hosts | text | |
MD5:454C90B79E5D63B82339FA94A68981FC | SHA256:DEBDAD24F64F37F7B340516981B02AB09B5402F8833999D69B5E16DC97DD1077 | |||
| 6484 | WinRAR.exe | C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\response_content#2.json | text | |
MD5:DBDA1CC6044ACF533F5BAB2F52C47B29 | SHA256:17BEED7E59AF6F99E0054A6BA1376DC9EE79AAE6F34F34CF6282DA3AC4F561EA | |||
| 6484 | WinRAR.exe | C:\Users\admin\Desktop\InterWebz-Spoofer-Dumped\README.md | text | |
MD5:76B51460D148A0071CCE102CCC301A79 | SHA256:A1FC2D678A5D128B76447FD78B7E03A87481B36CCA2A948527BFC8C4F842588D | |||
| 4692 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERE23E.tmp.WERInternalMetadata.xml | xml | |
MD5:80F80DEBF81F96BAC34AD5C14F5CD7C9 | SHA256:8E8D1CEBC555872CCCDB6E06336D72F8AB828EACFE8DC9DE7ECADDF296A131B1 | |||
| 4692 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERE25F.tmp.xml | xml | |
MD5:F0CA31EE4B8C57A7F8A1EDFA79E02AD0 | SHA256:7F192AF3E32AE044449F6A5F3CBB511513DF5FAAD17A8585E1731334ECDE7C4F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
45
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3476 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3476 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6872 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6824 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3208 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3980 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5336 | SearchApp.exe | 95.100.146.34:443 | www.bing.com | Akamai International B.V. | CZ | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3476 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |