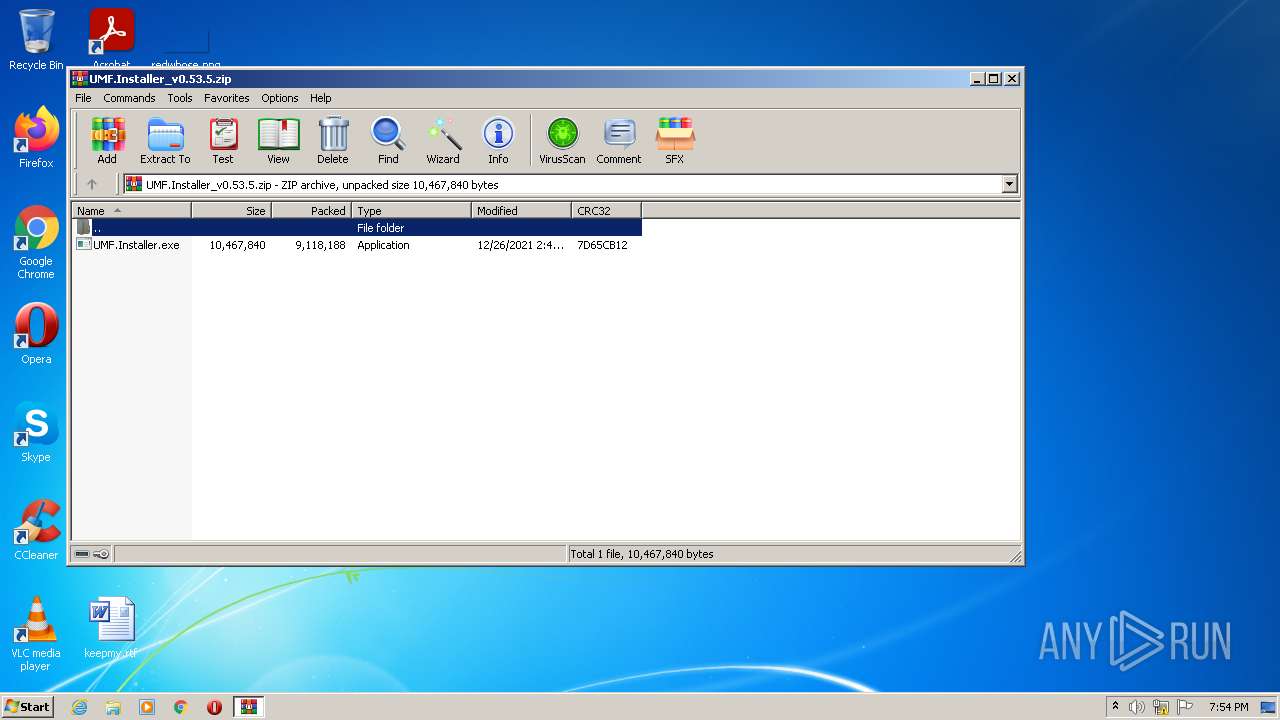
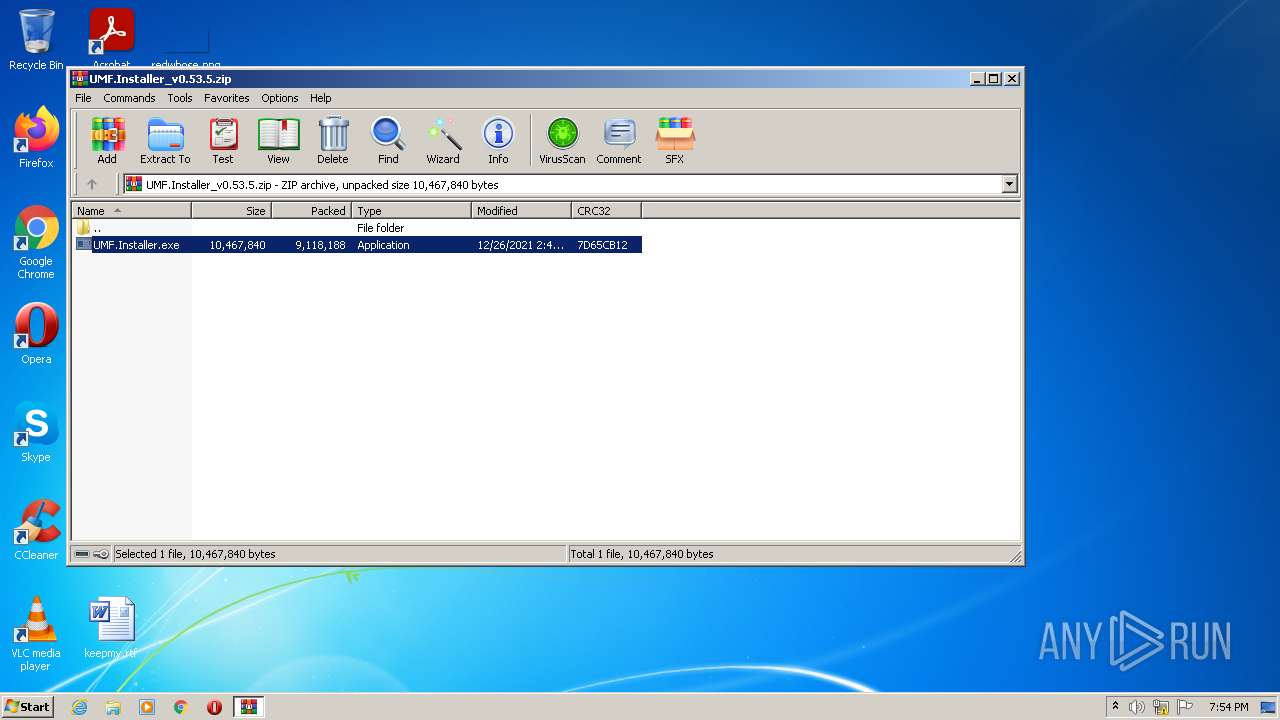
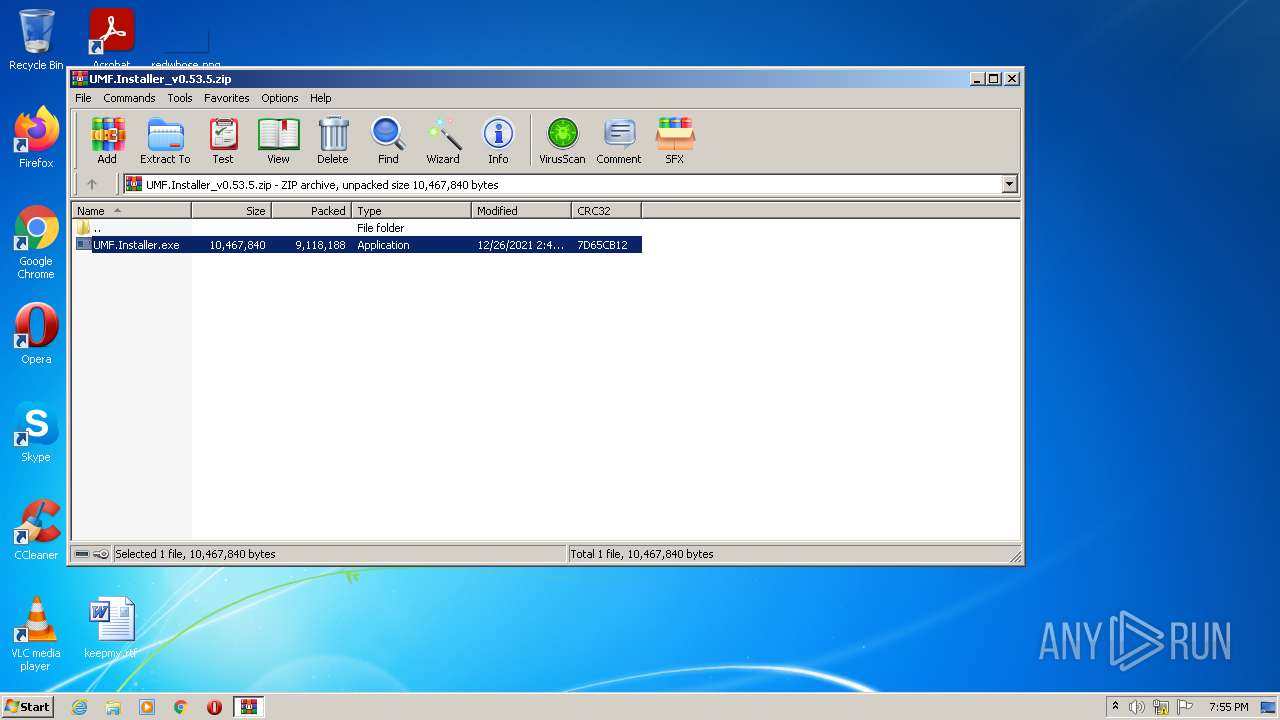
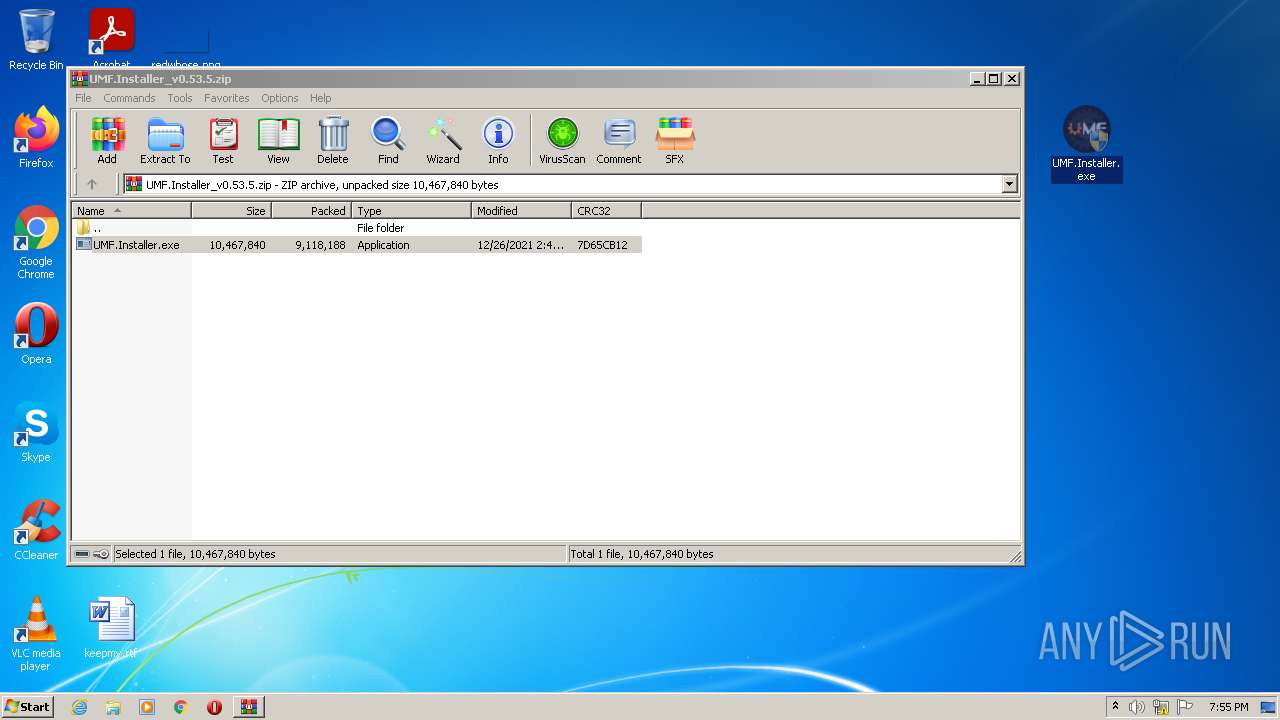
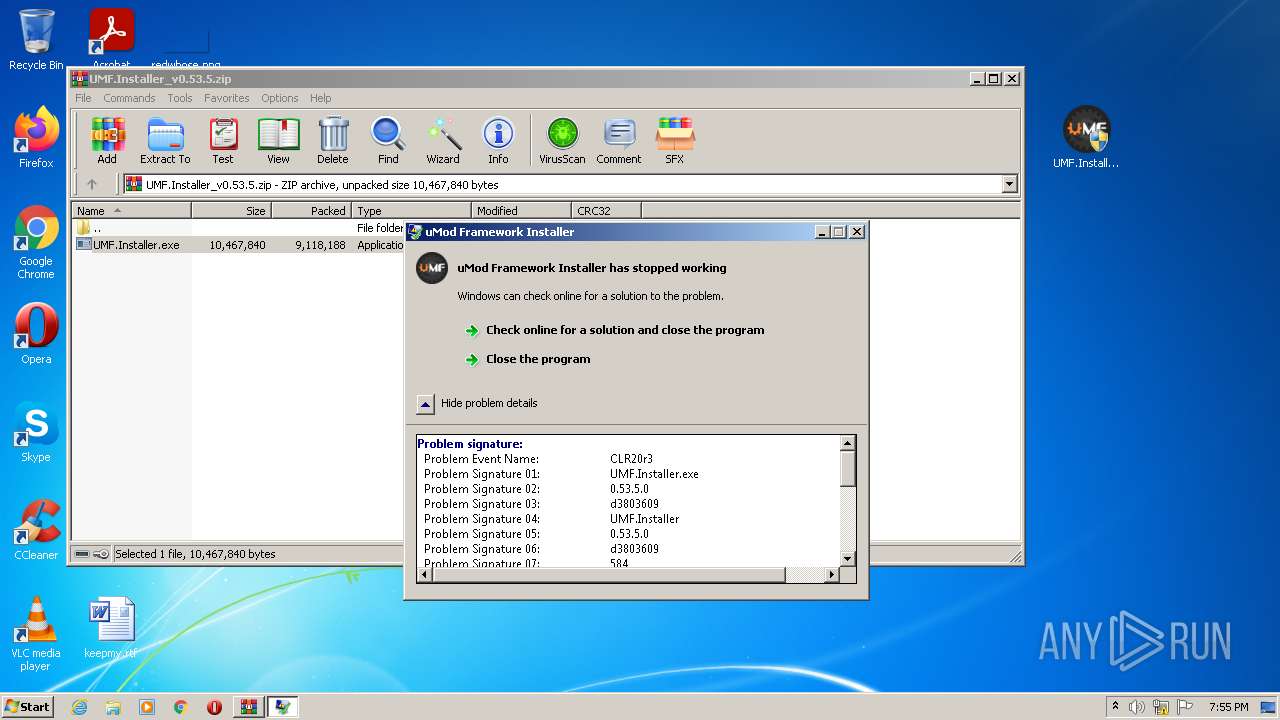
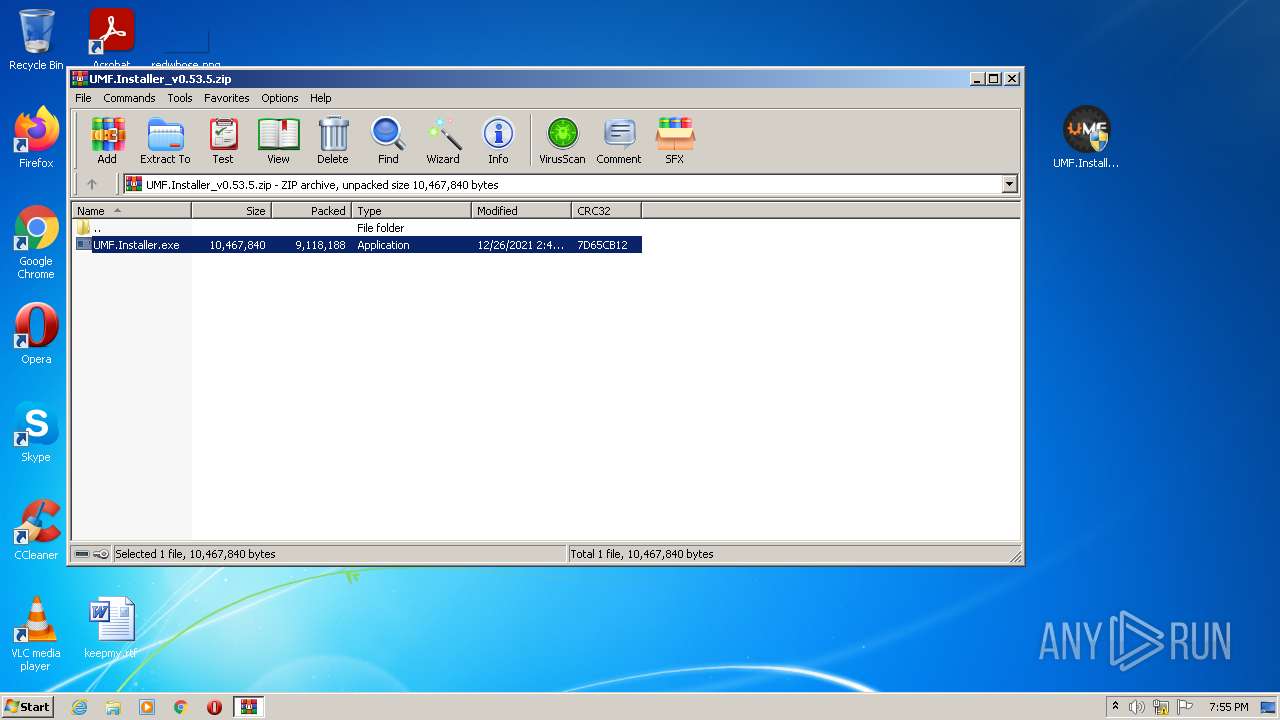
| File name: | UMF.Installer_v0.53.5.zip |
| Full analysis: | https://app.any.run/tasks/c1d12b27-72bf-4a02-9163-2c203e79cef0 |
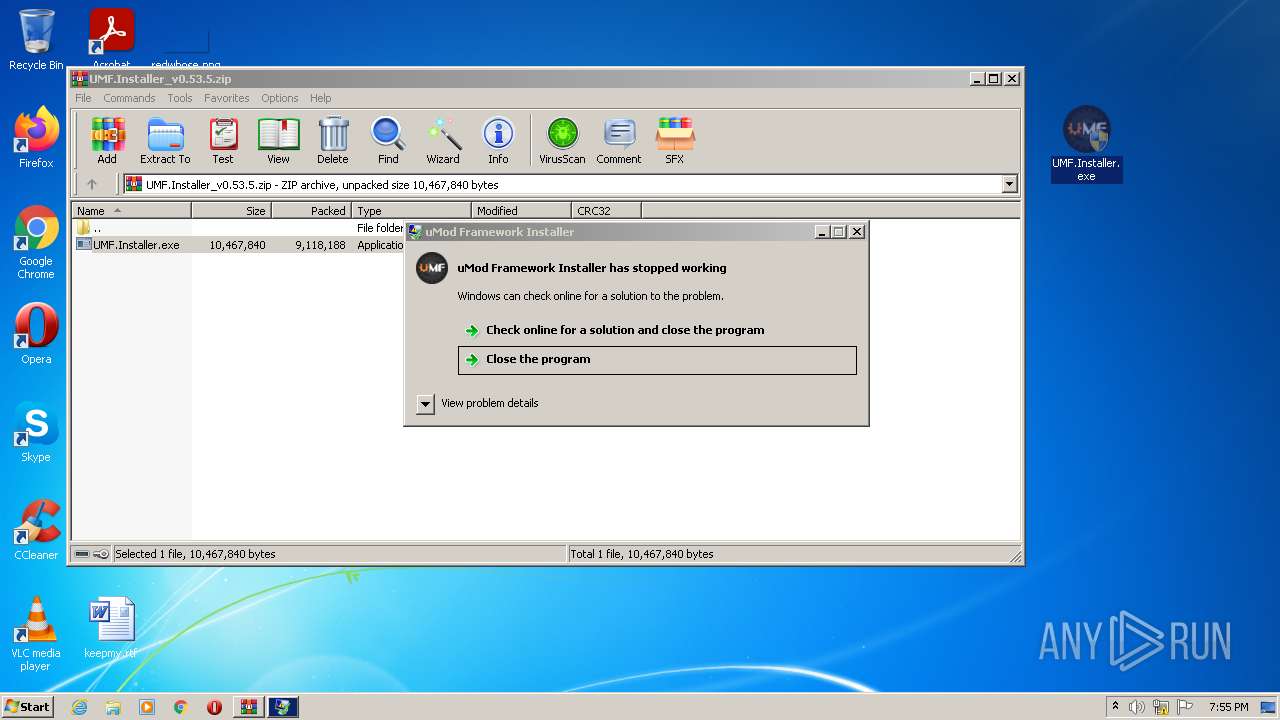
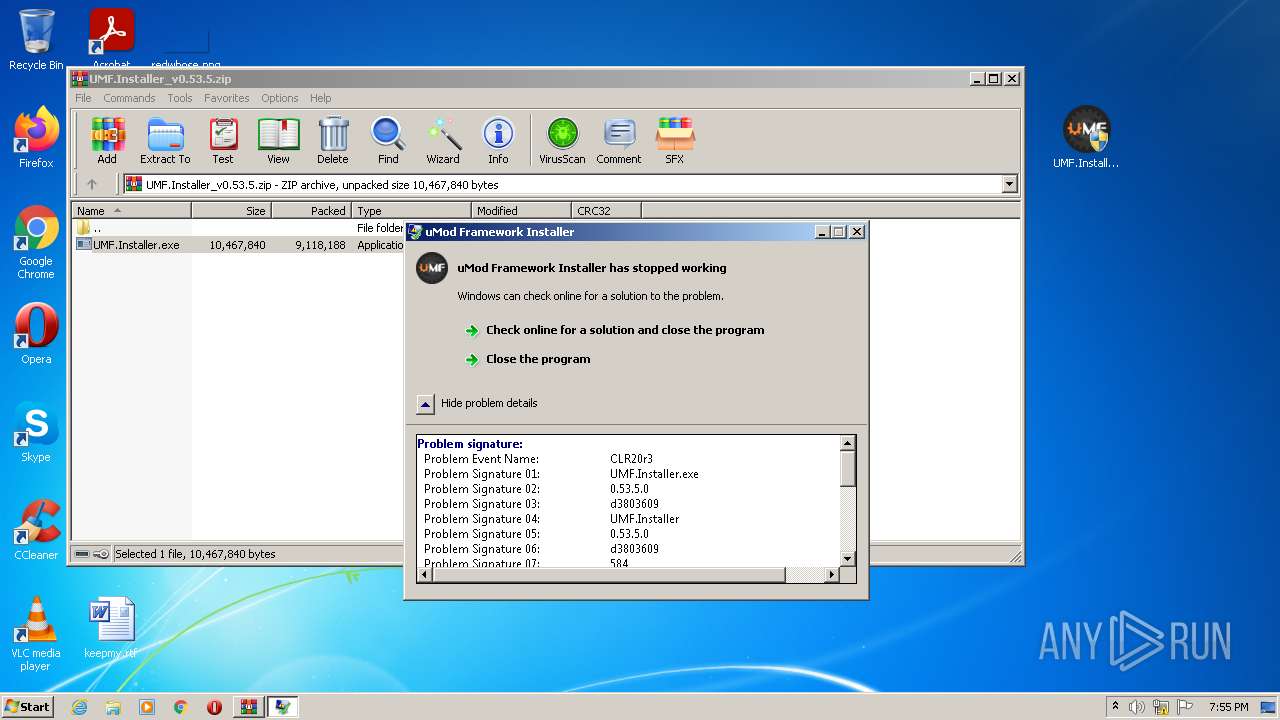
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 19:54:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 38F4392D0B6AC2017A456185543E4991 |
| SHA1: | 1B017FB608FFA750ED99DB2687ADEA0FF9F240B0 |
| SHA256: | 30A8F1AEC09F2CC225EC52C6CBAB9C6B541291525104DB9503450540789A1EF4 |
| SSDEEP: | 196608:urNFc+geu7W2k1hA0EjU4eUGyVBhMuiTgX5E/25dJd72D96/uf:Z3euSEjU4eUG4liME/Mrd72pauf |
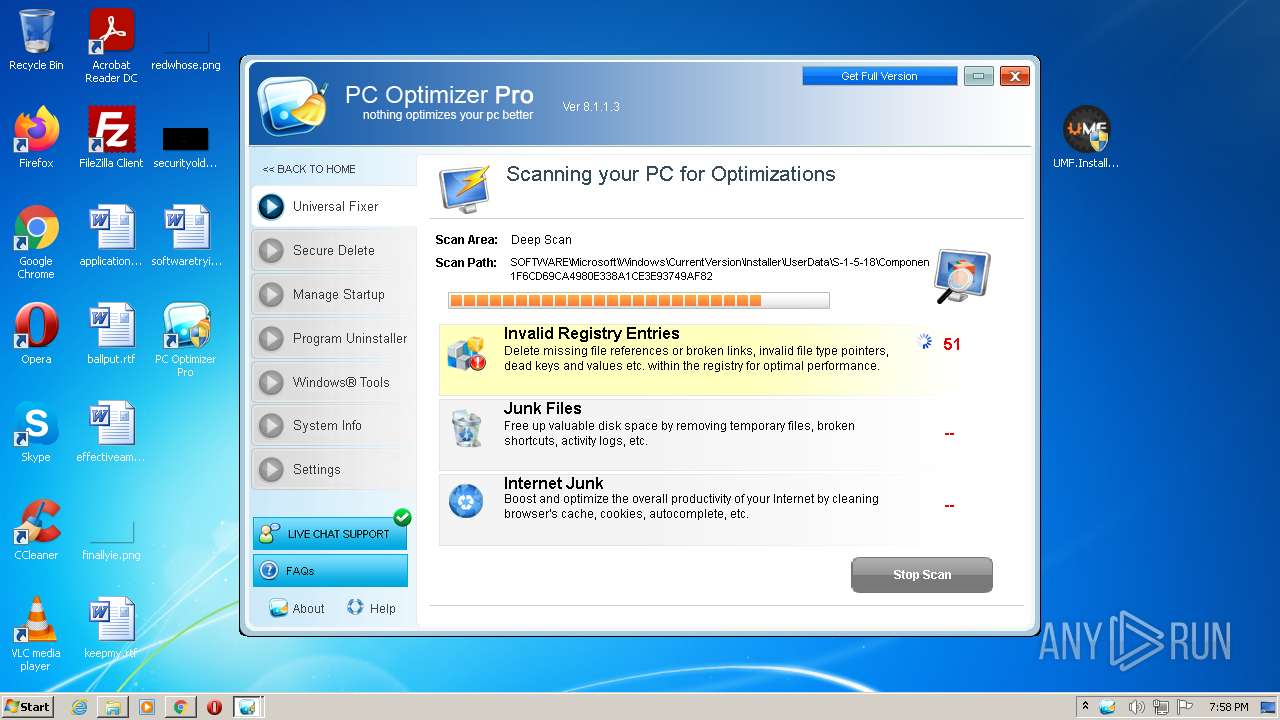
MALICIOUS
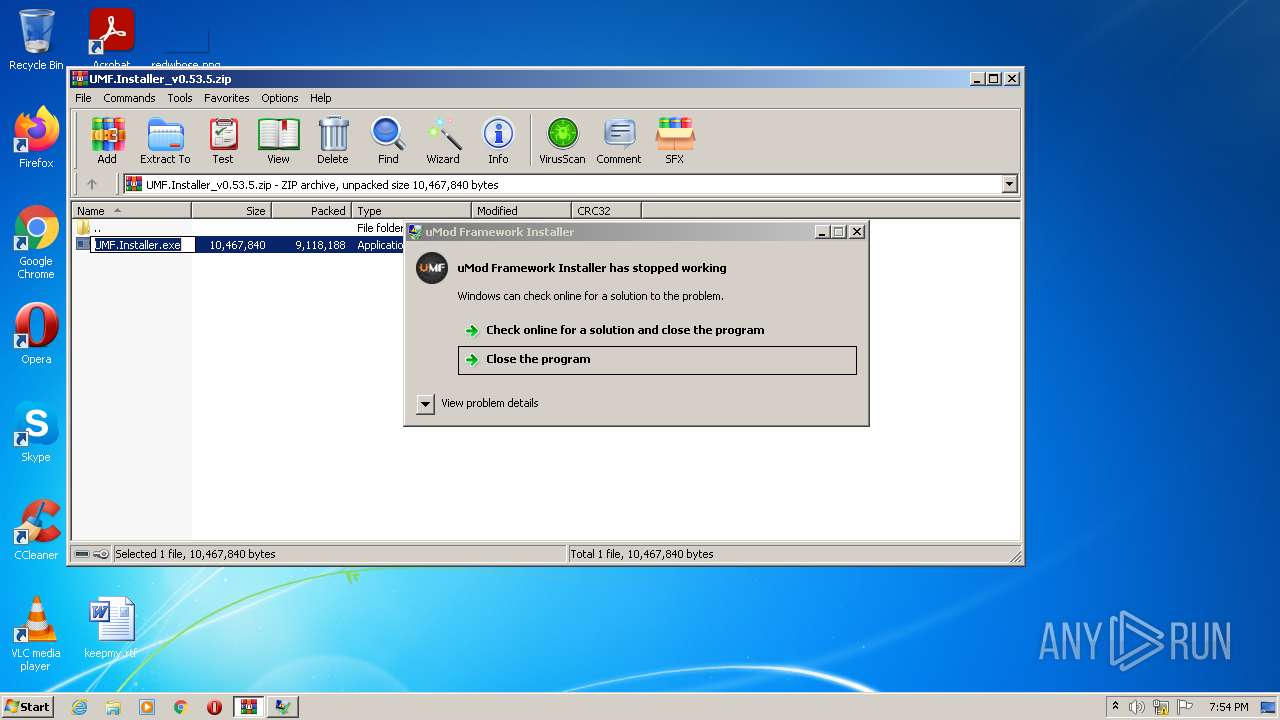
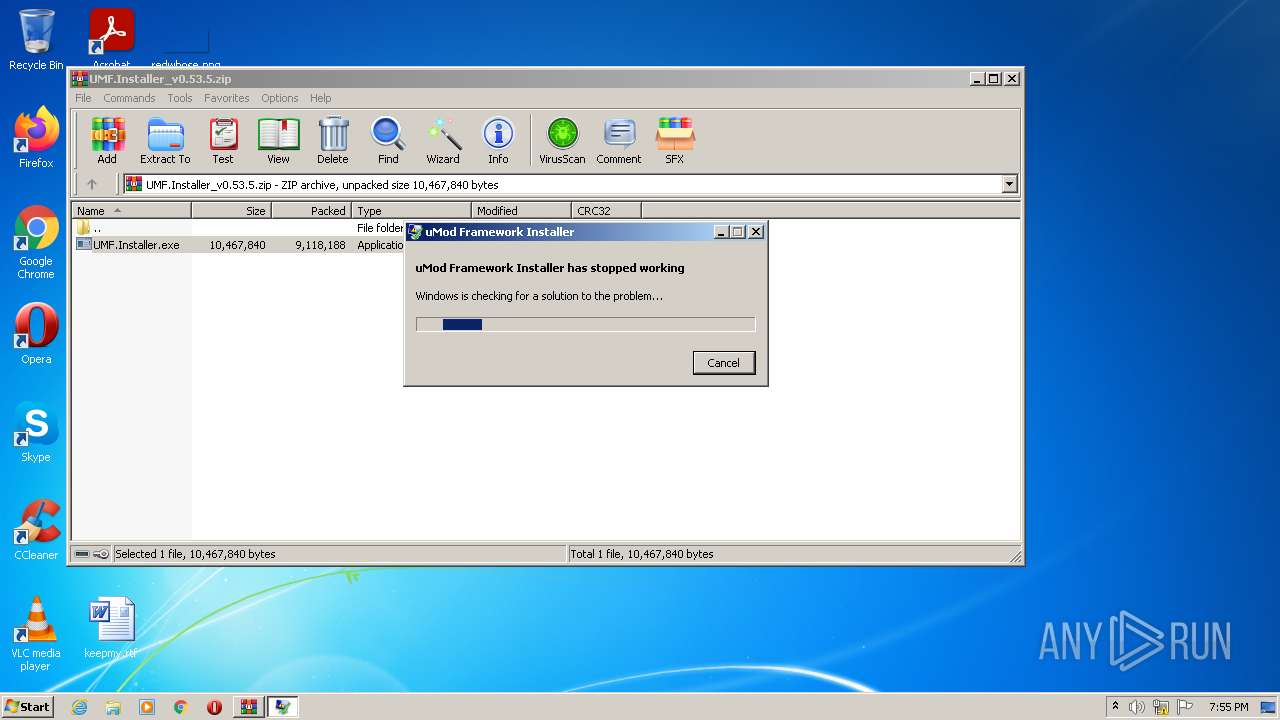
Application was dropped or rewritten from another process
- UMF.Installer.exe (PID: 3568)
- UMF.Installer.exe (PID: 2268)
- UMF.Installer.exe (PID: 2944)
- UMF.Installer.exe (PID: 3612)
- UMF.Installer.exe (PID: 2800)
- UMF.Installer.exe (PID: 1972)
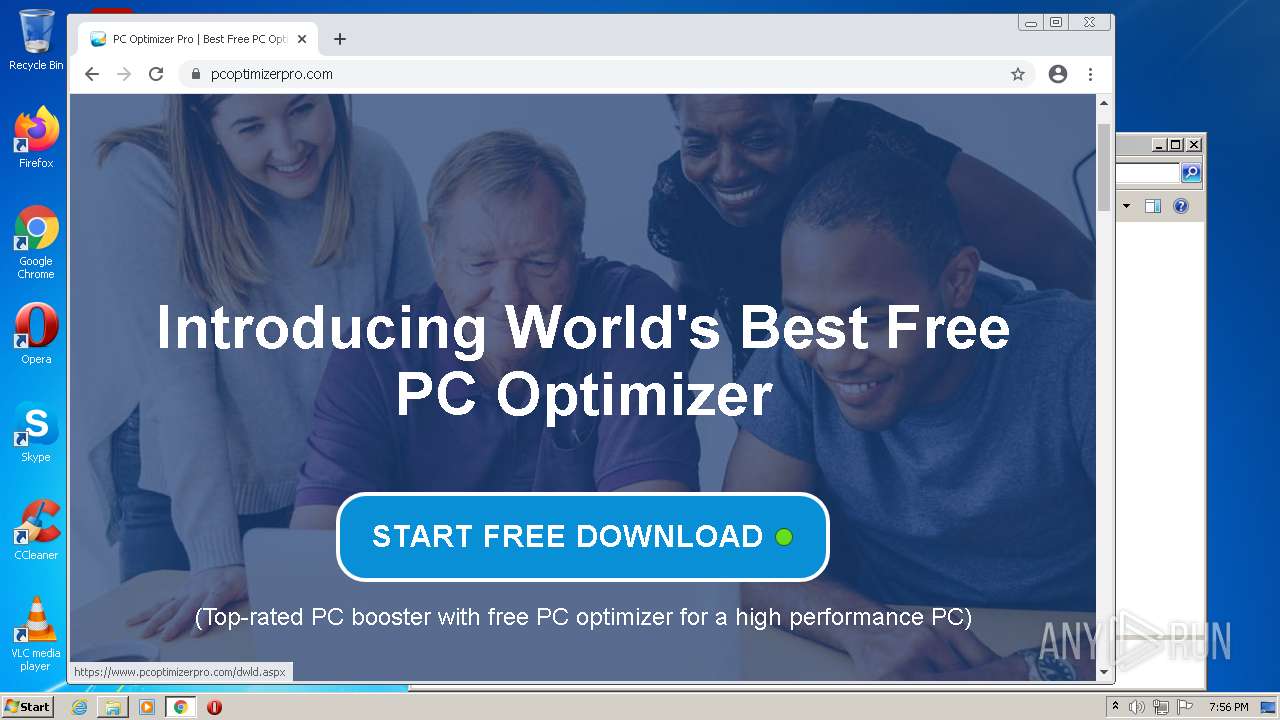
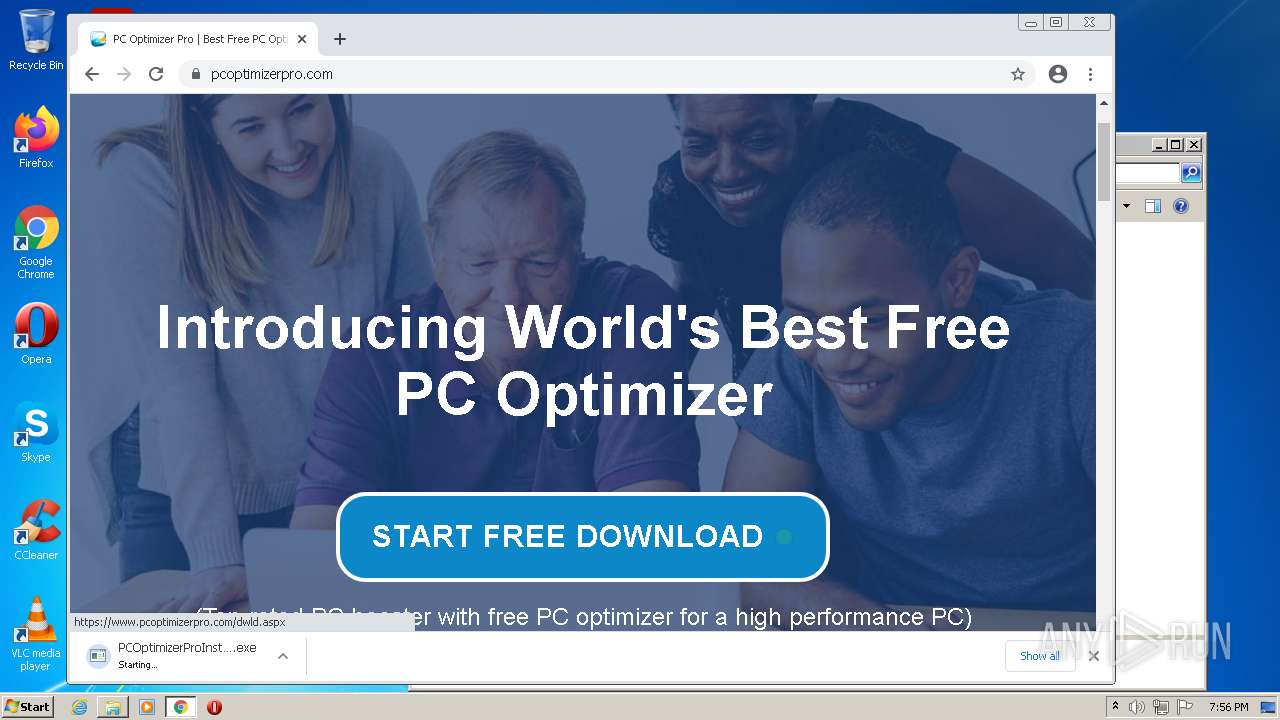
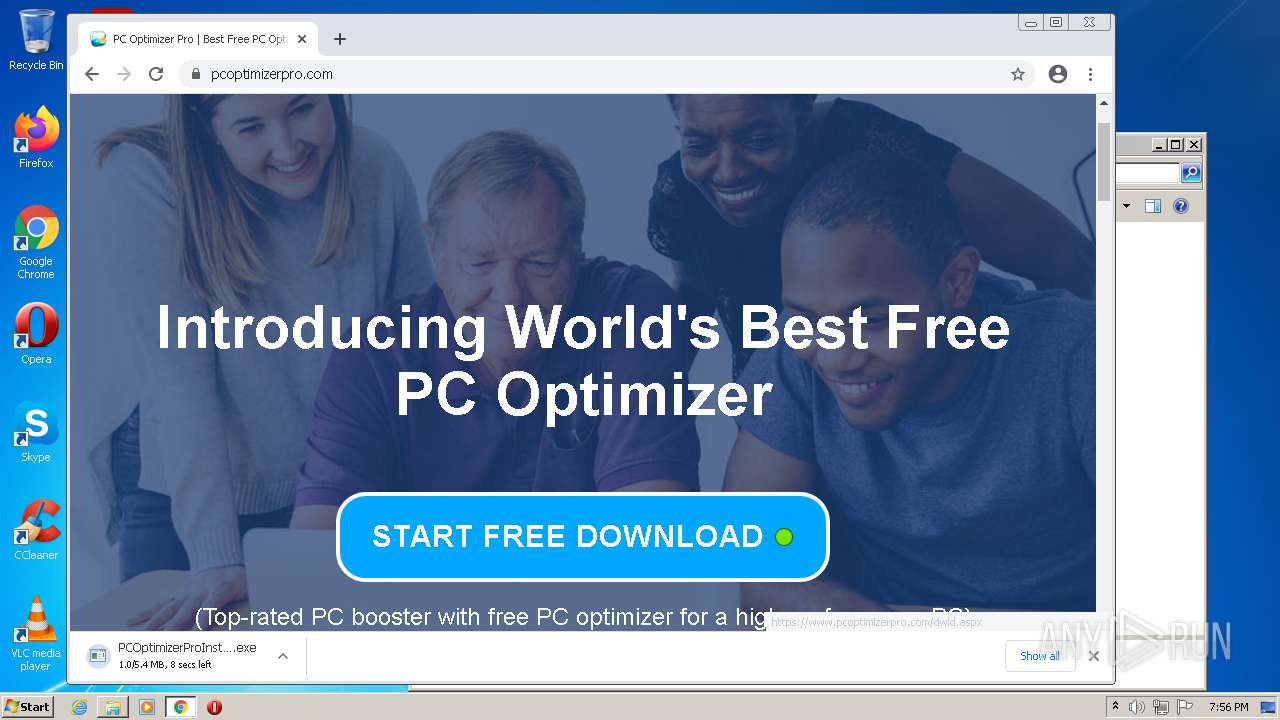
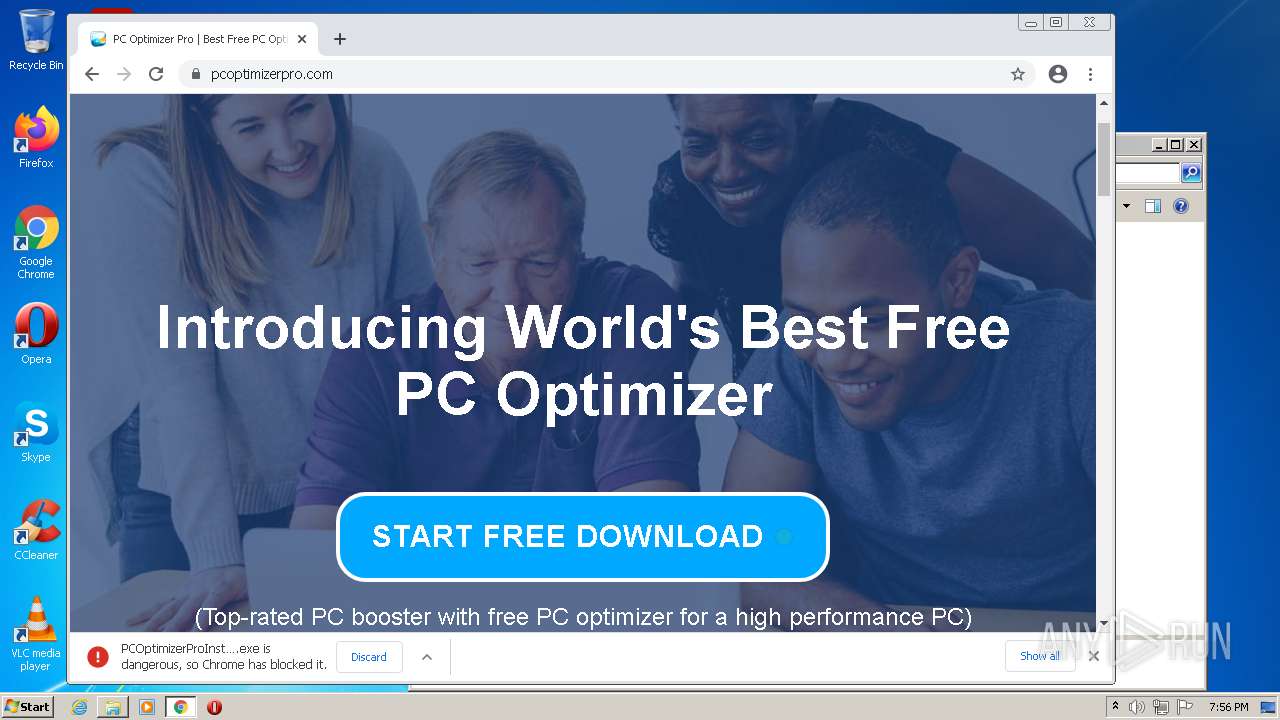
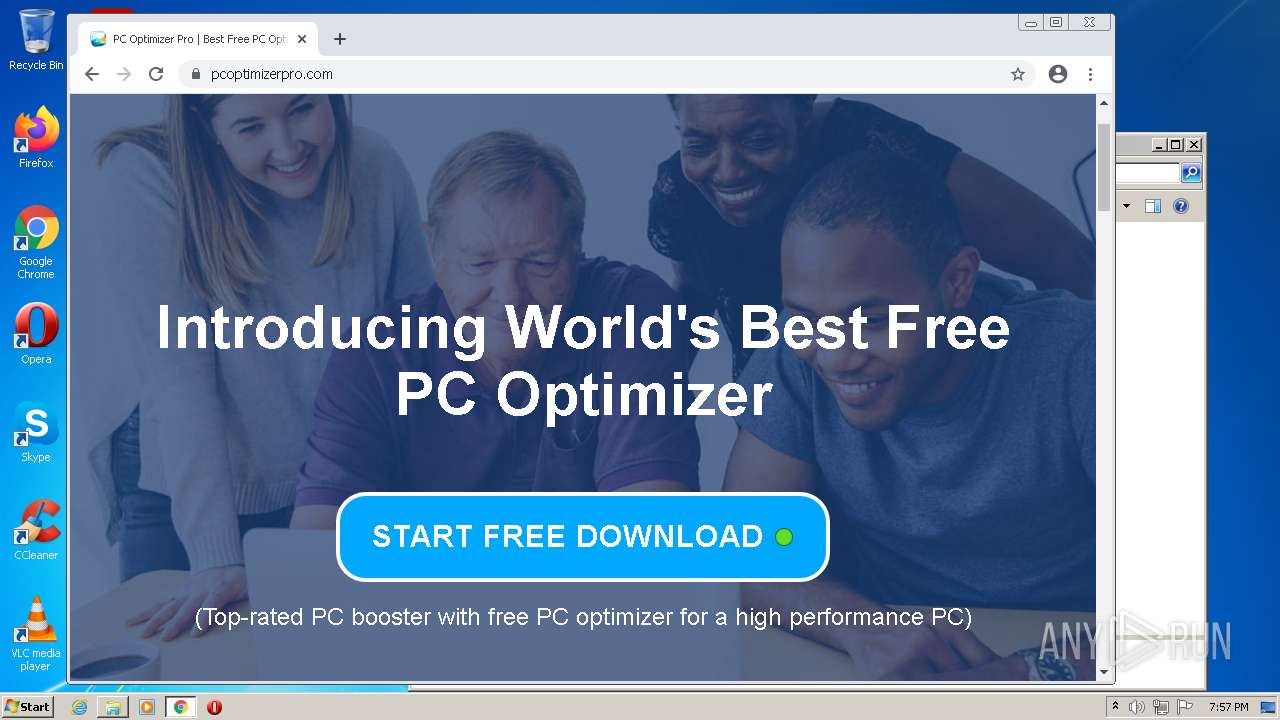
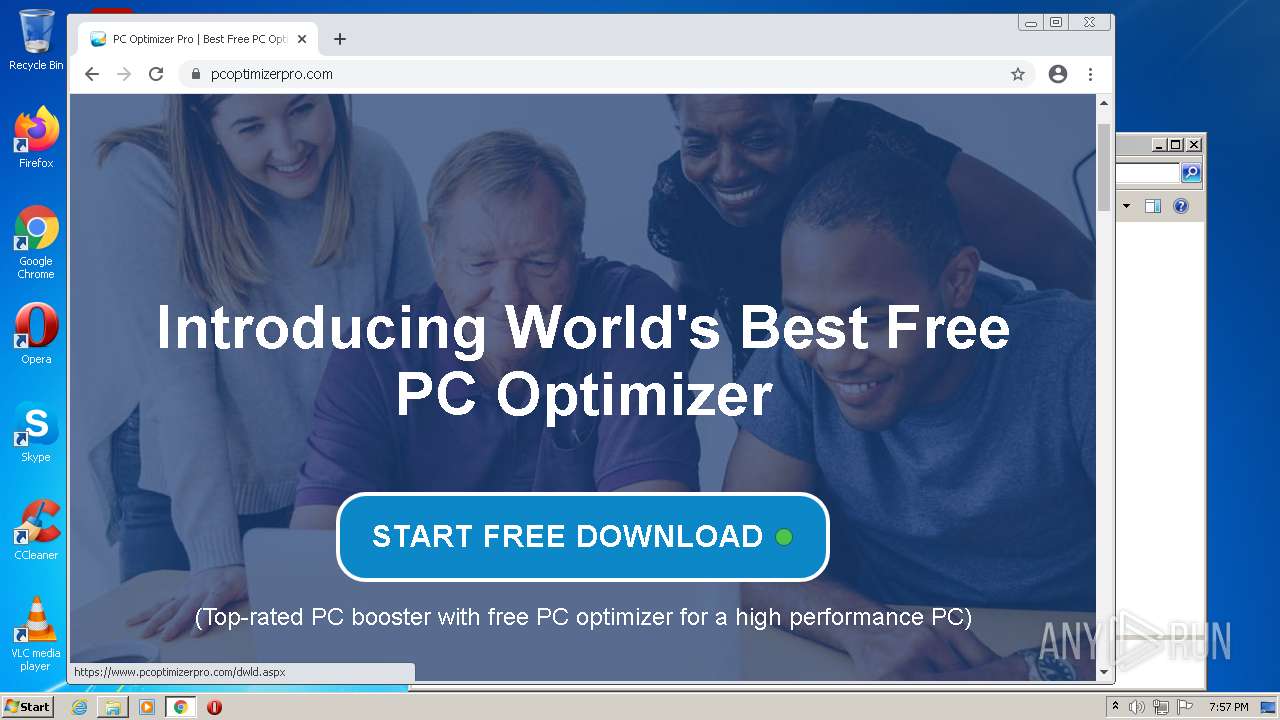
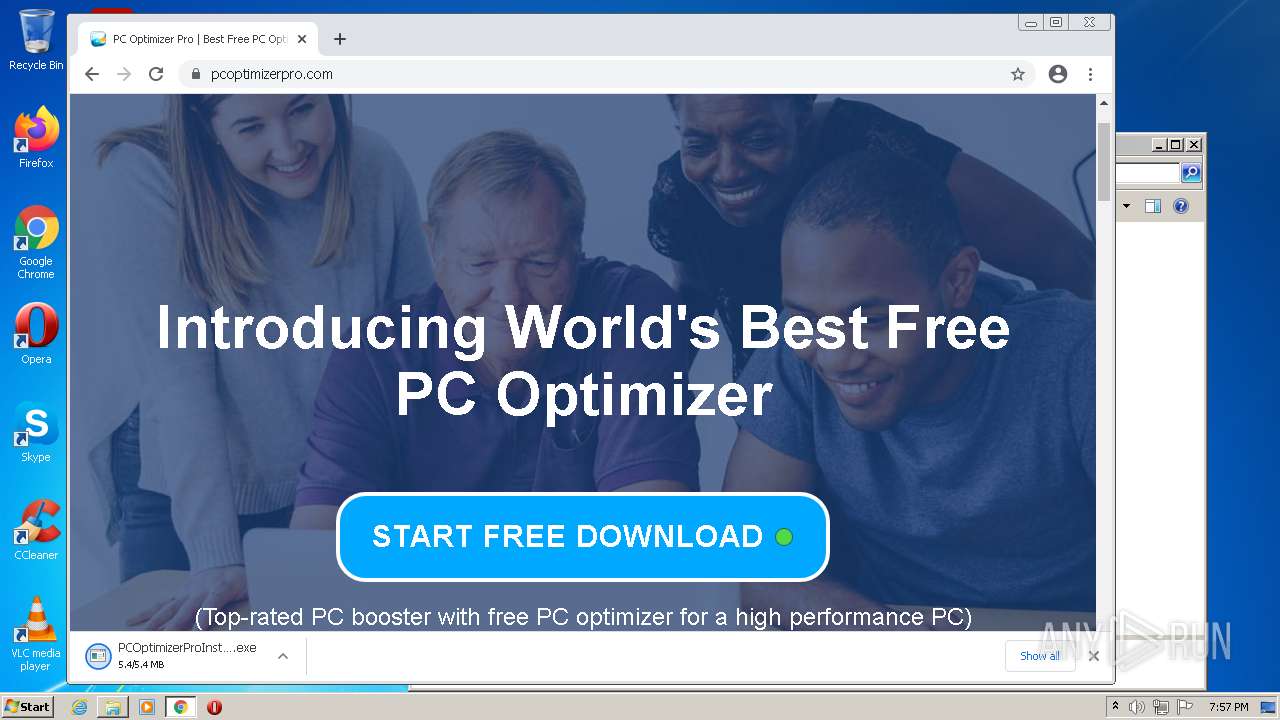
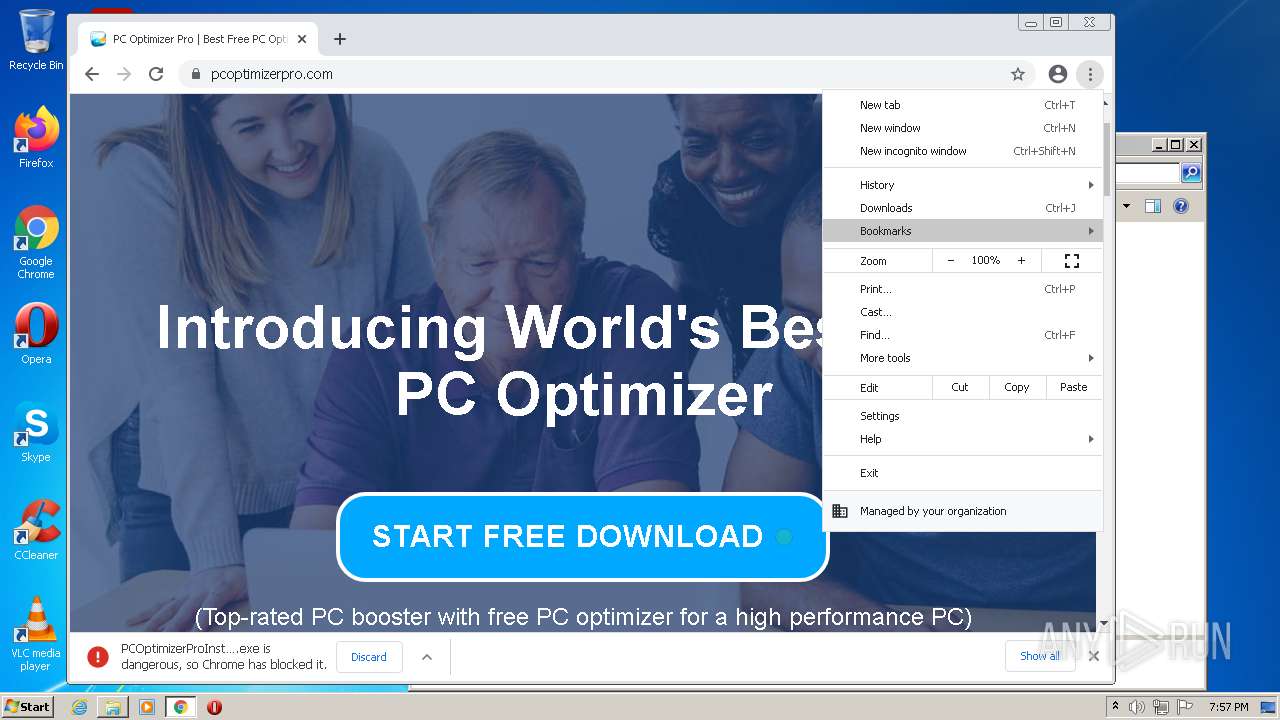
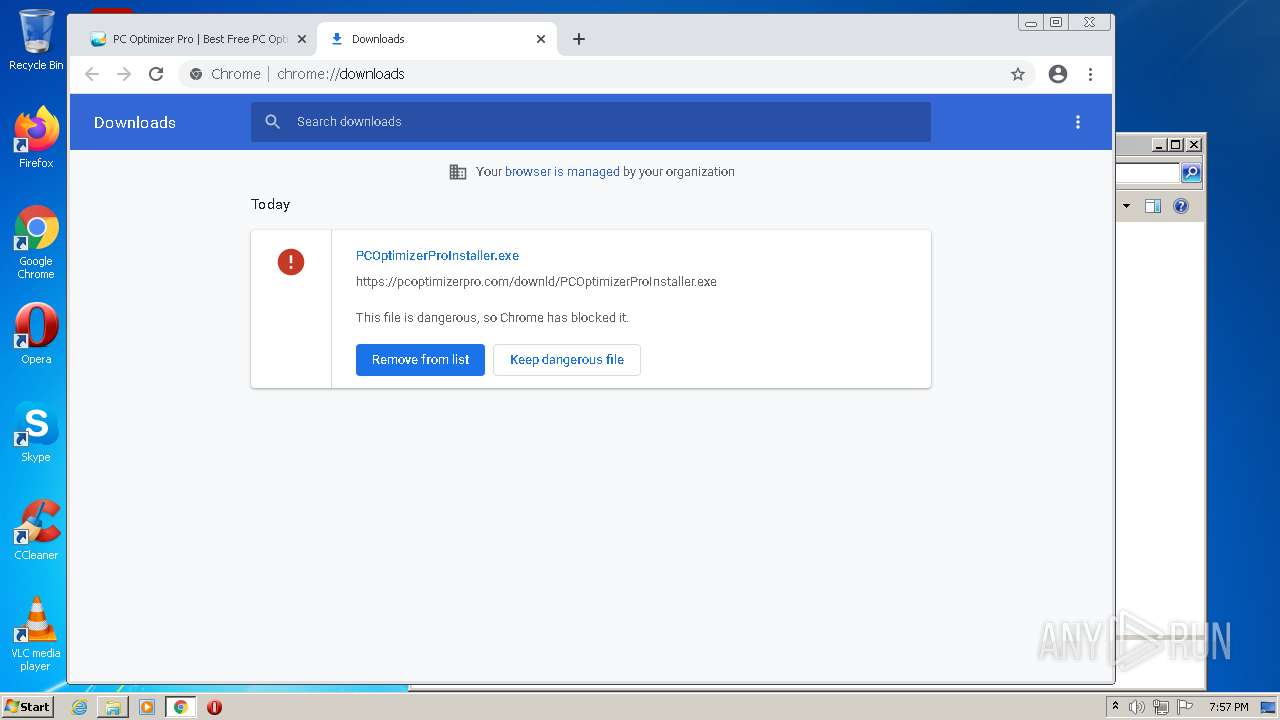
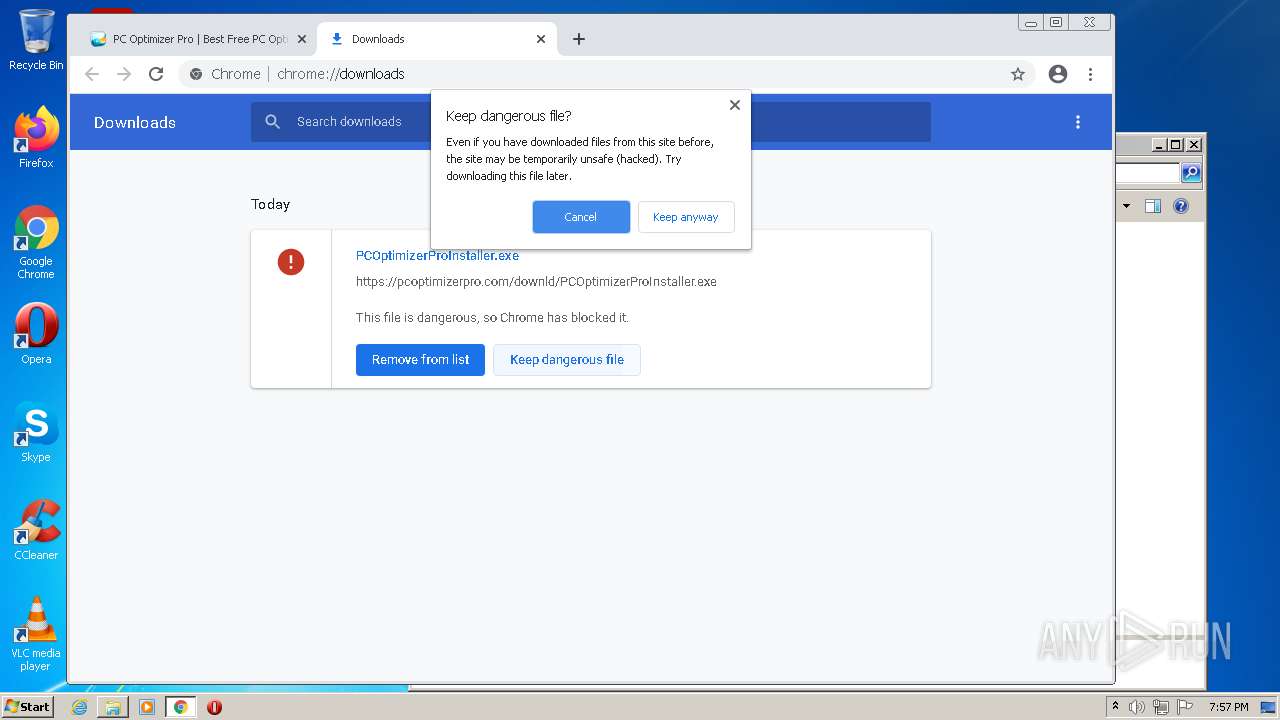
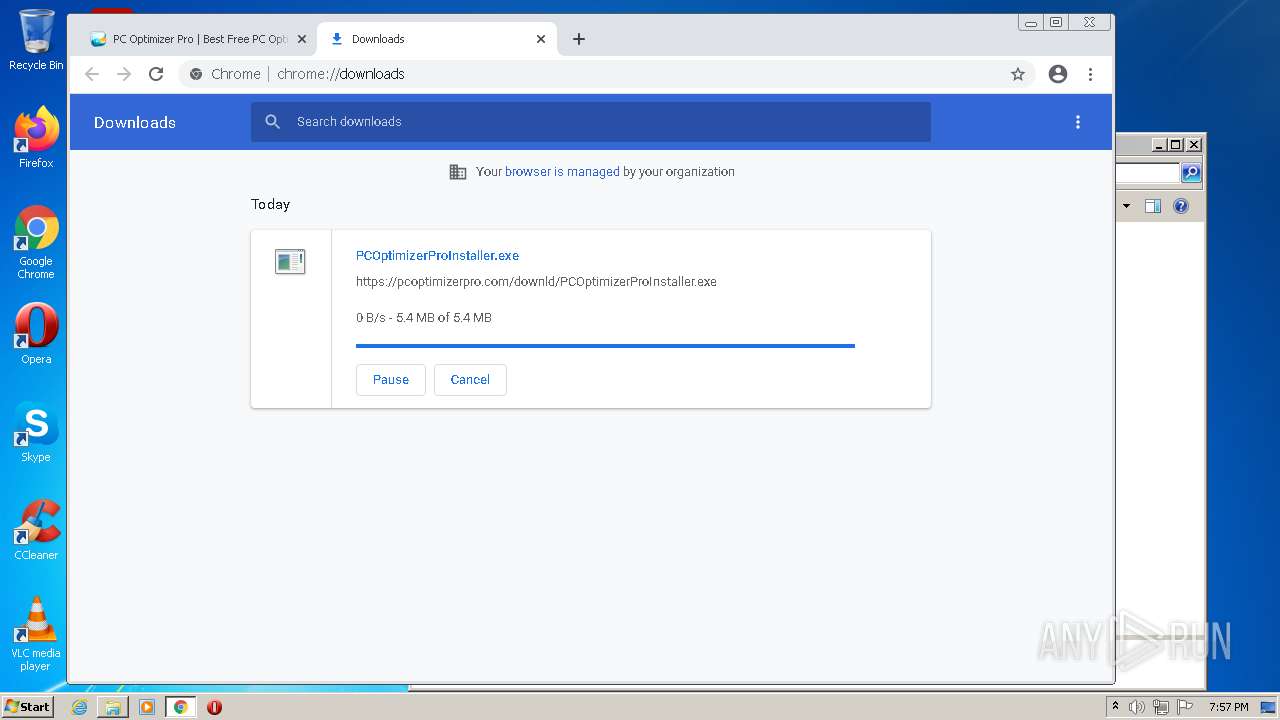
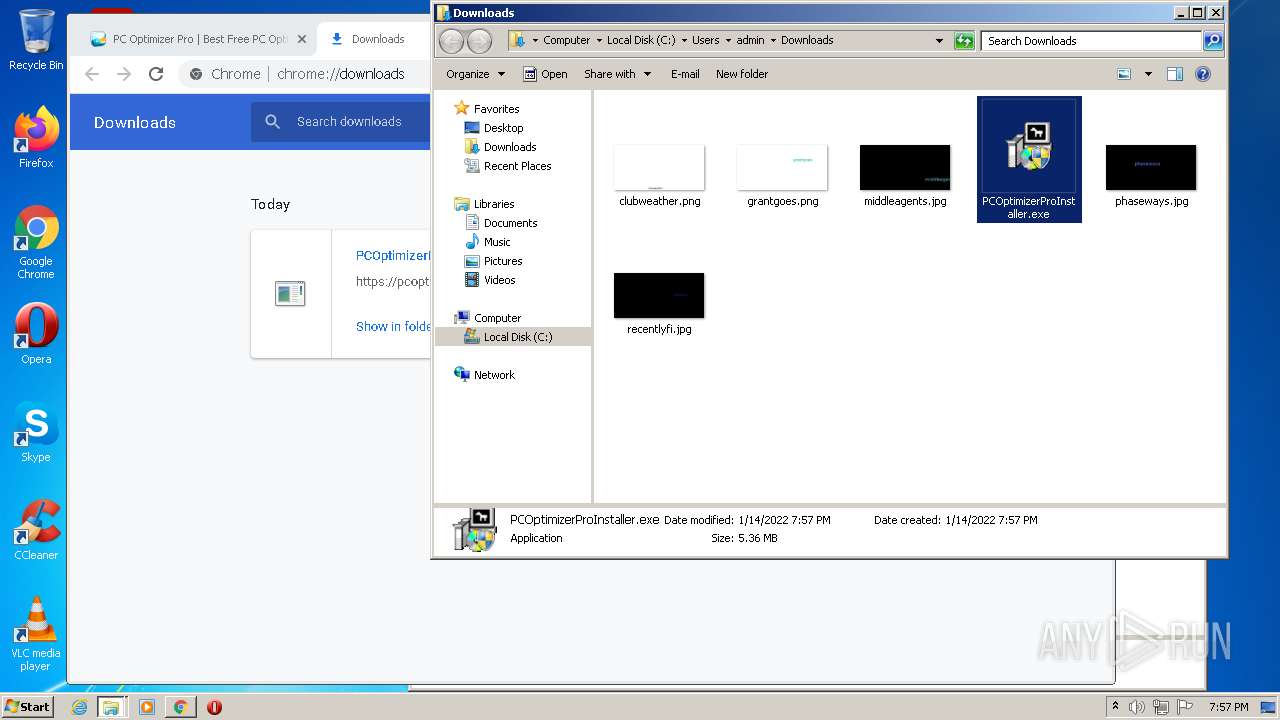
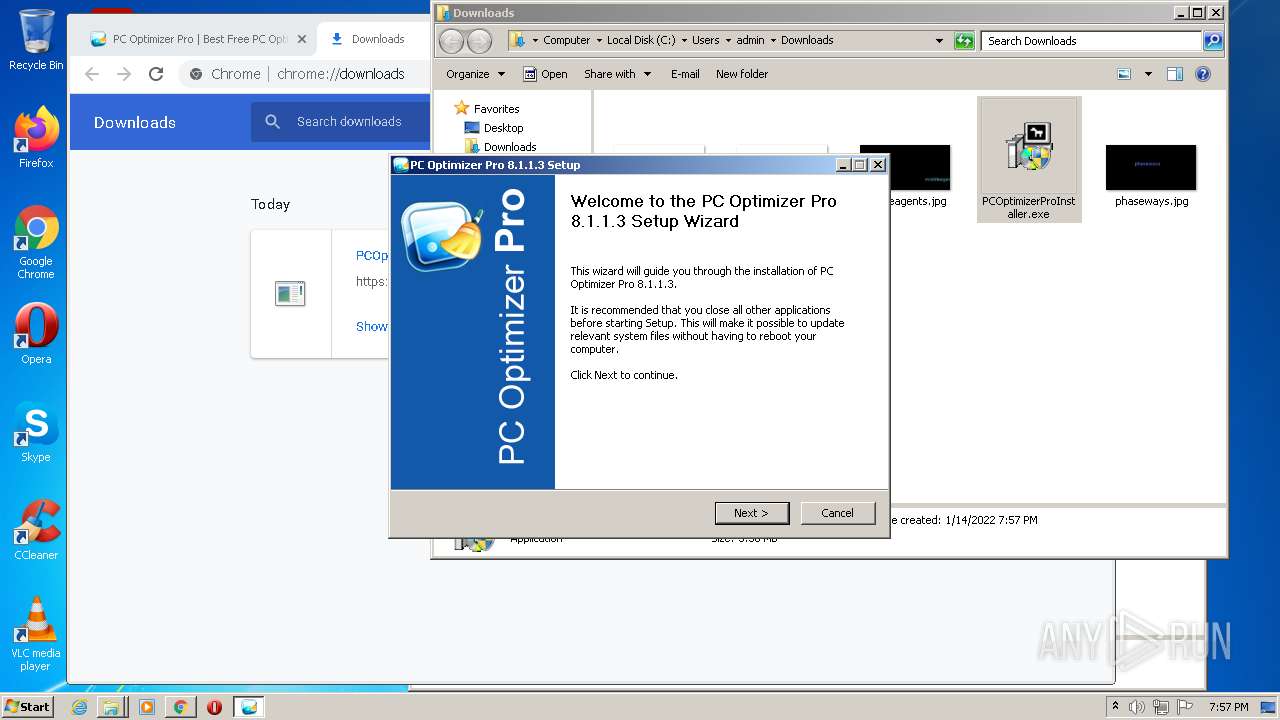
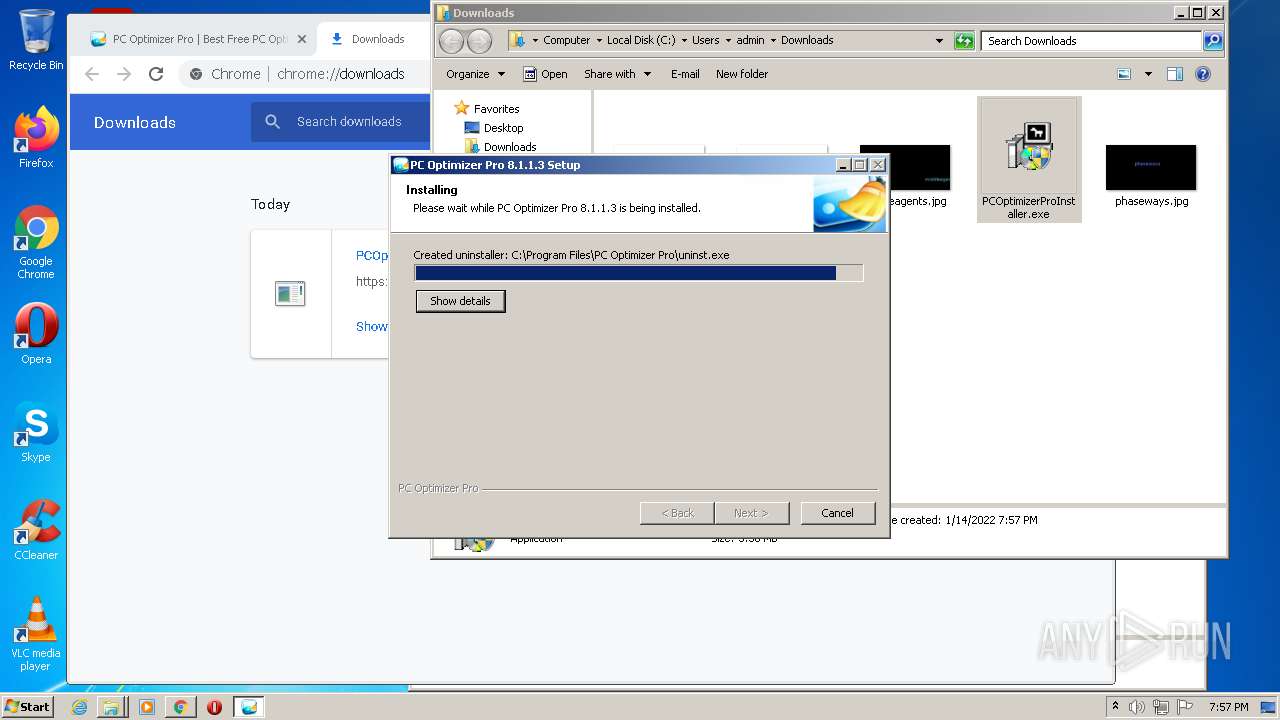
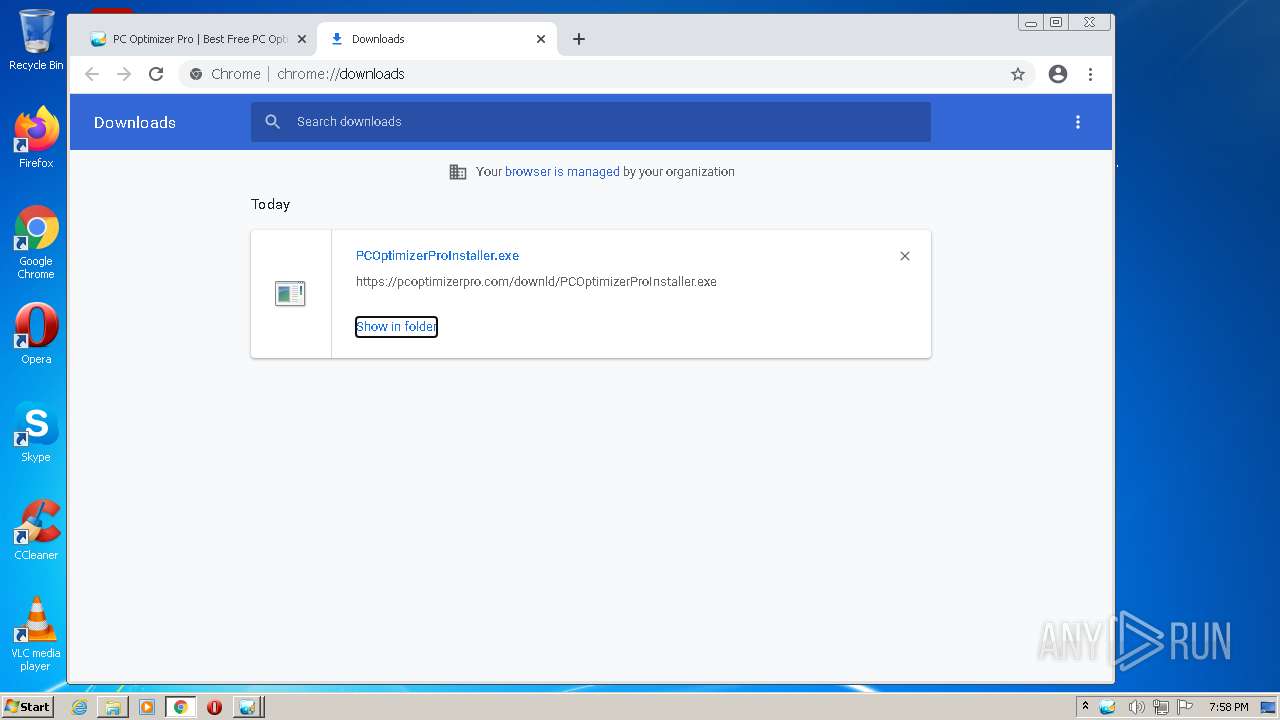
- PCOptimizerProInstaller.exe (PID: 1348)
- PCOptimizerProInstaller.exe (PID: 2336)
- PCOptimizerProSetup_STD.exe (PID: 3800)
- StartApps.exe (PID: 3540)
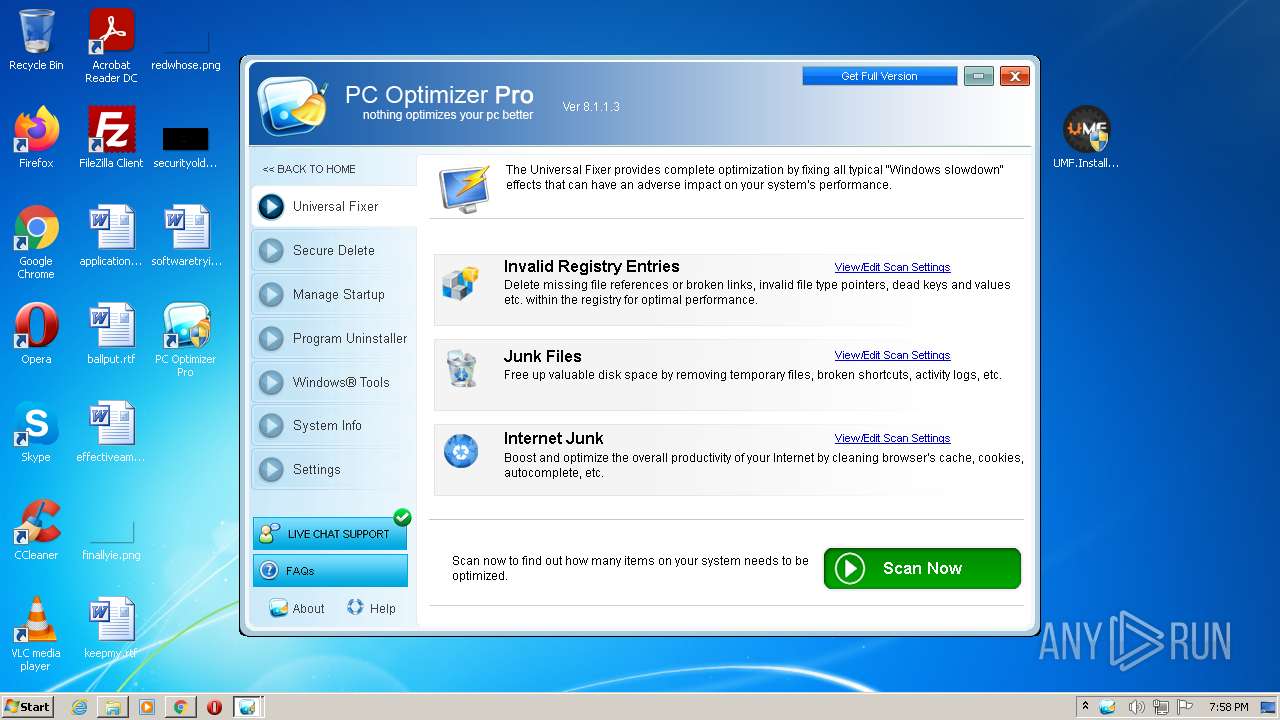
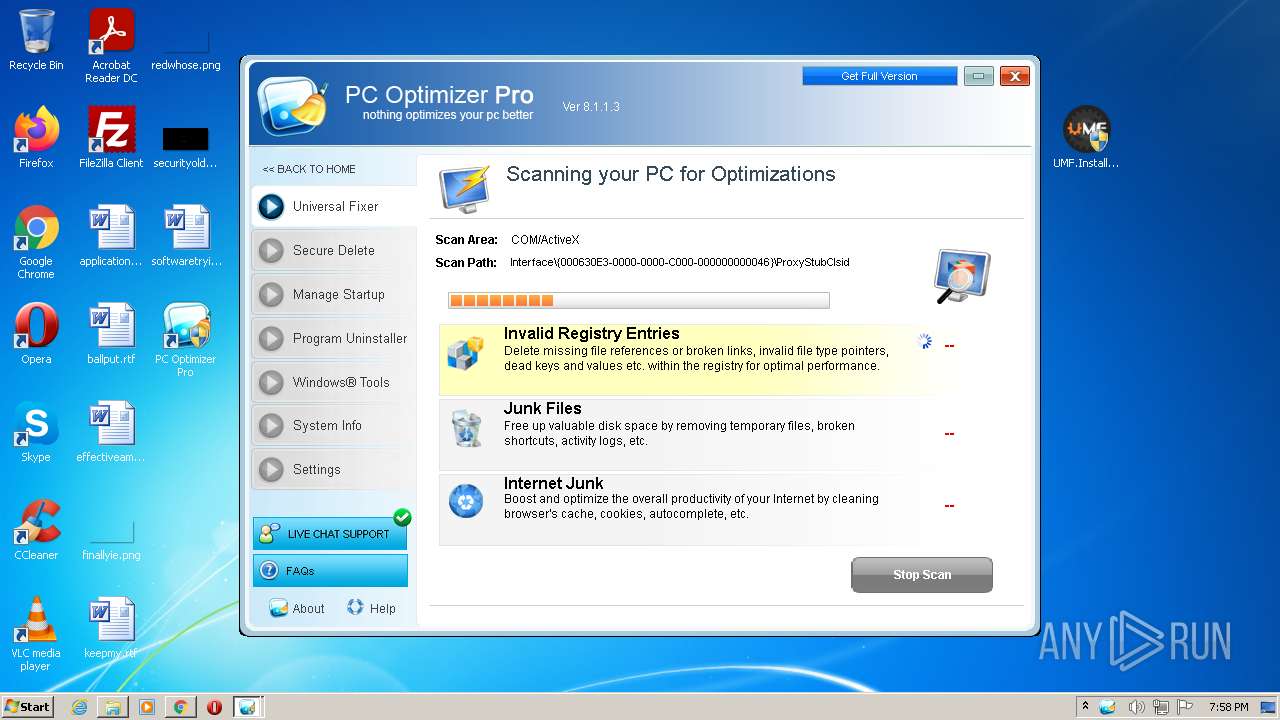
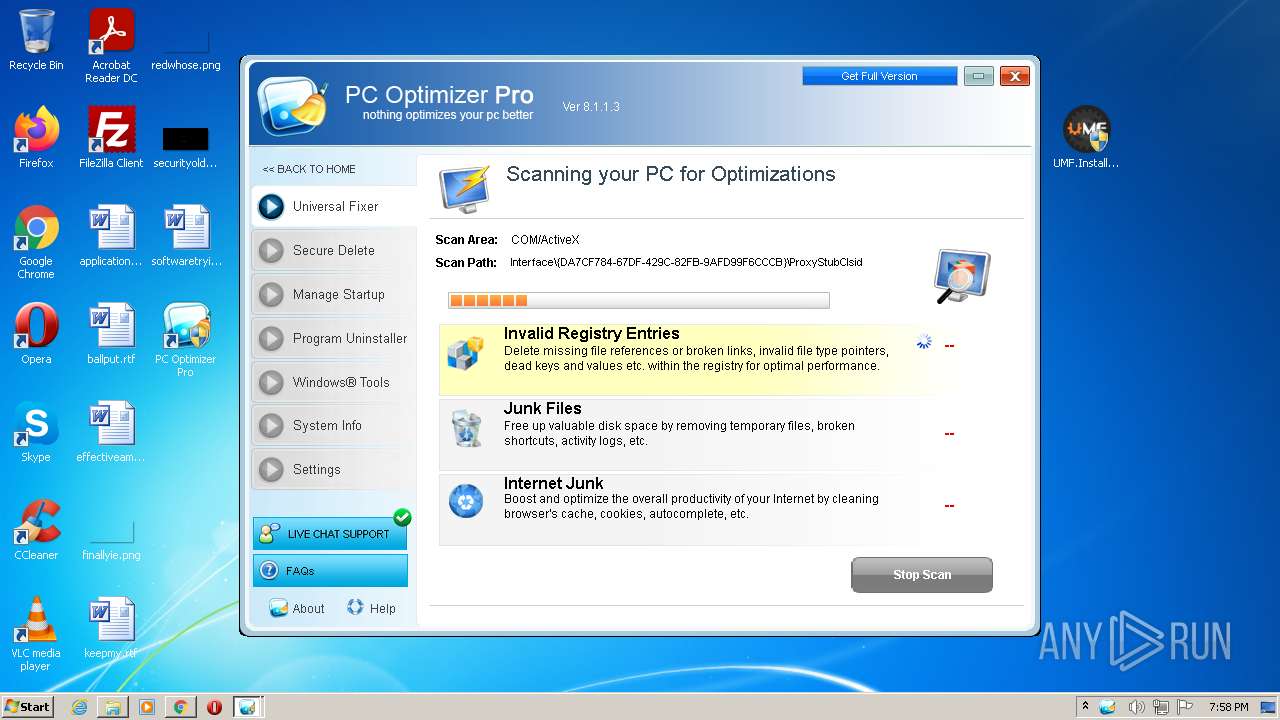
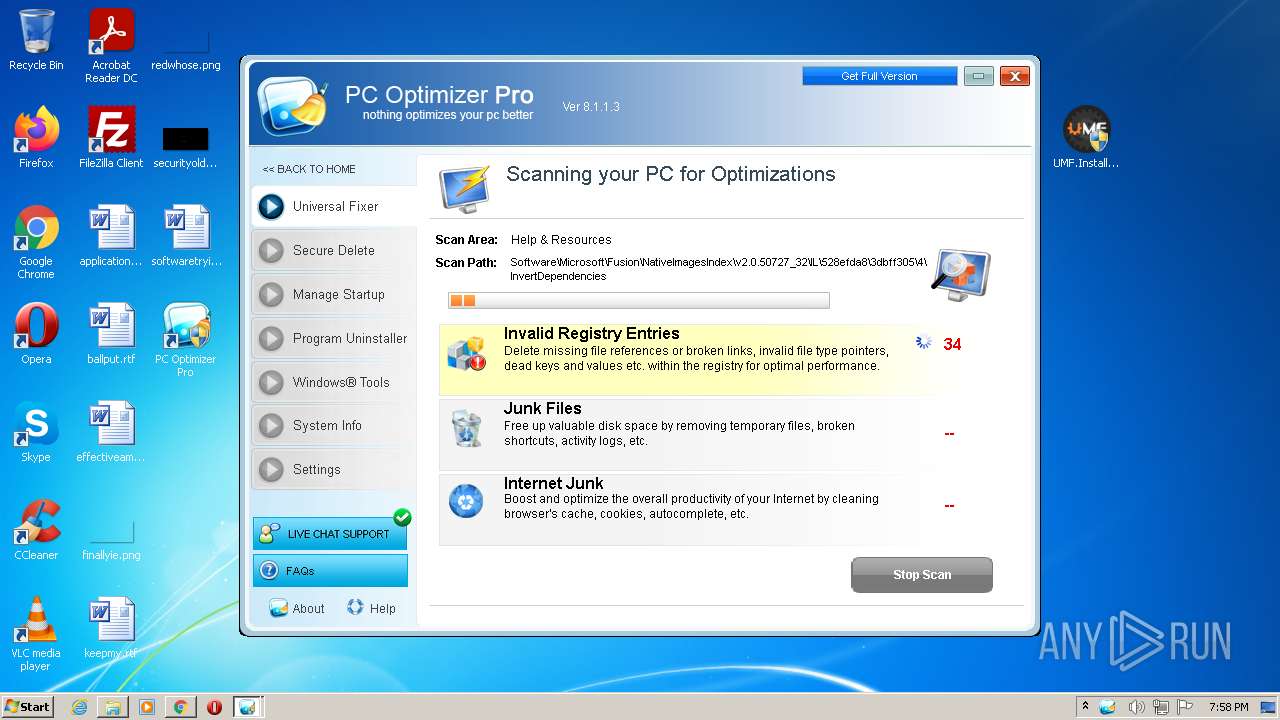
- PCOptimizerPro.exe (PID: 1944)
- PCOptimizerPro.exe (PID: 3836)
- PCOptimizerPro.exe (PID: 3752)
Loads dropped or rewritten executable
- PCOptimizerProSetup_STD.exe (PID: 3800)
- PCOptimizerProInstaller.exe (PID: 2336)
- regsvr32.exe (PID: 3804)
Registers / Runs the DLL via REGSVR32.EXE
- PCOptimizerProSetup_STD.exe (PID: 3800)
Changes settings of System certificates
- PCOptimizerProSetup_STD.exe (PID: 3800)
Loads the Task Scheduler DLL interface
- PCOptimizerPro.exe (PID: 3752)
- PCOptimizerPro.exe (PID: 1944)
SUSPICIOUS
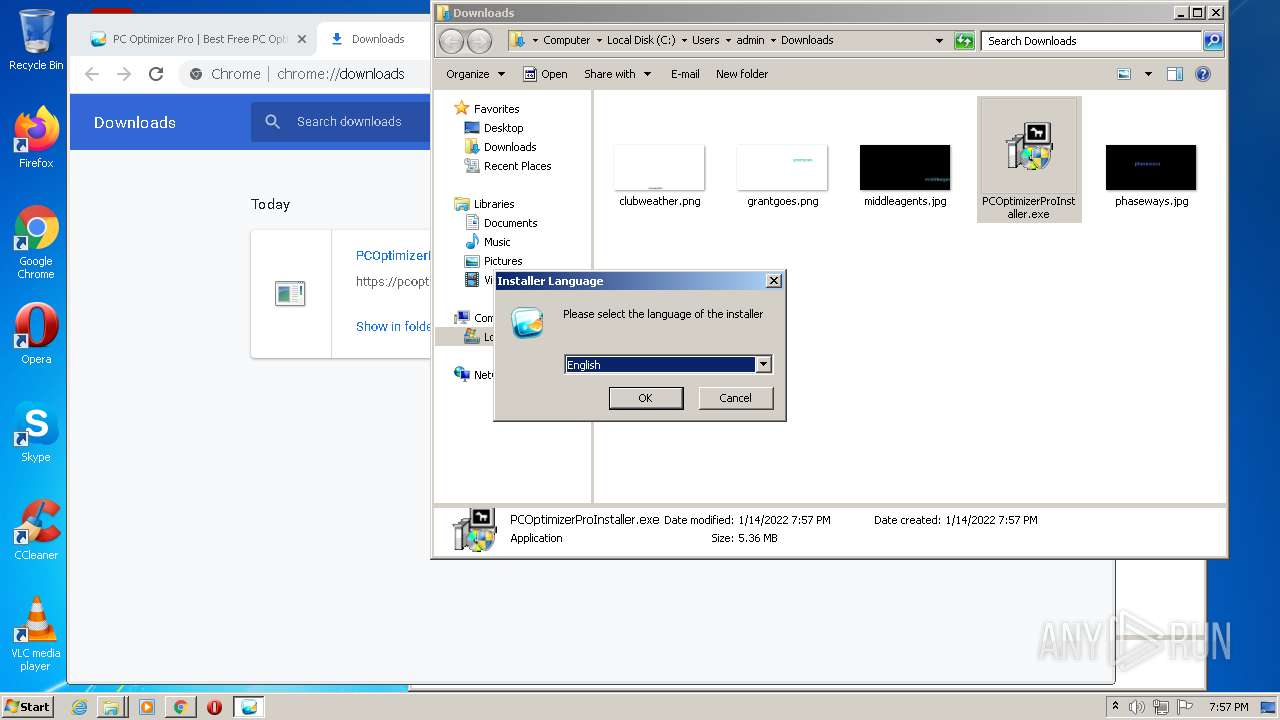
Checks supported languages
- UMF.Installer.exe (PID: 2268)
- UMF.Installer.exe (PID: 3612)
- WinRAR.exe (PID: 2396)
- MSASCui.exe (PID: 1968)
- UMF.Installer.exe (PID: 1972)
- PCOptimizerProInstaller.exe (PID: 2336)
- PCOptimizerProSetup_STD.exe (PID: 3800)
- StartApps.exe (PID: 3540)
- PCOptimizerPro.exe (PID: 1944)
- PCOptimizerPro.exe (PID: 3752)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2396)
Reads the computer name
- UMF.Installer.exe (PID: 2268)
- UMF.Installer.exe (PID: 3612)
- UMF.Installer.exe (PID: 1972)
- WinRAR.exe (PID: 2396)
- PCOptimizerProInstaller.exe (PID: 2336)
- PCOptimizerProSetup_STD.exe (PID: 3800)
- StartApps.exe (PID: 3540)
- PCOptimizerPro.exe (PID: 1944)
- PCOptimizerPro.exe (PID: 3752)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2396)
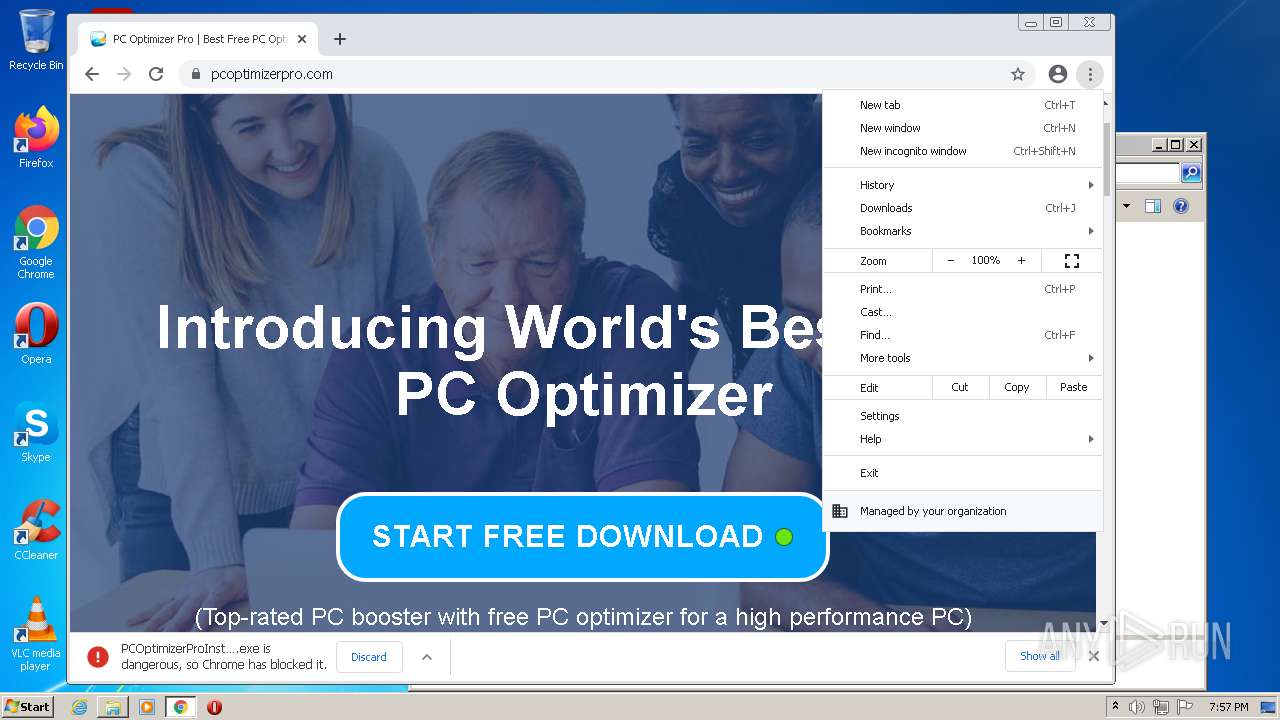
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3648)
- PCOptimizerProInstaller.exe (PID: 2336)
- PCOptimizerProSetup_STD.exe (PID: 3800)
- PCOptimizerPro.exe (PID: 3752)
Drops a file with too old compile date
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3648)
- PCOptimizerProSetup_STD.exe (PID: 3800)
- PCOptimizerProInstaller.exe (PID: 2336)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3840)
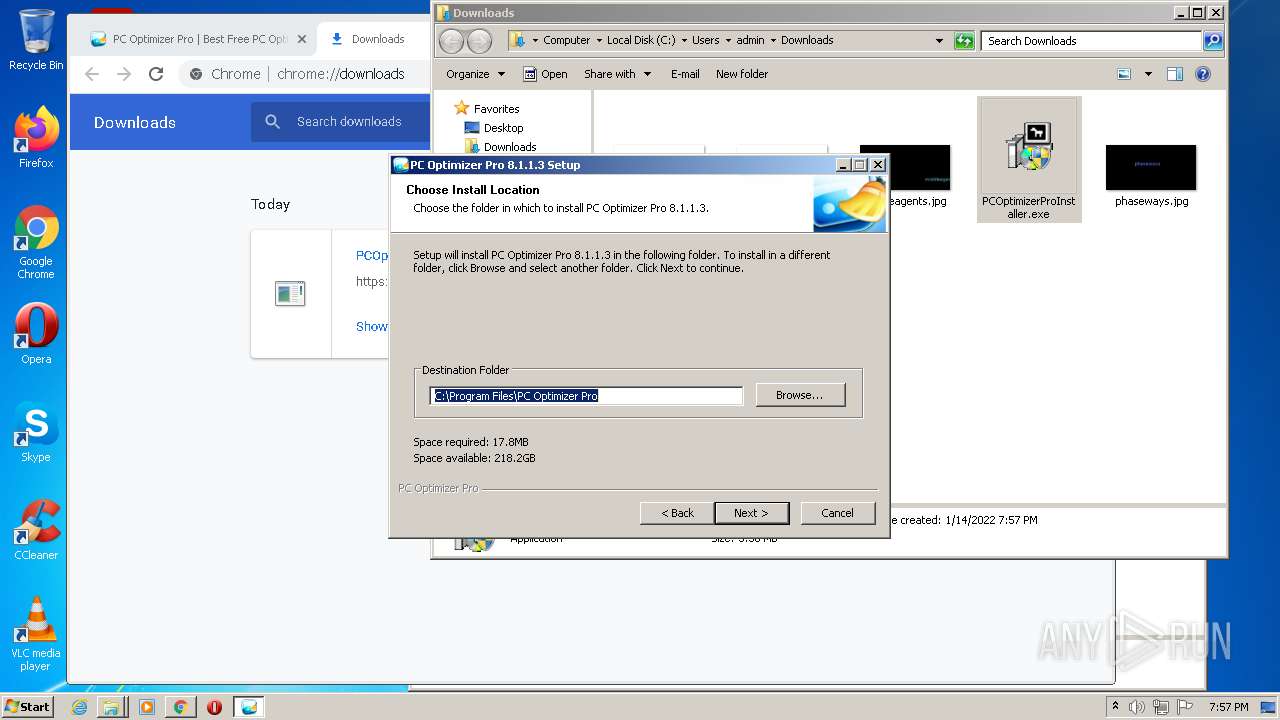
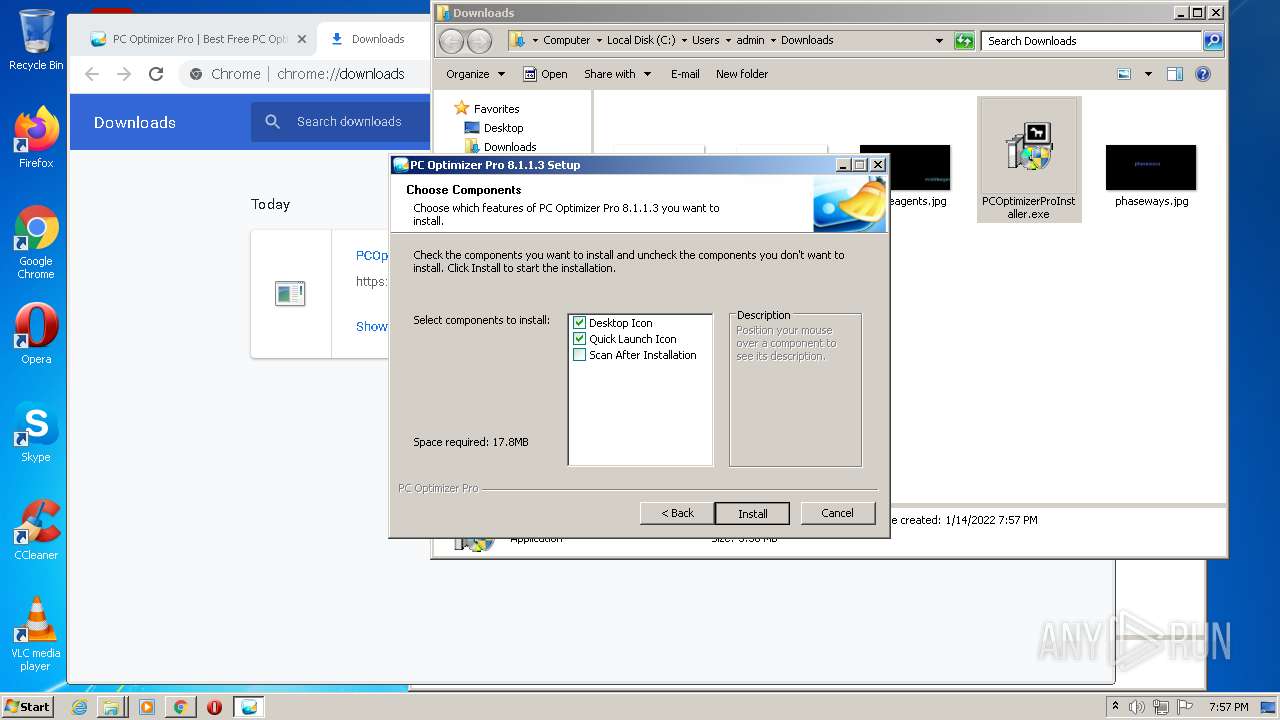
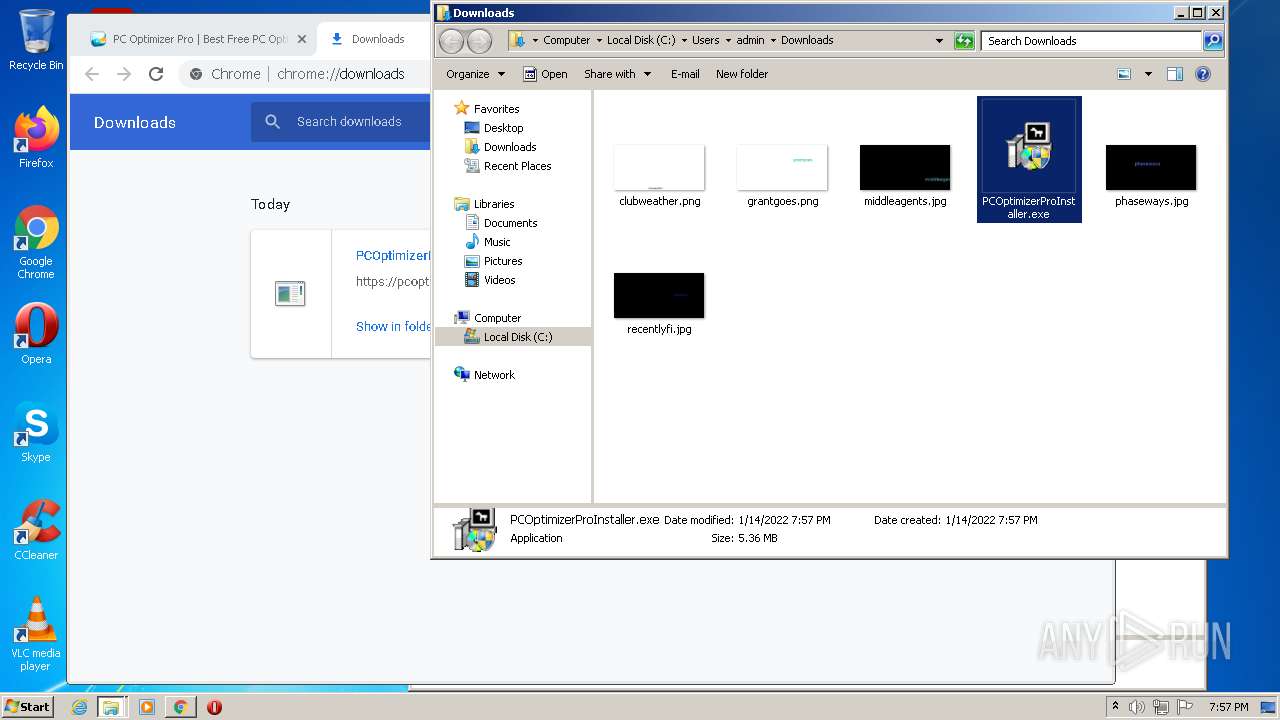
Creates a directory in Program Files
- PCOptimizerProSetup_STD.exe (PID: 3800)
Creates files in the program directory
- PCOptimizerProSetup_STD.exe (PID: 3800)
- PCOptimizerPro.exe (PID: 1944)
- PCOptimizerPro.exe (PID: 3752)
Drops a file that was compiled in debug mode
- PCOptimizerProSetup_STD.exe (PID: 3800)
- PCOptimizerPro.exe (PID: 3752)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3804)
Creates files in the user directory
- PCOptimizerProSetup_STD.exe (PID: 3800)
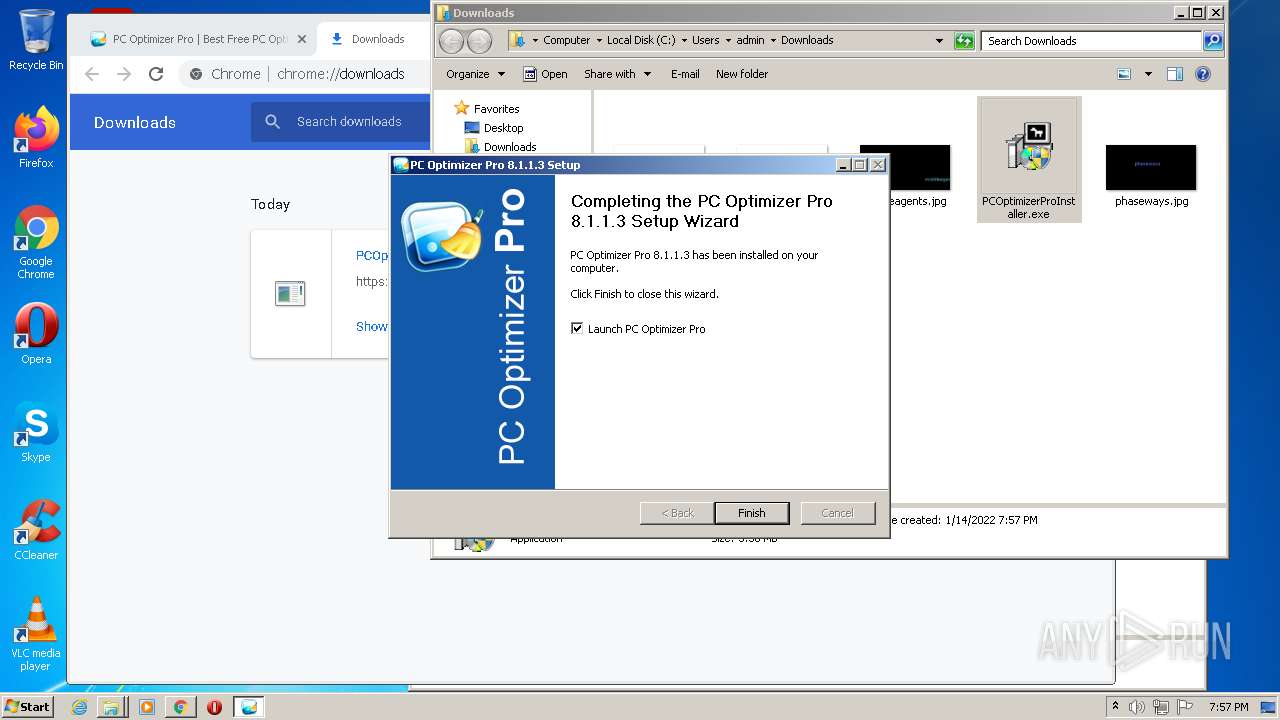
Creates a software uninstall entry
- PCOptimizerProSetup_STD.exe (PID: 3800)
Adds / modifies Windows certificates
- PCOptimizerProSetup_STD.exe (PID: 3800)
Reads CPU info
- PCOptimizerPro.exe (PID: 1944)
- PCOptimizerPro.exe (PID: 3752)
Creates files in the Windows directory
- PCOptimizerPro.exe (PID: 3752)
Searches for installed software
- PCOptimizerPro.exe (PID: 3752)
- PCOptimizerPro.exe (PID: 1944)
INFO
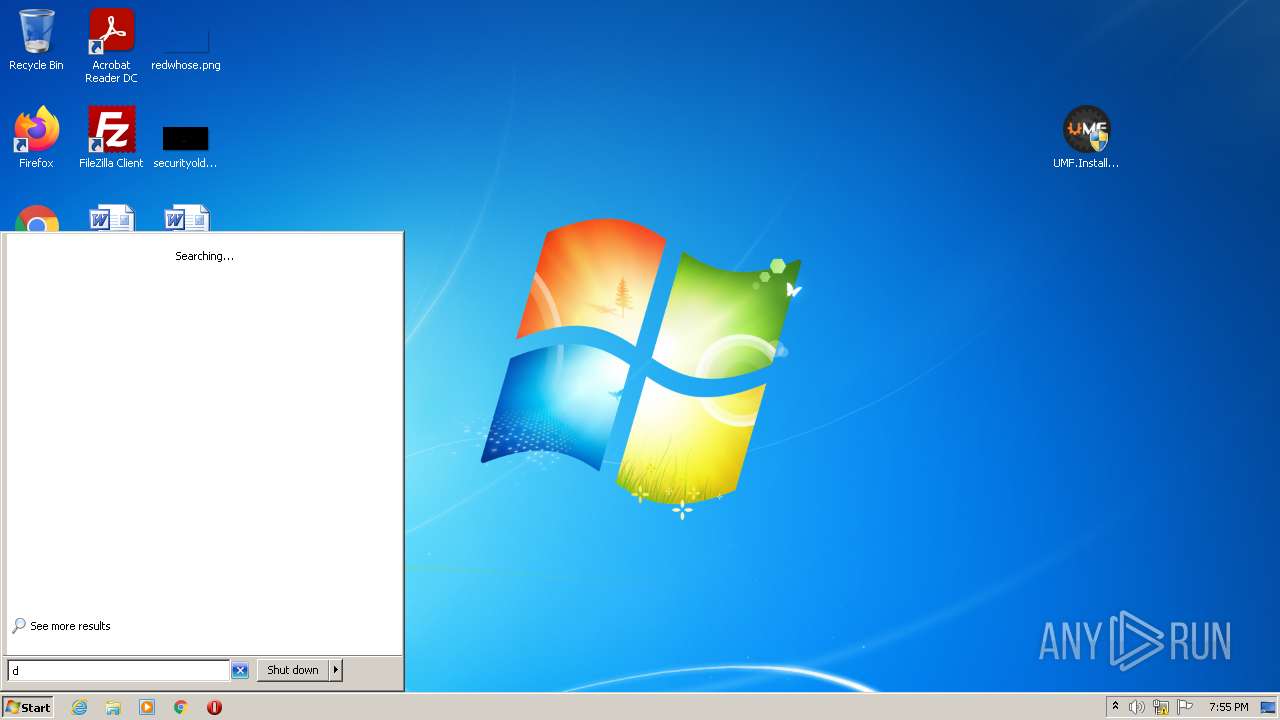
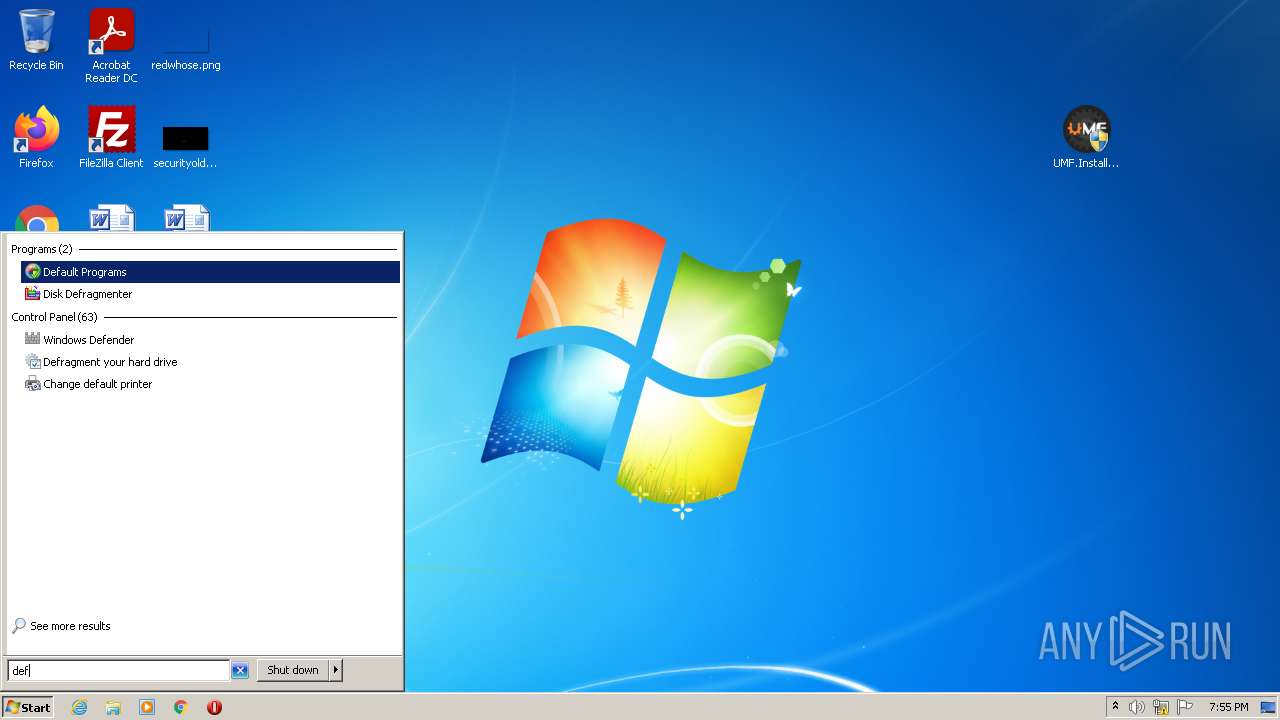
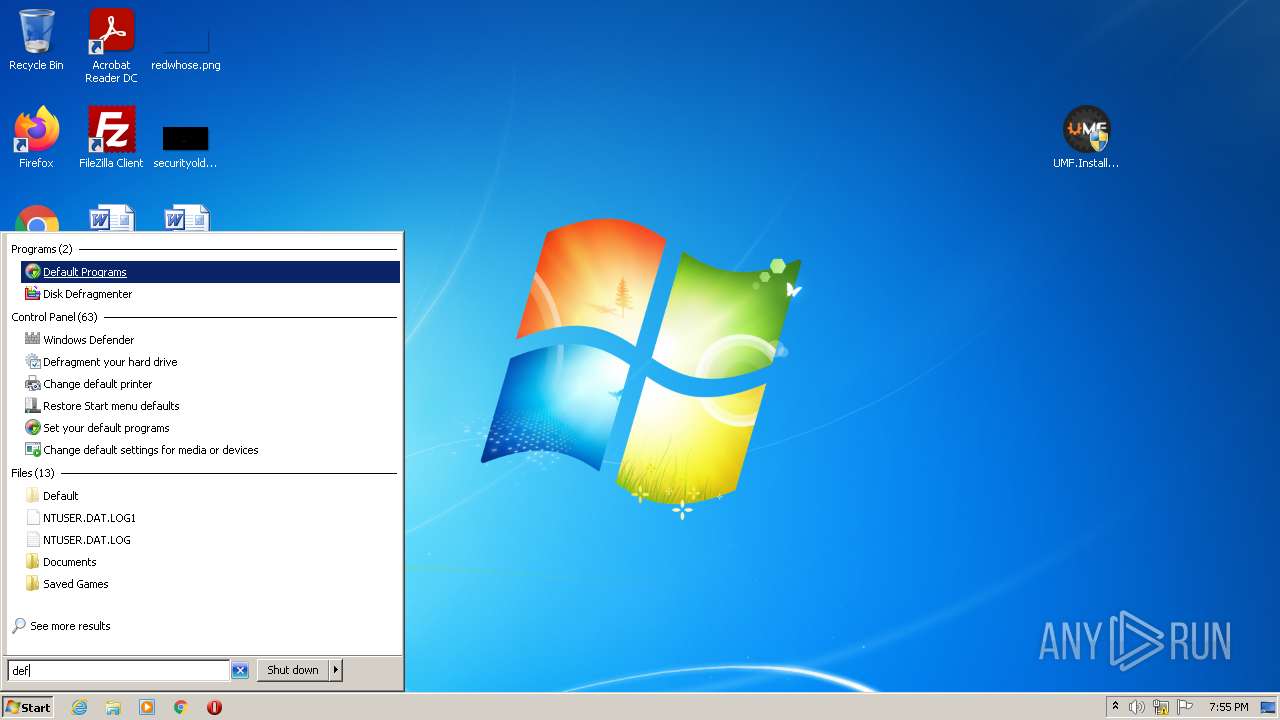
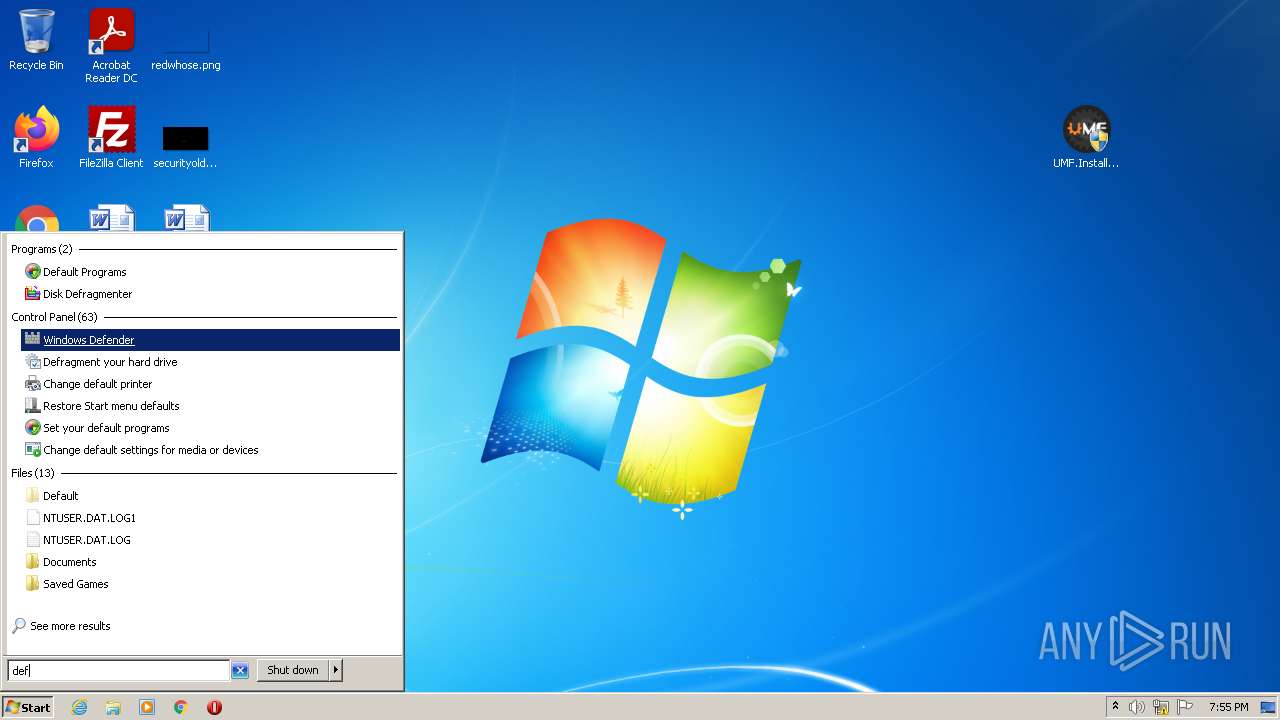
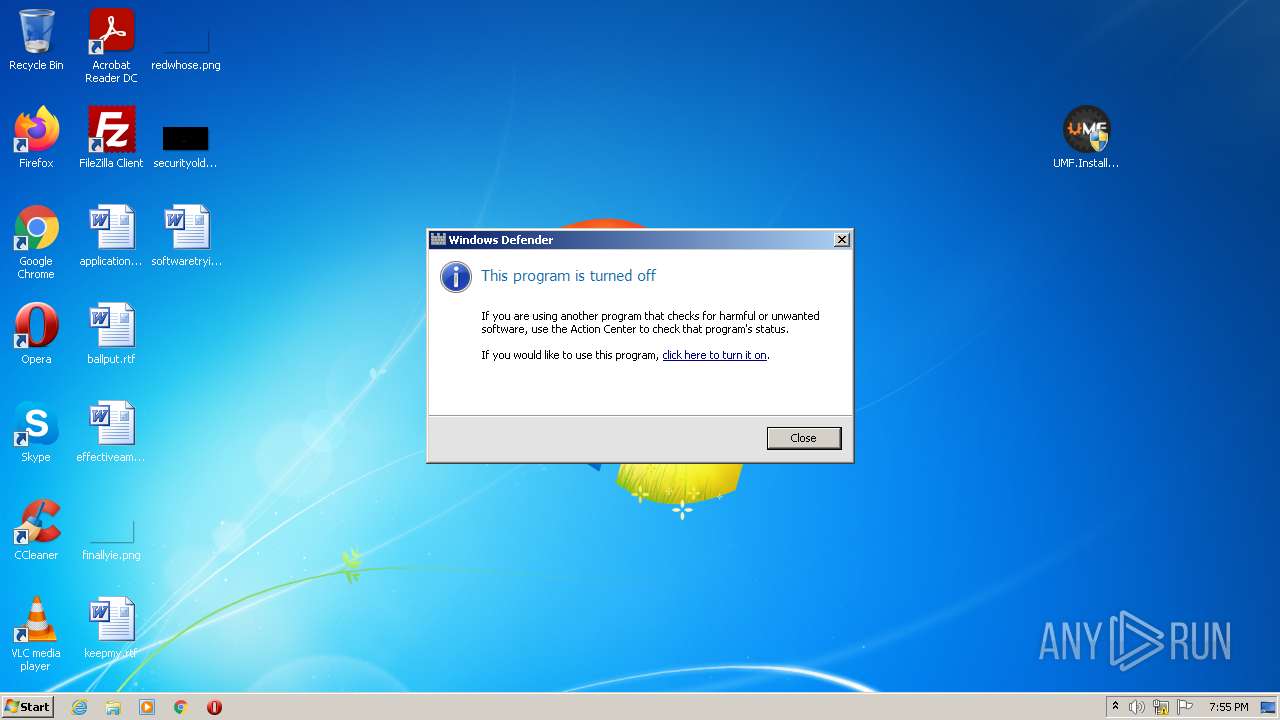
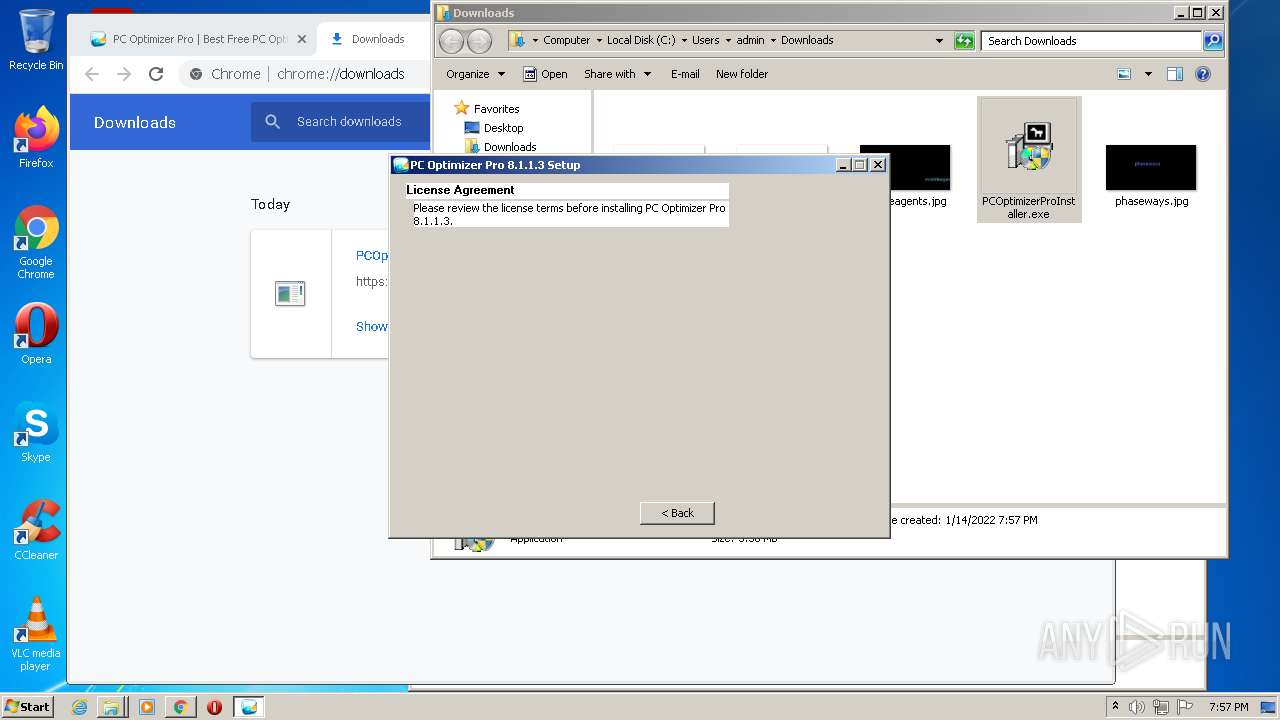
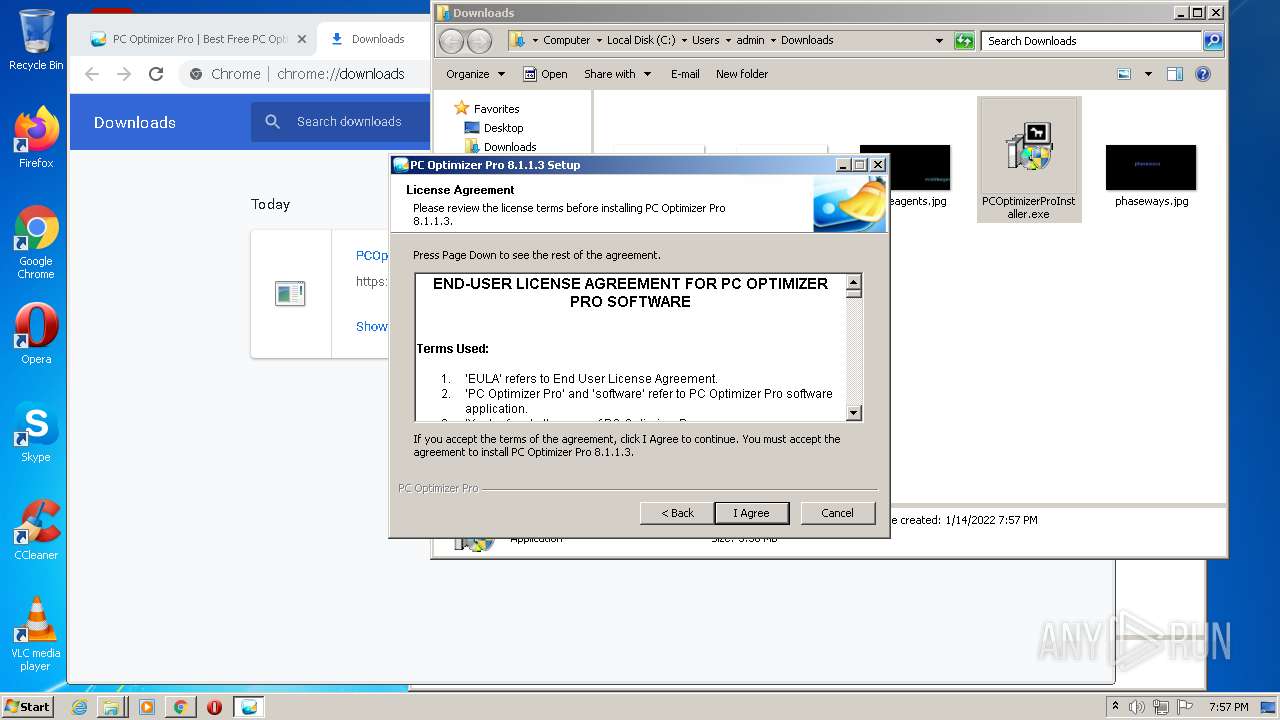
Manual execution by user
- MSASCui.exe (PID: 1968)
- UMF.Installer.exe (PID: 2800)
- UMF.Installer.exe (PID: 1972)
- chrome.exe (PID: 3840)
- explorer.exe (PID: 2236)
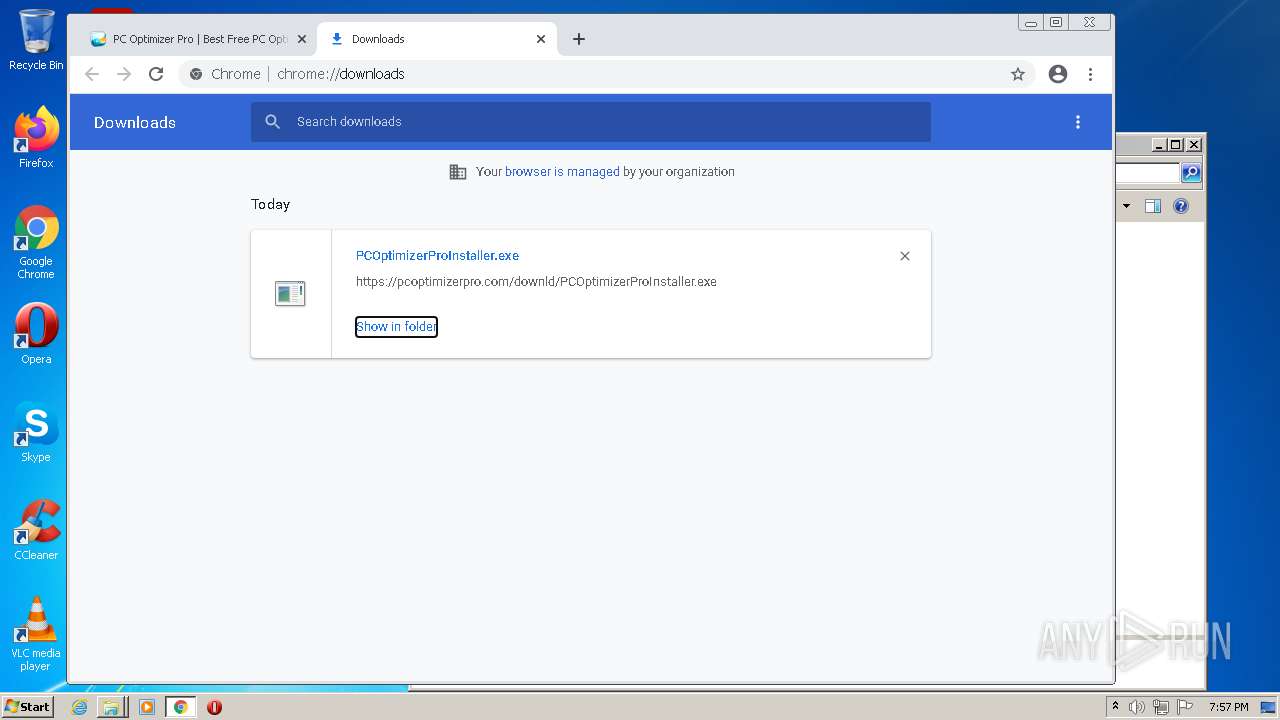
- PCOptimizerProInstaller.exe (PID: 1348)
- PCOptimizerProInstaller.exe (PID: 2336)
- PCOptimizerPro.exe (PID: 3752)
- PCOptimizerPro.exe (PID: 3836)
Checks supported languages
- explorer.exe (PID: 2236)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 2564)
- chrome.exe (PID: 1460)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 3316)
- chrome.exe (PID: 3276)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 1292)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 3212)
- chrome.exe (PID: 3664)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 576)
- chrome.exe (PID: 3512)
- chrome.exe (PID: 2108)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 1656)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 1780)
- chrome.exe (PID: 2080)
- chrome.exe (PID: 3368)
- chrome.exe (PID: 3516)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 460)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 1668)
- chrome.exe (PID: 3284)
- chrome.exe (PID: 1004)
- chrome.exe (PID: 3044)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 576)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 3664)
- chrome.exe (PID: 3236)
- chrome.exe (PID: 2512)
- chrome.exe (PID: 392)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 796)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 932)
- chrome.exe (PID: 2364)
- regsvr32.exe (PID: 3804)
- chrome.exe (PID: 1292)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 2696)
- chrome.exe (PID: 1656)
Reads the computer name
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 2564)
- explorer.exe (PID: 2236)
- chrome.exe (PID: 2316)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 1656)
- chrome.exe (PID: 1004)
- chrome.exe (PID: 1668)
- chrome.exe (PID: 3576)
- chrome.exe (PID: 3672)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 2364)
Application launched itself
- chrome.exe (PID: 3840)
Reads the hosts file
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3648)
Reads settings of System Certificates
- chrome.exe (PID: 3648)
- chrome.exe (PID: 3840)
- PCOptimizerProSetup_STD.exe (PID: 3800)
- PCOptimizerPro.exe (PID: 1944)
- PCOptimizerPro.exe (PID: 3752)
Reads the date of Windows installation
- chrome.exe (PID: 1668)
Checks Windows Trust Settings
- chrome.exe (PID: 3840)
- PCOptimizerProSetup_STD.exe (PID: 3800)
- PCOptimizerPro.exe (PID: 1944)
- PCOptimizerPro.exe (PID: 3752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | UMF.Installer.exe |
|---|---|
| ZipUncompressedSize: | 10467840 |
| ZipCompressedSize: | 9118188 |
| ZipCRC: | 0x7d65cb12 |
| ZipModifyDate: | 2021:12:26 02:45:16 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
137
Monitored processes
73
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1044,15437401599744611575,11702713775961535749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,15437401599744611575,11702713775961535749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4044 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,15437401599744611575,11702713775961535749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4168 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1044,15437401599744611575,11702713775961535749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2796 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,15437401599744611575,11702713775961535749,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=47 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3712 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1044,15437401599744611575,11702713775961535749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1044,15437401599744611575,11702713775961535749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4212 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1044,15437401599744611575,11702713775961535749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3760 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1044,15437401599744611575,11702713775961535749,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\Downloads\PCOptimizerProInstaller.exe" | C:\Users\admin\Downloads\PCOptimizerProInstaller.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Xportsoft.com Integrity Level: MEDIUM Description: PC Optimizer Pro Exit code: 3221226540 Version: 8.1.1.3 Modules
| |||||||||||||||
Total events
38 447
Read events
37 846
Write events
586
Delete events
15
Modification events
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\UMF.Installer_v0.53.5.zip | |||
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2396) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
25
Suspicious files
239
Text files
196
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61E1D555-F00.pma | — | |
MD5:— | SHA256:— | |||
| 2396 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2396.24771\UMF.Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 3840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF126fba.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF127131.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 2396 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2396.26296\UMF.Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 3648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 3840 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF126fd9.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
94
DNS requests
69
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 200 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1642189949&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigzrn7l.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | — | — | whitelisted |
860 | svchost.exe | HEAD | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1642189949&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigzrn7l.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 9.46 Kb | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
860 | svchost.exe | GET | 206 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1642189949&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigzrn7l.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 20.7 Kb | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
860 | svchost.exe | GET | 206 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1642189949&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigzrn7l.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 5.63 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3?cms_redirect=yes&mh=8t&mip=185.192.69.73&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1642189949&mv=m&mvi=5&pl=25&rmhost=r3---sn-aigzrn7l.gvt1.com&shardbypass=yes&smhost=r3---sn-aigzrn7e.gvt1.com | US | binary | 88.3 Kb | whitelisted |
860 | svchost.exe | GET | 302 | 142.250.185.110:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | html | 614 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
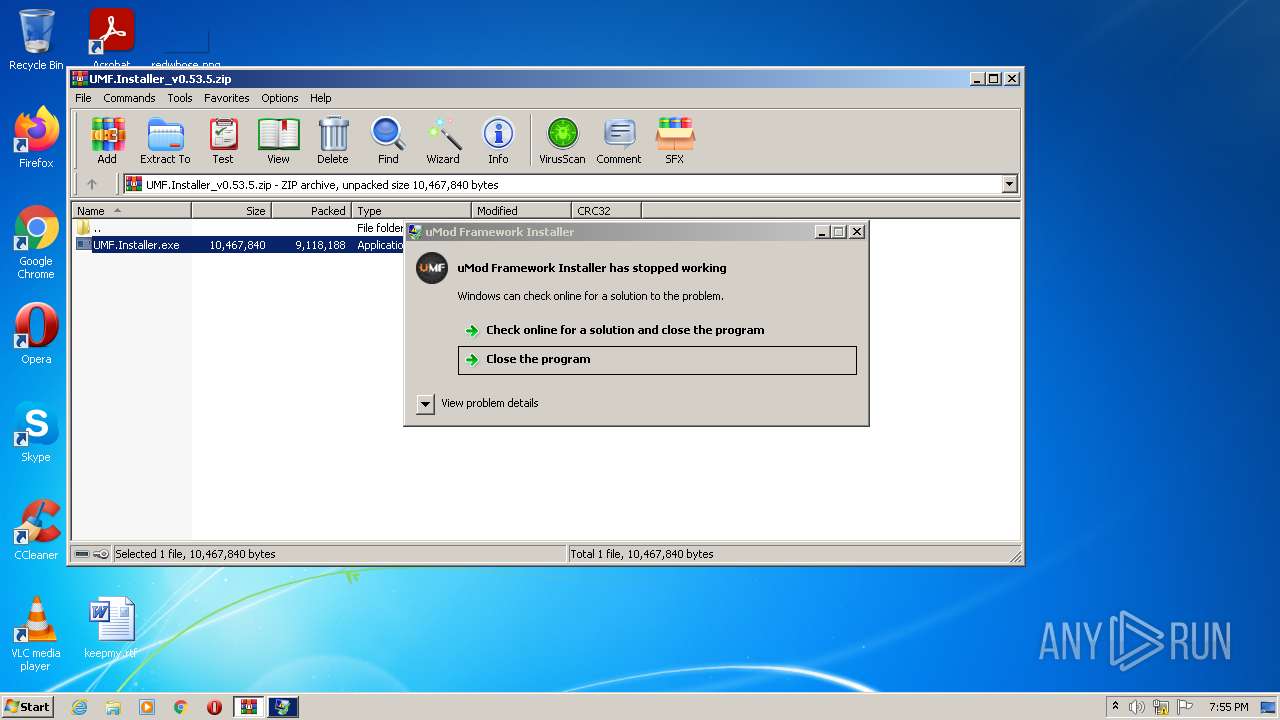
3124 | WerFault.exe | 52.168.117.172:443 | watson.microsoft.com | Microsoft Corporation | US | suspicious |
3648 | chrome.exe | 142.250.185.205:443 | accounts.google.com | Google Inc. | US | suspicious |
3648 | chrome.exe | 142.250.185.68:443 | www.google.com | Google Inc. | US | whitelisted |
3648 | chrome.exe | 142.250.185.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3648 | chrome.exe | 142.250.185.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3648 | chrome.exe | 172.217.16.131:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3648 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
— | — | 142.250.185.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3648 | chrome.exe | 142.250.184.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3648 | chrome.exe | 142.250.181.238:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
3648 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3648 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3648 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3648 | chrome.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3800 | PCOptimizerProSetup_STD.exe | A Network Trojan was detected | ET USER_AGENTS Suspicious User Agent (Microsoft Internet Explorer) |
3800 | PCOptimizerProSetup_STD.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
3800 | PCOptimizerProSetup_STD.exe | Potentially Bad Traffic | ET INFO Observed ZeroSSL SSL/TLS Certificate |
Process | Message |
|---|---|
regsvr32.exe | HKCR
{
NoRemove CLSID
{
ForceRemove {203ABD21-41F1-4F1B-BAE3-D6A89A90D239} = s 'PCProCtxMenu Class'
{
InprocServer32 = s 'C:\Program Files\PC Optimizer Pro\PCOptProCtxMenu.dll'
{
val ThreadingModel = s 'Apartment'
}
}
}
NoRemove *
{
NoRemove ShellEx
{
NoRemove ContextMenuHandlers
{
ForceRemove PCProCtxMenu = s '{203ABD21-41F1-4F1B-BAE3-D6A89A90D239}'
}
}
}
NoRemove lnkfile
{
NoRemove ShellEx
{
NoRemove ContextMenuHandlers
{
ForceRemove PCProCtxMenu = s '{203ABD21-41F1-4F1B-BAE3-D6A89A90D239}'
}
}
}
}
|
regsvr32.exe | HKCR
{
NoRemove CLSID
{
ForceRemove {203ABD21-41F1-4F1B-BAE3-D6A89A90D239} = s 'PCProCtxMenu Class'
{
InprocServer32 = s 'C:\Program Files\PC Optimizer Pro\PCOptProCtxMenu.dll'
{
val ThreadingModel = s 'Apartment'
}
}
}
NoRemove *
{
NoRemove ShellEx
{
NoRemove ContextMenuHandlers
{
ForceRemove PCProCtxMenu = s '{203ABD21-41F1-4F1B-BAE3-D6A89A90D239}'
}
}
}
NoRemove lnkfile
{
NoRemove ShellEx
{
NoRemove ContextMenuHandlers
{
ForceRemove PCProCtxMenu = s '{203ABD21-41F1-4F1B-BAE3-D6A89A90D239}'
}
}
}
}
|
PCOptimizerProSetup_STD.exe |
strData:8044520824 |
PCOptimizerProSetup_STD.exe |
Initial:aH77qbHab7 |
PCOptimizerProSetup_STD.exe |
Target:9hVTp |
PCOptimizerProSetup_STD.exe |
Target:aH77qbHab79hVTp |
PCOptimizerPro.exe |
:N
Need Help? Dial
Toll Free: 1-866-364-6553:
|
PCOptimizerPro.exe |
:N
Need Help? Dial
Toll Free: 1-866-364-6553:
|