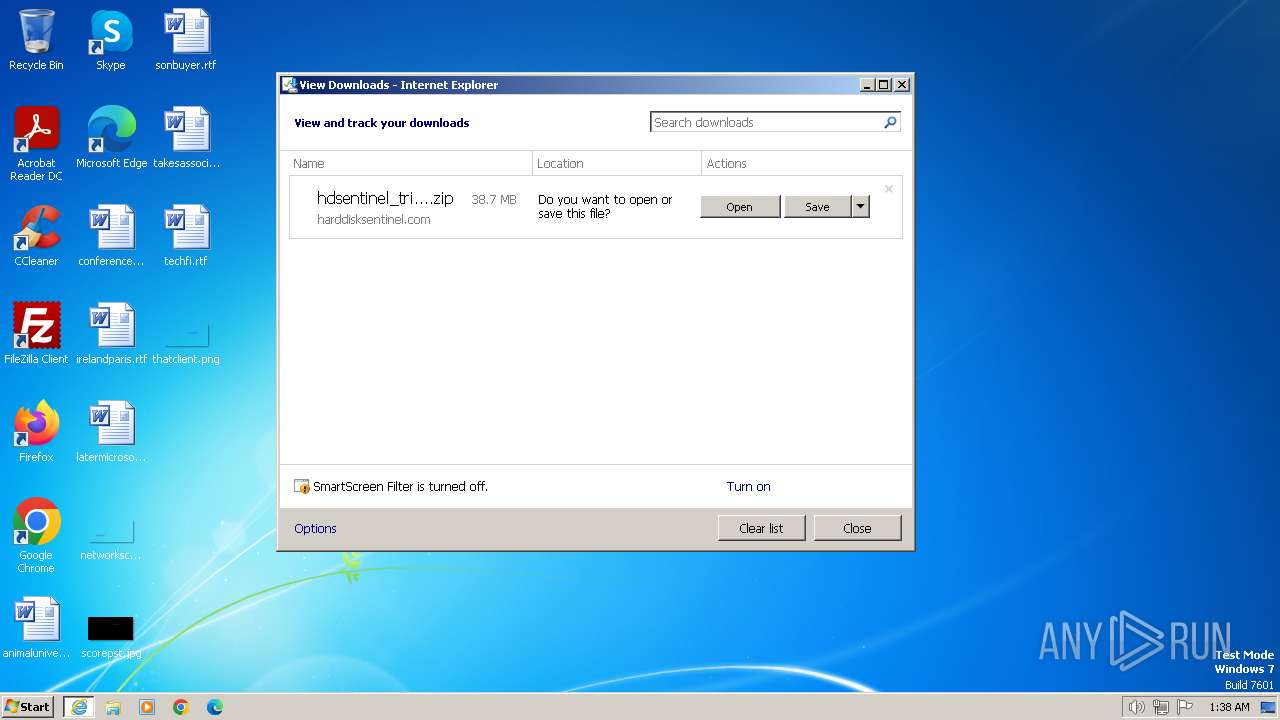
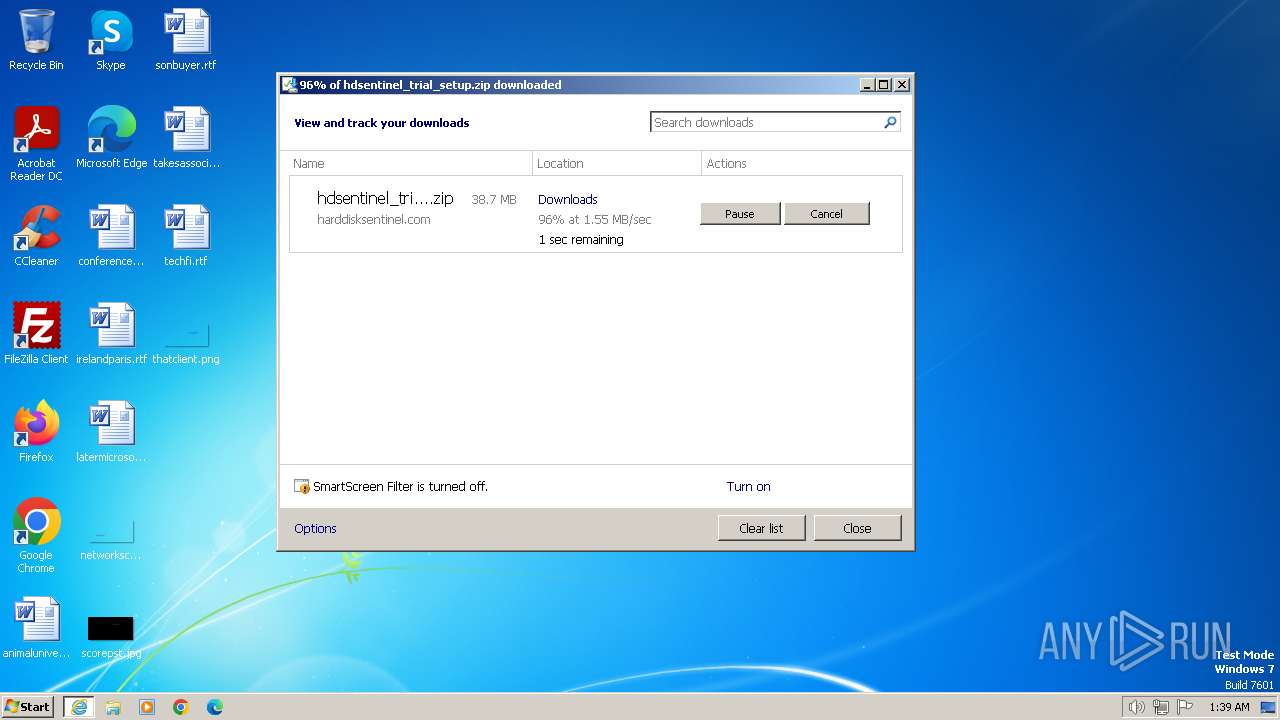
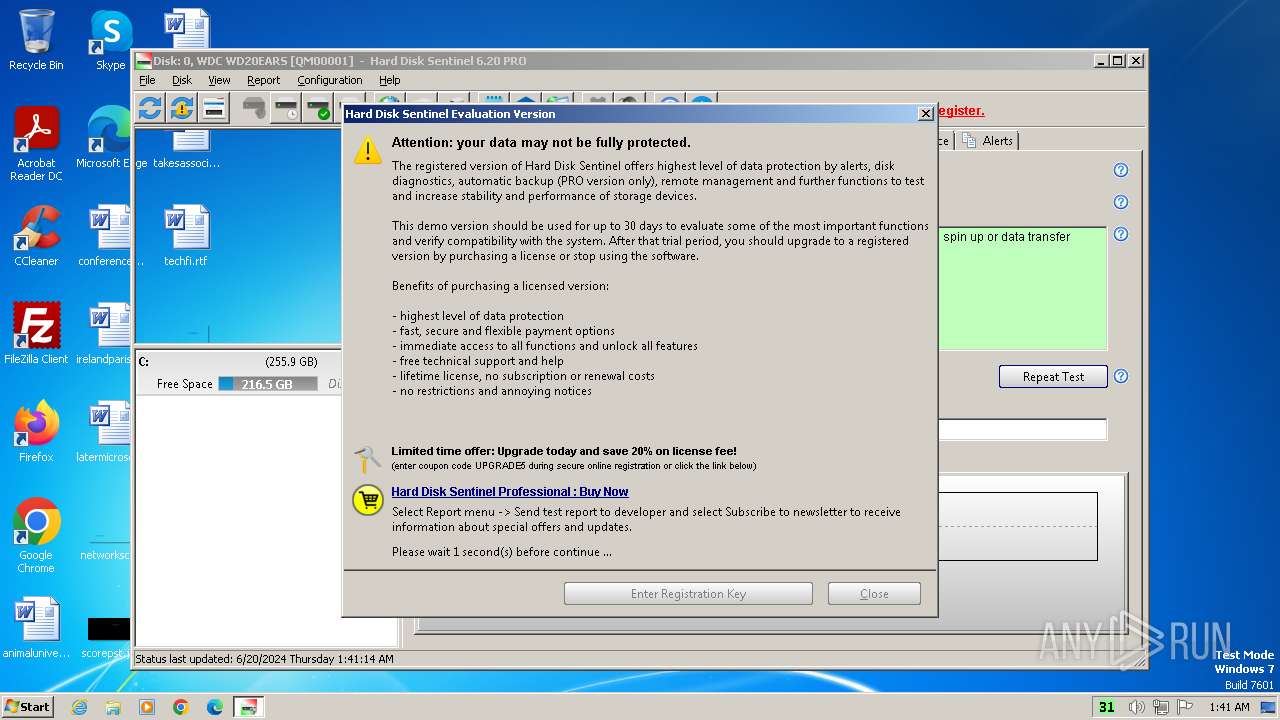
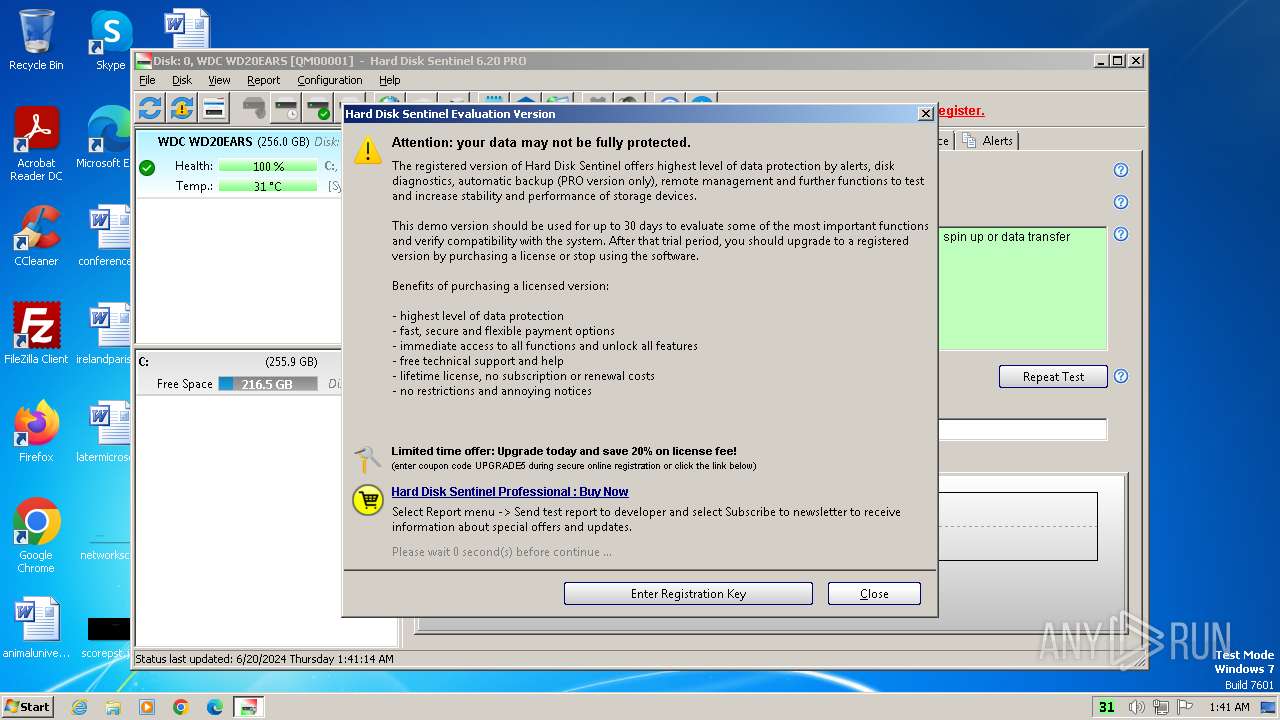
| URL: | https://www.harddisksentinel.com/hdsentinel_trial_setup.zip |
| Full analysis: | https://app.any.run/tasks/03a24016-110a-4a3b-b318-e5be91c63917 |
| Verdict: | Malicious activity |
| Analysis date: | June 20, 2024, 00:38:40 |
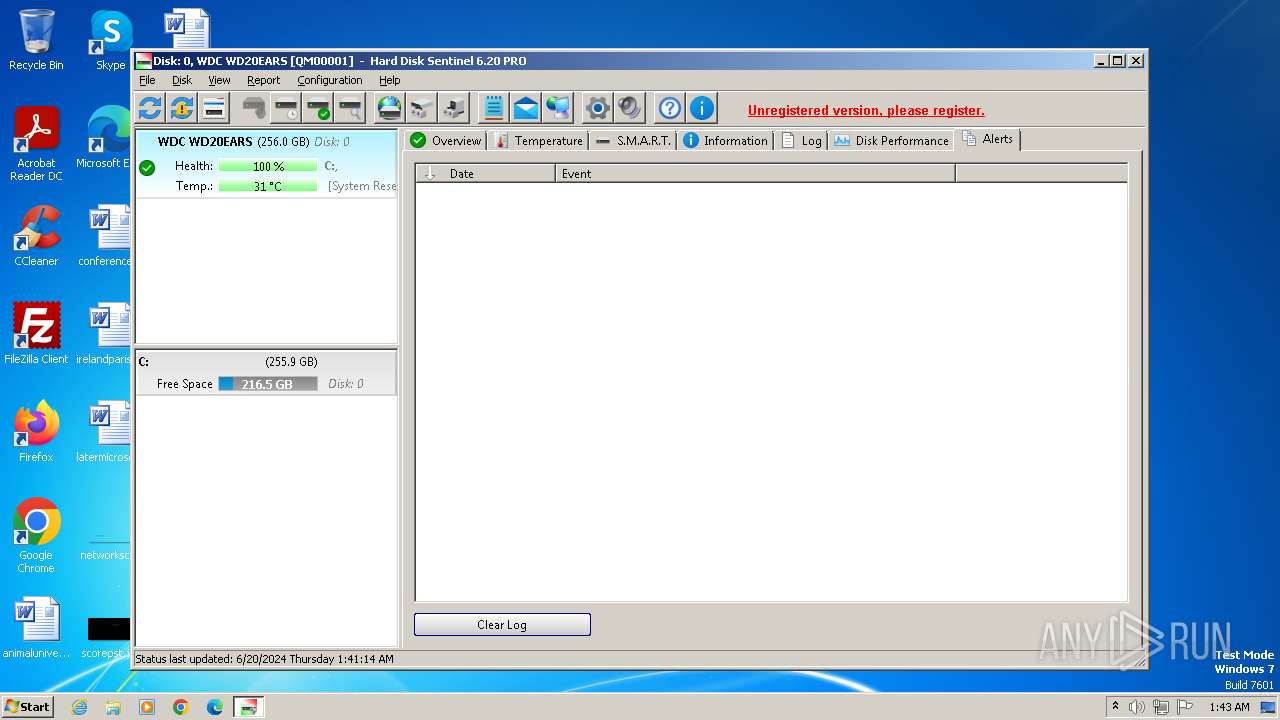
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BAF196BB462EAAA525E2BBBD1BDC7579 |
| SHA1: | 7D67ECBB7418D503C6D4E9A93345FC8C4A37B870 |
| SHA256: | 309E5F4CBA8BF935BBA1966353394E5D62CD424BEBAFA1BA1EB42C55954CFB01 |
| SSDEEP: | 3:N8DSLYX5ALDyaBH/8WHRALc:2OLYX5ALWSJRALc |
MALICIOUS
Drops the executable file immediately after the start
- hdsentinel_pro_setup.exe (PID: 2136)
- hdsentinel_pro_setup.exe (PID: 3984)
- hdsentinel_pro_setup.tmp (PID: 3988)
Creates a new scheduled task (SCRIPT)
- cscript.exe (PID: 2312)
Access Task Scheduler's settings (SCRIPT)
- cscript.exe (PID: 2312)
Gets context to execute command-line operations (SCRIPT)
- cscript.exe (PID: 2312)
Gets security context of the user (SCRIPT)
- cscript.exe (PID: 2312)
SUSPICIOUS
Executable content was dropped or overwritten
- hdsentinel_pro_setup.exe (PID: 2136)
- hdsentinel_pro_setup.exe (PID: 3984)
- hdsentinel_pro_setup.tmp (PID: 3988)
Reads the Windows owner or organization settings
- hdsentinel_pro_setup.tmp (PID: 3988)
Process drops legitimate windows executable
- hdsentinel_pro_setup.tmp (PID: 3988)
Drops a system driver (possible attempt to evade defenses)
- hdsentinel_pro_setup.tmp (PID: 3988)
The process drops C-runtime libraries
- hdsentinel_pro_setup.tmp (PID: 3988)
Starts application with an unusual extension
- HDSentinel.exe (PID: 3328)
Gets a folder of registered tasks (SCRIPT)
- cscript.exe (PID: 2284)
- cscript.exe (PID: 2880)
- cscript.exe (PID: 2312)
Gets context to manipulate scheduled tasks (SCRIPT)
- cscript.exe (PID: 2284)
- cscript.exe (PID: 2880)
- cscript.exe (PID: 2312)
Gets scheduled task context (SCRIPT)
- cscript.exe (PID: 2312)
Gets context to manipulate triggers of a scheduled task (SCRIPT)
- cscript.exe (PID: 2312)
The process executes VB scripts
- HDSentinel.exe (PID: 3328)
Accesses Scheduled Task settings (SCRIPT)
- cscript.exe (PID: 2312)
Gets or sets the principal for the task (SCRIPT)
- cscript.exe (PID: 2312)
Reads the Internet Settings
- StorageTest.dll (PID: 2704)
Accesses current user name via WMI (SCRIPT)
- cscript.exe (PID: 2312)
INFO
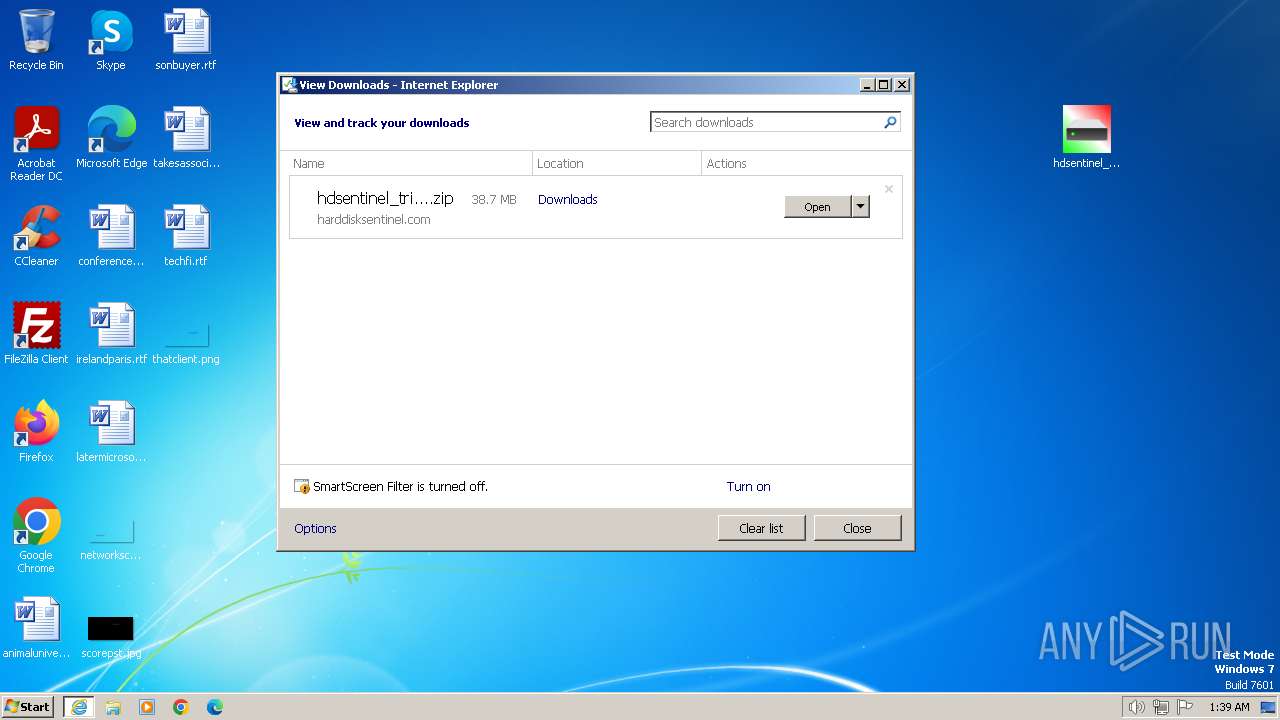
Drops the executable file immediately after the start
- iexplore.exe (PID: 3568)
Application launched itself
- iexplore.exe (PID: 3348)
- msedge.exe (PID: 3628)
- msedge.exe (PID: 3284)
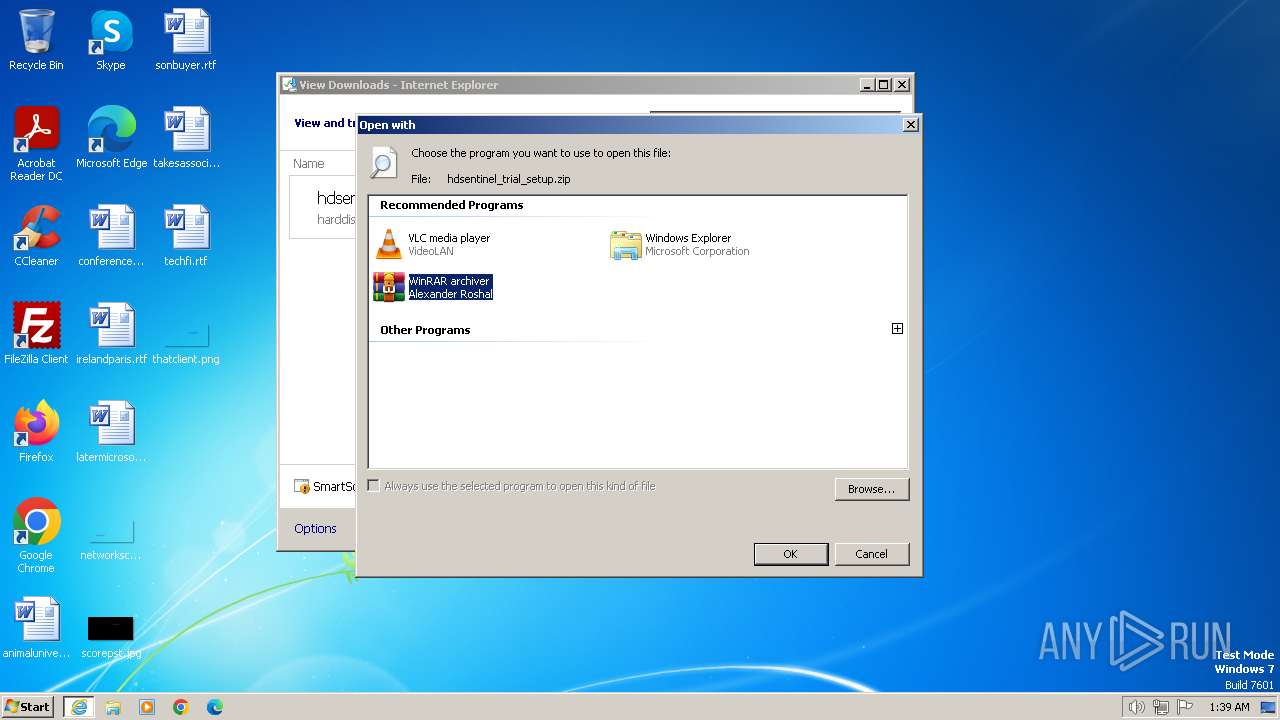
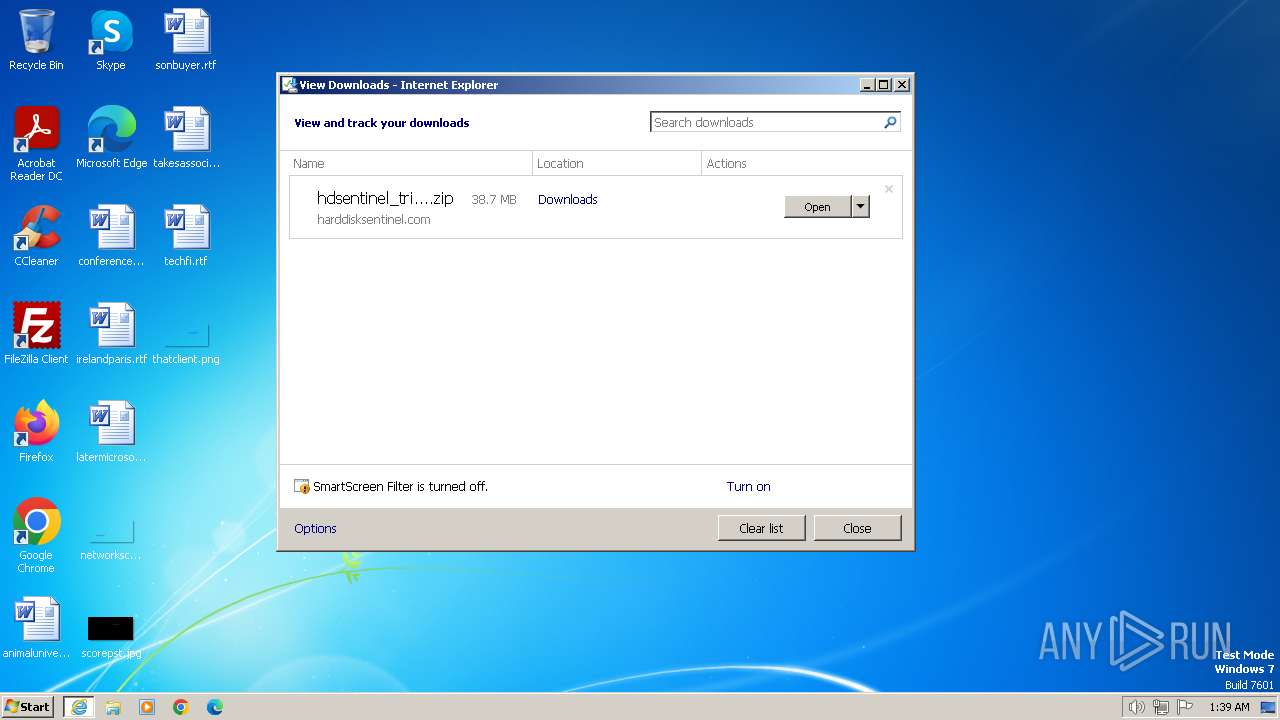
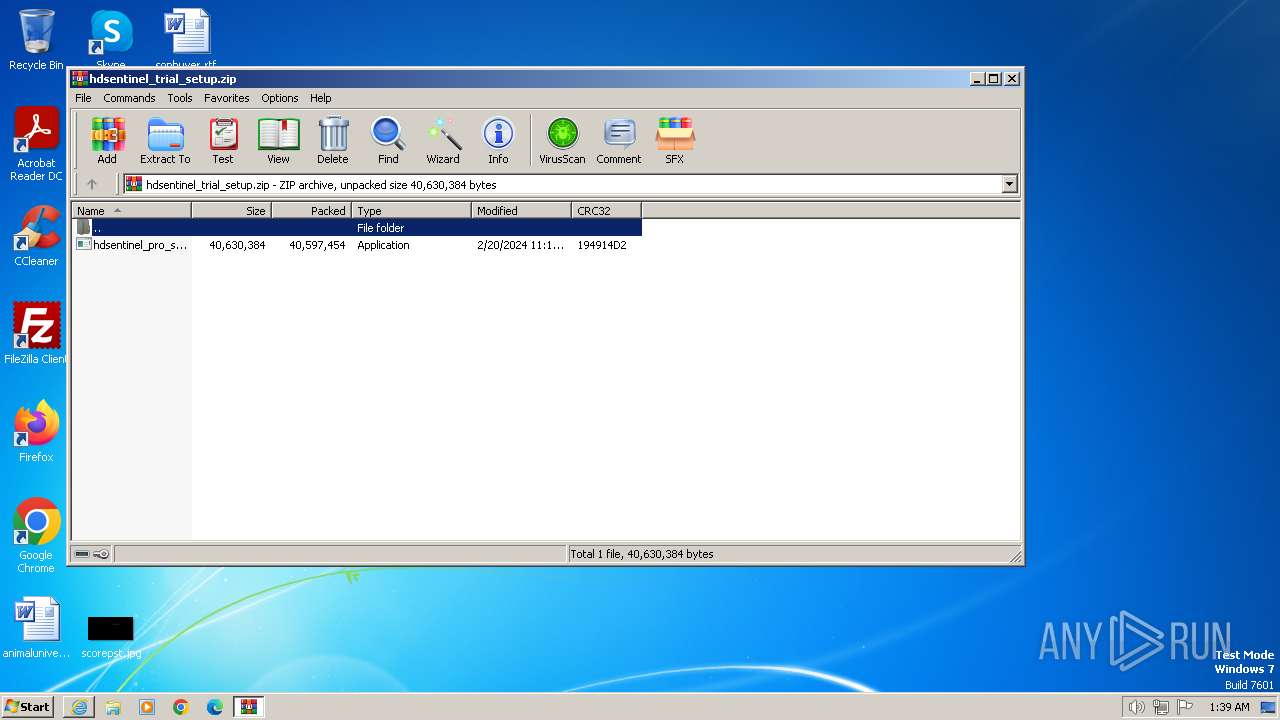
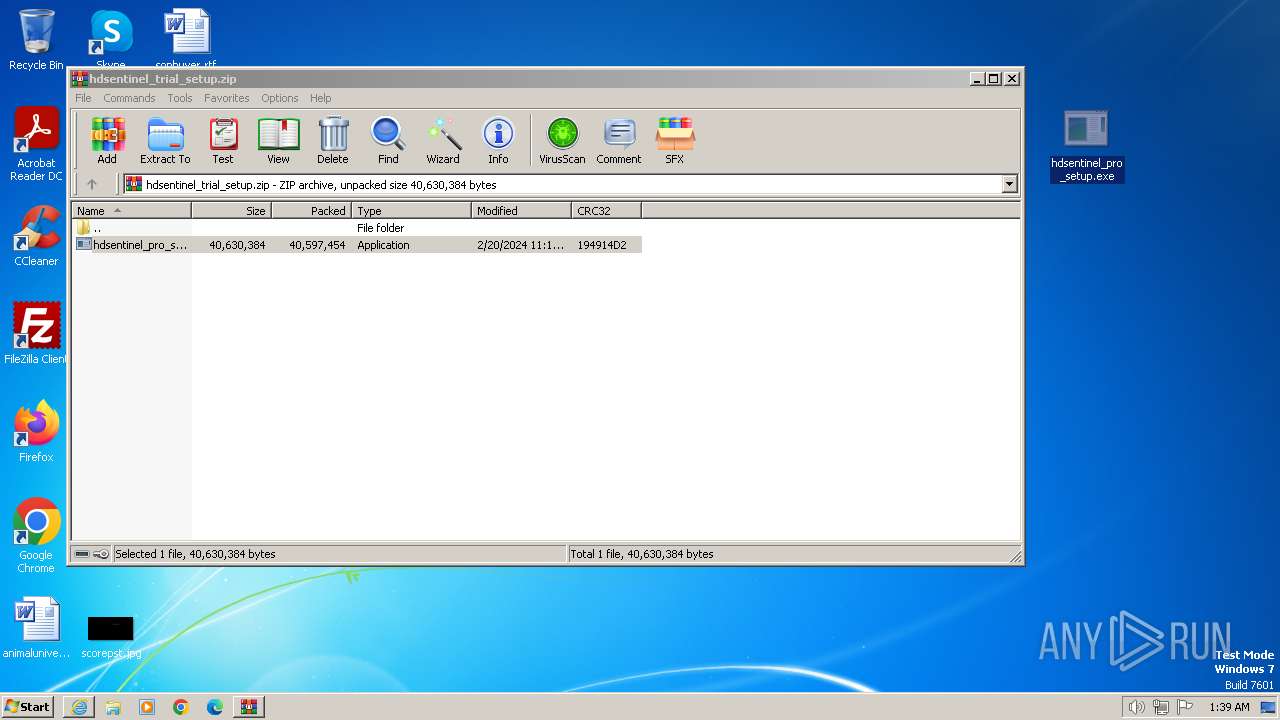
The process uses the downloaded file
- iexplore.exe (PID: 3348)
- WinRAR.exe (PID: 2420)
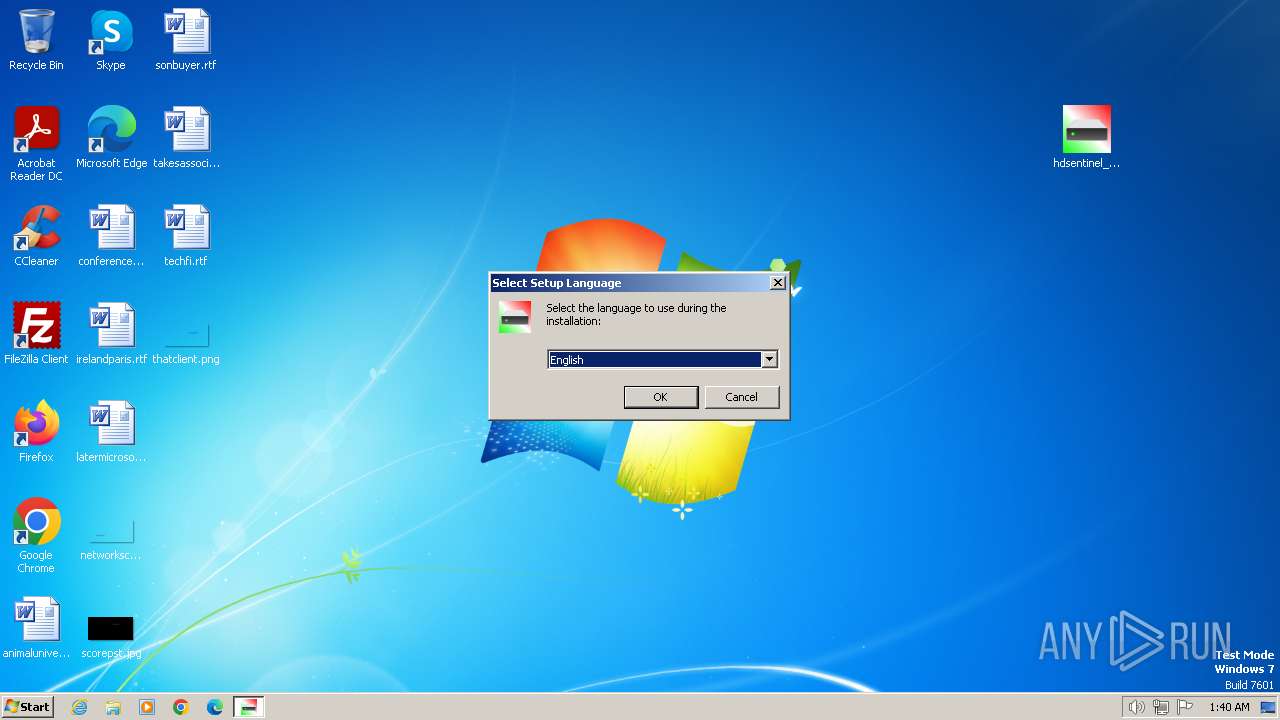
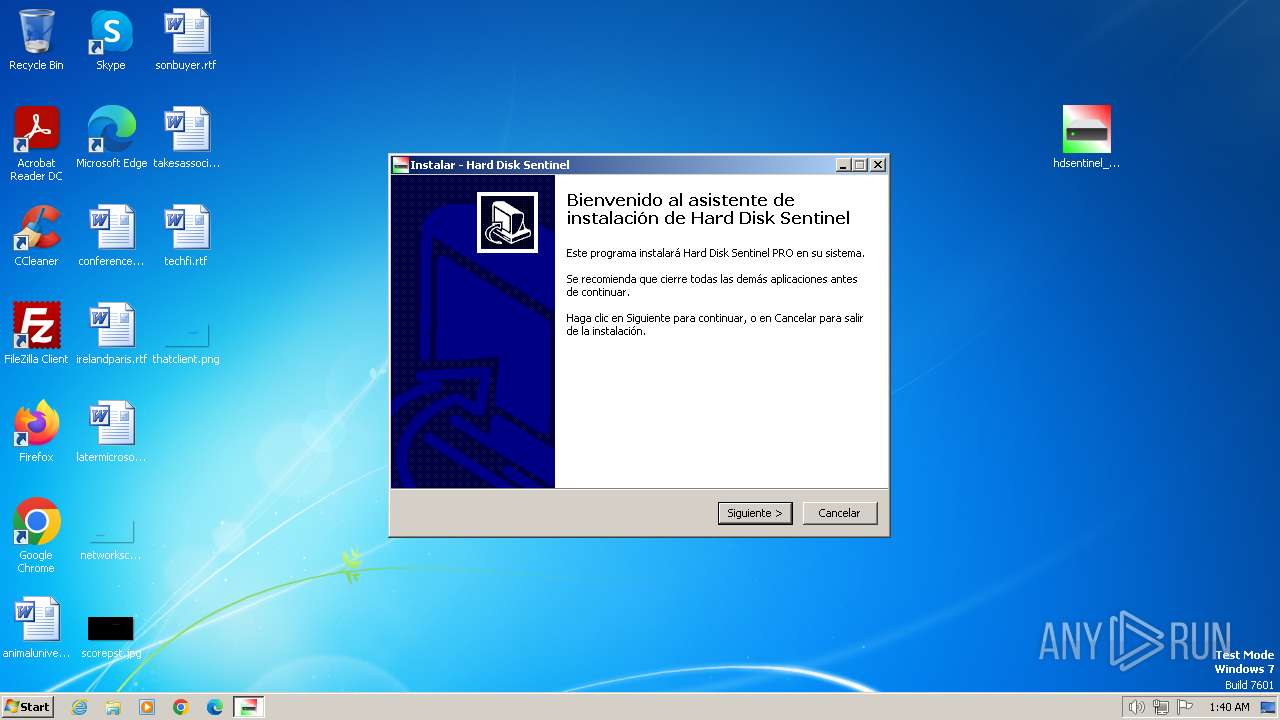
Manual execution by a user
- hdsentinel_pro_setup.exe (PID: 2136)
- HDSentinel.exe (PID: 3320)
- HDSentinel.exe (PID: 3328)
- msedge.exe (PID: 3284)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3348)
Create files in a temporary directory
- hdsentinel_pro_setup.exe (PID: 3984)
- hdsentinel_pro_setup.tmp (PID: 3988)
- detect.dll (PID: 1648)
- hdsentinel_pro_setup.exe (PID: 2136)
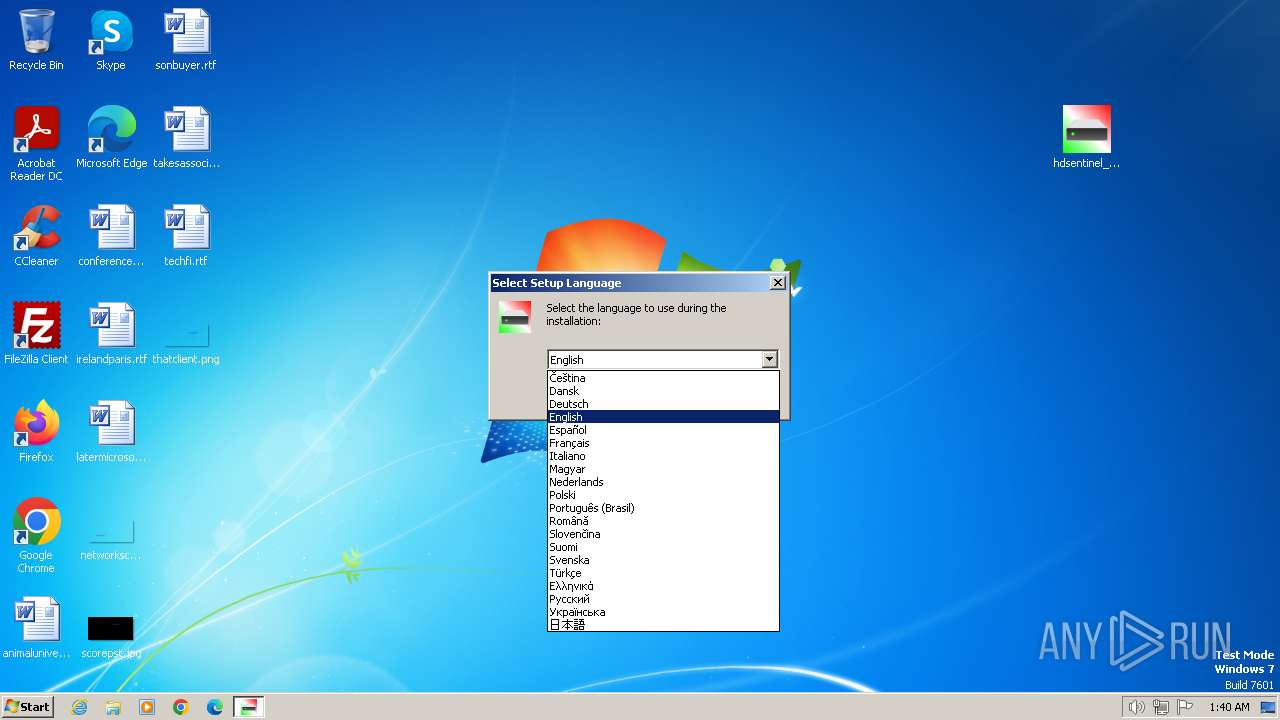
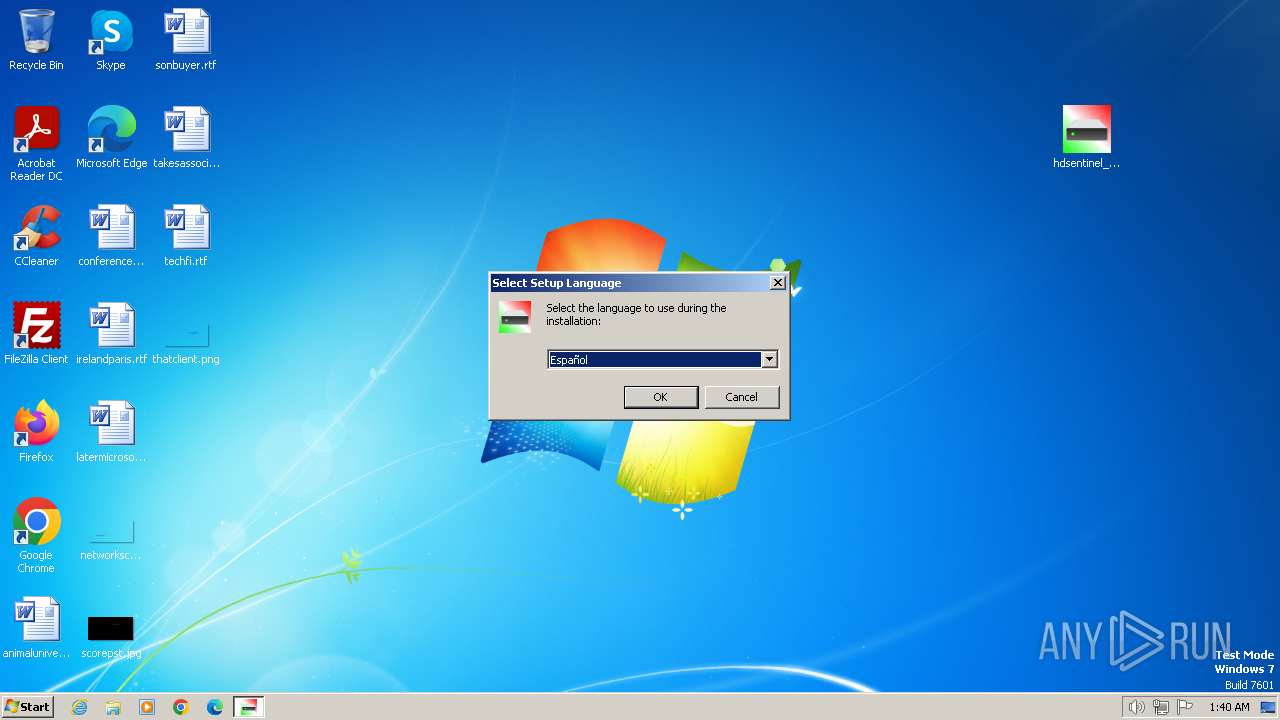
Checks supported languages
- hdsentinel_pro_setup.exe (PID: 2136)
- hdsentinel_pro_setup.exe (PID: 3984)
- hdsentinel_pro_setup.tmp (PID: 3884)
- hdsentinel_pro_setup.tmp (PID: 3988)
- HDSentinel.exe (PID: 3328)
- detect.dll (PID: 1648)
- StorageTest.dll (PID: 2704)
- StorageTest.dll (PID: 3096)
Reads the computer name
- hdsentinel_pro_setup.tmp (PID: 3884)
- hdsentinel_pro_setup.tmp (PID: 3988)
- HDSentinel.exe (PID: 3328)
- detect.dll (PID: 1648)
- StorageTest.dll (PID: 2704)
- StorageTest.dll (PID: 3096)
Creates files in the program directory
- hdsentinel_pro_setup.tmp (PID: 3988)
- HDSentinel.exe (PID: 3328)
Creates files or folders in the user directory
- hdsentinel_pro_setup.tmp (PID: 3988)
- HDSentinel.exe (PID: 3328)
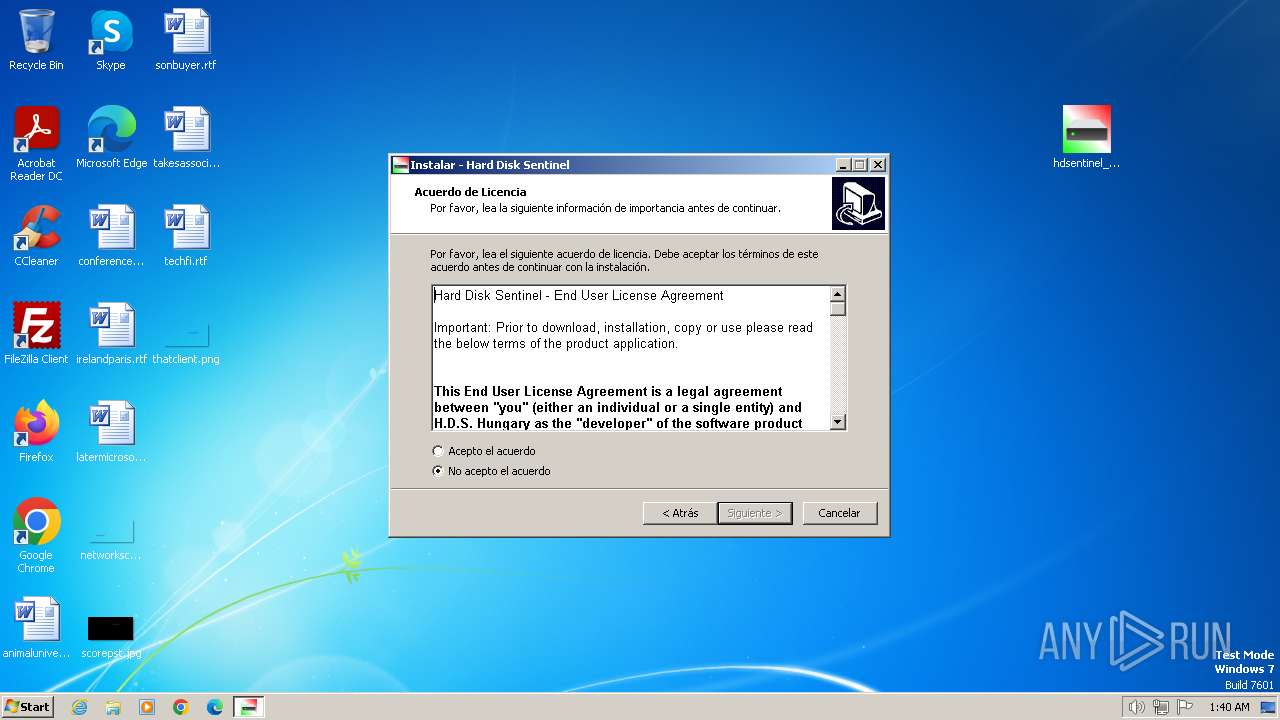
Creates a software uninstall entry
- hdsentinel_pro_setup.tmp (PID: 3988)
Reads Environment values
- HDSentinel.exe (PID: 3328)
- StorageTest.dll (PID: 2704)
- StorageTest.dll (PID: 3096)
Reads the machine GUID from the registry
- detect.dll (PID: 1648)
- StorageTest.dll (PID: 2704)
- HDSentinel.exe (PID: 3328)
- StorageTest.dll (PID: 3096)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2880)
- cscript.exe (PID: 2312)
- cscript.exe (PID: 2284)
Reads product name
- HDSentinel.exe (PID: 3328)
- StorageTest.dll (PID: 2704)
- StorageTest.dll (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
36
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 964 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --mojo-platform-channel-handle=2484 --field-trial-handle=1208,i,11870820754527563562,11102992906960729283,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1036 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1284 --field-trial-handle=1208,i,11870820754527563562,11102992906960729283,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1168 | fsutil behavior query disabledeletenotify | C:\Windows\System32\fsutil.exe | — | HDSentinel.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: fsutil.exe Exit code: 0 Version: 6.1.7601.17577 (win7sp1_gdr.110310-1504) Modules
| |||||||||||||||
| 1264 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3776 --field-trial-handle=1208,i,11870820754527563562,11102992906960729283,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Hard Disk Sentinel\detect.dll" *WMIC2* . "C:\Users\admin\AppData\Local\Temp\240620014113983.2402529.tmp" SELECT Index,PNPDeviceID FROM Win32_DiskDrive | C:\Program Files\Hard Disk Sentinel\detect.dll | — | HDSentinel.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2012 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3056 --field-trial-handle=1208,i,11870820754527563562,11102992906960729283,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2136 | "C:\Users\admin\Desktop\hdsentinel_pro_setup.exe" | C:\Users\admin\Desktop\hdsentinel_pro_setup.exe | explorer.exe | ||||||||||||
User: admin Company: Janos Mathe Integrity Level: MEDIUM Description: Hard Disk Sentinel Setup Exit code: 0 Version: 6.20.0.0 Modules
| |||||||||||||||
| 2284 | CSCRIPT //NOLOGO "C:\Users\admin\AppData\Roaming\Hard Disk Sentinel\hds_control_check.vbs" | C:\Windows\System32\cscript.exe | — | HDSentinel.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2312 | CSCRIPT //NOLOGO "C:\Users\admin\AppData\Roaming\Hard Disk Sentinel\hds_control_add.vbs" | C:\Windows\System32\cscript.exe | — | HDSentinel.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2376 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2320 --field-trial-handle=1208,i,11870820754527563562,11102992906960729283,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
56 207
Read events
55 979
Write events
203
Delete events
25
Modification events
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 883440192 | |||
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31113898 | |||
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31113898 | |||
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3348) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
134
Suspicious files
144
Text files
190
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | iexplore.exe | C:\Users\admin\Downloads\hdsentinel_trial_setup.zip | — | |
MD5:— | SHA256:— | |||
| 3568 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\hdsentinel_trial_setup[1].zip | compressed | |
MD5:FB2A9ECDFA167CE83E007E5664202539 | SHA256:943FA3290E3D69AD41C004C7263561285CD73C94CD3CEDBAC41F148C59FCEBA7 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:A20DCDD581A69F44E7DCBEEAB5084FB4 | SHA256:009768E52DED8DA33AC7D96D521E882EEF9765278997F2CE47311F637696D9C7 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver5BF2.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\YD3ZTD1K.txt | text | |
MD5:E4DB419C3558F8CD62AB57E64BD16F4B | SHA256:9827AD766C29AAE8390199F968B3792C8C2748C6ABEA934CB5A7F2E5E5A319E5 | |||
| 3348 | iexplore.exe | C:\Users\admin\Downloads\hdsentinel_trial_setup.zip.b8lzgpc.partial:Zone.Identifier | text | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\SA3S10ET.txt | text | |
MD5:24807A2EA66D5A51E01DEB5F191CCB84 | SHA256:DD64CEC3A944CC51550562348325B9ECE748AE853206D579DC34C52464FAEE62 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\FG7G6EJF.txt | text | |
MD5:B35E4757B9442F0F4E15472562F248C2 | SHA256:3F2D9D98E4B6B9E589B6028EC1DE9506973C966626179562A82459F5AD14AFC7 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Z7W978NV.txt | text | |
MD5:7E9228FC0AD826D6397FBB2740D0D221 | SHA256:8A7427F0D51E5EBC441F8611556C7C57711A6E19A5CE3AAA94D24A6D37851E9F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
49
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3568 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?019d1f622a31a21e | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
— | — | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQDTGClBmJ9aOQ%3D%3D | unknown | — | — | unknown |
3348 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e1c7fb6f69bbdcfa | unknown | — | — | unknown |
3568 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?04c083ac5861cd0c | unknown | — | — | unknown |
— | — | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
3348 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3568 | iexplore.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.124.249.23:80 | ocsp.godaddy.com | SUCURI-SEC | US | unknown |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1372 | svchost.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
1372 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |