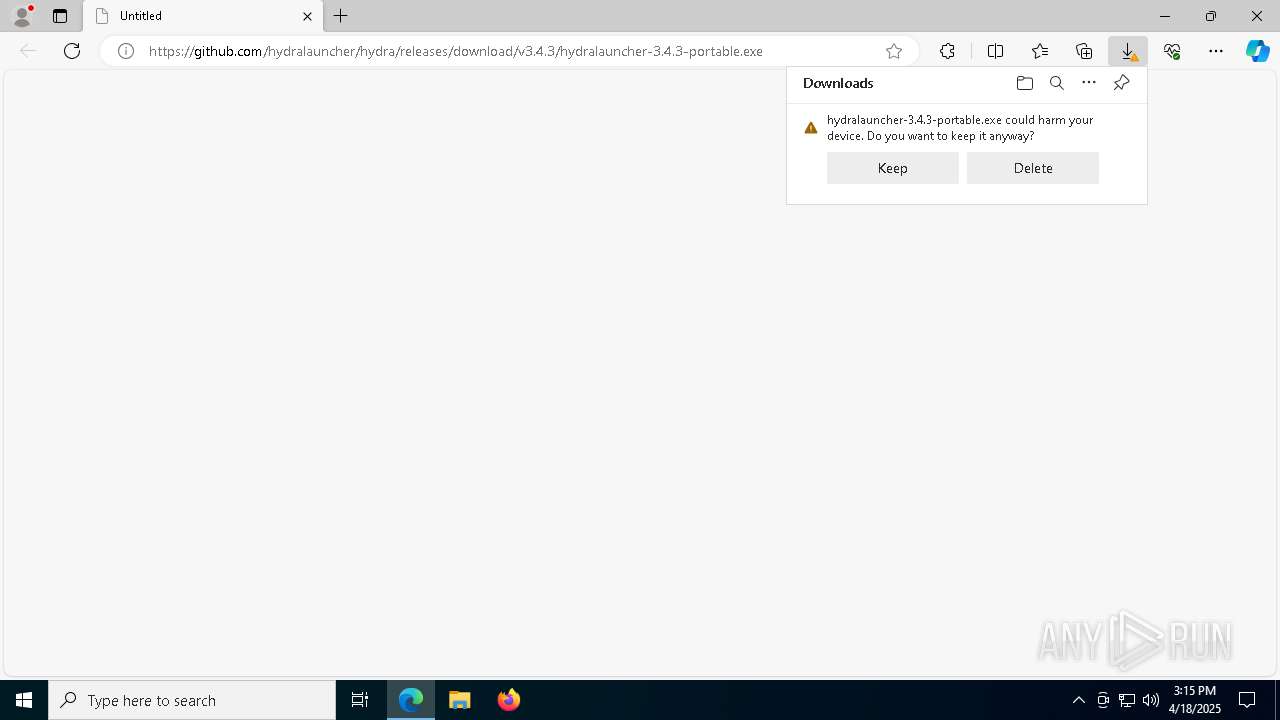
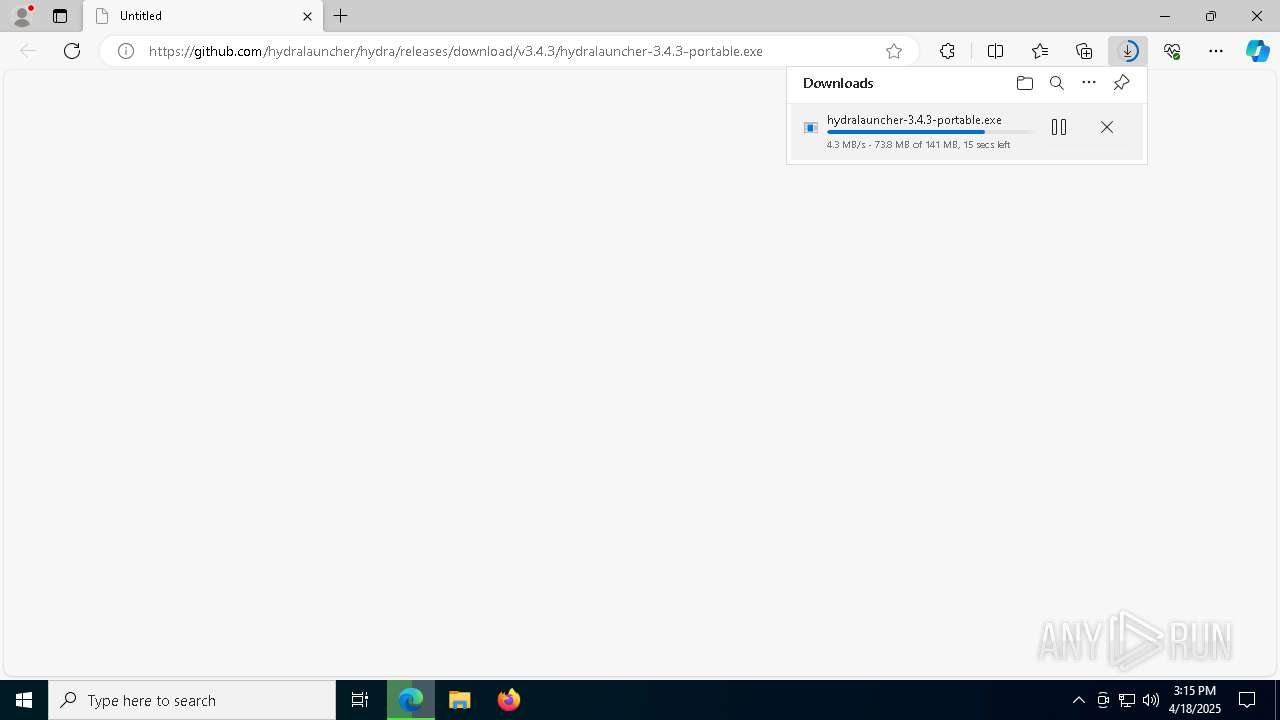
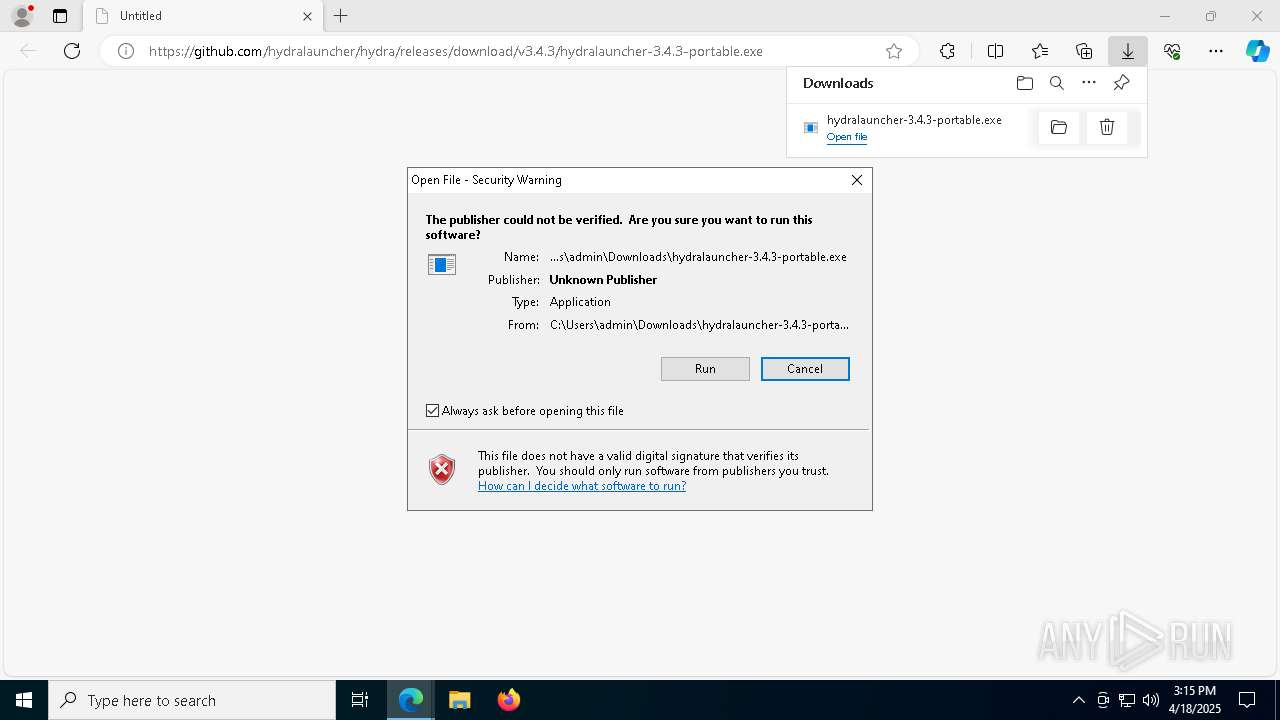
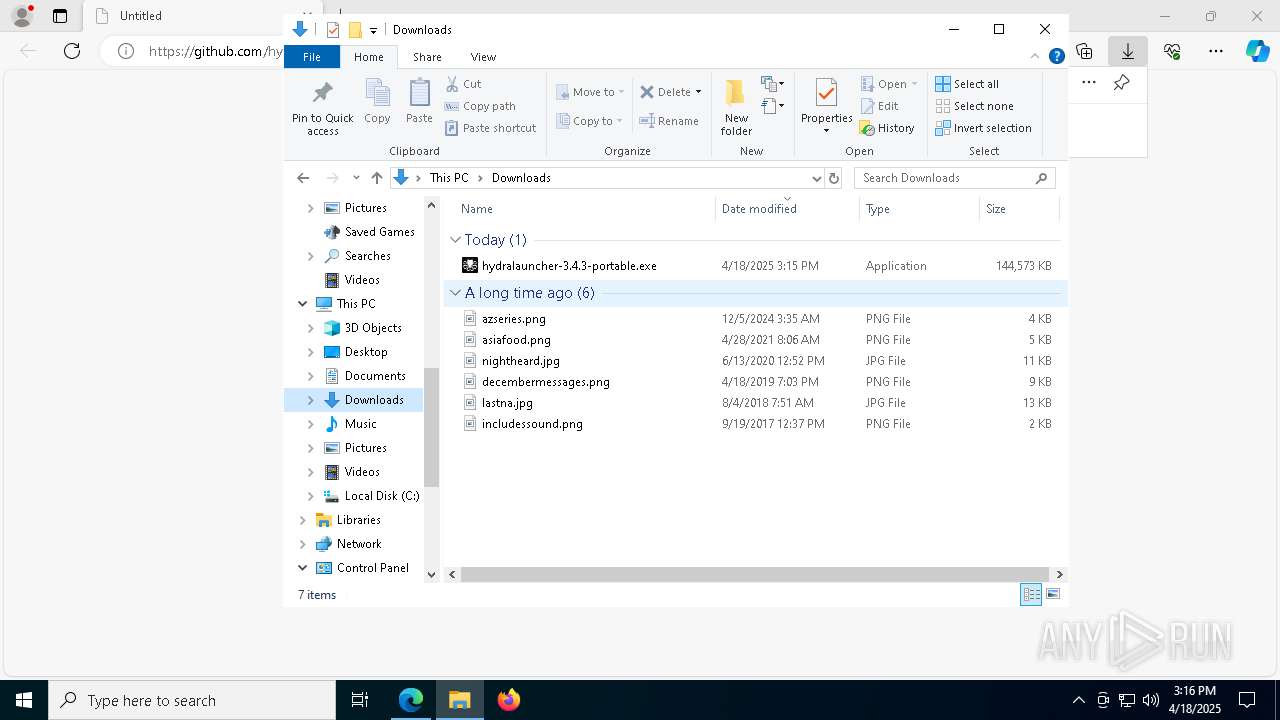
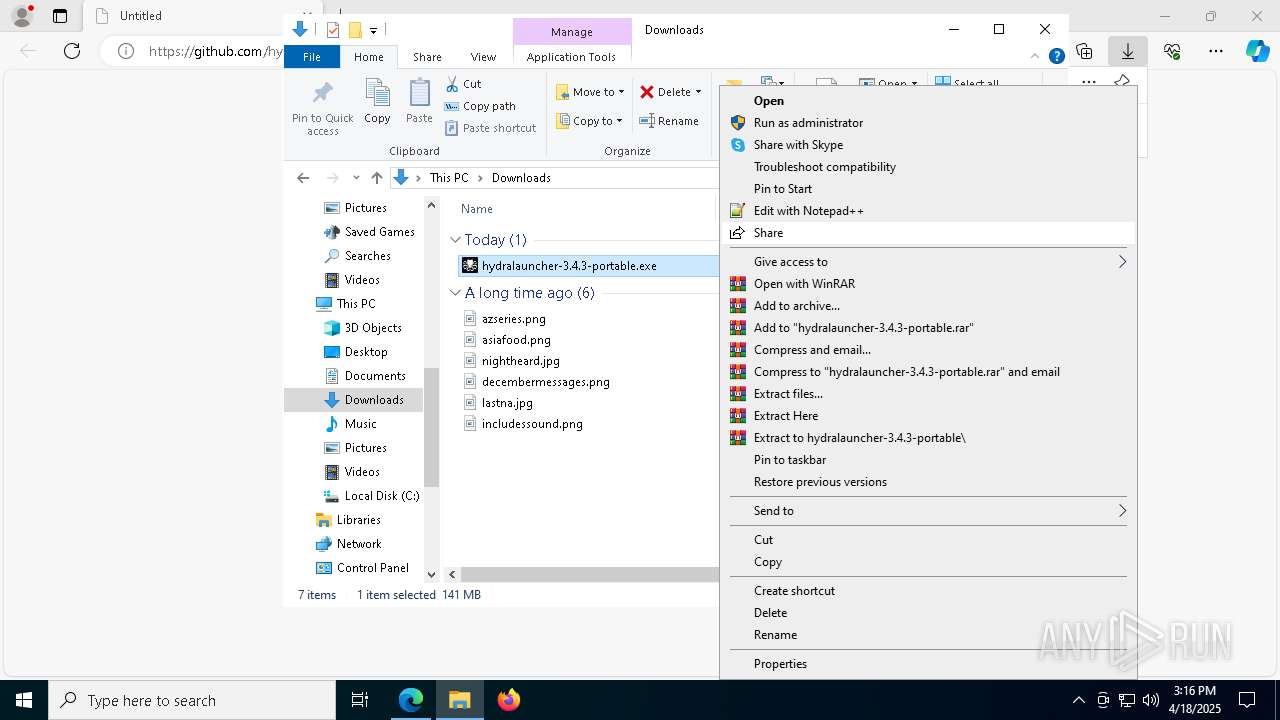
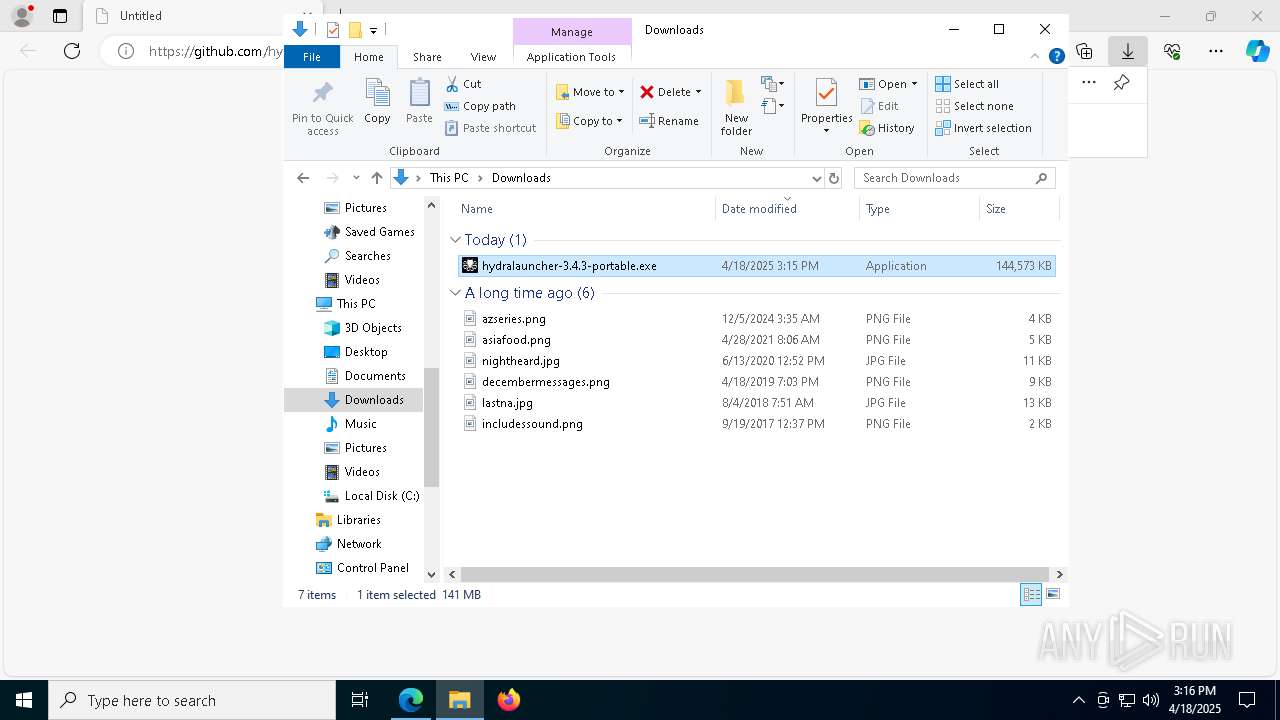
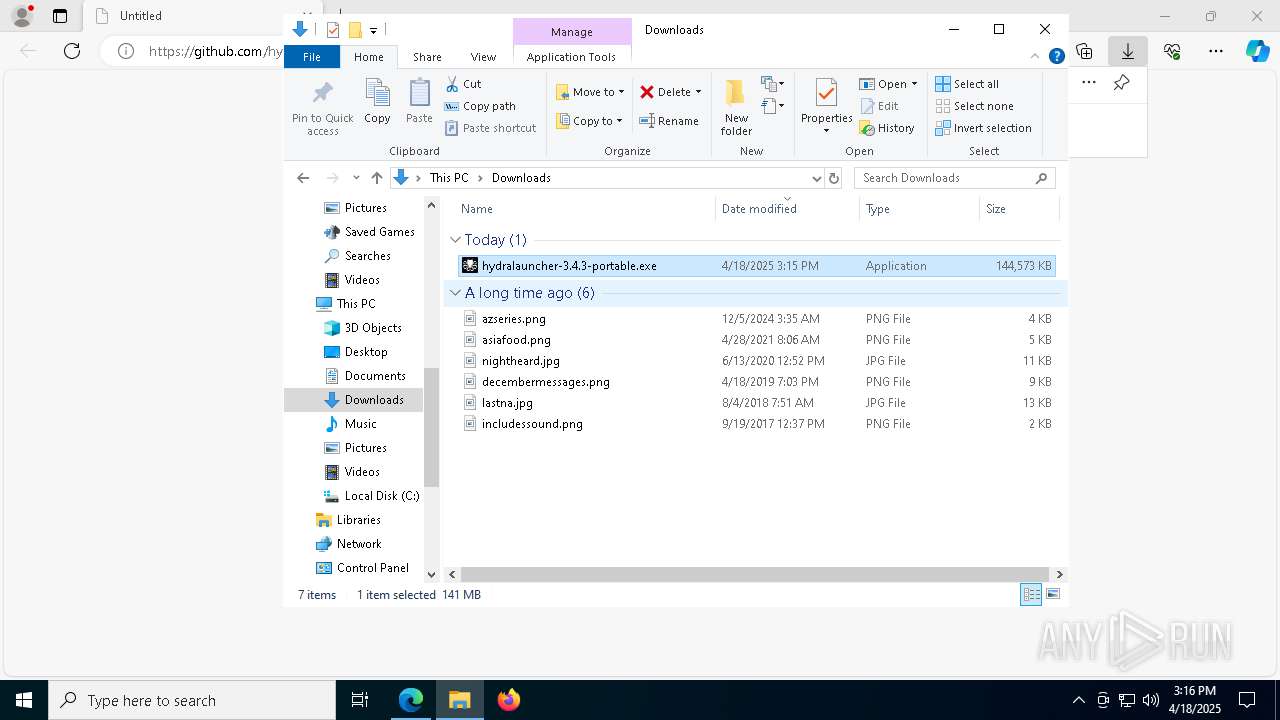
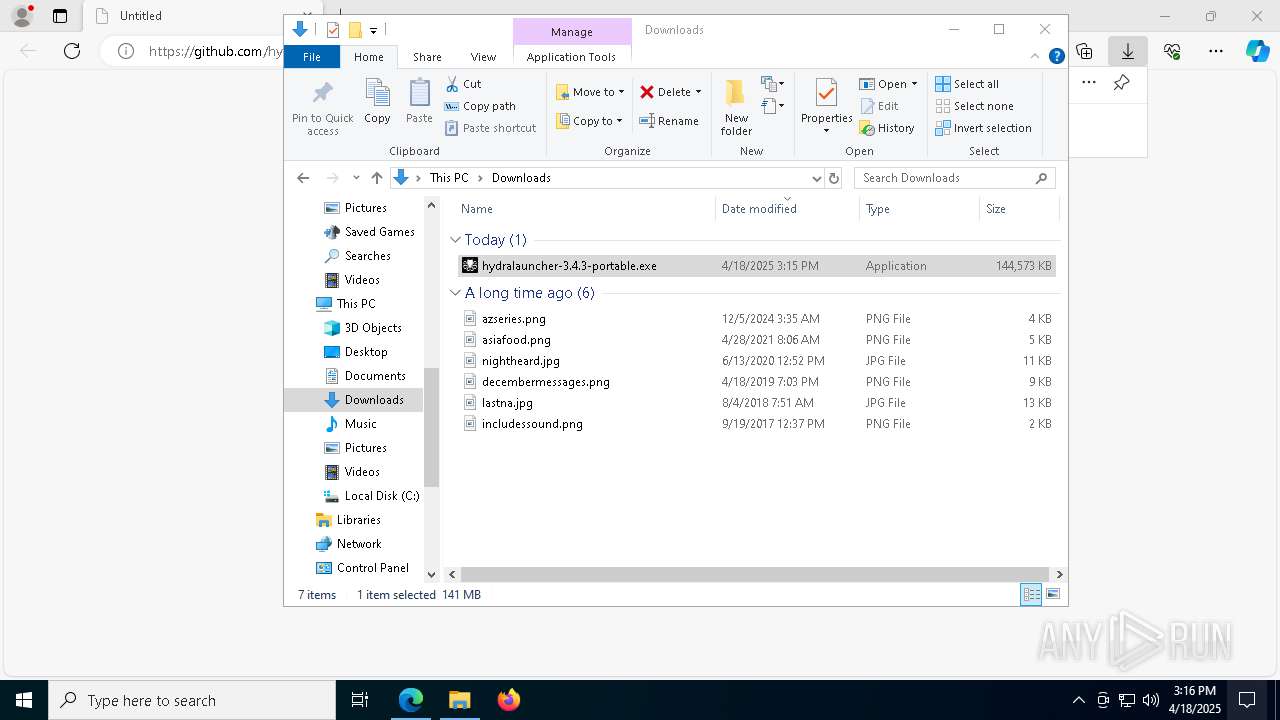
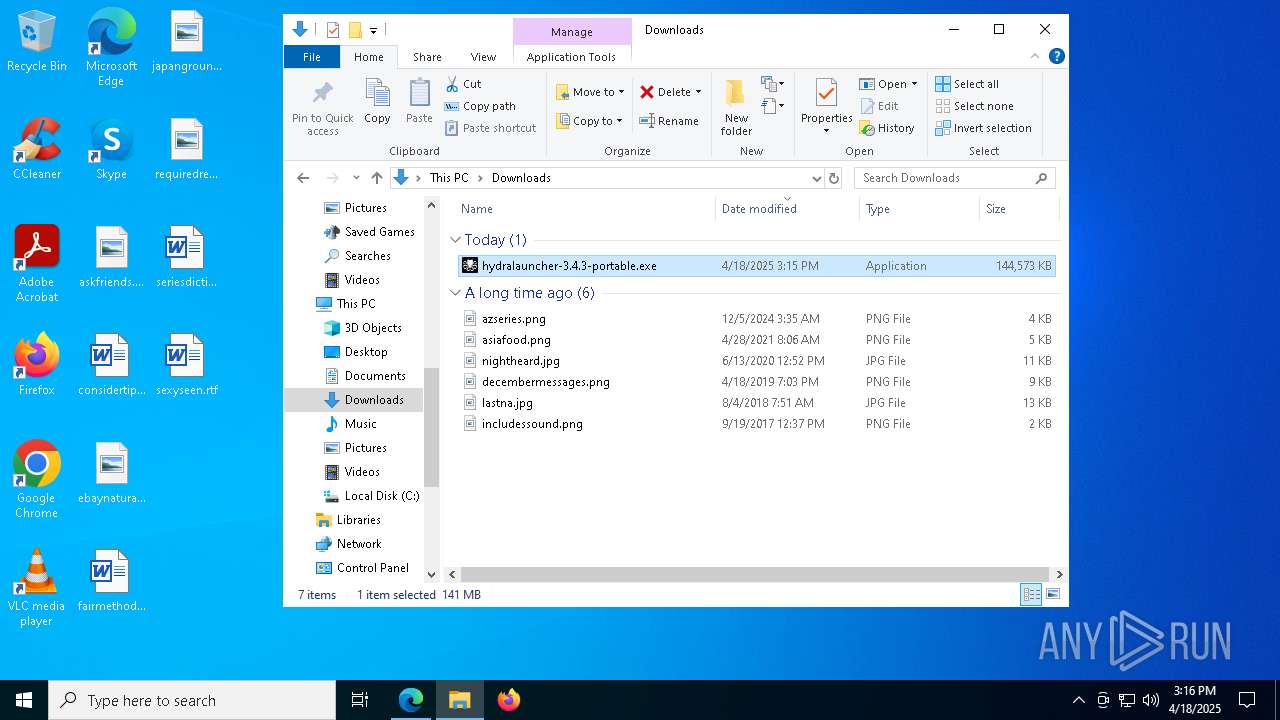
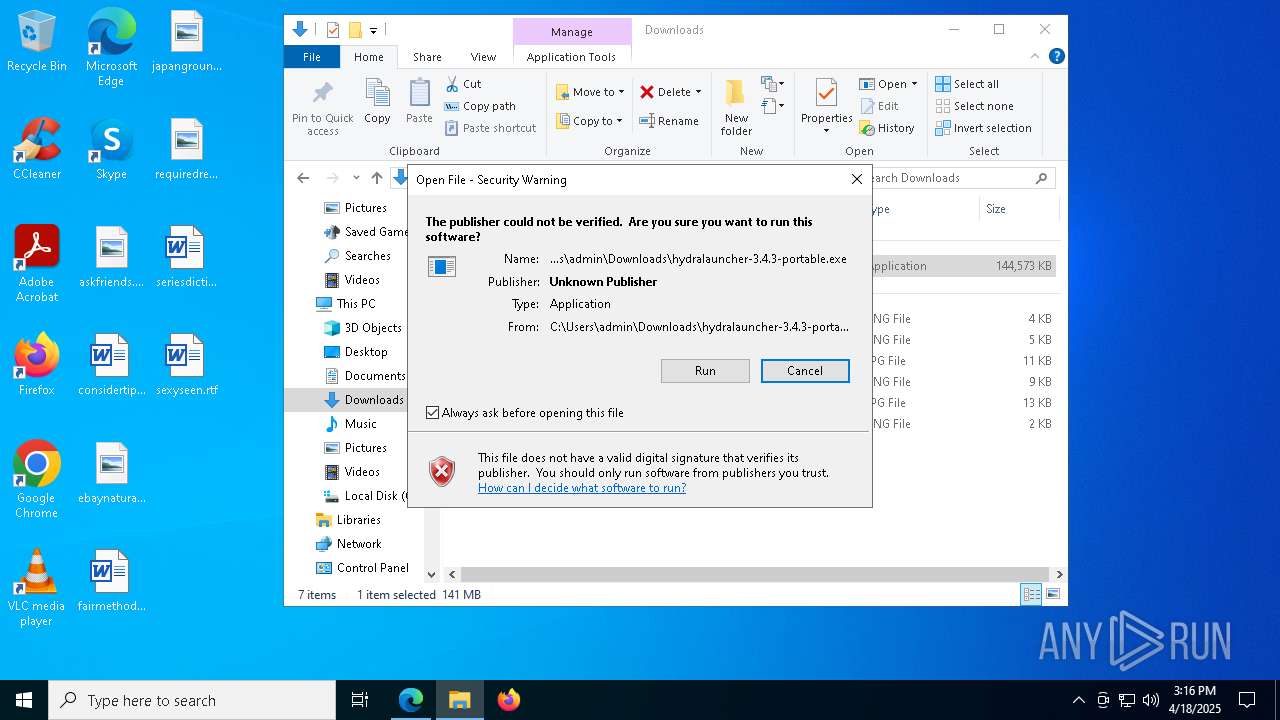
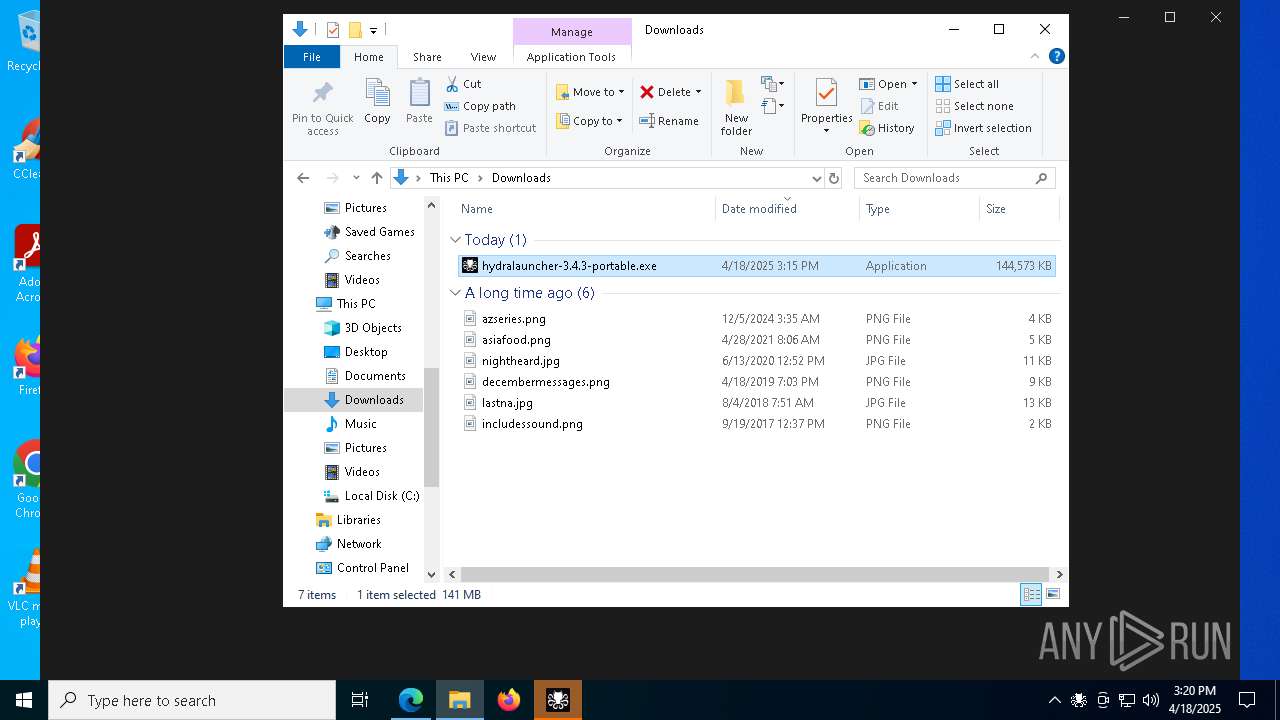
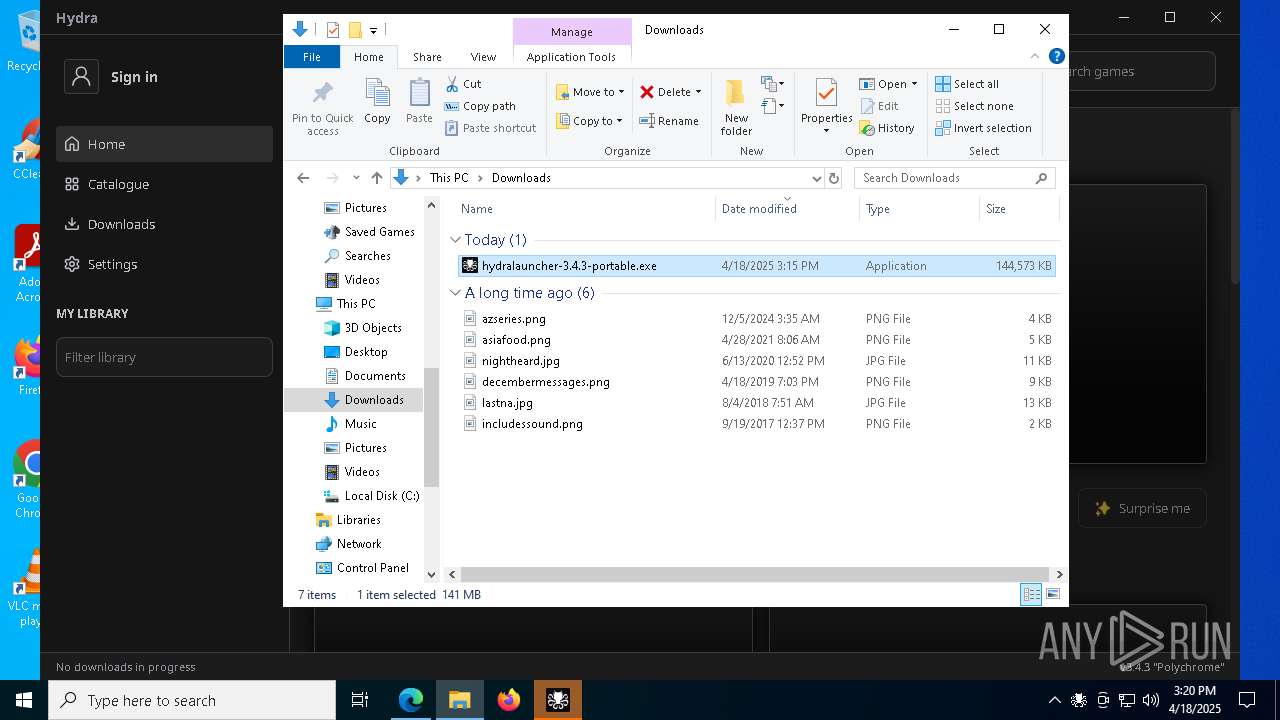
| URL: | https://github.com/hydralauncher/hydra/releases/download/v3.4.3/hydralauncher-3.4.3-portable.exe |
| Full analysis: | https://app.any.run/tasks/fd2e89e8-a9df-4ff0-9a44-5ebbfb25d623 |
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2025, 15:15:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BC4429B6F7F8D61BE1574D66B7FF56AE |
| SHA1: | 2DFD790452BE9163E15F7B19A5DBB0326E0FA6AF |
| SHA256: | 309E5CC0BEC33F638457F55B6CD04B500892C7D225DB7B4584C490202E668CFA |
| SSDEEP: | 3:N8tEd9cSjLhUKkCAt4XEjuX7:2uISv7ysEy |
MALICIOUS
BITTORRENT has been detected (SURICATA)
- hydra-python-rpc.exe (PID: 7124)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
The process creates files with name similar to system file names
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
Process drops python dynamic module
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
Executable content was dropped or overwritten
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- Hydra.exe (PID: 4016)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
There is functionality for taking screenshot (YARA)
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
Drops 7-zip archiver for unpacking
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 8128)
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
Process drops legitimate windows executable
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
- hydralauncher-3.4.3-portable.exe (PID: 904)
- Hydra.exe (PID: 4016)
The process drops C-runtime libraries
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
Application launched itself
- Hydra.exe (PID: 4016)
- Hydra.exe (PID: 5132)
- Hydra.exe (PID: 2104)
Starts CMD.EXE for commands execution
- Hydra.exe (PID: 5132)
- Hydra.exe (PID: 2104)
- Hydra.exe (PID: 4016)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4352)
Loads Python modules
- hydra-python-rpc.exe (PID: 7124)
INFO
Checks supported languages
- identity_helper.exe (PID: 5892)
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- ShellExperienceHost.exe (PID: 8128)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
- Hydra.exe (PID: 4016)
- Hydra.exe (PID: 5132)
- Hydra.exe (PID: 2104)
- Hydra.exe (PID: 6472)
- Hydra.exe (PID: 1748)
- Hydra.exe (PID: 1760)
- Hydra.exe (PID: 6980)
- Hydra.exe (PID: 6340)
- ludusavi.exe (PID: 4948)
- aria2c.exe (PID: 2524)
- hydra-python-rpc.exe (PID: 7124)
- Hydra.exe (PID: 672)
- Hydra.exe (PID: 6044)
- Hydra.exe (PID: 4448)
Application launched itself
- msedge.exe (PID: 4628)
Reads Environment values
- identity_helper.exe (PID: 5892)
- Hydra.exe (PID: 4016)
- Hydra.exe (PID: 5132)
- Hydra.exe (PID: 2104)
Reads the computer name
- identity_helper.exe (PID: 5892)
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- ShellExperienceHost.exe (PID: 8128)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
- Hydra.exe (PID: 4016)
- Hydra.exe (PID: 5132)
- Hydra.exe (PID: 2104)
- Hydra.exe (PID: 6472)
- Hydra.exe (PID: 6980)
- Hydra.exe (PID: 4448)
- aria2c.exe (PID: 2524)
- hydra-python-rpc.exe (PID: 7124)
Executable content was dropped or overwritten
- msedge.exe (PID: 4628)
- msedge.exe (PID: 4424)
Create files in a temporary directory
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
- Hydra.exe (PID: 4016)
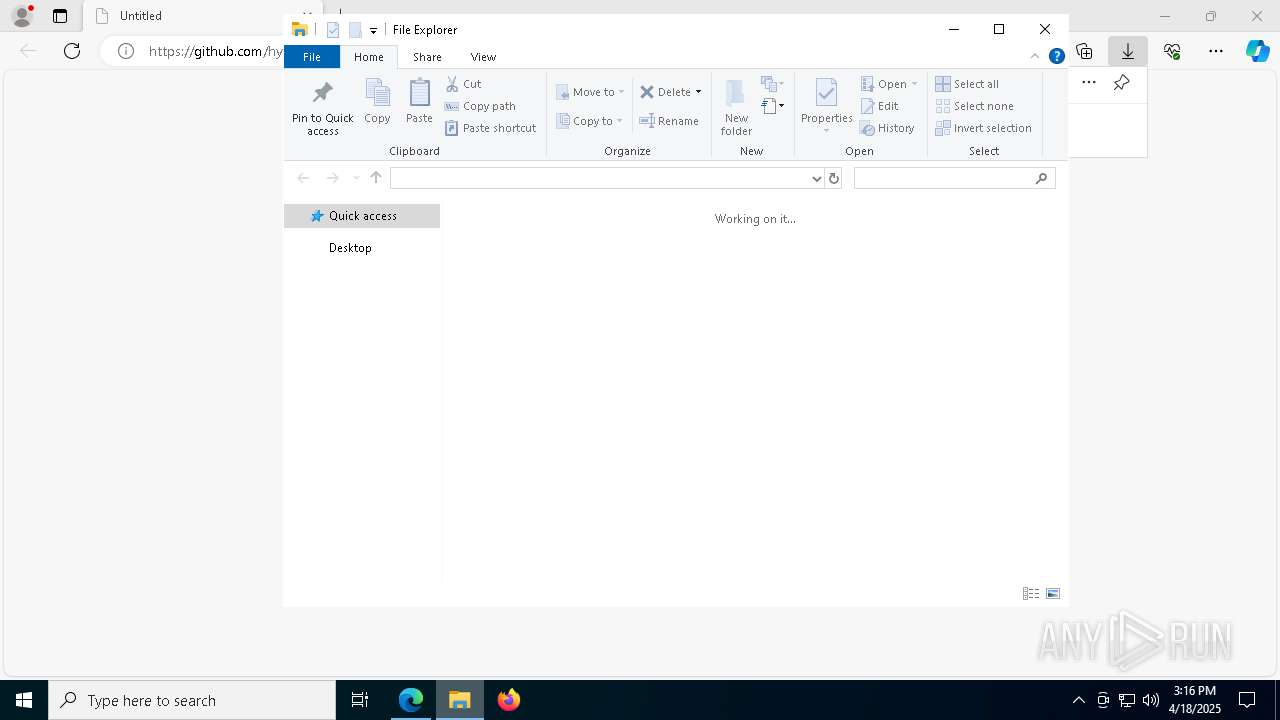
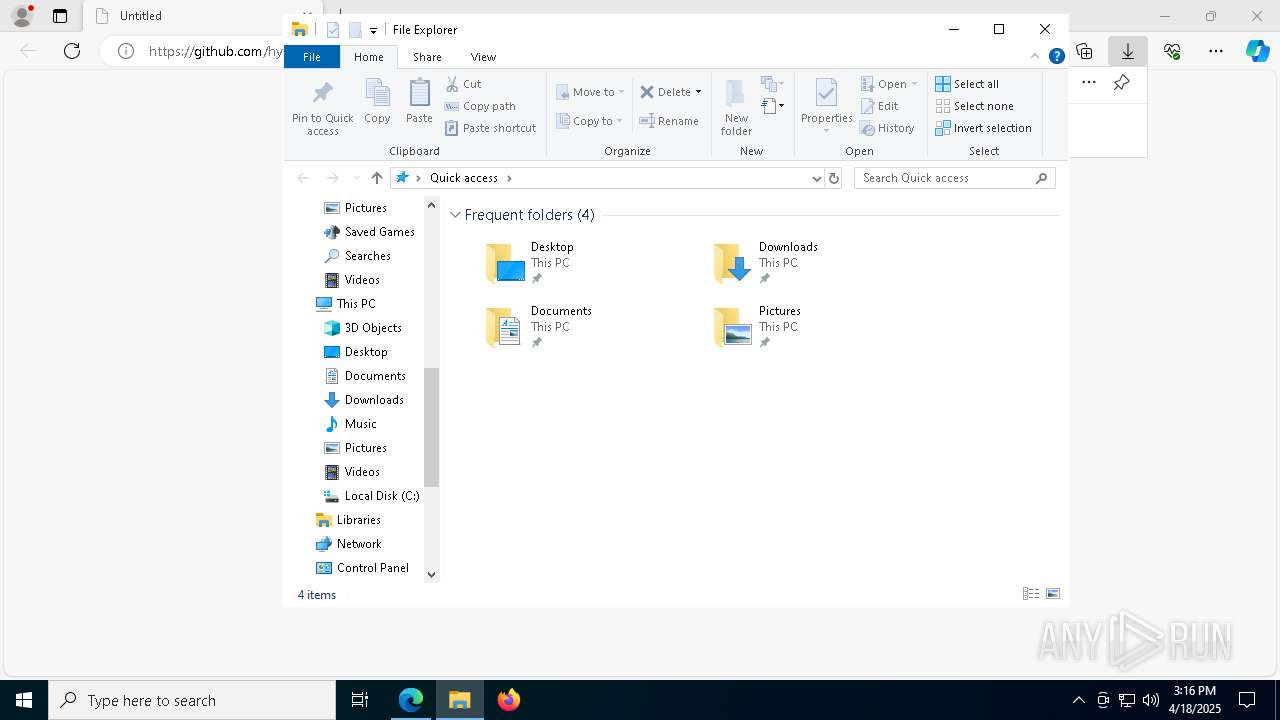
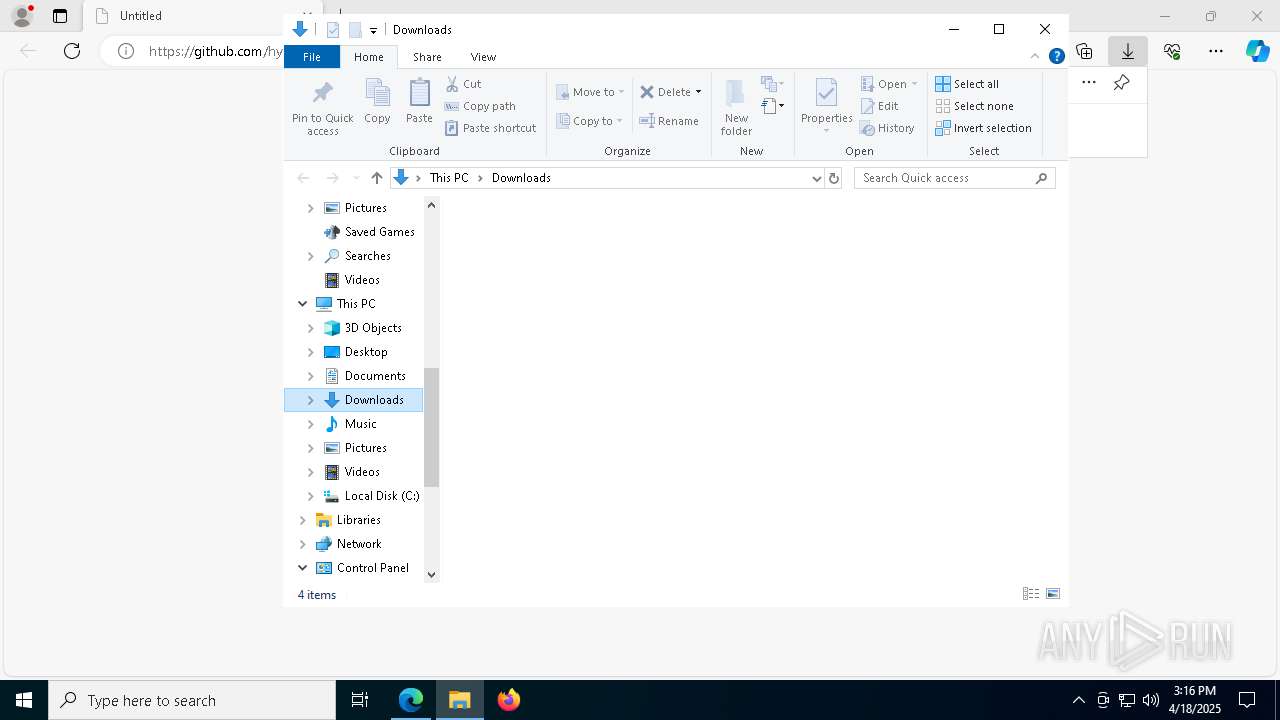
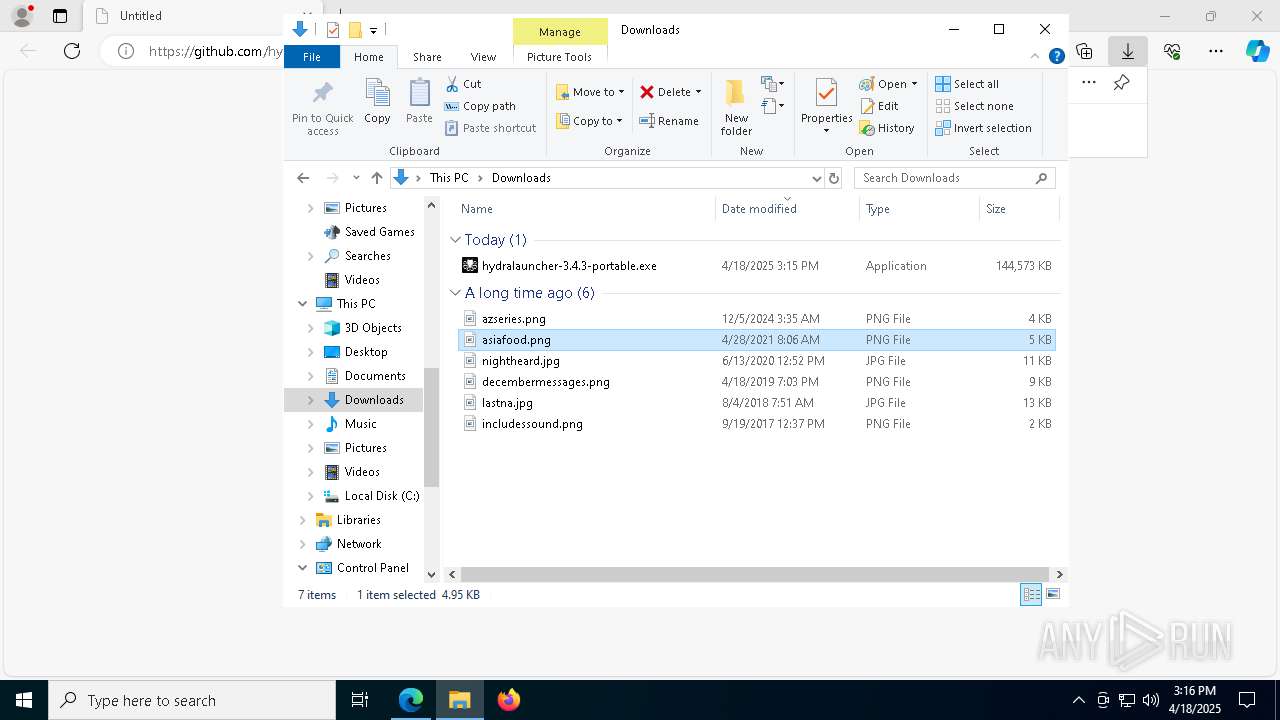
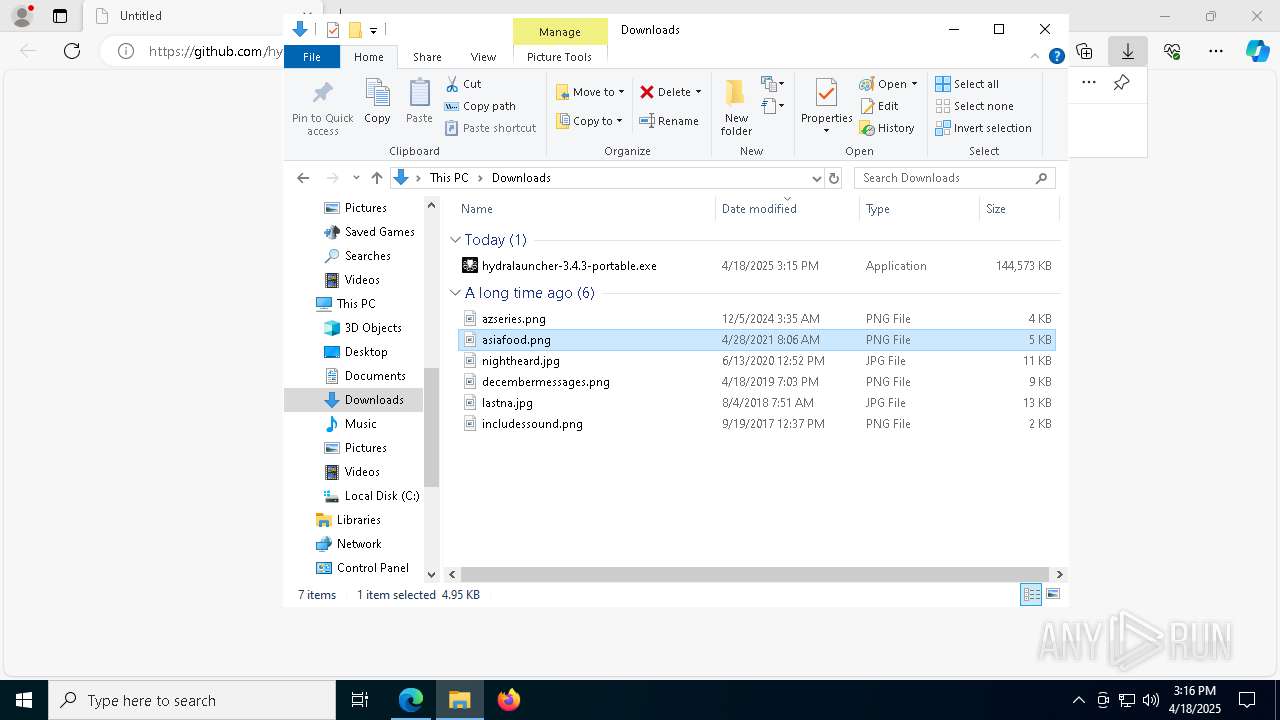
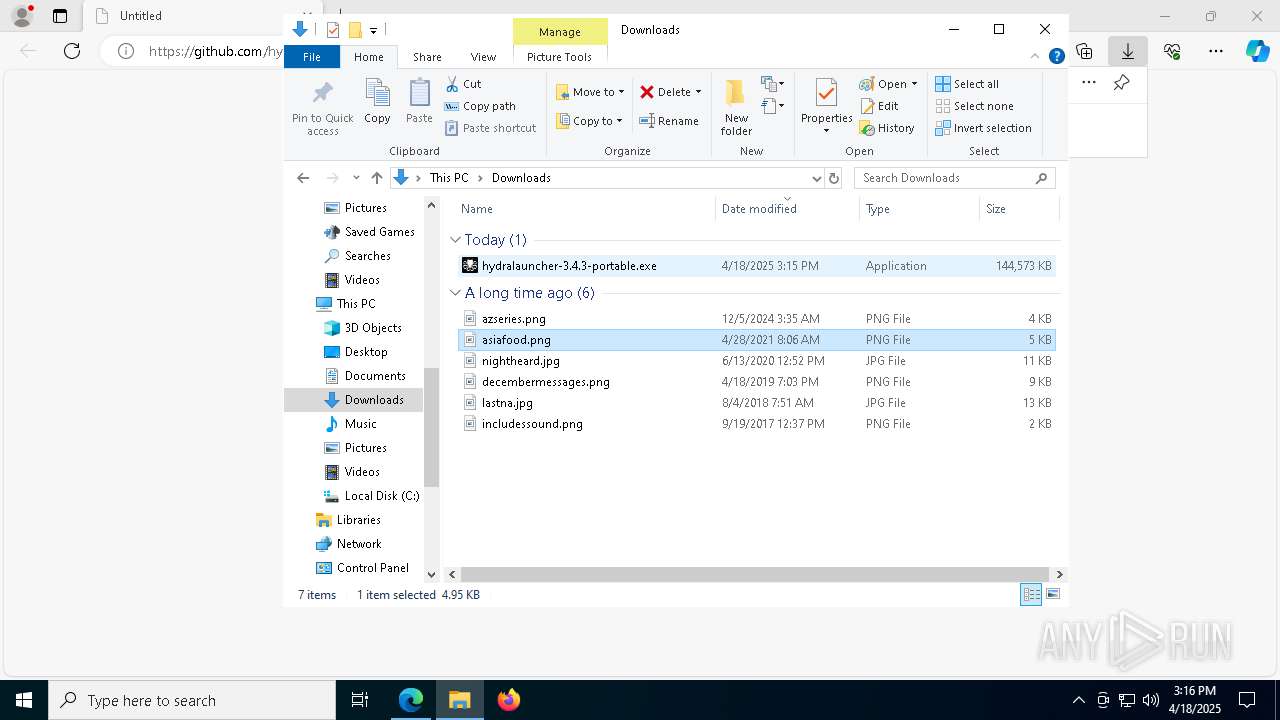
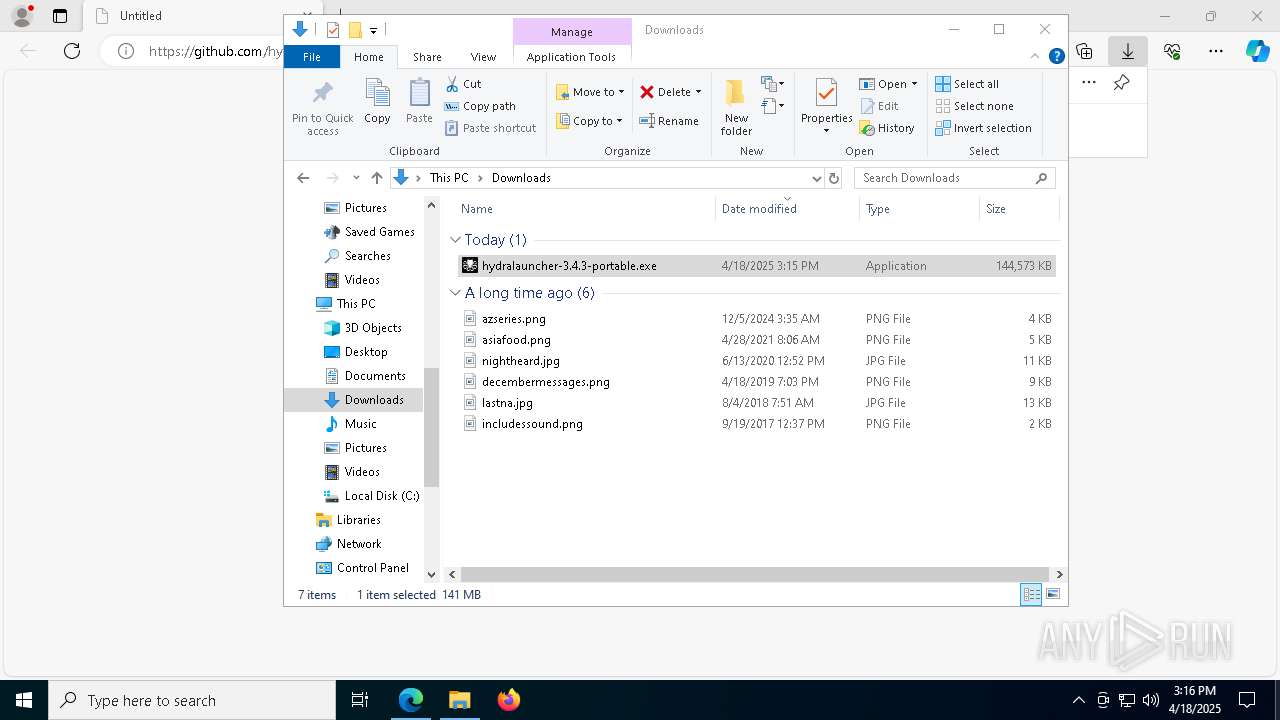
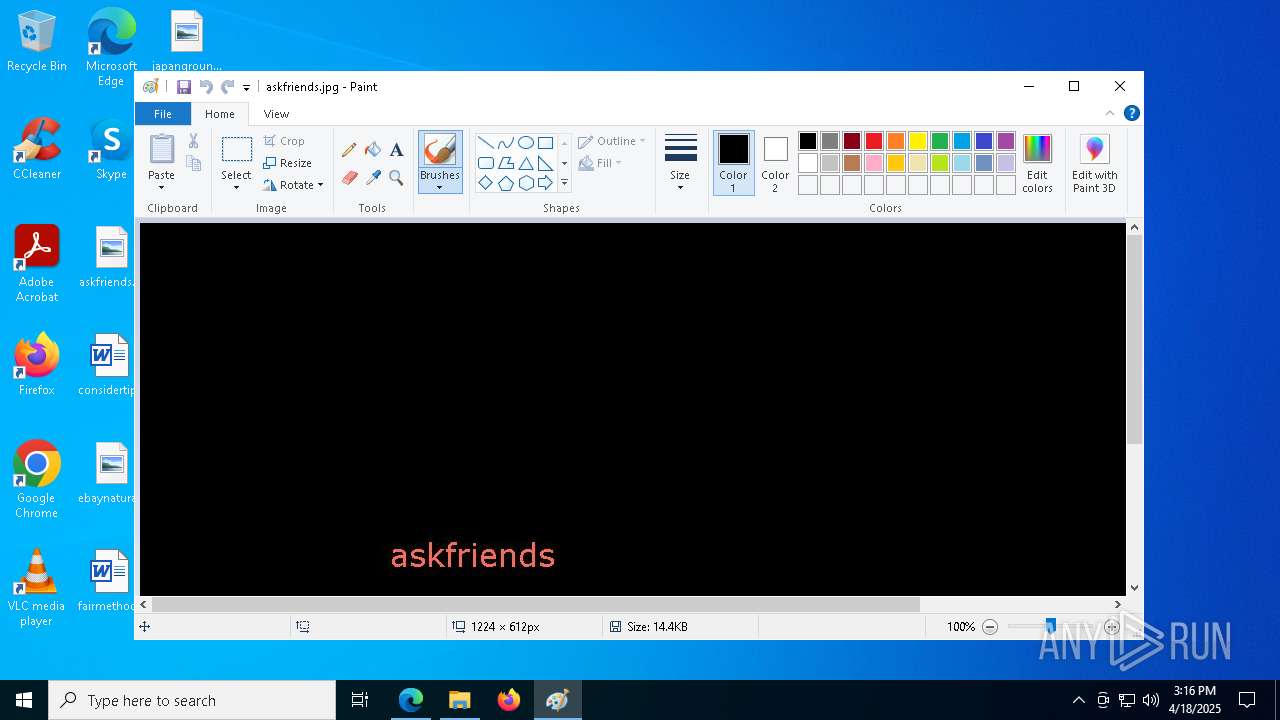
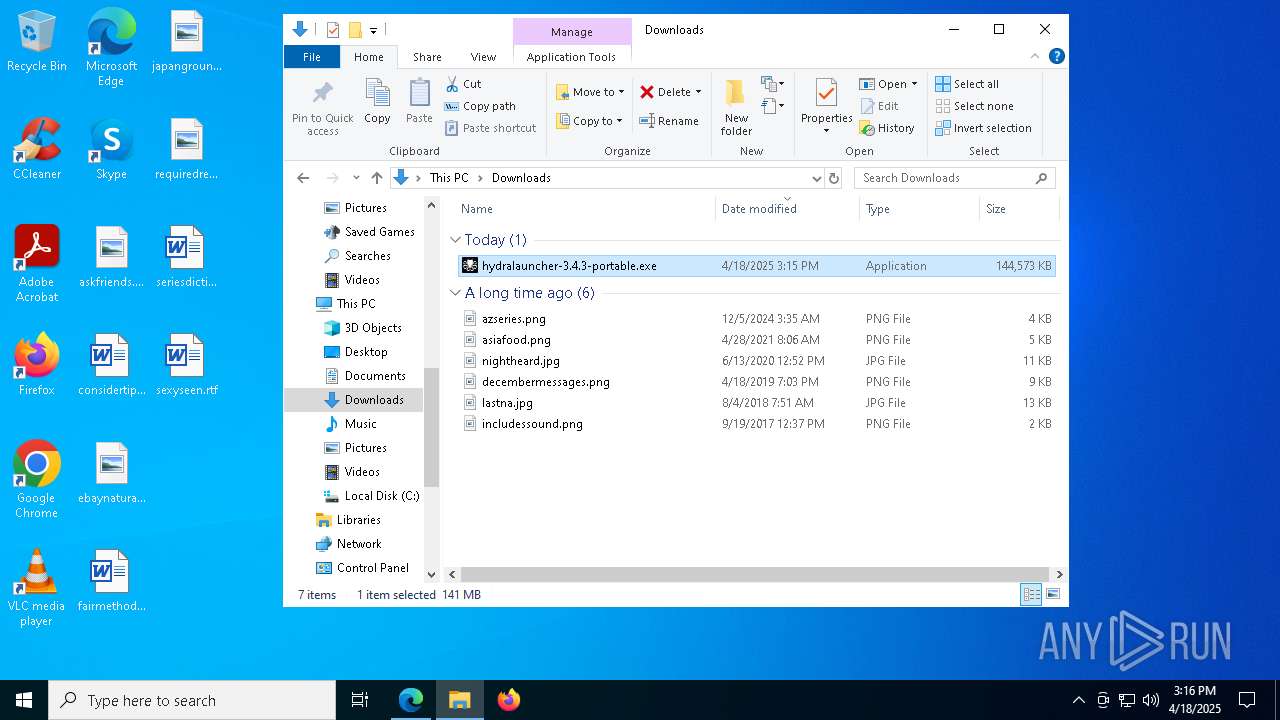
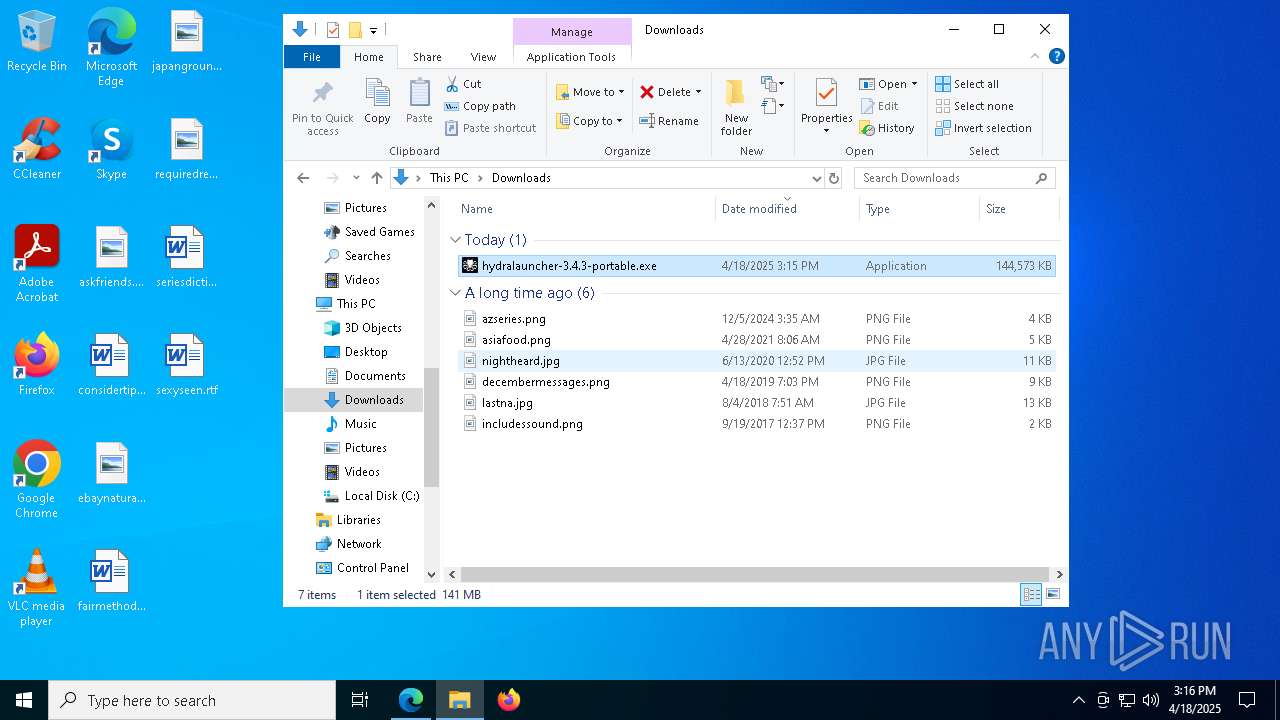
Manual execution by a user
- mspaint.exe (PID: 5744)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- mspaint.exe (PID: 516)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
The sample compiled with english language support
- hydralauncher-3.4.3-portable.exe (PID: 904)
- hydralauncher-3.4.3-portable.exe (PID: 4188)
- msedge.exe (PID: 4424)
- hydralauncher-3.4.3-portable.exe (PID: 2344)
- Hydra.exe (PID: 4016)
Reads the software policy settings
- slui.exe (PID: 4380)
- slui.exe (PID: 4180)
Checks proxy server information
- slui.exe (PID: 4180)
- Hydra.exe (PID: 4016)
- Hydra.exe (PID: 2104)
- Hydra.exe (PID: 5132)
Reads product name
- Hydra.exe (PID: 4016)
- Hydra.exe (PID: 2104)
- Hydra.exe (PID: 5132)
Process checks computer location settings
- Hydra.exe (PID: 4016)
- Hydra.exe (PID: 5132)
- Hydra.exe (PID: 2104)
- Hydra.exe (PID: 6044)
- Hydra.exe (PID: 672)
Reads the machine GUID from the registry
- Hydra.exe (PID: 4016)
- Hydra.exe (PID: 5132)
- Hydra.exe (PID: 2104)
- aria2c.exe (PID: 2524)
- hydra-python-rpc.exe (PID: 7124)
Creates files or folders in the user directory
- Hydra.exe (PID: 5132)
- Hydra.exe (PID: 2104)
- Hydra.exe (PID: 4016)
- ludusavi.exe (PID: 4948)
- Hydra.exe (PID: 6980)
Drops encrypted JS script (Microsoft Script Encoder)
- ludusavi.exe (PID: 4948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
91
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Desktop\askfriends.jpg" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Users\admin\AppData\Local\Temp\2vlsF67LldpCoaW61lpbhtf0JGT\Hydra.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\hydralauncher" --app-user-model-id=gg.hydralauncher.hydra --app-path="C:\Users\admin\AppData\Local\Temp\2vlsF67LldpCoaW61lpbhtf0JGT\resources\app.asar" --no-sandbox --no-zygote --no-sandbox --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --field-trial-handle=3208,i,1475722447217548632,12715807549968599995,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=3000 /prefetch:1 | C:\Users\admin\AppData\Local\Temp\2vlsF67LldpCoaW61lpbhtf0JGT\Hydra.exe | — | Hydra.exe | |||||||||||
User: admin Company: Los Broxas Integrity Level: HIGH Description: Hydra Version: 3.4.3 Modules
| |||||||||||||||
| 744 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | "C:\Users\admin\Downloads\hydralauncher-3.4.3-portable.exe" | C:\Users\admin\Downloads\hydralauncher-3.4.3-portable.exe | msedge.exe | ||||||||||||
User: admin Company: Los Broxas Integrity Level: MEDIUM Description: Hydra Exit code: 0 Version: 3.4.3 Modules
| |||||||||||||||
| 960 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6936 --field-trial-handle=2336,i,11880470640886663977,1495566861520433411,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7456 --field-trial-handle=2336,i,11880470640886663977,1495566861520433411,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=6384 --field-trial-handle=2336,i,11880470640886663977,1495566861520433411,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1176 | netstat -nao | C:\Windows\System32\NETSTAT.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Netstat Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3252 --field-trial-handle=2336,i,11880470640886663977,1495566861520433411,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
24 803
Read events
24 700
Write events
83
Delete events
20
Modification events
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 51891545A5912F00 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 326D2C45A5912F00 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328418 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {79A41F13-5B1F-469A-A844-BFA1F2DF6F5C} | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328418 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {5913194D-4518-4FB6-ADF2-9498F318649F} | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 615D5145A5912F00 | |||
Executable files
551
Suspicious files
3 607
Text files
4 882
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b344.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b344.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b335.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b344.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b354.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
102
DNS requests
91
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5452 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6228 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745353892&P2=404&P3=2&P4=byk7AQAWepqxPsLJDelEDrTJcd2URieeOQhZX3cJ19ISORsgsFKe0yfYTxv3zADB9HkWP2wBpDGwkGE%2bC%2bsv1w%3d%3d | DE | — | — | whitelisted |
5452 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
6228 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745353892&P2=404&P3=2&P4=byk7AQAWepqxPsLJDelEDrTJcd2URieeOQhZX3cJ19ISORsgsFKe0yfYTxv3zADB9HkWP2wBpDGwkGE%2bC%2bsv1w%3d%3d | DE | binary | 1.09 Kb | whitelisted |
6228 | svchost.exe | HEAD | 200 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745353893&P2=404&P3=2&P4=NeWnibUnkdy99xIYE0ut7WR5cht2EV1vEGWmdAt3I12xLdTV11cgudkUHakaoopRPa5uWdLnGWKvNdoQ8CjOfA%3d%3d | DE | compressed | 764 b | whitelisted |
6228 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745353893&P2=404&P3=2&P4=NeWnibUnkdy99xIYE0ut7WR5cht2EV1vEGWmdAt3I12xLdTV11cgudkUHakaoopRPa5uWdLnGWKvNdoQ8CjOfA%3d%3d | DE | binary | 4.38 Kb | whitelisted |
6228 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745353893&P2=404&P3=2&P4=NeWnibUnkdy99xIYE0ut7WR5cht2EV1vEGWmdAt3I12xLdTV11cgudkUHakaoopRPa5uWdLnGWKvNdoQ8CjOfA%3d%3d | DE | binary | 21.6 Kb | whitelisted |
6228 | svchost.exe | GET | 206 | 23.50.131.72:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5d32607d-eea9-44fc-ac55-77800b9862a5?P1=1745353893&P2=404&P3=2&P4=NeWnibUnkdy99xIYE0ut7WR5cht2EV1vEGWmdAt3I12xLdTV11cgudkUHakaoopRPa5uWdLnGWKvNdoQ8CjOfA%3d%3d | DE | binary | 2.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4628 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7352 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7352 | msedge.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
7352 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7352 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7124 | hydra-python-rpc.exe | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |
6980 | Hydra.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6980 | Hydra.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6980 | Hydra.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6980 | Hydra.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6980 | Hydra.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
6980 | Hydra.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |