| URL: | https://urldefense.proofpoint.com/v2/url?u=https-3A__learn.broadcom.com_e2t_c_-2AN650QyqBG9ZJW8f3ytw1gj59Z0_-2AW1Kb-2D3H9c3fXfV-5FN4qY595R3c0_5_f18dQhb0Sq5y8YHtvCN7Y0QqxJmjWyW243DQh1GndWfW7tWqhv63XfM8W5q9kQw8DsQm8MS9KdyQbSM2N1lRb6z3lqD3W3SQHLW2-2DCQXLW3Mdr3j2nVpwdW3VNQ7W49MJhhW3SLYcb49JfBwW3C8bwH3-5F3J-2DzW7QQY1G1ZXS-2D1VkkDH92FDPPfW35L-2D3F7xR9-5FsW2Vjhb05bPxTtW7nb5ds8YdqVlW7m9-5Fzt1FpGmLW7w4nLl3yy-2DR9W7xwSFG1CcbxHW8PPgDV2hBMKRW5KFQFN5-2DlMJcW5tl0jY42cx-2DCW5f4N1y3WqWtmW38ZWzh6mRhLcW3N-5FhWm4GgzP6W6yKDxp3Y510SW3GS37Q2HR4JxW3NPpXr4RZhpRW4scsPS3H0mk5W5FZTdK51ltQyW4mX-5FyL2x-2D3wmW6QzcFm6Zz9YTW38jxhk3BR0v2W82G-2DSP4JS-2DKGW8PXPqR3ygvH8W8c3fN-2D5lDQRzW2SBDGb2PjknlW7Bk1kN1HlYJHN7zszmj10NbdW5x6QZh3qVnTjN81w-5FPtKMxTzVmcVHF1-5FZlgQW3KqV4s4sH3v1N3pxWL3cTSRKVcSH611qGgpm102&d=DwMFaQ&c=udBTRvFvXC5Dhqg7UHpJlPps3mZ3LRxpb6__0PomBTQ&r=5RmU8M7E3ECkqTmoaML_EjRZH4qtg9w-PW8XRRLYa1w&m=Buhm7Sh4bUpdDIa6u4OXpfV45j8mVjOPM9ThBITajIY&s=5rIkE27V8ptzdNS-klm2eacX9ylNy6vDQJGf4sKLif0&e= |
| Full analysis: | https://app.any.run/tasks/3a1b604b-44cc-4962-89b4-76f1d2ba227e |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 14:18:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C09F6826B23807A3C37F2FF46AA3DA84 |
| SHA1: | 9535C0A618B19BF91B2FA7F8E1F3F91FB8F25708 |
| SHA256: | 3093BD14C24F4197A82DFC895624DBC72136E07D218A7D154237DA29E77F3050 |
| SSDEEP: | 24:2ctYJpsnQ9EL9WzVl7sQz1yWDddHusiuVNiQxOoNt:5ysnDL9W77lByWWzuuqOUt |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2984)
INFO
Application launched itself
- chrome.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4125808406830759957,12853412734896277655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3478544722195946334 --mojo-platform-channel-handle=3512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4125808406830759957,12853412734896277655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8114389030174241238 --mojo-platform-channel-handle=3800 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4125808406830759957,12853412734896277655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11041838701678417769 --mojo-platform-channel-handle=3560 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4125808406830759957,12853412734896277655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1703467186530864882 --mojo-platform-channel-handle=3500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4125808406830759957,12853412734896277655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10161028754703855727 --mojo-platform-channel-handle=3676 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4125808406830759957,12853412734896277655,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8168946403900881497 --mojo-platform-channel-handle=1548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,4125808406830759957,12853412734896277655,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=884697720164117127 --mojo-platform-channel-handle=2920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,4125808406830759957,12853412734896277655,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6558853749778125213 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x70fea9d0,0x70fea9e0,0x70fea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2456 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,4125808406830759957,12853412734896277655,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=586725091826031505 --mojo-platform-channel-handle=3944 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
598
Read events
512
Write events
81
Delete events
5
Modification events
| (PID) Process: | (2824) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2984-13210179489777250 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
21
Text files
95
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\791579d5-df8f-44b9-8ba9-afa6f52a1a7b.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF378c17.TMP | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF378c56.TMP | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF378c17.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
40
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1892 | chrome.exe | GET | 200 | 104.17.112.180:80 | http://learn.broadcom.com/hs/hsstatic/content_shared_assets/static-1.4091/css/public_common.css | US | text | 3.48 Kb | shared |
1892 | chrome.exe | GET | 200 | 172.217.16.170:80 | http://fonts.googleapis.com/css?family=Lato:300,400,300italic,400italic | US | text | 485 b | whitelisted |
1892 | chrome.exe | GET | 200 | 104.17.69.176:80 | http://js.hs-analytics.net/analytics/1565704800000/5156294.js | US | text | 24.6 Kb | whitelisted |
1892 | chrome.exe | GET | 301 | 104.17.184.73:80 | http://js.hsforms.net/forms/v2-debug.js | US | — | — | whitelisted |
1892 | chrome.exe | GET | 200 | 104.17.112.180:80 | http://learn.broadcom.com/hs/hsstatic/cos-i18n/static-1.10/bundles/project.js | US | text | 561 b | shared |
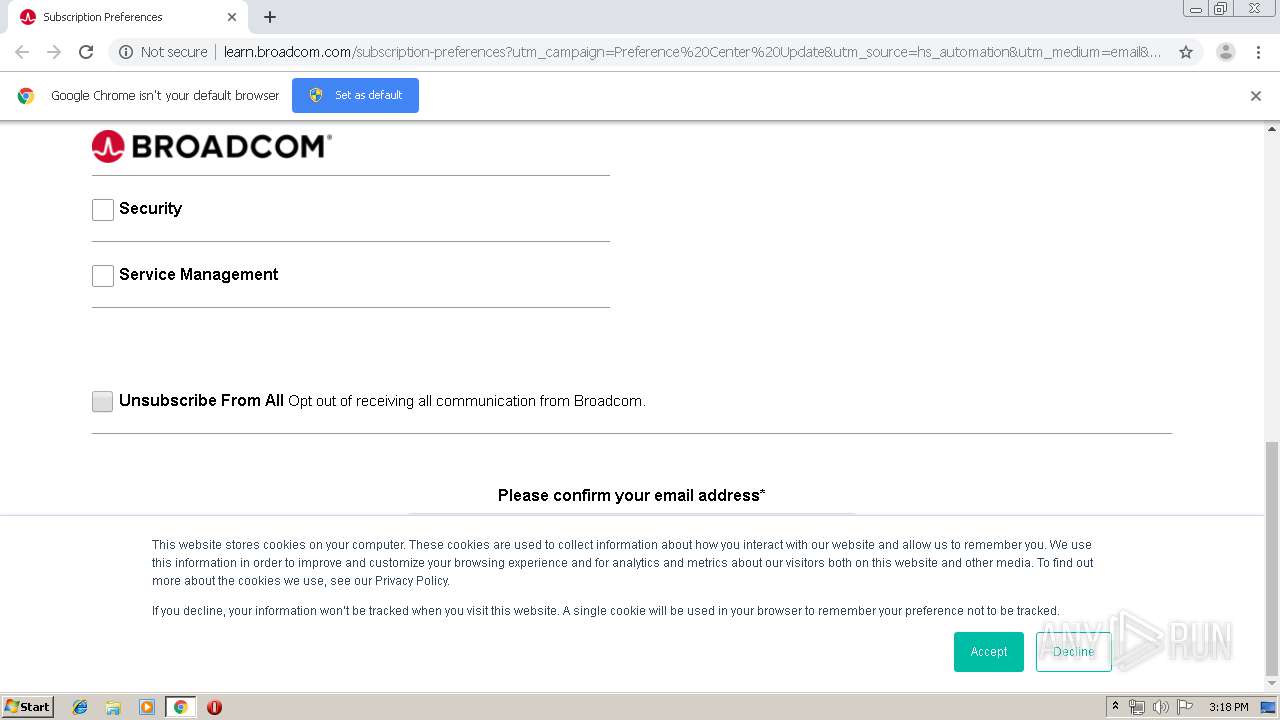
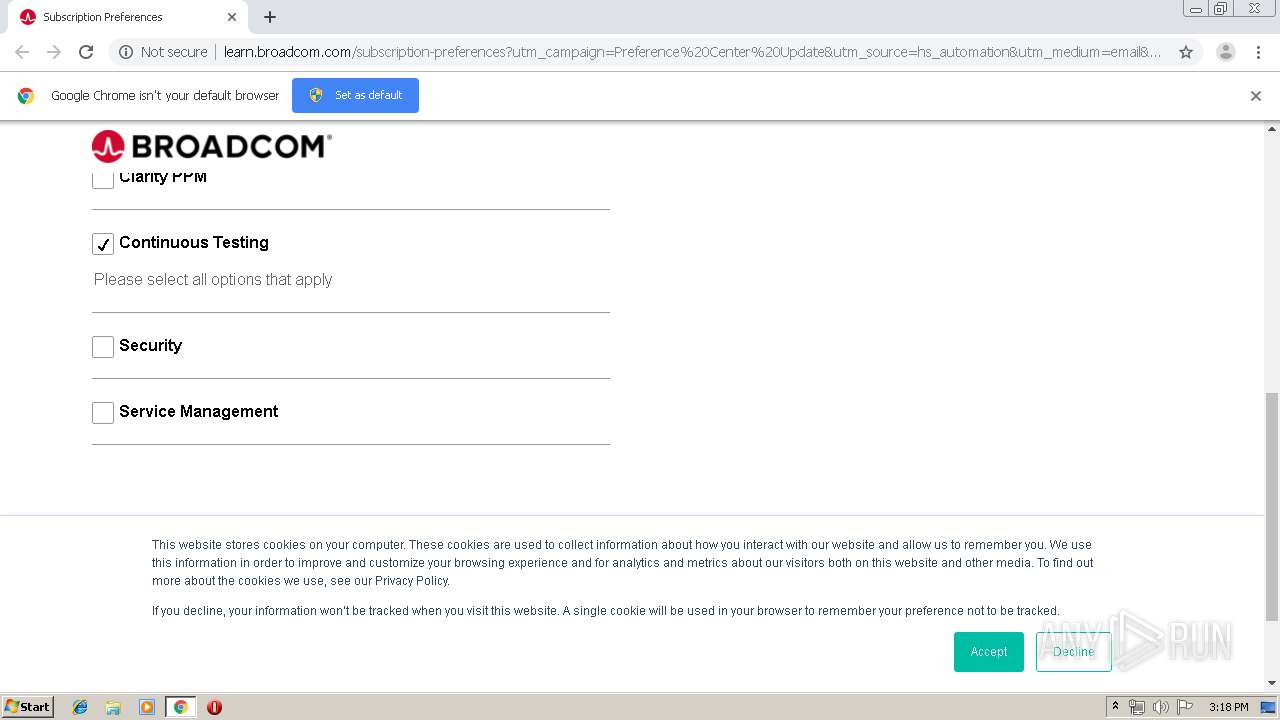
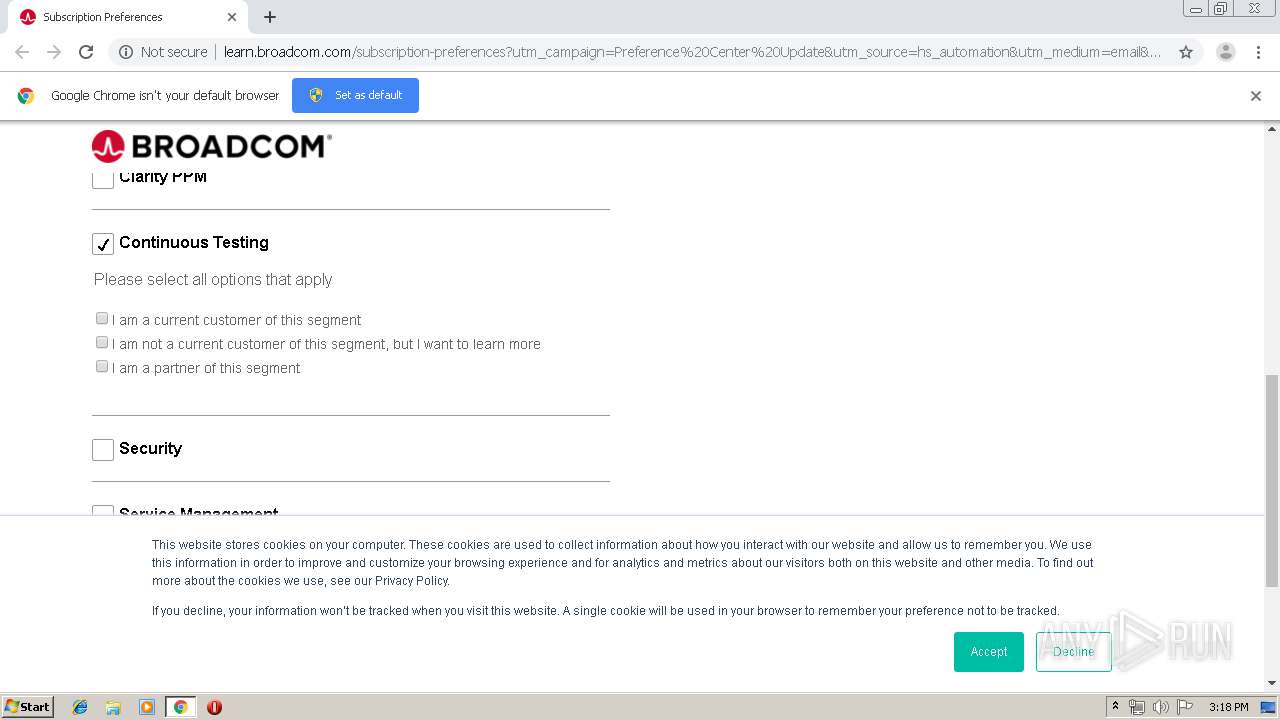
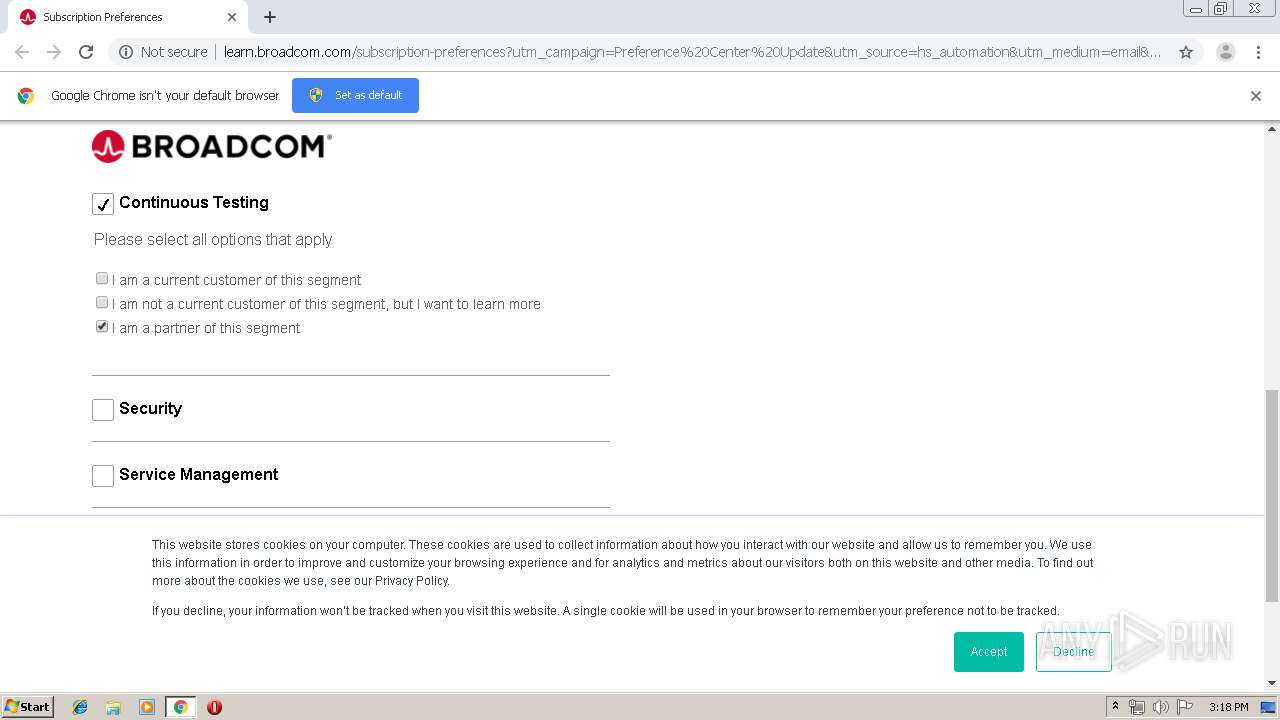
1892 | chrome.exe | GET | 200 | 104.17.112.180:80 | http://learn.broadcom.com/subscription-preferences?utm_campaign=Preference%20Center%20Update&utm_source=hs_automation&utm_medium=email&utm_content=75585146&_hsenc=p2ANqtz--c-VESL7iIeyO4jyBD-0usIalKOvjfC8PpEoTtYXdvtyifITypX0xowoI3YfaIfLGmt8IBKb00xev2g4pDoJiojRZDag&_hsmi=75585146 | US | html | 4.24 Kb | shared |
1892 | chrome.exe | GET | 200 | 104.17.112.180:80 | http://learn.broadcom.com/hs/scriptloader/5156294.js | US | text | 228 b | shared |
1892 | chrome.exe | GET | 200 | 104.17.243.204:80 | http://cdn2.hubspot.net/hub/-1/hub_generated/template_assets/1495141902003/hubspot_default/shared/responsive/layout.min.css | US | text | 1.26 Kb | whitelisted |
1892 | chrome.exe | GET | 200 | 172.217.16.170:80 | http://fonts.googleapis.com/css?family=Montserrat:700,400 | US | text | 565 b | whitelisted |
1892 | chrome.exe | GET | 200 | 172.217.23.131:80 | http://fonts.gstatic.com/s/montserrat/v14/JTURjIg1_i6t8kCHKm45_dJE3gnD_g.woff2 | US | woff2 | 19.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1892 | chrome.exe | 172.217.18.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1892 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1892 | chrome.exe | 172.217.22.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
1892 | chrome.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
1892 | chrome.exe | 104.17.112.180:80 | learn.broadcom.com | Cloudflare Inc | US | shared |
1892 | chrome.exe | 104.17.184.73:80 | js.hsforms.net | Cloudflare Inc | US | shared |
1892 | chrome.exe | 104.17.243.204:80 | cdn2.hubspot.net | Cloudflare Inc | US | shared |
1892 | chrome.exe | 172.217.16.170:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1892 | chrome.exe | 172.217.21.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1892 | chrome.exe | 104.17.120.180:443 | designers.hubspot.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
urldefense.proofpoint.com |
| whitelisted |
accounts.google.com |
| shared |
learn.broadcom.com |
| unknown |
www.google.com |
| malicious |
cdn2.hubspot.net |
| whitelisted |
js.hsforms.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
designers.hubspot.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
Threats
Process | Message |
|---|---|
chrome.exe | Error - |
chrome.exe | Too long restart command line passed |
chrome.exe |