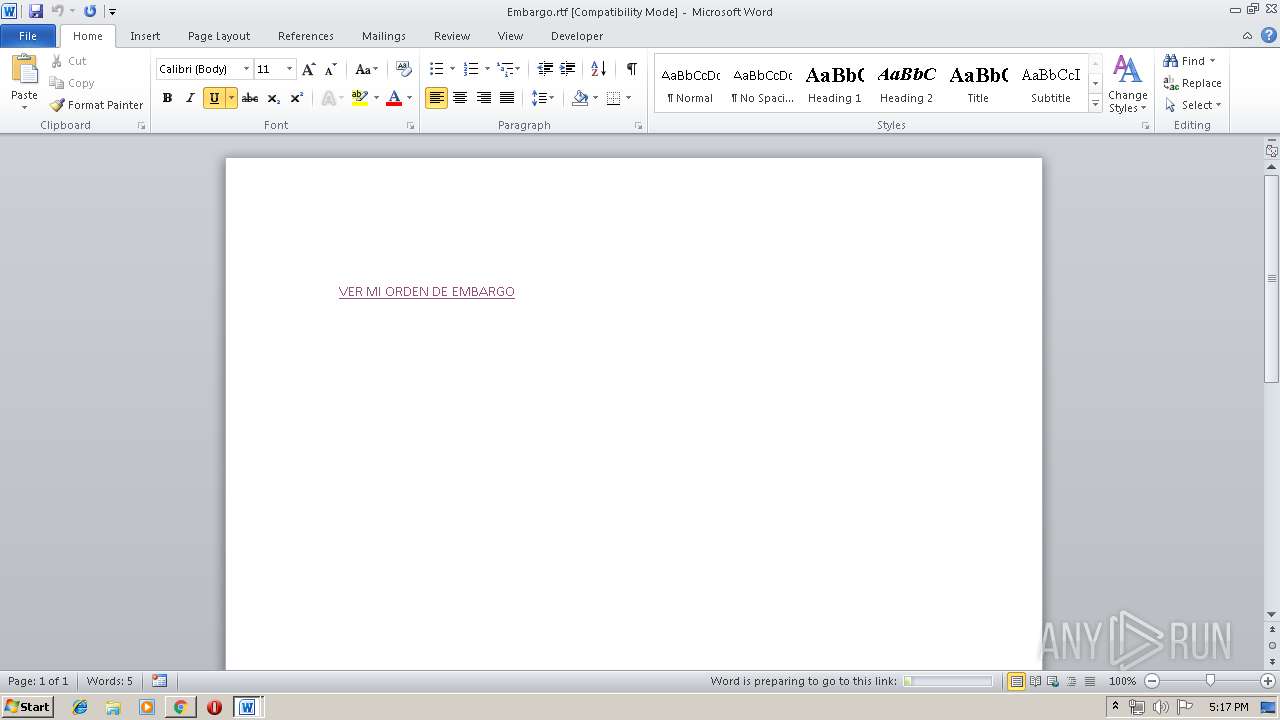
| File name: | Embargo.rtf |
| Full analysis: | https://app.any.run/tasks/9c353062-8903-4118-b67e-3d4541feca57 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 16:16:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | C38C4B22F46E83C63D85AF1BC1DAE826 |
| SHA1: | 12D4C868505037A28F3684716D023C6713EBC326 |
| SHA256: | 308A67ED89716A959752514B18DFD2CE3250B56271C23E259C710F1BBEE62503 |
| SSDEEP: | 384:lugKf+2OrN7vQtV6nEFPVi6rGsqWqtZccVF3V7Ly4nMNLoJ0t:lugKfYIQbtZVWNLoJ0t |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- WINWORD.EXE (PID: 2948)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2984)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2948)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2948)
Application launched itself
- chrome.exe (PID: 2984)
Manual execution by user
- chrome.exe (PID: 2984)
Reads settings of System Certificates
- chrome.exe (PID: 2984)
Reads Internet Cache Settings
- chrome.exe (PID: 2984)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
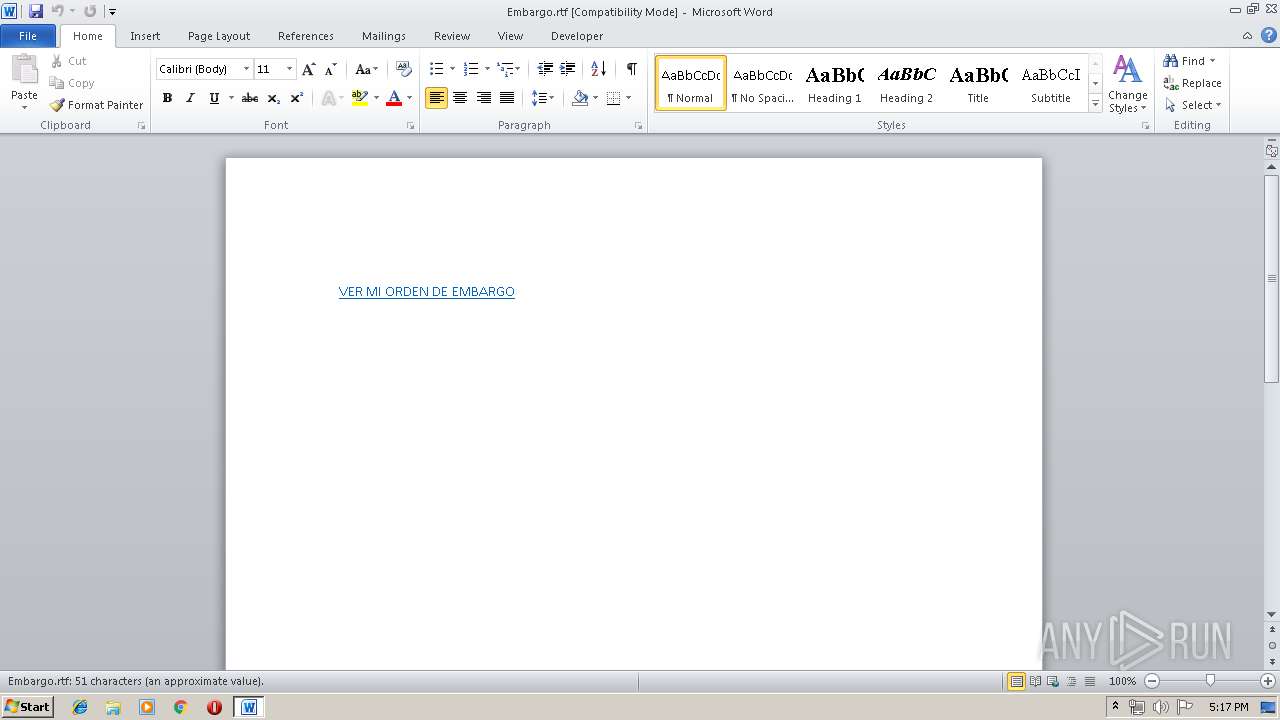
| LastModifiedBy: | Centro de Servicios Judiciales |
|---|---|
| CreateDate: | 2019:05:28 22:57:00 |
| ModifyDate: | 2019:06:18 10:54:00 |
| RevisionNumber: | 16 |
| TotalEditTime: | 13 minutes |
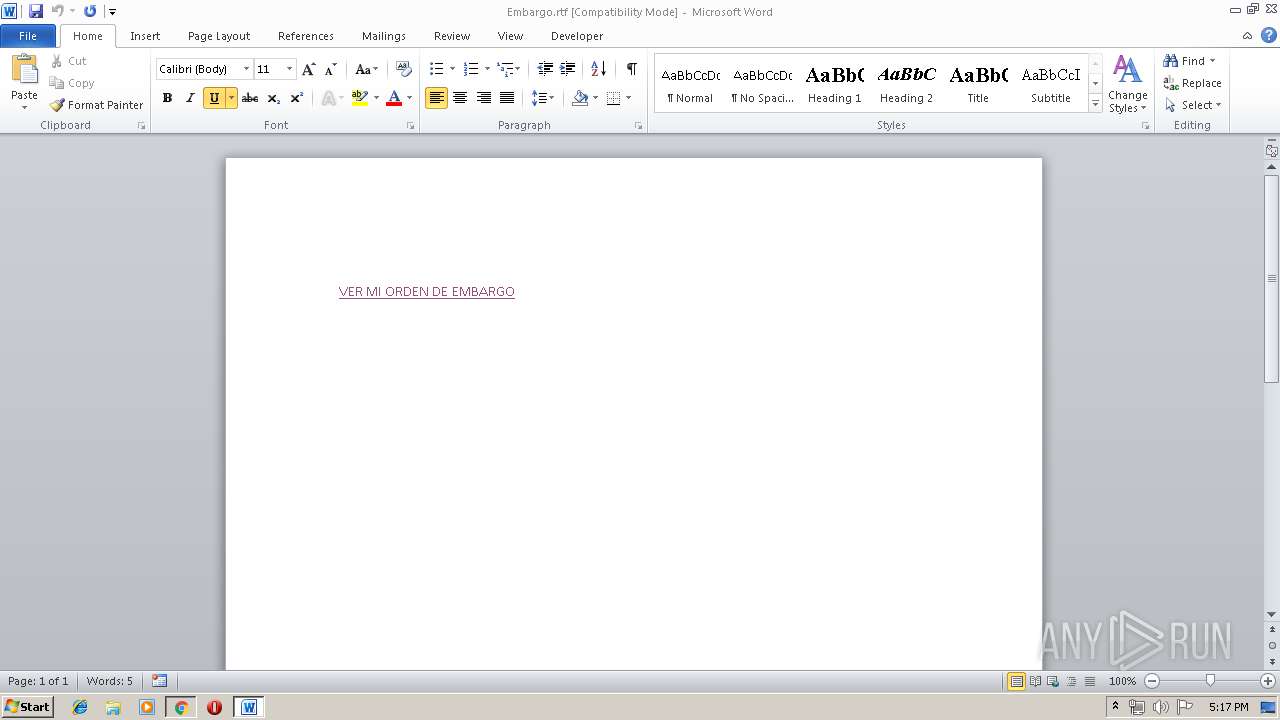
| Pages: | 1 |
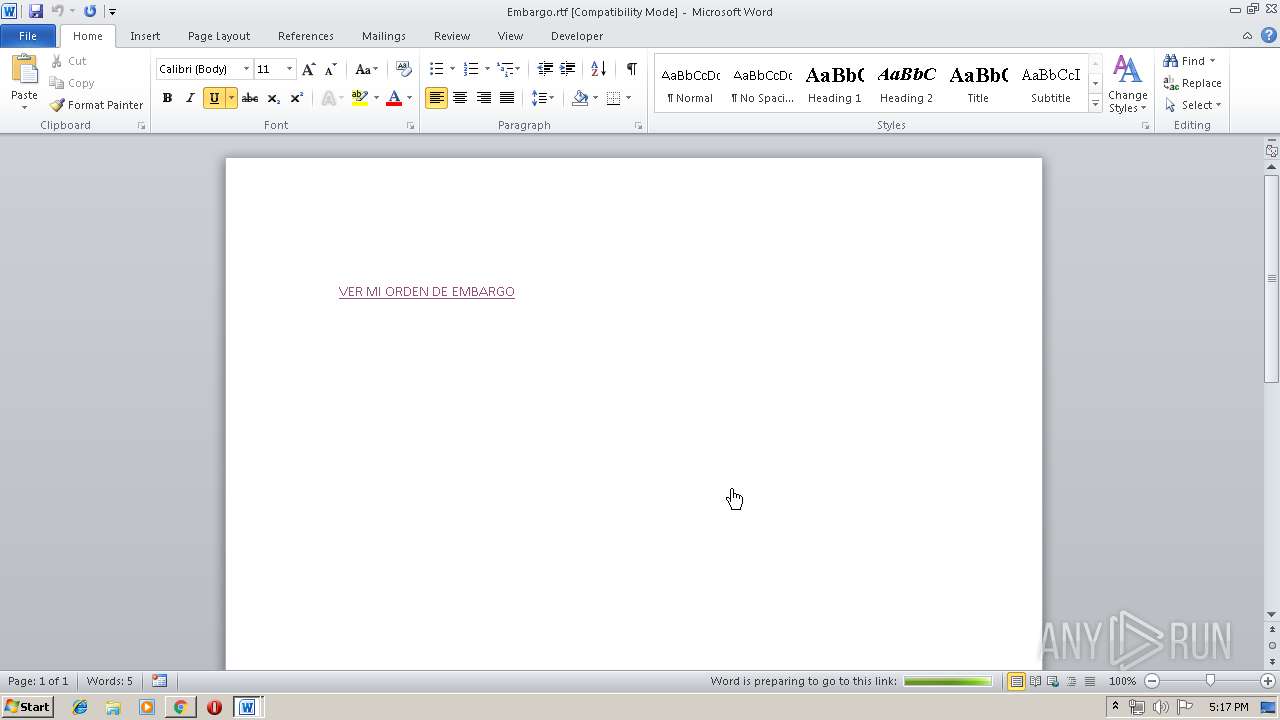
| Words: | 9 |
| Characters: | 53 |
| CharactersWithSpaces: | 61 |
| InternalVersionNumber: | 105 |
Total processes
56
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,11239468760062132102,7141305336353322920,131072 --enable-features=PasswordImport --service-pipe-token=18033408403165902451 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18033408403165902451 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2032 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,11239468760062132102,7141305336353322920,131072 --enable-features=PasswordImport --service-pipe-token=894477369748243661 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=894477369748243661 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,11239468760062132102,7141305336353322920,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11851806765866281478 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11851806765866281478 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,11239468760062132102,7141305336353322920,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8224313176276773052 --mojo-platform-channel-handle=4884 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,11239468760062132102,7141305336353322920,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11139003612442100985 --mojo-platform-channel-handle=972 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,11239468760062132102,7141305336353322920,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3878360579038781915 --mojo-platform-channel-handle=4108 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,11239468760062132102,7141305336353322920,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9676627196349992150 --mojo-platform-channel-handle=4248 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,11239468760062132102,7141305336353322920,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3958054907486578705 --mojo-platform-channel-handle=2228 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,11239468760062132102,7141305336353322920,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5357503766557208257 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5357503766557208257 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2948 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Embargo.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 624
Read events
919
Write events
695
Delete events
10
Modification events
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2"= |
Value: 32223D00840B0000010000000000000000000000 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1322450974 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451088 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322451089 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 840B0000963BDF6EBA26D50100000000 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | +#= |
Value: 2B233D00840B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | +#= |
Value: 2B233D00840B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2948) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
68
Text files
166
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2948 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE12.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2948 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@mediafire[1].txt | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\360d19c1-aa70-4565-9480-a7f0d18785bb.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
36
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
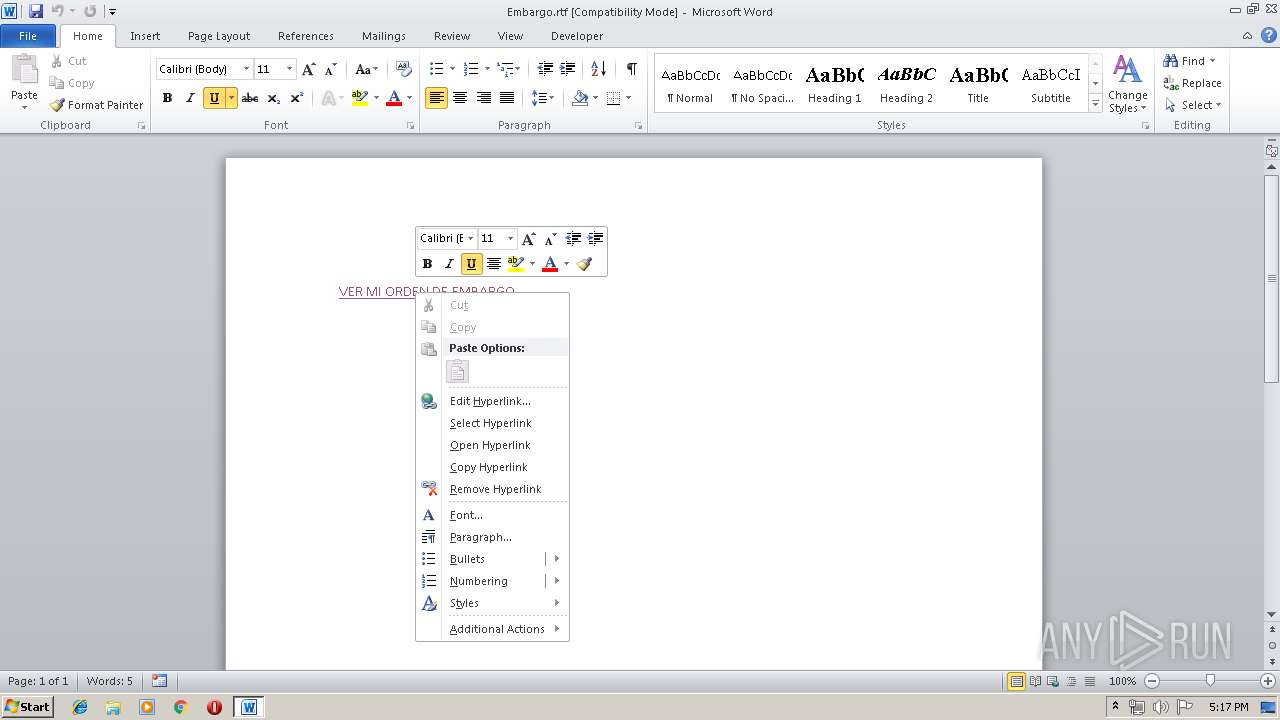
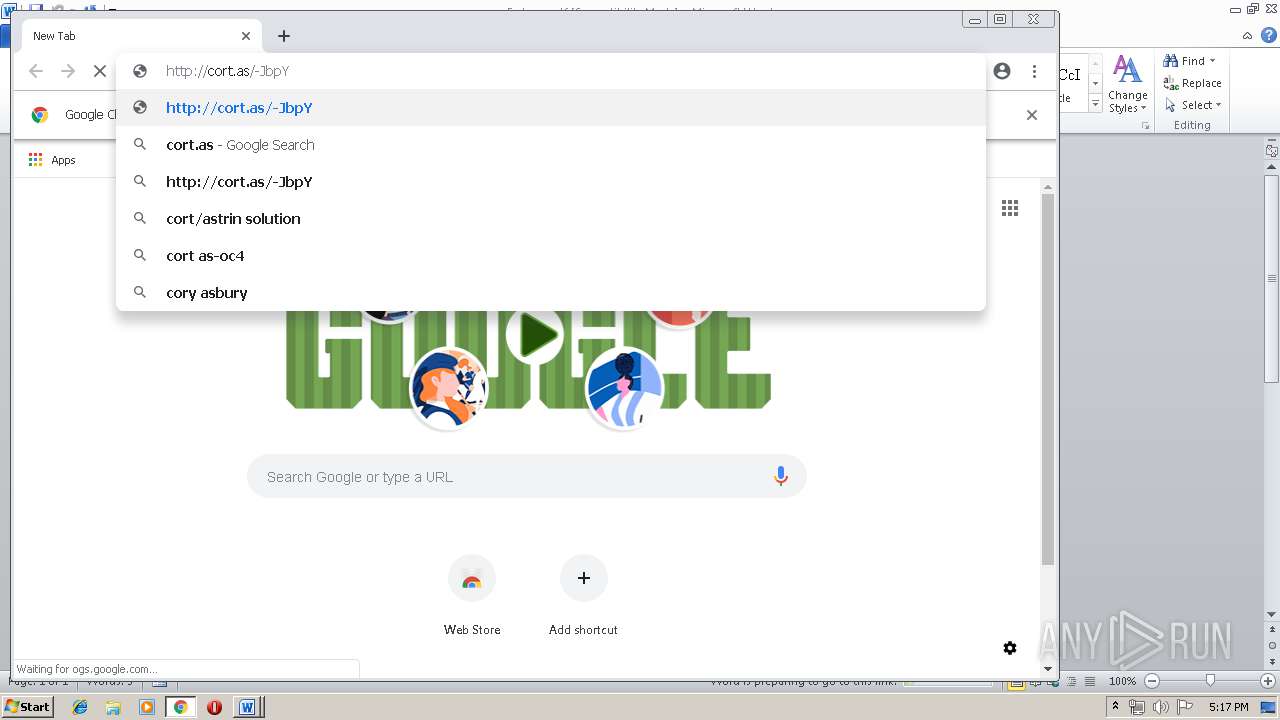
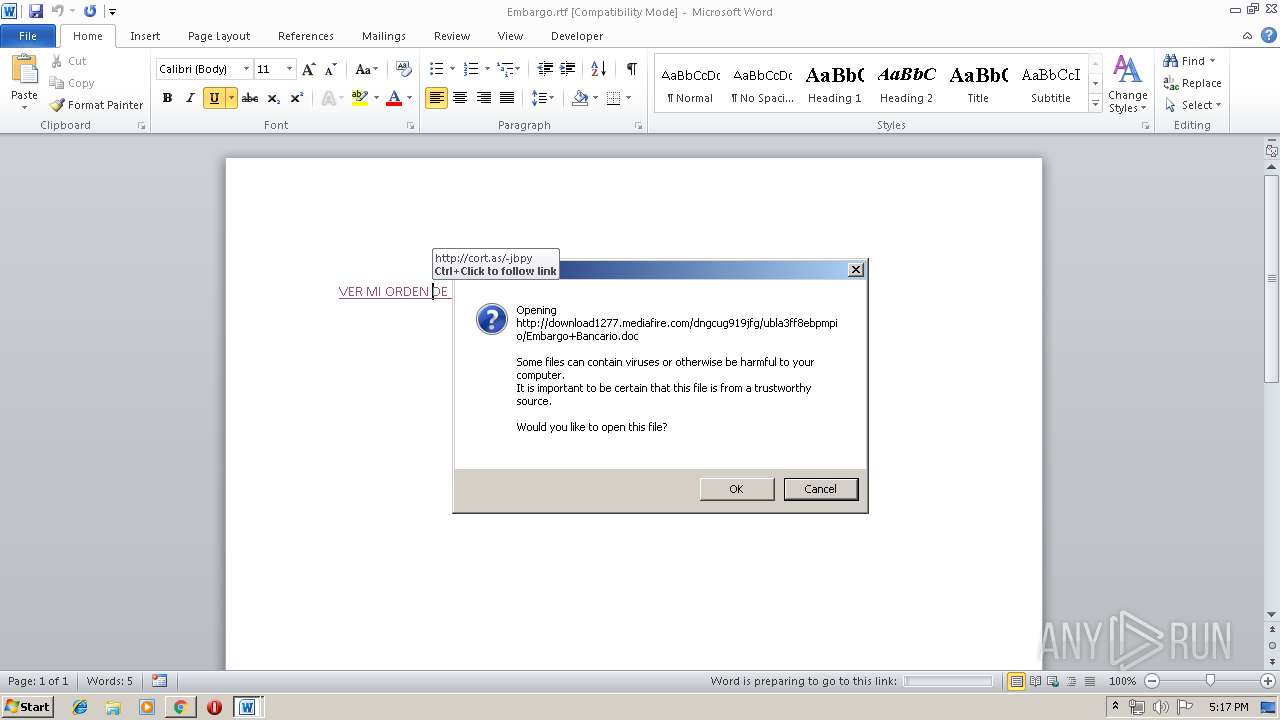
2948 | WINWORD.EXE | GET | 302 | 104.19.194.29:80 | http://www.mediafire.com/file/ubla3ff8ebpmpio/Embargo_Bancario.doc/file | US | — | — | shared |
2948 | WINWORD.EXE | GET | — | 205.196.122.218:80 | http://download1277.mediafire.com/dngcug919jfg/ubla3ff8ebpmpio/Embargo+Bancario.doc | US | — | — | malicious |
2984 | chrome.exe | GET | 302 | 104.19.194.29:80 | http://www.mediafire.com/file/ubla3ff8ebpmpio/Embargo_Bancario.doc/file | US | — | — | shared |
2948 | WINWORD.EXE | HEAD | 302 | 104.19.194.29:80 | http://www.mediafire.com/file/ubla3ff8ebpmpio/Embargo_Bancario.doc/file | US | — | — | shared |
2948 | WINWORD.EXE | HEAD | 200 | 205.196.122.218:80 | http://download1277.mediafire.com/spp9i9pkch3g/ubla3ff8ebpmpio/Embargo+Bancario.doc | US | — | — | malicious |
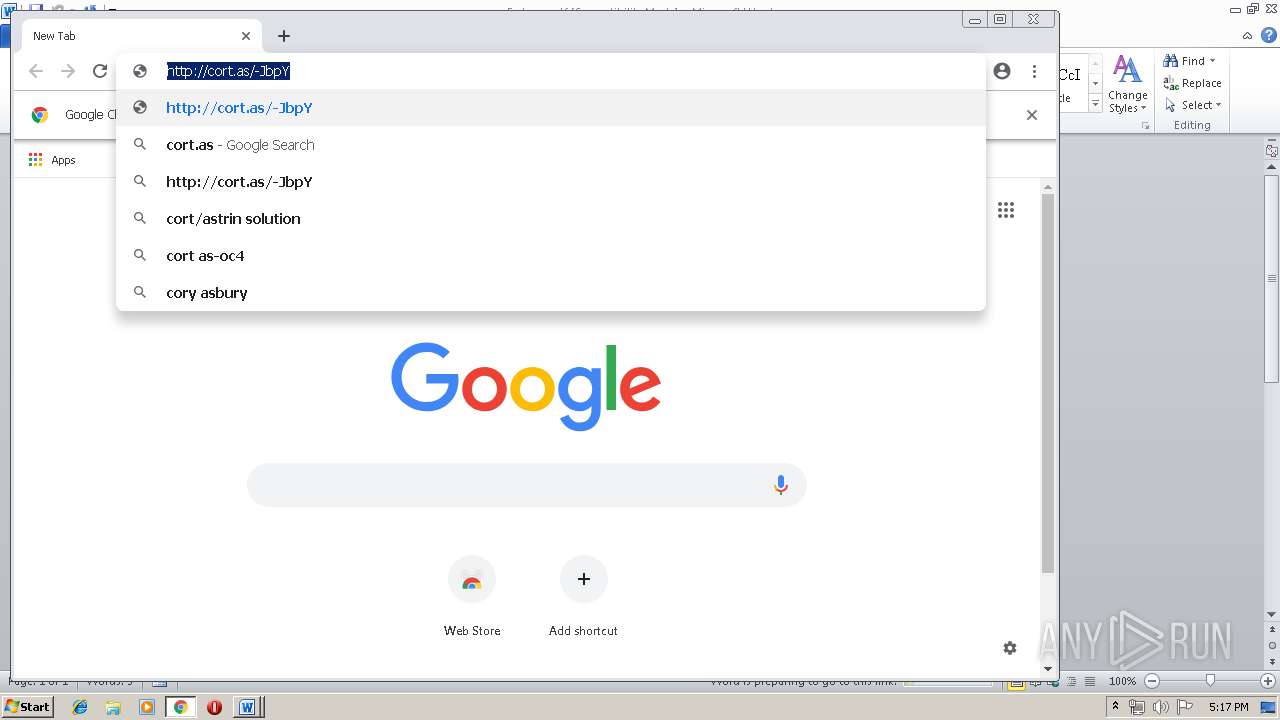
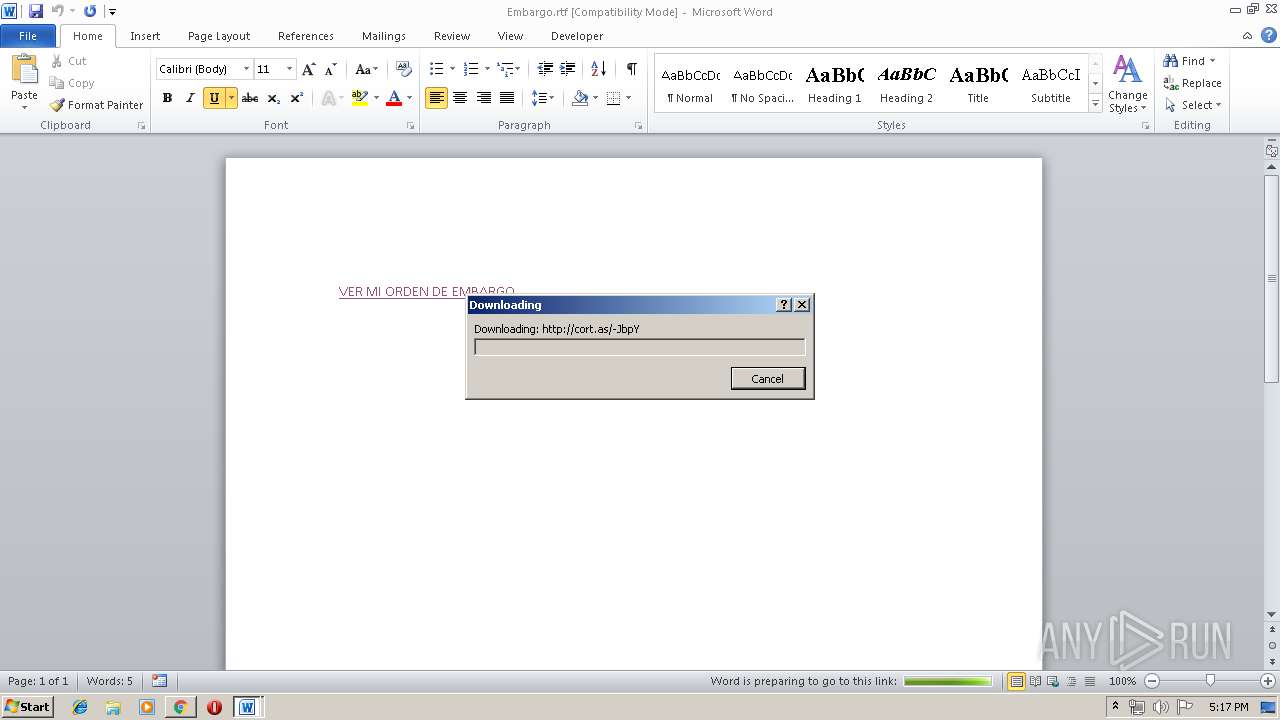
2948 | WINWORD.EXE | GET | 301 | 91.216.63.240:80 | http://cort.as/-JbpY | ES | html | 279 b | unknown |
2984 | chrome.exe | GET | 302 | 173.194.76.198:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
2948 | WINWORD.EXE | GET | 200 | 205.196.122.218:80 | http://download1277.mediafire.com/dngcug919jfg/ubla3ff8ebpmpio/Embargo+Bancario.doc | US | text | 142 Kb | malicious |
2948 | WINWORD.EXE | OPTIONS | 301 | 91.216.63.240:80 | http://cort.as/ | ES | html | 197 b | unknown |
2984 | chrome.exe | GET | 301 | 91.216.63.240:80 | http://cort.as/-JbpY | ES | html | 279 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2948 | WINWORD.EXE | 91.216.63.240:80 | cort.as | Ediciones El Pais, S.L. | ES | unknown |
2948 | WINWORD.EXE | 104.19.194.29:80 | www.mediafire.com | Cloudflare Inc | US | shared |
2948 | WINWORD.EXE | 205.196.122.218:80 | download1277.mediafire.com | MediaFire, LLC | US | malicious |
2984 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.22.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
2984 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 91.216.63.240:80 | cort.as | Ediciones El Pais, S.L. | ES | unknown |
— | — | 205.196.122.218:80 | download1277.mediafire.com | MediaFire, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cort.as |
| unknown |
www.mediafire.com |
| shared |
download1277.mediafire.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |