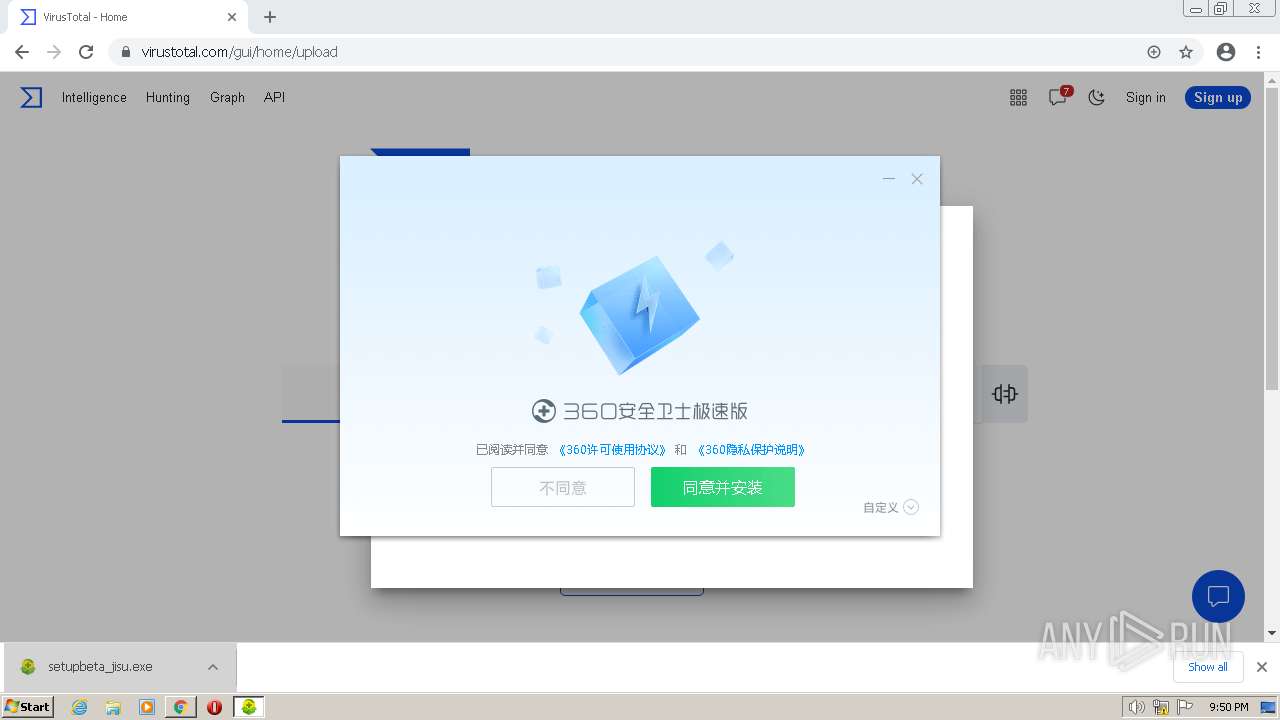
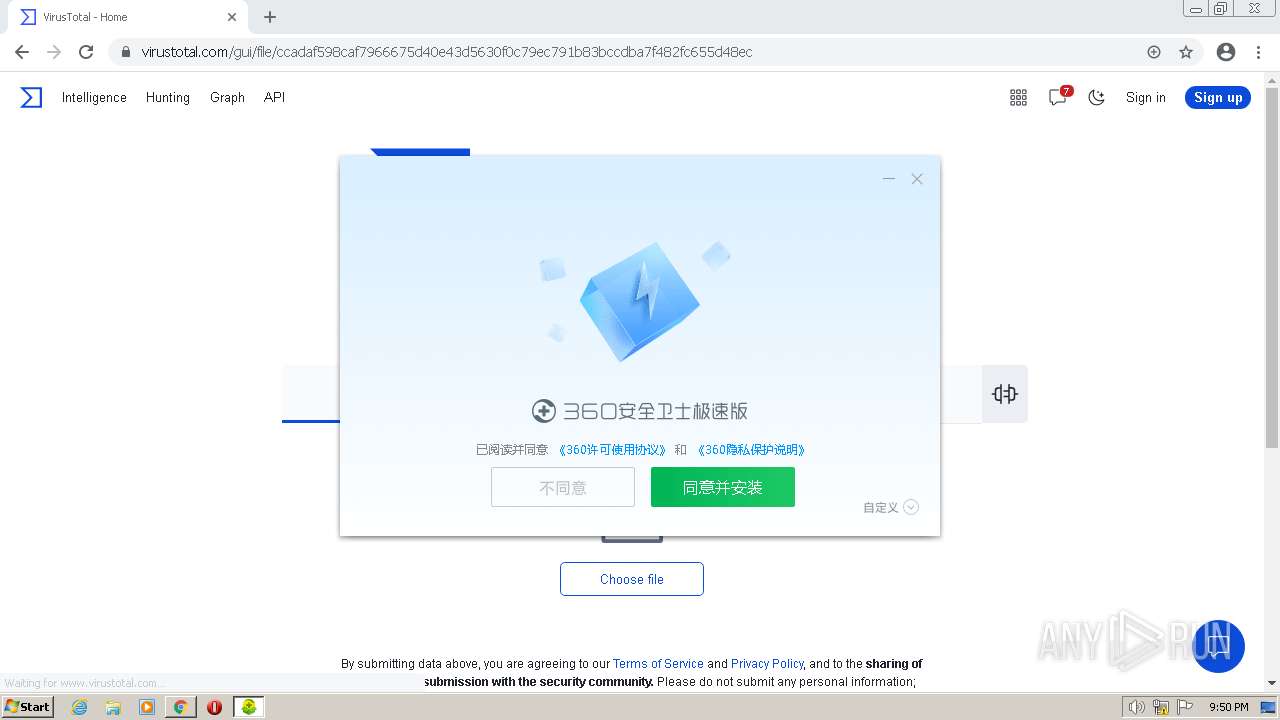
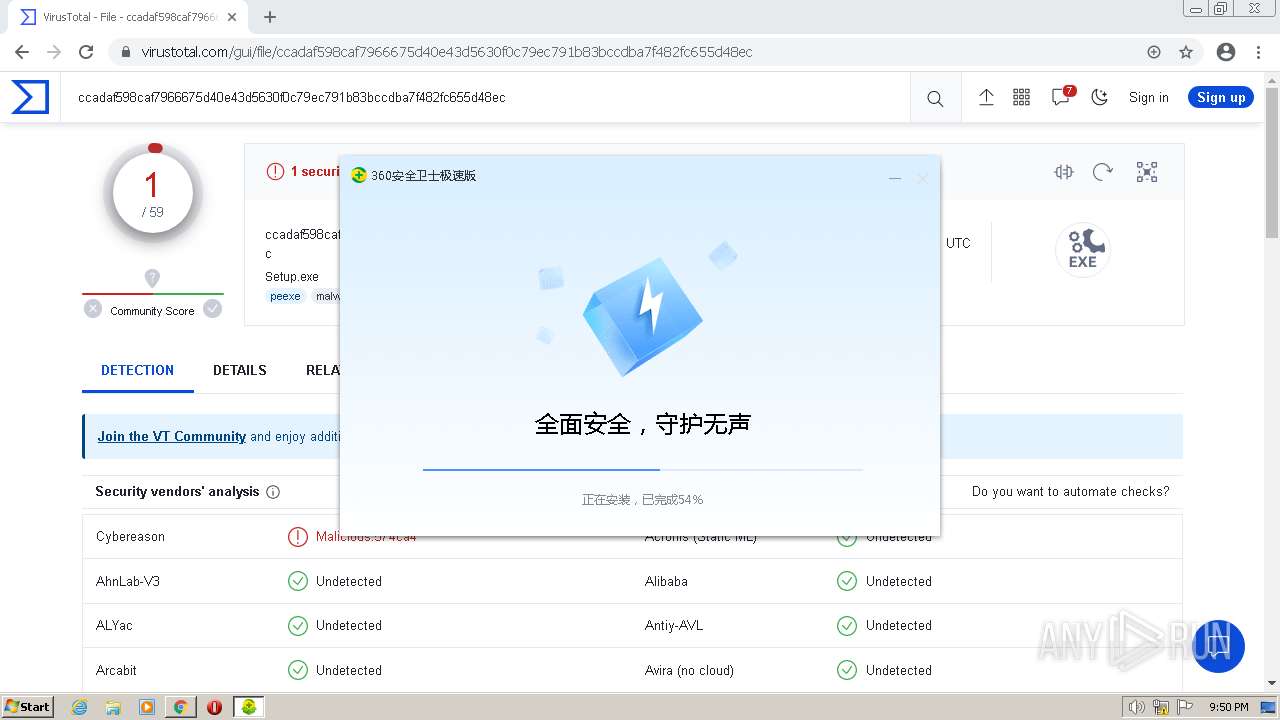
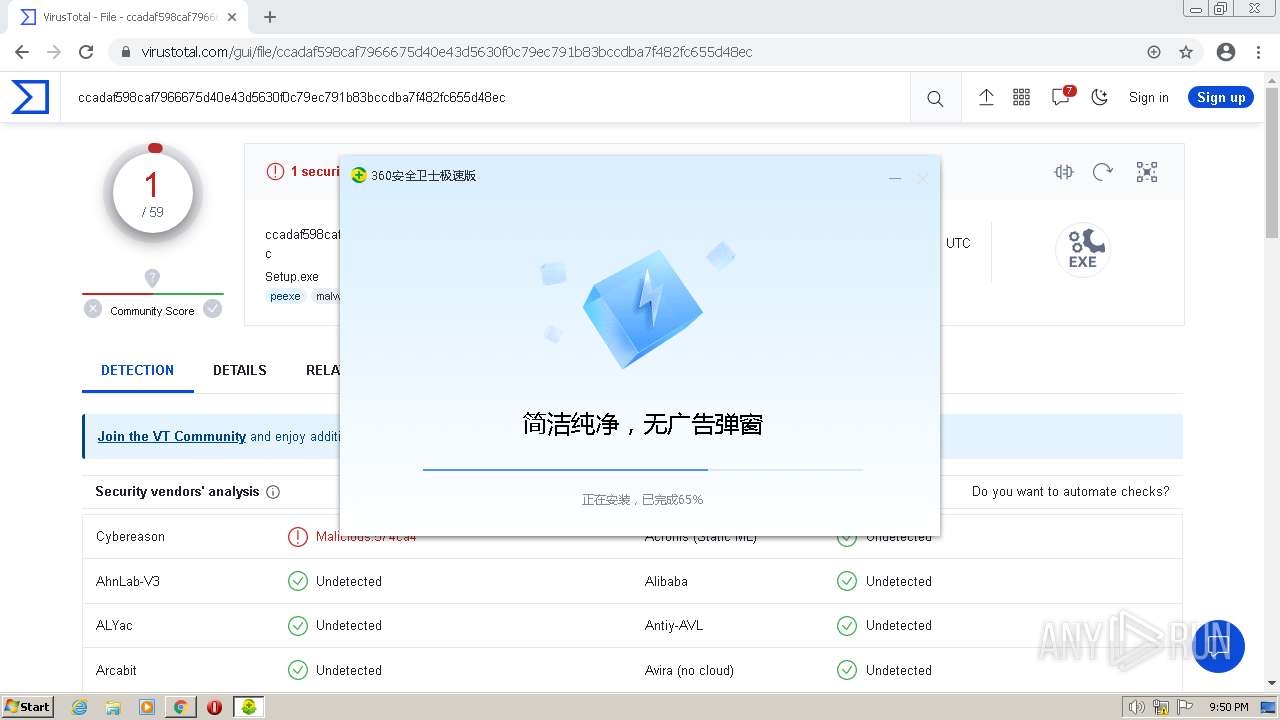
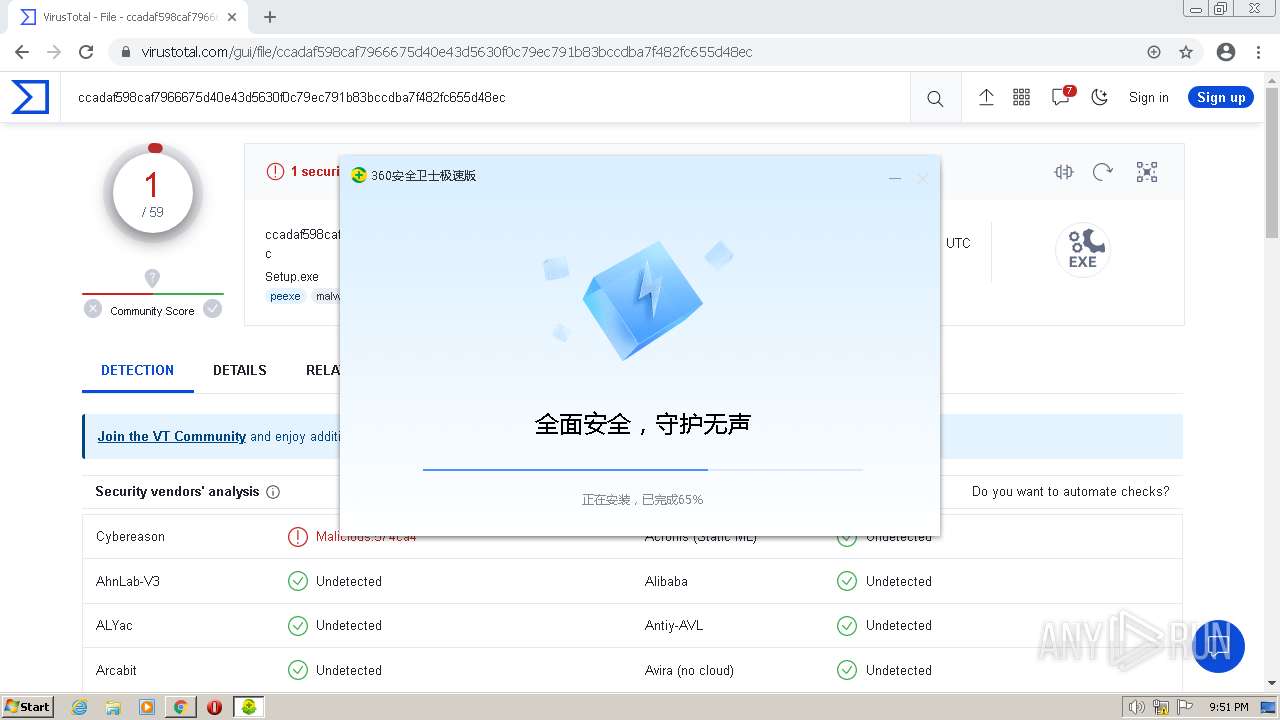
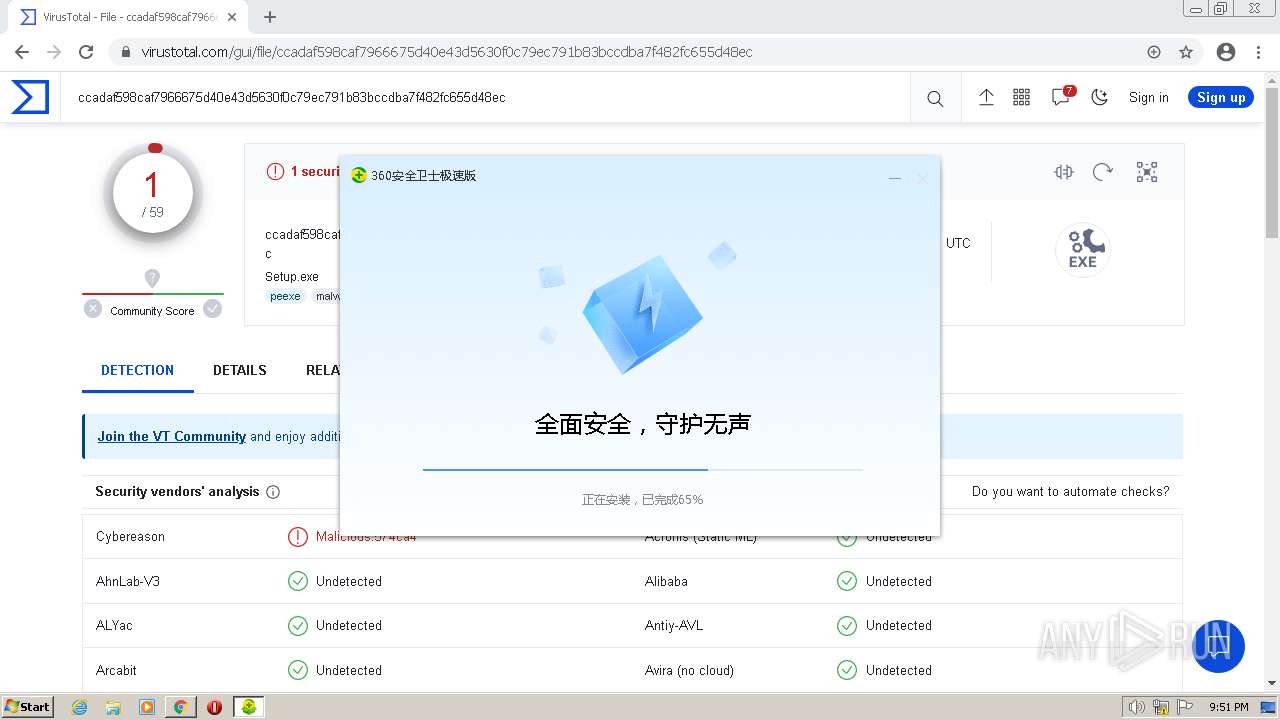
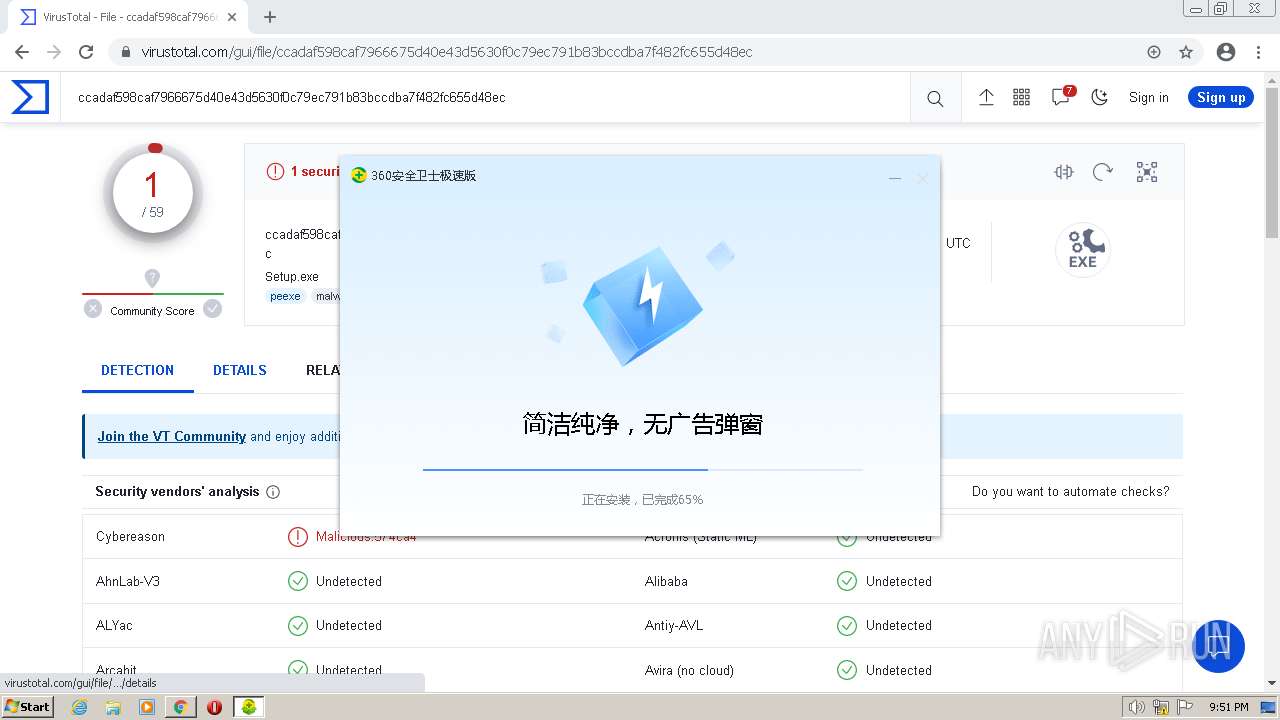
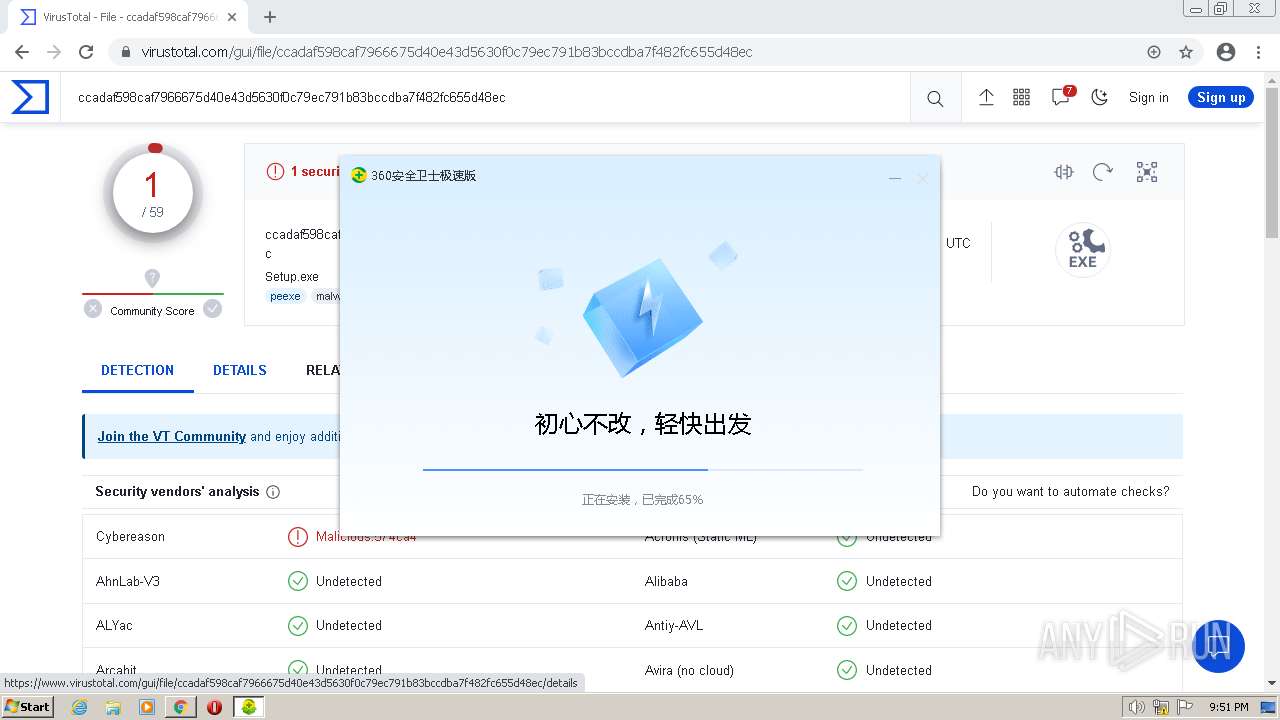
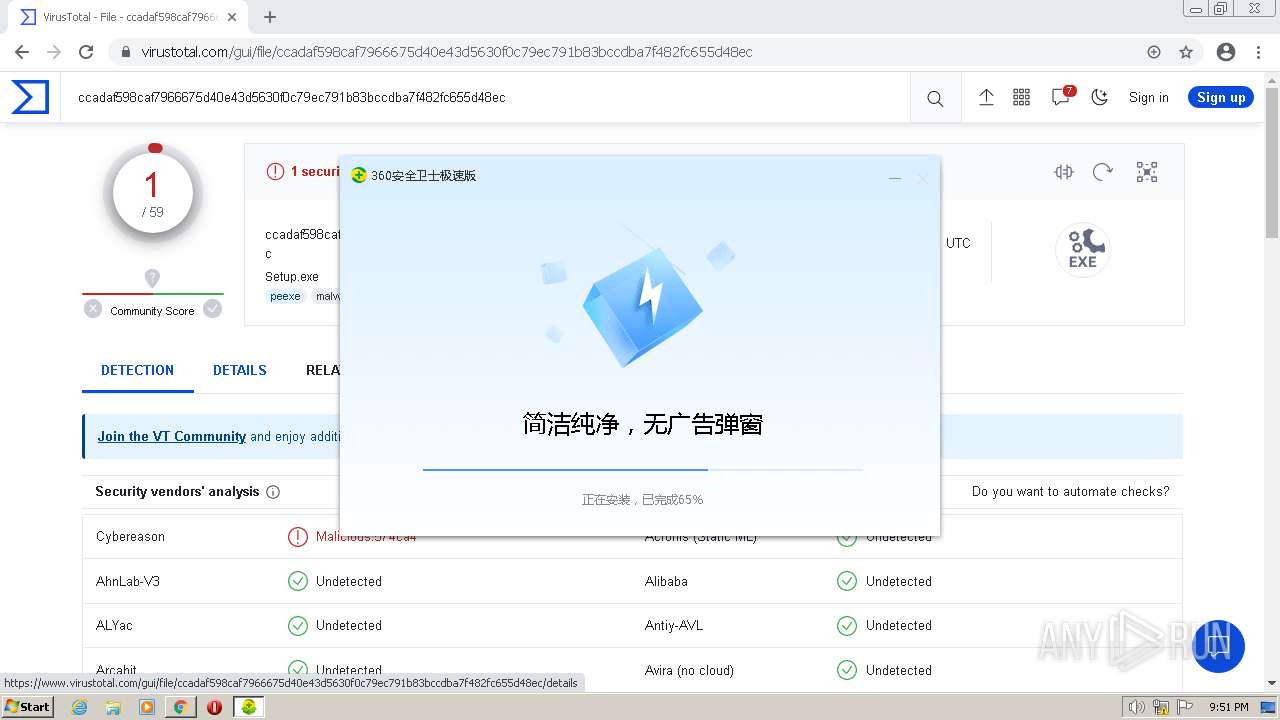
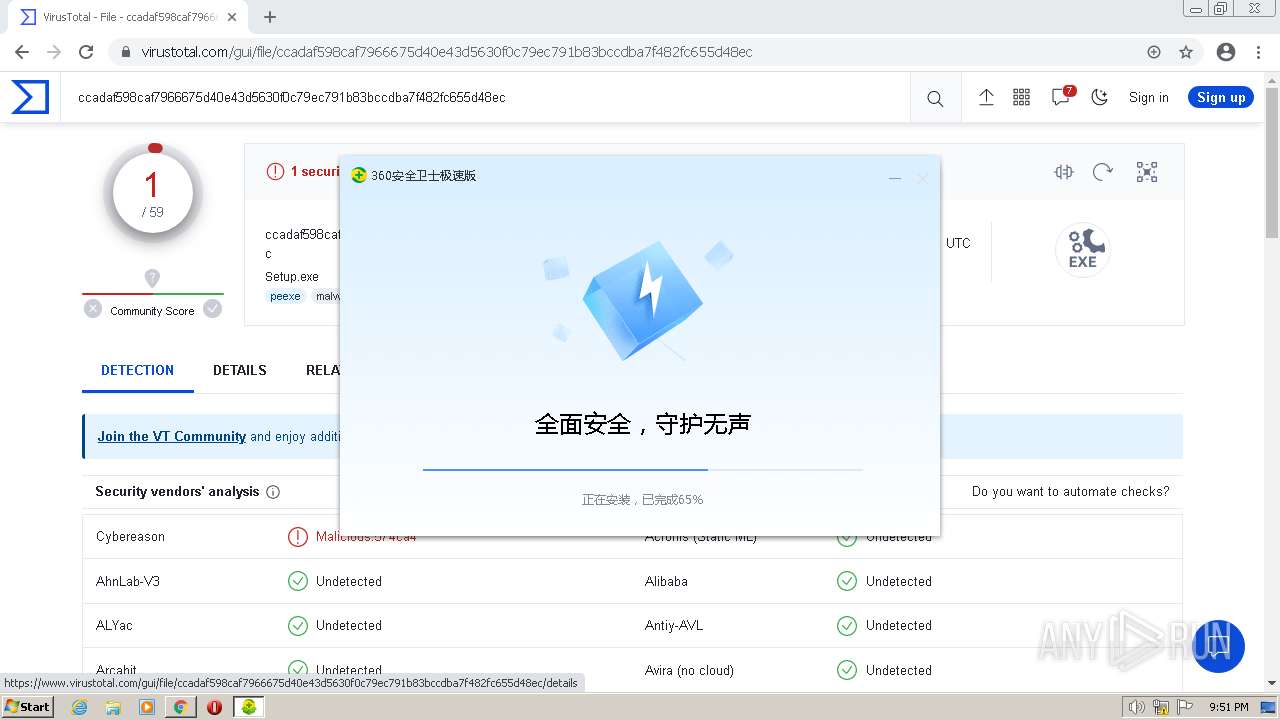
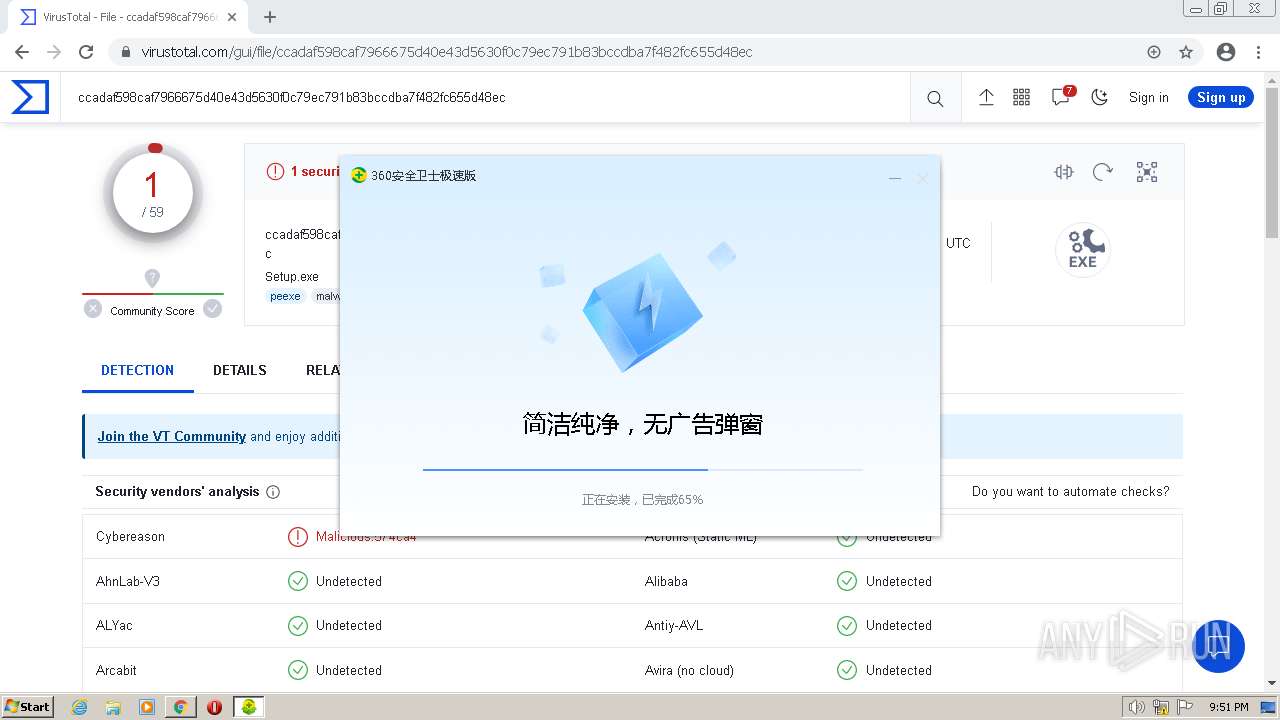
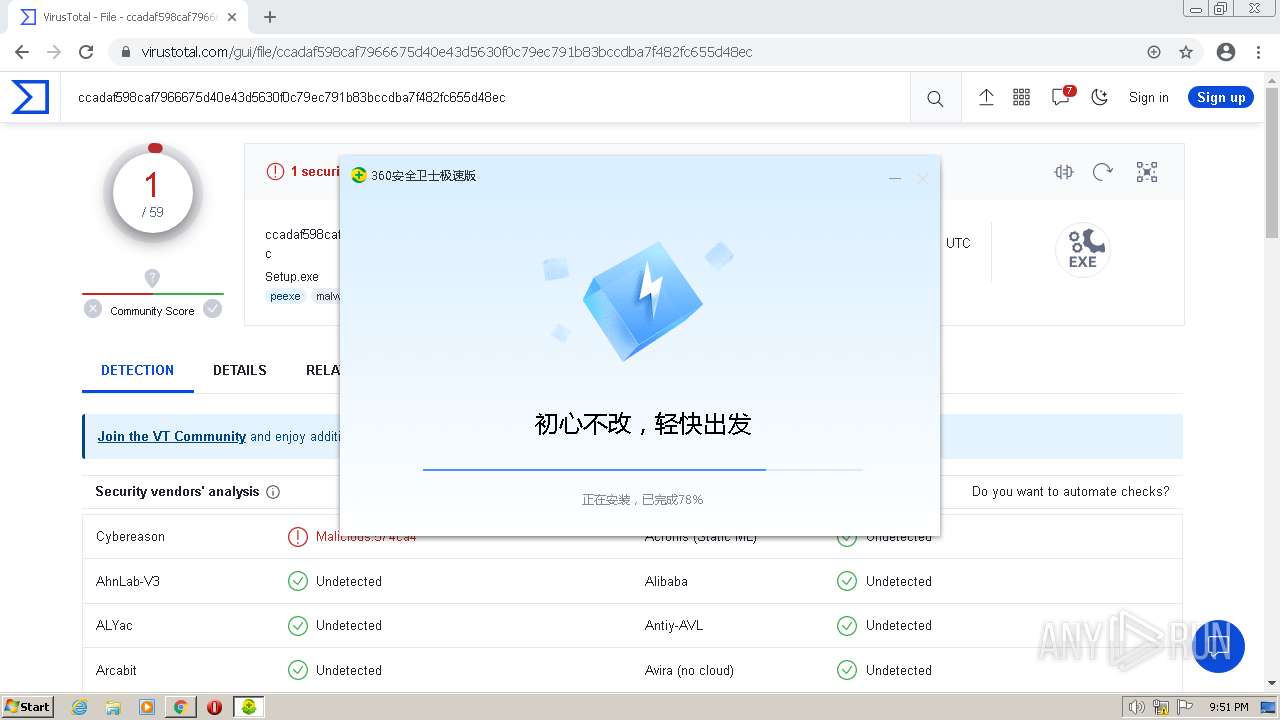
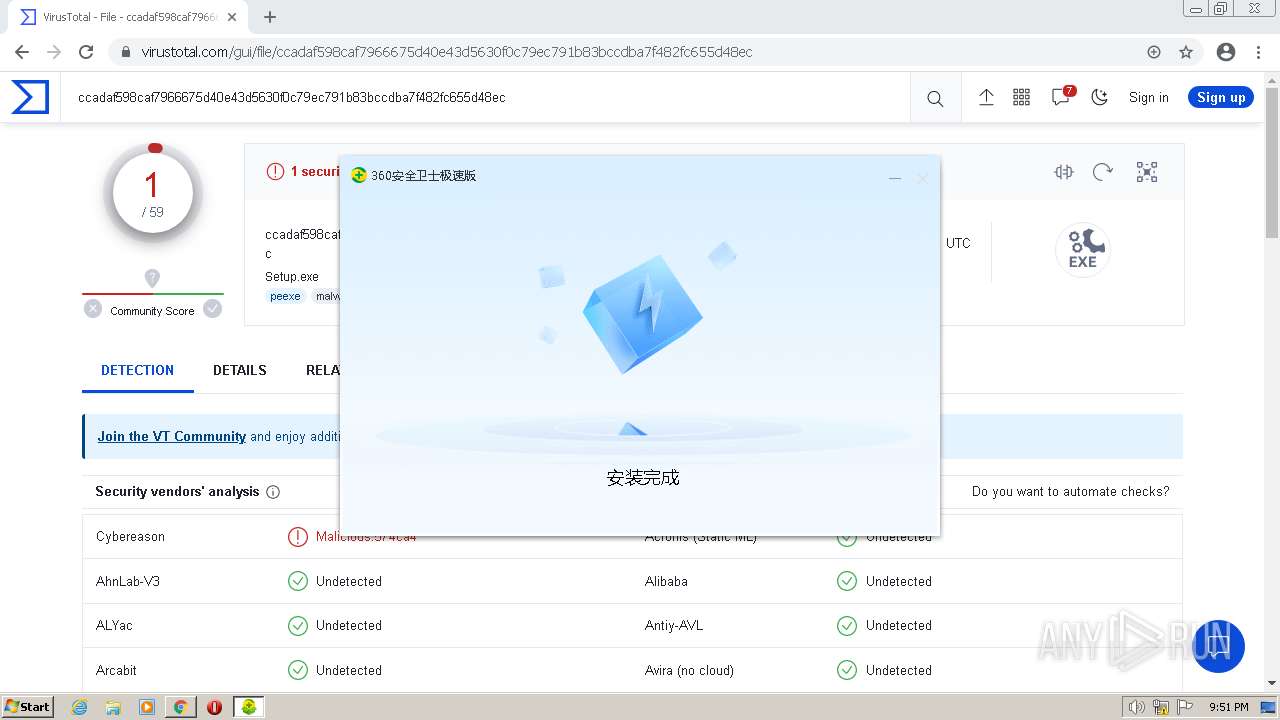
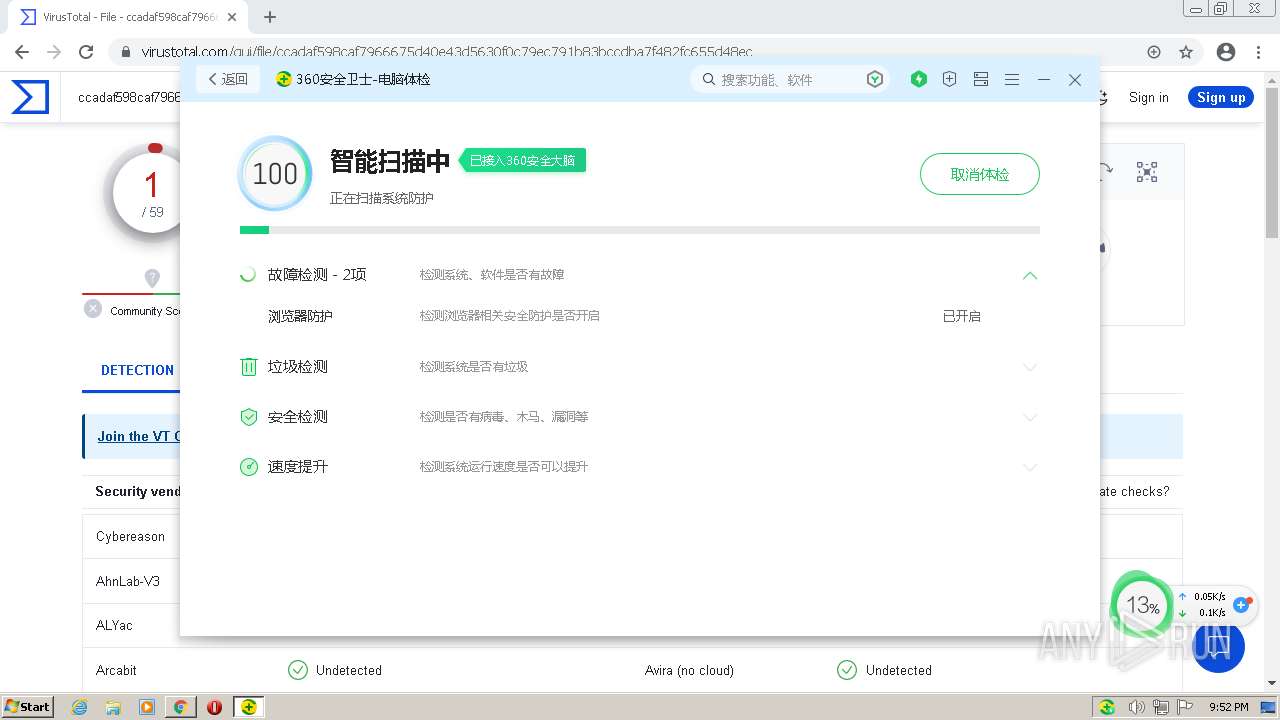
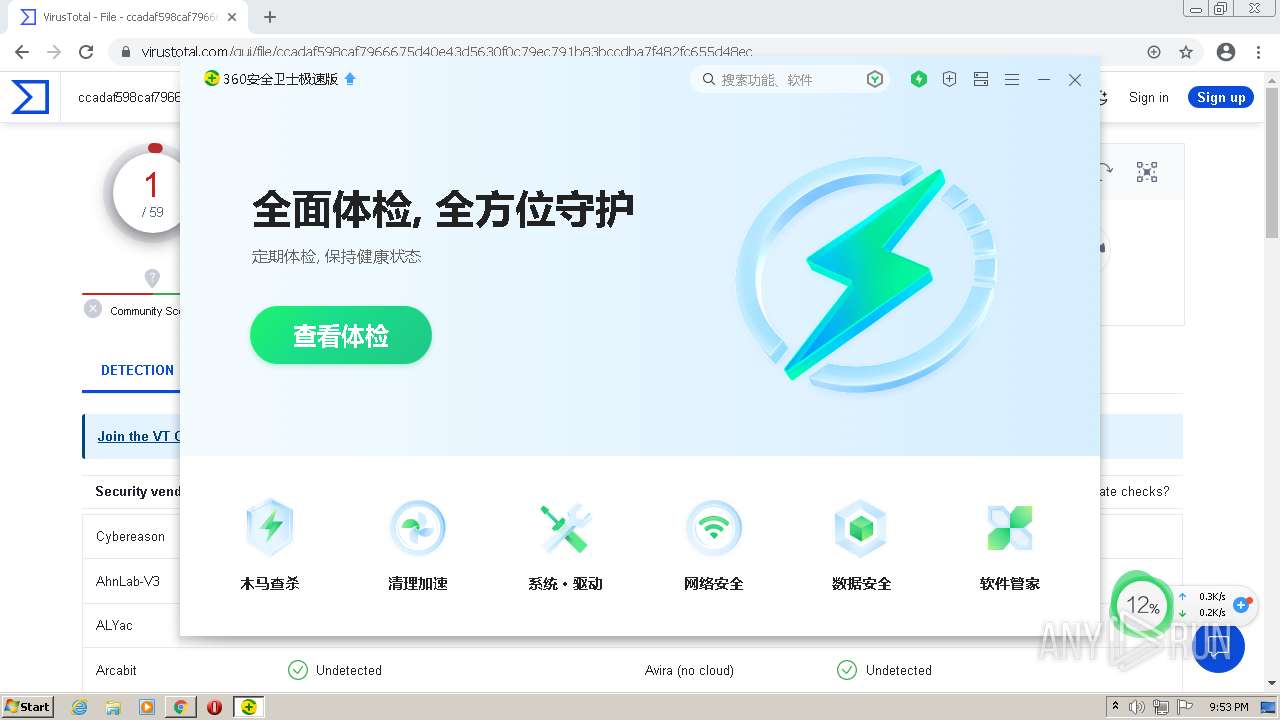
| URL: | http://360safe.com |
| Full analysis: | https://app.any.run/tasks/1f079628-3a19-4059-87a6-9f57e1e917fb |
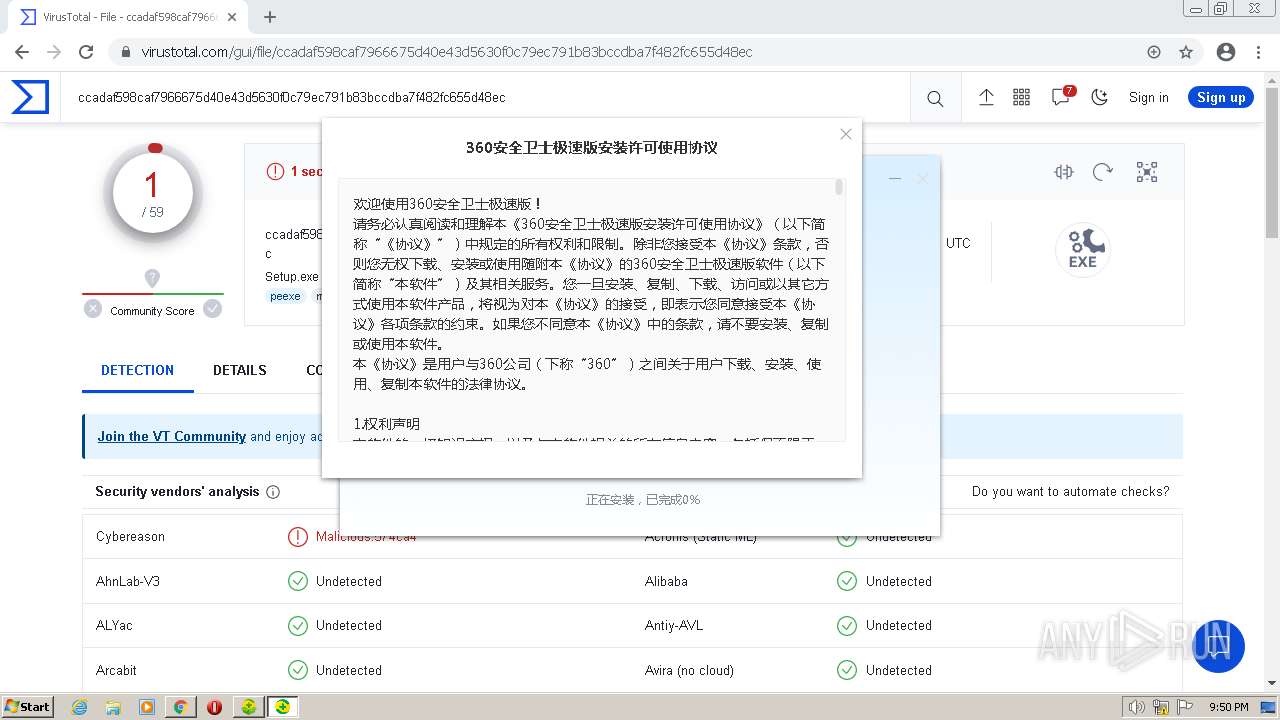
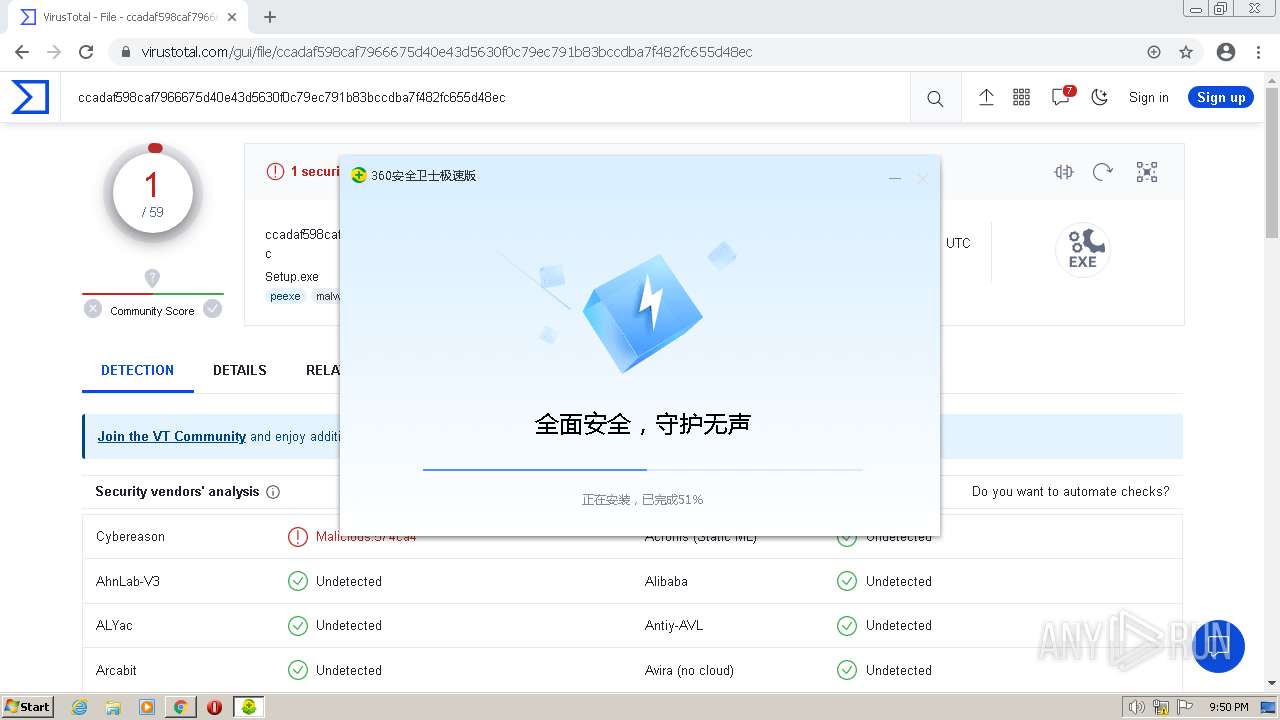
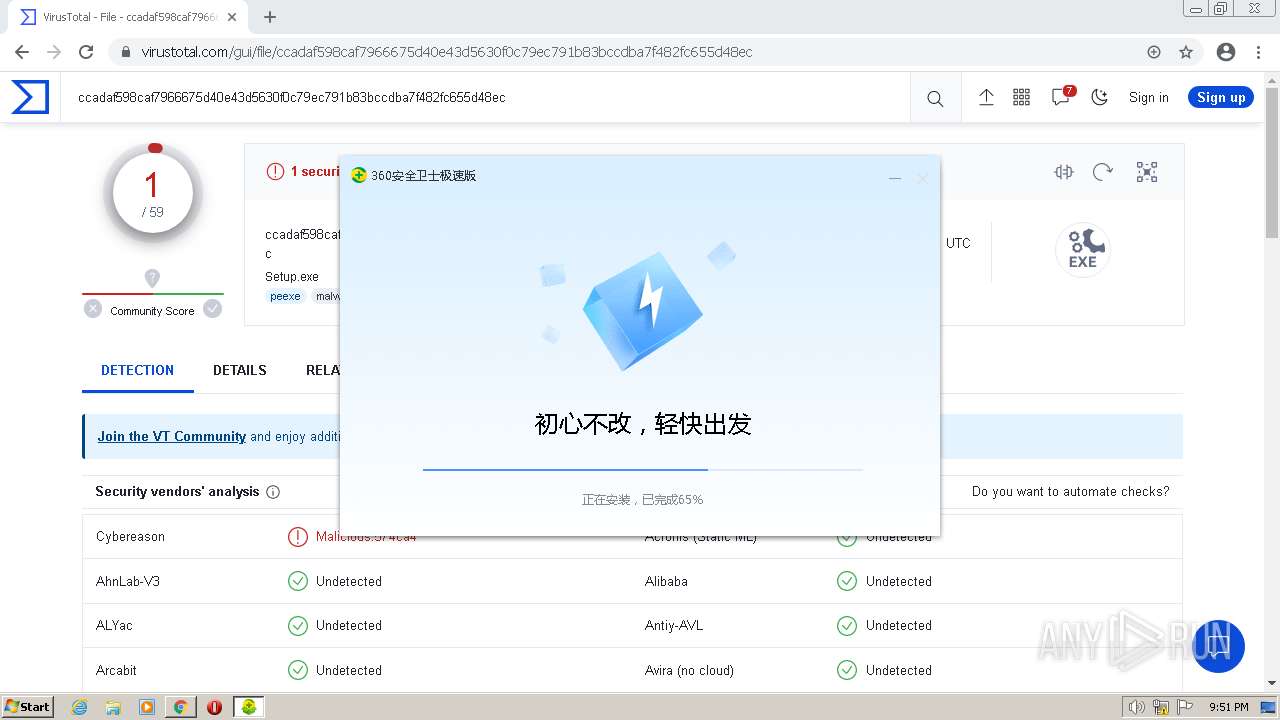
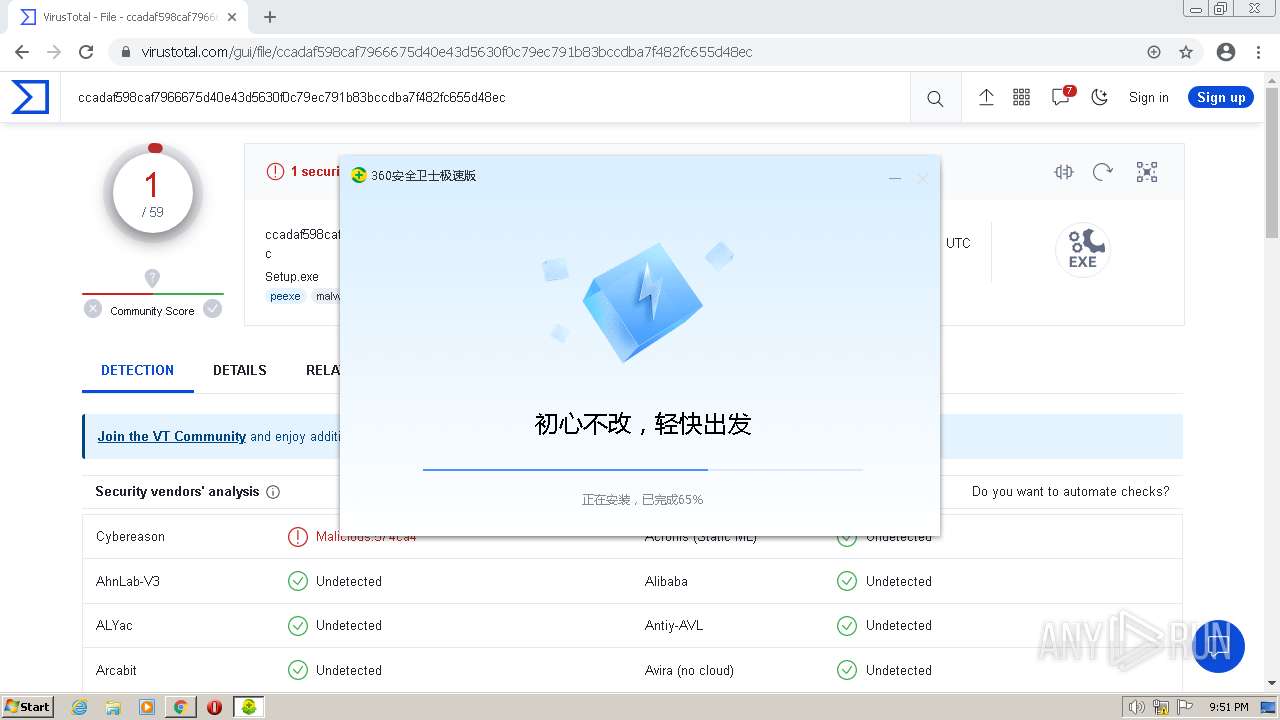
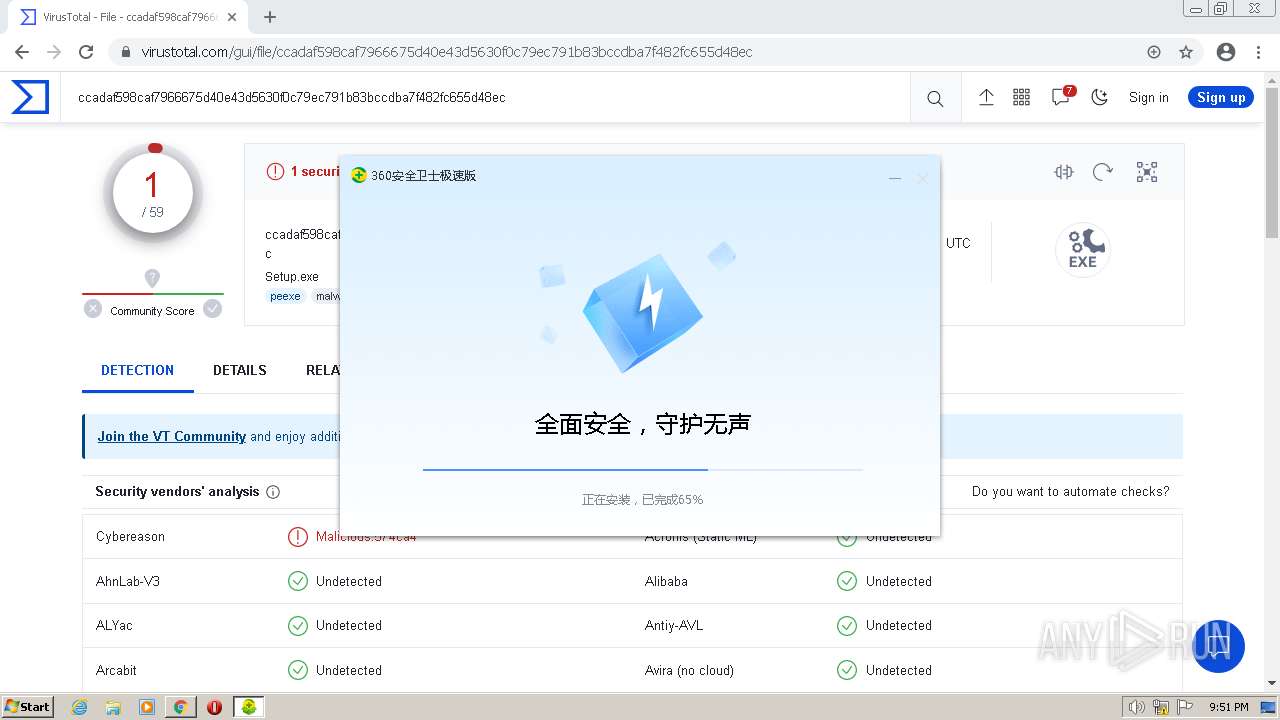
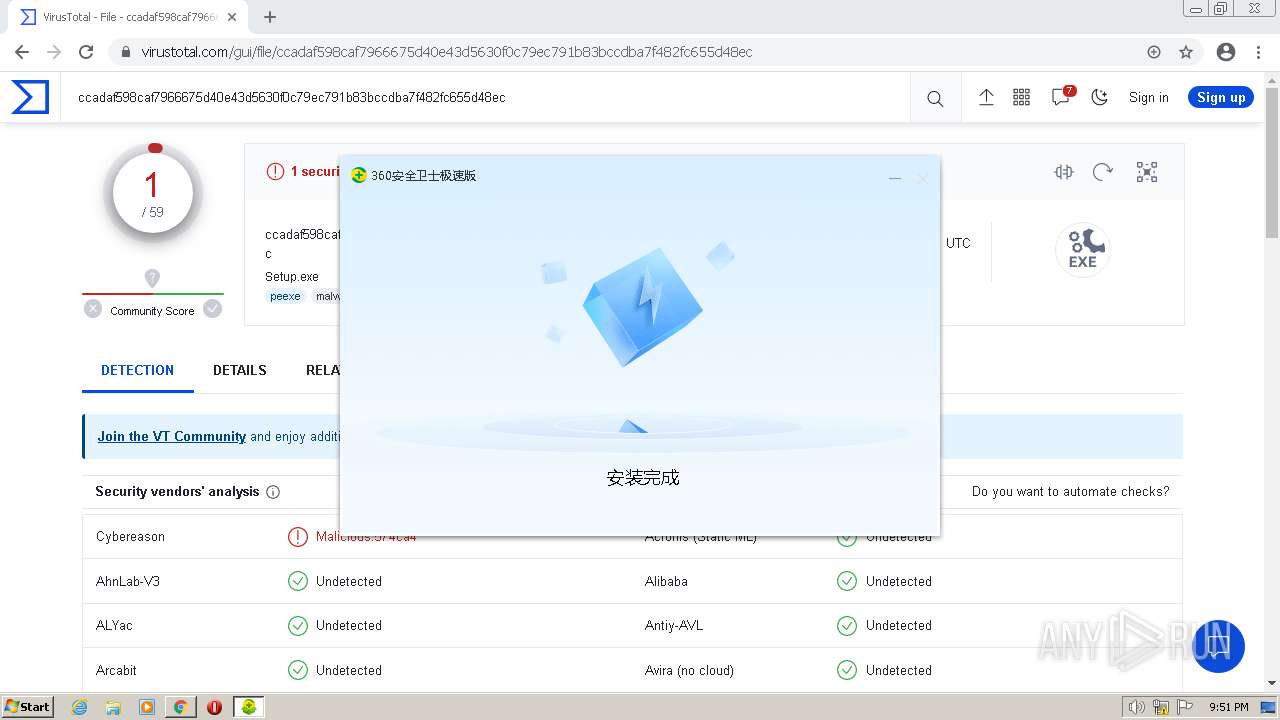
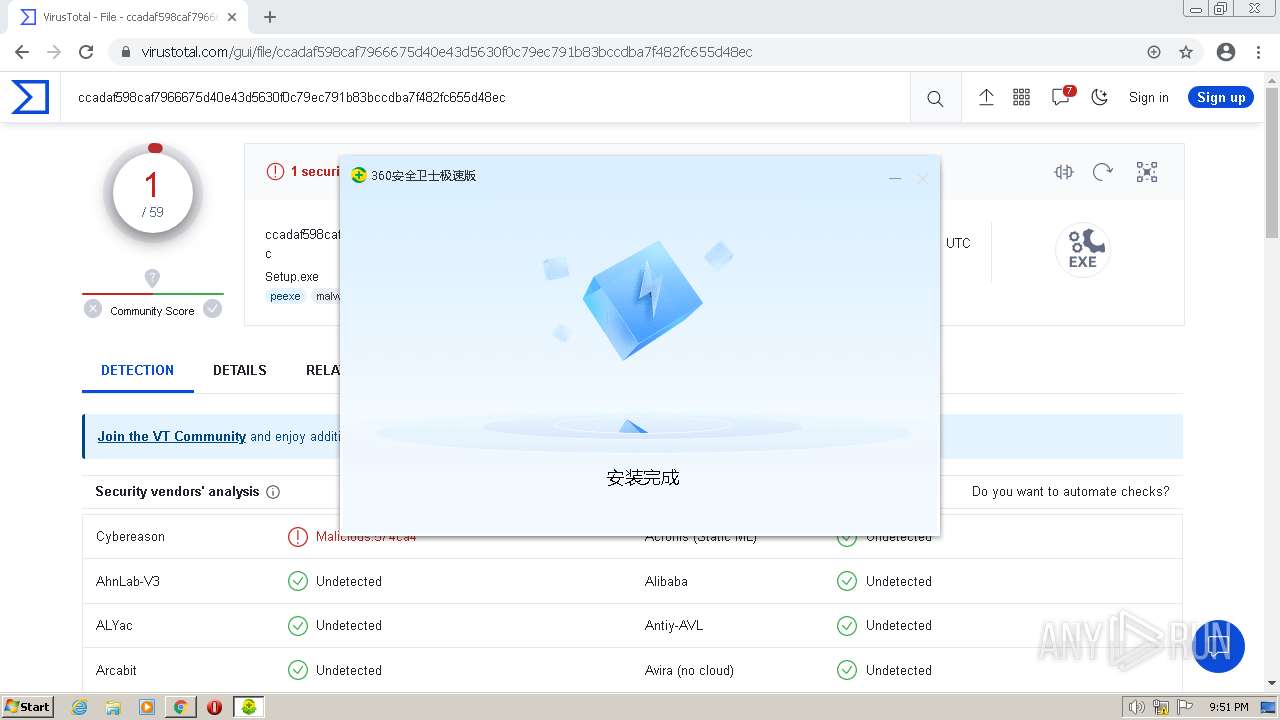
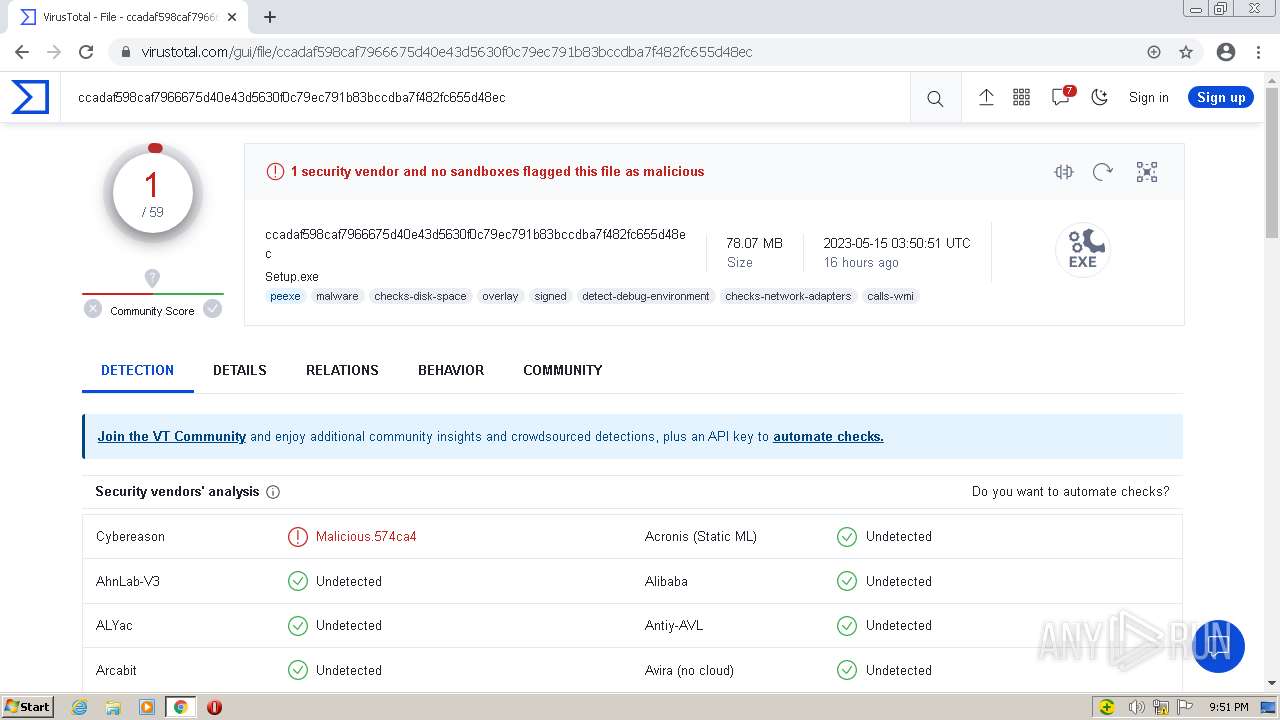
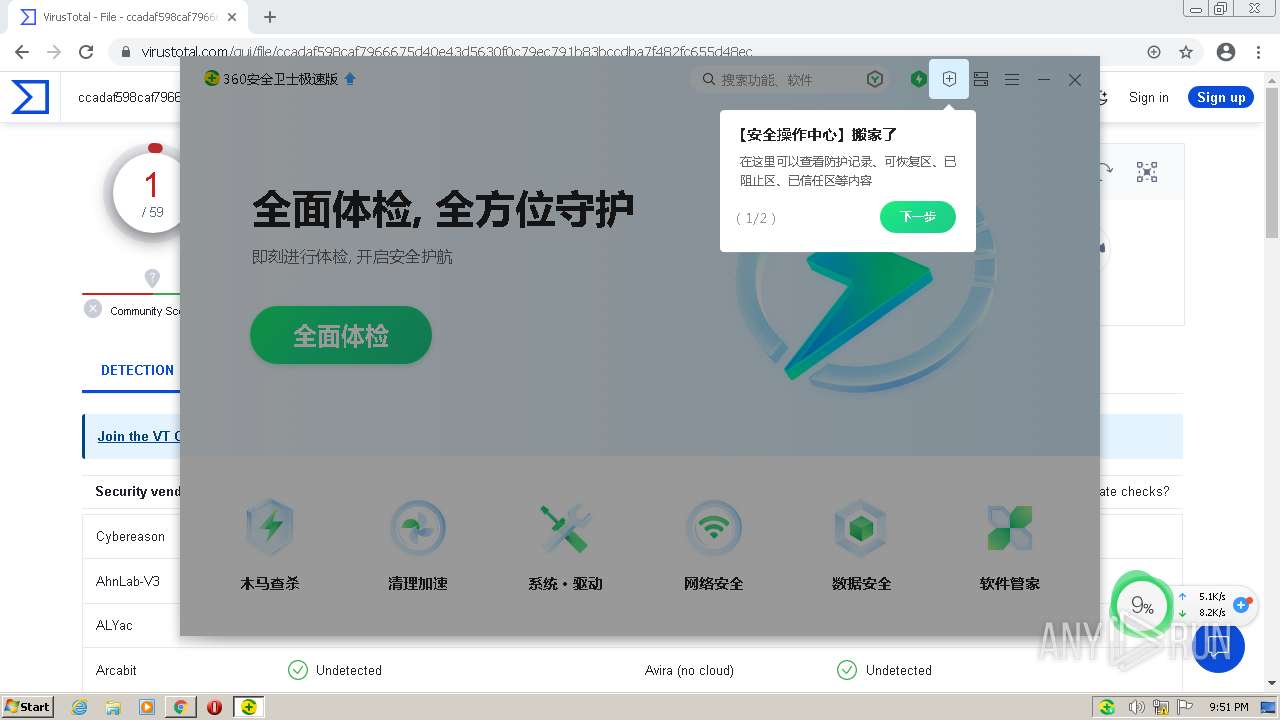
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2023, 20:48:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3A090BA603C346D080C45C3437D8711B |
| SHA1: | FE54F45B824AE23E3B65998DA6520CF871394BB0 |
| SHA256: | 308936FC5401B79213DC541C2D5FAF64E1ADA0DE279082D8B57A5A446117EC72 |
| SSDEEP: | 3:N1KBVW7LK:CjWC |
MALICIOUS
Actions looks like stealing of personal data
- explorer.exe (PID: 1068)
- svchost.exe (PID: 852)
- EaInstHelper.exe (PID: 2276)
- 360SecLogonHelper.exe (PID: 3184)
- PopWndTracker.exe (PID: 3884)
- PowerSaver.exe (PID: 1004)
- PowerSaver.exe (PID: 2036)
- zhudongfangyu.exe (PID: 2176)
- SoftupNotify.exe (PID: 1928)
- ZhuDongFangYu.exe (PID: 2764)
- regsvr32.exe (PID: 2896)
- regsvr32.exe (PID: 2660)
- ZhuDongFangYu.exe (PID: 3720)
- 360Safe.exe (PID: 1464)
- 360tray.exe (PID: 3856)
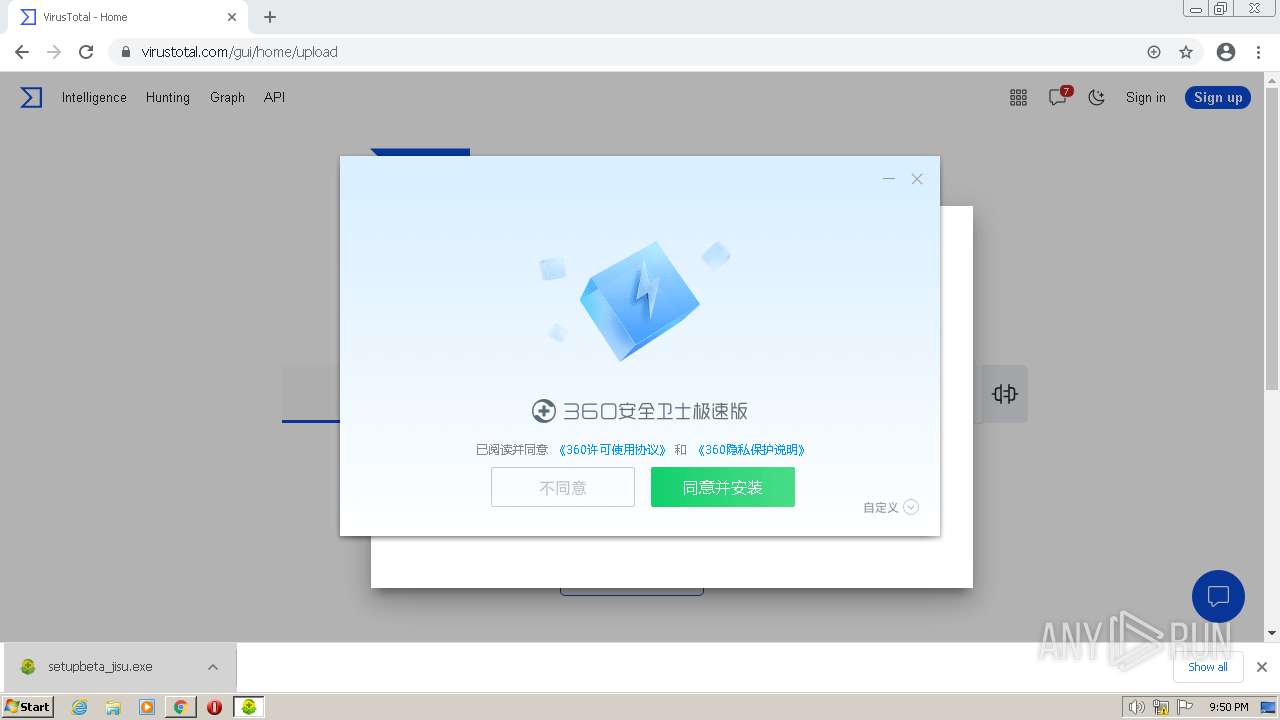
- setupbeta_jisu.exe (PID: 4020)
Creates a writable file the system directory
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
Registers / Runs the DLL via REGSVR32.EXE
- SoftupNotify.exe (PID: 1928)
SUSPICIOUS
Searches for installed software
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
Reads the Internet Settings
- setupbeta_jisu.exe (PID: 4020)
- SoftupNotify.exe (PID: 1928)
- 360tray.exe (PID: 3856)
- 360Safe.exe (PID: 1464)
Executable content was dropped or overwritten
- AgreementViewer.exe (PID: 2852)
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
- 360Safe.exe (PID: 1464)
The process verifies whether the antivirus software is installed
- explorer.exe (PID: 1068)
- 360SecLogonHelper.exe (PID: 3184)
- PopWndTracker.exe (PID: 3884)
- EaInstHelper.exe (PID: 2276)
- svchost.exe (PID: 852)
- zhudongfangyu.exe (PID: 2176)
- PowerSaver.exe (PID: 1004)
- ZhuDongFangYu.exe (PID: 2764)
- SoftupNotify.exe (PID: 1928)
- 360Safe.exe (PID: 1464)
- ZhuDongFangYu.exe (PID: 3720)
- regsvr32.exe (PID: 2896)
- regsvr32.exe (PID: 2660)
- 360tray.exe (PID: 3856)
- setupbeta_jisu.exe (PID: 4020)
Creates a software uninstall entry
- setupbeta_jisu.exe (PID: 4020)
Process requests binary or script from the Internet
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
- 360Safe.exe (PID: 1464)
Drops a system driver (possible attempt to evade defenses)
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
Creates files in the driver directory
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
Creates or modifies Windows services
- setupbeta_jisu.exe (PID: 4020)
- zhudongfangyu.exe (PID: 2176)
- ZhuDongFangYu.exe (PID: 3720)
- 360tray.exe (PID: 3856)
Reads security settings of Internet Explorer
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
Checks Windows Trust Settings
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
Reads settings of System Certificates
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
Executes as Windows Service
- ZhuDongFangYu.exe (PID: 3720)
The process checks if it is being run in the virtual environment
- 360tray.exe (PID: 3856)
Reads Microsoft Outlook installation path
- 360tray.exe (PID: 3856)
Reads the BIOS version
- 360tray.exe (PID: 3856)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 3420)
The process uses the downloaded file
- chrome.exe (PID: 3420)
- chrome.exe (PID: 2864)
Reads the machine GUID from the registry
- setupbeta_jisu.exe (PID: 4020)
- 360SecLogonHelper.exe (PID: 3184)
- 360tray.exe (PID: 3856)
- 360Safe.exe (PID: 1464)
- SoftupNotify.exe (PID: 1928)
Create files in a temporary directory
- chrome.exe (PID: 3420)
- setupbeta_jisu.exe (PID: 4020)
- svchost.exe (PID: 852)
- AgreementViewer.exe (PID: 2852)
- 360tray.exe (PID: 3856)
Reads the computer name
- setupbeta_jisu.exe (PID: 4020)
- 360SecLogonHelper.exe (PID: 3184)
- zhudongfangyu.exe (PID: 2176)
- 360tray.exe (PID: 3856)
- 360Safe.exe (PID: 1464)
- ZhuDongFangYu.exe (PID: 2764)
- ZhuDongFangYu.exe (PID: 3720)
- SoftupNotify.exe (PID: 1928)
The process checks LSA protection
- setupbeta_jisu.exe (PID: 4020)
- svchost.exe (PID: 1264)
- 360SecLogonHelper.exe (PID: 3184)
- zhudongfangyu.exe (PID: 2176)
- 360tray.exe (PID: 3856)
- 360Safe.exe (PID: 1464)
- SoftupNotify.exe (PID: 1928)
Checks proxy server information
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
- 360Safe.exe (PID: 1464)
Checks supported languages
- setupbeta_jisu.exe (PID: 4020)
- AgreementViewer.exe (PID: 2852)
- 360SecLogonHelper.exe (PID: 3184)
- PopWndTracker.exe (PID: 3884)
- EaInstHelper.exe (PID: 2276)
- zhudongfangyu.exe (PID: 2176)
- PowerSaver.exe (PID: 2036)
- PowerSaver.exe (PID: 1004)
- 360tray.exe (PID: 3856)
- 360Safe.exe (PID: 1464)
- SoftupNotify.exe (PID: 1928)
- ZhuDongFangYu.exe (PID: 2764)
- ZhuDongFangYu.exe (PID: 3720)
Application launched itself
- chrome.exe (PID: 3420)
Creates files or folders in the user directory
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
- 360Safe.exe (PID: 1464)
Process checks are UAC notifies on
- setupbeta_jisu.exe (PID: 4020)
- 360tray.exe (PID: 3856)
Dropped object may contain TOR URL's
- setupbeta_jisu.exe (PID: 4020)
Creates files in the program directory
- PopWndTracker.exe (PID: 3884)
- ZhuDongFangYu.exe (PID: 3720)
- SoftupNotify.exe (PID: 1928)
- 360tray.exe (PID: 3856)
- setupbeta_jisu.exe (PID: 4020)
Reads CPU info
- 360tray.exe (PID: 3856)
Manual execution by a user
- wmpnscfg.exe (PID: 1544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
117
Monitored processes
75
Malicious processes
16
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,4108069770652213085,17448281235646516303,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=2692 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,4108069770652213085,17448281235646516303,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,4108069770652213085,17448281235646516303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2388 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,4108069770652213085,17448281235646516303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3156 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1016,4108069770652213085,17448281235646516303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1016,4108069770652213085,17448281235646516303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3128 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 828 | C:\Windows\system32\svchost.exe -k LocalService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e0ad988,0x6e0ad998,0x6e0ad9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1016,4108069770652213085,17448281235646516303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3000 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
105 684
Read events
103 316
Write events
1 182
Delete events
1 186
Modification events
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
| (PID) Process: | (3420) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
978
Suspicious files
3 509
Text files
1 656
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-64629AC1-D5C.pma | — | |
MD5:— | SHA256:— | |||
| 828 | svchost.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\~FontCache-S-1-5-21-1302019708-1500728564-335382590-1000.dat | — | |
MD5:— | SHA256:— | |||
| 876 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF10ce5e.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF10ce5e.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF10d033.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF10d023.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3420 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
359
TCP/UDP connections
253
DNS requests
144
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
676 | chrome.exe | GET | — | 13.224.189.23:80 | http://p0.ssl.qhimg.com/t010955d40c76ee3cac.png | US | — | — | malicious |
676 | chrome.exe | GET | 200 | 52.222.214.57:80 | http://s.ssl.qhimg.com/static/5026c8045e19af4c.css | US | text | 2.25 Kb | whitelisted |
676 | chrome.exe | GET | 200 | 52.222.214.57:80 | http://s.ssl.qhimg.com/static/3a56b28eba98cb2e.css | US | text | 1.85 Kb | whitelisted |
676 | chrome.exe | GET | 200 | 13.224.189.73:80 | http://p1.ssl.qhimg.com/t01c6c4e7b12bdd62e9.png | US | image | 608 b | shared |
676 | chrome.exe | GET | 200 | 13.224.189.73:80 | http://p1.ssl.qhimg.com/t01142a5003c283acb5.png | US | image | 1.96 Kb | shared |
676 | chrome.exe | GET | 200 | 13.224.189.73:80 | http://p1.ssl.qhimg.com/t01a2e1d15c0d36c7e4.png | US | image | 572 b | shared |
676 | chrome.exe | GET | 200 | 13.224.189.73:80 | http://p1.ssl.qhimg.com/t0124ffc462e472bfd1.png | US | image | 1.71 Kb | shared |
676 | chrome.exe | GET | 200 | 101.226.4.13:80 | http://360safe.com/ | CN | html | 78.2 Kb | whitelisted |
676 | chrome.exe | GET | 200 | 13.224.189.115:80 | http://p4.ssl.qhimg.com/t01e56c4f3d09a42415.png | US | image | 5.78 Kb | shared |
676 | chrome.exe | GET | 200 | 13.224.189.115:80 | http://p4.ssl.qhimg.com/t01f3d0a9ed119db92c.png | US | image | 1.63 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3420 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
676 | chrome.exe | 142.250.186.173:443 | accounts.google.com | GOOGLE | US | suspicious |
676 | chrome.exe | 142.250.186.78:443 | clients2.google.com | GOOGLE | US | whitelisted |
676 | chrome.exe | 13.224.189.23:80 | p1.ssl.qhimg.com | AMAZON-02 | US | malicious |
676 | chrome.exe | 13.224.189.23:443 | p1.ssl.qhimg.com | AMAZON-02 | US | malicious |
676 | chrome.exe | 13.224.189.115:80 | p1.ssl.qhimg.com | AMAZON-02 | US | unknown |
676 | chrome.exe | 13.32.99.99:80 | p8.qhimg.com | AMAZON-02 | US | suspicious |
676 | chrome.exe | 172.217.18.10:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
360safe.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
s.ssl.qhimg.com |
| whitelisted |
p1.ssl.qhimg.com |
| shared |
p3.ssl.qhimg.com |
| shared |
p5.ssl.qhimg.com |
| shared |
p2.ssl.qhimg.com |
| shared |
p4.ssl.qhimg.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3856 | 360tray.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 8 through 15 set |
3856 | 360tray.exe | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 8 through 15 set |
4 | System | Potential Corporate Privacy Violation | ET DNS Non-DNS or Non-Compliant DNS traffic on DNS port Opcode 6 or 7 set |
3196 | LiveUpdate360.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
3196 | LiveUpdate360.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag true change port flag false) |
3196 | LiveUpdate360.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag true) |
3196 | LiveUpdate360.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
3196 | LiveUpdate360.exe | Generic Protocol Command Decode | ET INFO Session Traversal Utilities for NAT (STUN Binding Request obsolete rfc 3489 CHANGE-REQUEST attribute change IP flag false change port flag false) |
Process | Message |
|---|---|
SoftupNotify.exe | /install |
SoftupNotify.exe | /install |
360tray.exe | ??LoadLibraryFormSystem32??dll:C:\Program Files\360\360Safe\360conf.dll
|
360tray.exe | ??LoadLibraryFormSystem32??dll:C:\Program Files\360\360Safe\360conf.dll
|
360tray.exe | ??LoadLibraryFormSystem32??dll:C:\Program Files\360\360Safe\deepscan\heavygate.dll
|
360tray.exe | ??LoadLibraryFormSystem32??dll:C:\Program Files\360\360Safe\deepscan\heavygate.dll
|