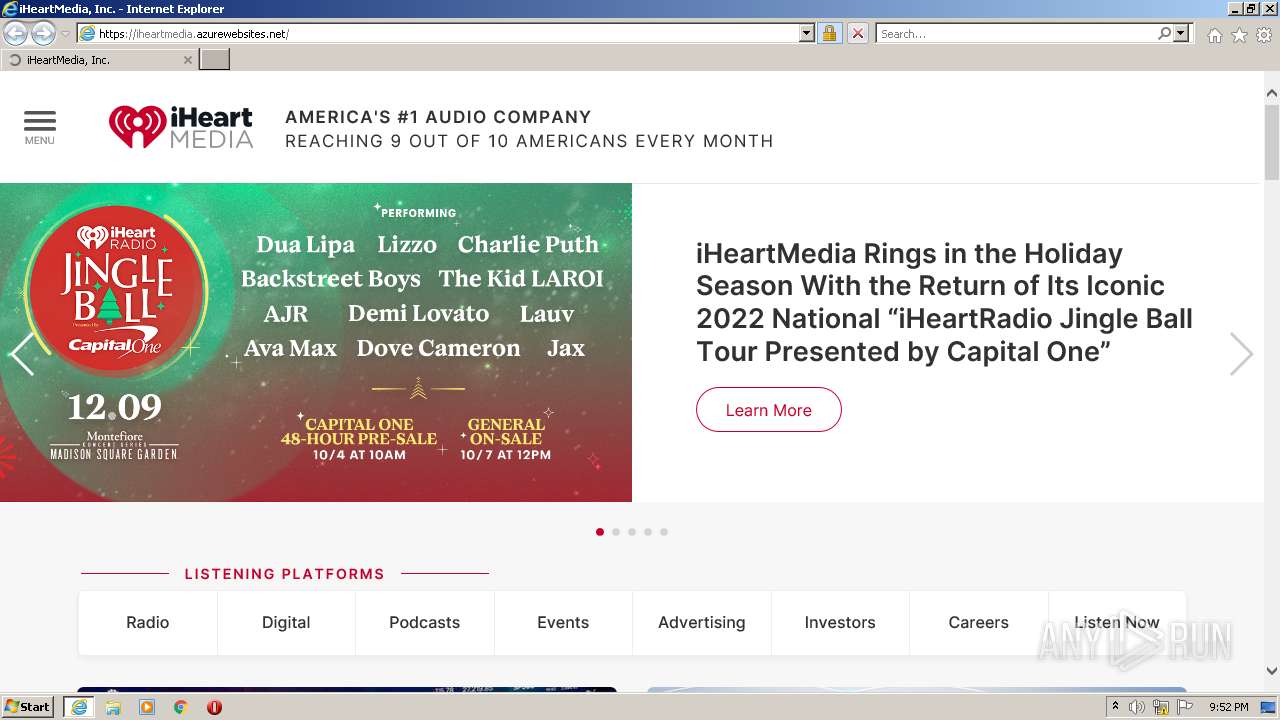
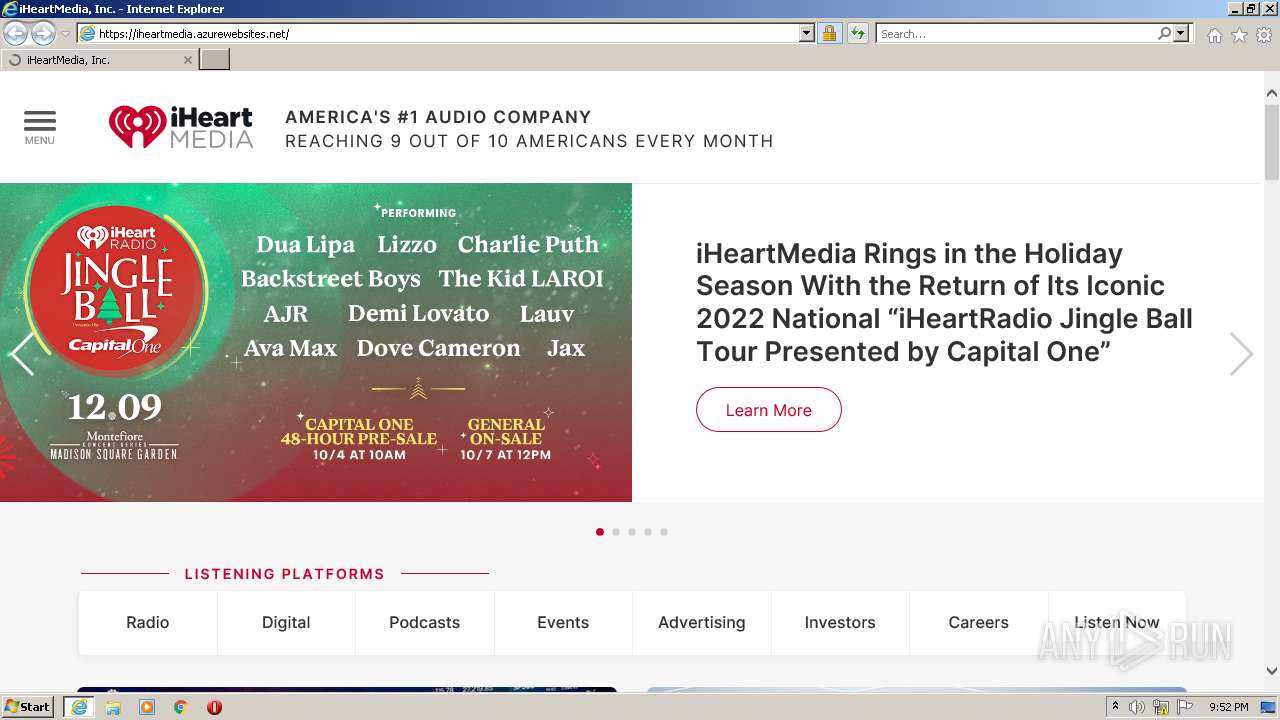
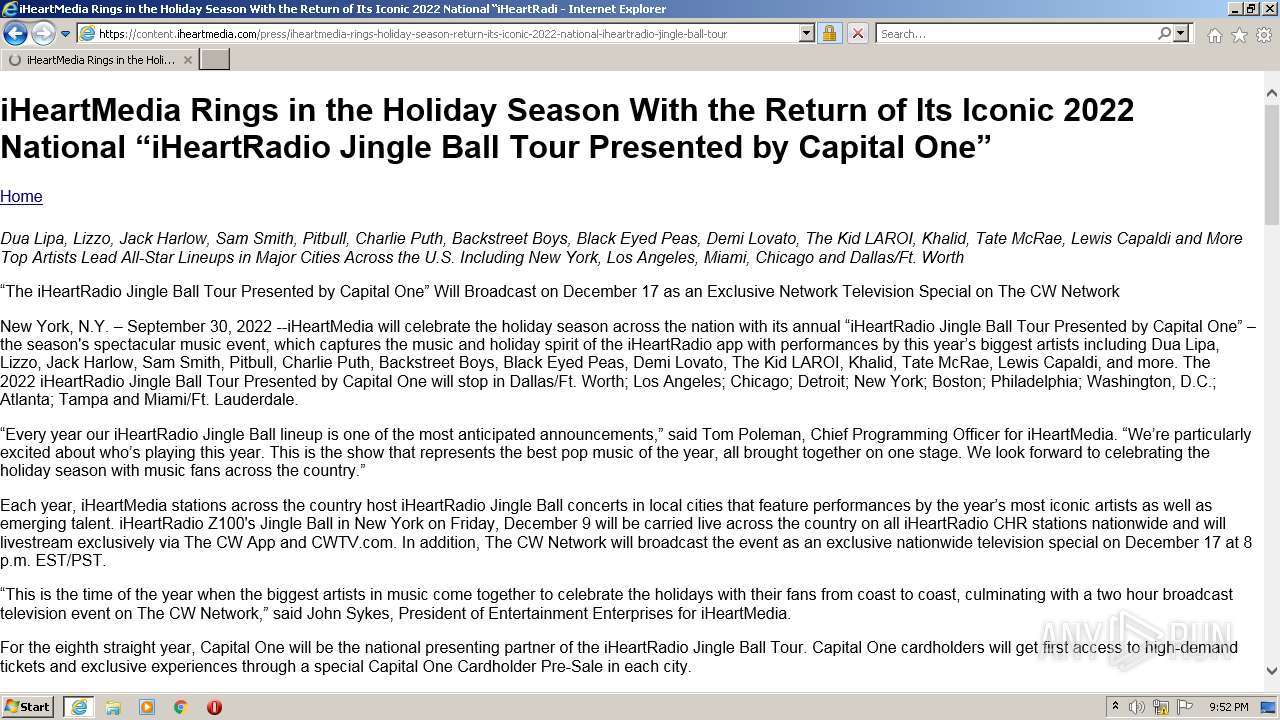
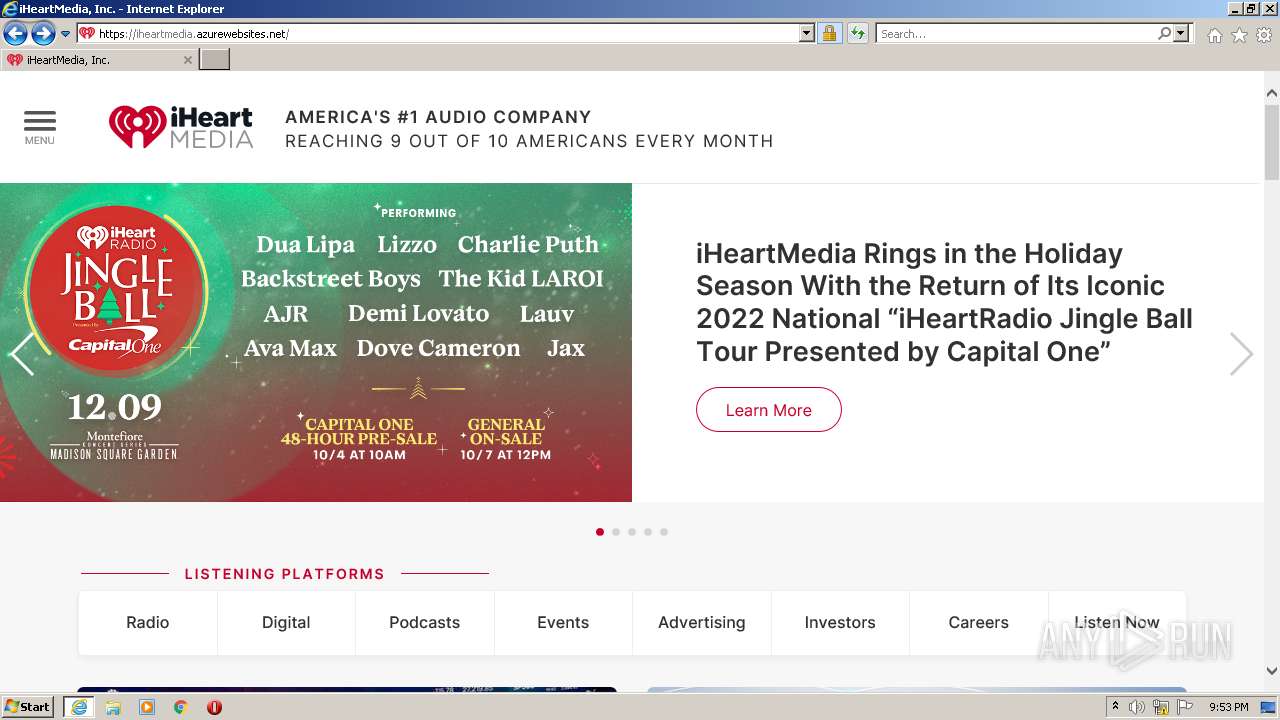
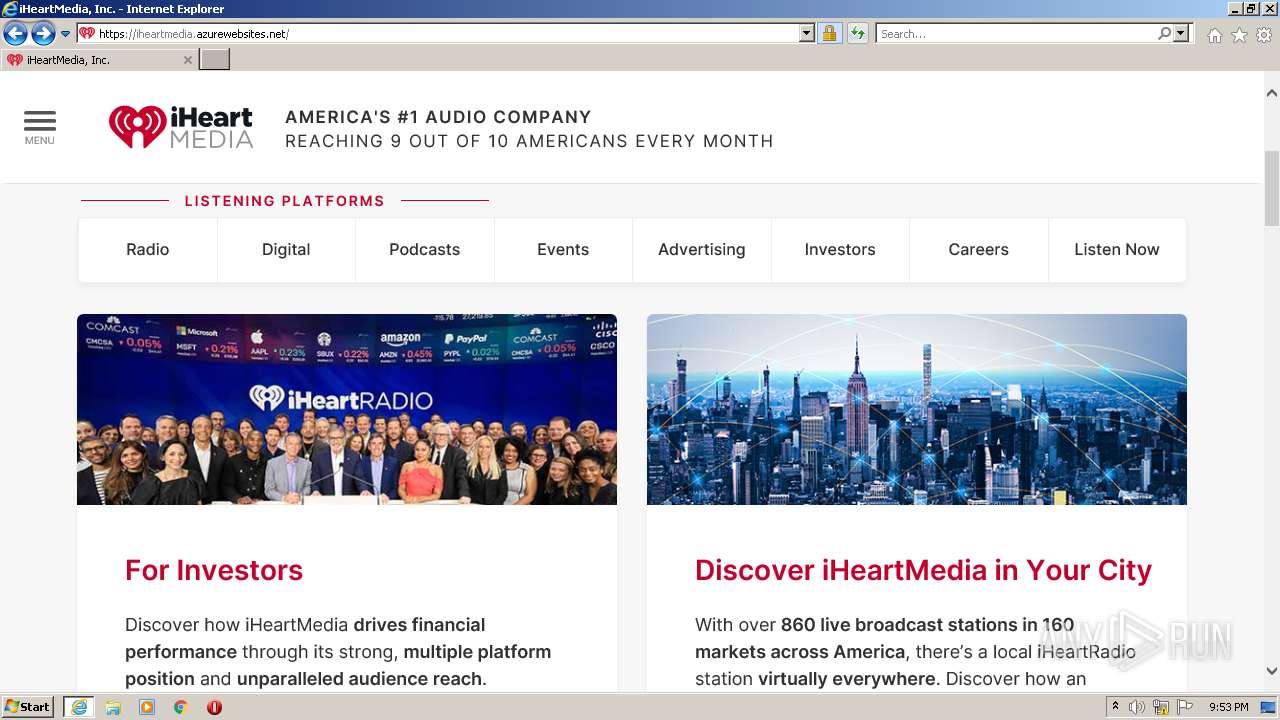
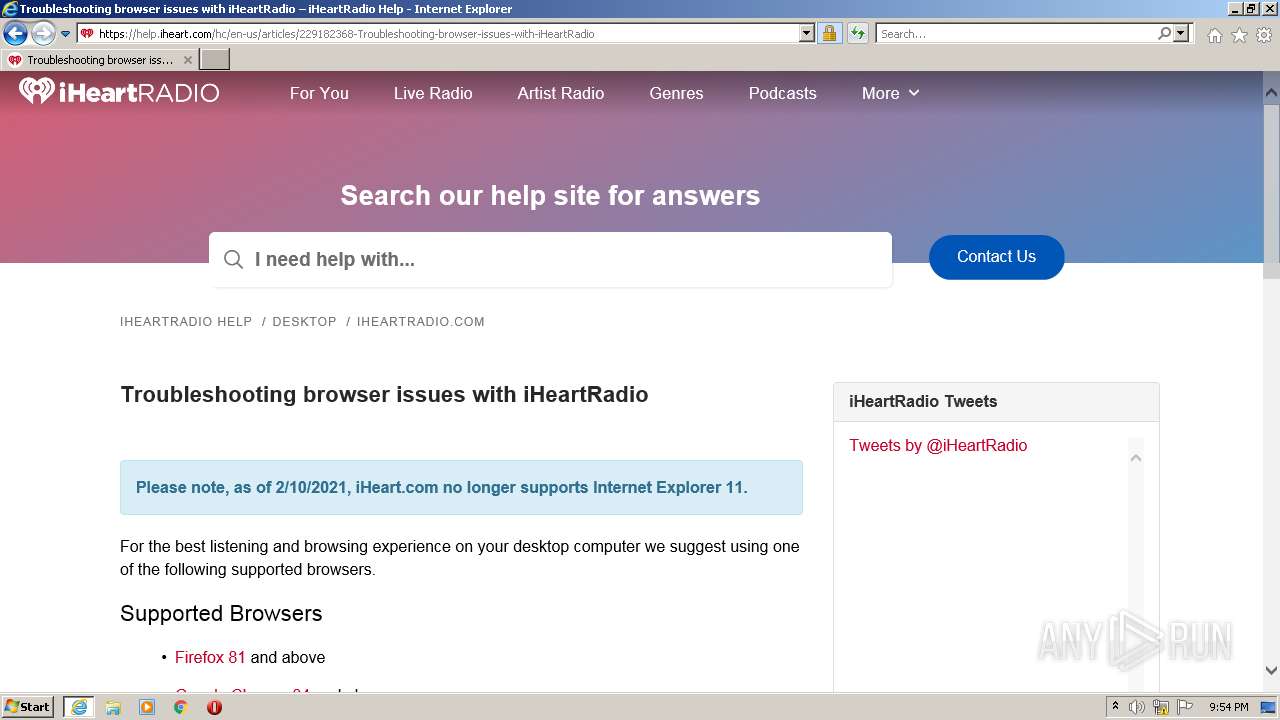
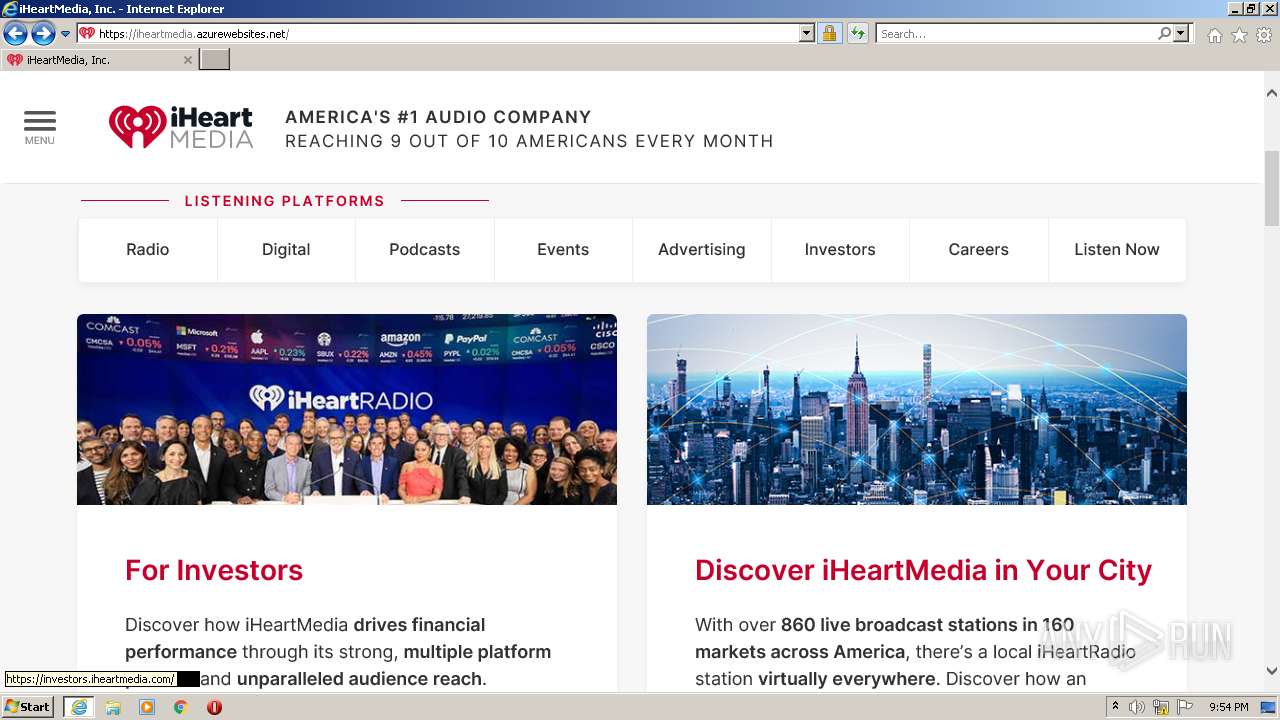
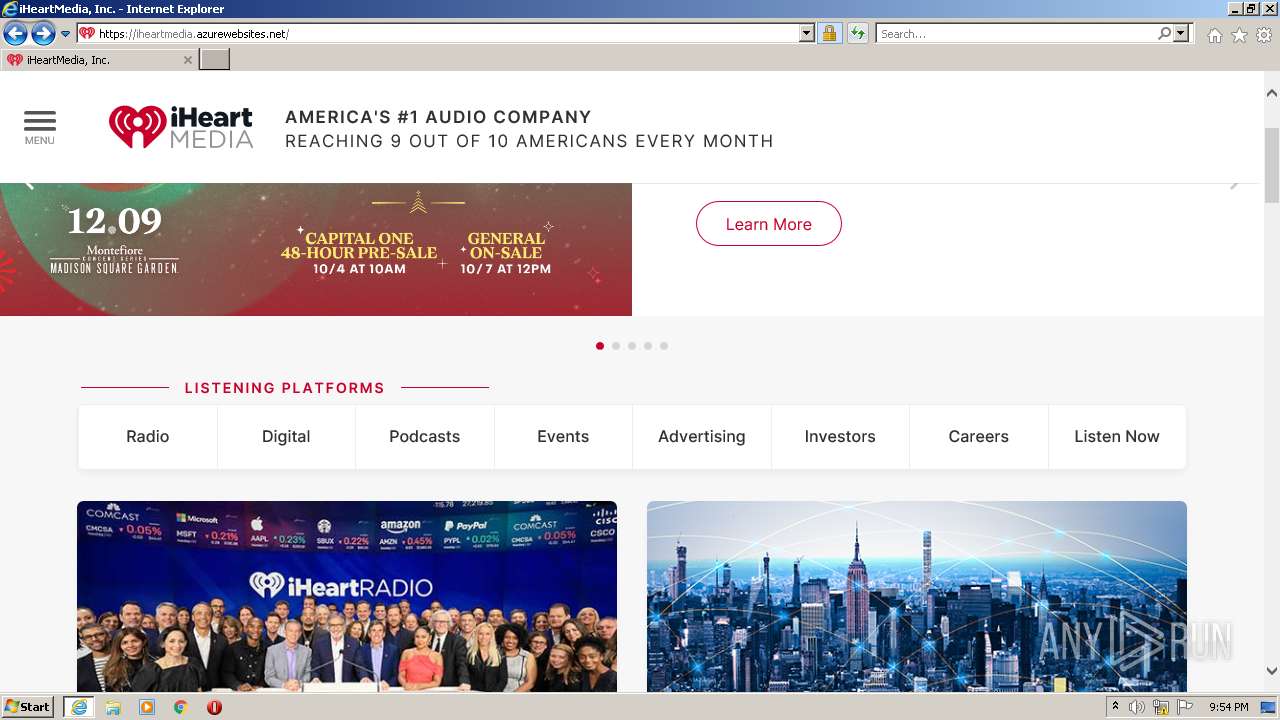
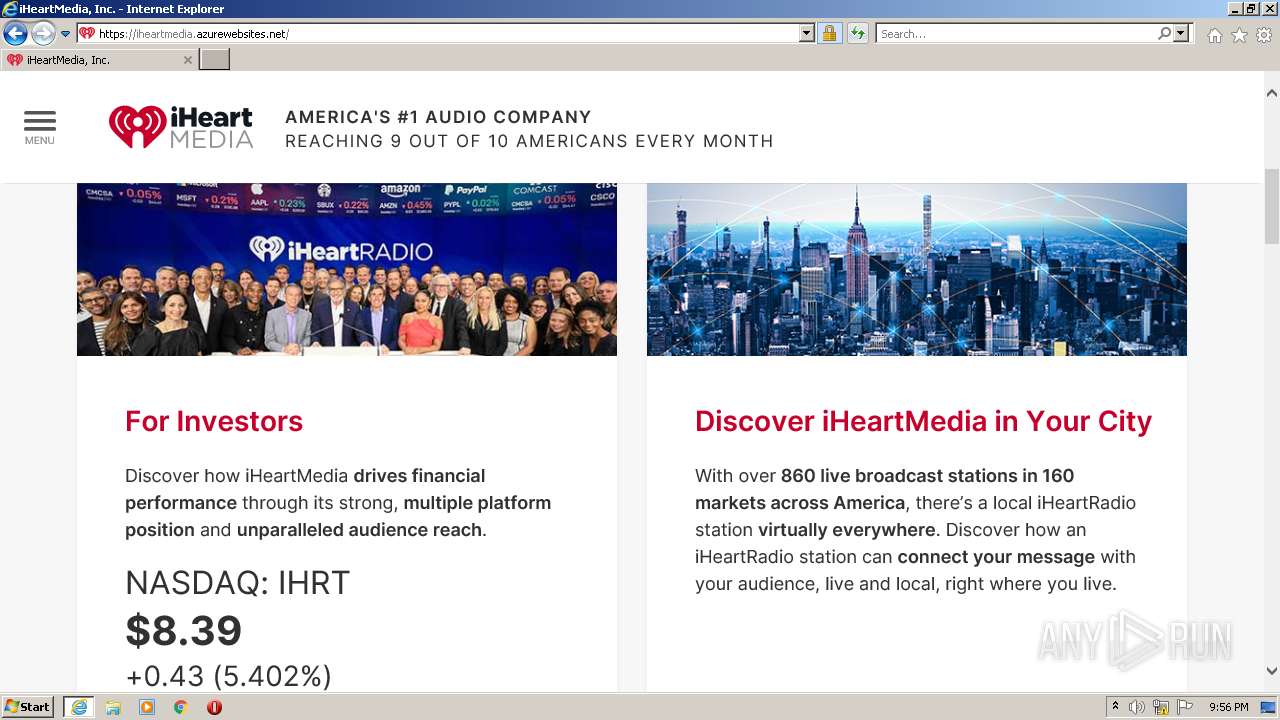
| URL: | https://iheartmedia.azurewebsites.net |
| Full analysis: | https://app.any.run/tasks/58ba4bd3-6a02-452b-9209-da4ebd1104a7 |
| Verdict: | Malicious activity |
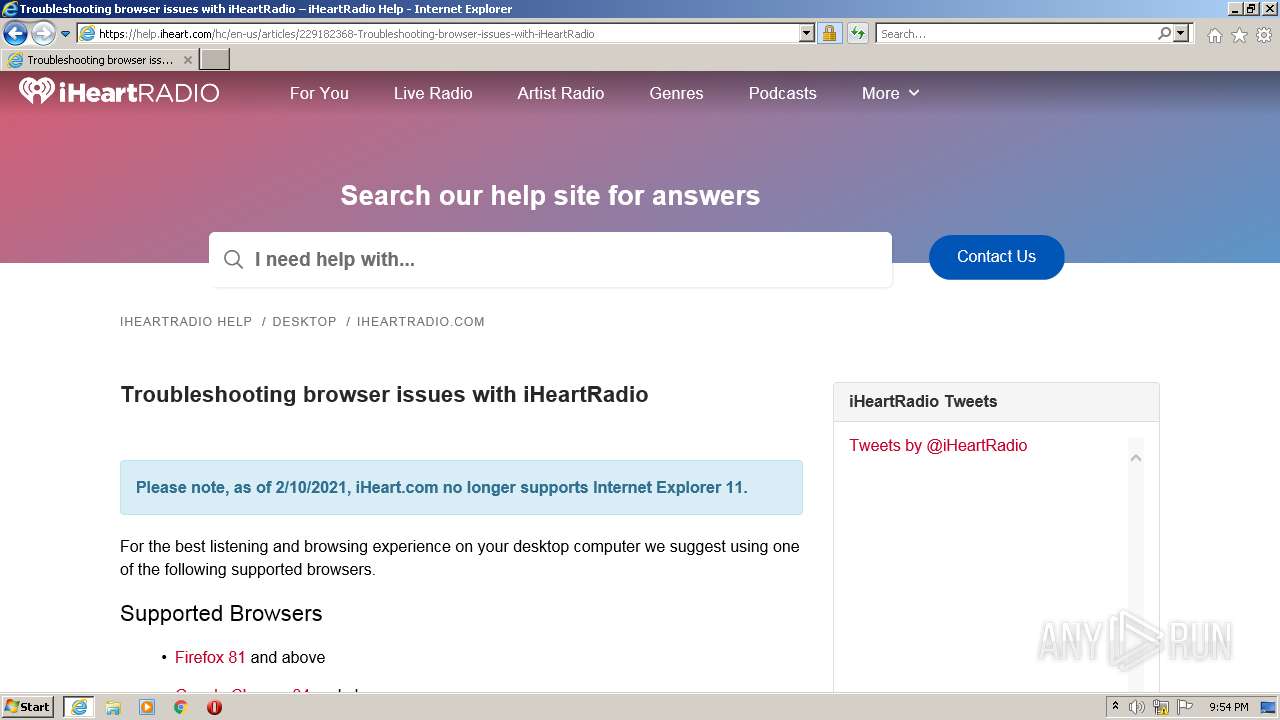
| Analysis date: | October 04, 2022, 20:51:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C50B09AA54C84C600651570927ED1D6D |
| SHA1: | B590D092EAB4AF6D7C251DF0FF539FA541BAFCAB |
| SHA256: | 3066C1A39C7F0834286CBA96F982645AA51739F8CFF2D878ADD6FC6A19580BA3 |
| SSDEEP: | 3:N88XRNEfvHWL:2V36 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2160)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 4040)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2160)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2160)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 2160)
INFO
Reads the computer name
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 3648)
Checks Windows Trust Settings
- iexplore.exe (PID: 3648)
- iexplore.exe (PID: 4040)
Reads settings of System Certificates
- iexplore.exe (PID: 3648)
- iexplore.exe (PID: 4040)
Creates files in the user directory
- iexplore.exe (PID: 3648)
- iexplore.exe (PID: 4040)
Application launched itself
- iexplore.exe (PID: 3648)
Checks supported languages
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 3648)
Reads CPU info
- iexplore.exe (PID: 4040)
Reads internet explorer settings
- iexplore.exe (PID: 4040)
Changes internet zones settings
- iexplore.exe (PID: 3648)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3648)
Changes settings of System certificates
- iexplore.exe (PID: 3648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2160 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 3648 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://iheartmedia.azurewebsites.net" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4040 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3648 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
33 320
Read events
33 117
Write events
195
Delete events
8
Modification events
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 641038656 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30988339 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 941198656 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30988339 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3648) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
57
Text files
409
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | binary | |
MD5:— | SHA256:— | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C5130A0BDC8C859A2757D77746C10868 | der | |
MD5:— | SHA256:— | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\iheartmedia.min[1].css | text | |
MD5:— | SHA256:— | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_BFEAFA0428B5B3BEDBF9F08F632429BE | binary | |
MD5:— | SHA256:— | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B039FEA45CB4CC4BBACFC013C7C55604_BFEAFA0428B5B3BEDBF9F08F632429BE | der | |
MD5:— | SHA256:— | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\0JQ7CD60.htm | html | |
MD5:— | SHA256:— | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\home[1].css | text | |
MD5:— | SHA256:— | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\aHR0cHM6Ly93d3cub21ueWNvbnRlbnQuY29tL2QvcGxheWxpc3QvZTczYzk5OGUtNmU2MC00MzJmLTg2MTAtYWUyMTAxNDBjNWIxL2NmNzc0NjY2LTczYWItNGEwZC1hZjU5LWFlMmUwMTQ0MDNjNi9mYT[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
206
DNS requests
75
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
4040 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHueQfY9sYqur%2B17E2BPFJI%3D | US | der | 1.40 Kb | whitelisted |
4040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | US | der | 471 b | whitelisted |
4040 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD6a7qQTCYd8hJU9n3M3mXb | US | der | 472 b | whitelisted |
4040 | iexplore.exe | GET | 200 | 65.9.84.191:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
4040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
4040 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDcThR%2BKEYP2BK026EbsM6F | US | der | 472 b | whitelisted |
4040 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEBJBetlj4ZeUEqggpI8HVMI%3D | US | der | 471 b | whitelisted |
4040 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCYpnK6j8BifgrC1DXWISSg | US | der | 472 b | whitelisted |
4040 | iexplore.exe | GET | 200 | 172.217.18.3:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDcThR%2BKEYP2BK026EbsM6F | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4040 | iexplore.exe | 52.171.221.170:443 | iheartmedia.azurewebsites.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4040 | iexplore.exe | 13.107.4.50:80 | ctldl.windowsupdate.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4040 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
4040 | iexplore.exe | 172.217.23.104:443 | www.googletagmanager.com | GOOGLE | US | suspicious |
4040 | iexplore.exe | 13.107.246.45:443 | cdn.iheartmedia.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | malicious |
4040 | iexplore.exe | 199.232.210.84:443 | i.iheart.com | FASTLY | US | unknown |
4040 | iexplore.exe | 142.250.186.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
4040 | iexplore.exe | 142.250.13.157:443 | stats.g.doubleclick.net | GOOGLE | US | suspicious |
4040 | iexplore.exe | 104.18.21.226:80 | ocsp2.globalsign.com | CLOUDFLARENET | — | shared |
4040 | iexplore.exe | 172.217.18.3:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iheartmedia.azurewebsites.net |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cdn.iheartmedia.com |
| suspicious |
i.iheart.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |