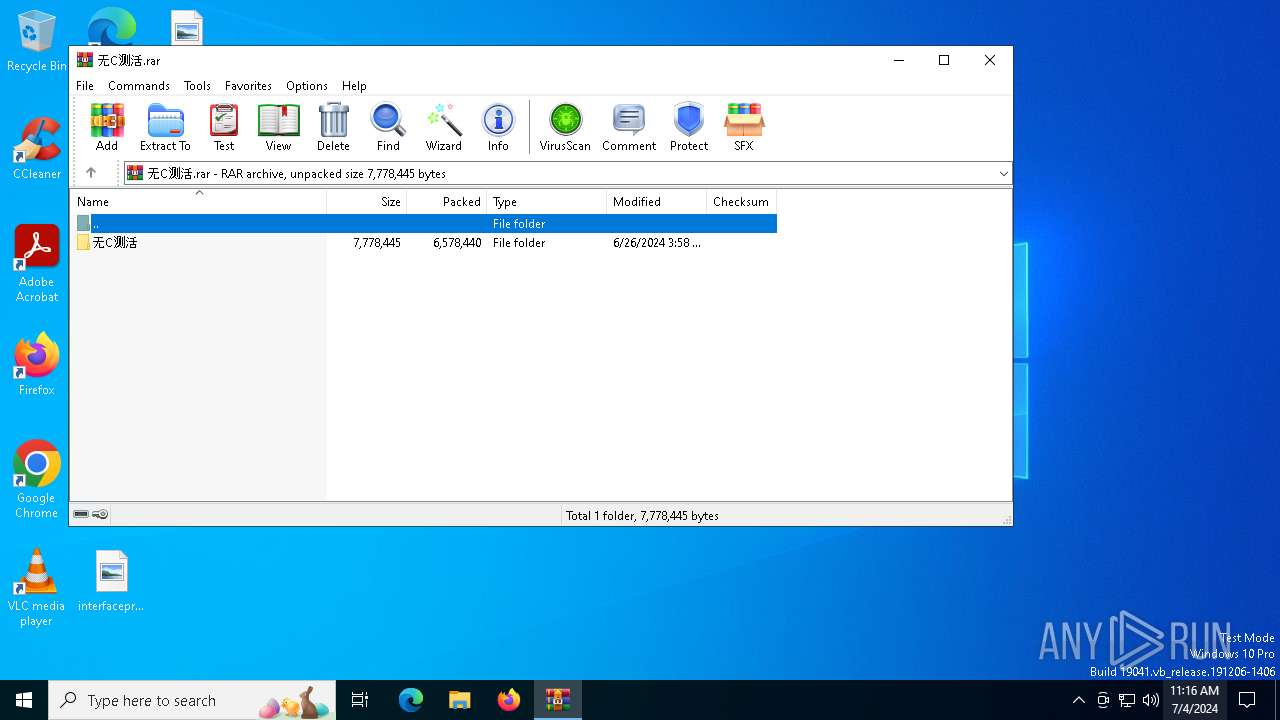
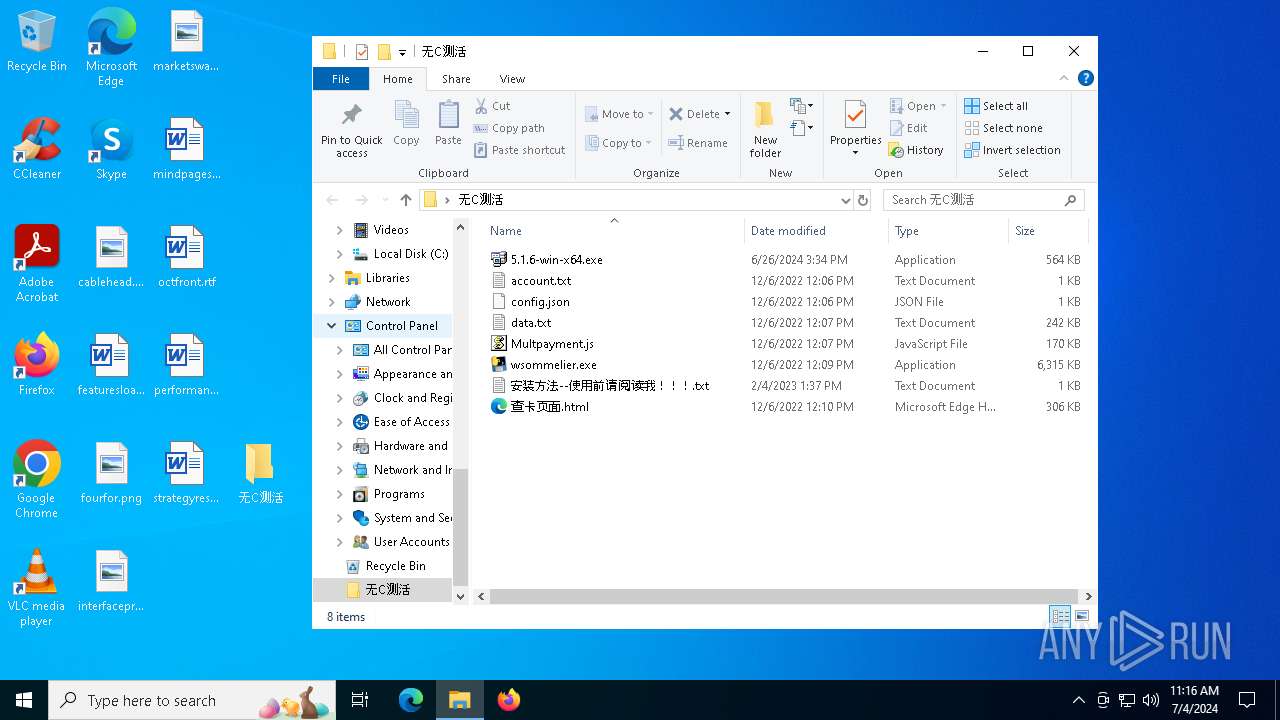
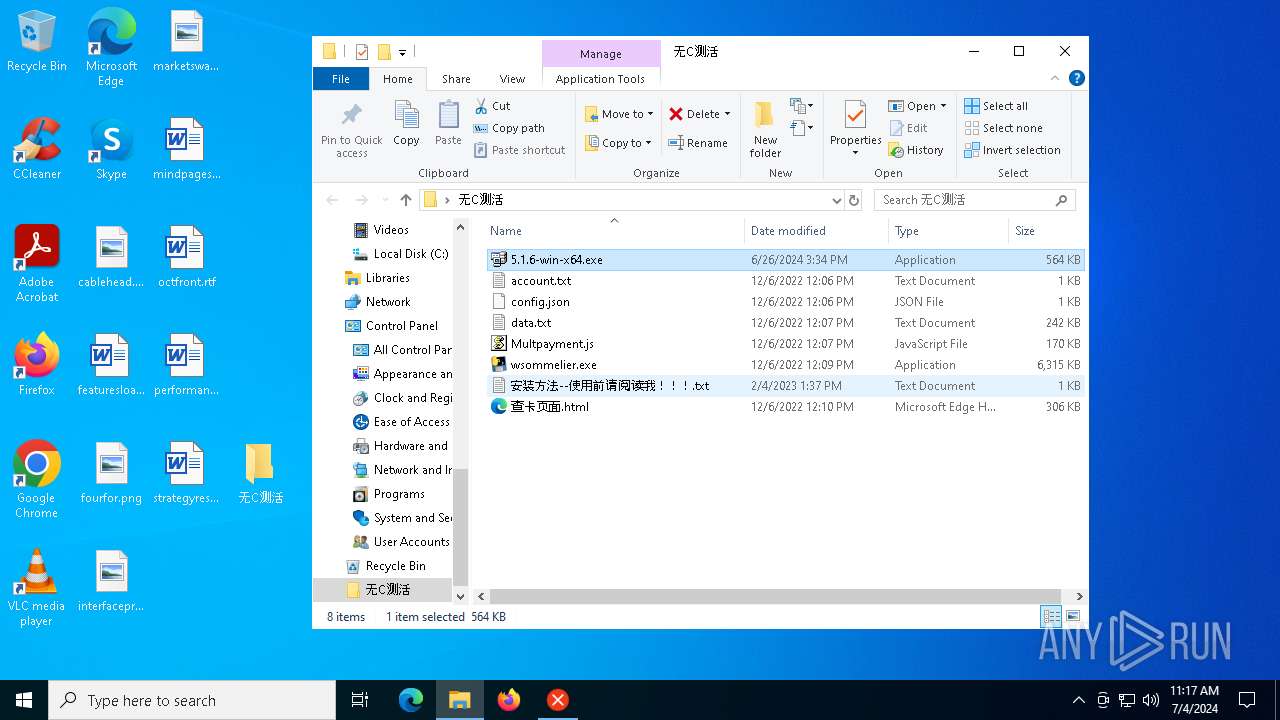
| File name: | 无C测活.rar |
| Full analysis: | https://app.any.run/tasks/4e6d380a-dae5-482a-8594-9b66490955fd |
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2024, 11:16:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 2D79C72865606A908E416B6AE01C185E |
| SHA1: | 0682B89C7B8B9ECC0CFFEAC8019E8DB9BF320E8A |
| SHA256: | 304FEF69D122D93F20F4B9D60D630165B0D1CDC674C4BD91B6BEB053D1150DE2 |
| SSDEEP: | 98304:bQHBSPVtQHBa2v1EGqpVDAgEGcmBh07+NqH1bG74NIhF4IcQxvQ4f5lUsR395CHL:GXrm4fK7DOtUK |
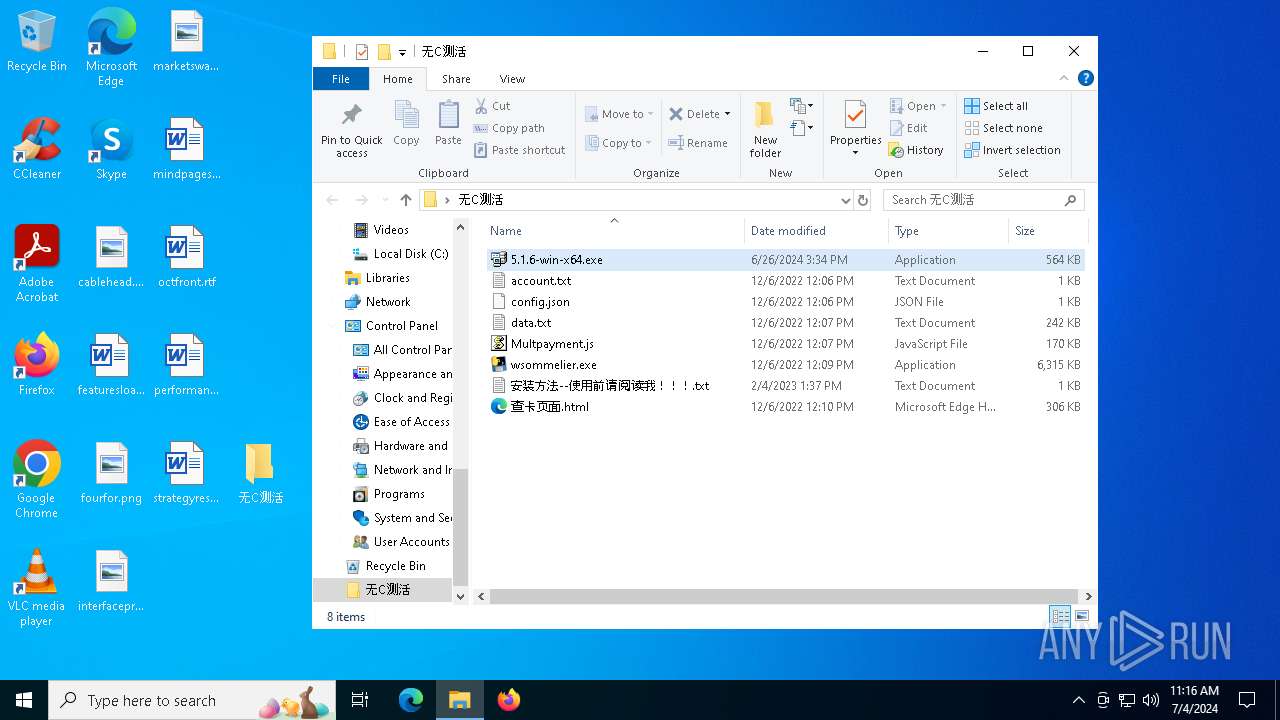
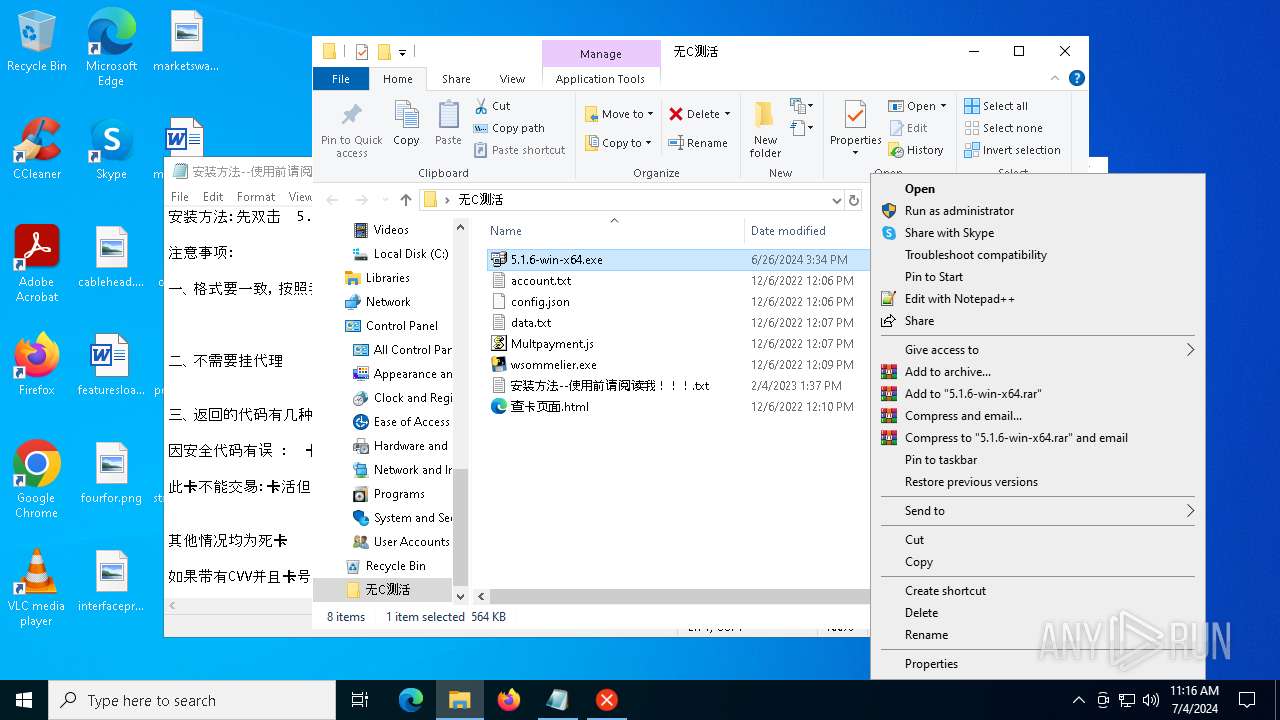
MALICIOUS
Changes the autorun value in the registry
- 5.1.6-win-x64.exe (PID: 6828)
Drops the executable file immediately after the start
- 5.1.6-win-x64.exe (PID: 6828)
- wsommelier.exe (PID: 7116)
SUSPICIOUS
Reads security settings of Internet Explorer
- 5.1.6-win-x64.exe (PID: 2888)
- 5.1.6-win-x64.exe (PID: 6828)
Checks Windows Trust Settings
- 5.1.6-win-x64.exe (PID: 2888)
- 5.1.6-win-x64.exe (PID: 6828)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 6900)
- cmd.exe (PID: 6908)
Starts CMD.EXE for commands execution
- 5.1.6-win-x64.exe (PID: 6828)
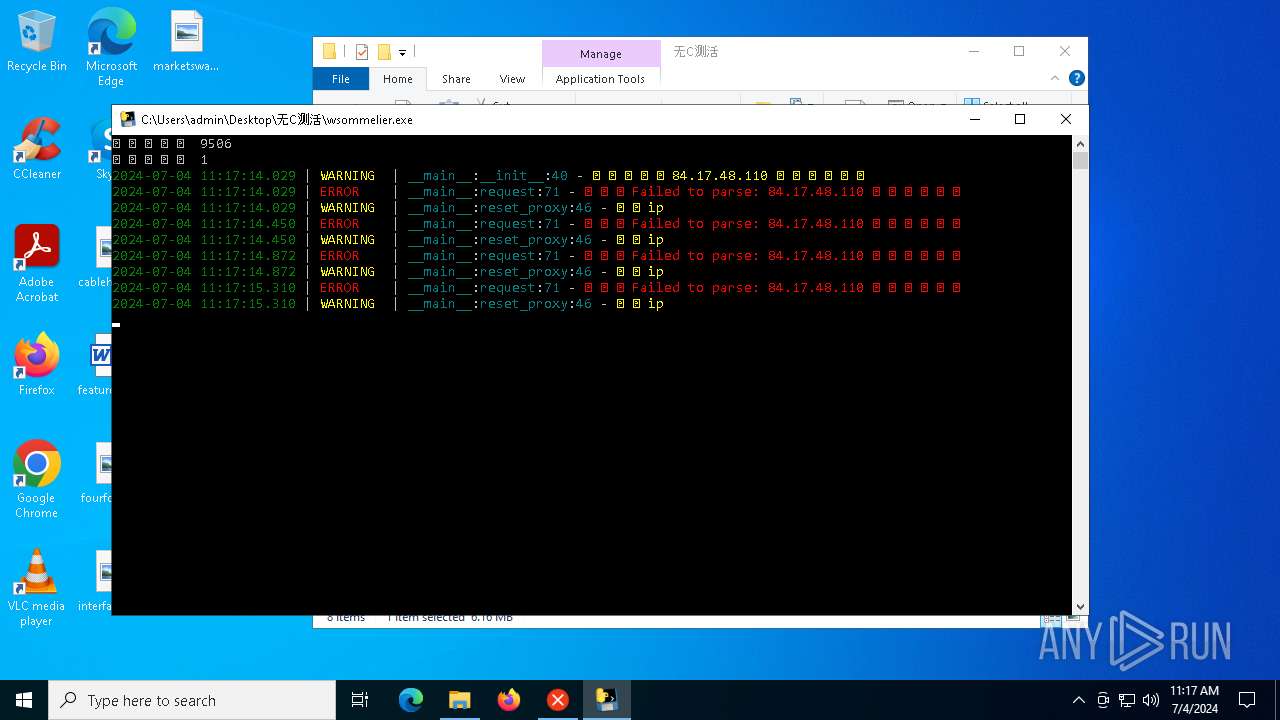
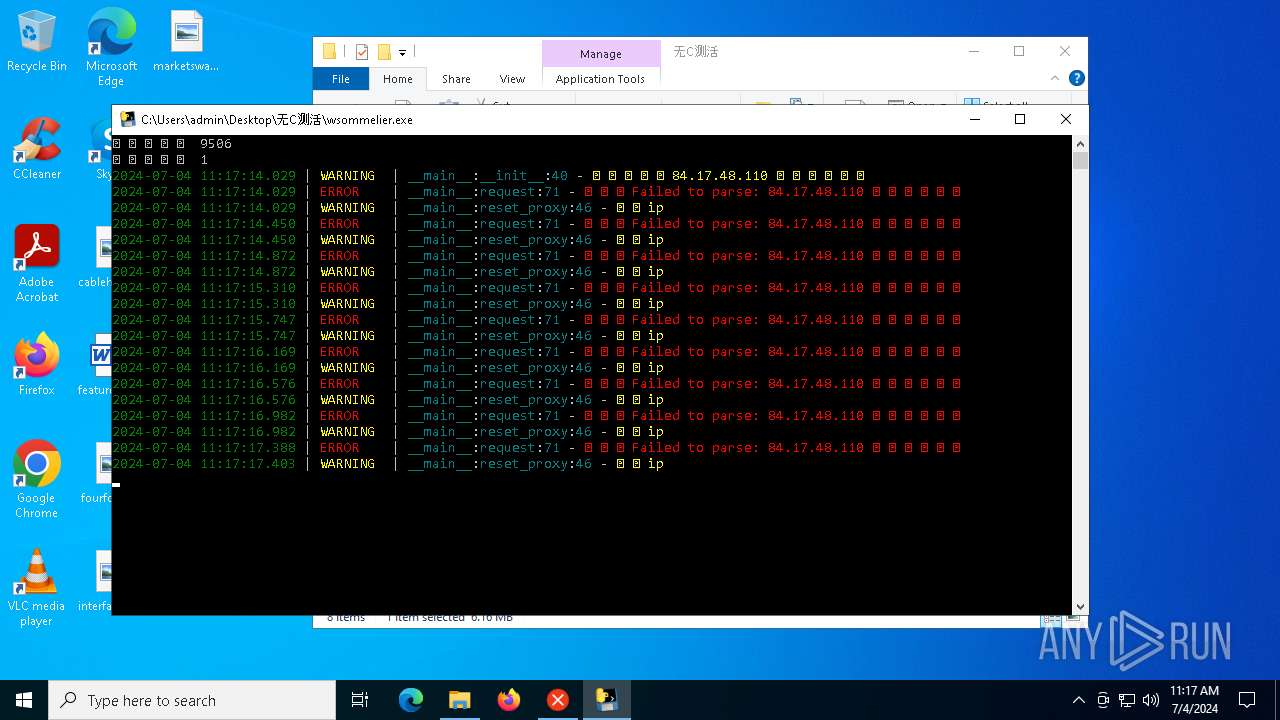
Connects to unusual port
- 5.1.6-win-x64.exe (PID: 6828)
- wsommelier.exe (PID: 448)
Executable content was dropped or overwritten
- 5.1.6-win-x64.exe (PID: 6828)
- wsommelier.exe (PID: 7116)
Drops a system driver (possible attempt to evade defenses)
- 5.1.6-win-x64.exe (PID: 6828)
Process drops legitimate windows executable
- wsommelier.exe (PID: 7116)
The process drops C-runtime libraries
- wsommelier.exe (PID: 7116)
Process drops python dynamic module
- wsommelier.exe (PID: 7116)
Potential Corporate Privacy Violation
- wsommelier.exe (PID: 448)
Application launched itself
- wsommelier.exe (PID: 7116)
Loads Python modules
- wsommelier.exe (PID: 448)
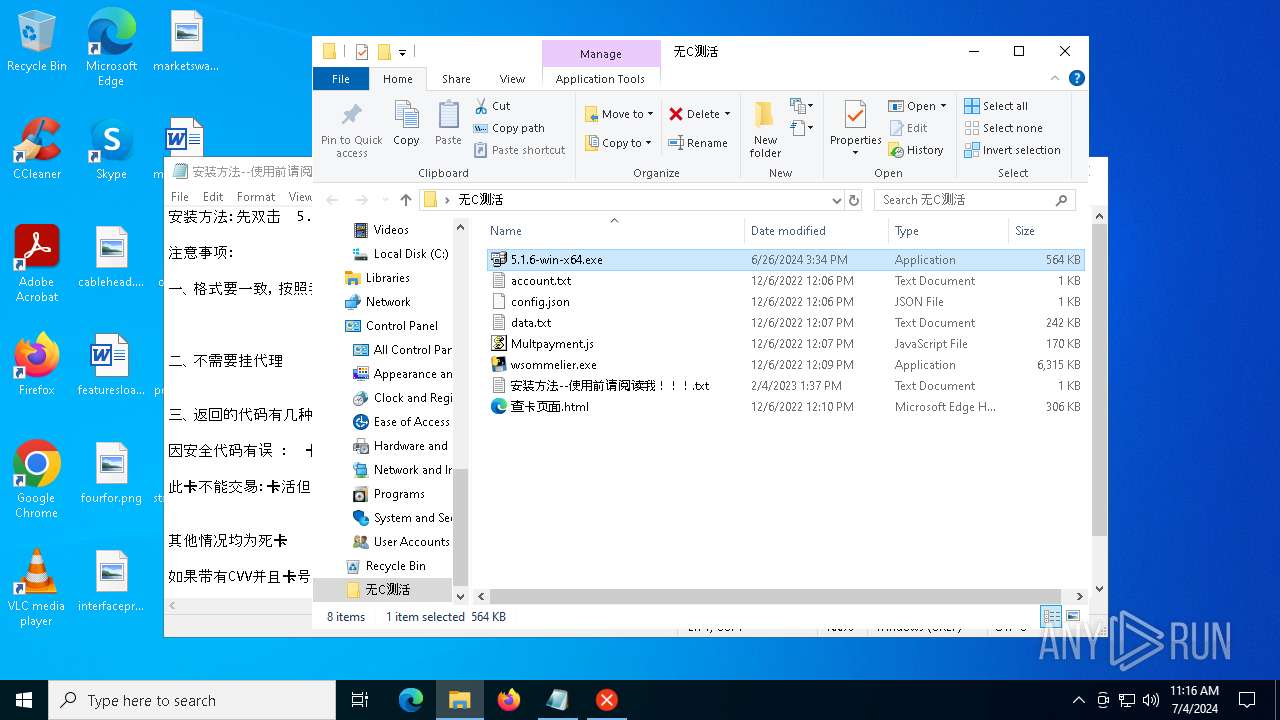
INFO
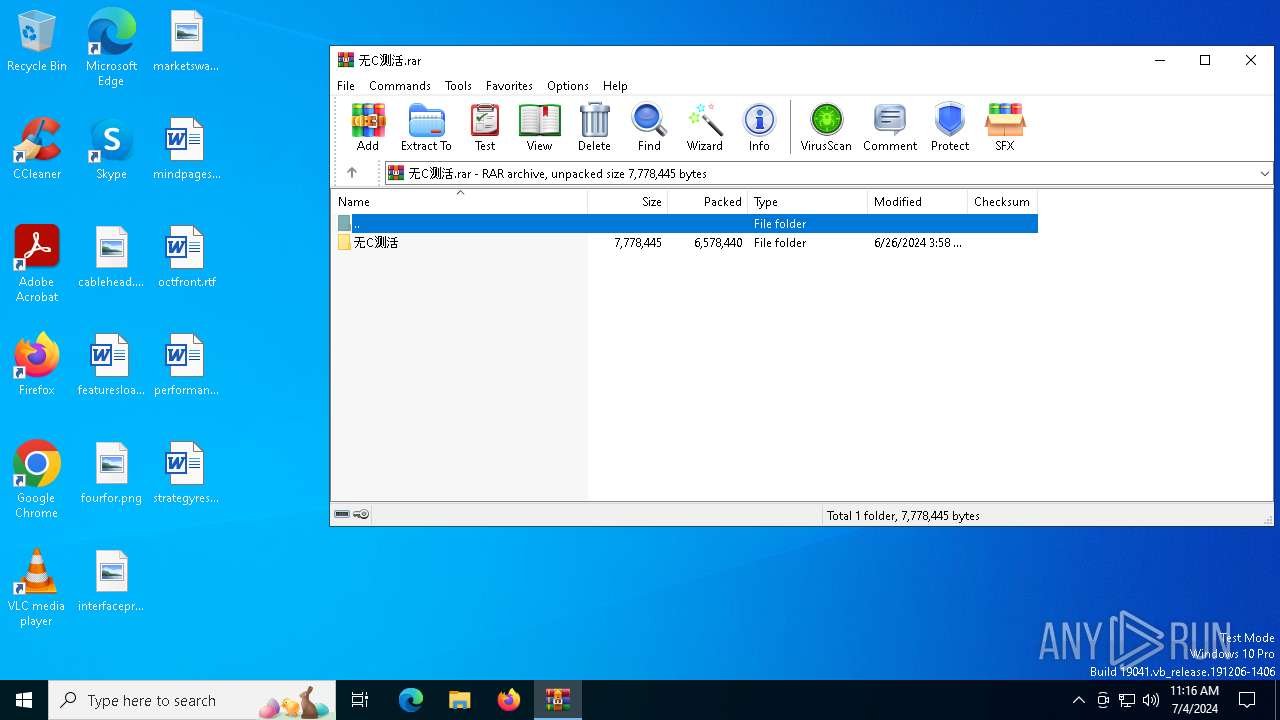
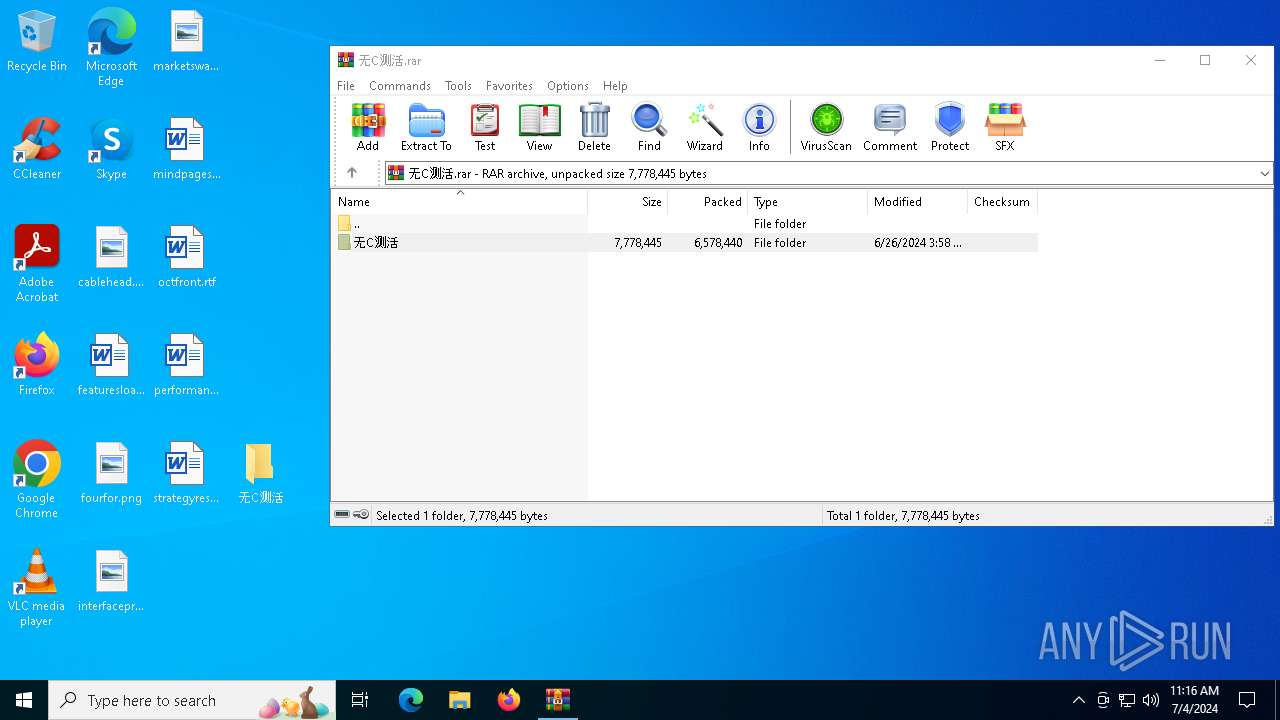
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5592)
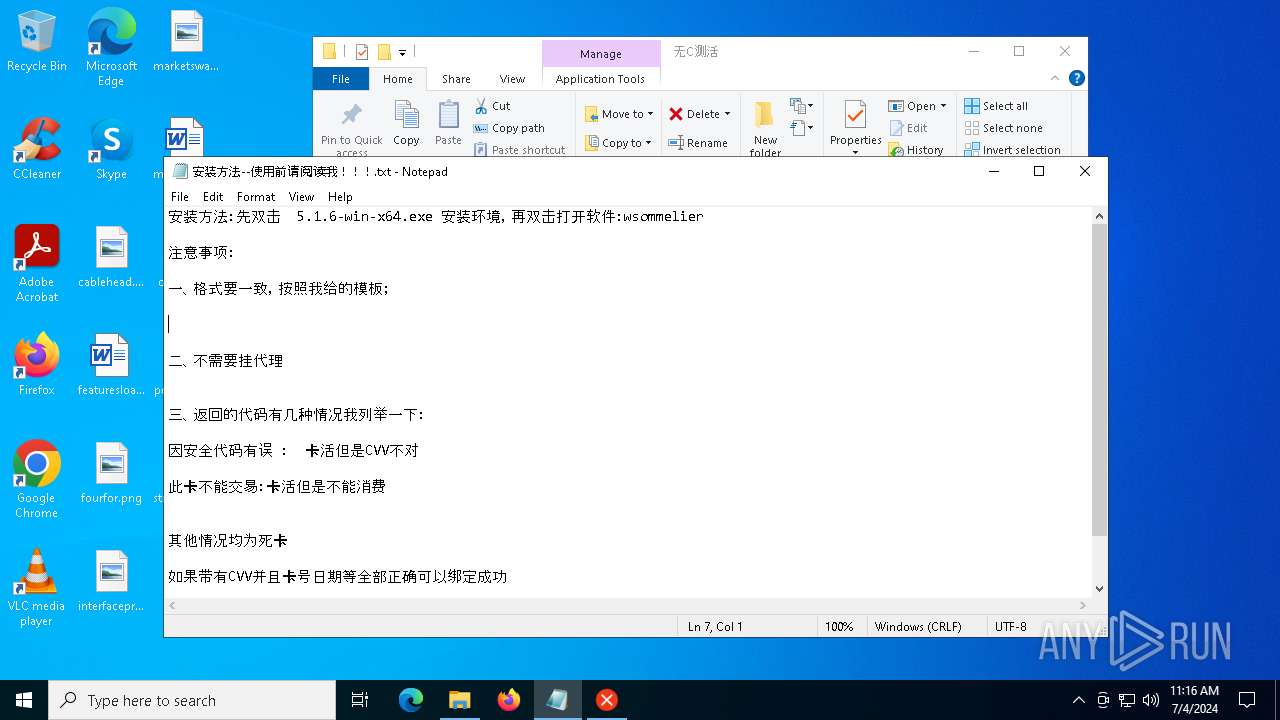
Manual execution by a user
- 5.1.6-win-x64.exe (PID: 2888)
- notepad.exe (PID: 2176)
- 5.1.6-win-x64.exe (PID: 6828)
- wsommelier.exe (PID: 7116)
Reads the machine GUID from the registry
- 5.1.6-win-x64.exe (PID: 2888)
- 5.1.6-win-x64.exe (PID: 6828)
- wsommelier.exe (PID: 448)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2176)
Checks supported languages
- 5.1.6-win-x64.exe (PID: 2888)
- 5.1.6-win-x64.exe (PID: 6828)
- wsommelier.exe (PID: 7116)
- wsommelier.exe (PID: 448)
Creates files in the program directory
- 5.1.6-win-x64.exe (PID: 2888)
- 5.1.6-win-x64.exe (PID: 6828)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 5592)
Reads the computer name
- 5.1.6-win-x64.exe (PID: 2888)
- 5.1.6-win-x64.exe (PID: 6828)
- wsommelier.exe (PID: 7116)
- wsommelier.exe (PID: 448)
Creates files or folders in the user directory
- 5.1.6-win-x64.exe (PID: 2888)
- 5.1.6-win-x64.exe (PID: 6828)
Checks proxy server information
- 5.1.6-win-x64.exe (PID: 2888)
- 5.1.6-win-x64.exe (PID: 6828)
- wsommelier.exe (PID: 448)
Reads the software policy settings
- 5.1.6-win-x64.exe (PID: 2888)
- 5.1.6-win-x64.exe (PID: 6828)
Reads CPU info
- 5.1.6-win-x64.exe (PID: 6828)
Create files in a temporary directory
- wsommelier.exe (PID: 7116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
151
Monitored processes
12
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
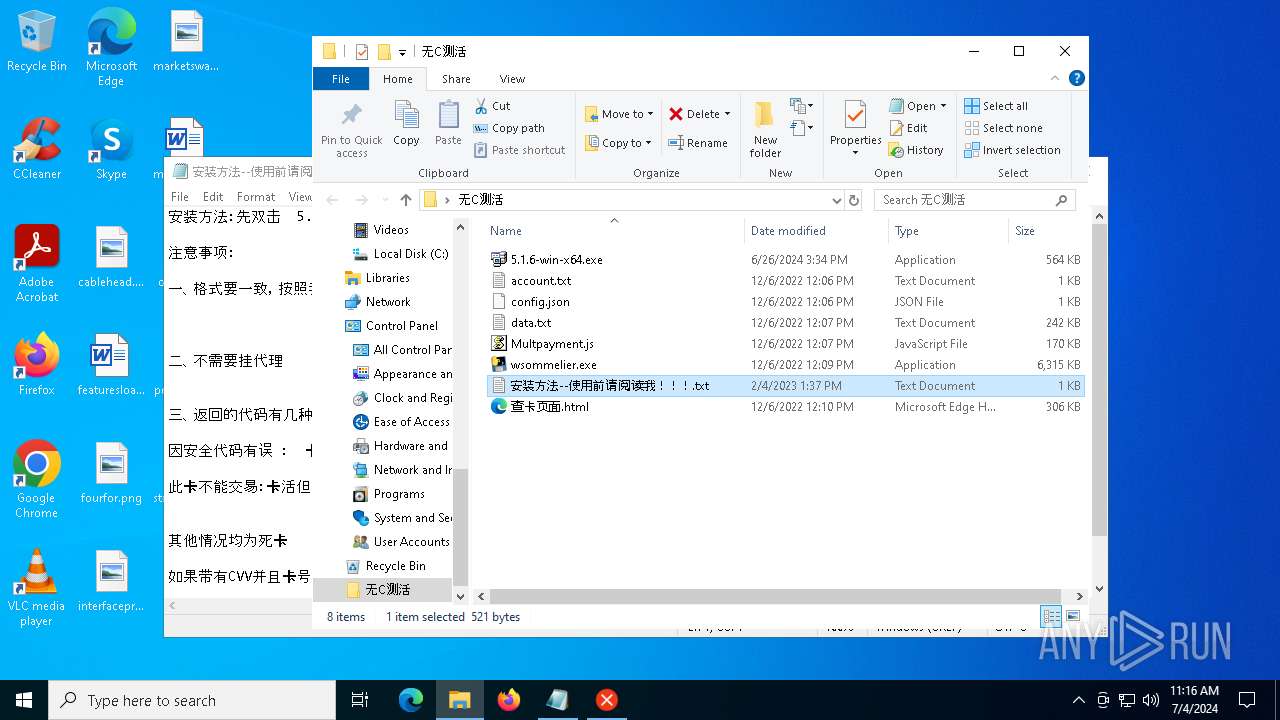
| 448 | "C:\Users\admin\Desktop\无C测活\wsommelier.exe" | C:\Users\admin\Desktop\无C测活\wsommelier.exe | wsommelier.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
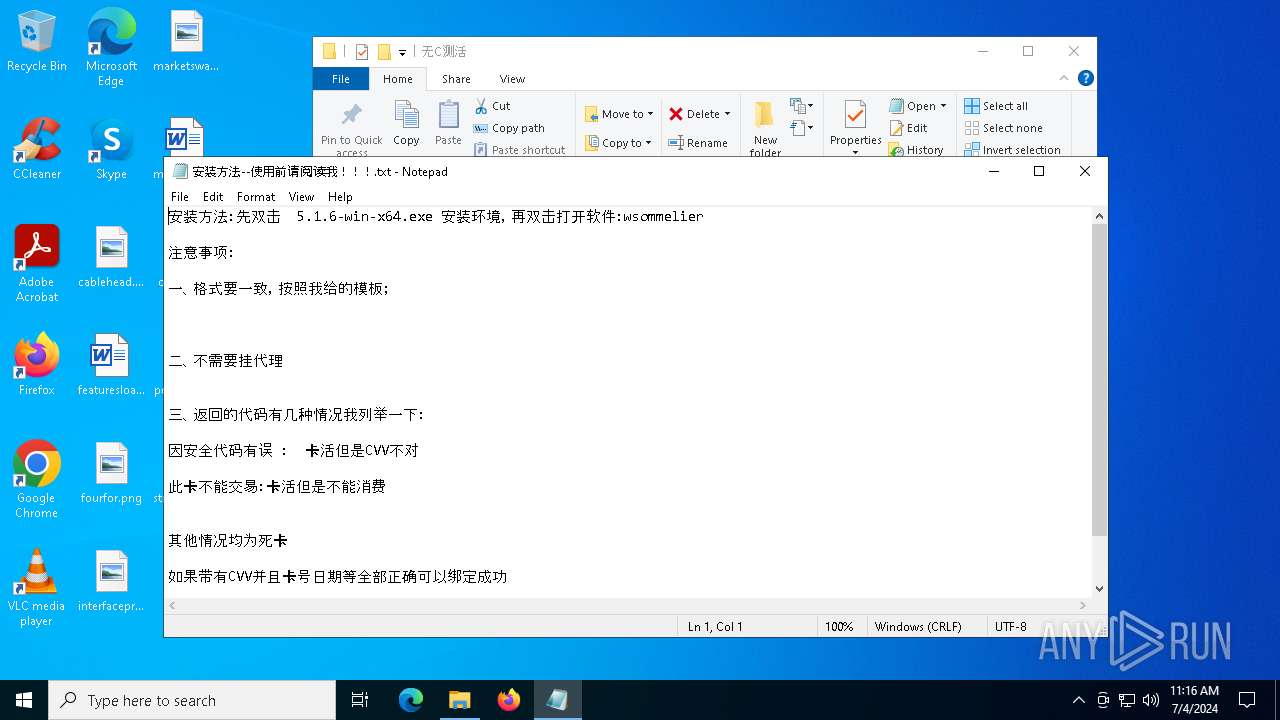
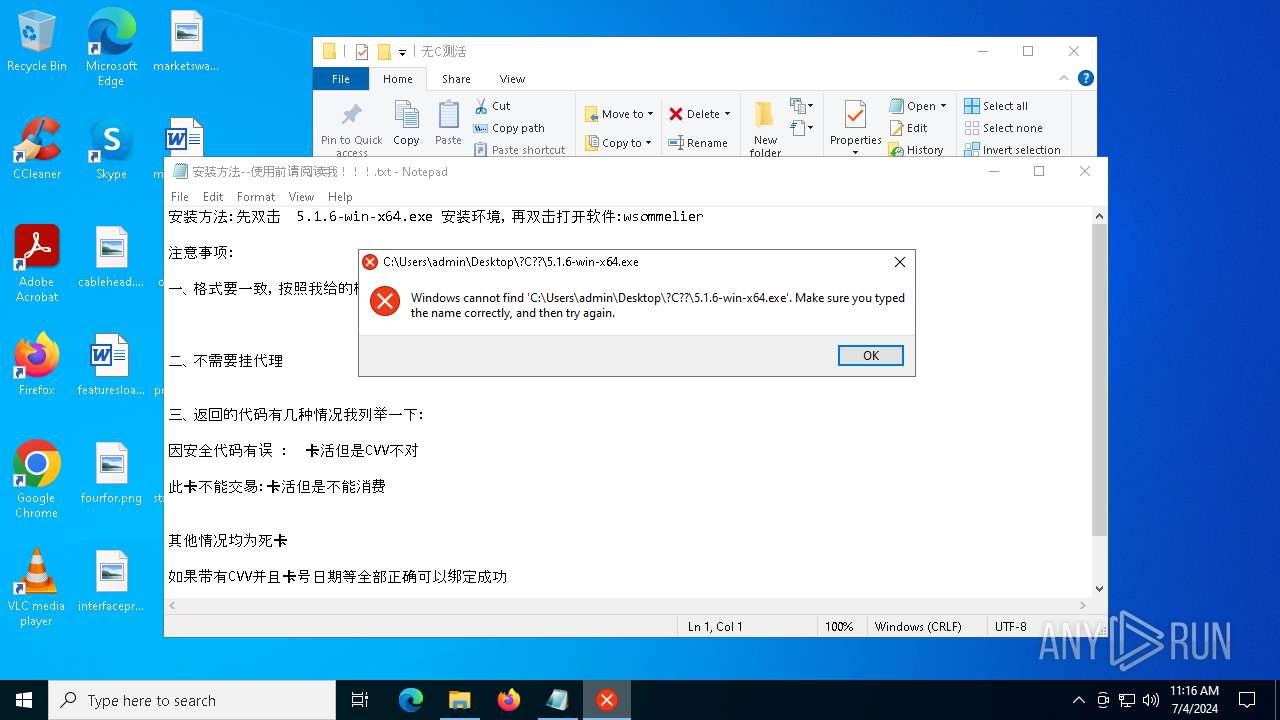
| 2176 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\无C测活\安装方法--使用前请阅读我!!!.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2888 | "C:\Users\admin\Desktop\无C测活\5.1.6-win-x64.exe" | C:\Users\admin\Desktop\无C测活\5.1.6-win-x64.exe | explorer.exe | ||||||||||||
User: admin Company: Pablo Software Solutions Integrity Level: MEDIUM Description: FTPServer MFC Application Version: 1, 0, 0, 8 Modules
| |||||||||||||||
| 4152 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5592 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\无C测活.rar | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6828 | "C:\Users\admin\Desktop\无C测活\5.1.6-win-x64.exe" | C:\Users\admin\Desktop\无C测活\5.1.6-win-x64.exe | explorer.exe | ||||||||||||
User: admin Company: Pablo Software Solutions Integrity Level: HIGH Description: FTPServer MFC Application Version: 1, 0, 0, 8 Modules
| |||||||||||||||
| 6900 | cmd /c md C:\Users\Public\Documents\MM | C:\Windows\SysWOW64\cmd.exe | — | 5.1.6-win-x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6908 | cmd /c md C:\Users\Public\Documents\MM | C:\Windows\SysWOW64\cmd.exe | — | 5.1.6-win-x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6916 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6948 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 645
Read events
8 601
Write events
44
Delete events
0
Modification events
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\无C测活.rar | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF420100002D0000000205000016020000 | |||
| (PID) Process: | (5592) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
26
Suspicious files
10
Text files
7
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5592 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5592.9637\无C测活\安装方法--使用前请阅读我!!!.txt | text | |
MD5:575DD56E10DD3F04813EE46452DA40AF | SHA256:7F12DCDC35F6A1CC37A4B717F2A6301931AD8F54A858783B7D4E983D8A626324 | |||
| 6828 | 5.1.6-win-x64.exe | C:\Users\Public\Documents\MM\1.sys | executable | |
MD5:21E13F2CB269DEFEAE5E1D09887D47BB | SHA256:543991CA8D1C65113DFF039B85AE3F9A87F503DAEC30F46929FD454BC57E5A91 | |||
| 6828 | 5.1.6-win-x64.exe | C:\Users\Public\Documents\MM\2.txt | binary | |
MD5:34D759FC3E6F0C56CE0B93C9C586A623 | SHA256:9CCA42991992DFF8282491E5946C15FE6EC670B219EF0179FF386B541F74E38D | |||
| 5592 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5592.9637\无C测活\wsommelier.exe | executable | |
MD5:232A601CEDC54391AF5BFBCC068CFE64 | SHA256:E95E66692AA4F533F1A14121EA17B91A1509B3D734215A52B12CCB6818B01F84 | |||
| 5592 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5592.9637\无C测活\config.json | text | |
MD5:09AF31666964FDC8CAA4759E3347F6C2 | SHA256:91D6EABA06DADAC2F50270421E5FB5BB65EB3E8FFE32DEBAF10ACB580FE3B075 | |||
| 2888 | 5.1.6-win-x64.exe | C:\ProgramData\3.TXT | binary | |
MD5:93C24E7101B69C5C1E88BF45E32468F5 | SHA256:1FFEFA2227BCA35A7504F711642F480D7D96292477976ABC0CDF78F7D4913C82 | |||
| 2888 | 5.1.6-win-x64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3FE2BD01AB6BC312BF0DADE7F797388F_953CA3EA42F903AAF05DC35F3854754B | binary | |
MD5:386BA0E20BF76BD2094340C84AD430EE | SHA256:52887423470A05E9E6B88C7C565285327FDF74634127DC7B536954F7E28E71CA | |||
| 5592 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa5592.9637\无C测活\查卡页面.html | html | |
MD5:71BAA00F499974EDAB3D0B0D979DC447 | SHA256:65A1FB2D37E51441641A51C3962469FB4E66CEB2787B15CECE880FEAAAA95013 | |||
| 2888 | 5.1.6-win-x64.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BC16B2ECE312D7AC56CE801D5C6ED1A4_B9C2B000696A21C0D71B40842850D55F | der | |
MD5:FAD33C25B9DA2CCB02F19509083FC387 | SHA256:962700EC268FCCE55263A29CA463C050D176E3555A5AC4E7799FA708C3369DD8 | |||
| 2888 | 5.1.6-win-x64.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\AH8CR9J5\klk[1].txt | binary | |
MD5:93C24E7101B69C5C1E88BF45E32468F5 | SHA256:1FFEFA2227BCA35A7504F711642F480D7D96292477976ABC0CDF78F7D4913C82 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
78
DNS requests
20
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
448 | wsommelier.exe | GET | 200 | 34.92.5.66:8088 | http://list.rola.info:8088/user_get_ip_list?token=kgzbUg4XTrY5kG501669197086185&qty=1&country=&state=&city=&time=5&format=txt&protocol=http&filter=1 | unknown | — | — | unknown |
448 | wsommelier.exe | GET | 200 | 34.92.5.66:8088 | http://list.rola.info:8088/user_get_ip_list?token=kgzbUg4XTrY5kG501669197086185&qty=1&country=&state=&city=&time=5&format=txt&protocol=http&filter=1 | unknown | — | — | unknown |
4448 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
4448 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
2888 | 5.1.6-win-x64.exe | GET | 200 | 163.181.92.241:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEANnihZNYn0Q7n1uAg7HHnk%3D | unknown | — | — | unknown |
2888 | 5.1.6-win-x64.exe | GET | 200 | 163.181.92.241:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTAYhVVBolGXL98B12VBQmMNc4EWAQUmtkNEMnEX0wy0ufwG61Kpi0lO9QCEAh%2BTyqv7uWN0S0Qkr2oj%2BM%3D | unknown | — | — | unknown |
4656 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | unknown |
5600 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
2008 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | unknown |
6608 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4448 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1856 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4772 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4448 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4448 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4448 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
2888 | 5.1.6-win-x64.exe | 111.177.9.205:443 | fs-im-kefu.7moor-fs1.com | Xiangyang, Hubei Province, P.R.China. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fs-im-kefu.7moor-fs1.com |
| unknown |
ocsp.digicert.cn |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
19 ETPRO signatures available at the full report