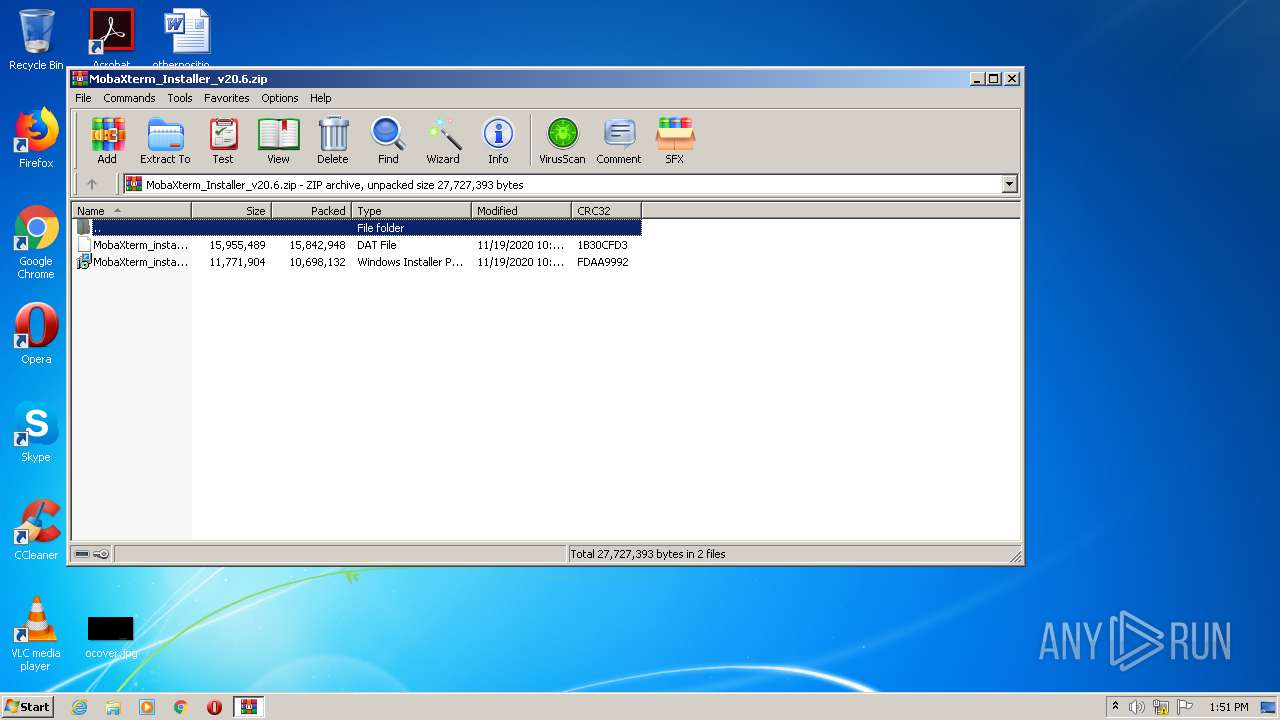
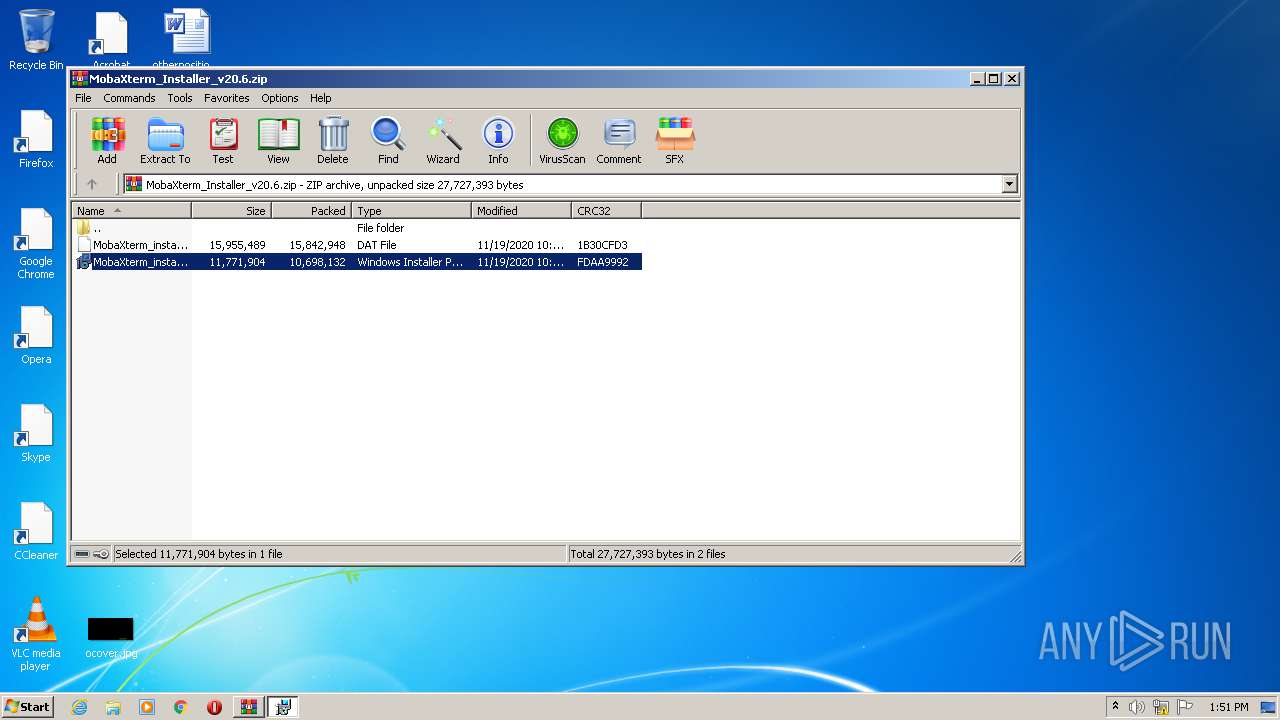
| download: | MobaXterm_Installer_v20.6.zip |
| Full analysis: | https://app.any.run/tasks/d6b8cfd3-471f-4db5-b8ea-a3d75f59b4e4 |
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2020, 13:50:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 50DB247780E96C9B9B3FE4D00DDDEEF7 |
| SHA1: | 5FE660CC59B9D99817153CB2F66873EBB72618BF |
| SHA256: | 304782B10F3E9B4173B879968280DEFAF61F5032C4F1DAE42BD1B386185F90F1 |
| SSDEEP: | 786432:5DhoyxToE1Q1/y5AzGWyMexeXYFs2k6J/Vtn:5bxTVesWVyee1n |
MALICIOUS
Application was dropped or rewritten from another process
- MobaXterm.exe (PID: 2840)
- MobaXterm.exe (PID: 1760)
- XWin_MobaX.exe (PID: 3028)
- xkbcomp_w32.exe (PID: 2280)
- cygtermd.exe (PID: 3604)
- motty.exe (PID: 3444)
- cygtermd.exe (PID: 2780)
- bash.exe (PID: 2156)
- bash.exe (PID: 3584)
- busybox.exe (PID: 2496)
- bash.exe (PID: 3808)
- busybox.exe (PID: 2332)
- bash.exe (PID: 332)
- bash.exe (PID: 2680)
Detects Cygwin installation
- MobaXterm.exe (PID: 1760)
Loads dropped or rewritten executable
- XWin_MobaX.exe (PID: 3028)
- SearchProtocolHost.exe (PID: 3184)
- cygtermd.exe (PID: 3604)
- bash.exe (PID: 2156)
- xkbcomp_w32.exe (PID: 2280)
- cygtermd.exe (PID: 2780)
- bash.exe (PID: 3584)
- busybox.exe (PID: 2496)
- bash.exe (PID: 3808)
- busybox.exe (PID: 2332)
- bash.exe (PID: 332)
- bash.exe (PID: 2680)
SUSPICIOUS
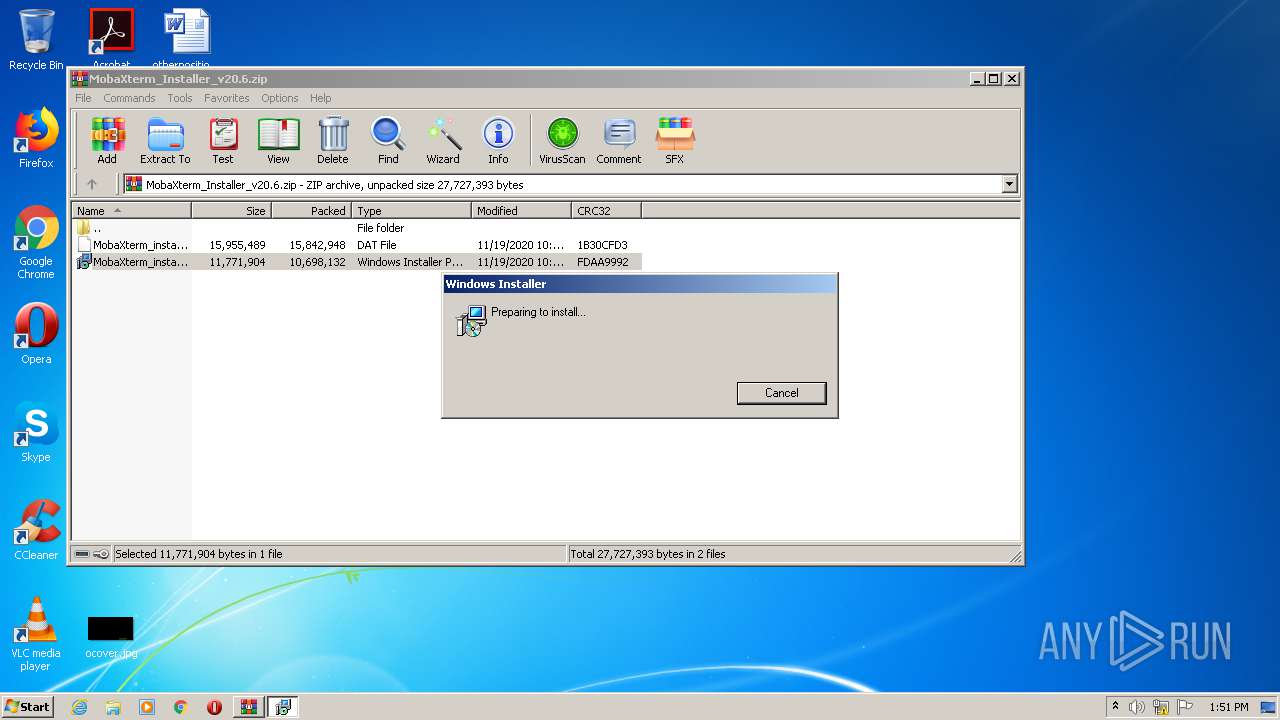
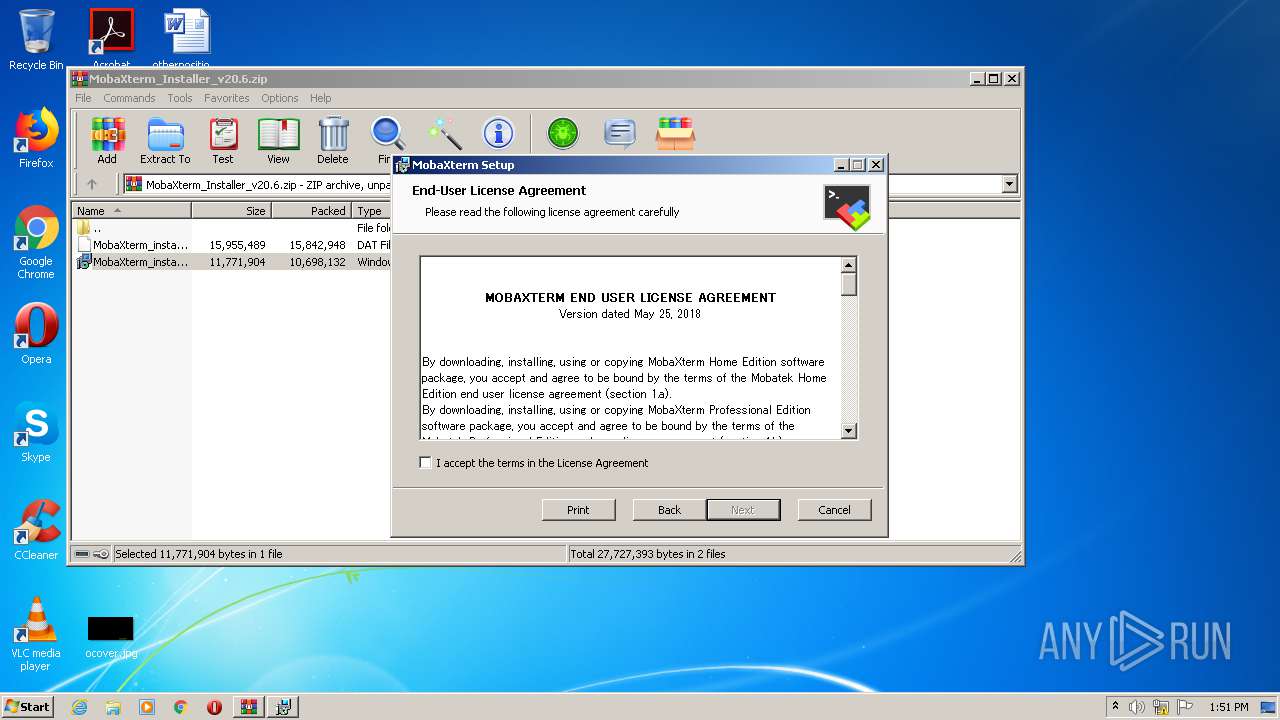
Starts Microsoft Installer
- WinRAR.exe (PID: 3048)
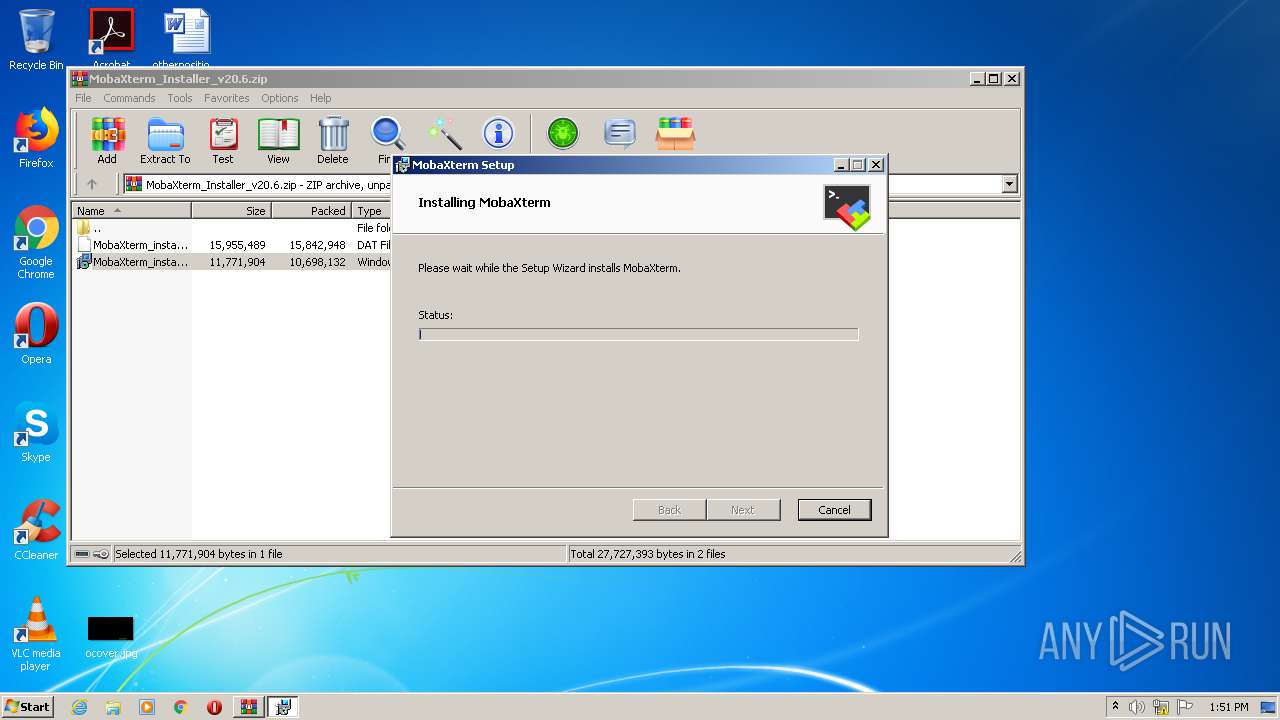
Executable content was dropped or overwritten
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 2540)
- MobaXterm.exe (PID: 1760)
Drops a file with too old compile date
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 2540)
- MobaXterm.exe (PID: 1760)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 2852)
- msiexec.exe (PID: 2540)
Executed as Windows Service
- vssvc.exe (PID: 2740)
Changes default file association
- msiexec.exe (PID: 2540)
Creates files in the program directory
- MobaXterm.exe (PID: 2840)
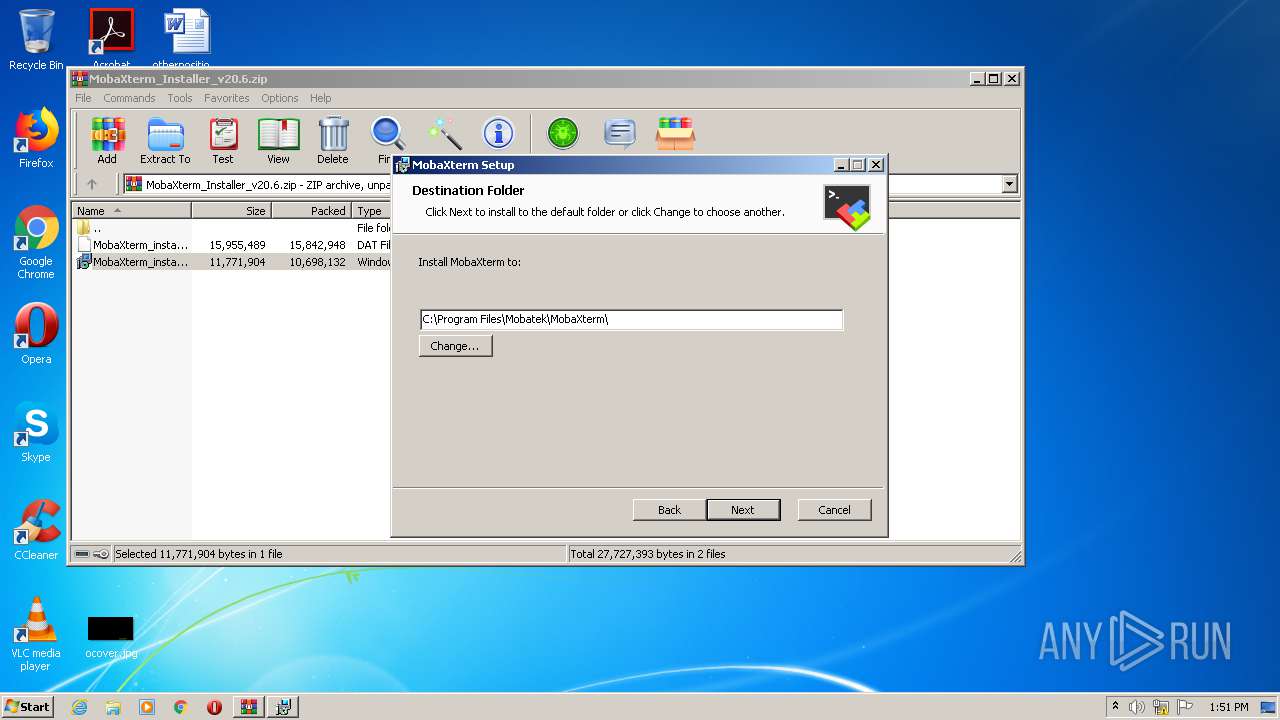
Creates a directory in Program Files
- msiexec.exe (PID: 2540)
Drops a file with a compile date too recent
- MobaXterm.exe (PID: 1760)
Application launched itself
- cygtermd.exe (PID: 3604)
- bash.exe (PID: 2156)
INFO
Searches for installed software
- msiexec.exe (PID: 2540)
Application launched itself
- msiexec.exe (PID: 2540)
Creates files in the program directory
- MsiExec.exe (PID: 2848)
- msiexec.exe (PID: 2540)
Creates a software uninstall entry
- msiexec.exe (PID: 2540)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2848)
- MsiExec.exe (PID: 1976)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2740)
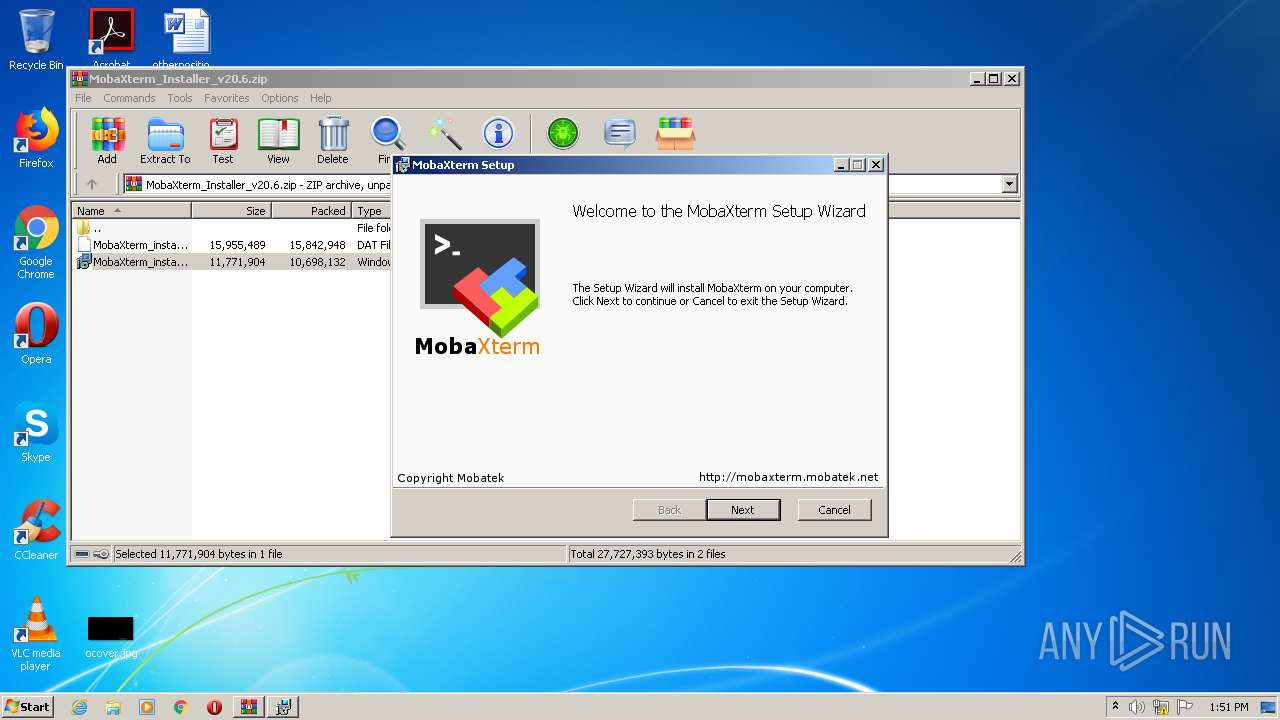
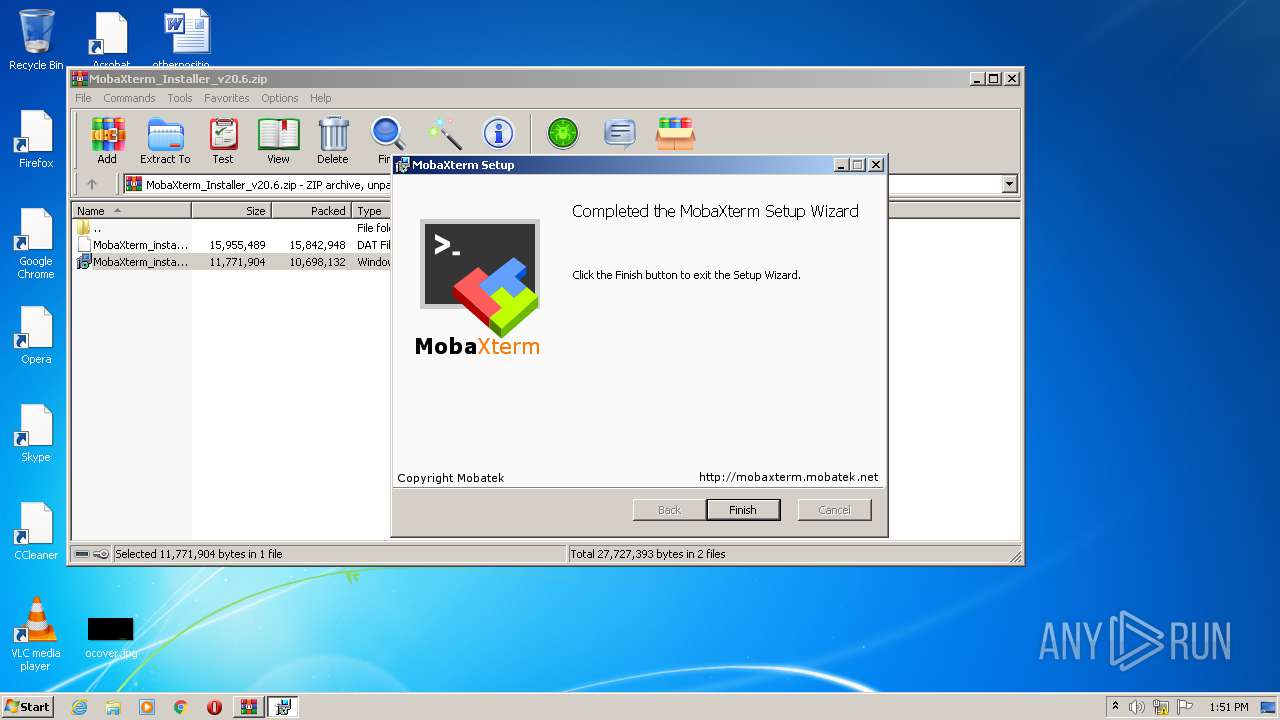
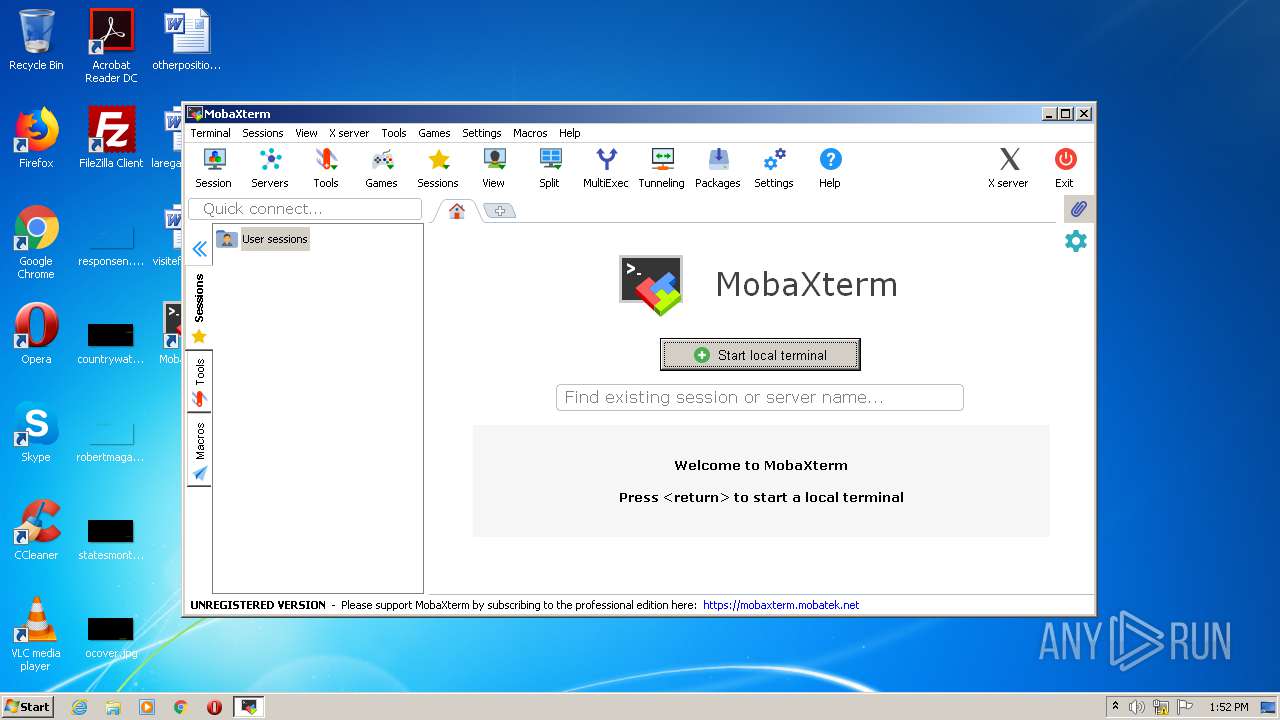
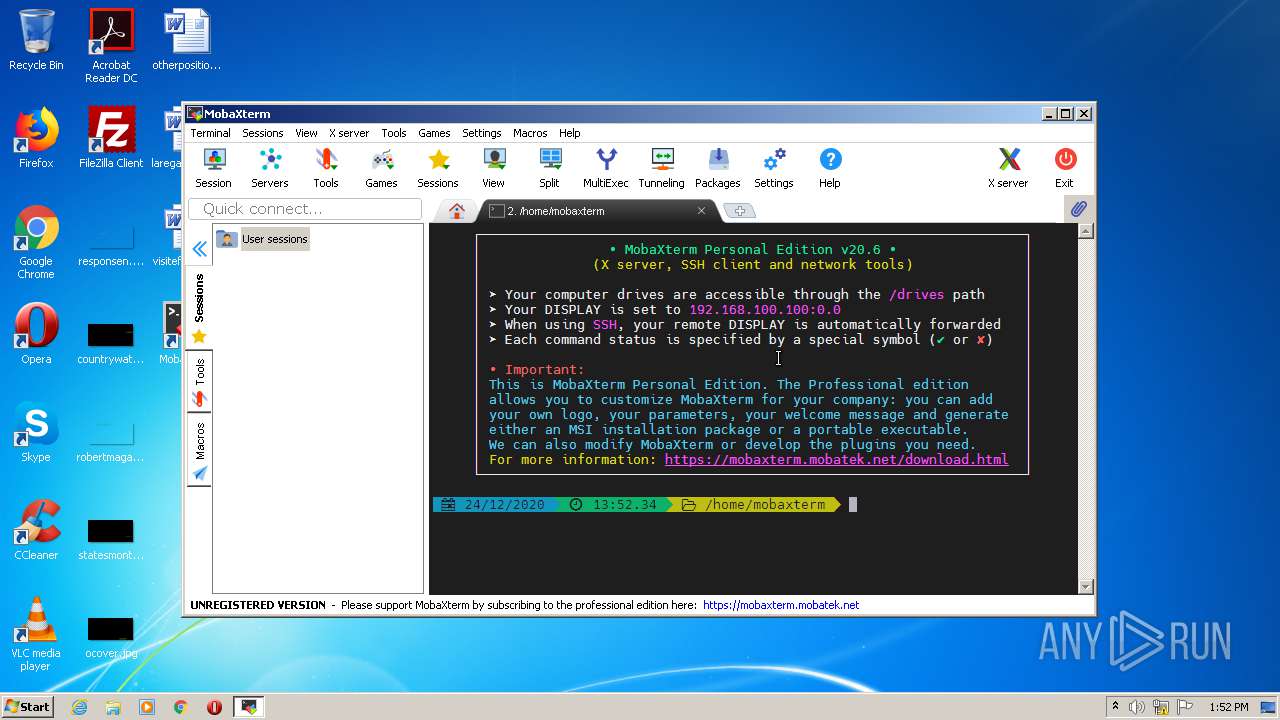
Manual execution by user
- MobaXterm.exe (PID: 1760)
Dropped object may contain Bitcoin addresses
- MobaXterm.exe (PID: 1760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:11:19 23:02:08 |
| ZipCRC: | 0xfdaa9992 |
| ZipCompressedSize: | 10698132 |
| ZipUncompressedSize: | 11771904 |
| ZipFileName: | MobaXterm_installer_20.6.msi |
Total processes
59
Monitored processes
22
Malicious processes
10
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\bash.exe" | C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\bash.exe | — | bash.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Mobatek\MobaXterm\MobaXterm.exe" | C:\Program Files\Mobatek\MobaXterm\MobaXterm.exe | explorer.exe | ||||||||||||
User: admin Company: Mobatek Integrity Level: MEDIUM Description: MobaXterm Exit code: 0 Version: 20.6.0.4532 Modules
| |||||||||||||||
| 1976 | C:\Windows\system32\MsiExec.exe -Embedding 5E47FCE9A71C86D9DEF38E39D0DF2924 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\bash.exe" | C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\bash.exe | — | cygtermd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 2280 | "C:\Users\admin\DOCUME~1\MobaXterm\slash\bin\xkbcomp_w32.exe" -w 1 "-RC:\Users\admin\DOCUME~1\MobaXterm\slash\usr\share\X11\xkb" -xkm "C:\Users\admin\DOCUME~1\MobaXterm\slash\var\log\xwin\xkb_a03036" -em1 "The XKEYBOARD keymap compiler (xkbcomp) reports:" -emp "> " -eml "Errors from xkbcomp are not fatal to the X server" "C:\Users\admin\DOCUME~1\MobaXterm\slash\var\log\xwin\server-0.xkm" | C:\Users\admin\DOCUME~1\MobaXterm\slash\bin\xkbcomp_w32.exe | — | XWin_MobaX.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2332 | "C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\busybox.exe" | C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\busybox.exe | — | bash.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 256 Modules
| |||||||||||||||
| 2496 | "C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\busybox.exe" | C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\busybox.exe | — | bash.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2540 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2680 | "C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\bash.exe" | C:\Users\admin\DOCUME~1\MOBAXT~1\slash\bin\bash.exe | — | bash.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2740 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 535
Read events
1 813
Write events
704
Delete events
18
Modification events
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MobaXterm_Installer_v20.6.zip | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msimsg.dll,-34 |
Value: Windows Installer Package | |||
| (PID) Process: | (3048) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
247
Suspicious files
286
Text files
974
Unknown types
141
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3048.19570\MobaXterm_installer_20.6.msi | — | |
MD5:— | SHA256:— | |||
| 2540 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2540 | msiexec.exe | C:\Windows\Installer\13236a.msi | — | |
MD5:— | SHA256:— | |||
| 2540 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF0EA7A41AE2854AF1.TMP | — | |
MD5:— | SHA256:— | |||
| 2740 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2540 | msiexec.exe | C:\Windows\Installer\13236d.msi | — | |
MD5:— | SHA256:— | |||
| 2540 | msiexec.exe | C:\Config.Msi\13236c.rbs | — | |
MD5:— | SHA256:— | |||
| 2540 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF6DE031606F2513AF.TMP | — | |
MD5:— | SHA256:— | |||
| 3048 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3048.19570\MobaXterm_installer.dat | compressed | |
MD5:— | SHA256:— | |||
| 2540 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{911be242-84dc-40bb-84b8-82da66de2872}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report