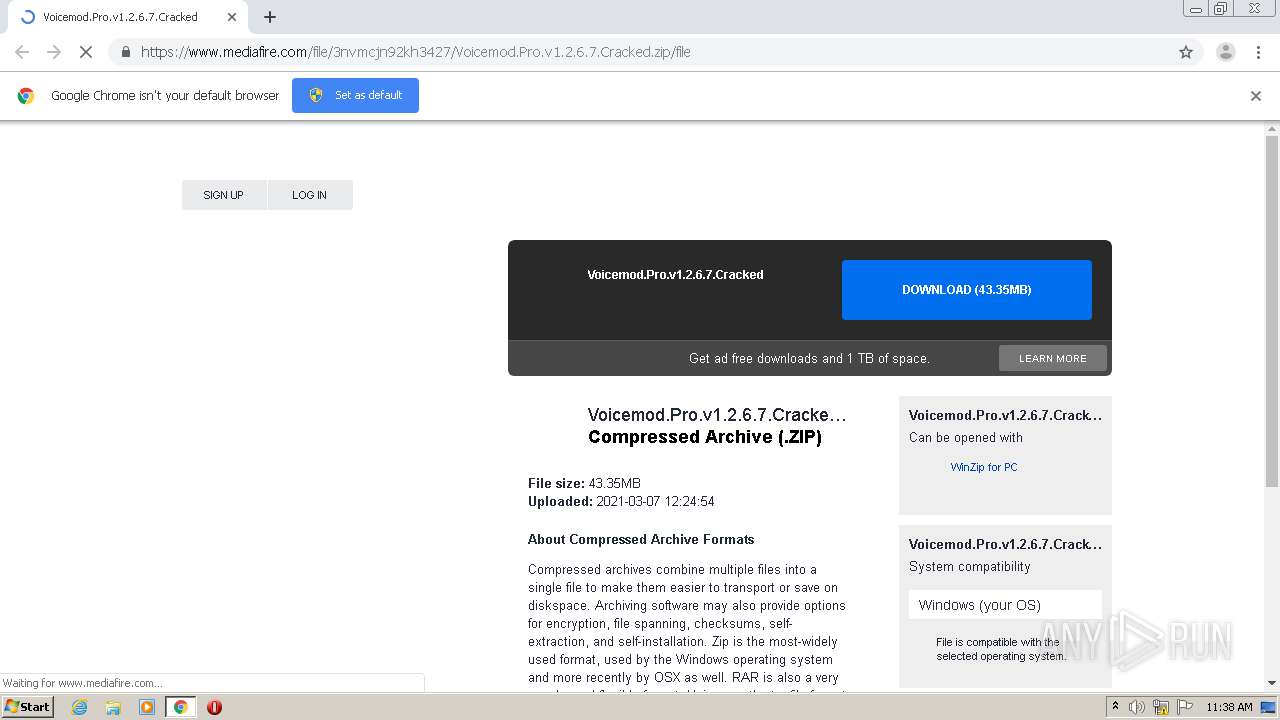
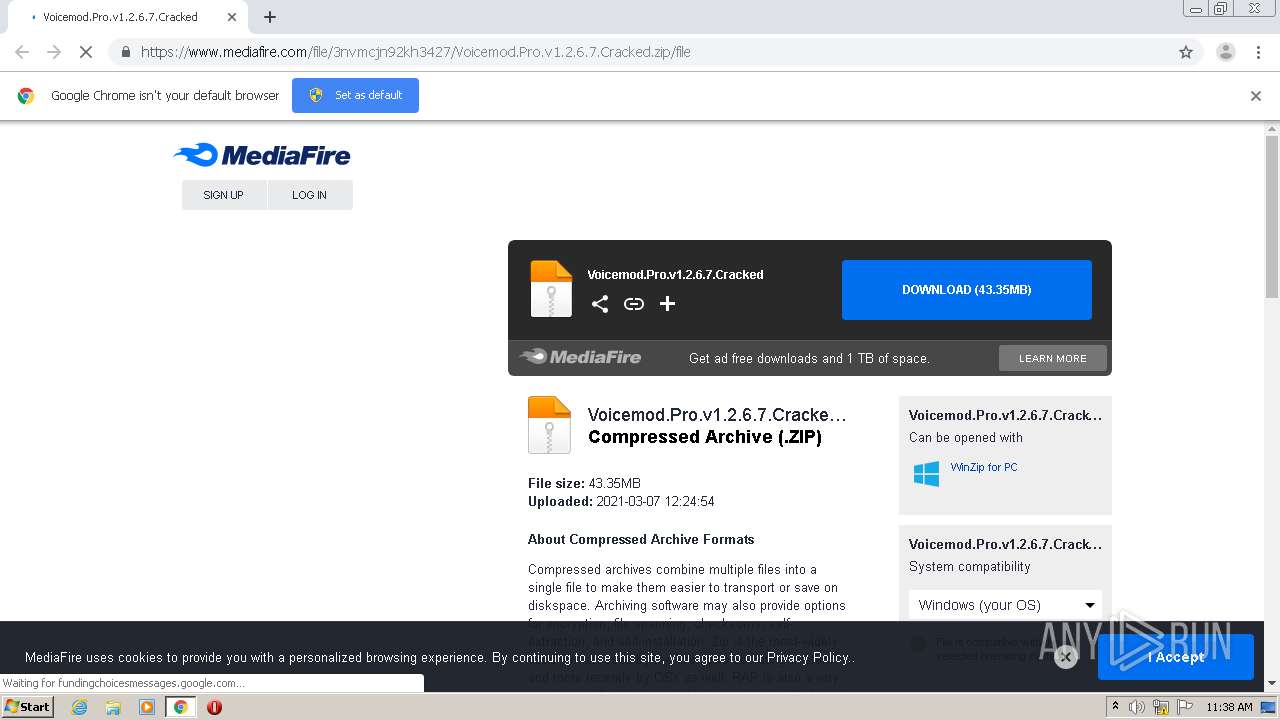
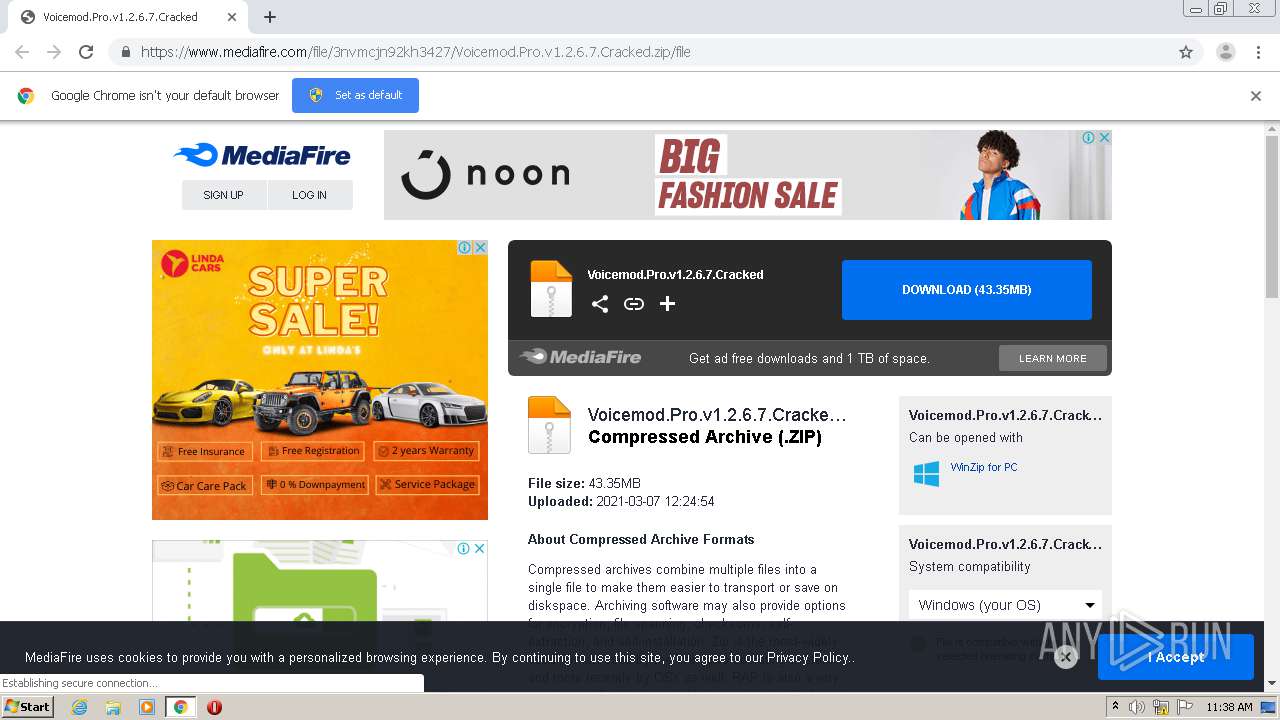
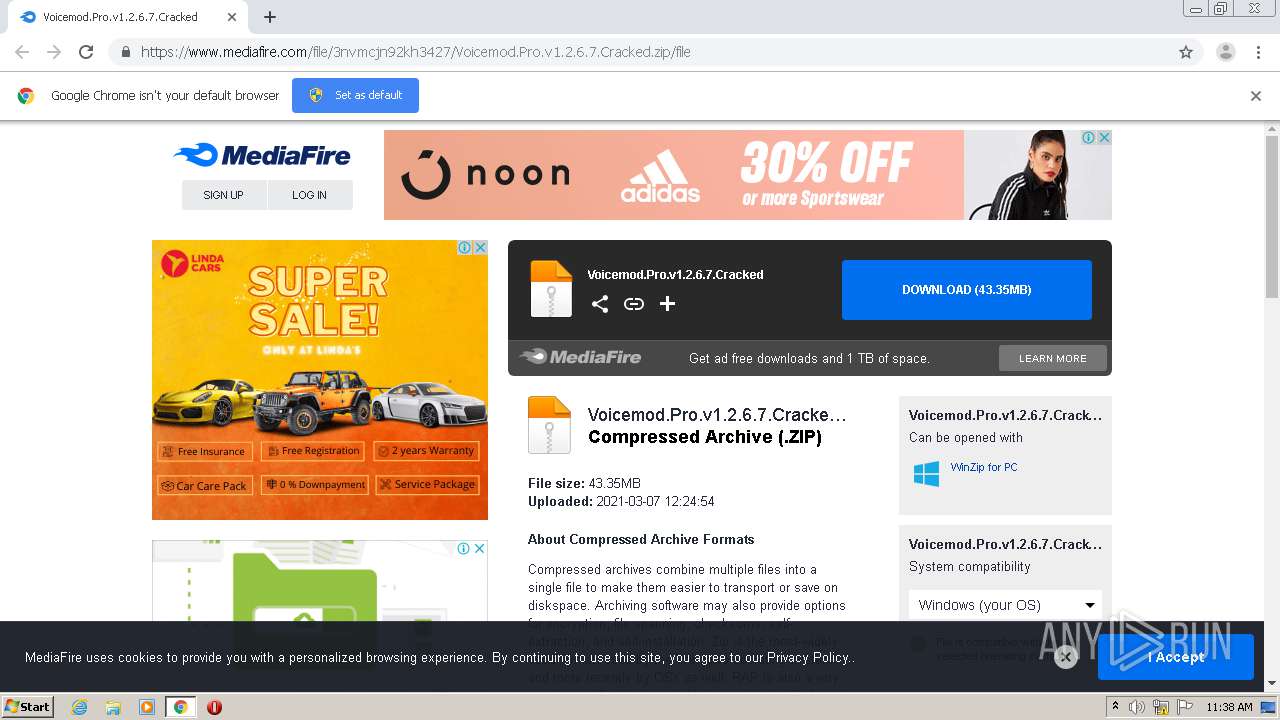
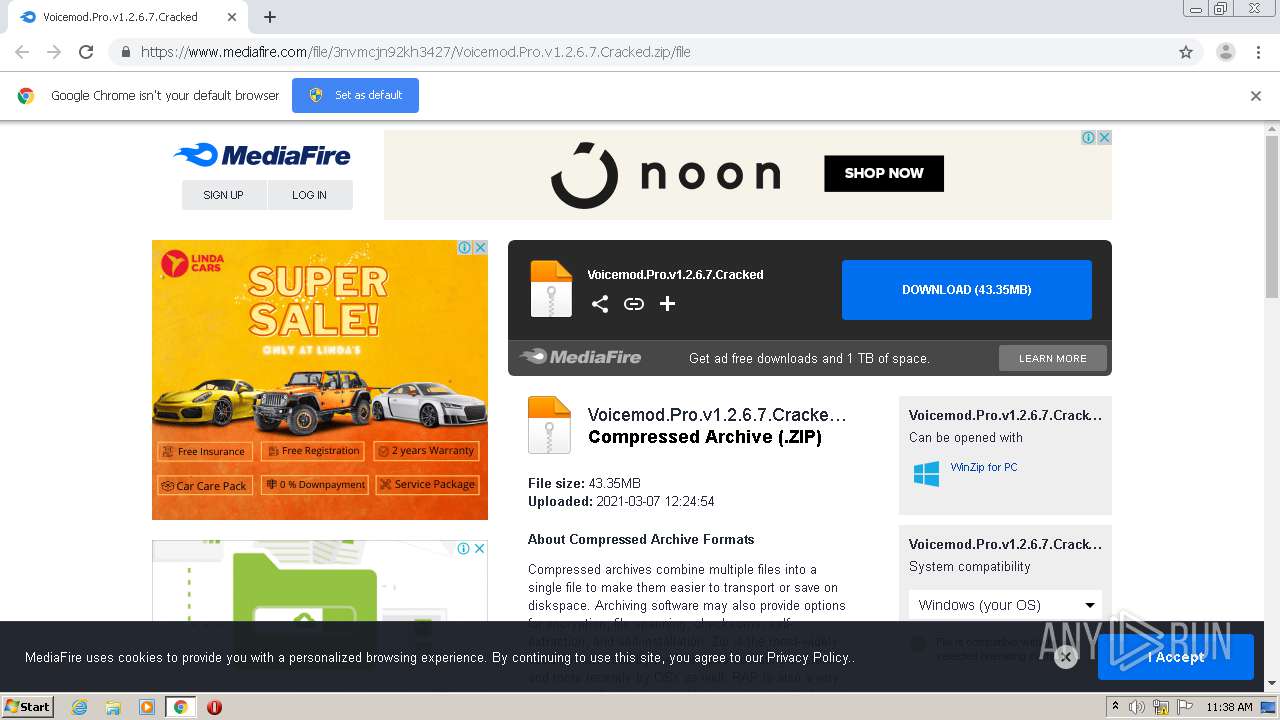
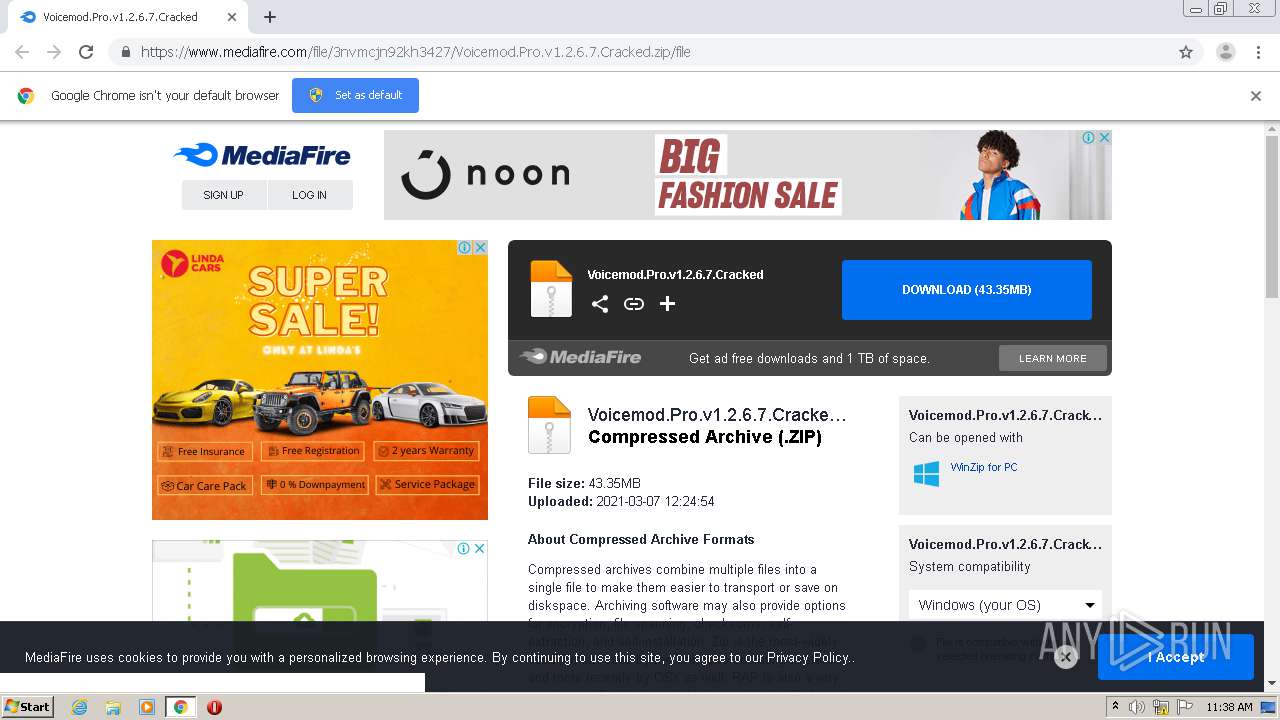
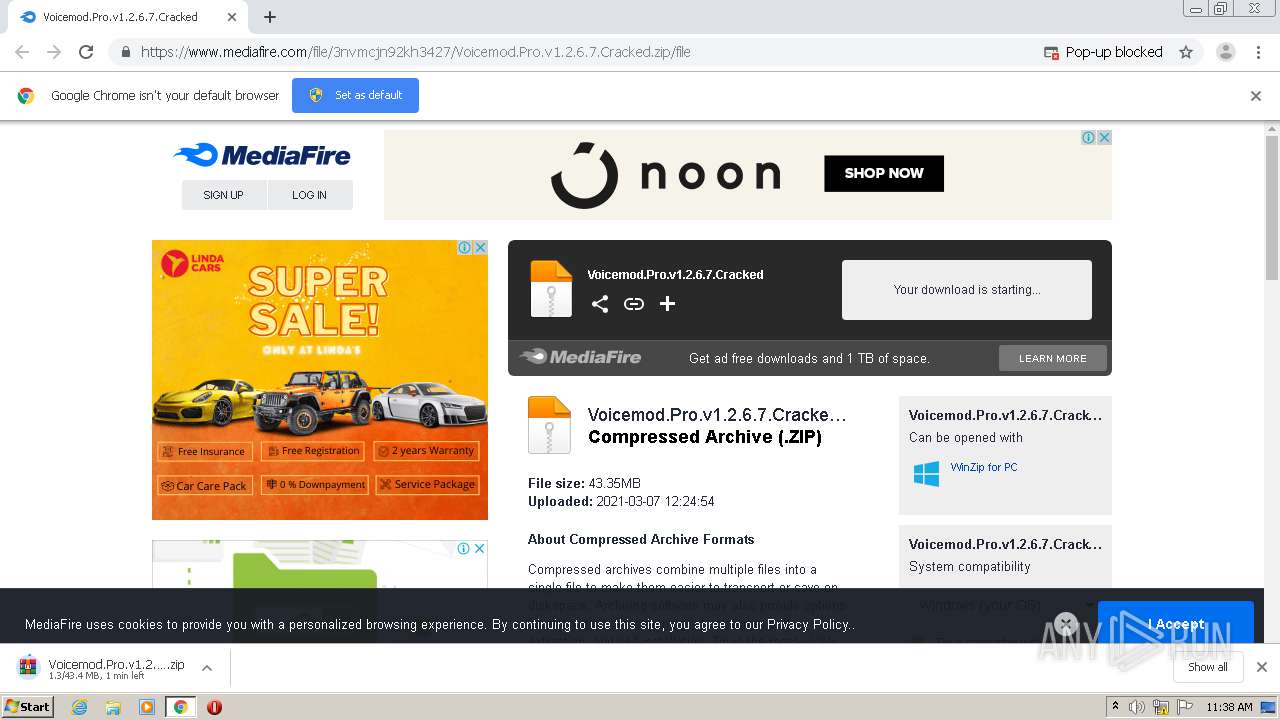
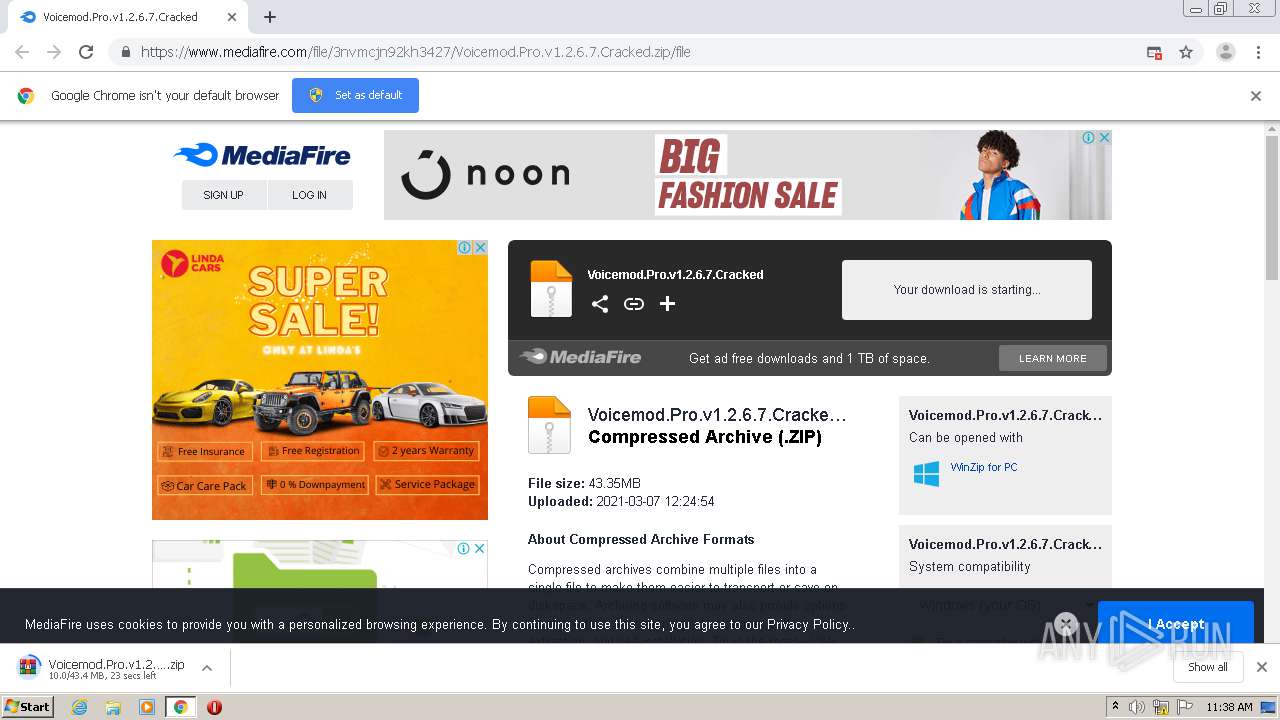
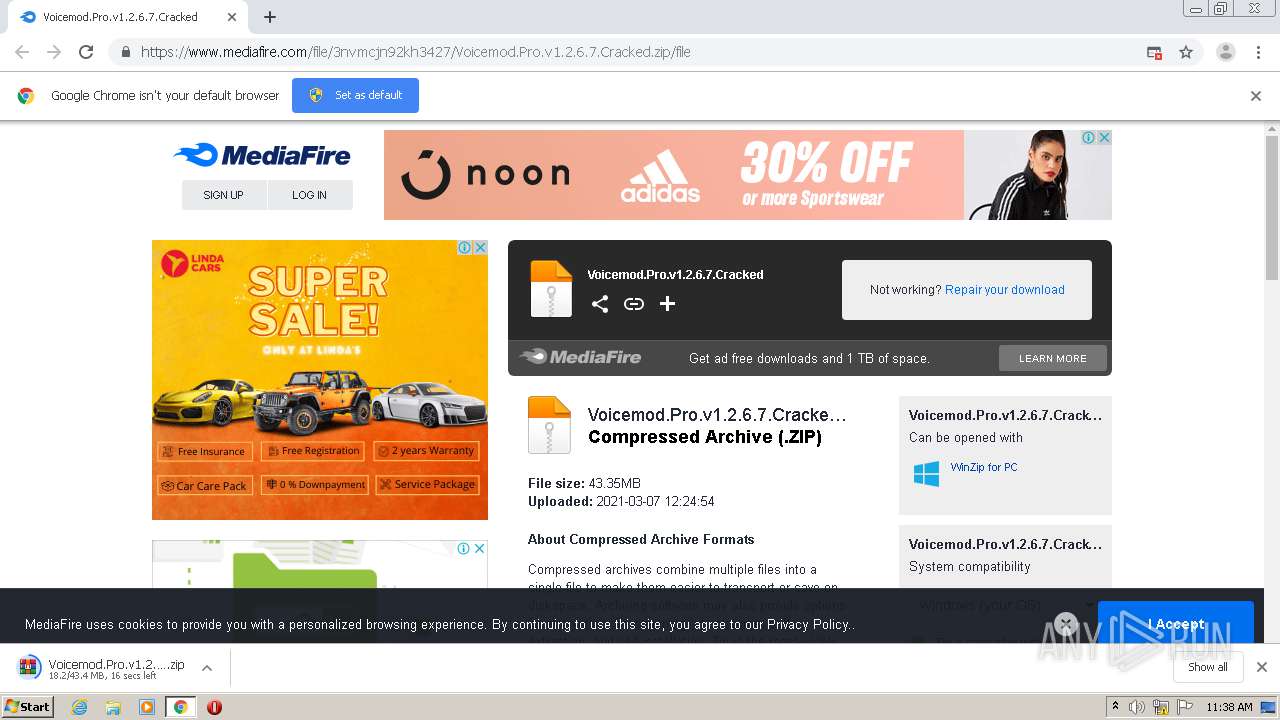
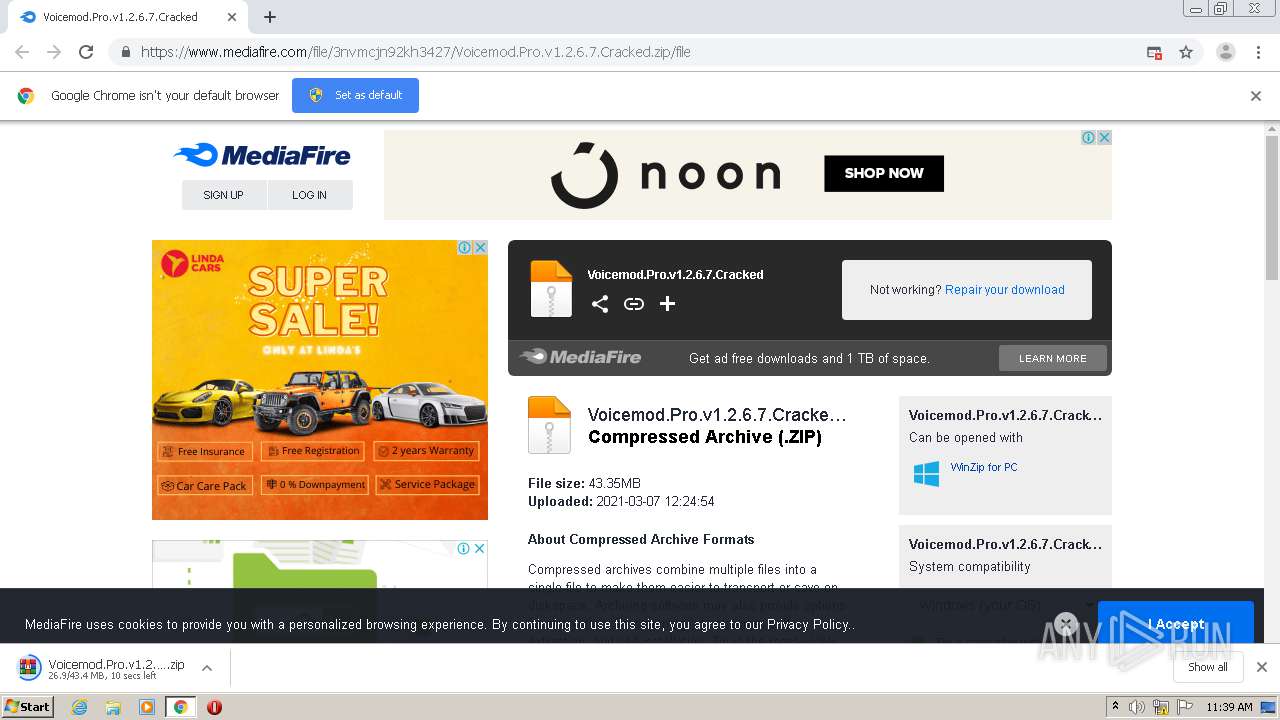
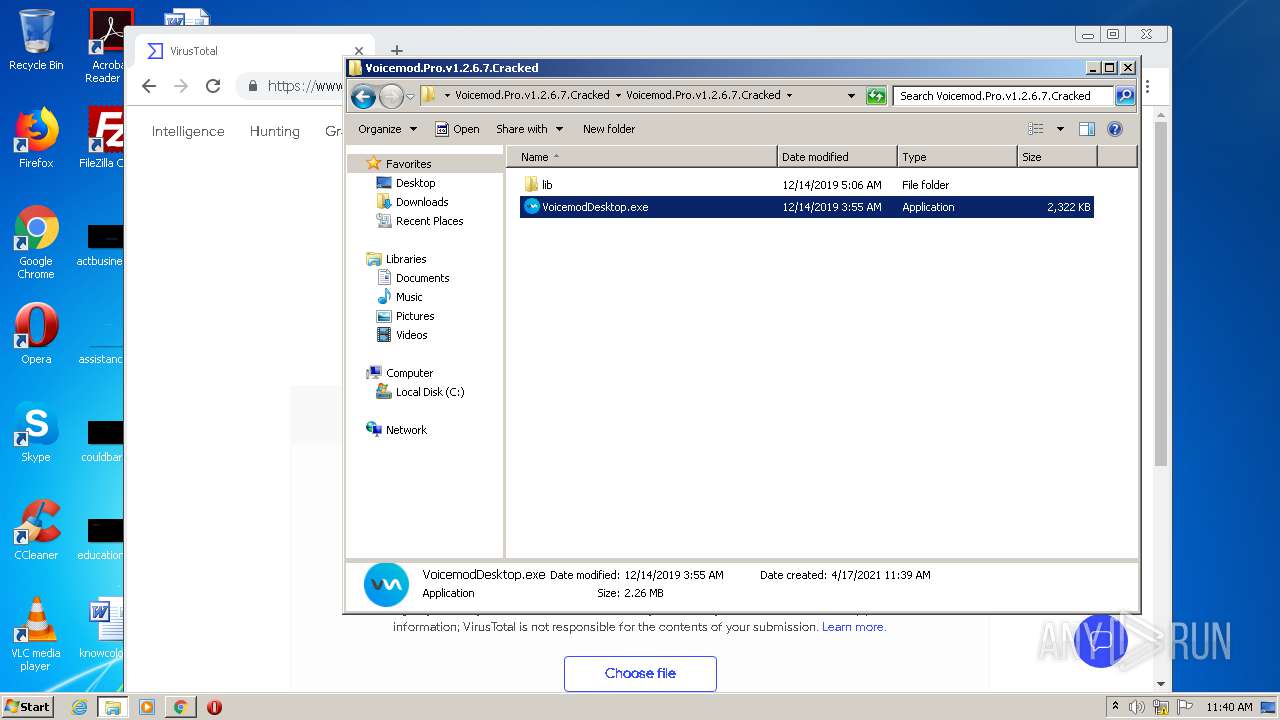
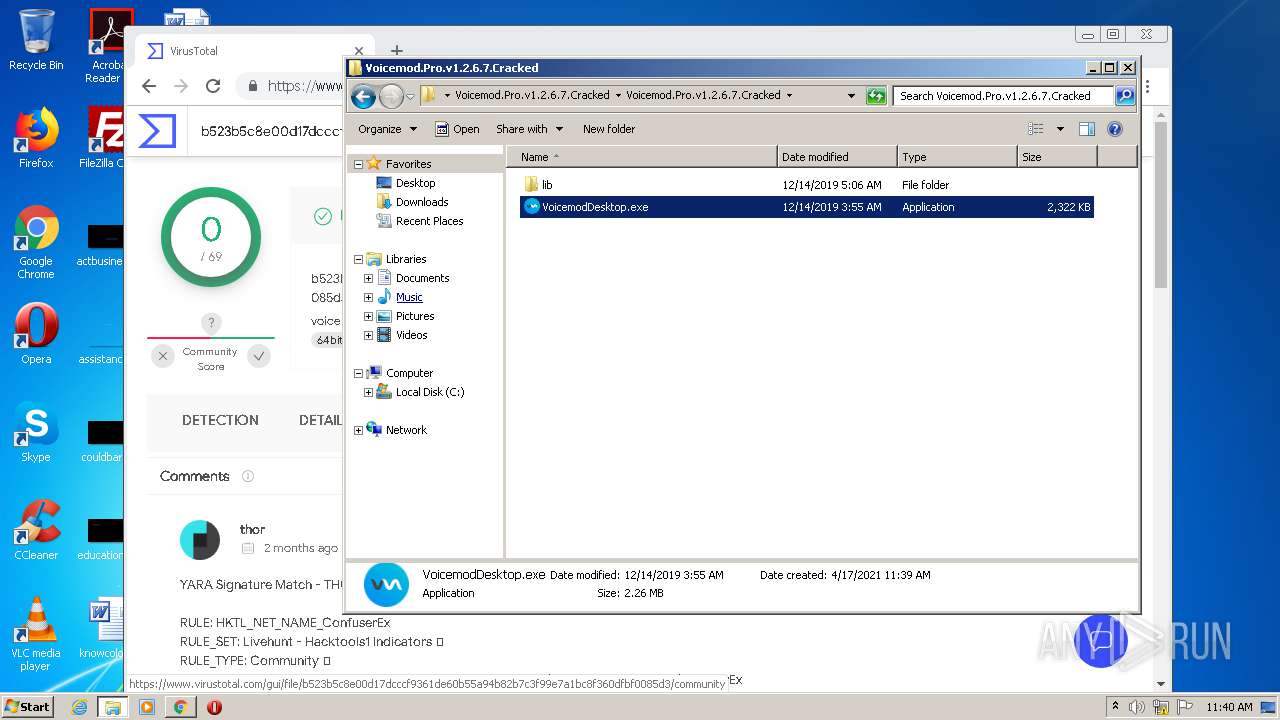
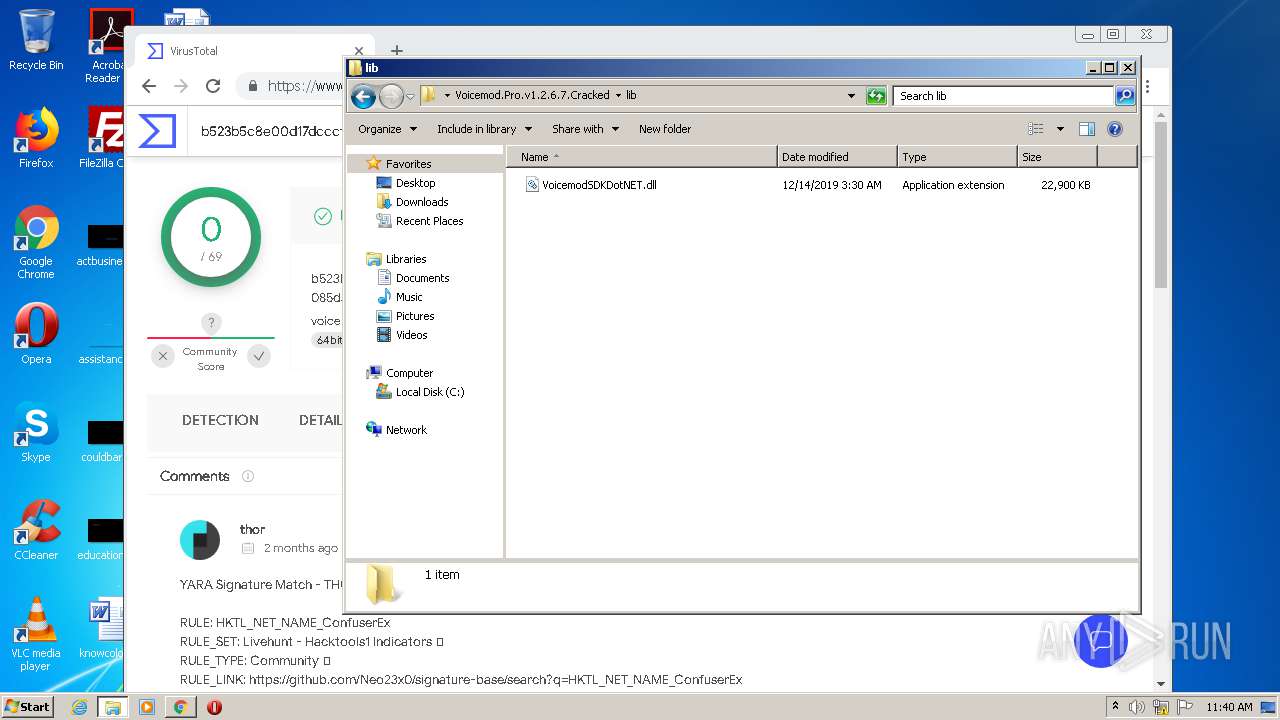
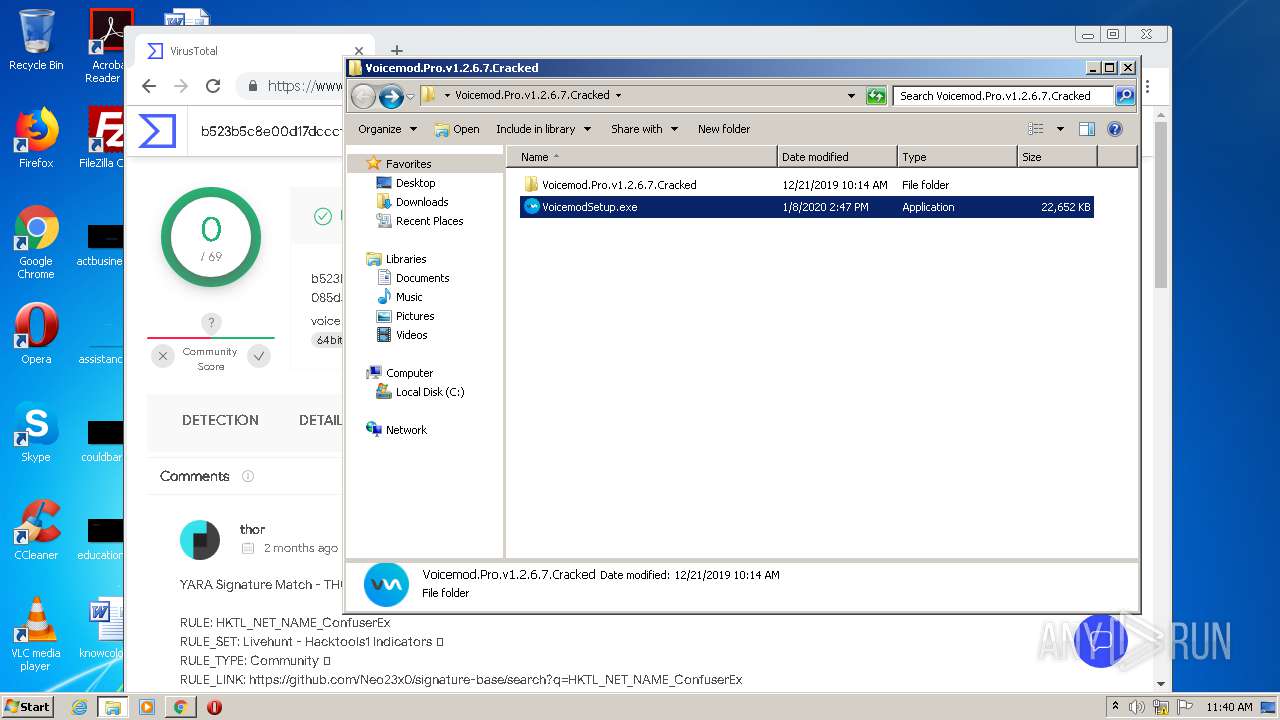
| URL: | https://www.mediafire.com/file/3nvmcjn92kh3427/Voicemod.Pro.v1.2.6.7.Cracked.zip/file |
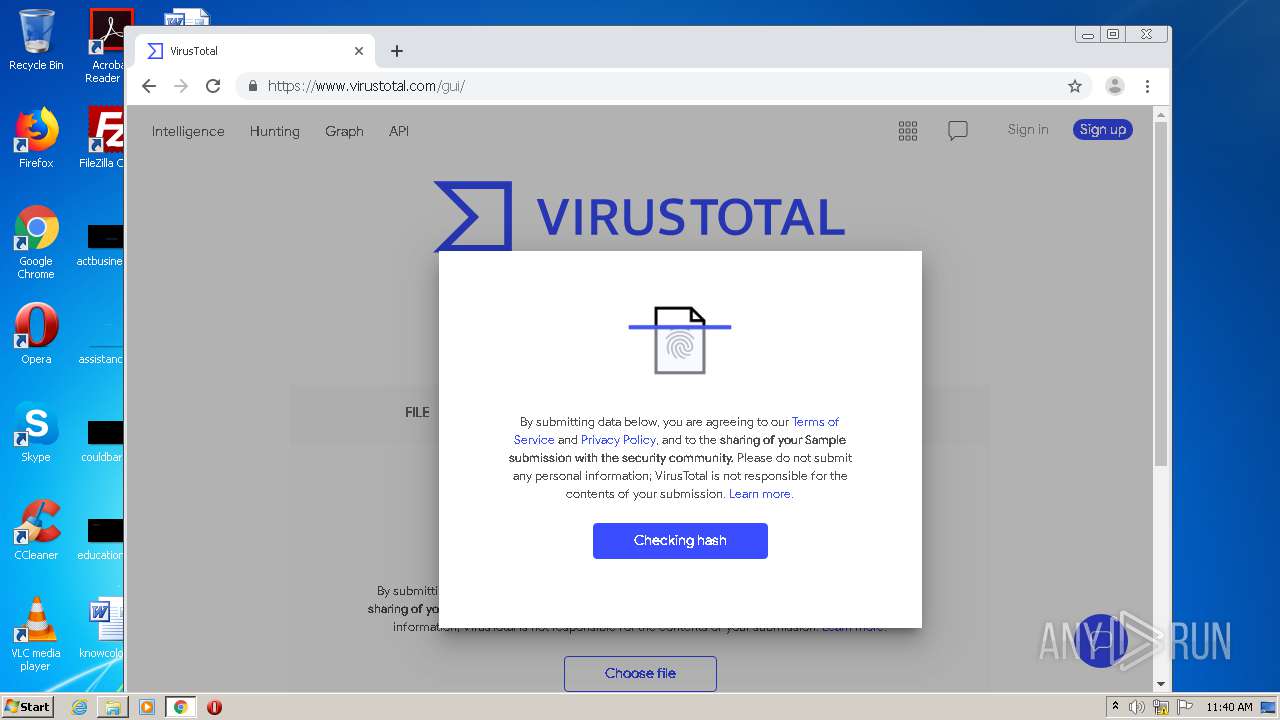
| Full analysis: | https://app.any.run/tasks/ea58cfba-af0d-482a-8e2a-bc456e06bc1b |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2021, 10:38:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
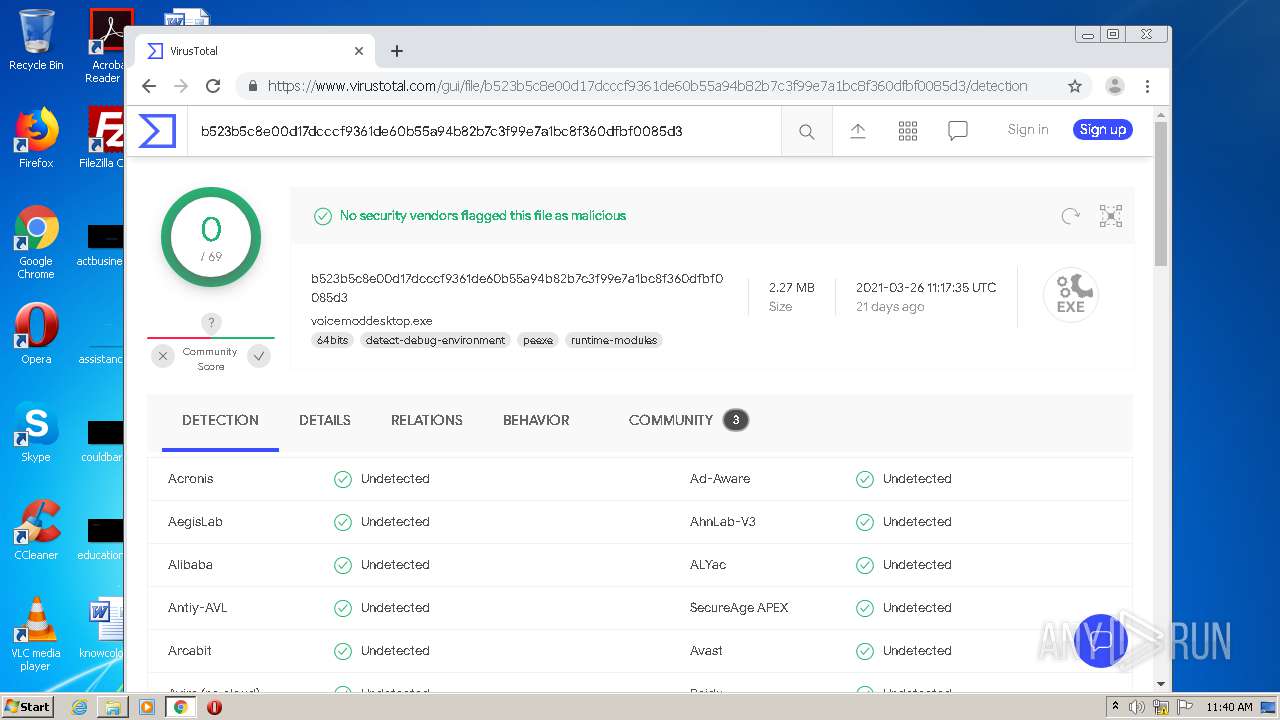
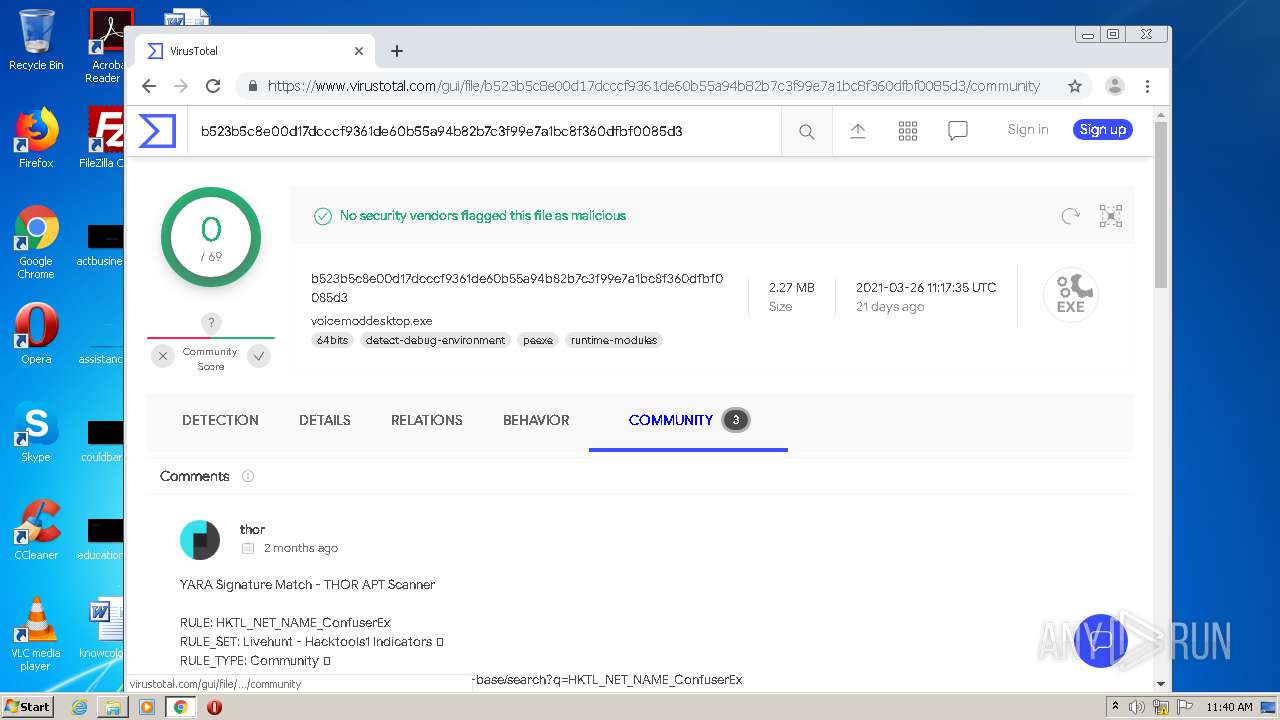
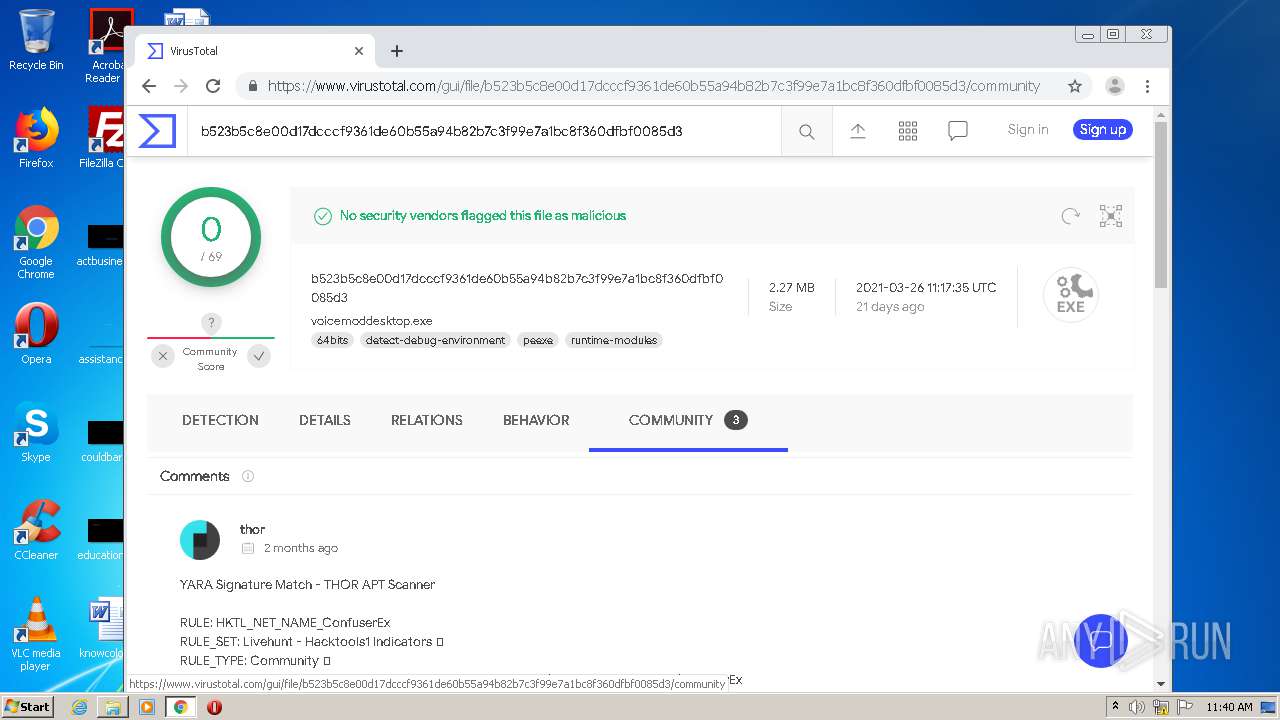
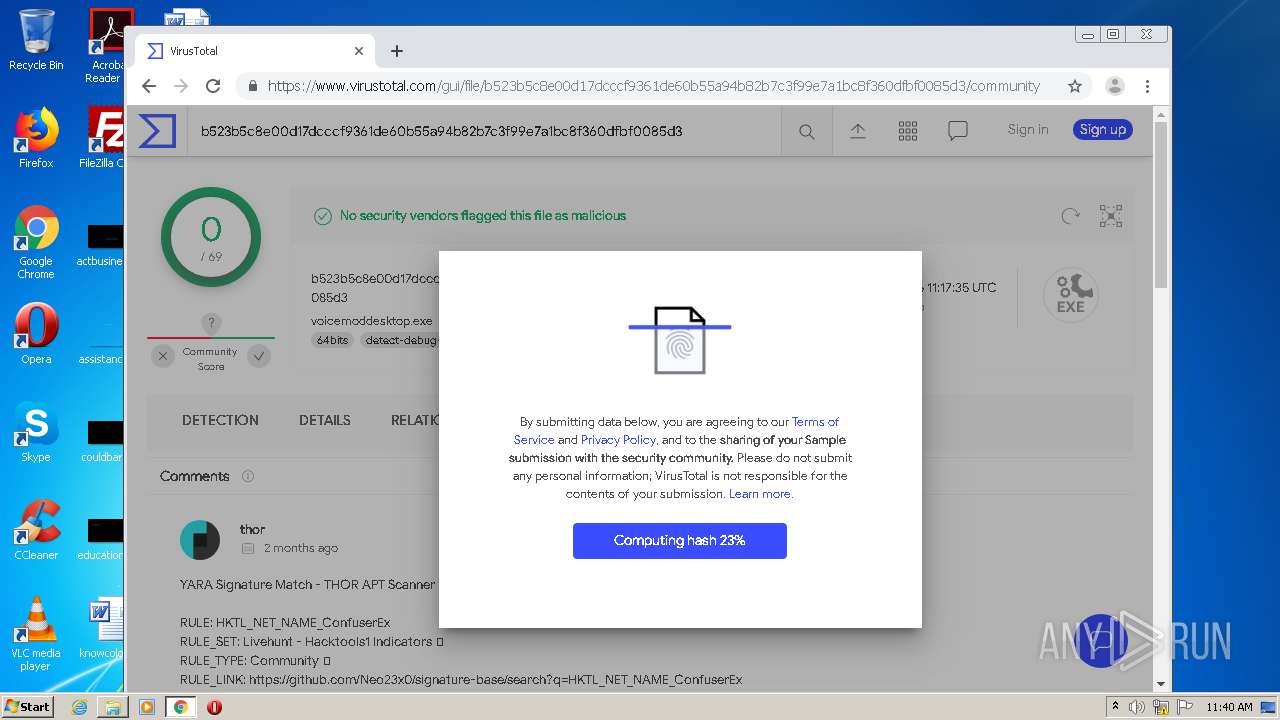
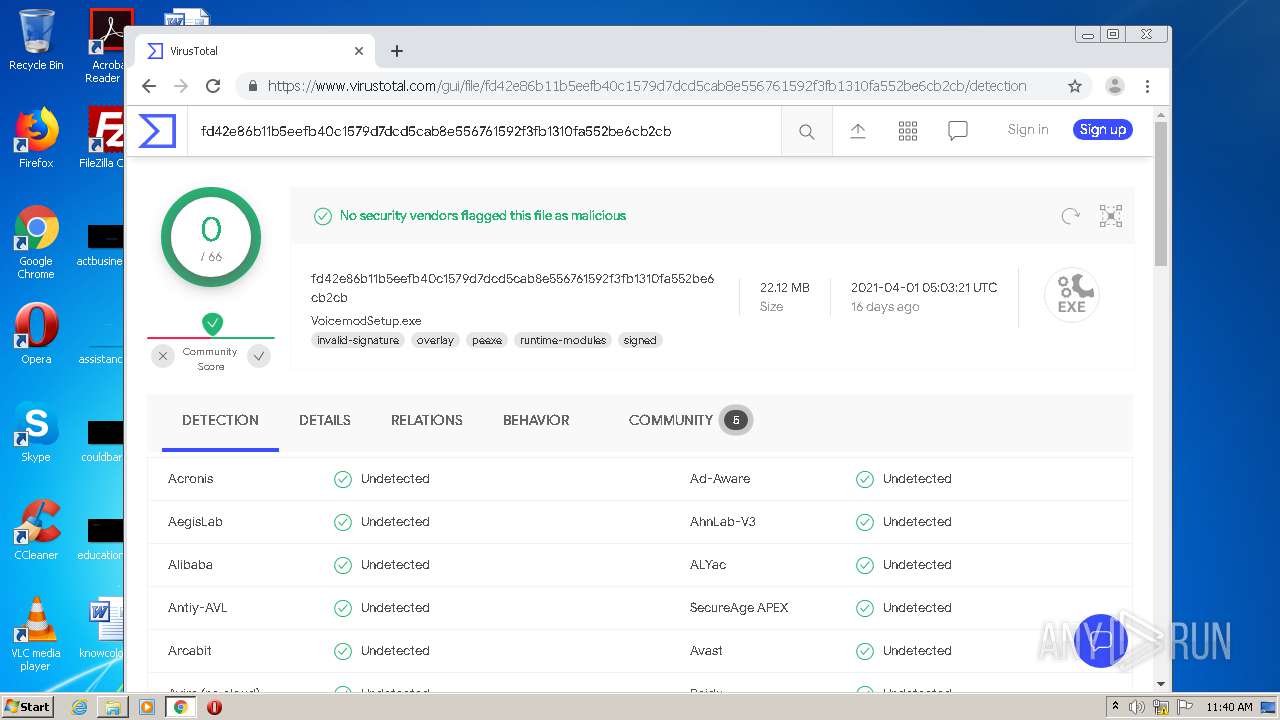
| MD5: | ACD4A41616A1780E82A442B63B4F8941 |
| SHA1: | 4F111752AF6B8AC44DB30C8543F6BA4A0A10839E |
| SHA256: | 304774295AA5F917A7BC925707D34D9CBAF0E32E495347DA13C75EC8565CBA88 |
| SSDEEP: | 3:N8DSLw3eGUoW7wLX5TBBXKUL3mNGOcMVY9:2OLw3eG2O/hXWNm |
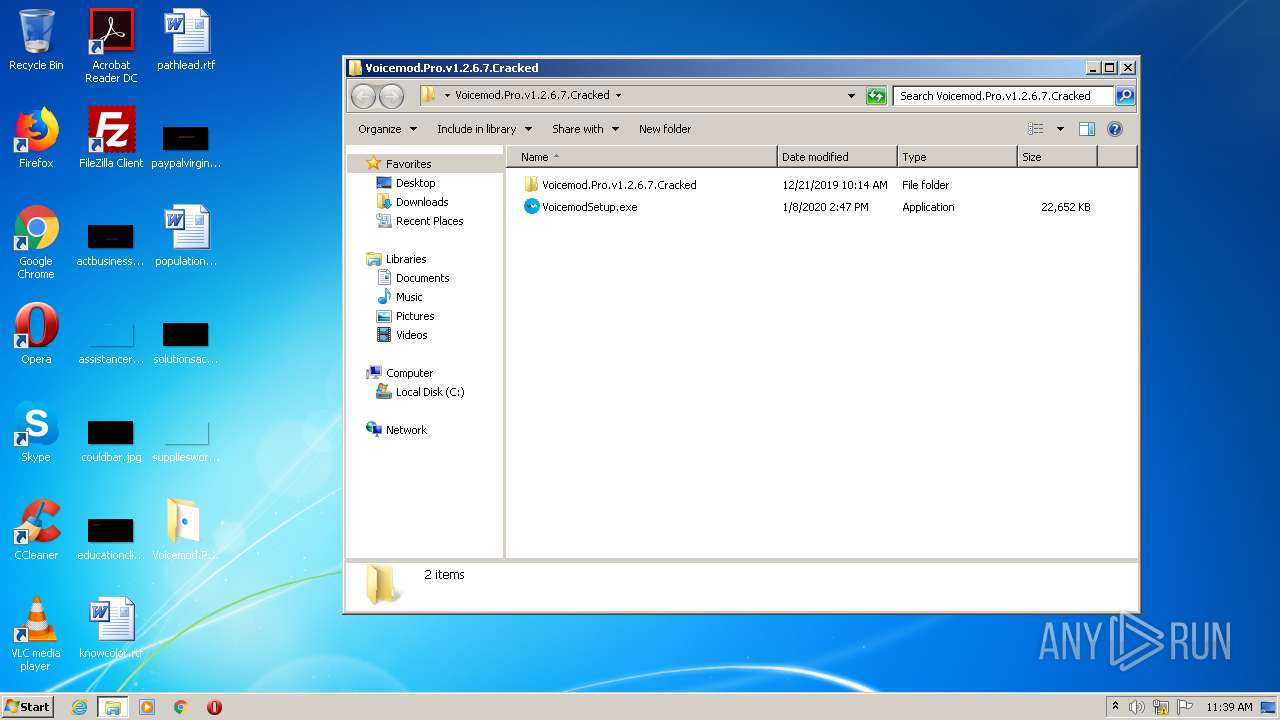
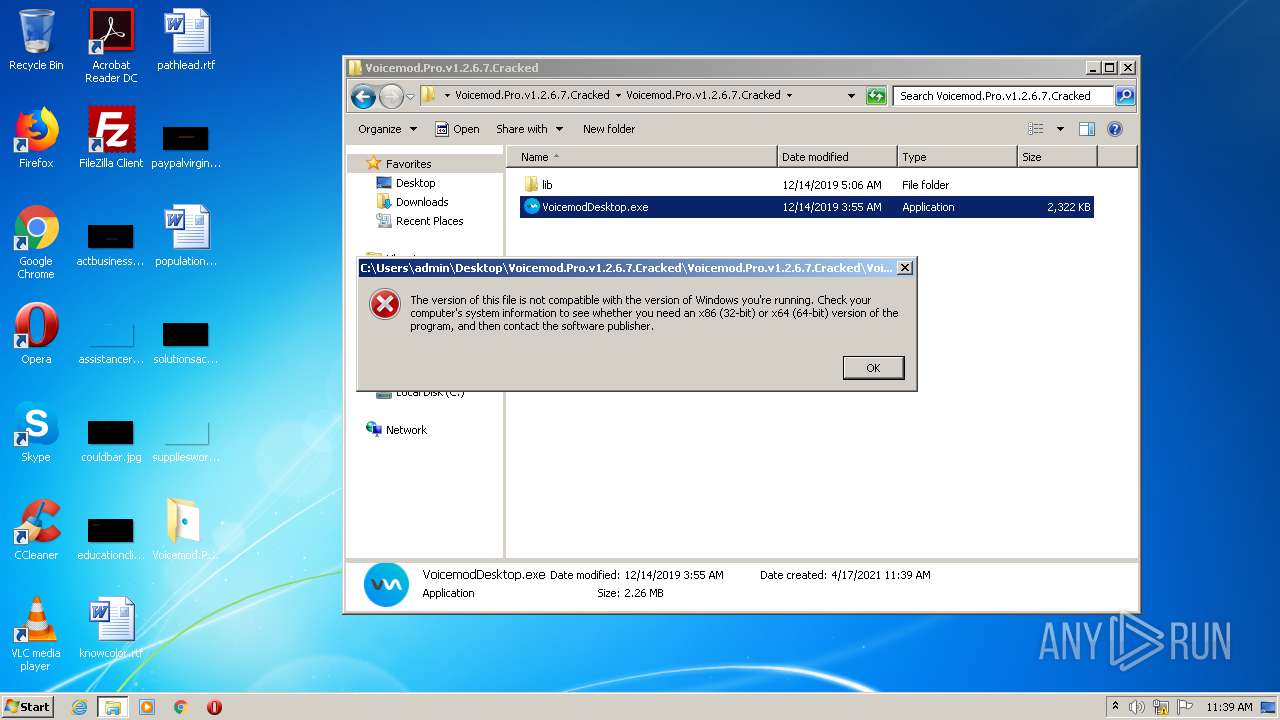
MALICIOUS
Drops executable file immediately after starts
- VoicemodSetup.exe (PID: 2780)
Application was dropped or rewritten from another process
- VoicemodSetup.exe (PID: 2780)
- VoicemodSetup.exe (PID: 1572)
Runs injected code in another process
- chrome.exe (PID: 1248)
Application was injected by another process
- dllhost.exe (PID: 3828)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 916)
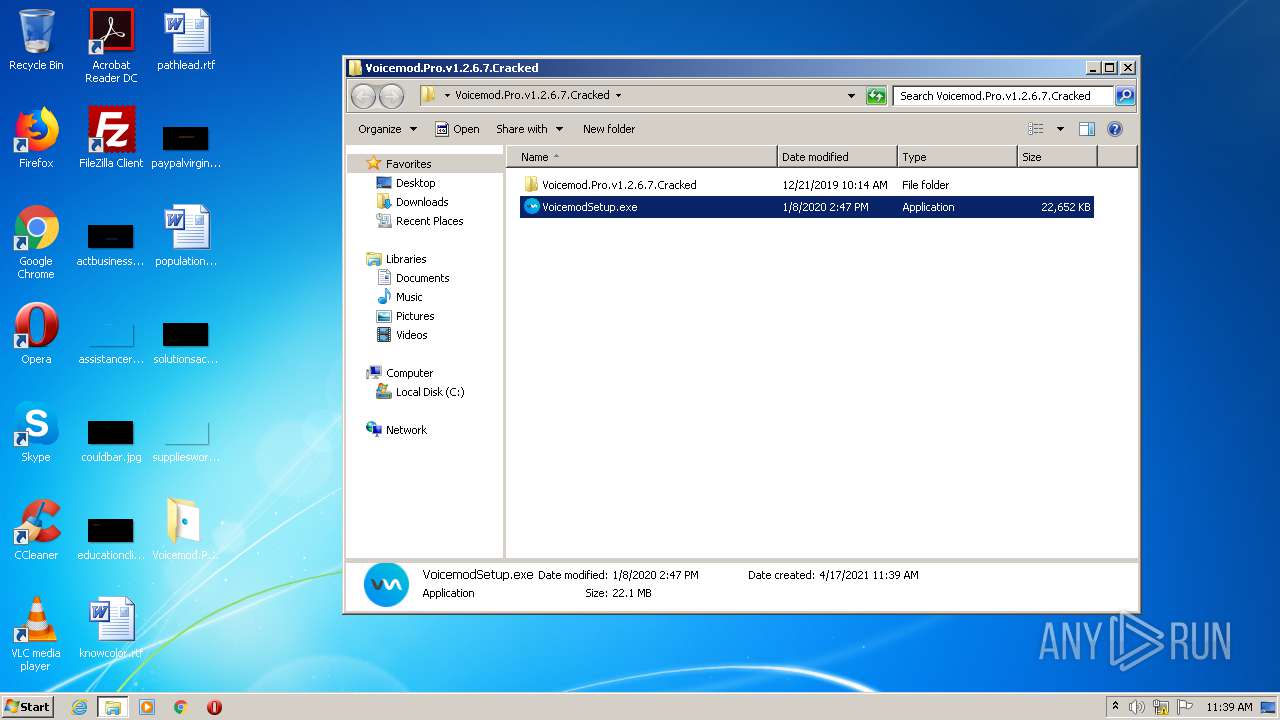
Executable content was dropped or overwritten
- VoicemodSetup.exe (PID: 2780)
- WinRAR.exe (PID: 2184)
- VoicemodSetup.exe (PID: 1572)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3116)
- chrome.exe (PID: 2480)
Reads the hosts file
- chrome.exe (PID: 916)
- chrome.exe (PID: 3116)
- chrome.exe (PID: 1248)
- chrome.exe (PID: 2480)
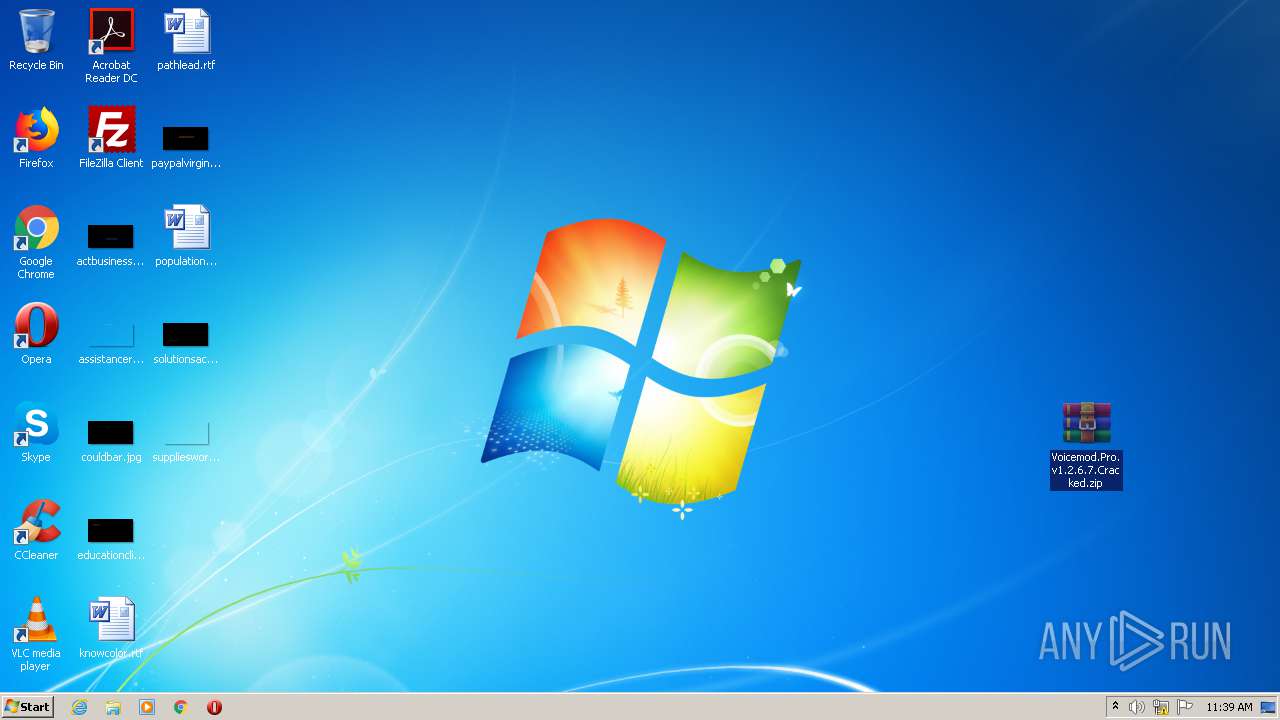
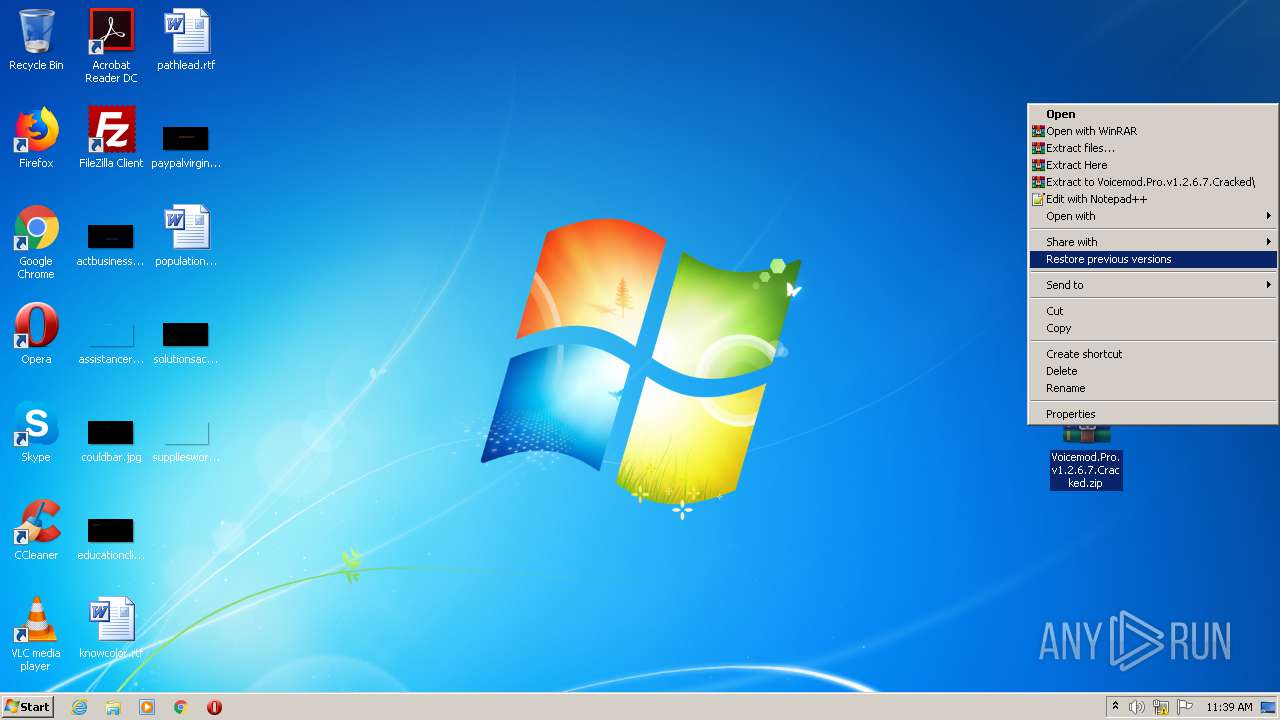
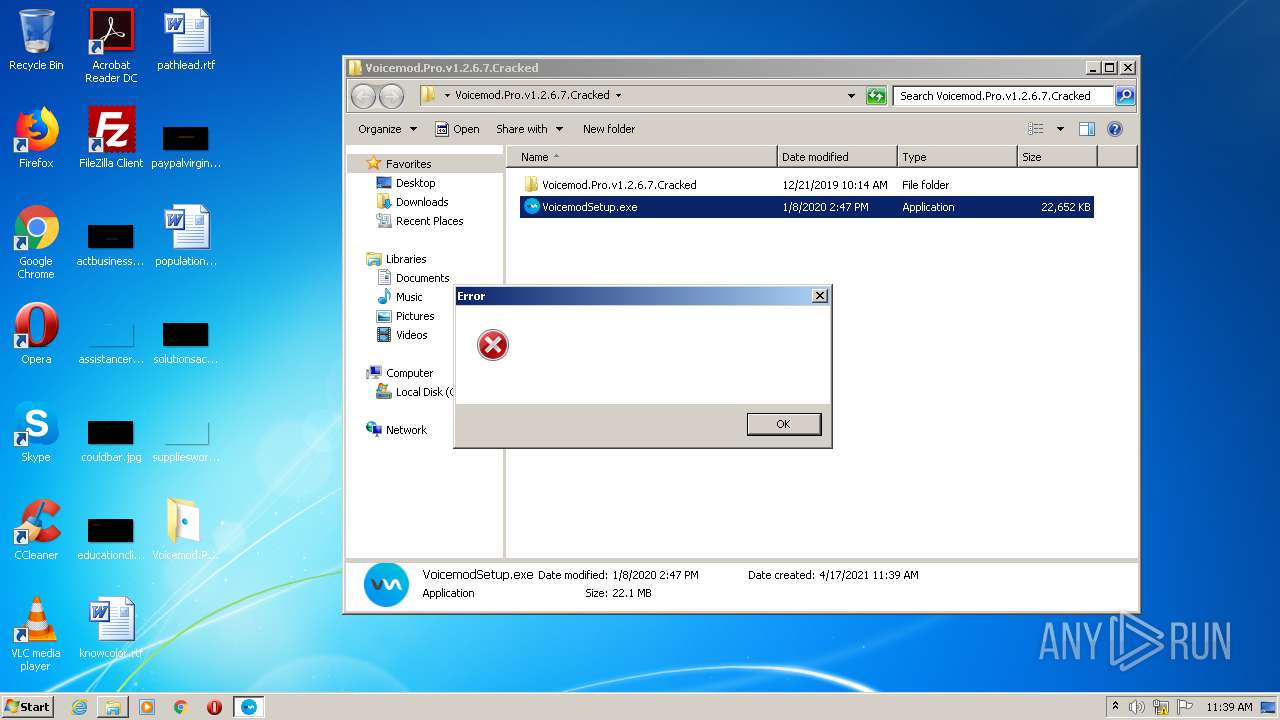
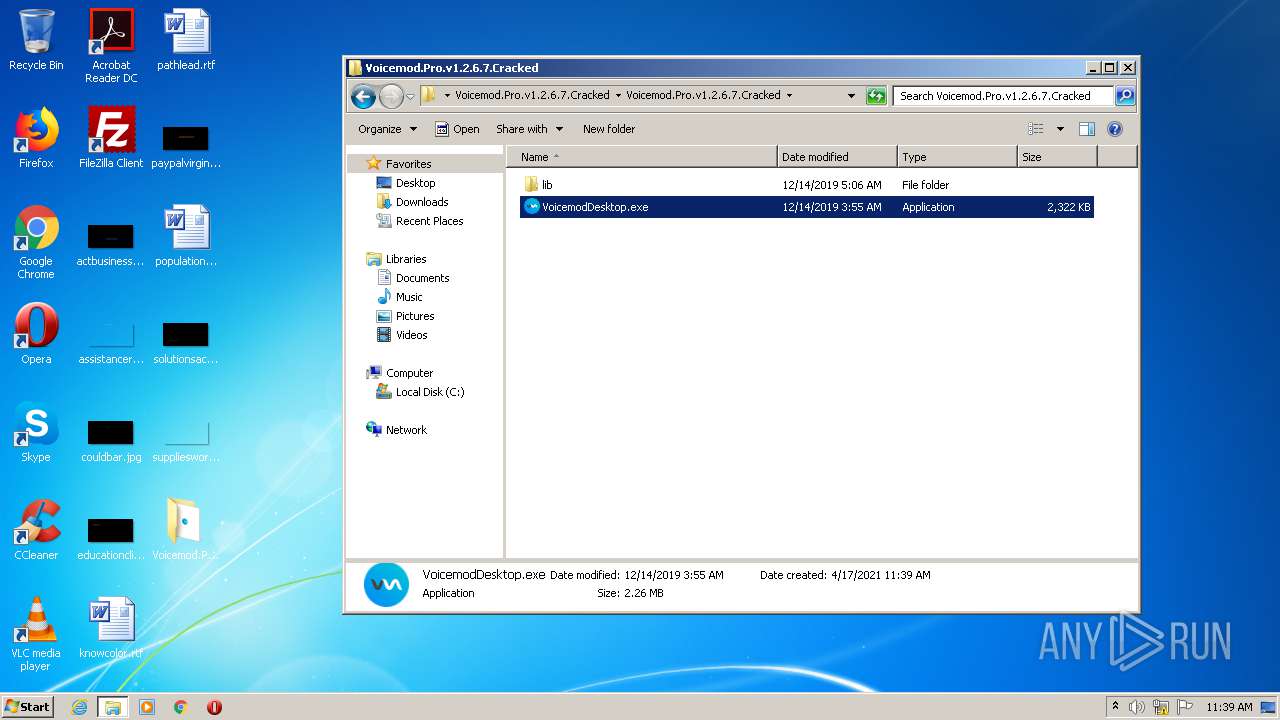
Manual execution by user
- VoicemodSetup.exe (PID: 2780)
- WinRAR.exe (PID: 2184)
- chrome.exe (PID: 1248)
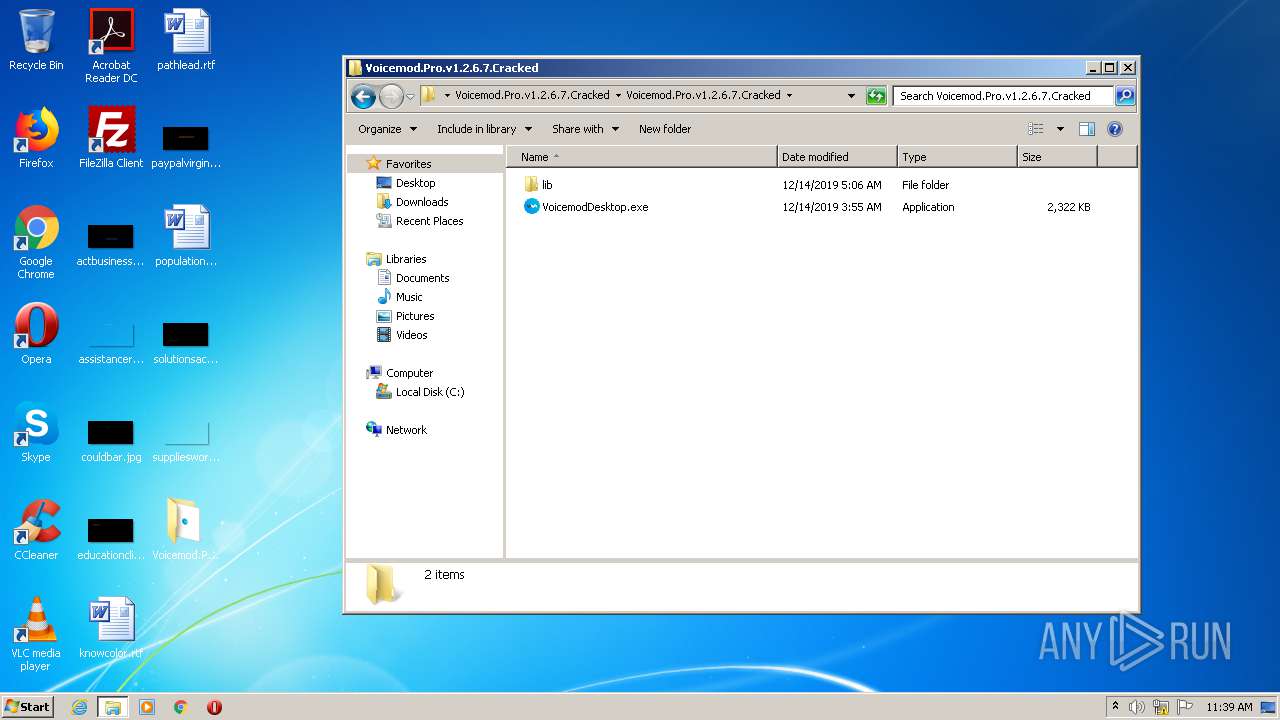
Application was dropped or rewritten from another process
- VoicemodSetup.tmp (PID: 4084)
- VoicemodSetup.tmp (PID: 4072)
Application launched itself
- chrome.exe (PID: 1248)
- chrome.exe (PID: 916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
65
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,472692878980263446,4947057110406906625,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16565060369600865954 --mojo-platform-channel-handle=5120 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,472692878980263446,4947057110406906625,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5220449560657628283 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,472692878980263446,4947057110406906625,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9946604277946102470 --mojo-platform-channel-handle=5828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://www.mediafire.com/file/3nvmcjn92kh3427/Voicemod.Pro.v1.2.6.7.Cracked.zip/file" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,472692878980263446,4947057110406906625,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=718392807638609291 --mojo-platform-channel-handle=5224 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ddba9d0,0x6ddba9e0,0x6ddba9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,472692878980263446,4947057110406906625,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15833202809382704187 --mojo-platform-channel-handle=4932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,4756755795328647778,5233677525565342149,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10009193959344981062 --mojo-platform-channel-handle=1356 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,472692878980263446,4947057110406906625,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14667296519283520257 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5712 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 598
Read events
1 416
Write events
174
Delete events
8
Modification events
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 916-13263129506271125 |
Value: 259 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
5
Suspicious files
123
Text files
356
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-607ABAA2-394.pma | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e6dae956-4915-492e-b9ec-4a44417768c0.tmp | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1debab.TMP | text | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1deb9b.TMP | text | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1dedbe.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
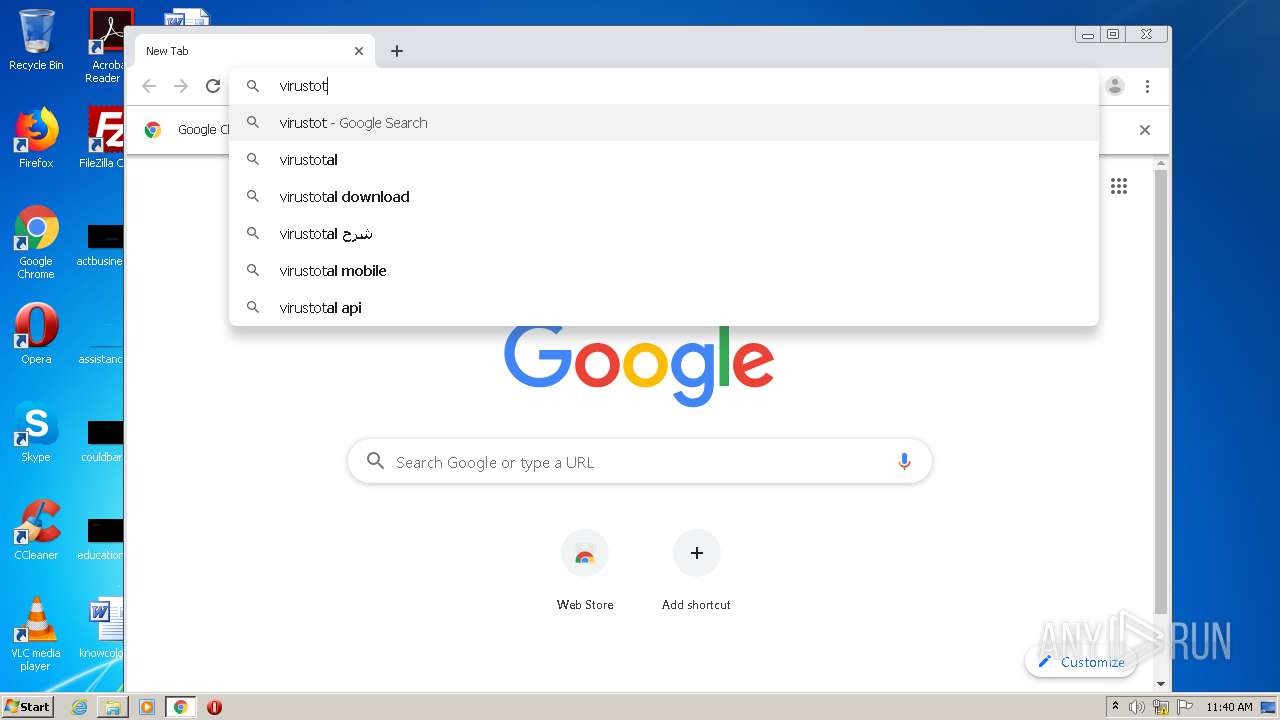
HTTP(S) requests
3
TCP/UDP connections
128
DNS requests
94
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2480 | chrome.exe | GET | 302 | 216.239.36.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
3116 | chrome.exe | GET | 302 | 142.250.186.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
3116 | chrome.exe | GET | 200 | 74.125.173.7:80 | http://r1---sn-f5f7lnel.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=84.17.55.69&mm=28&mn=sn-f5f7lnel&ms=nvh&mt=1618655534&mv=m&mvi=1&pl=25&shardbypass=yes | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3116 | chrome.exe | 142.250.186.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 216.58.214.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 142.250.185.174:443 | fundingchoicesmessages.google.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 172.217.16.98:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
3116 | chrome.exe | 104.117.198.191:443 | c.aaxads.com | TPG Telecom Limited | US | unknown |
3116 | chrome.exe | 142.250.185.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
3116 | chrome.exe | 35.244.159.8:443 | mediafire-d.openx.net | — | US | whitelisted |
3116 | chrome.exe | 185.64.189.112:443 | hbopenbid.pubmatic.com | PubMatic, Inc. | GB | unknown |
3116 | chrome.exe | 104.117.203.54:443 | www.aaxdetect.com | TPG Telecom Limited | US | unknown |
3116 | chrome.exe | 104.17.167.186:443 | c.adsco.re | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.mediafire.com |
| shared |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
securepubads.g.doubleclick.net |
| whitelisted |
c.aaxads.com |
| whitelisted |
static.mediafire.com |
| shared |