| URL: | https://149.154.175.59/api |
| Full analysis: | https://app.any.run/tasks/da16148d-6b00-4d5d-9019-c8b164befdd7 |
| Verdict: | Malicious activity |
| Analysis date: | October 02, 2020, 18:33:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A19673C6DCFE4A5417D3D2FF1F7DAB49 |
| SHA1: | A4502105BB2A32C1D1C787C0EE39FDCE1D97F76F |
| SHA256: | 303791D0AAE4F2FD83F51A7CB570557841976177C11E728D6FD202ED52384959 |
| SSDEEP: | 3:N866QLM:266Qw |
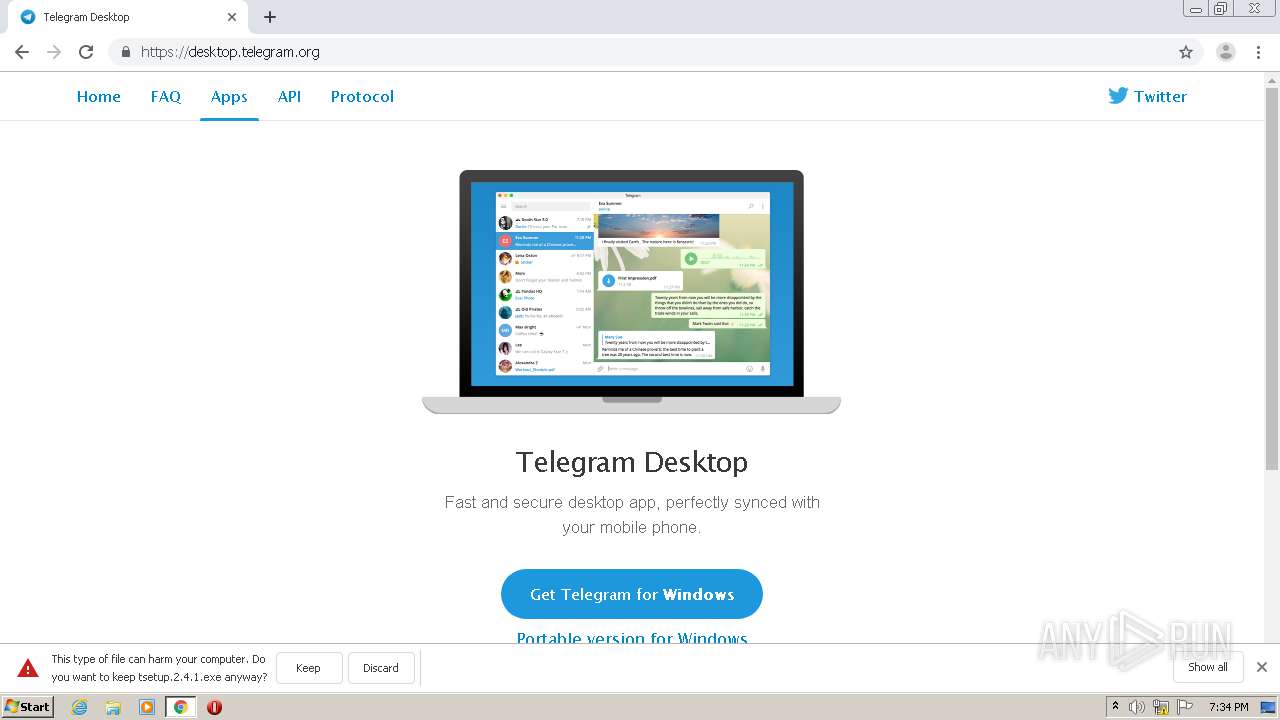
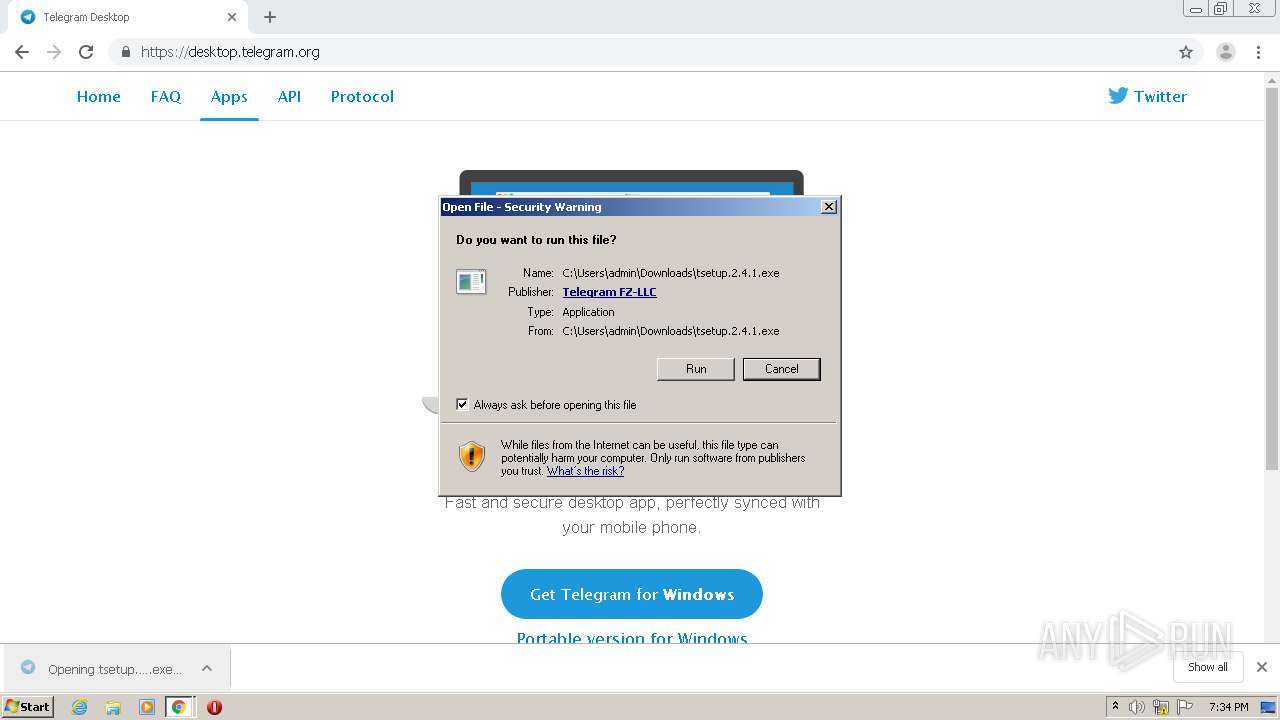
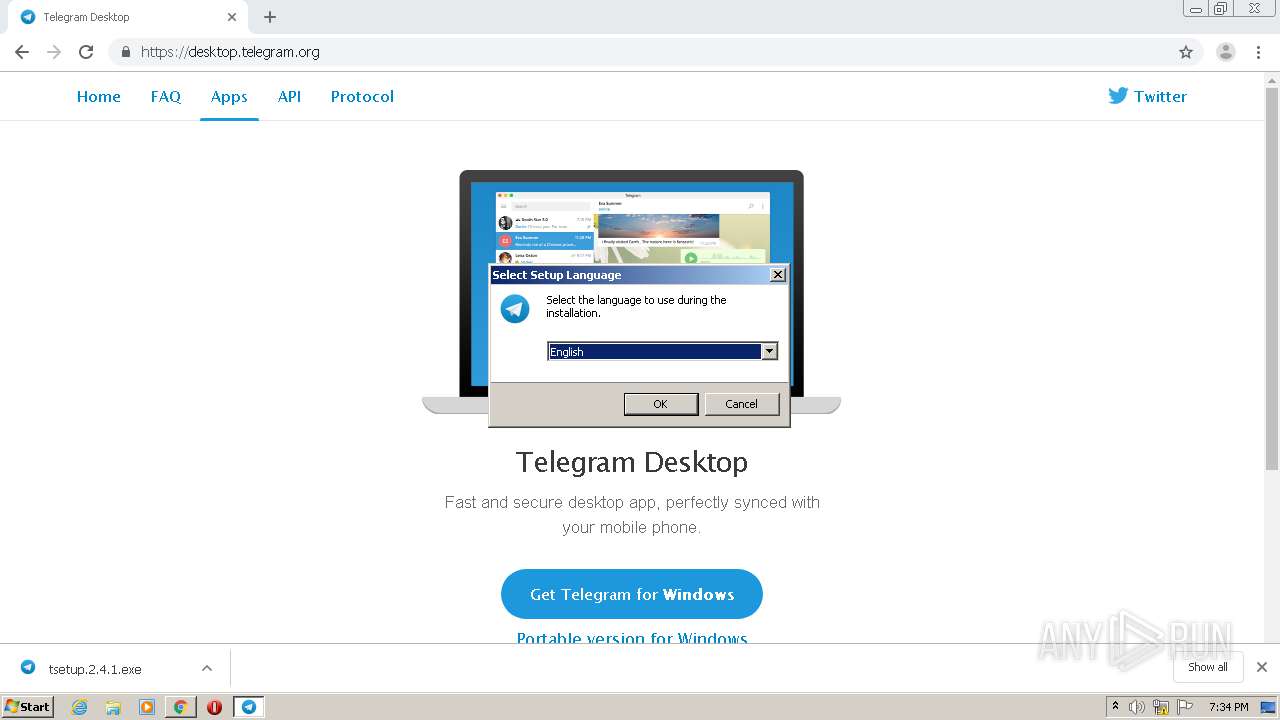
MALICIOUS
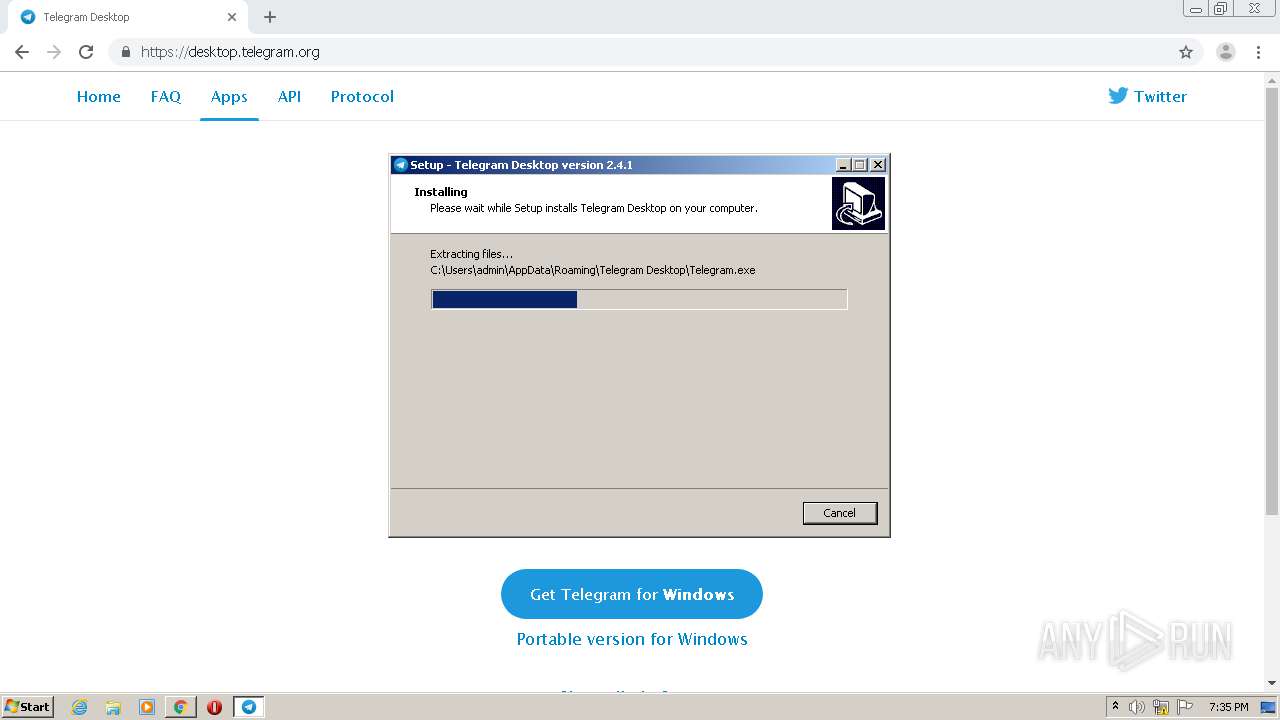
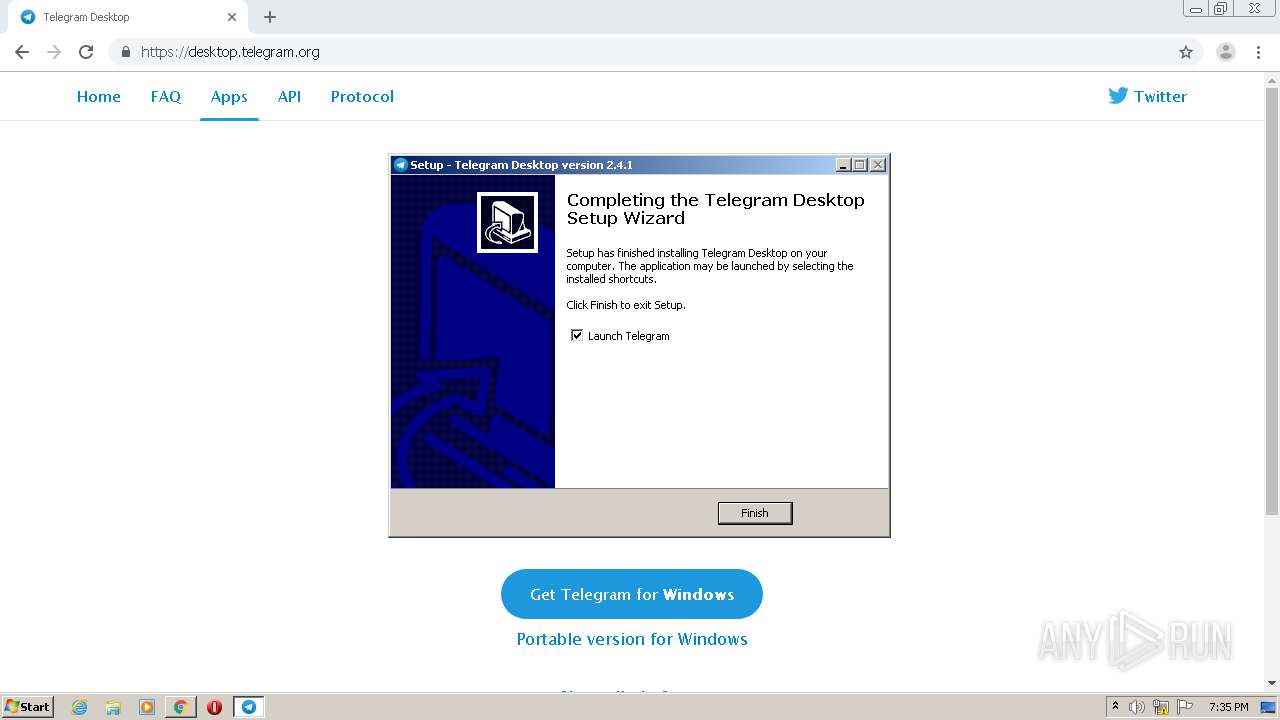
Application was dropped or rewritten from another process
- tsetup.2.4.1.exe (PID: 1812)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2232)
- tsetup.2.4.1.tmp (PID: 4044)
- chrome.exe (PID: 2632)
- tsetup.2.4.1.exe (PID: 1812)
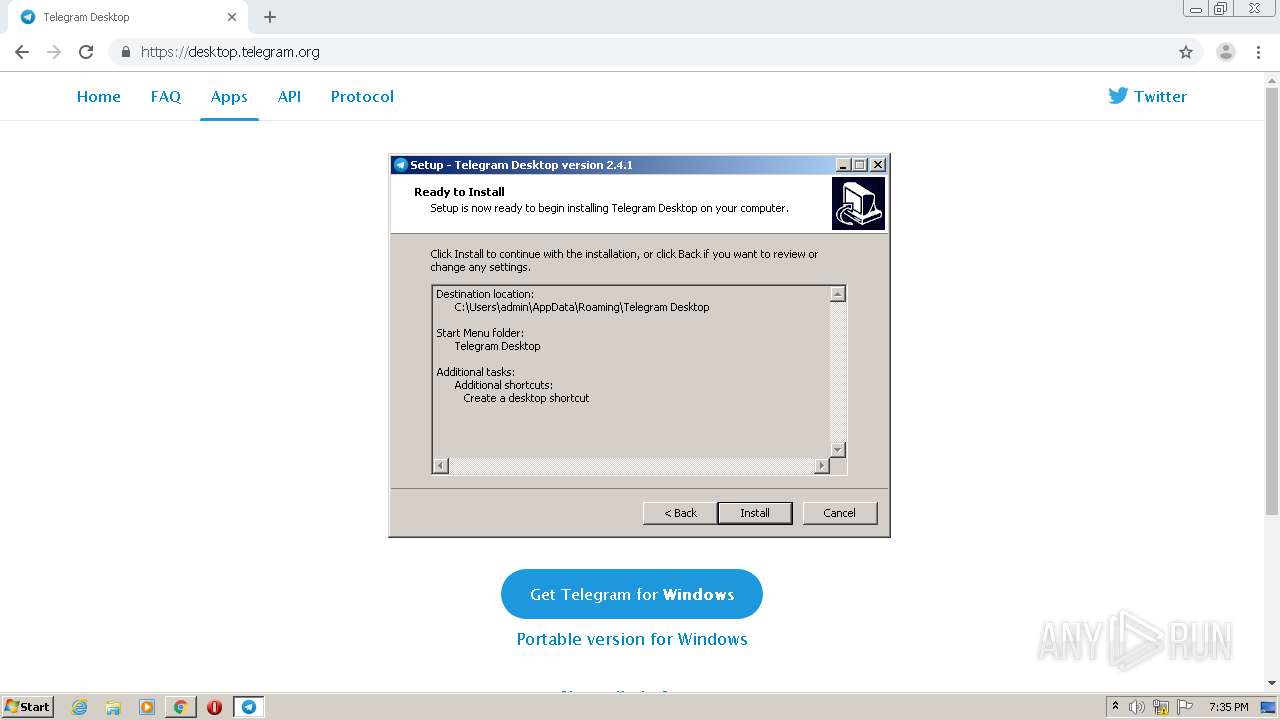
Creates files in the user directory
- Telegram.exe (PID: 2872)
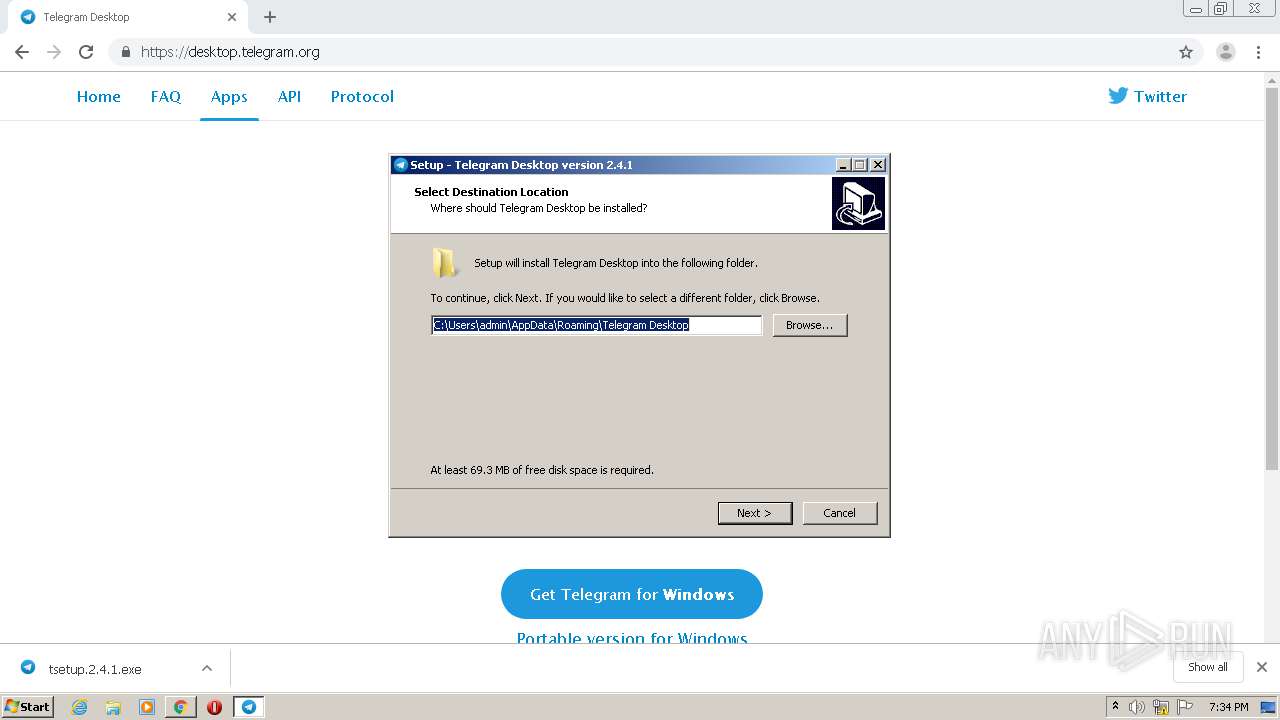
- tsetup.2.4.1.tmp (PID: 4044)
Modifies the open verb of a shell class
- Telegram.exe (PID: 2872)
Reads Windows owner or organization settings
- tsetup.2.4.1.tmp (PID: 4044)
Reads the Windows organization settings
- tsetup.2.4.1.tmp (PID: 4044)
INFO
Reads the hosts file
- chrome.exe (PID: 2632)
- chrome.exe (PID: 2232)
Application launched itself
- chrome.exe (PID: 2232)
Dropped object may contain Bitcoin addresses
- Telegram.exe (PID: 2872)
Creates a software uninstall entry
- tsetup.2.4.1.tmp (PID: 4044)
Application was dropped or rewritten from another process
- tsetup.2.4.1.tmp (PID: 4044)
Reads Internet Cache Settings
- chrome.exe (PID: 2232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
24
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,1184488586429825153,5549271513412027231,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11121006004659269304 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,1184488586429825153,5549271513412027231,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8915896059323654500 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,1184488586429825153,5549271513412027231,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5326326549576353524 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3420 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3088 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,1184488586429825153,5549271513412027231,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13794206080855736436 --mojo-platform-channel-handle=900 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,1184488586429825153,5549271513412027231,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=10432386167482306455 --mojo-platform-channel-handle=3744 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
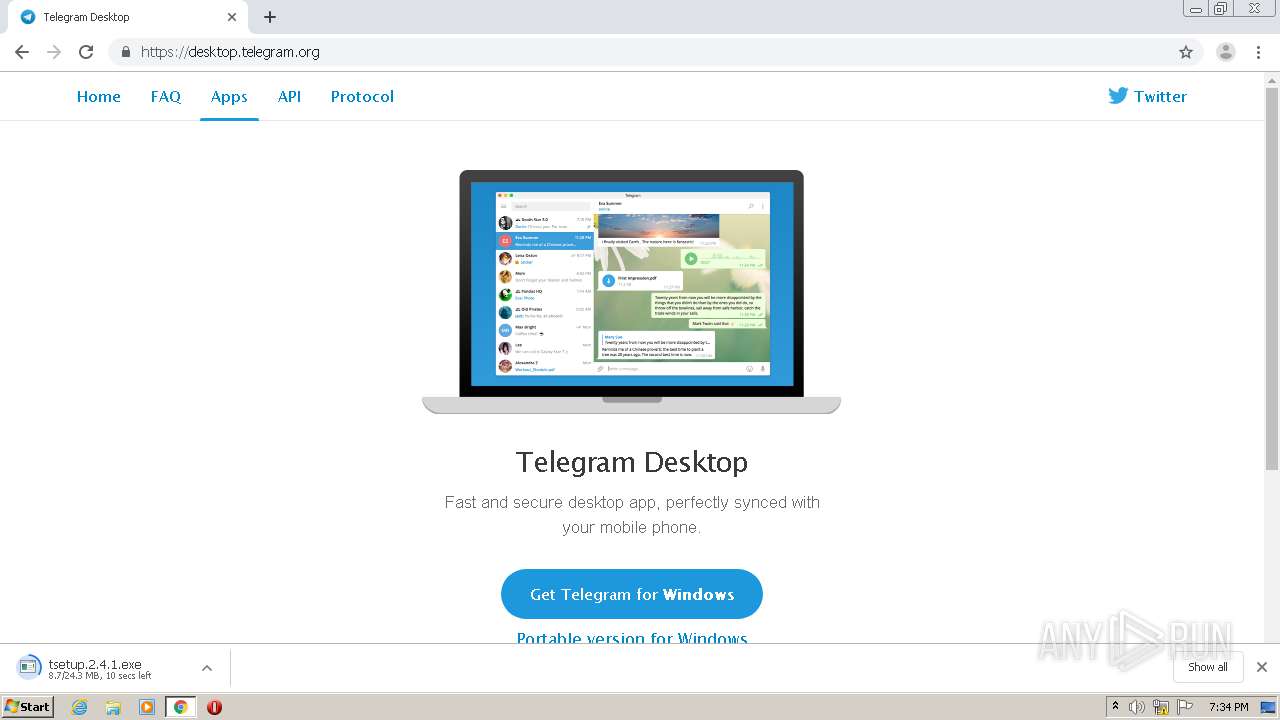
| 1812 | "C:\Users\admin\Downloads\tsetup.2.4.1.exe" | C:\Users\admin\Downloads\tsetup.2.4.1.exe | chrome.exe | ||||||||||||
User: admin Company: Telegram FZ-LLC Integrity Level: MEDIUM Description: Telegram Desktop Setup Exit code: 0 Version: 2.4.1.0 Modules
| |||||||||||||||
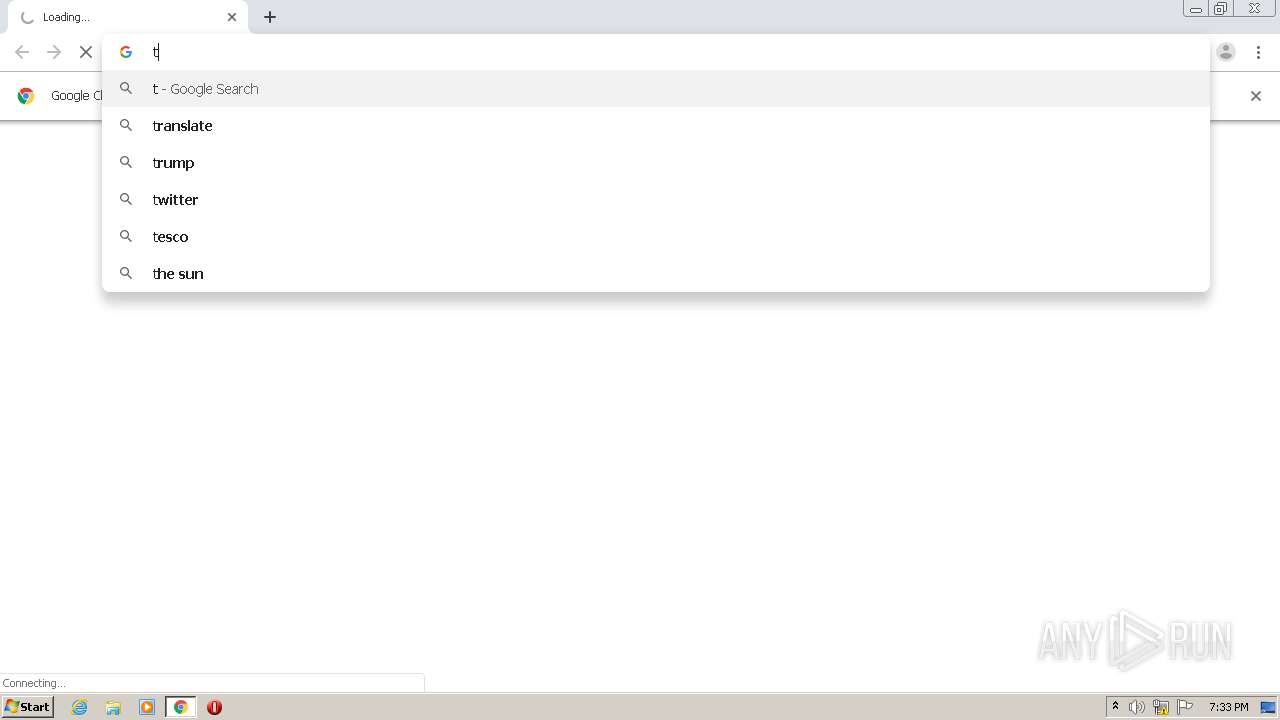
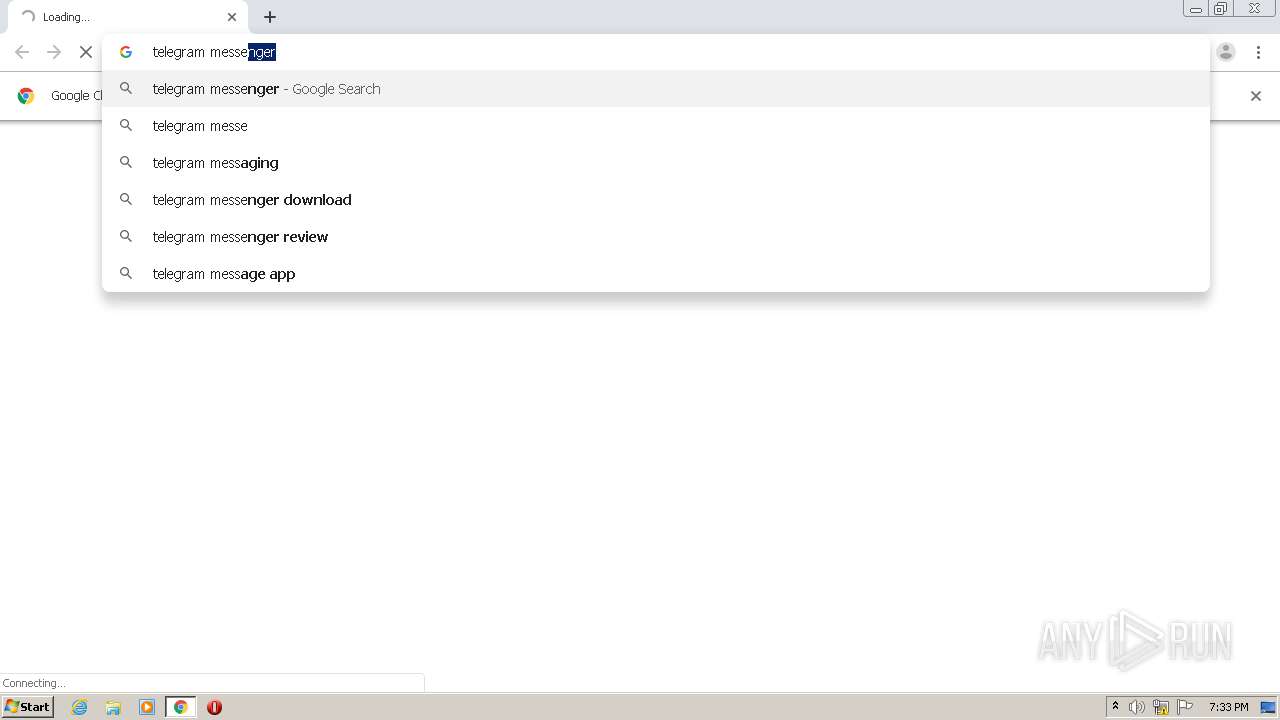
| 2232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://149.154.175.59/api" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,1184488586429825153,5549271513412027231,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9441185654134233344 --mojo-platform-channel-handle=2648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=988,1184488586429825153,5549271513412027231,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17642722237270144452 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 463
Read events
1 281
Write events
172
Delete events
10
Modification events
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (792) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2232-13246137216164500 |
Value: 259 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
8
Suspicious files
64
Text files
103
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F777280-8B8.pma | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3b761b.TMP | text | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF3b763a.TMP | text | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3b763a.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
61
DNS requests
24
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2872 | Telegram.exe | POST | — | 149.154.167.92:80 | http://149.154.167.92:80/api | GB | — | — | suspicious |
2872 | Telegram.exe | POST | 200 | 149.154.167.92:80 | http://149.154.167.92:80/api | GB | binary | 84 b | suspicious |
2872 | Telegram.exe | POST | 200 | 149.154.167.92:80 | http://149.154.167.92:80/api | GB | binary | 92 b | suspicious |
2872 | Telegram.exe | POST | 200 | 149.154.167.92:80 | http://149.154.167.92:80/api | GB | binary | 652 b | suspicious |
2872 | Telegram.exe | POST | 200 | 149.154.167.92:80 | http://149.154.167.92:80/api | GB | binary | 72 b | suspicious |
2872 | Telegram.exe | POST | — | 149.154.167.92:80 | http://149.154.167.92:80/api | GB | — | — | suspicious |
2872 | Telegram.exe | POST | 200 | 149.154.167.92:80 | http://149.154.167.92:80/api | GB | binary | 84 b | suspicious |
2872 | Telegram.exe | POST | — | 95.161.76.100:80 | http://95.161.76.100:80/api | RU | — | — | suspicious |
2872 | Telegram.exe | POST | — | 149.154.167.51:80 | http://149.154.167.51:80/api | GB | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2632 | chrome.exe | 149.154.175.59:443 | — | Telegram Messenger LLP | GB | suspicious |
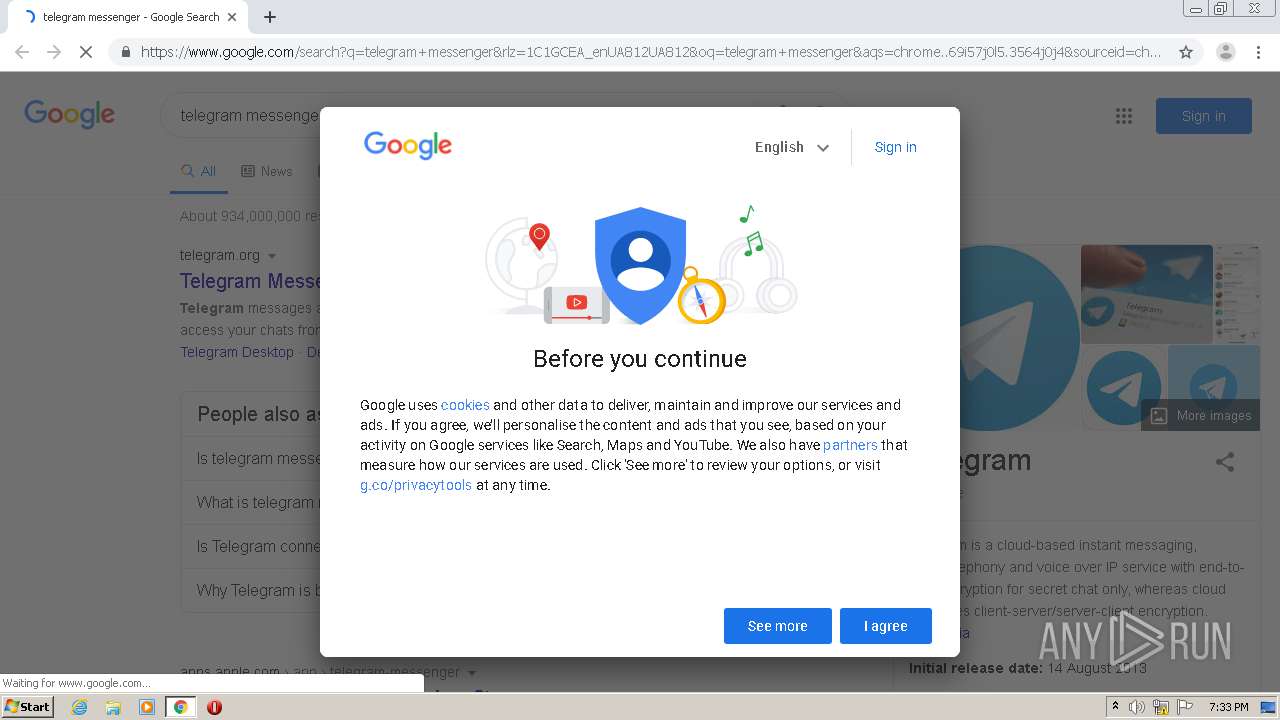
2632 | chrome.exe | 216.58.205.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2632 | chrome.exe | 142.250.74.196:443 | www.google.com | Google Inc. | US | whitelisted |
2632 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2632 | chrome.exe | 149.154.167.99:443 | telegram.org | Telegram Messenger LLP | GB | malicious |
2632 | chrome.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2632 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2632 | chrome.exe | 172.217.18.174:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
2632 | chrome.exe | 216.58.212.174:443 | ogs.google.com | Google Inc. | US | whitelisted |
2632 | chrome.exe | 172.217.21.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
consent.google.com |
| shared |
telegram.org |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2872 | Telegram.exe | Misc activity | APP [PTsecurity] Telegram Messenger v2 |
2872 | Telegram.exe | Misc activity | APP [PTsecurity] Telegram Messenger v2 |
2872 | Telegram.exe | Misc activity | APP [PTsecurity] Telegram Messenger v2 |
2872 | Telegram.exe | Misc activity | APP [PTsecurity] Telegram Messenger v3 HTTP |
2872 | Telegram.exe | Misc activity | APP [PTsecurity] Telegram Messenger v3 HTTP |
2872 | Telegram.exe | Misc activity | APP [PTsecurity] Telegram Messenger v3 HTTP |
2872 | Telegram.exe | Misc activity | APP [PTsecurity] Telegram Messenger v3 HTTP |
10 ETPRO signatures available at the full report