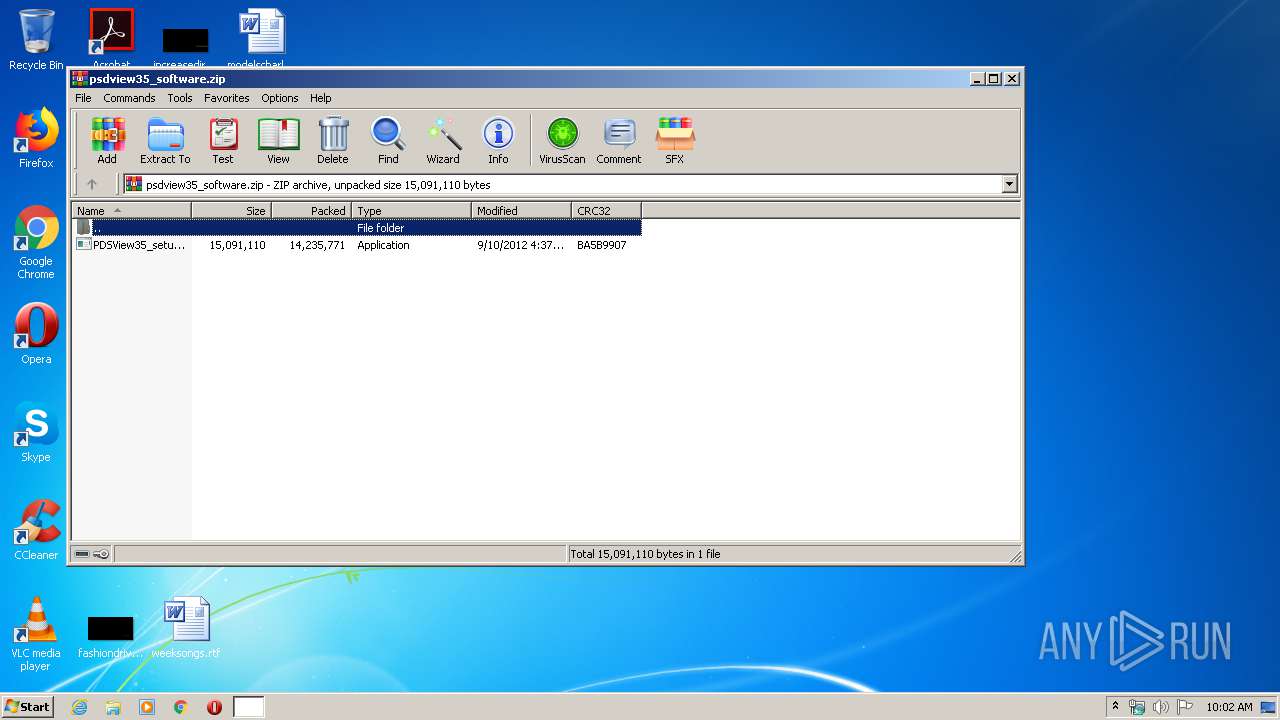
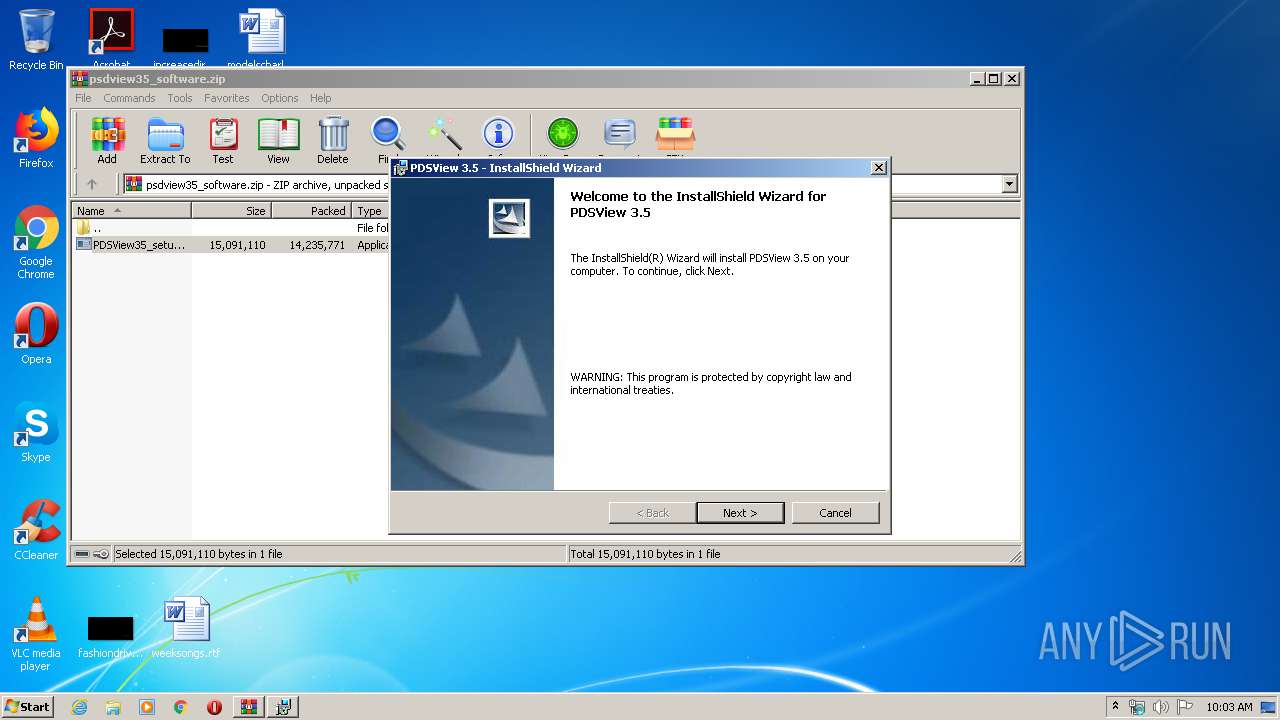
| File name: | psdview35_software.zip |
| Full analysis: | https://app.any.run/tasks/4434439d-86c8-40b8-9a20-7b94ed4ed8d6 |
| Verdict: | Malicious activity |
| Analysis date: | February 07, 2020, 10:02:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 678397C1C6BDE41EFBF4BA0CD9CDC3D3 |
| SHA1: | D684F0E24E9999036961FFBAFCBF292AE82F87BC |
| SHA256: | 303412FCFA9F2986E5E9D9D22C975D0BF51E6D2C913EE610926411B364CF7D02 |
| SSDEEP: | 393216:ozxkXBNnhs1KPUSrWhnq+pDHNXEXgCxu9LP:ozxkXds1KPrW5qENXELxOP |
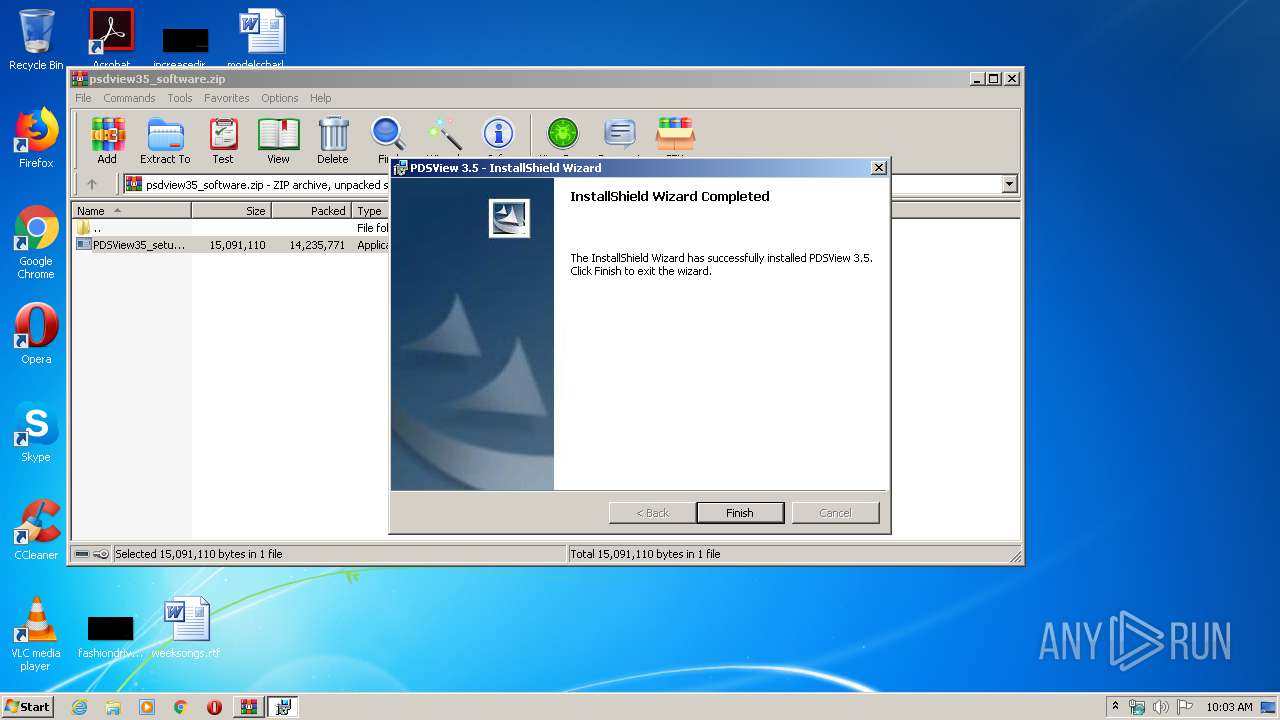
MALICIOUS
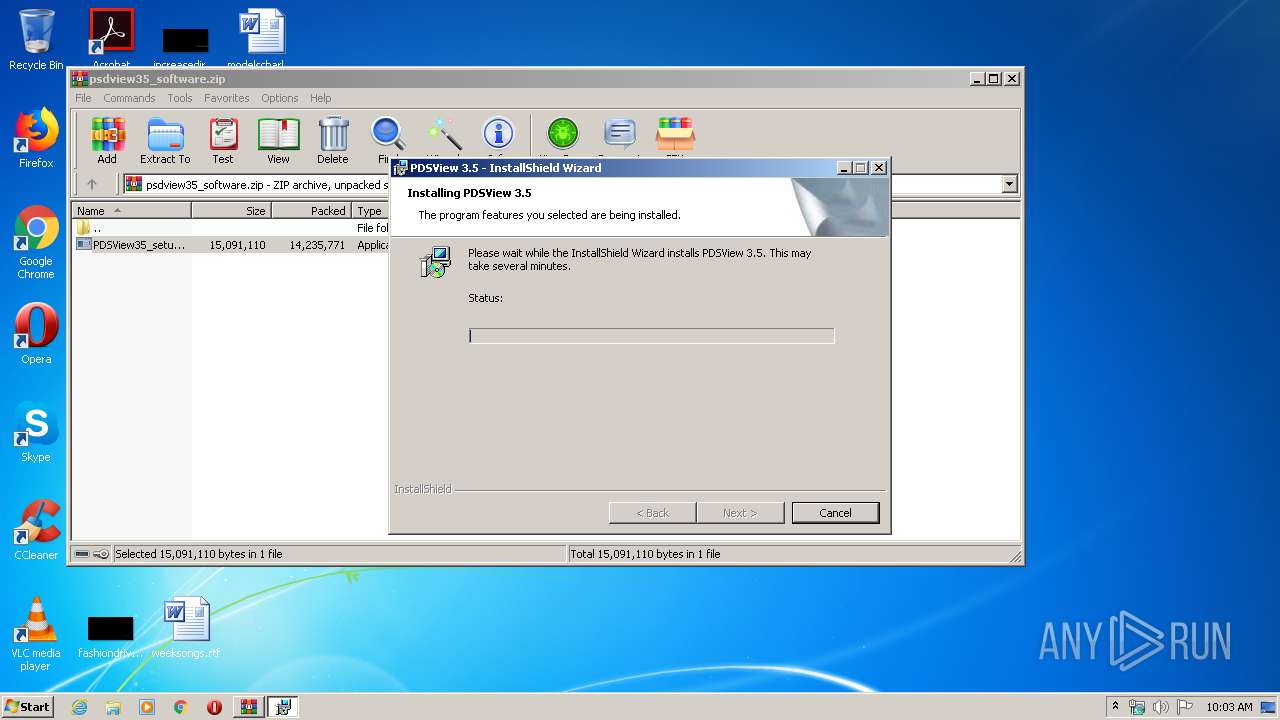
Application was dropped or rewritten from another process
- PDSView35_setup.exe (PID: 2976)
- PDSView.exe (PID: 2744)
Loads dropped or rewritten executable
- PDSView.exe (PID: 2744)
SUSPICIOUS
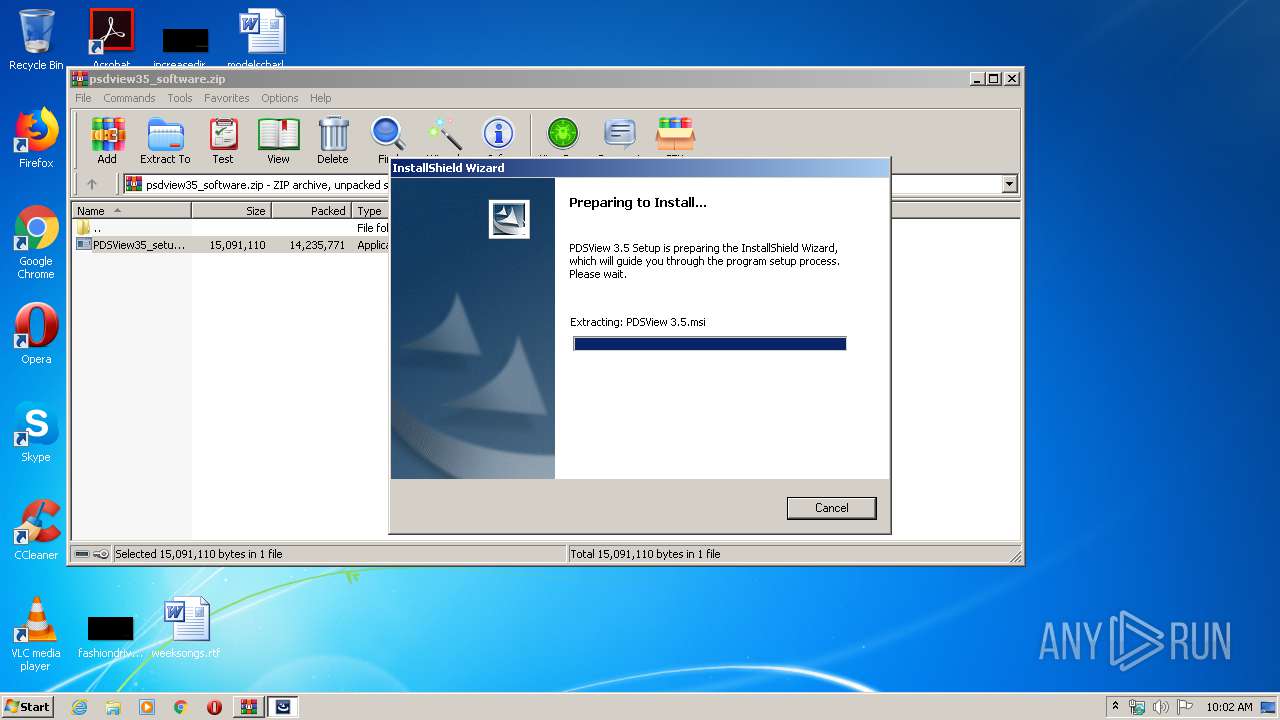
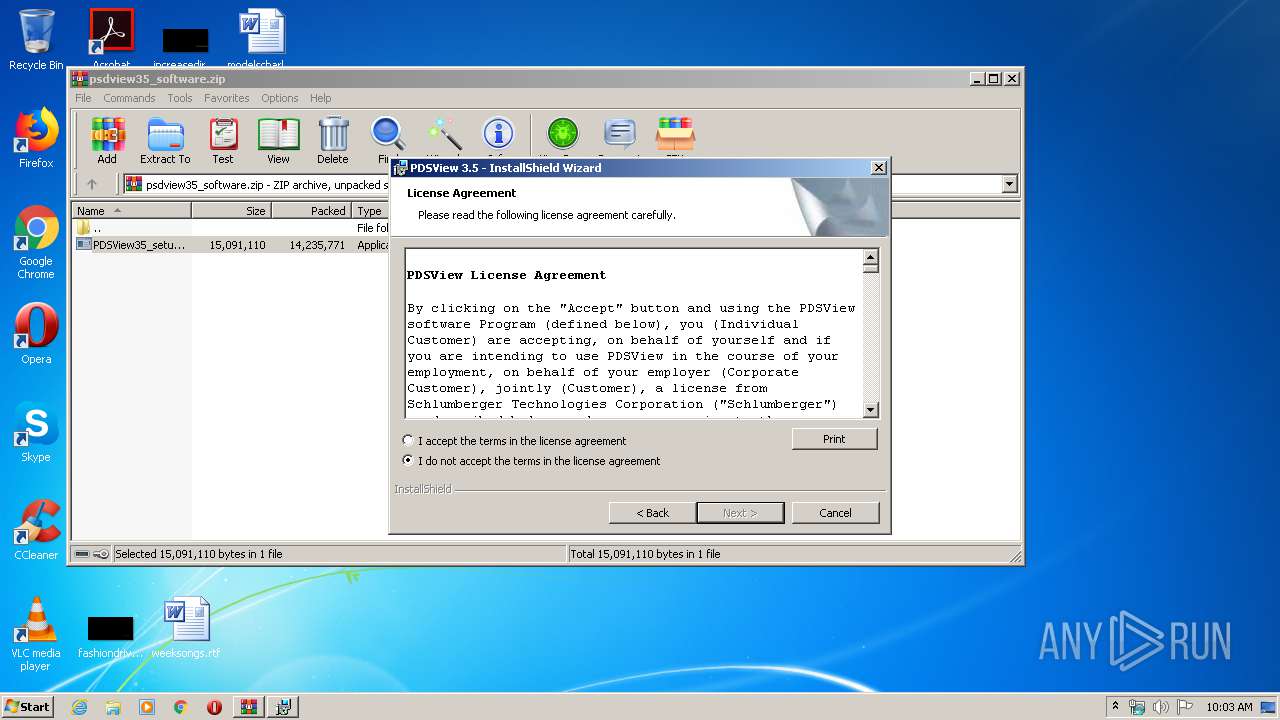
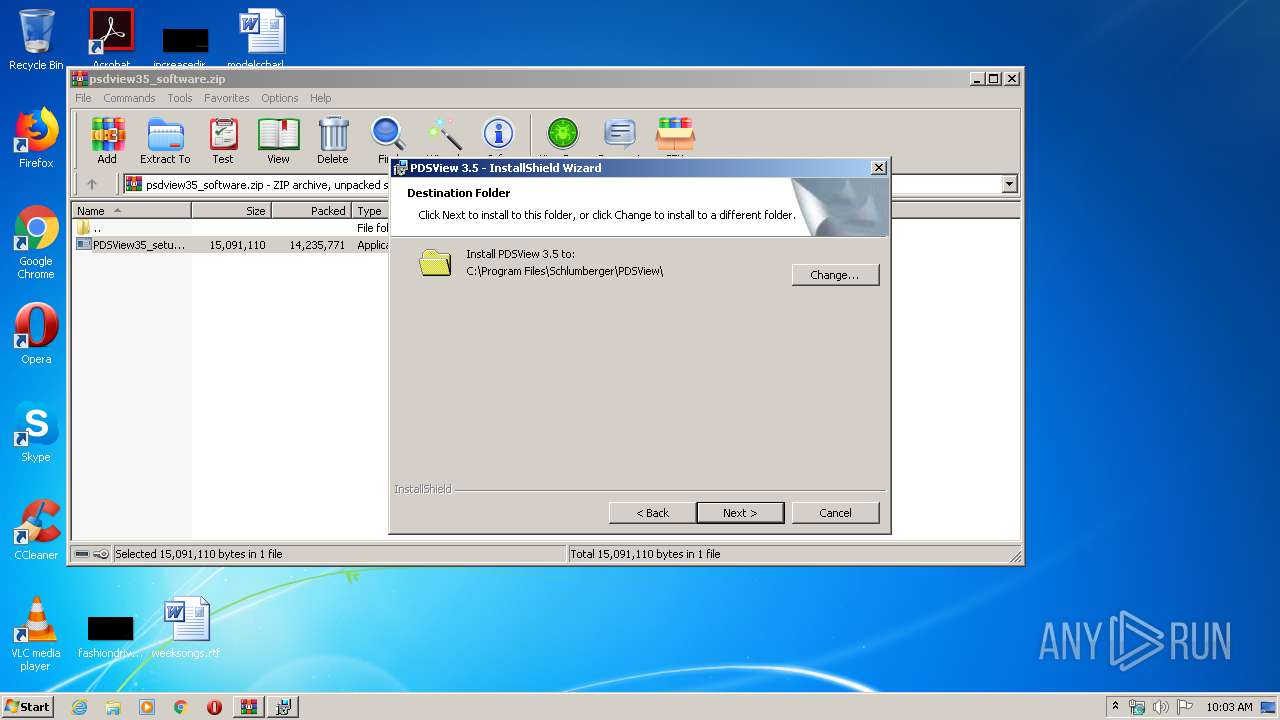
Starts Microsoft Installer
- PDSView35_setup.exe (PID: 2976)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1888)
- MSIEXEC.EXE (PID: 968)
- MsiExec.exe (PID: 3284)
- msiexec.exe (PID: 2012)
Executed as Windows Service
- vssvc.exe (PID: 1488)
Application launched itself
- MSIEXEC.EXE (PID: 968)
Creates files in the Windows directory
- msiexec.exe (PID: 2012)
Creates files in the user directory
- msiexec.exe (PID: 2012)
Modifies the open verb of a shell class
- msiexec.exe (PID: 2012)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3284)
Searches for installed software
- msiexec.exe (PID: 2012)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1488)
Creates a software uninstall entry
- msiexec.exe (PID: 2012)
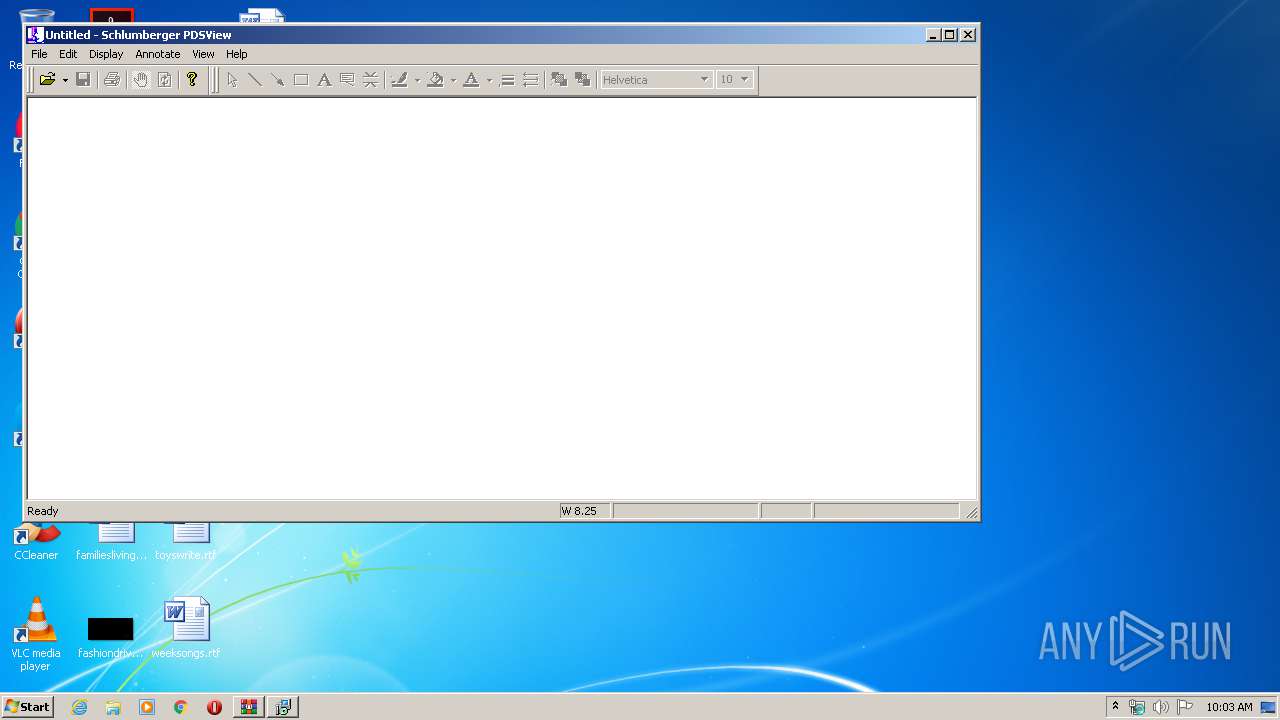
Manual execution by user
- PDSView.exe (PID: 2744)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2012)
Creates files in the program directory
- msiexec.exe (PID: 2012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
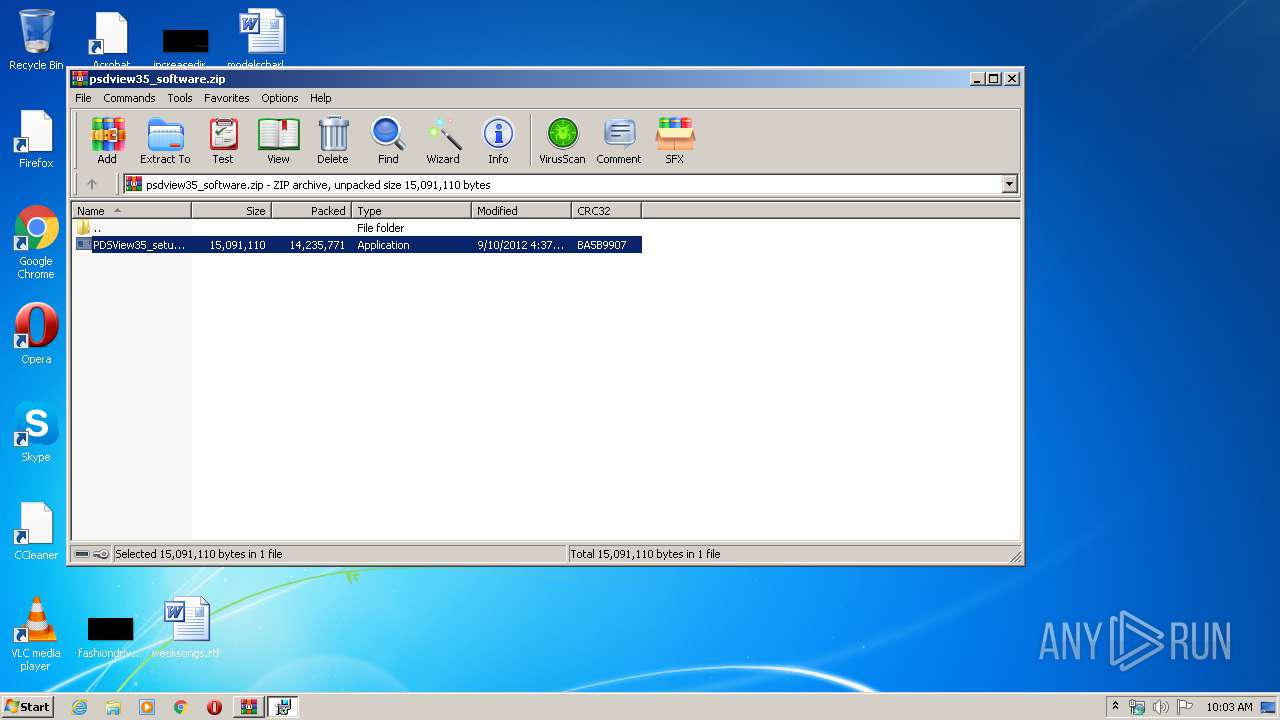
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2012:09:10 10:37:04 |
| ZipCRC: | 0xba5b9907 |
| ZipCompressedSize: | 14235771 |
| ZipUncompressedSize: | 15091110 |
| ZipFileName: | PDSView35_setup.exe |
Total processes
46
Monitored processes
10
Malicious processes
1
Suspicious processes
2
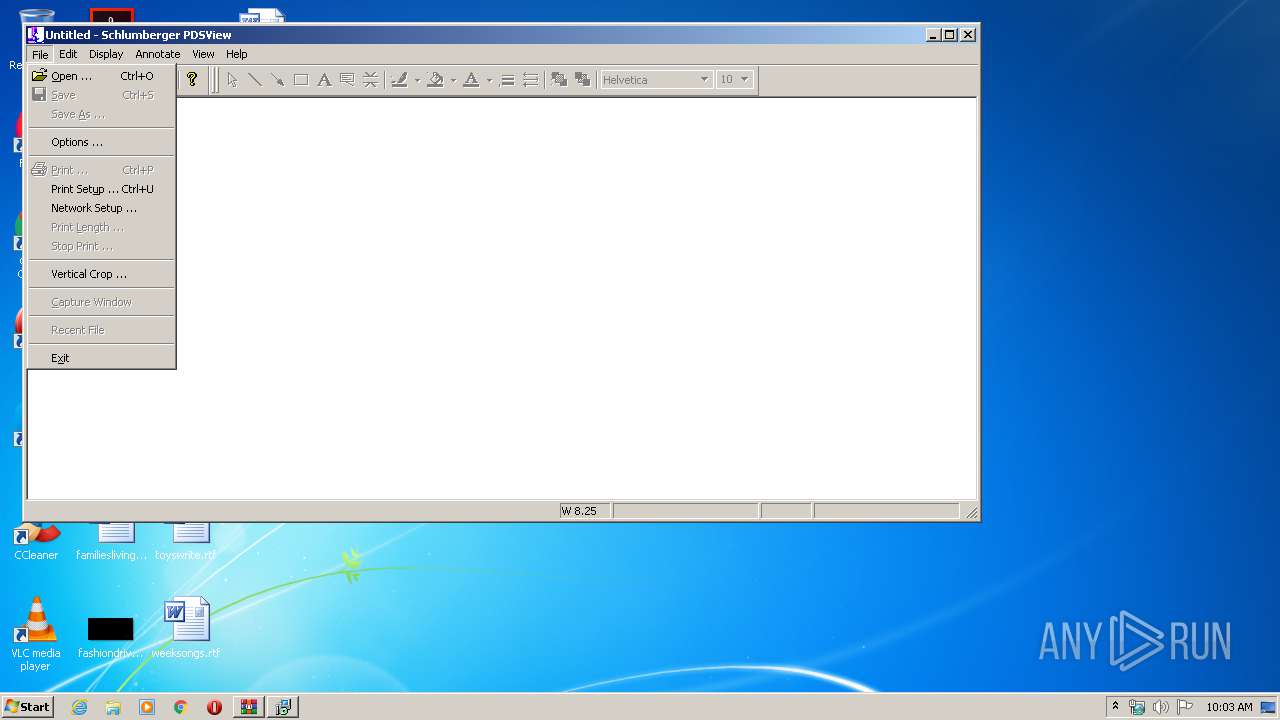
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 968 | MSIEXEC.EXE /i "C:\Users\admin\AppData\Local\Temp\{71BBE2B9-D4C7-4123-AEE0-33DB630B7FE4}\PDSView 3.5.msi" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp\Rar$EXa1888.27756" | C:\Windows\system32\MSIEXEC.EXE | PDSView35_setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1488 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\psdview35_software.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2012 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | msiexec /x {2BF7BF2F-A564-4CEF-ADA3-AFEF71A80184} /qn | C:\Windows\system32\msiexec.exe | — | MSIEXEC.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1605 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2744 | "C:\Program Files\Schlumberger\PDSView\PDSView.exe" | C:\Program Files\Schlumberger\PDSView\PDSView.exe | explorer.exe | ||||||||||||
User: admin Company: Schlumberger Integrity Level: MEDIUM Description: PDSView Exit code: 0 Version: 19C2-270 Modules
| |||||||||||||||
| 2796 | msiexec /x {1F21E618-6CE6-4EA6-91CC-45F5BF5FF41D} /qn | C:\Windows\system32\msiexec.exe | — | MSIEXEC.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1605 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1888.27756\PDSView35_setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1888.27756\PDSView35_setup.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Schlumberger Integrity Level: MEDIUM Description: Setup Launcher Exit code: 0 Version: 3.5 Modules
| |||||||||||||||
| 3244 | msiexec /x {AEB7C6A2-14A3-4DC2-9349-1FCEE58D9B54} /qn | C:\Windows\system32\msiexec.exe | — | MSIEXEC.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1605 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3284 | C:\Windows\system32\MsiExec.exe -Embedding BA4EA32774B25EA7A49FF143B68E2596 C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 829
Read events
1 091
Write events
726
Delete events
12
Modification events
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\psdview35_software.zip | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
43
Suspicious files
58
Text files
32
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | PDSView35_setup.exe | C:\Users\admin\AppData\Local\Temp\~9071.tmp | — | |
MD5:— | SHA256:— | |||
| 2976 | PDSView35_setup.exe | C:\Users\admin\AppData\Local\Temp\{71BBE2B9-D4C7-4123-AEE0-33DB630B7FE4}\PDSView 3.5.msi | — | |
MD5:— | SHA256:— | |||
| 968 | MSIEXEC.EXE | C:\Users\admin\AppData\Local\Temp\MSIA5BE.tmp | — | |
MD5:— | SHA256:— | |||
| 968 | MSIEXEC.EXE | C:\Users\admin\AppData\Local\Temp\MSIA775.tmp | — | |
MD5:— | SHA256:— | |||
| 3284 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\{183E1CE4-BDBE-4788-8FD1-F907FE54BF29}\setup.inx | — | |
MD5:— | SHA256:— | |||
| 3284 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\{183E1CE4-BDBE-4788-8FD1-F907FE54BF29}\ISRT.dll | — | |
MD5:— | SHA256:— | |||
| 3284 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\{183E1CE4-BDBE-4788-8FD1-F907FE54BF29}\IsConfig.ini | — | |
MD5:— | SHA256:— | |||
| 3284 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\{183E1CE4-BDBE-4788-8FD1-F907FE54BF29}\_isres.dll | — | |
MD5:— | SHA256:— | |||
| 3284 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\{183E1CE4-BDBE-4788-8FD1-F907FE54BF29}\String1033.txt | — | |
MD5:— | SHA256:— | |||
| 2012 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
PDSView.exe | Invalid parameter passed to C runtime function.
|