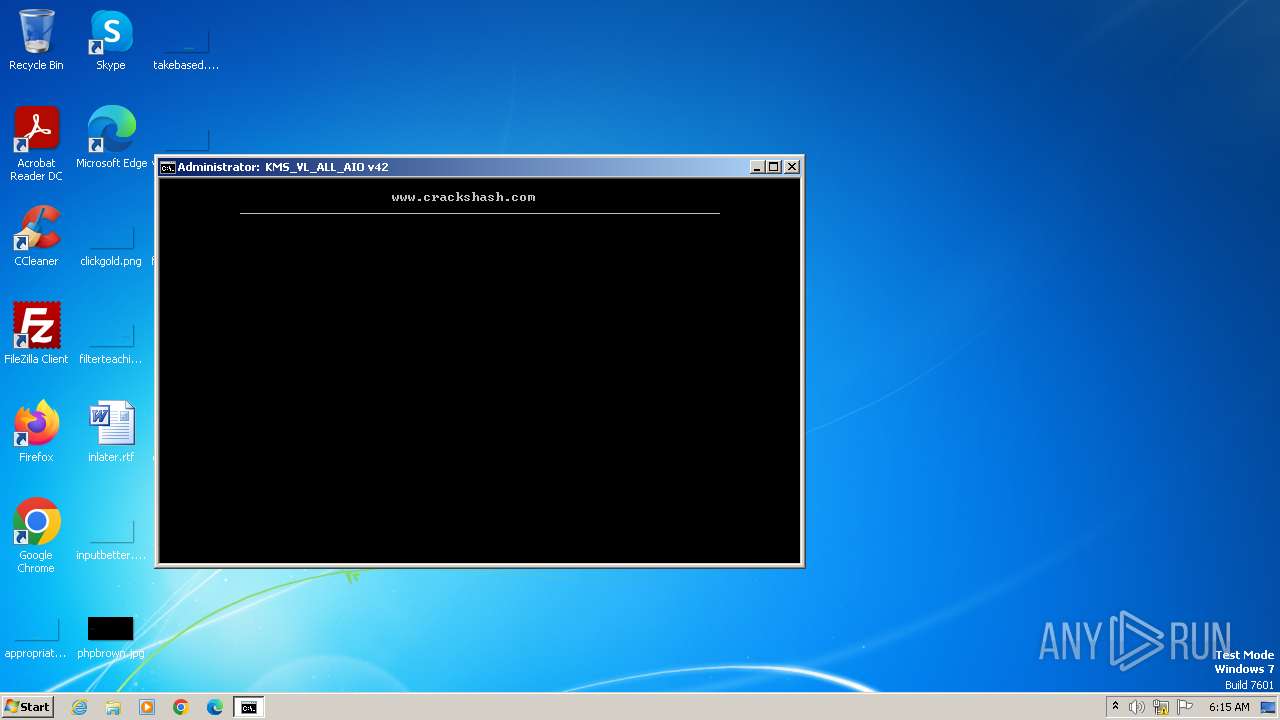
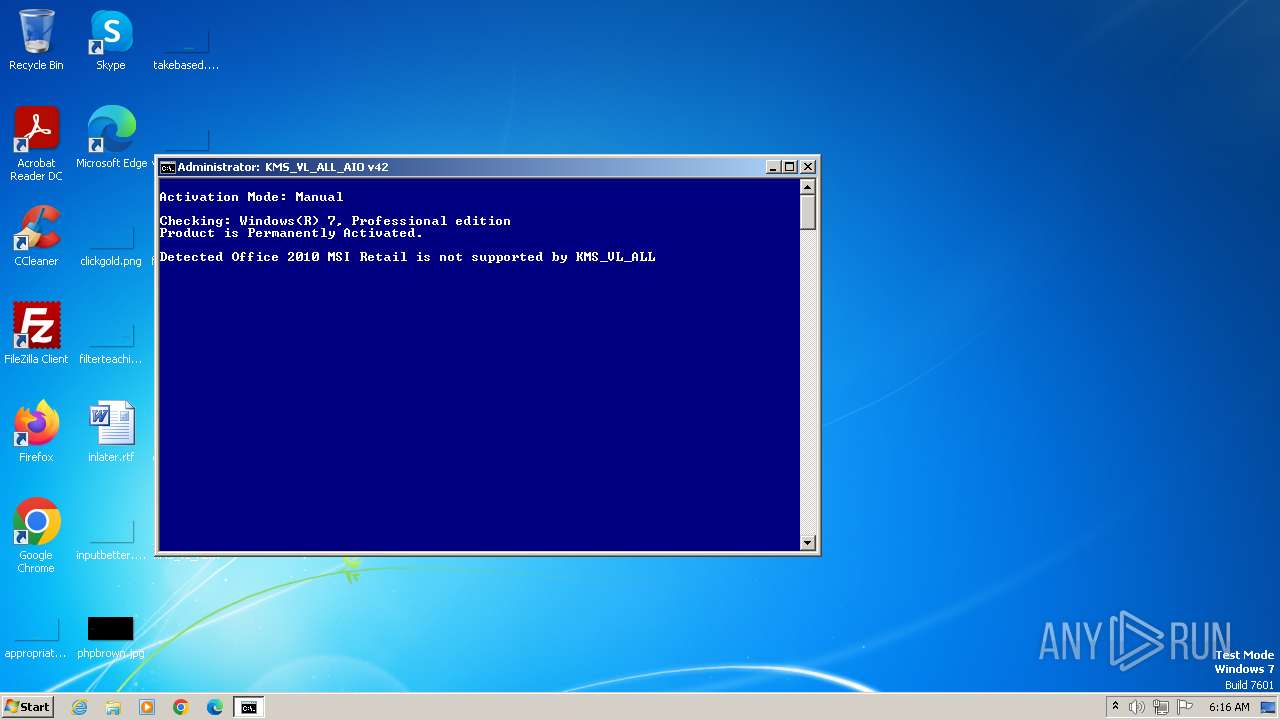
| File name: | KMS_VL_ALL_AIO_Getintopc.cmd |
| Full analysis: | https://app.any.run/tasks/f1fa5d71-59d1-4791-bd17-b1cb212a47f9 |
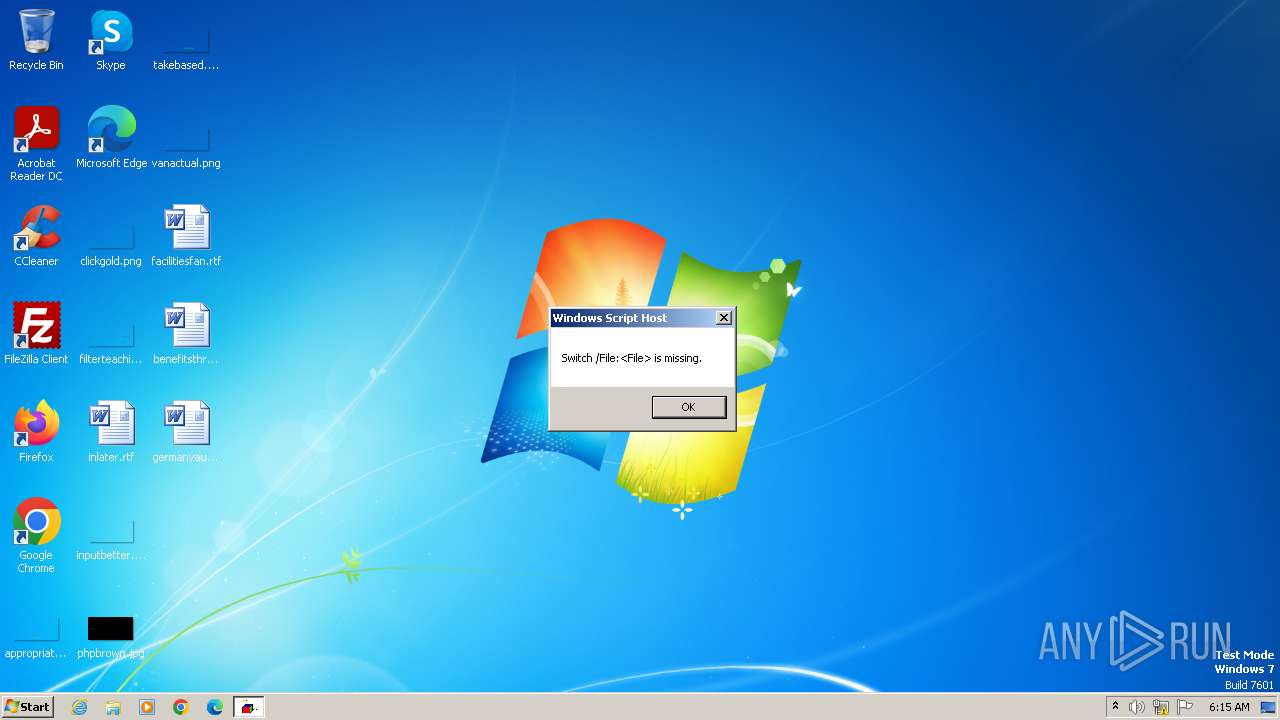
| Verdict: | Malicious activity |
| Analysis date: | November 26, 2023, 06:15:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | exported SGML document, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 2A0CEF56F3B0D339121E6F15060E6254 |
| SHA1: | B6963E21F8455021B201231EA123BB6771116AB9 |
| SHA256: | 302E8CEB93E6316F2C2241E38FD1AEAD5EF2E647CEAC0CF1C94DFDF1B6C0ACBF |
| SSDEEP: | 6144:sJ6J/nu6Sfm0z/GnkSzM4fK02PYKSFLGJ18QH6kzvlv:sJ6J/BSfm00M4yFAKSMJ18q6k7lv |
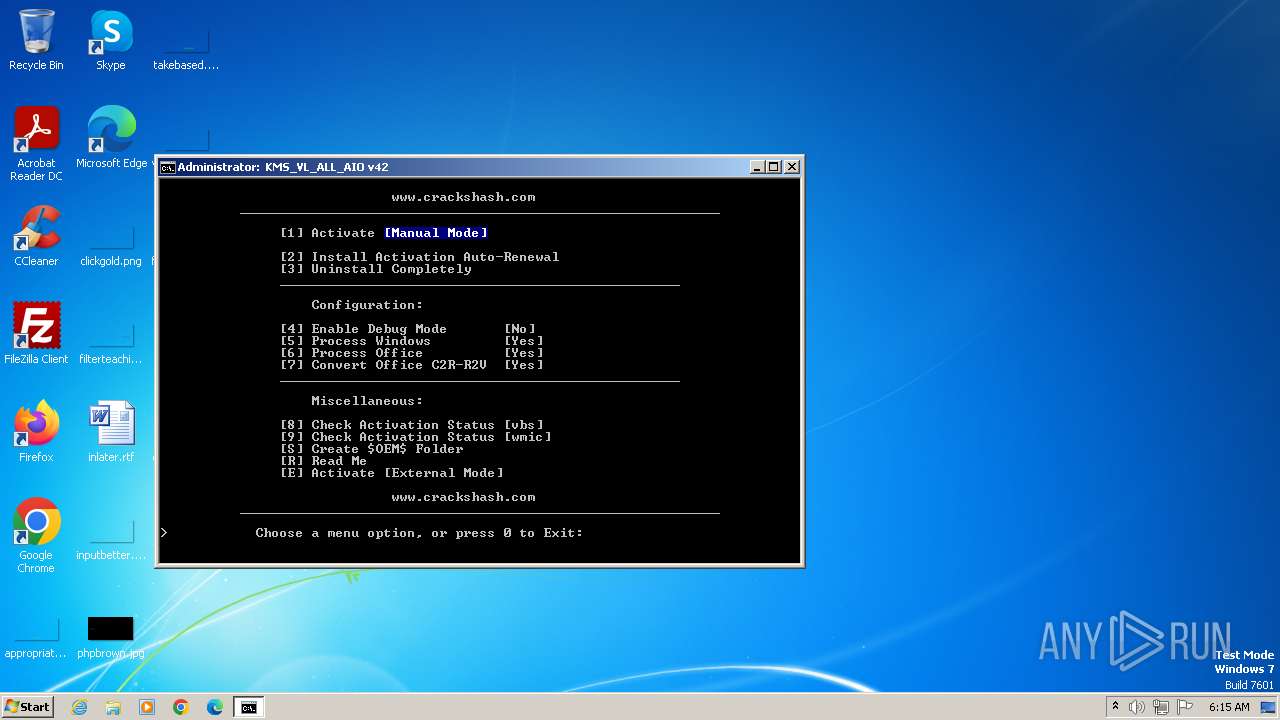
MALICIOUS
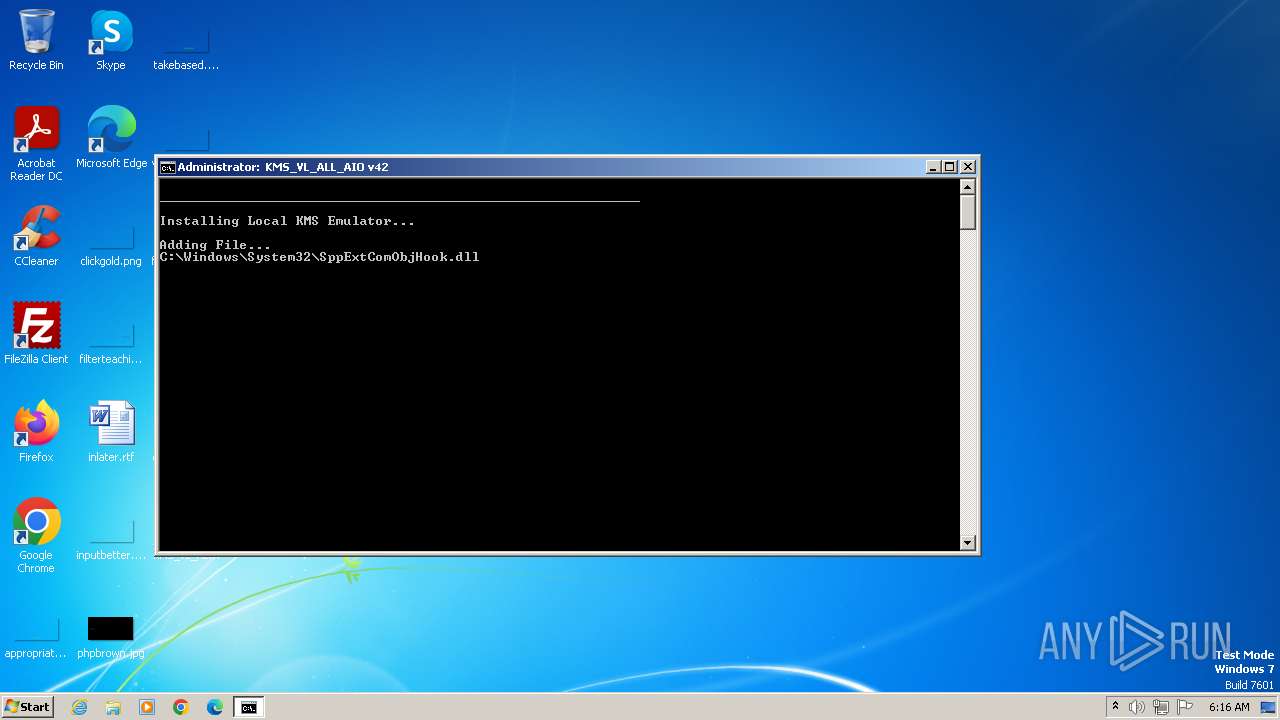
Creates a writable file in the system directory
- powershell.exe (PID: 1900)
- powershell.exe (PID: 3244)
Drops the executable file immediately after the start
- powershell.exe (PID: 1900)
- csc.exe (PID: 2416)
- csc.exe (PID: 476)
- powershell.exe (PID: 3244)
Starts Visual C# compiler
- powershell.exe (PID: 1900)
- powershell.exe (PID: 3244)
Starts NET.EXE for service management
- cmd.exe (PID: 3160)
- net.exe (PID: 2312)
- net.exe (PID: 276)
- net.exe (PID: 2968)
- net.exe (PID: 844)
- net.exe (PID: 3468)
- net.exe (PID: 2396)
- net.exe (PID: 2400)
SUSPICIOUS
Reads the Internet Settings
- wscript.exe (PID: 2708)
- cscript.exe (PID: 1988)
- cmd.exe (PID: 3160)
- WMIC.exe (PID: 3432)
- WMIC.exe (PID: 2152)
- WMIC.exe (PID: 3724)
- WMIC.exe (PID: 3732)
- WMIC.exe (PID: 2396)
- WMIC.exe (PID: 3872)
- WMIC.exe (PID: 1508)
- WMIC.exe (PID: 4020)
- WMIC.exe (PID: 3424)
- WMIC.exe (PID: 2376)
- WMIC.exe (PID: 2884)
- WMIC.exe (PID: 128)
- WMIC.exe (PID: 4028)
- WMIC.exe (PID: 3280)
- WMIC.exe (PID: 3104)
- WMIC.exe (PID: 2512)
- WMIC.exe (PID: 1728)
- WMIC.exe (PID: 3740)
- WMIC.exe (PID: 1496)
- WMIC.exe (PID: 3688)
- WMIC.exe (PID: 2984)
- WMIC.exe (PID: 3600)
Starts CMD.EXE for commands execution
- cscript.exe (PID: 1988)
- cmd.exe (PID: 3160)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 1988)
Executing commands from ".cmd" file
- cscript.exe (PID: 1988)
Runs shell command (SCRIPT)
- cscript.exe (PID: 1988)
Starts SC.EXE for service management
- cmd.exe (PID: 3160)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3160)
Application launched itself
- cmd.exe (PID: 3160)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 3160)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 3160)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3160)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 3160)
Powershell version downgrade attack
- powershell.exe (PID: 1460)
- powershell.exe (PID: 1900)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 3244)
- powershell.exe (PID: 2184)
Uses .NET C# to load dll
- powershell.exe (PID: 1900)
- powershell.exe (PID: 3244)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3160)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 3616)
- cmd.exe (PID: 3896)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1784)
- cmd.exe (PID: 2220)
- cmd.exe (PID: 2492)
- cmd.exe (PID: 3376)
- cmd.exe (PID: 3160)
INFO
Reads security settings of Internet Explorer
- cscript.exe (PID: 1988)
Manual execution by a user
- cmd.exe (PID: 1668)
- msedge.exe (PID: 3624)
- wmpnscfg.exe (PID: 2136)
Checks operating system version
- cmd.exe (PID: 3160)
Application launched itself
- msedge.exe (PID: 3216)
- msedge.exe (PID: 3624)
Checks supported languages
- mode.com (PID: 1696)
- cvtres.exe (PID: 1988)
- csc.exe (PID: 2416)
- wmpnscfg.exe (PID: 2136)
- mode.com (PID: 3152)
- mode.com (PID: 3016)
- csc.exe (PID: 476)
- cvtres.exe (PID: 3188)
Reads the computer name
- wmpnscfg.exe (PID: 2136)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 2136)
- cvtres.exe (PID: 1988)
- csc.exe (PID: 476)
- cvtres.exe (PID: 3188)
- csc.exe (PID: 2416)
Create files in a temporary directory
- cvtres.exe (PID: 1988)
- csc.exe (PID: 476)
- cvtres.exe (PID: 3188)
- csc.exe (PID: 2416)
Reads Microsoft Office registry keys
- reg.exe (PID: 3924)
- reg.exe (PID: 1696)
- reg.exe (PID: 3916)
- reg.exe (PID: 3156)
- reg.exe (PID: 3576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .wsf | | | Windows Script File (72.7) |
|---|---|---|
| .html | | | HyperText Markup Language (27.2) |
Total processes
342
Monitored processes
294
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | sc query sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 128 | wmic path SoftwareLicensingService get Version /VALUE | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 188 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe" /f /v KMS_RenewalInterval /t REG_DWORD /d 43200 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 276 | net stop osppsvc /y | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 276 | findstr "1" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 304 | C:\Windows\system32\cmd.exe /c dir /b /ad C:\Windows\System32\spp\tokens\channels | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 476 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\rsdqtbd8.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.5483 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 476 | sc query ClickToRunSvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 544 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /f /v KMS_RenewalInterval /t REG_DWORD /d 43200 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 580 | sc query OfficeSvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
12 996
Read events
12 664
Write events
322
Delete events
10
Modification events
| (PID) Process: | (1988) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1988) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1988) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1988) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3216) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3216) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3216) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3216) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3216) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3216) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
4
Suspicious files
86
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3528 | msedge.exe | — | ||
MD5:— | SHA256:— | |||
| 3624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1c266b.TMP | — | |
MD5:— | SHA256:— | |||
| 3624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1c268b.TMP | — | |
MD5:— | SHA256:— | |||
| 3624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Sync Data\LevelDB\LOG.old~RF1c268b.TMP | text | |
MD5:7F169CD2570538CEC8F1F23C0814272F | SHA256:3E92388691F2F940500E93E73FAF1BB90ADB857E508C2C04A94D166F6983342D | |||
| 2860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:C612E96CBFAC63232FC2062E15600FB1 | SHA256:DB3C05D5EC0B6719A73E7F0BE84BCE9342772DA70567E7CE08CF6573480B38FF | |||
| 3216 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\857abeb5-500a-47ba-bf16-577eda3a65d4.tmp | binary | |
MD5:01DB1C50EC424903DB5F310184FDFF9A | SHA256:63E08BFCDFE214452D6E0F6F8664C5C1AA0B3B66F4150F31764DA1CF5C597703 | |||
| 3624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1c26e8.TMP | — | |
MD5:— | SHA256:— | |||
| 3624 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
27
DNS requests
28
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3624 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3608 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3608 | msedge.exe | 20.103.180.120:443 | nav-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
3608 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
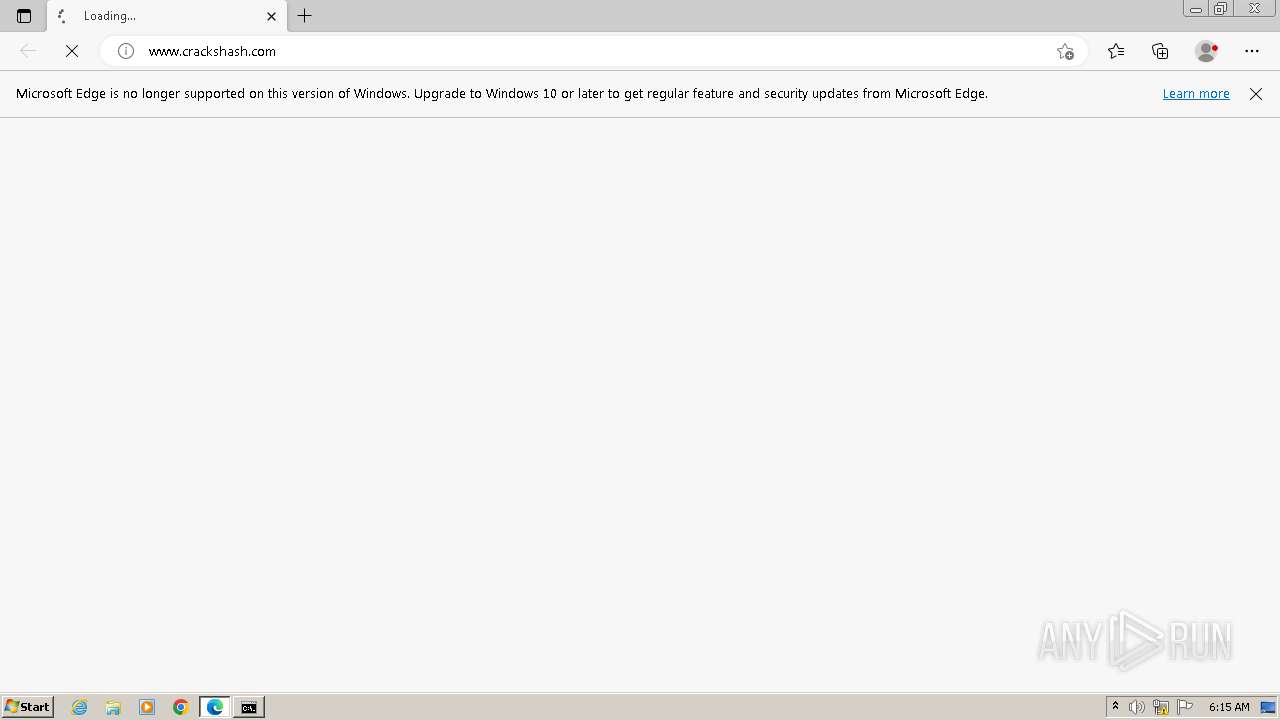
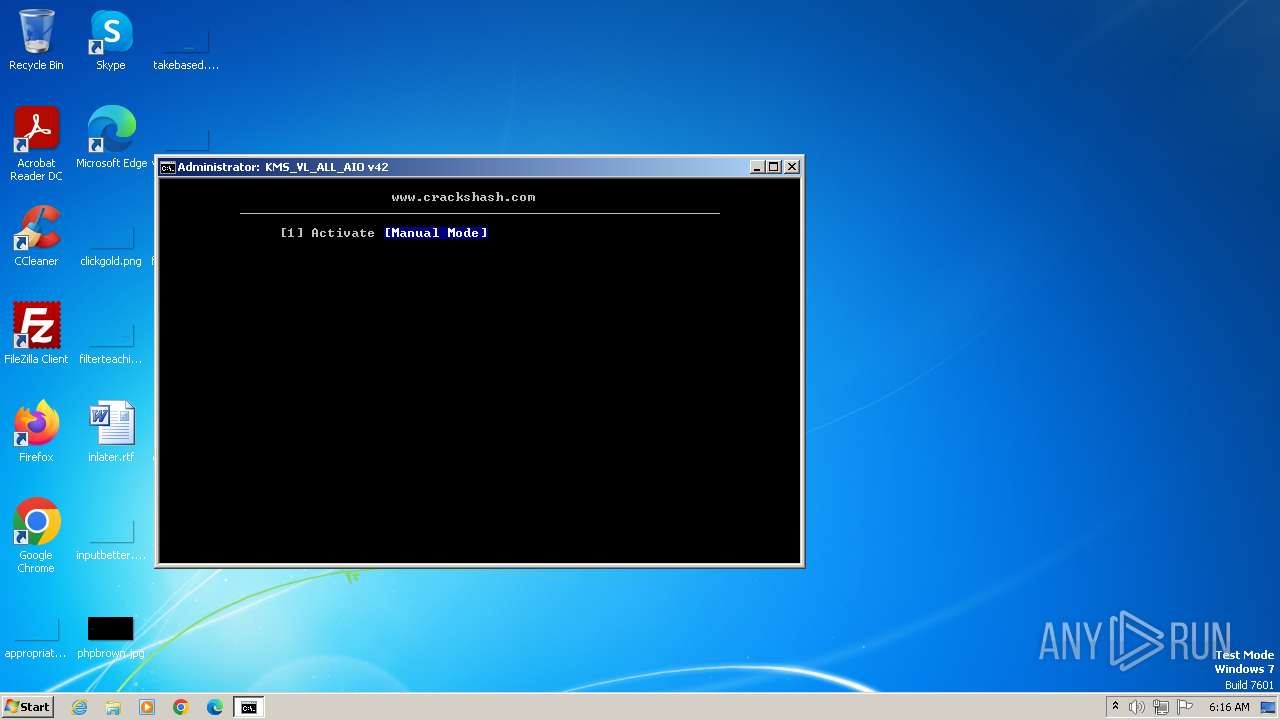
3608 | msedge.exe | 104.21.0.236:443 | www.crackshash.com | CLOUDFLARENET | — | unknown |
3608 | msedge.exe | 20.105.95.163:443 | data-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
www.crackshash.com |
| unknown |
nav-edge.smartscreen.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
data-edge.smartscreen.microsoft.com |
| whitelisted |
crackshash.com |
| malicious |
cdn.jsdelivr.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|