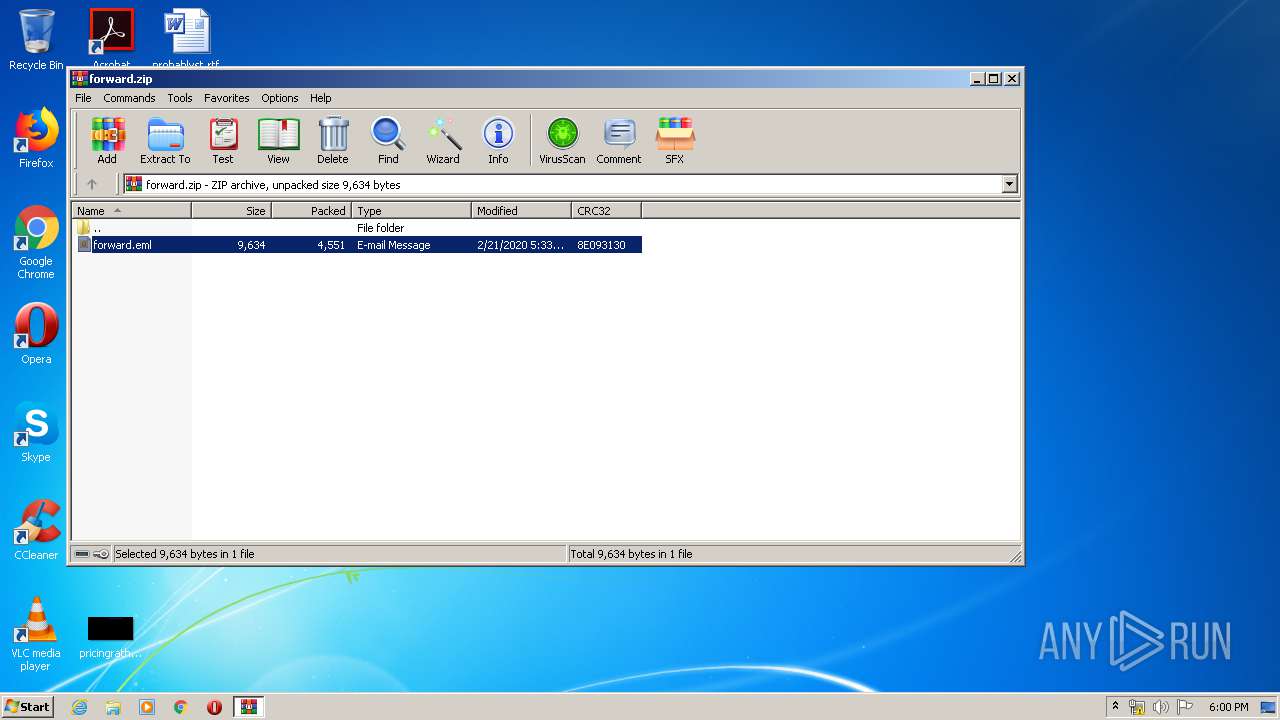
| File name: | forward.zip |
| Full analysis: | https://app.any.run/tasks/9d108150-6b65-4d74-a1df-a147c1994dfe |
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 17:58:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E70EEFC05C58DD9F3C1B78E345DD6430 |
| SHA1: | E5902C6FF7673514C174A27831A1874F0CF44A55 |
| SHA256: | 302D1A50BF88F394B16E6B55583AC5A4EEA14F3B7D27B37A106C50A0B4F39215 |
| SSDEEP: | 96:YLTqfCQO5CSj8CI4R/vpfpkhvE43Dftq7GuKy3nmjCJ:0LjCHKv0h9D+93nx |
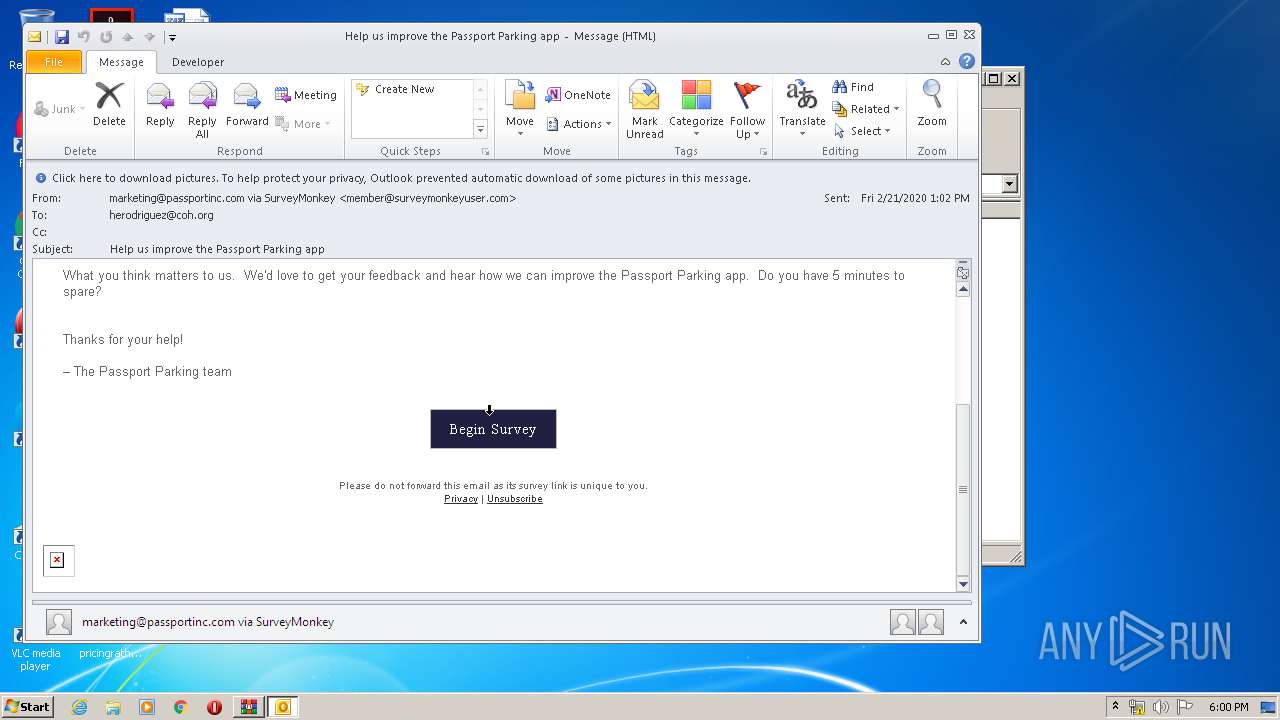
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2460)
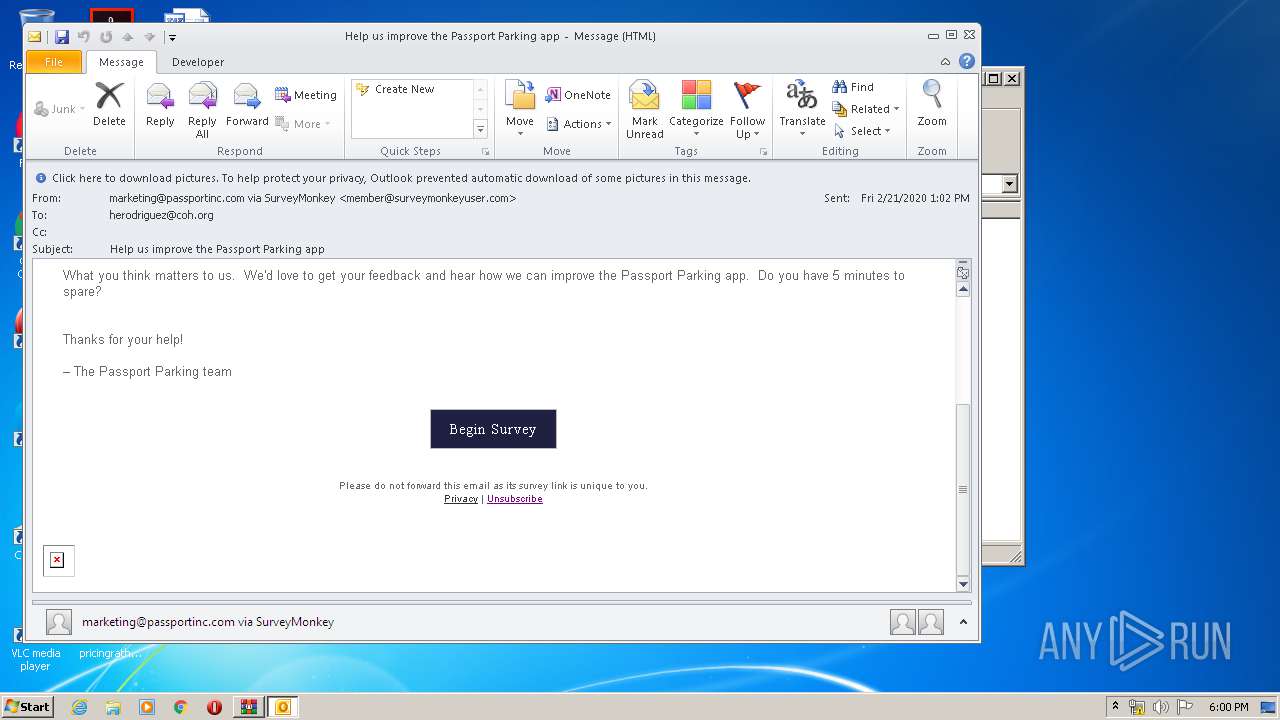
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2460)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2460)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3052)
- iexplore.exe (PID: 2736)
Application launched itself
- iexplore.exe (PID: 3052)
Changes internet zones settings
- iexplore.exe (PID: 3052)
Reads settings of System Certificates
- iexplore.exe (PID: 2736)
- iexplore.exe (PID: 3052)
Reads internet explorer settings
- iexplore.exe (PID: 2736)
Creates files in the user directory
- iexplore.exe (PID: 2736)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2460)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3052)
Changes settings of System certificates
- iexplore.exe (PID: 3052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
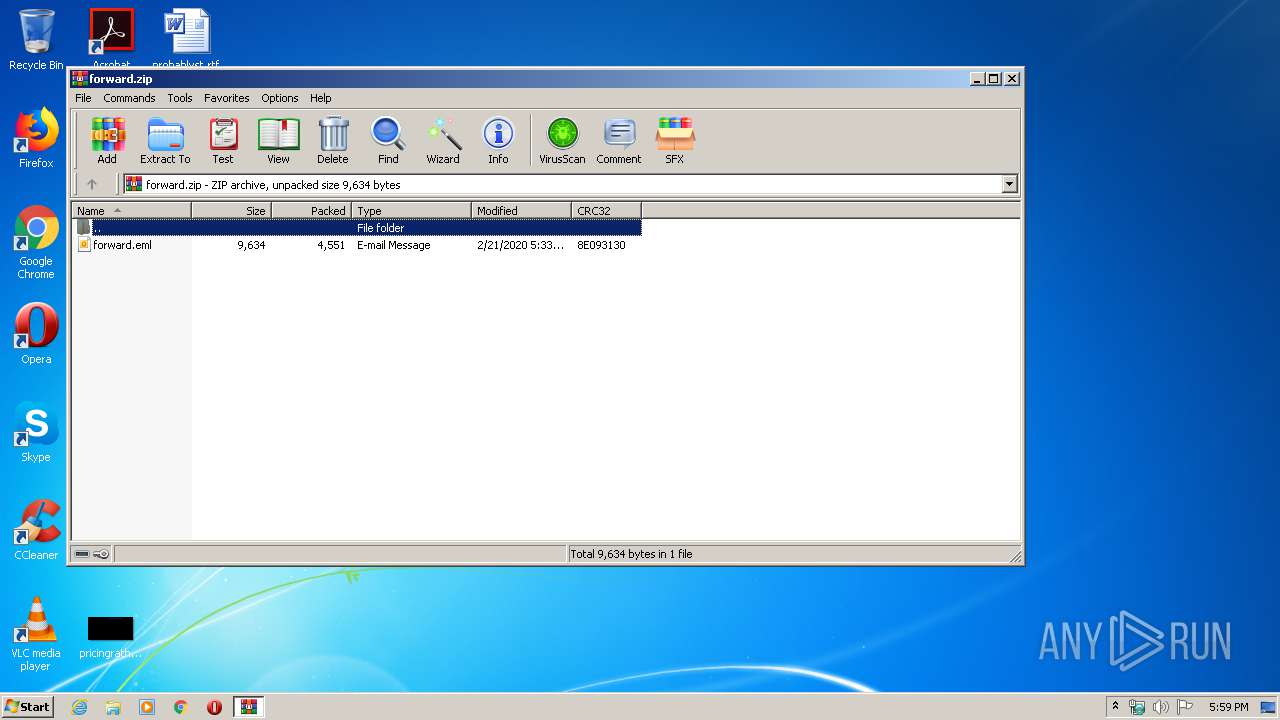
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:02:21 09:33:18 |
| ZipCRC: | 0x8e093130 |
| ZipCompressedSize: | 4551 |
| ZipUncompressedSize: | 9634 |
| ZipFileName: | forward.eml |
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
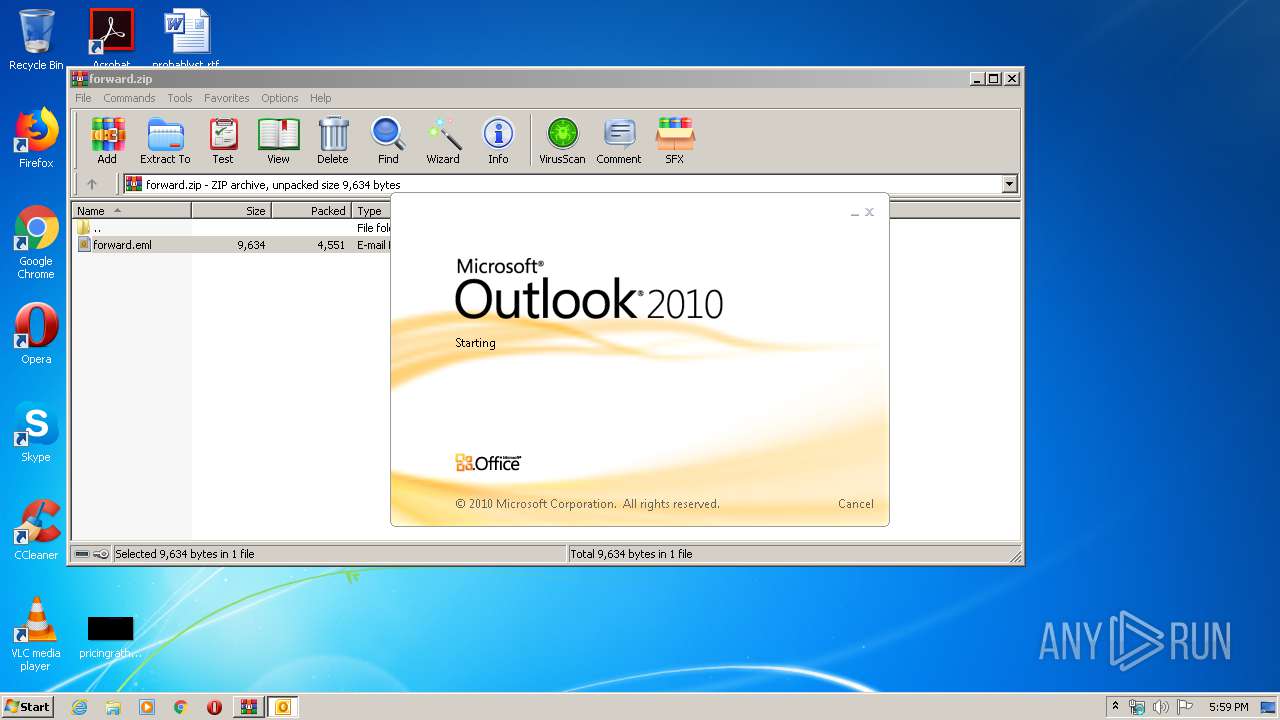
| 2460 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIa2876.49842\forward.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
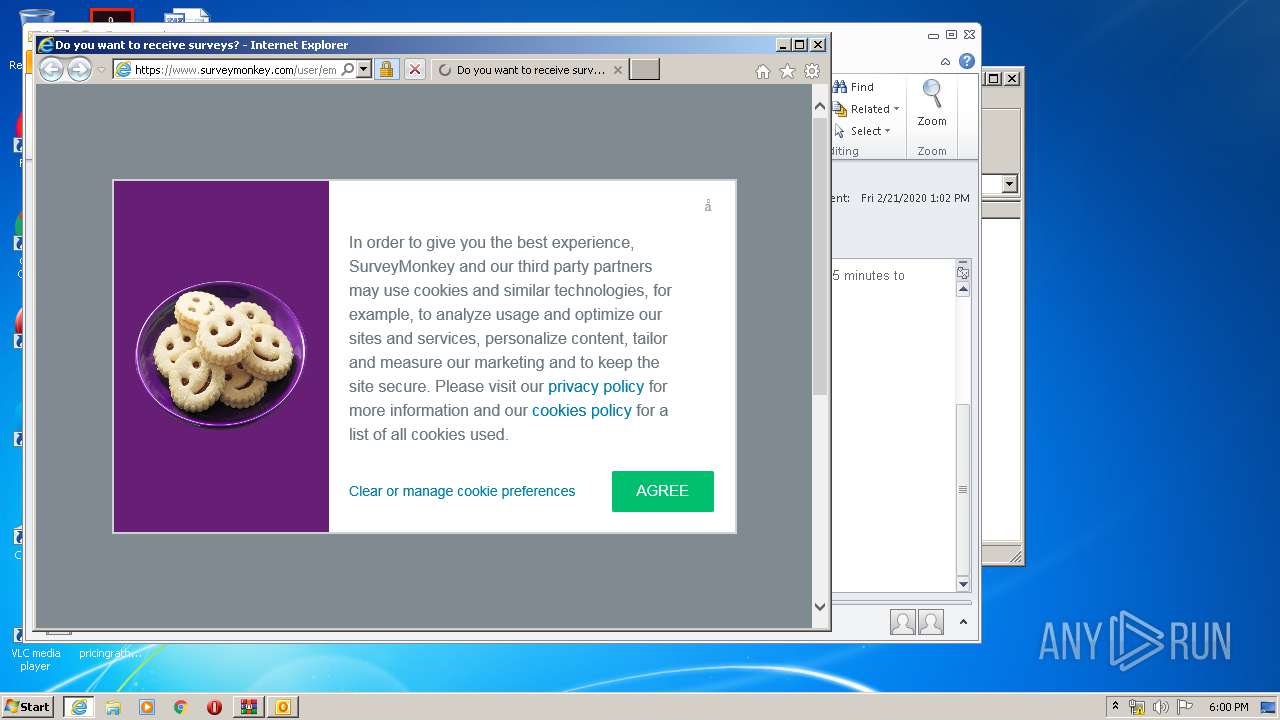
| 2736 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3052 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
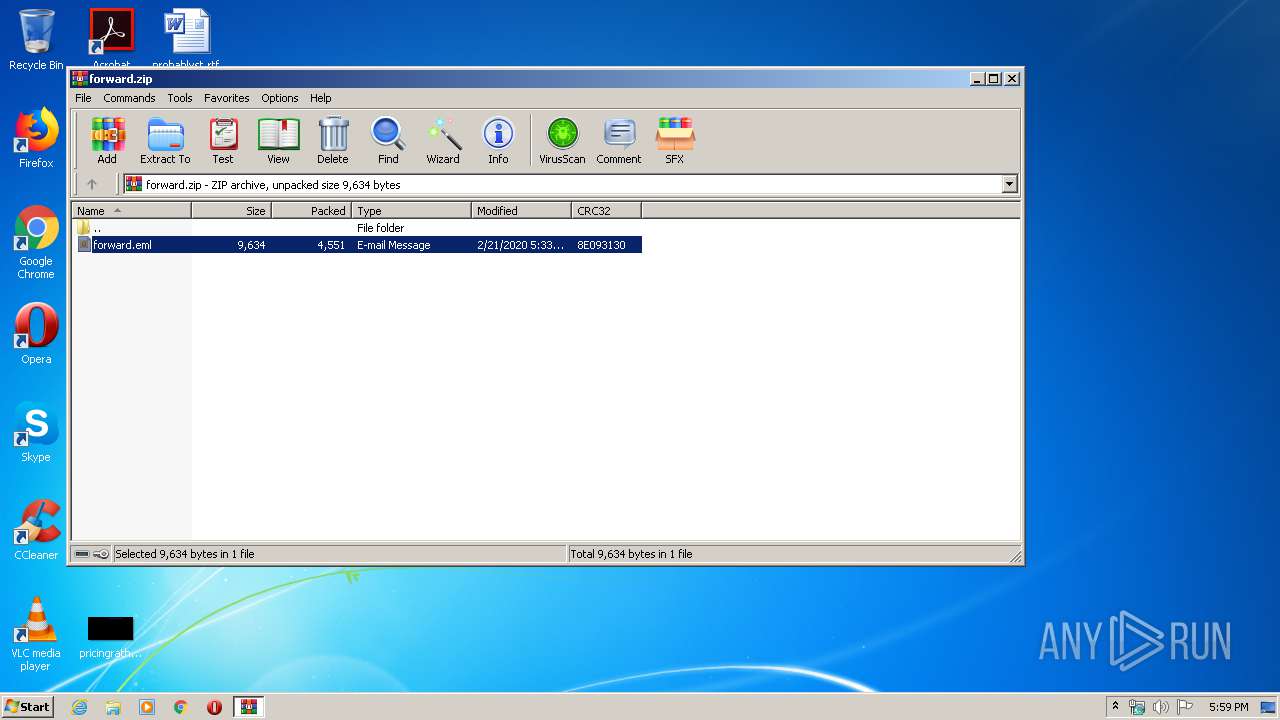
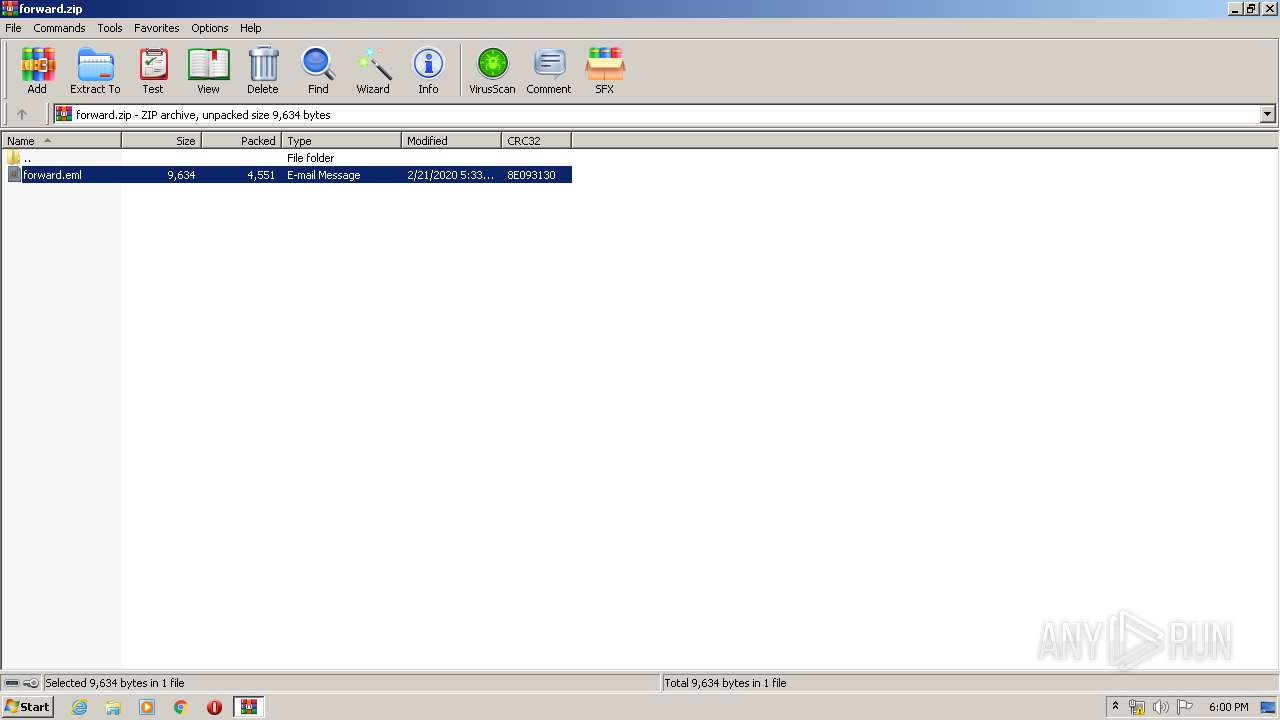
| 2876 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\forward.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
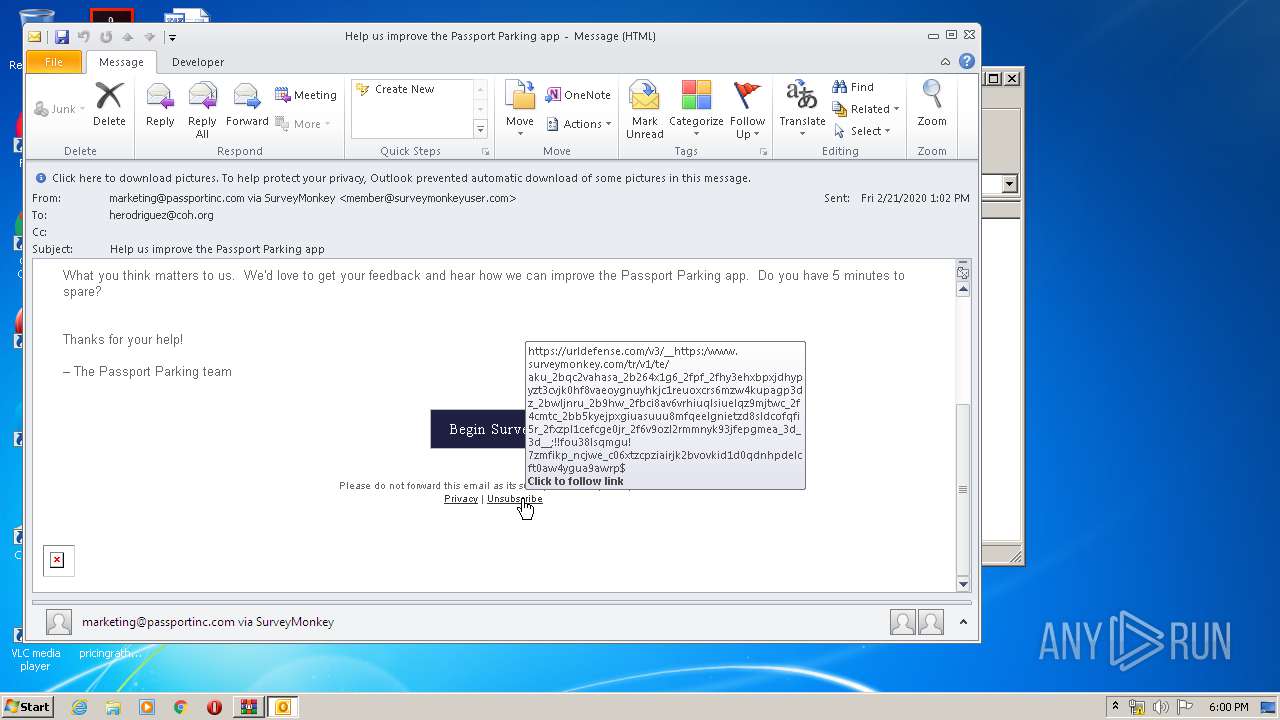
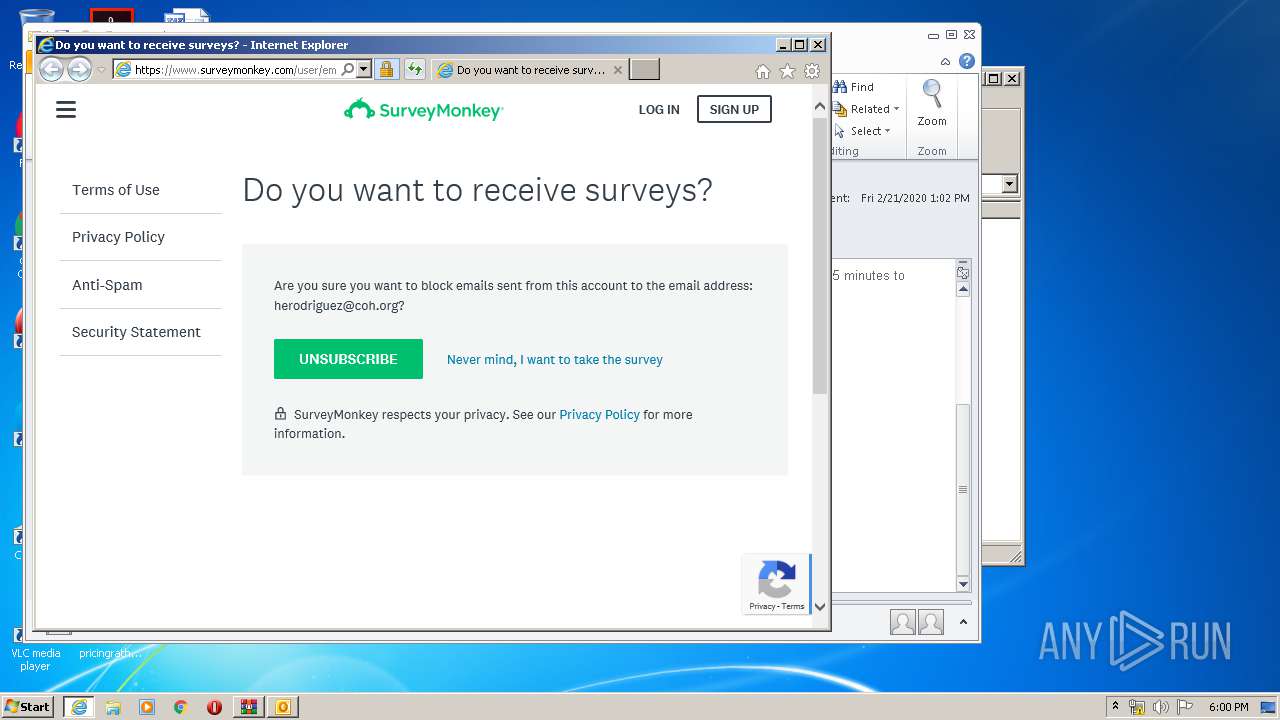
| 3052 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.com/v3/__https:/www.surveymonkey.com/tr/v1/te/akU_2BQc2vAhAsa_2B264x1g6_2FpF_2Fhy3EhxbpxJDHYpYZT3CvJK0hF8VaeoYgNuYHKjC1rEUOxcRs6mZw4kUPaGP3dZ_2BwLJNRU_2B9hw_2FBci8aV6vrhiUqlSiUElQZ9mJtwc_2F4CMtC_2Bb5KYeJpXgiuaSuuu8mfqEElgnIeTzD8SLDcOfqfi5R_2FXzpl1ceFCGE0Jr_2F6v9Ozl2RMmNYK93JFEPGMEA_3D_3D__;!!Fou38LsQmgU!7ZMfiKP_NCJwe_C06xtZCpziairJk2BvoVkid1D0qdNhpdeLCft0aw4YguA9aWRp$ | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
7 986
Read events
2 193
Write events
4 052
Delete events
1 741
Modification events
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\forward.zip | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2876) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2460) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2460) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
Executable files
0
Suspicious files
61
Text files
69
Unknown types
35
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2460 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR14A4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3052 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7EC8.tmp | — | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7EC9.tmp | — | |
MD5:— | SHA256:— | |||
| 2460 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2460 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2876 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2876.49842\forward.eml | eml | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_AD319D6DA1A11BC83AC8B4E4D3638231 | der | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5EEJNDKY.txt | — | |
MD5:— | SHA256:— | |||
| 2736 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5V5DZYFV.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
54
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2460 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJaiu8Zb34NbCEEshrmcCs%3D | US | der | 471 b | whitelisted |
2736 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCgdZM8AVzzKAgAAAAALnDU | US | der | 472 b | whitelisted |
2736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.thawte.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSFvn094QJ%2BcWGTwWWEy%2BBXPZkW8AQUo8heZVTlMHjBBeoHCmpZzLn%2B3loCEA53cAOejRmtccb8jN4MVZM%3D | US | der | 471 b | whitelisted |
2736 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2736 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkbwjNvPLFRm7zMB3V80 | US | der | 1.49 Kb | whitelisted |
2736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
2736 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2736 | iexplore.exe | GET | 200 | 172.217.22.99:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDu3mVgzTXArwIAAAAAWXG3 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2736 | iexplore.exe | 52.204.90.22:443 | urldefense.com | Amazon.com, Inc. | US | suspicious |
2460 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3052 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
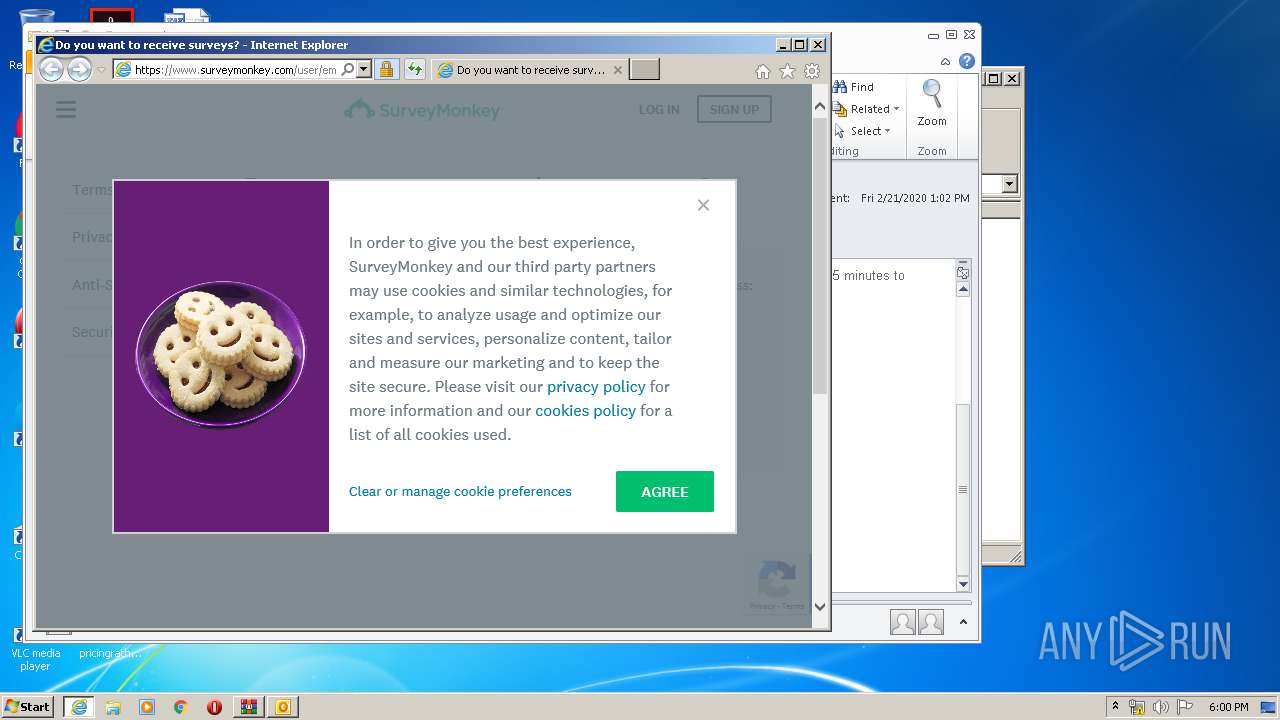
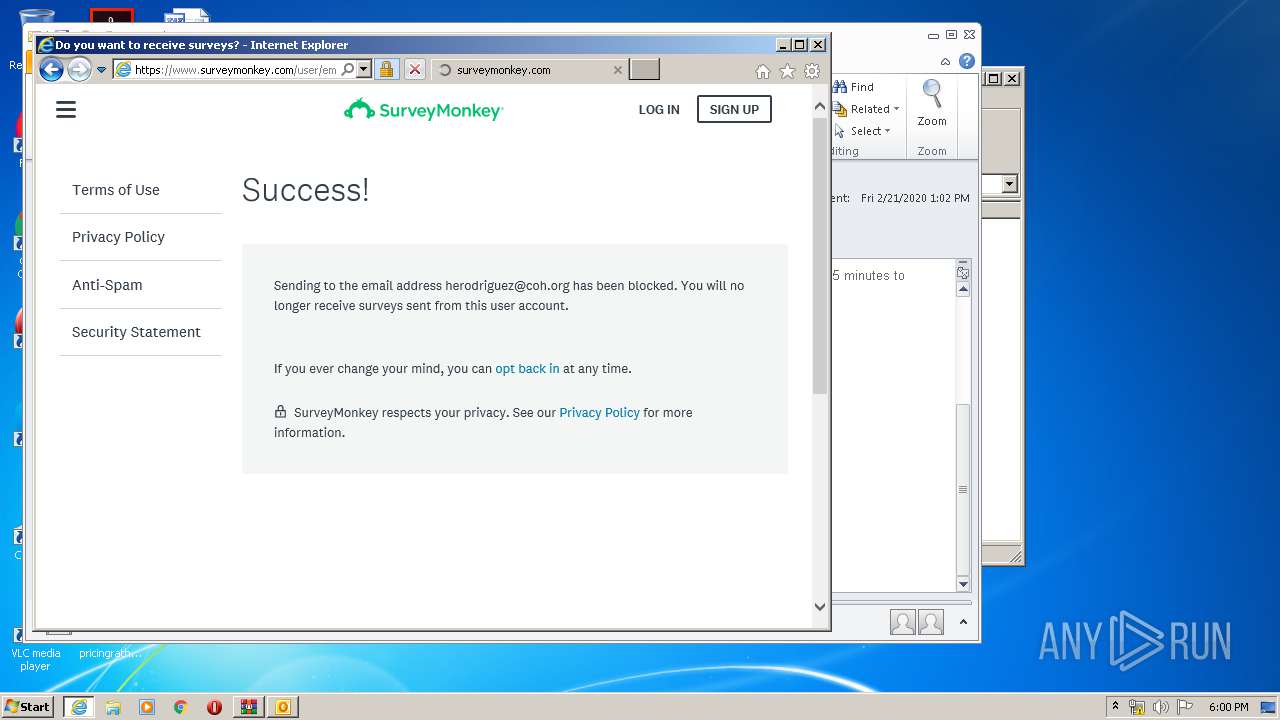
2736 | iexplore.exe | 64.191.16.50:443 | www.surveymonkey.com | SurveyMonkey Inc. | US | suspicious |
2736 | iexplore.exe | 2.16.181.24:443 | secure.surveymonkey.com | Akamai International B.V. | — | whitelisted |
2736 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2736 | iexplore.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
2736 | iexplore.exe | 2.16.187.11:443 | cdn.smassets.net | Akamai International B.V. | — | whitelisted |
2736 | iexplore.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2736 | iexplore.exe | 216.58.207.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
urldefense.com |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.thawte.com |
| whitelisted |
www.surveymonkey.com |
| whitelisted |
secure.surveymonkey.com |
| shared |
cdn.smassets.net |
| shared |
www.google.com |
| malicious |