analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| File name: | Sample.exe |
| Full analysis: | https://app.any.run/tasks/fcce1eaf-9c8e-4f86-8516-be4429469bab |
| Verdict: | Malicious activity |
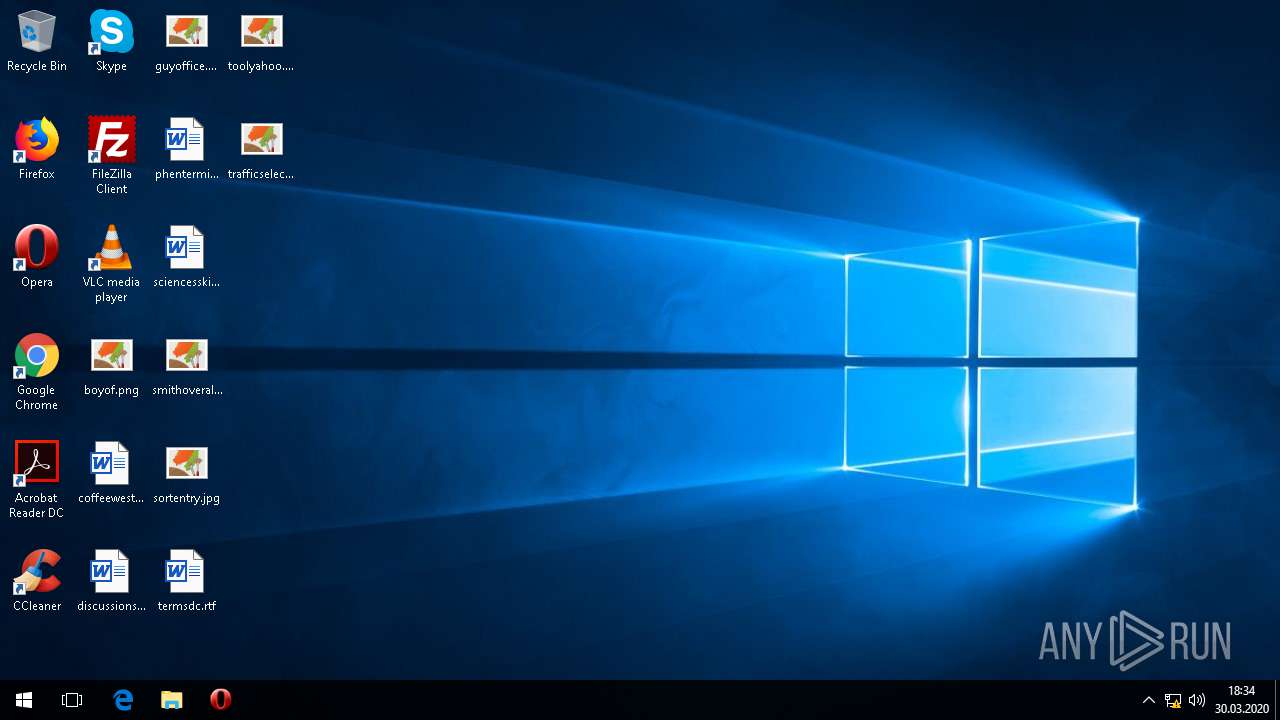
| Analysis date: | March 30, 2020, 18:34:33 |
| OS: | Windows 10 Professional (build: 16299, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 860887EDA7F501AE0EB217D141E6A3E9 |
| SHA1: | 1C72B2C43959C95BA03E91DE78B74AE87B609581 |
| SHA256: | 302B22EF958F04EEEF47EAEF2FE2D2FD062A17C16683EC8F2CF0B899F19C2ACB |
| SSDEEP: | 3072:kJq/4ppTq9xAkLG3uGN8D3Wx78HA6RO3f1cHr7IE0IVvsLexyHwIC2y:kJPTqDAkAuGK+7mA6RO3Ctf |
MALICIOUS
Loads the Task Scheduler COM API
- svchost.exe (PID: 196)
Uses SVCHOST.EXE for hidden code execution
- Sample.exe (PID: 1208)
Loads dropped or rewritten executable
- svchost.exe (PID: 196)
Actions looks like stealing of personal data
- svchost.exe (PID: 196)
SUSPICIOUS
Executable content was dropped or overwritten
- svchost.exe (PID: 196)
Starts CMD.EXE for commands execution
- svchost.exe (PID: 196)
Uses SYSTEMINFO.EXE to read environment
- svchost.exe (PID: 196)
Uses WMIC.EXE to obtain a list of AntiViruses
- svchost.exe (PID: 196)
Starts application with an unusual extension
- cmd.exe (PID: 780)
Reads the cookies of Google Chrome
- svchost.exe (PID: 196)
Uses IPCONFIG.EXE to discover IP address
- svchost.exe (PID: 196)
Uses WMIC.EXE to obtain a system information
- svchost.exe (PID: 196)
Executed via COM
- TiWorker.exe (PID: 4016)
Starts NET.EXE for network exploration
- svchost.exe (PID: 196)
INFO
Reads the software policy settings
- svchost.exe (PID: 196)
- Sample.exe (PID: 1208)
Reads settings of System Certificates
- svchost.exe (PID: 196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:03:30 17:25:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 114688 |
| InitializedDataSize: | 73728 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa4eb |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.69.27 |
| ProductVersionNumber: | 0.0.69.27 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Wheelin sch choosenothing observe |
| CompanyName: | www.onCorspace.com |
| FileDescription: | White Wingshoe paintshow |
| FileVersion: | 0.0.69.27 |
| InternalName: | Afra.exe |
| LegalCopyright: | Copyright © 2008-2013 Numeralfun Veryconsider |
| LegalTrademarks: | White Wingshoe paintshow |
| OriginalFileName: | Afra.exe |
| ProductName: | White Wingshoe paintshow |
| ProductVersion: | 0.0.69.27 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Mar-2006 15:25:56 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | Wheelin sch choosenothing observe |
| CompanyName: | www.onCorspace.com |
| FileDescription: | White Wingshoe paintshow |
| FileVersion: | 0.0.69.27 |
| InternalName: | Afra.exe |
| LegalCopyright: | Copyright © 2008-2013 Numeralfun Veryconsider |
| LegalTrademarks: | White Wingshoe paintshow |
| OriginalFilename: | Afra.exe |
| ProductName: | White Wingshoe paintshow |
| ProductVersion: | 0.0.69.27 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Mar-2006 15:25:56 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001BDBD | 0x0001C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71935 |
.rdata | 0x0001D000 | 0x00008052 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20407 |
.data | 0x00026000 | 0x0001BCD4 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.25658 |
.rsrc | 0x00042000 | 0x00000C9C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.65587 |
.reloc | 0x00043000 | 0x00004E00 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.56469 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.65542 | 86 | Latin 1 / Western European | English - United States | RT_MANIFEST |
16 | 6.04779 | 600 | Latin 1 / Western European | UNKNOWN | BINARES |
17 | 6.02563 | 600 | Latin 1 / Western European | UNKNOWN | BINARES |
18 | 6.03144 | 596 | Latin 1 / Western European | UNKNOWN | BINARES |
Imports
GDI32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
USER32.dll |
VERSION.dll |
WINSPOOL.DRV (delay-loaded) |
Total processes
73
Monitored processes
23
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 1208 | "C:\Users\admin\AppData\Roaming\Sample.exe" | C:\Users\admin\AppData\Roaming\Sample.exe | explorer.exe | |
User: admin Company: www.onCorspace.com Integrity Level: MEDIUM Description: White Wingshoe paintshow Exit code: 0 Version: 0.0.69.27 | ||||
| 196 | C:\windows\system32\svchost.exe | C:\windows\system32\svchost.exe | Sample.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Version: 10.0.16299.15 (WinBuild.160101.0800) | ||||
| 780 | cmd /c chcp | C:\windows\system32\cmd.exe | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) | ||||
| 2352 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) | ||||
| 804 | chcp | C:\WINDOWS\system32\chcp.com | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) | ||||
| 2116 | WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntiVirusProduct Get * /Format:List | C:\WINDOWS\System32\Wbem\WMIC.exe | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) | ||||
| 1404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | — | WMIC.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) | ||||
| 3536 | ipconfig /all | C:\windows\system32\ipconfig.exe | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) | ||||
| 2204 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\WINDOWS\system32\conhost.exe | — | ipconfig.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) | ||||
| 3496 | systeminfo | C:\windows\system32\systeminfo.exe | — | svchost.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Displays system information Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) | ||||
Total events
435
Read events
393
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 196 | svchost.exe | C:\Users\admin\AppData\Local\Temp\caor.tmp | — | |
MD5:— | SHA256:— | |||
| 196 | svchost.exe | C:\Users\admin\AppData\Local\Temp\Yupu3.tmp | — | |
MD5:— | SHA256:— | |||
| 196 | svchost.exe | C:\Users\admin\AppData\Local\Temp\Yupu3.tmp-shm | — | |
MD5:— | SHA256:— | |||
| 196 | svchost.exe | C:\Users\admin\AppData\Local\Temp\tuel64.tmp | — | |
MD5:— | SHA256:— | |||
| 196 | svchost.exe | C:\Users\admin\AppData\Local\Temp\okav3.tmp | — | |
MD5:— | SHA256:— | |||
| 196 | svchost.exe | C:\Users\admin\AppData\Local\Temp\Ajdu.tmp | — | |
MD5:— | SHA256:— | |||
| 1208 | Sample.exe | C:\Users\admin\AppData\Local\Umudac64\{8887D924-E01D-EB51-4D80-9C1F8F0E6D53}\adabac1.png | image | |
MD5:6A44BEFDED3DA2245EF3A78E396CE5E0 | SHA256:0F9B9CBC1251667075C231DADF01D9A708C3A3206278505FC8E9CA9613A07BF8 | |||
| 4016 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:9637B1F14B0F275DD437F7FFB75F3FDF | SHA256:185CFC708681752CC7450B9D6203C3CAA1B1214F02B990C0AA826A8282B9D440 | |||
| 196 | svchost.exe | C:\Users\admin\AppData\Local\admin\uvojnn.exe | executable | |
MD5:860887EDA7F501AE0EB217D141E6A3E9 | SHA256:302B22EF958F04EEEF47EAEF2FE2D2FD062A17C16683EC8F2CF0B899F19C2ACB | |||
| 196 | svchost.exe | C:\Users\admin\AppData\Local\Temp\sqlite32.dll | executable | |
MD5:5E5BA61531D74E45B11CADB79E7394A1 | SHA256:99E91AE250C955BD403EC1A2321D6B11FCB715BDCC7CB3F63FFB46B349AFDE5C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
7
DNS requests
7
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1208 | Sample.exe | 139.60.161.88:443 | loacorecoder.club | — | US | suspicious |
196 | svchost.exe | 139.60.161.88:443 | loacorecoder.club | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
loacorecoder.club |
| suspicious |
pythonfinder.top |
| suspicious |
cosomeder.pw |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1208 | Sample.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
— | — | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
196 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
196 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
196 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
— | — | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
196 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
— | — | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
196 | svchost.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
— | — | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |