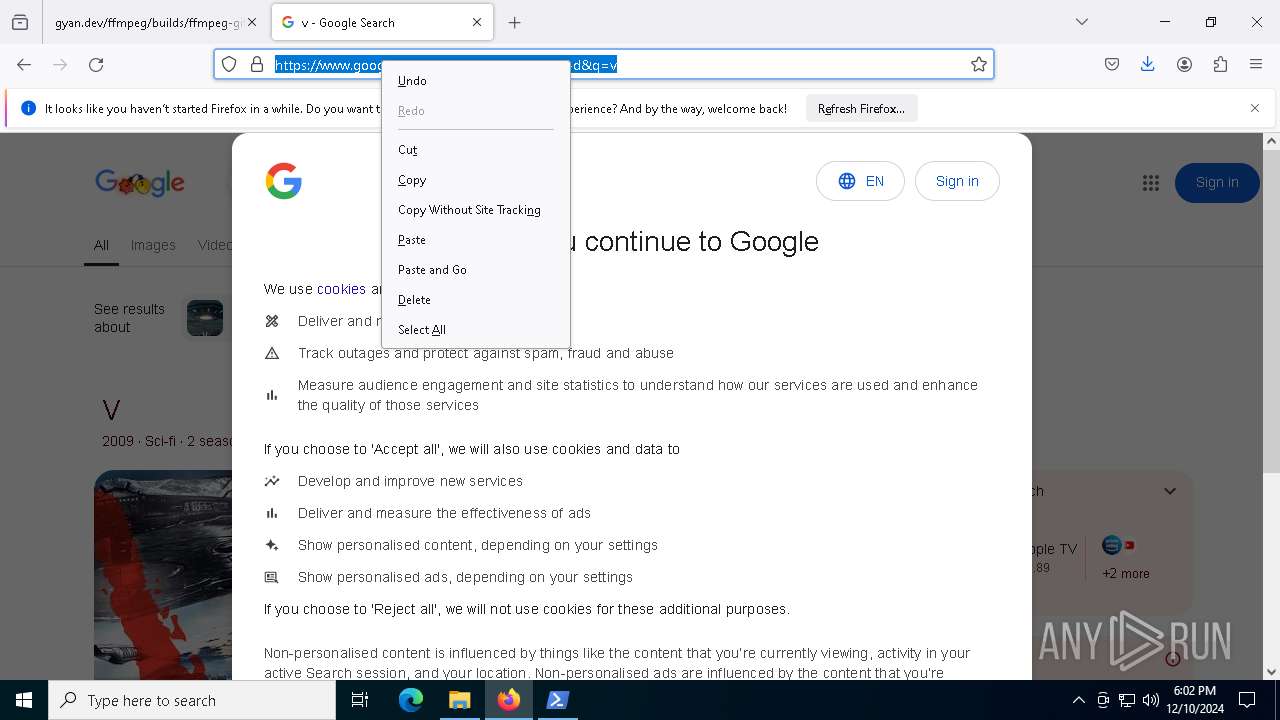
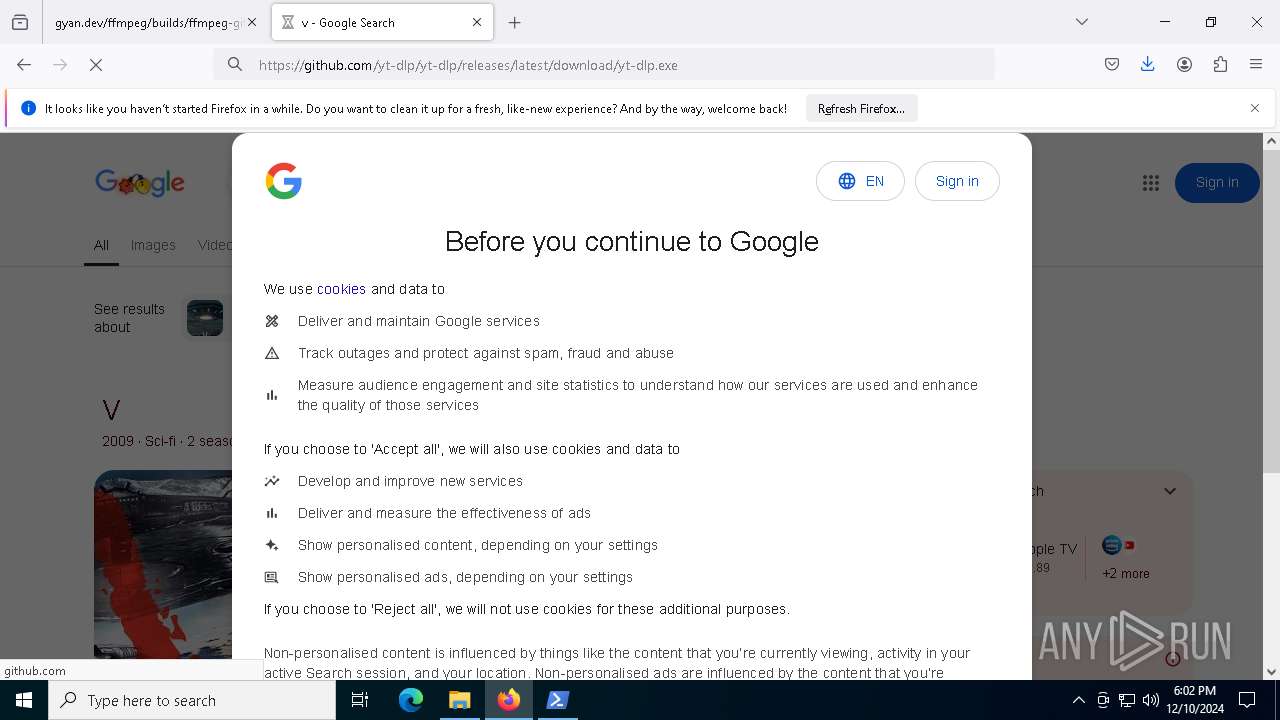
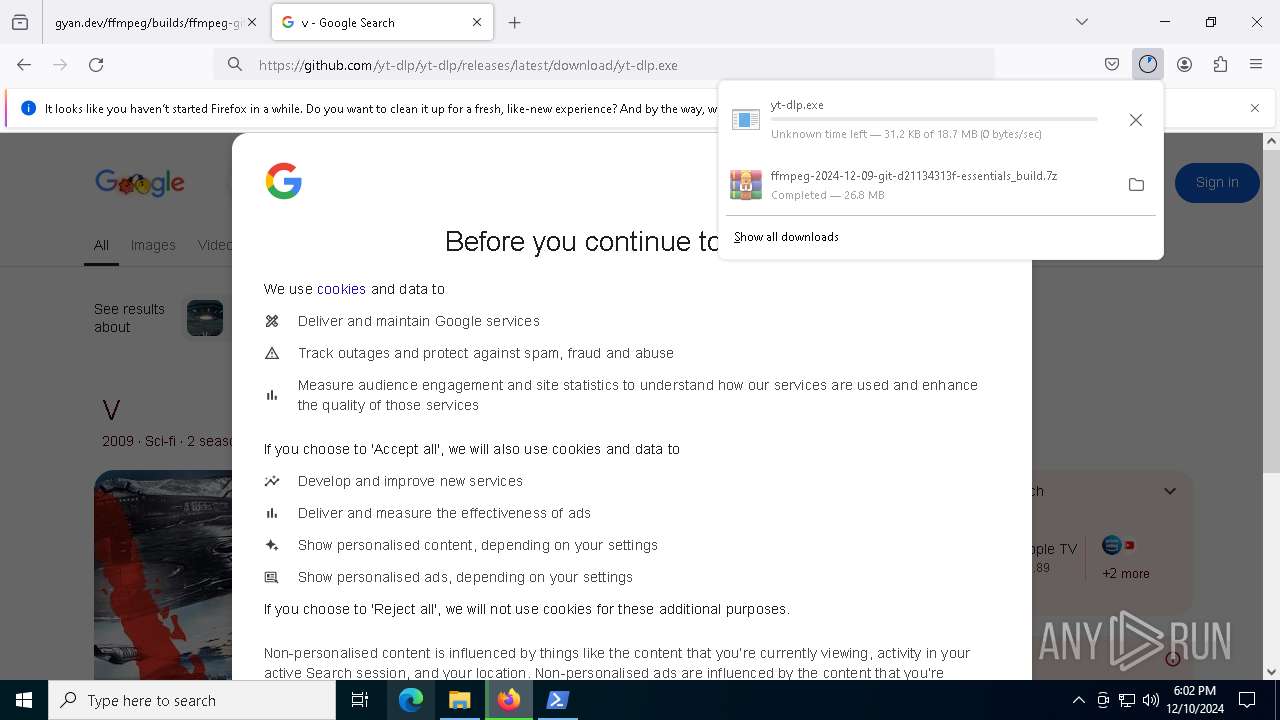
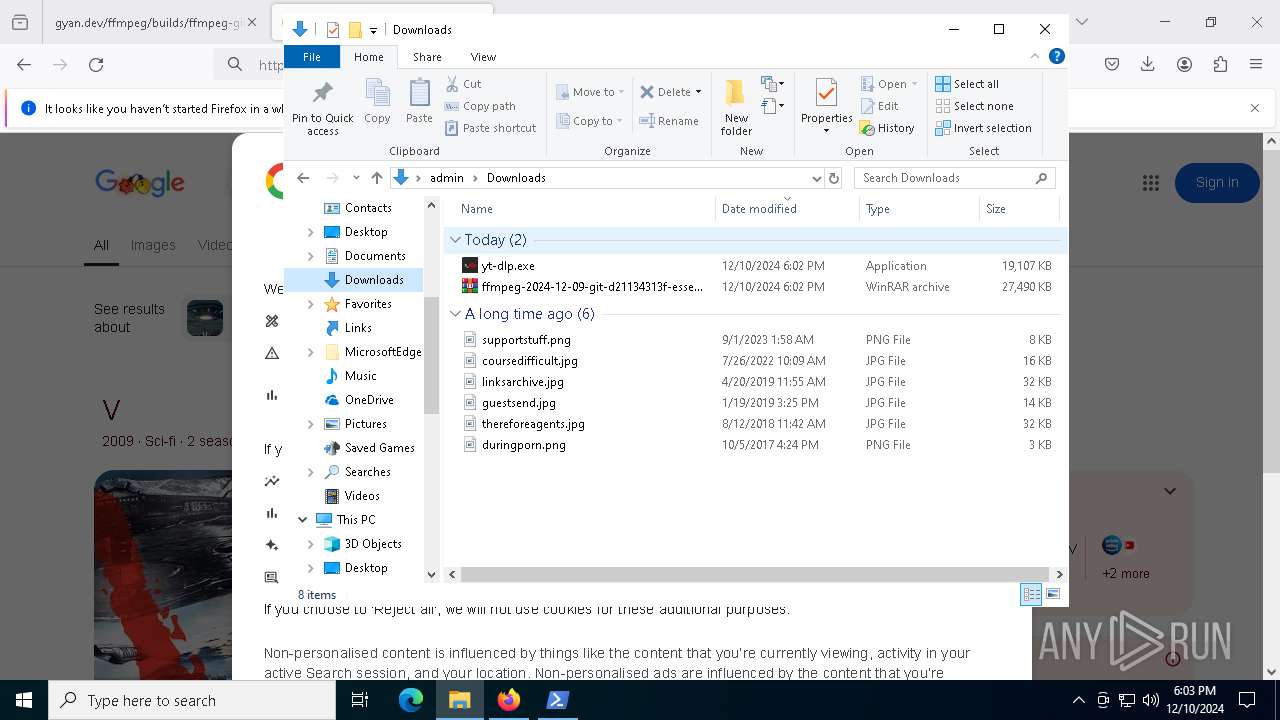
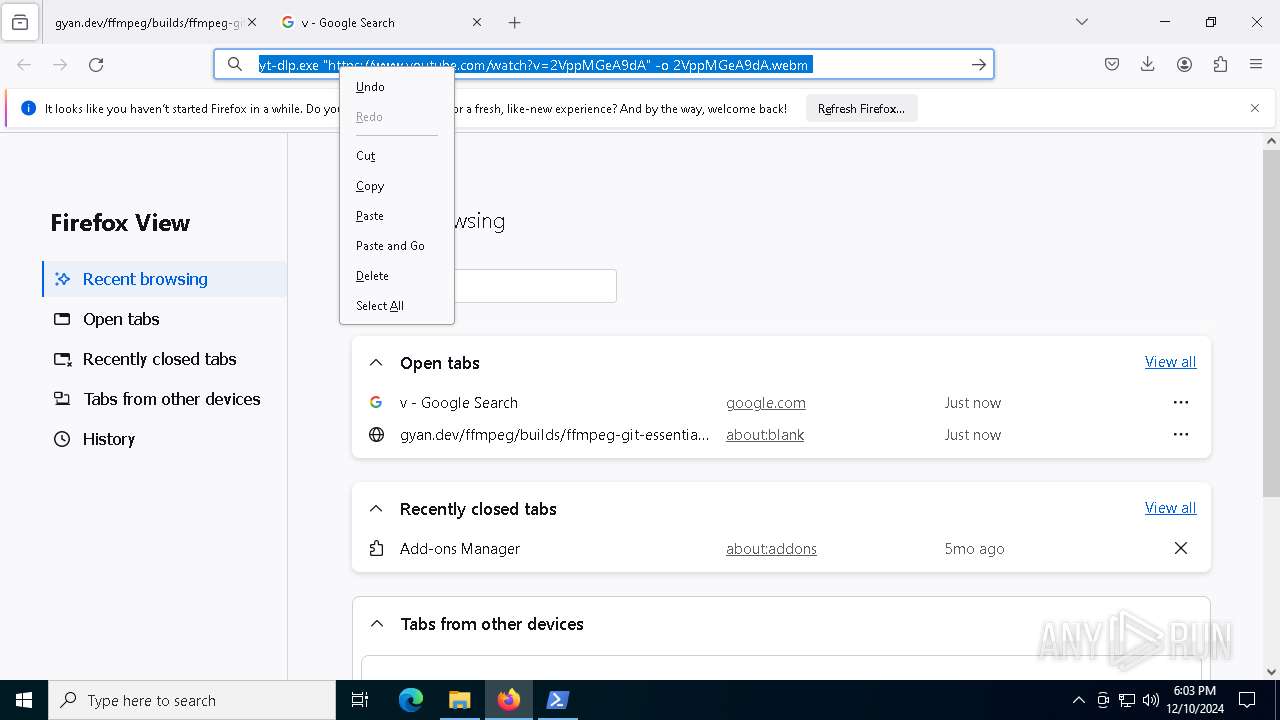
| URL: | https://www.gyan.dev/ffmpeg/builds/ffmpeg-git-essentials.7z |
| Full analysis: | https://app.any.run/tasks/53df6568-fa1f-4bbb-b8b7-5fd441ee5b92 |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2024, 18:01:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D95620E948A180AFF9C25891023E6552 |
| SHA1: | C7290D1746CE49FEB42E89003A1B6E88118069C1 |
| SHA256: | 30186161B2AB1F66D9F56F6A1B18E39B8392A6E548B40B61775F299242BB7DC5 |
| SSDEEP: | 3:N8DSL0ATuoKwIPVkf:2OLbgo |
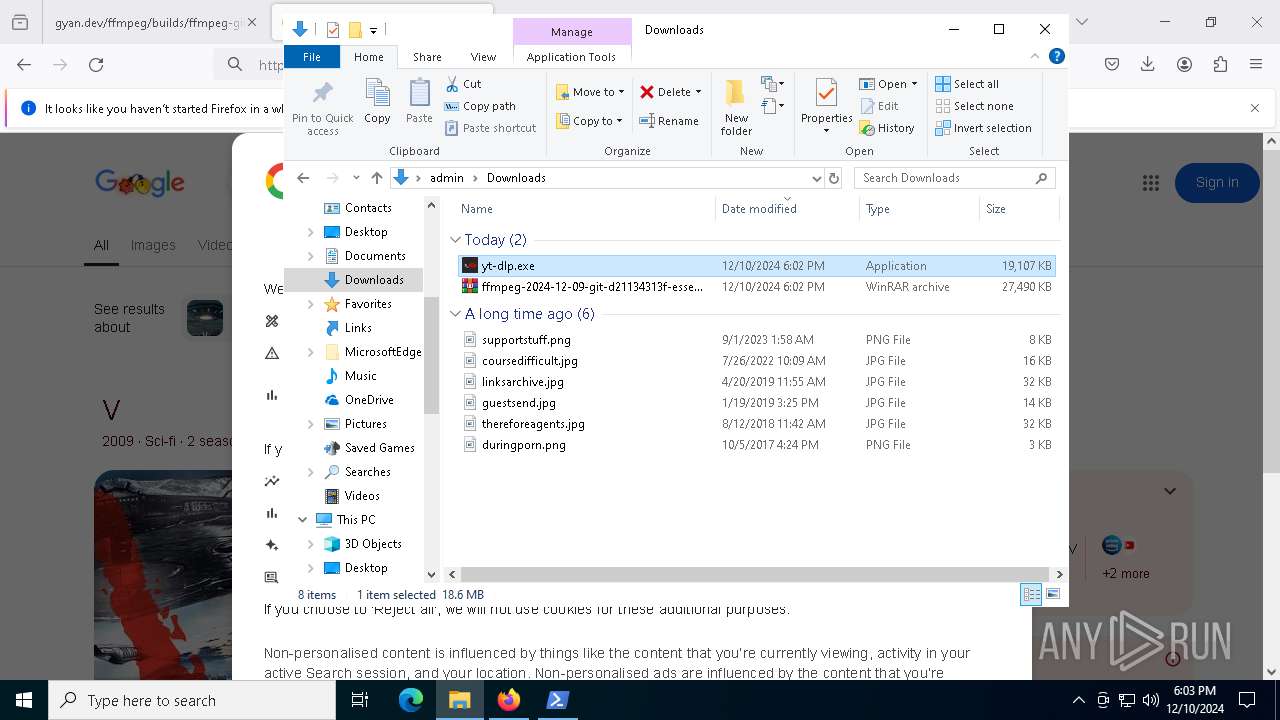
MALICIOUS
No malicious indicators.SUSPICIOUS
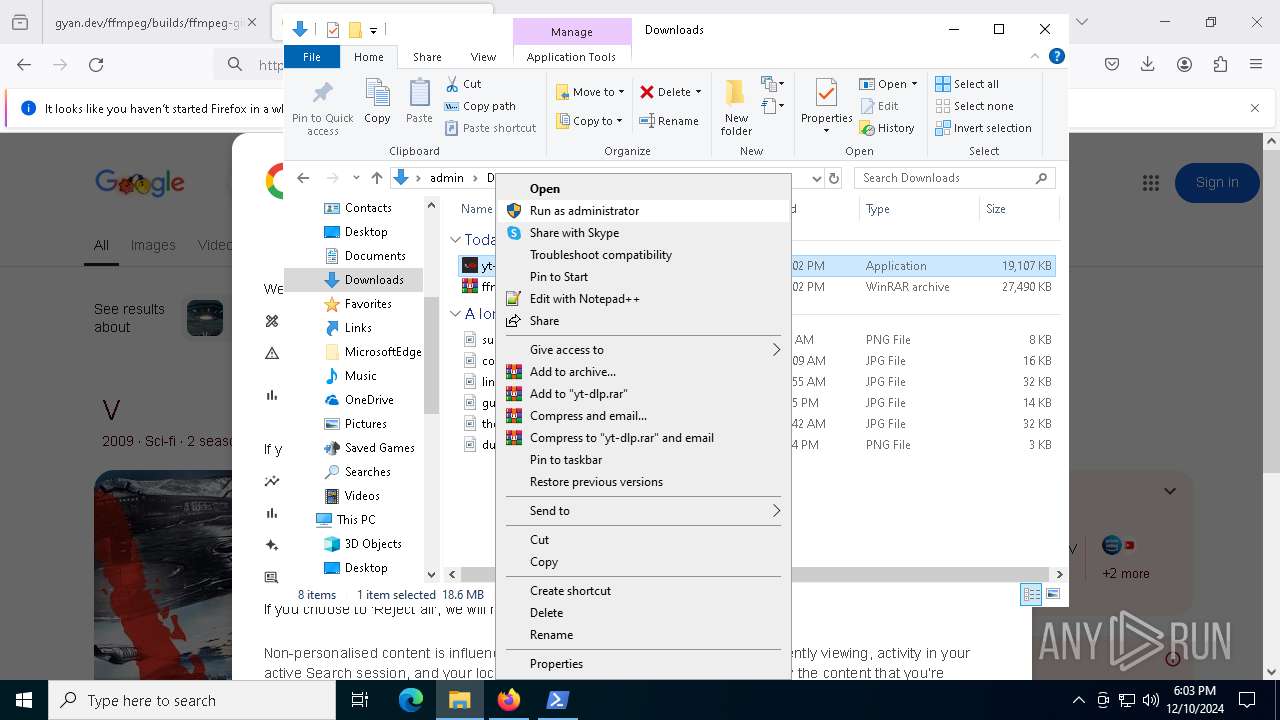
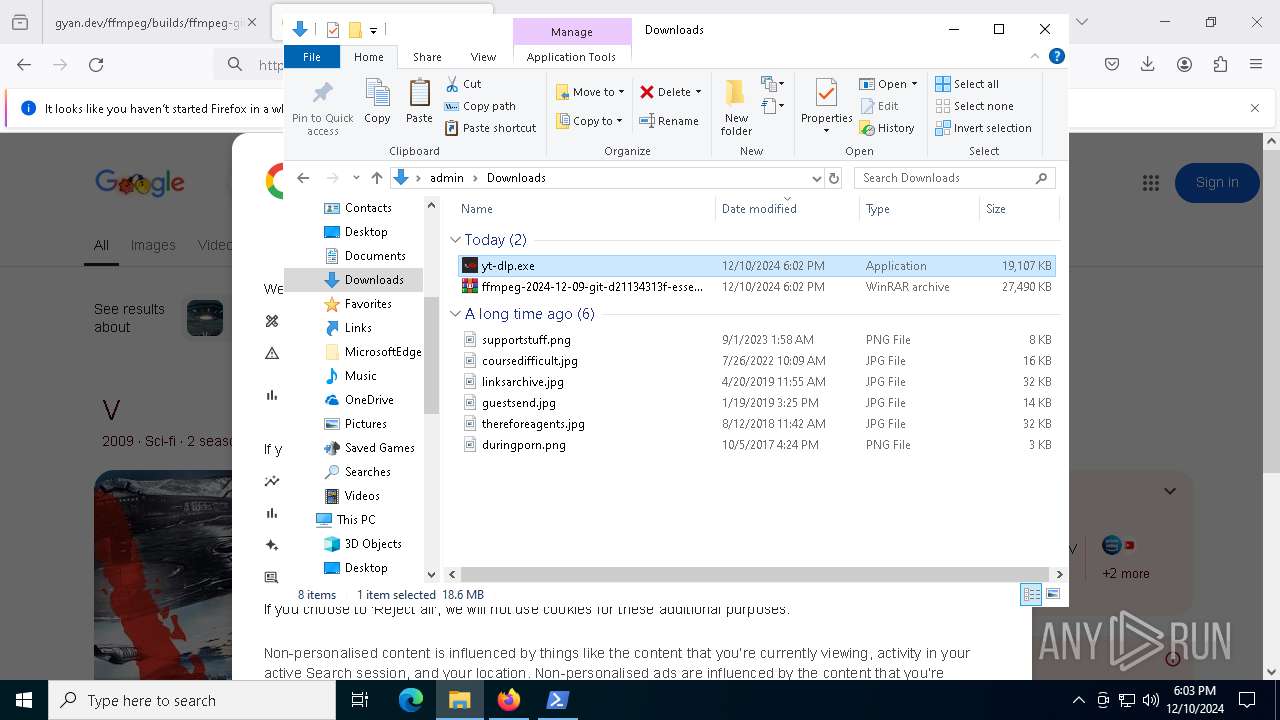
Process drops python dynamic module
- yt-dlp.exe (PID: 6404)
Process drops legitimate windows executable
- yt-dlp.exe (PID: 6404)
Executable content was dropped or overwritten
- yt-dlp.exe (PID: 6404)
The process drops C-runtime libraries
- yt-dlp.exe (PID: 6404)
Application launched itself
- yt-dlp.exe (PID: 6404)
Starts CMD.EXE for commands execution
- yt-dlp.exe (PID: 5748)
Loads Python modules
- yt-dlp.exe (PID: 5748)
Found regular expressions for crypto-addresses (YARA)
- yt-dlp.exe (PID: 5748)
INFO
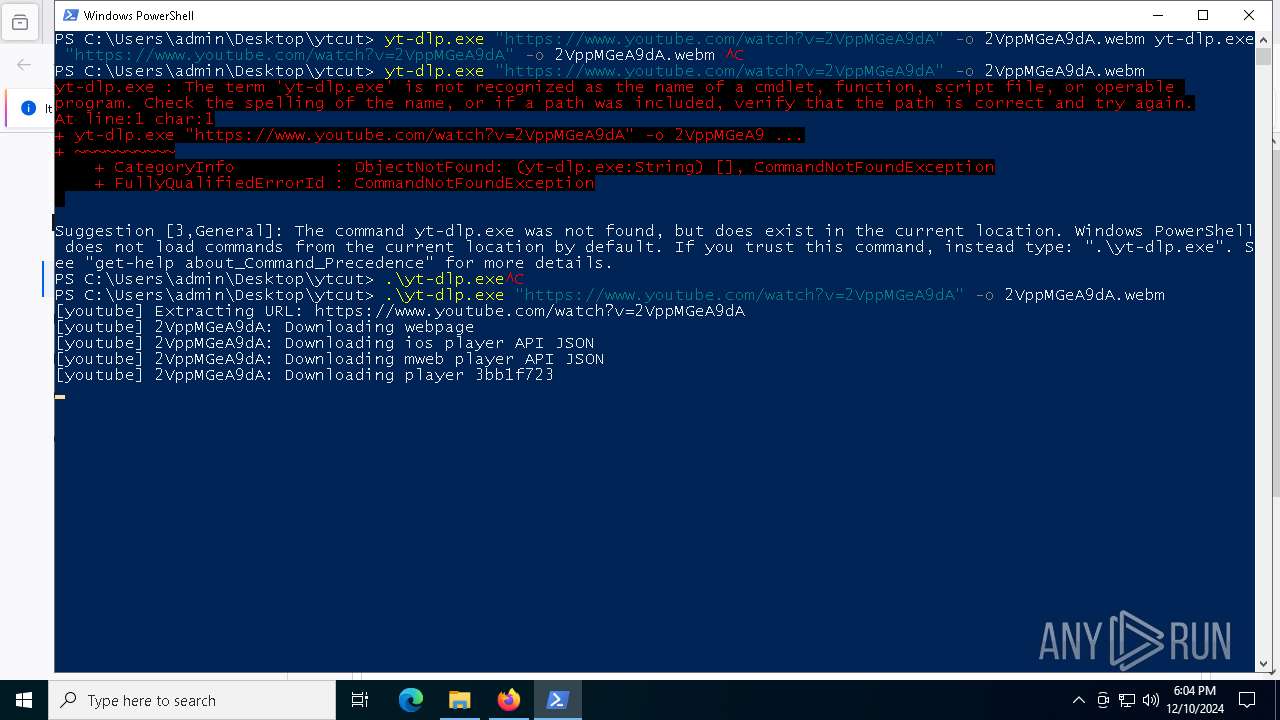
The process uses the downloaded file
- powershell.exe (PID: 6196)
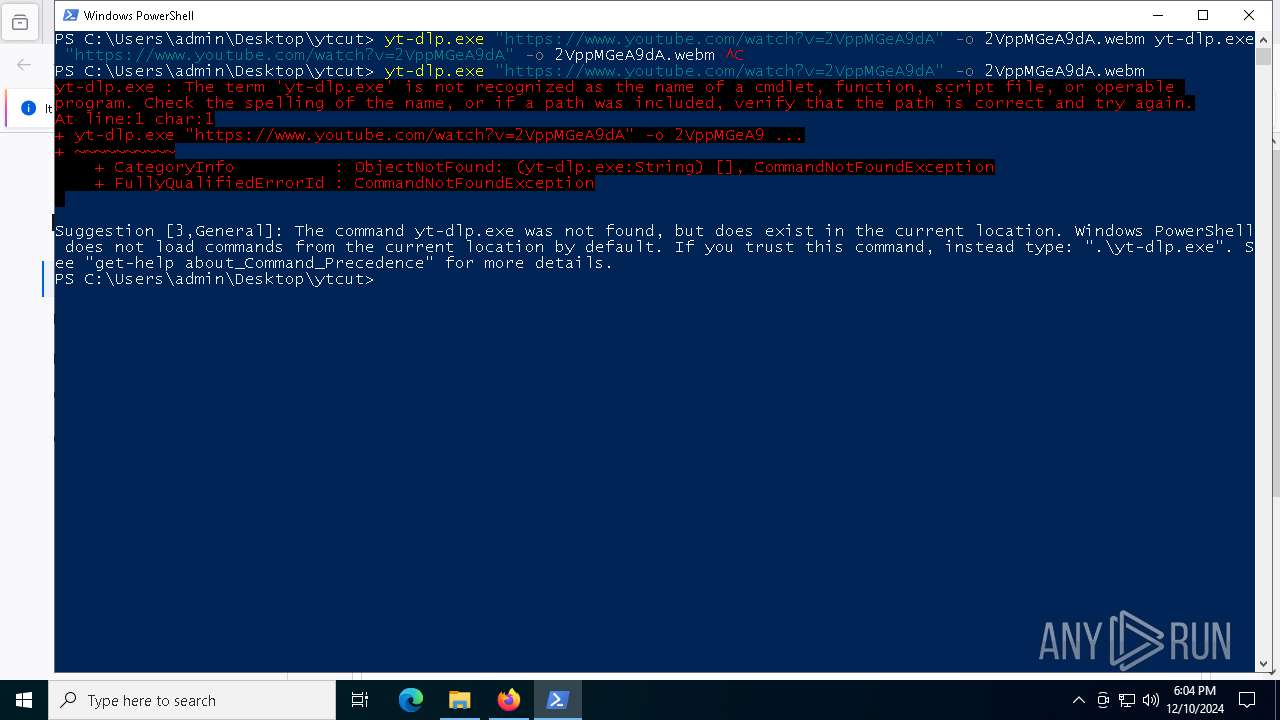
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6196)
Create files in a temporary directory
- yt-dlp.exe (PID: 6404)
The sample compiled with english language support
- yt-dlp.exe (PID: 6404)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6196)
Checks supported languages
- yt-dlp.exe (PID: 5748)
- ffmpeg.exe (PID: 7704)
Reads the machine GUID from the registry
- yt-dlp.exe (PID: 5748)
Checks operating system version
- yt-dlp.exe (PID: 5748)
Checks proxy server information
- yt-dlp.exe (PID: 5748)
Reads the computer name
- yt-dlp.exe (PID: 5748)
PyInstaller has been detected (YARA)
- yt-dlp.exe (PID: 6404)
- yt-dlp.exe (PID: 5748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
145
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3612 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | yt-dlp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3984 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4136 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | yt-dlp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\System32\cmd.exe | — | yt-dlp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
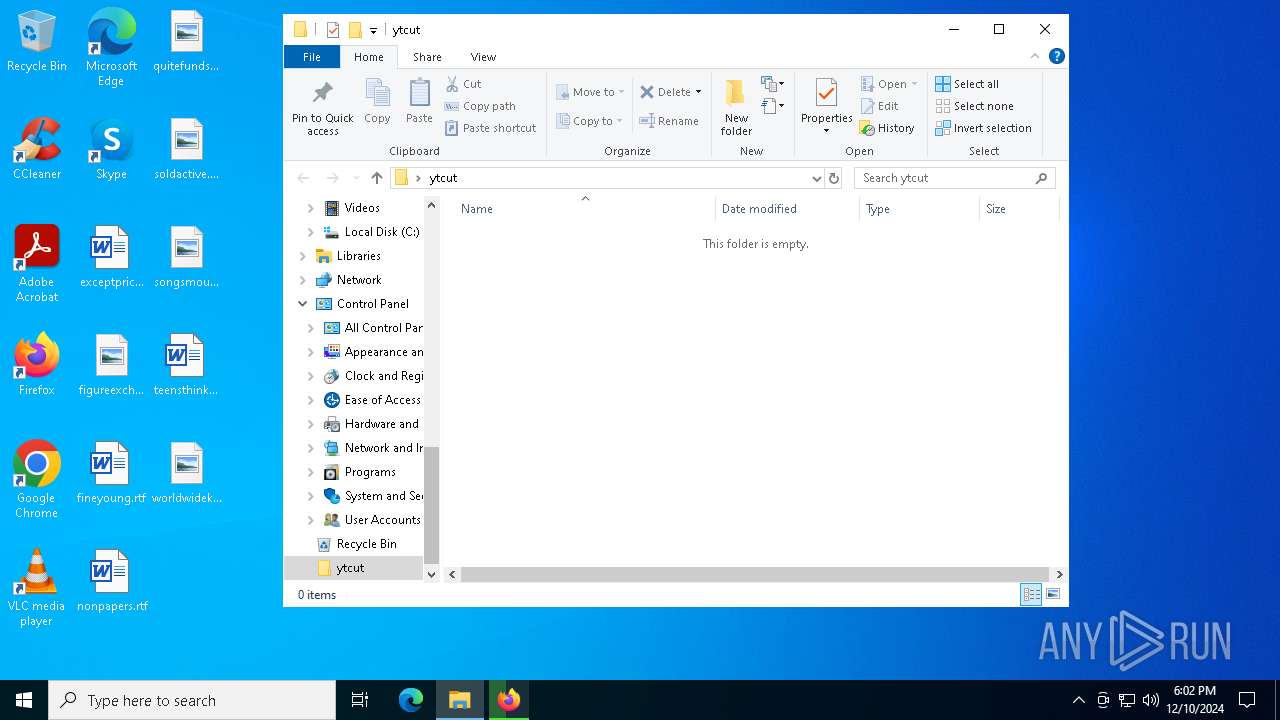
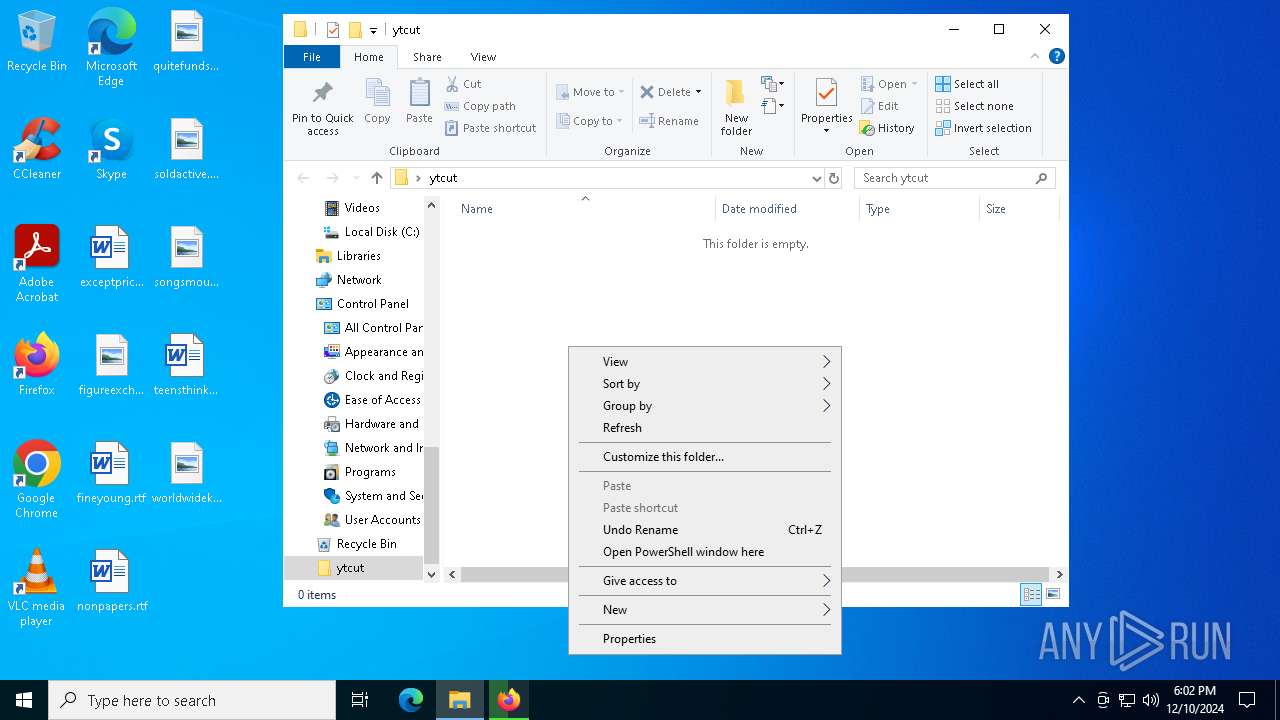
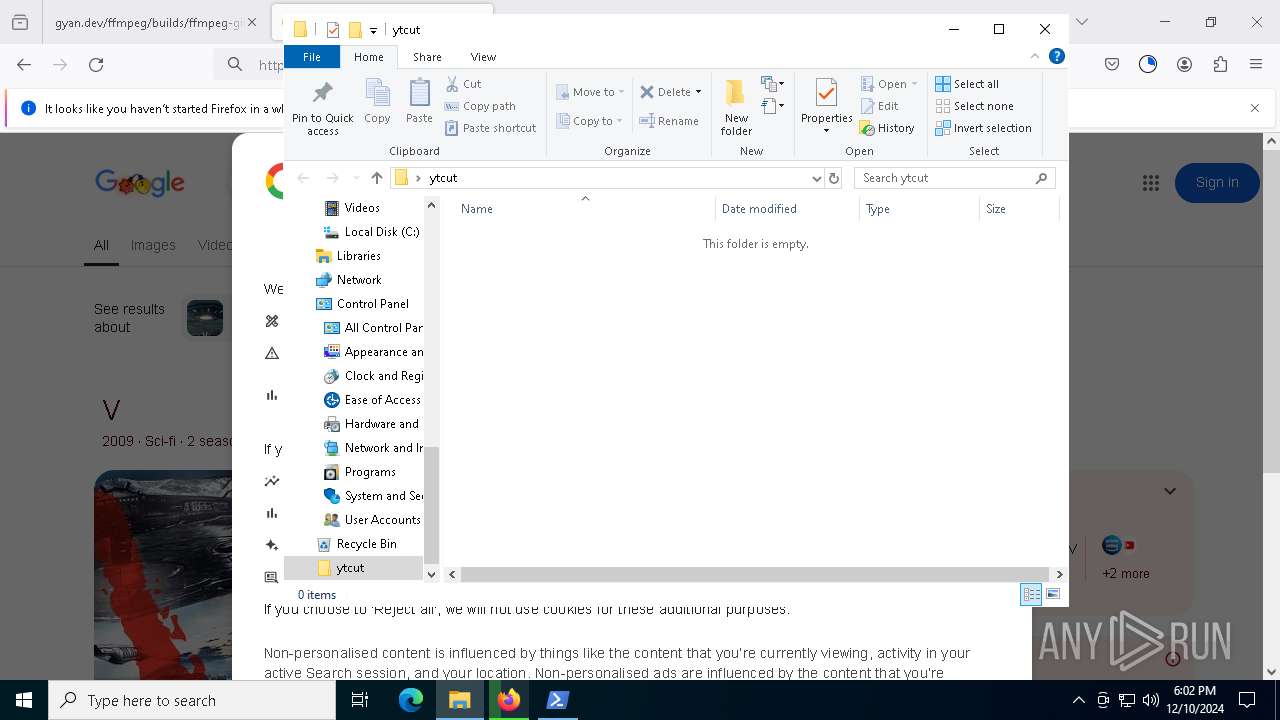
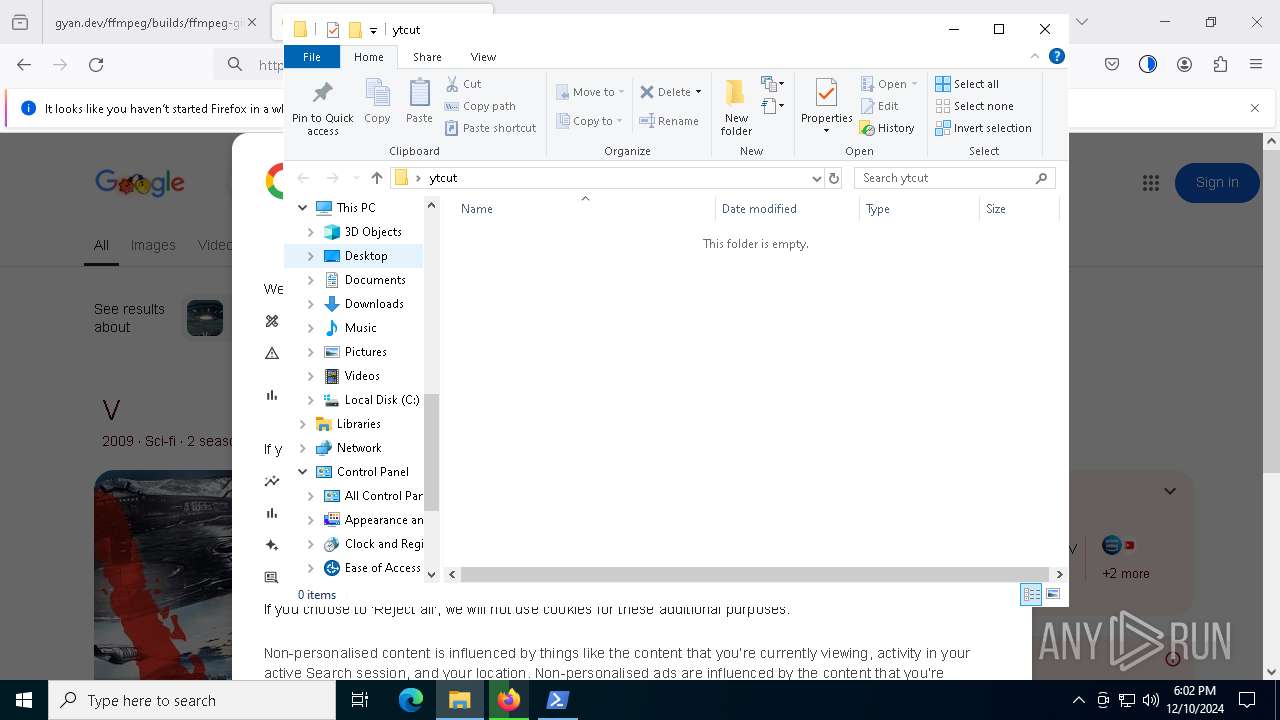
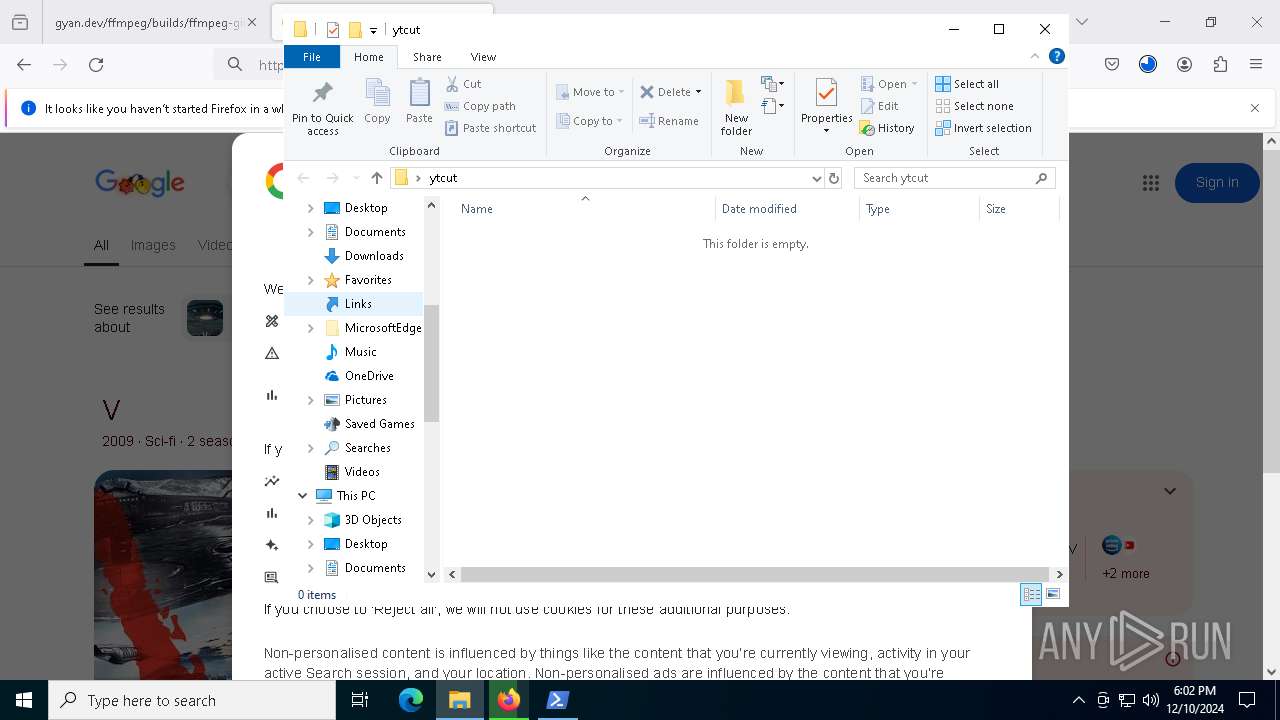
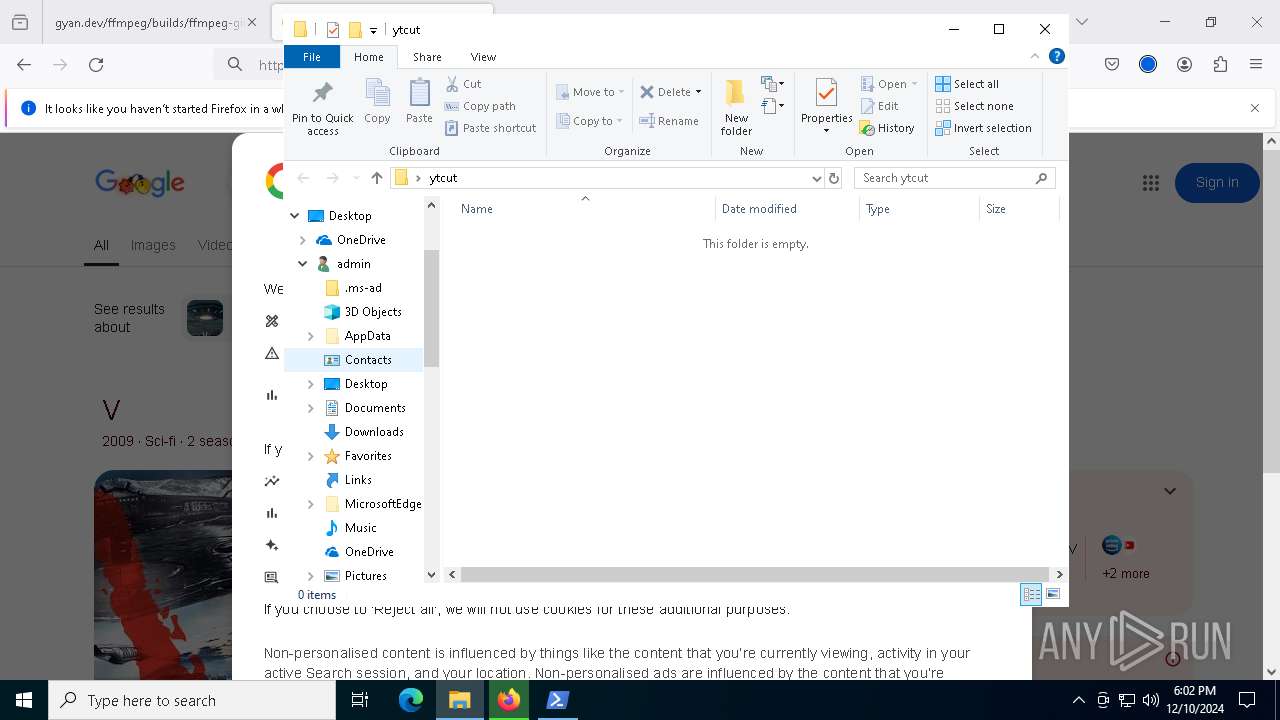
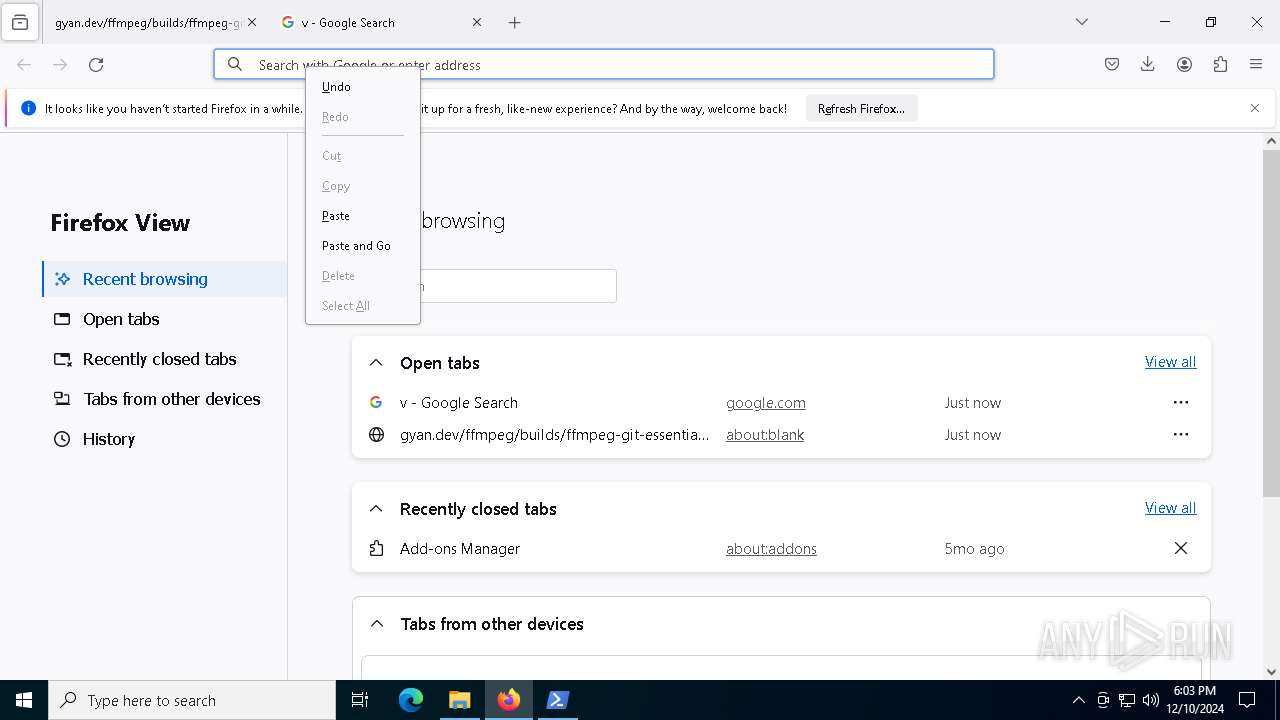
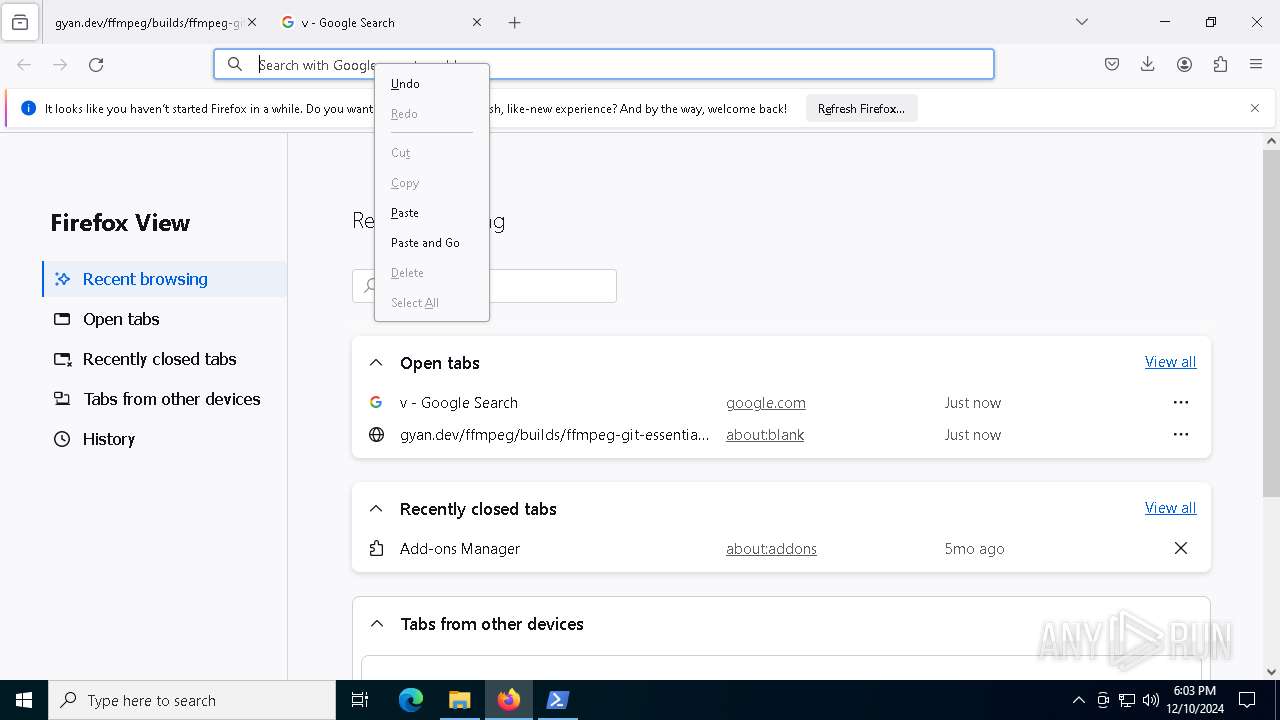
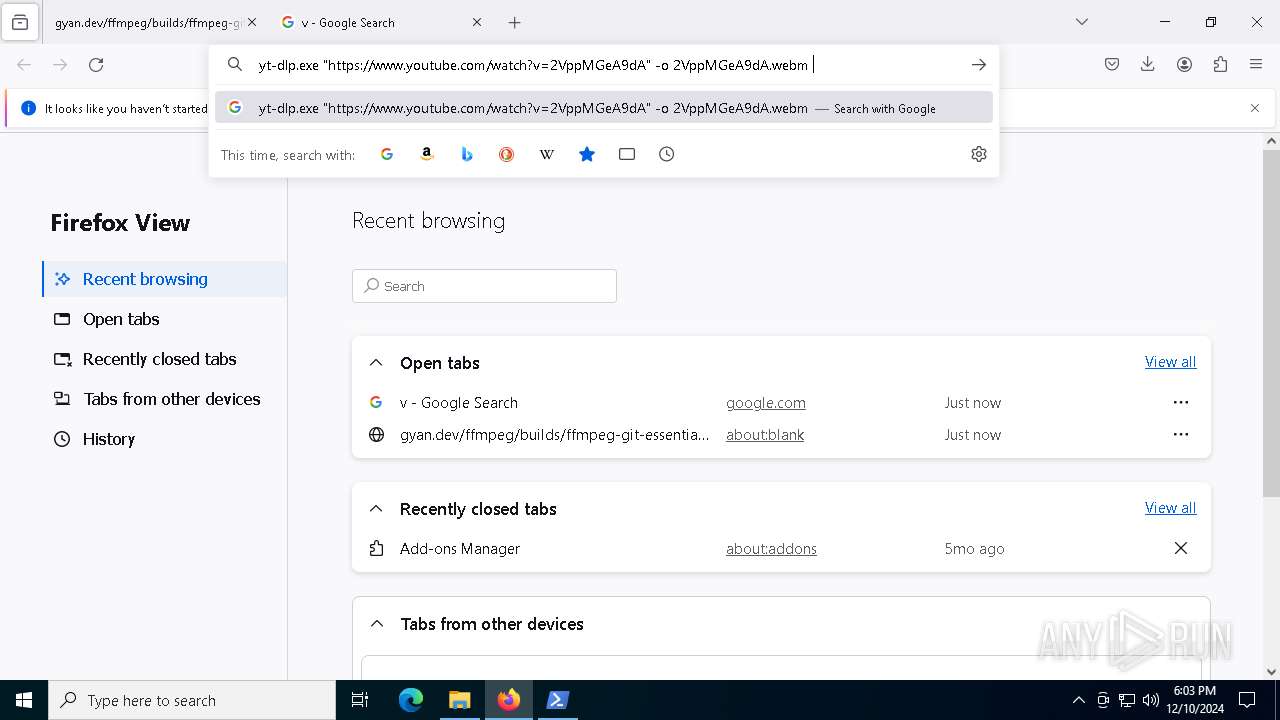
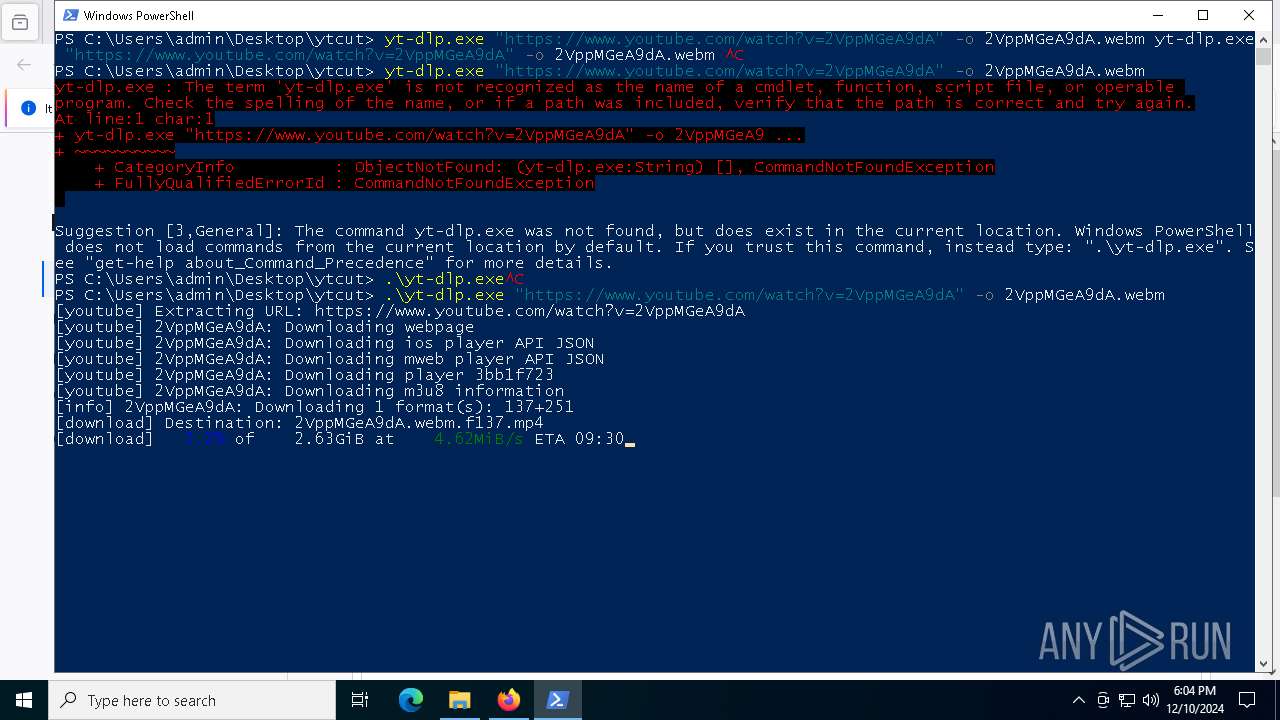
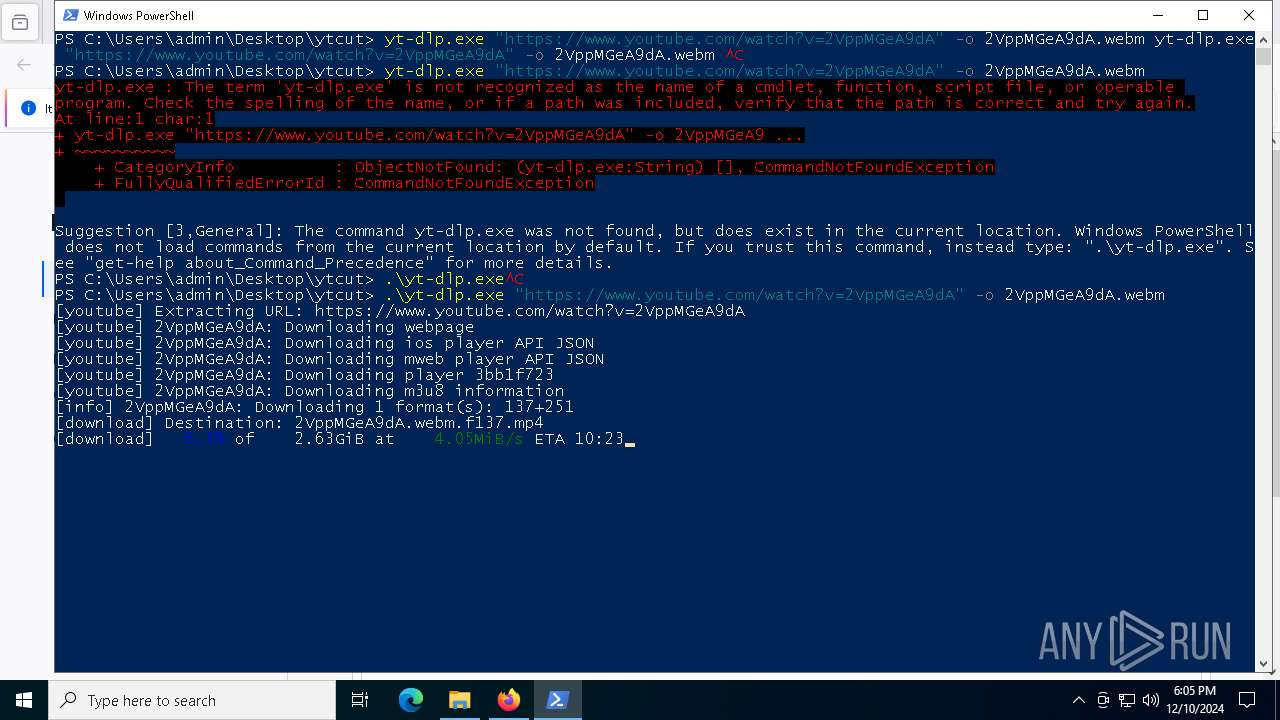
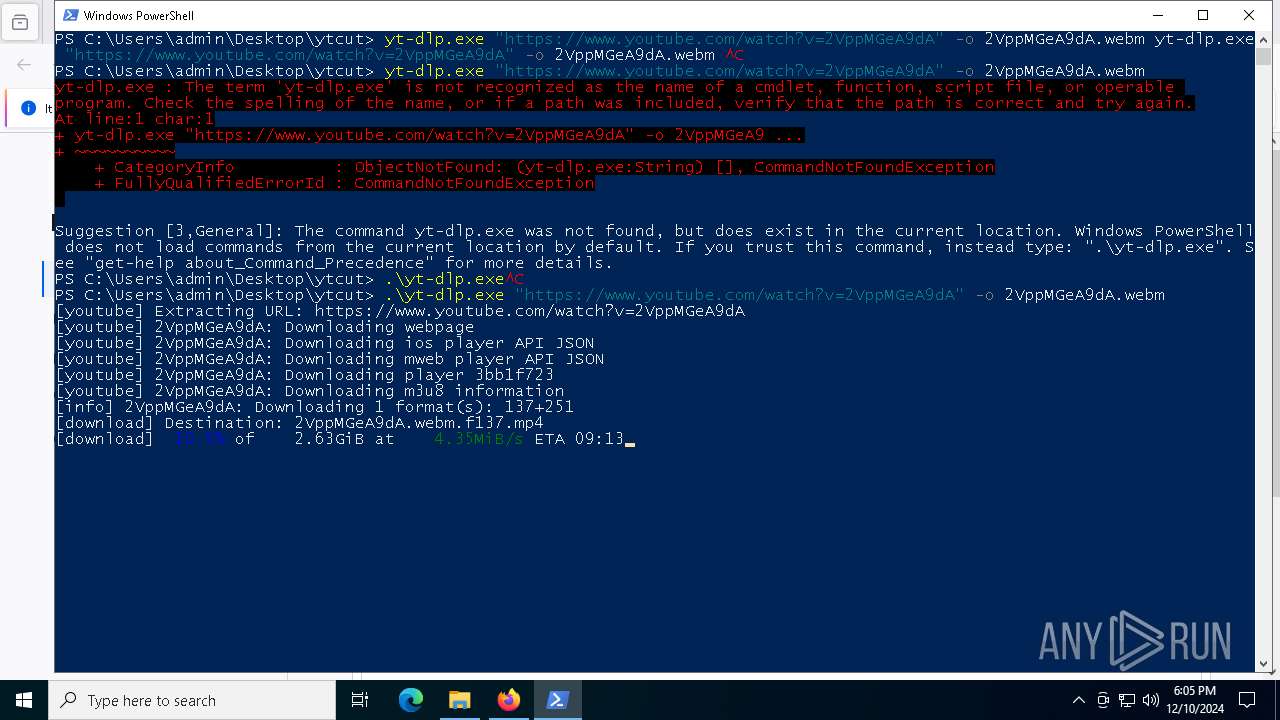
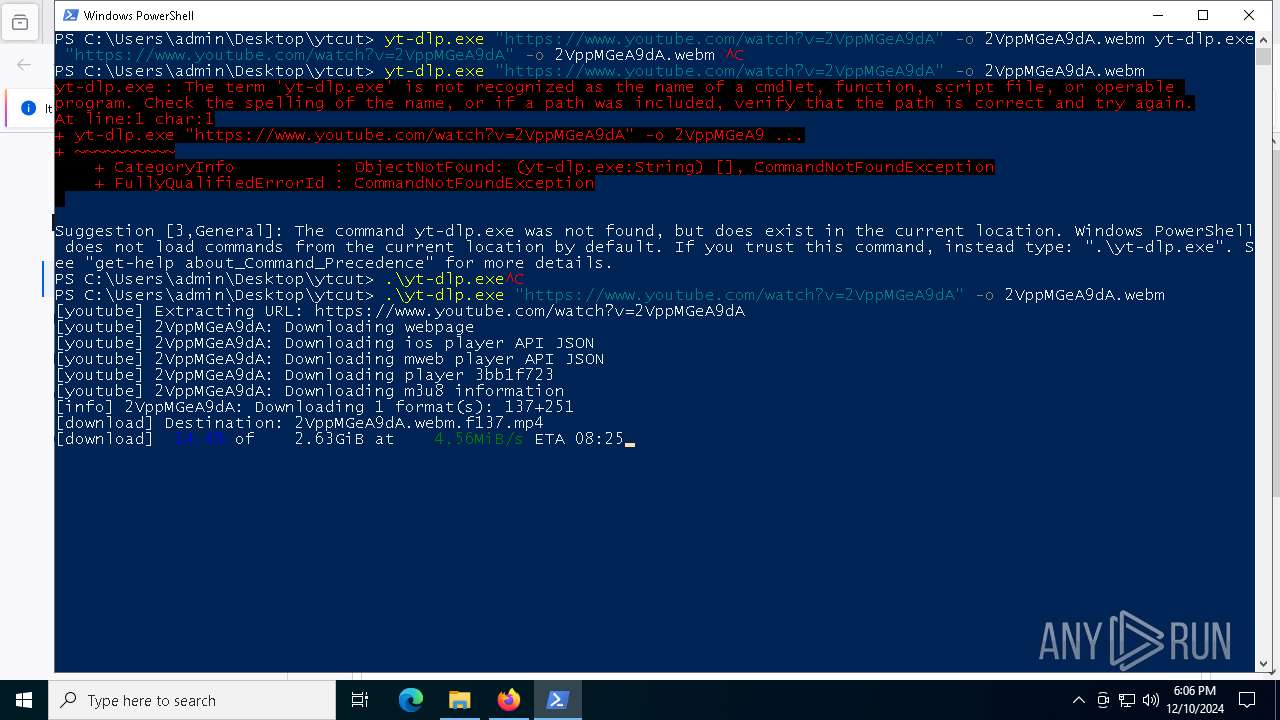
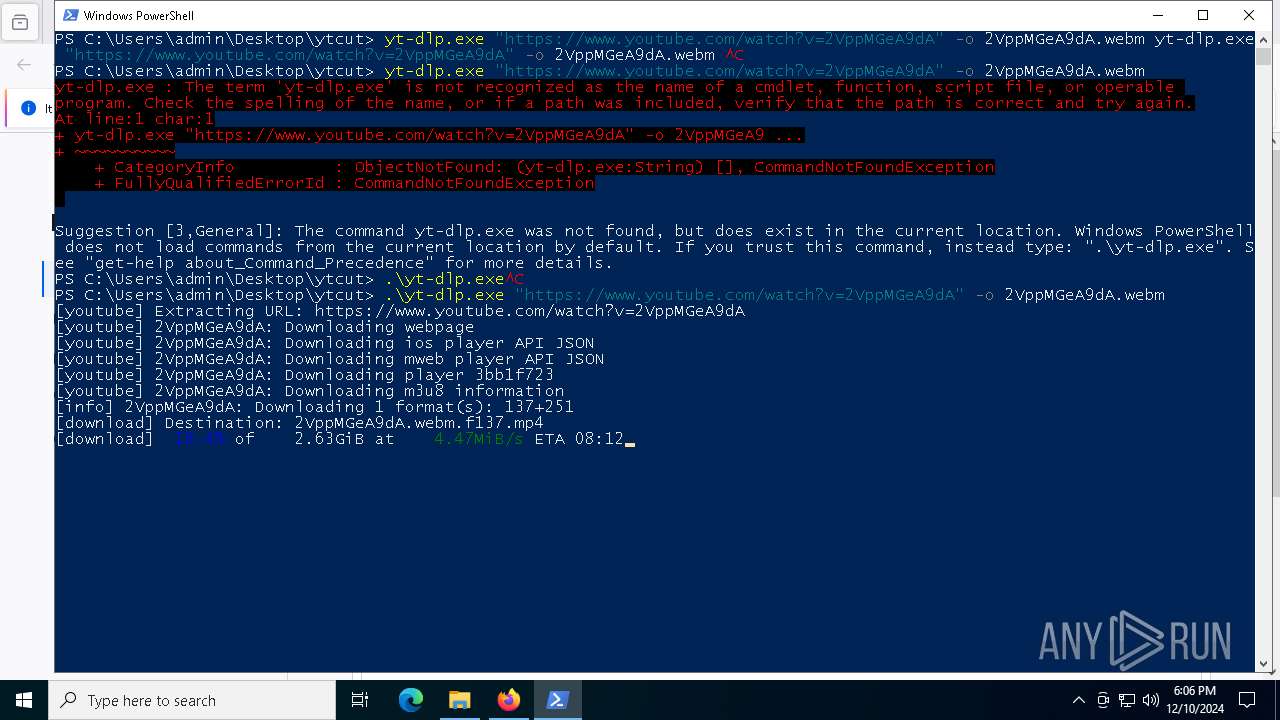
| 5748 | "C:\Users\admin\Desktop\ytcut\yt-dlp.exe" https://www.youtube.com/watch?v=2VppMGeA9dA -o 2VppMGeA9dA.webm | C:\Users\admin\Desktop\ytcut\yt-dlp.exe | yt-dlp.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
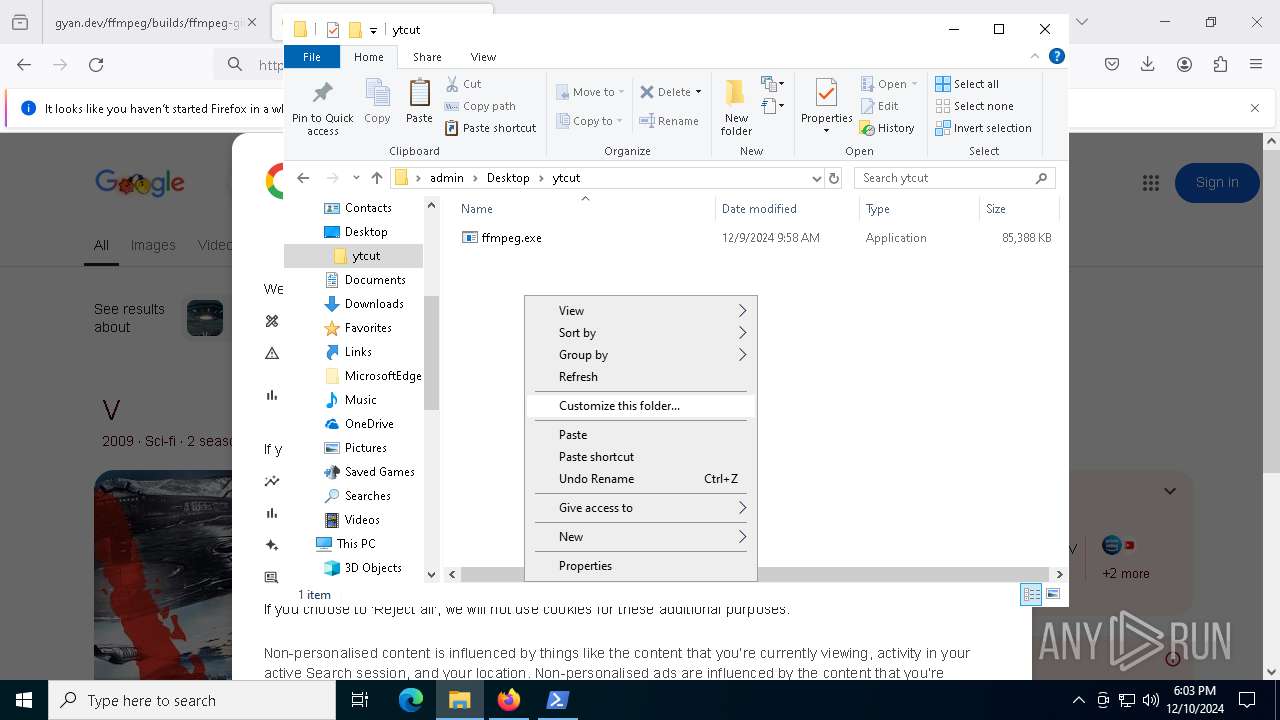
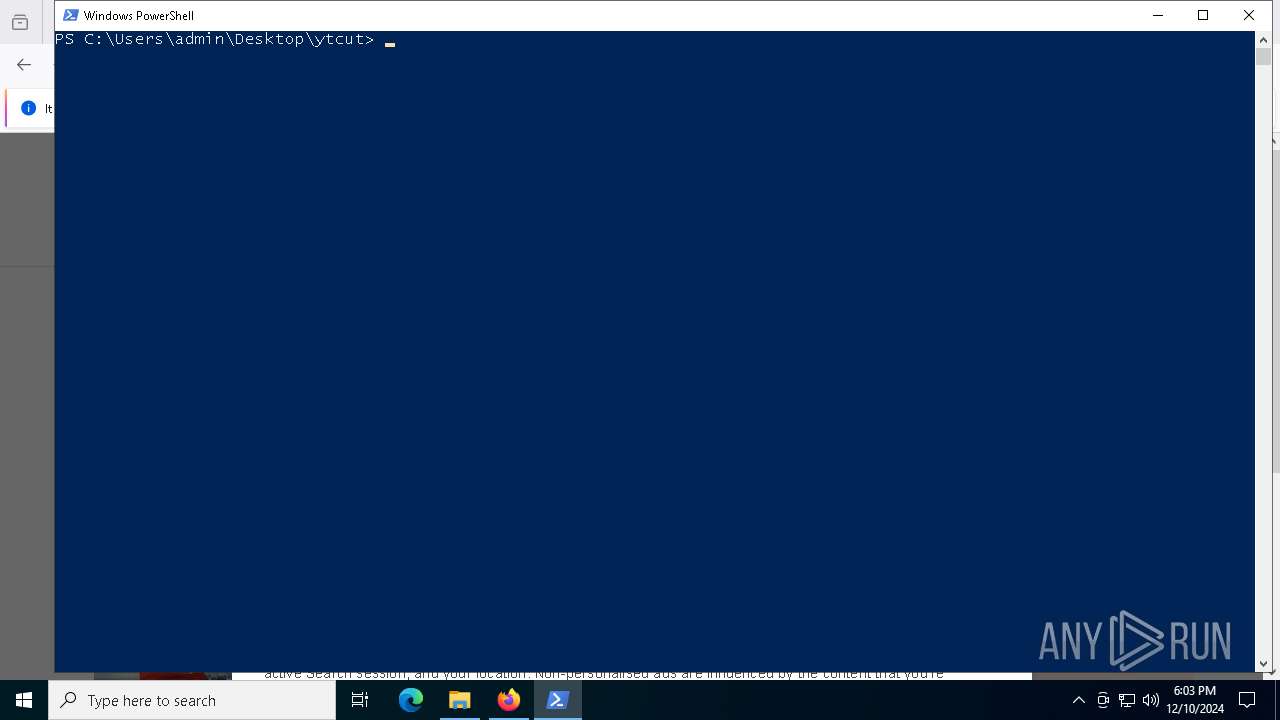
| 6196 | "PowerShell.exe" -noexit -command Set-Location -literalPath 'C:\Users\admin\Desktop\ytcut' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6404 | "C:\Users\admin\Desktop\ytcut\yt-dlp.exe" https://www.youtube.com/watch?v=2VppMGeA9dA -o 2VppMGeA9dA.webm | C:\Users\admin\Desktop\ytcut\yt-dlp.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
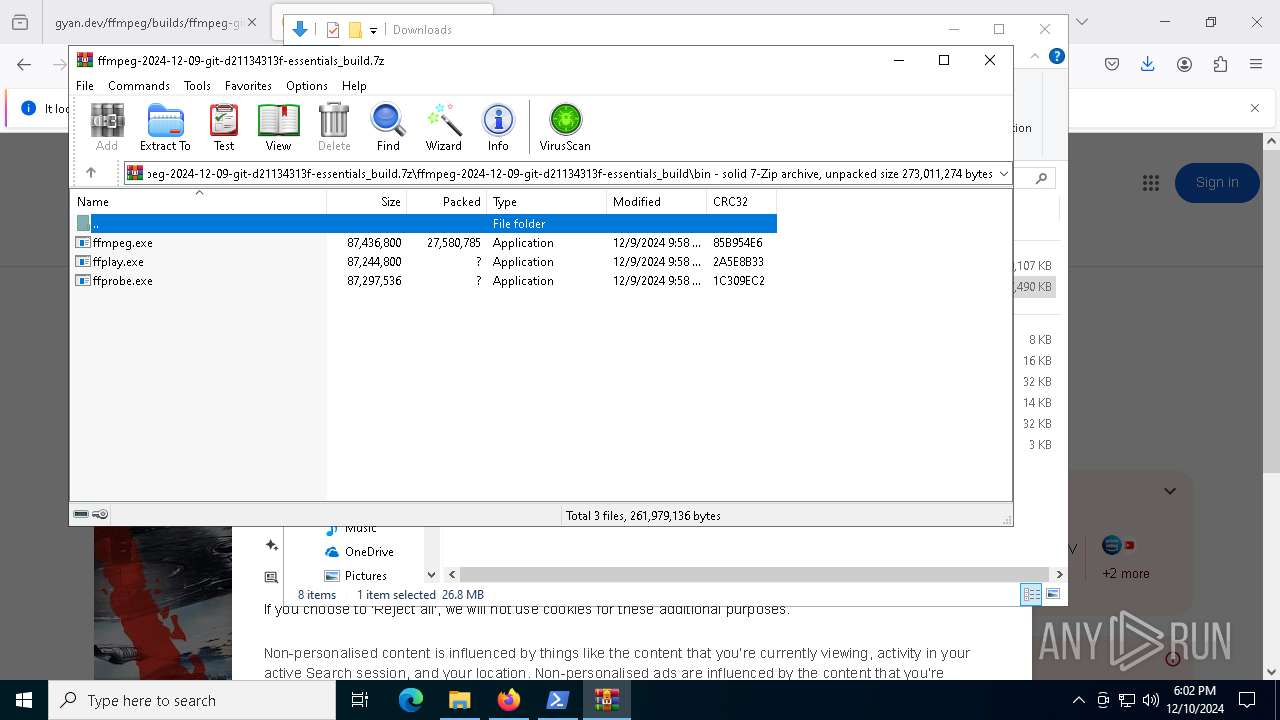
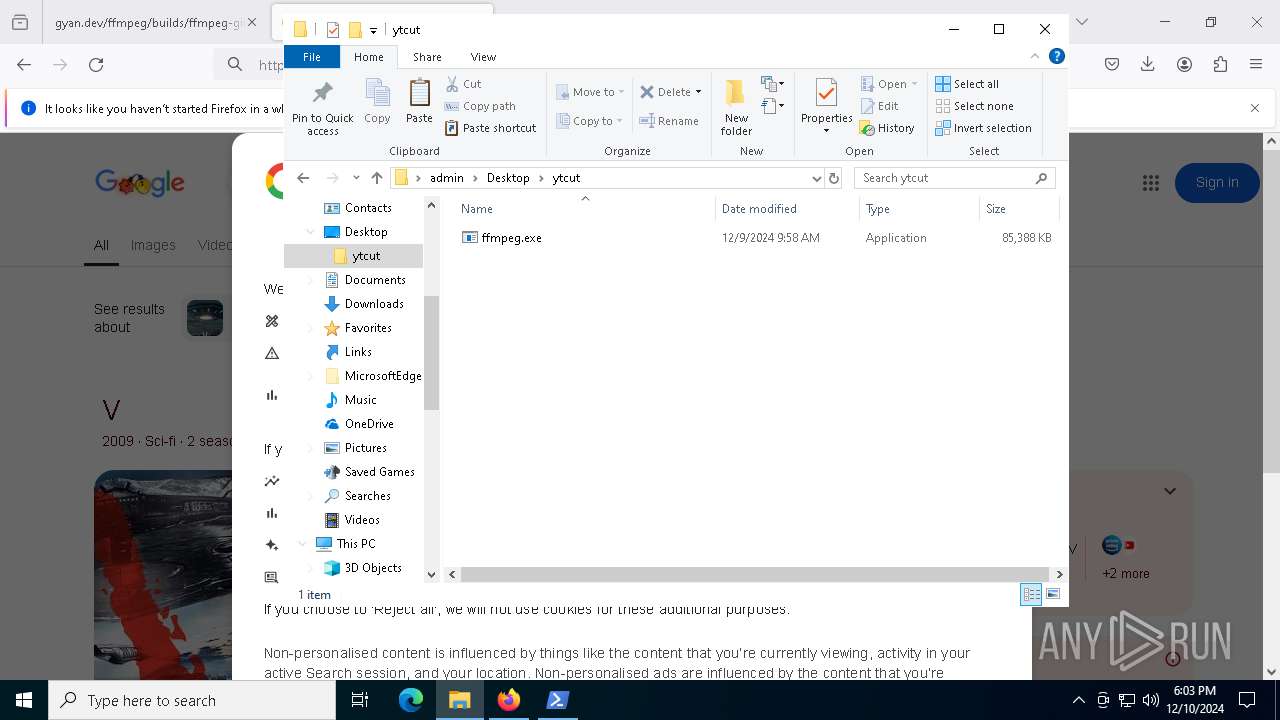
| 7704 | ffmpeg -bsfs | C:\Users\admin\Desktop\ytcut\ffmpeg.exe | — | yt-dlp.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
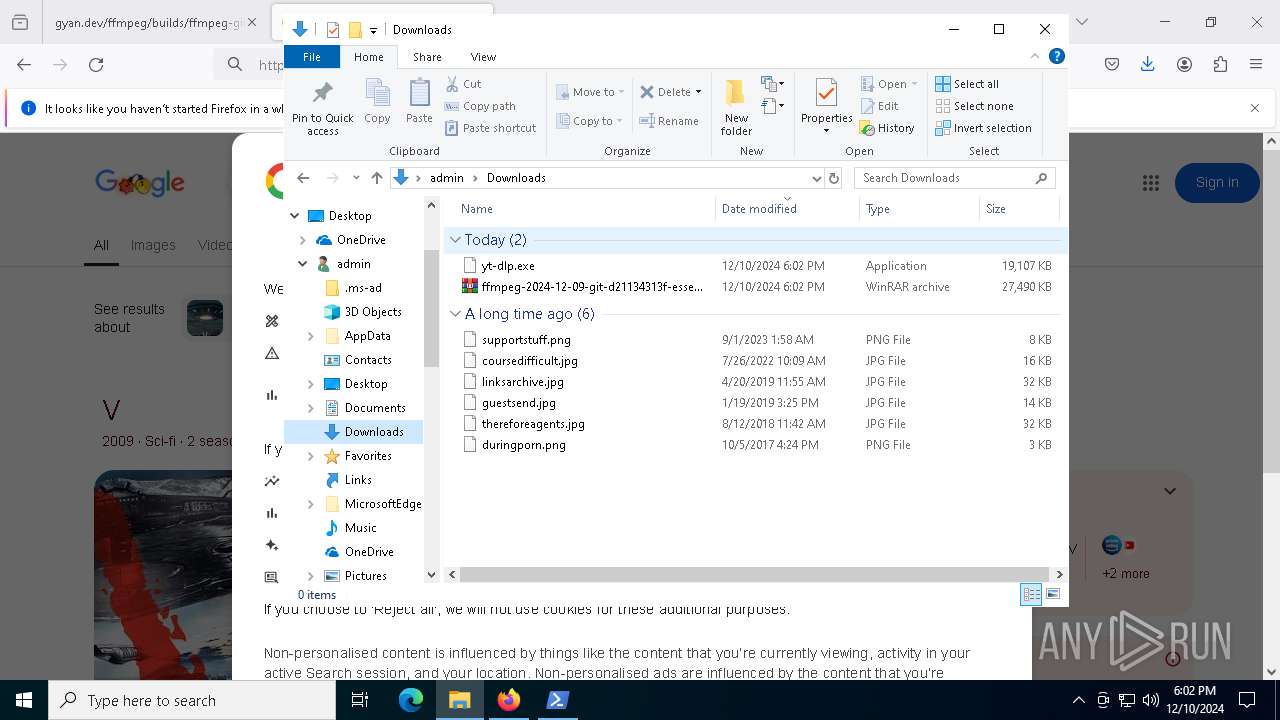
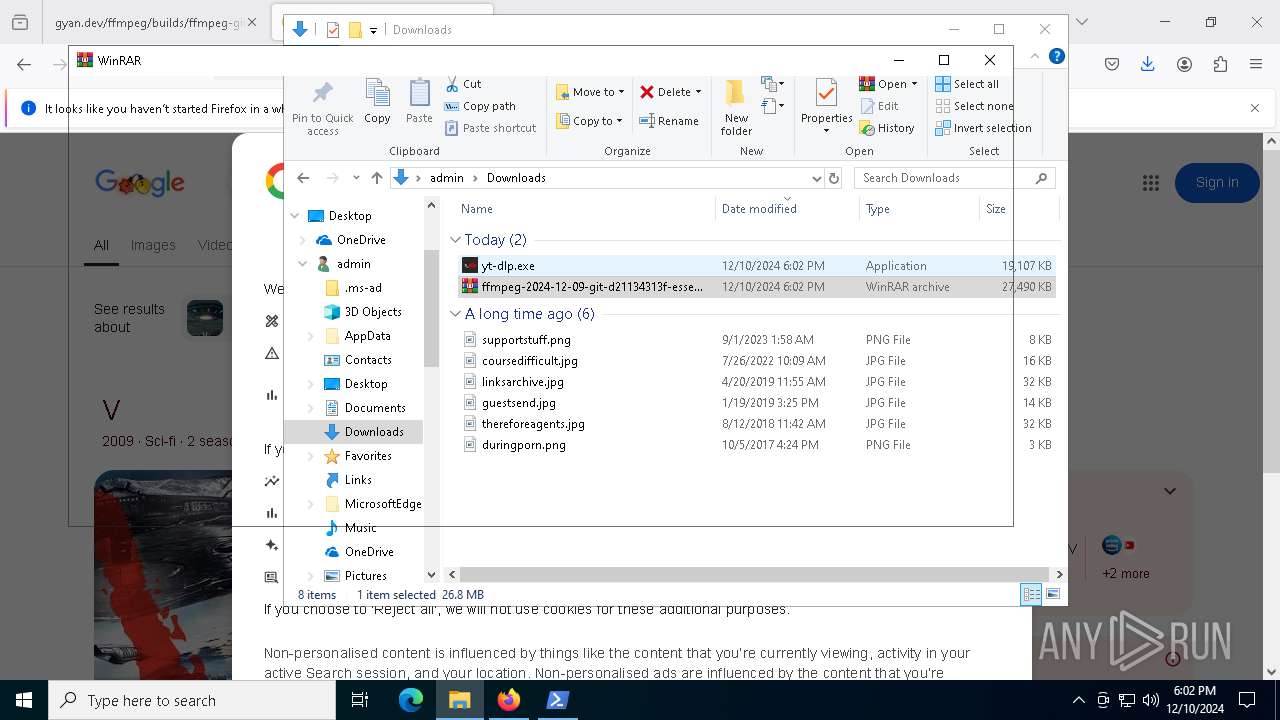
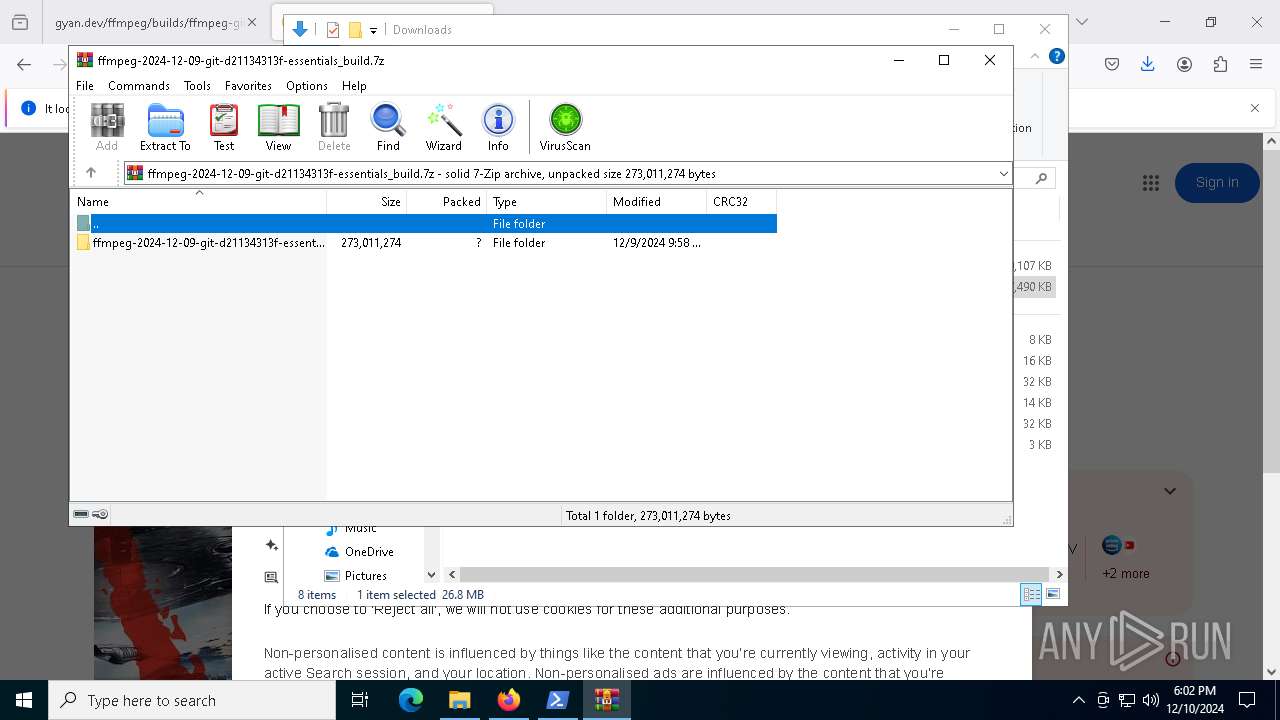
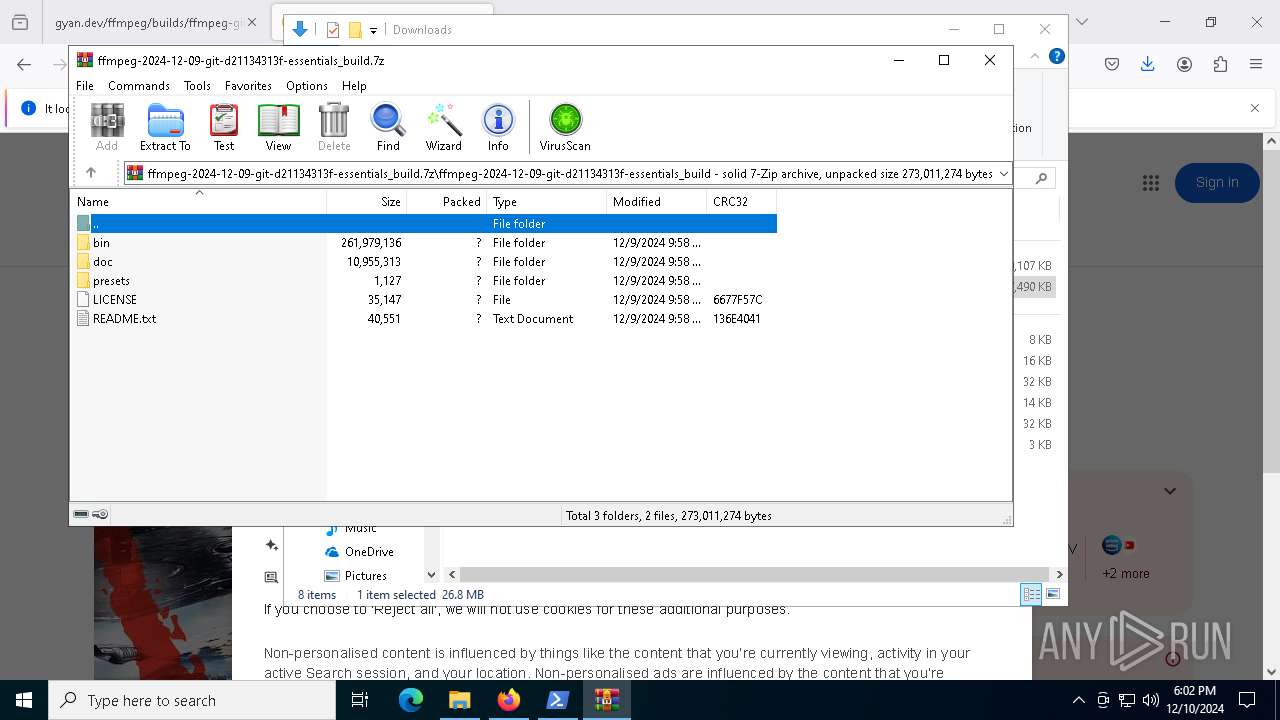
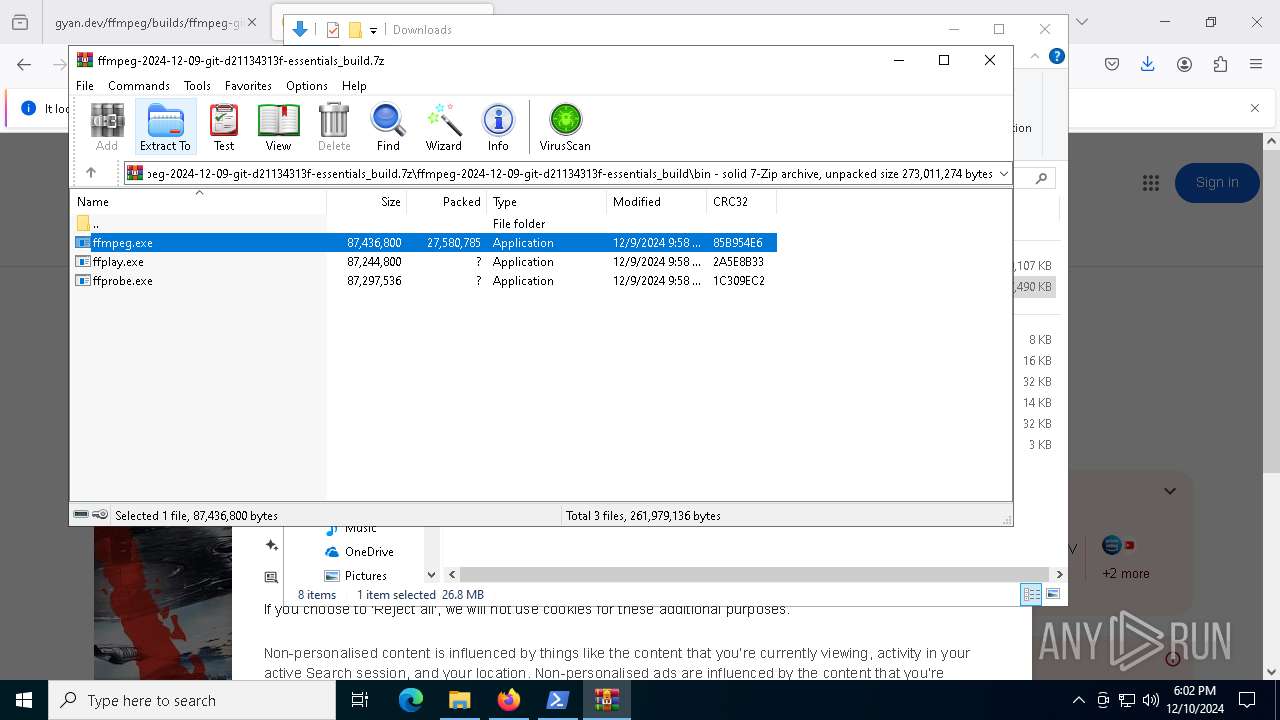
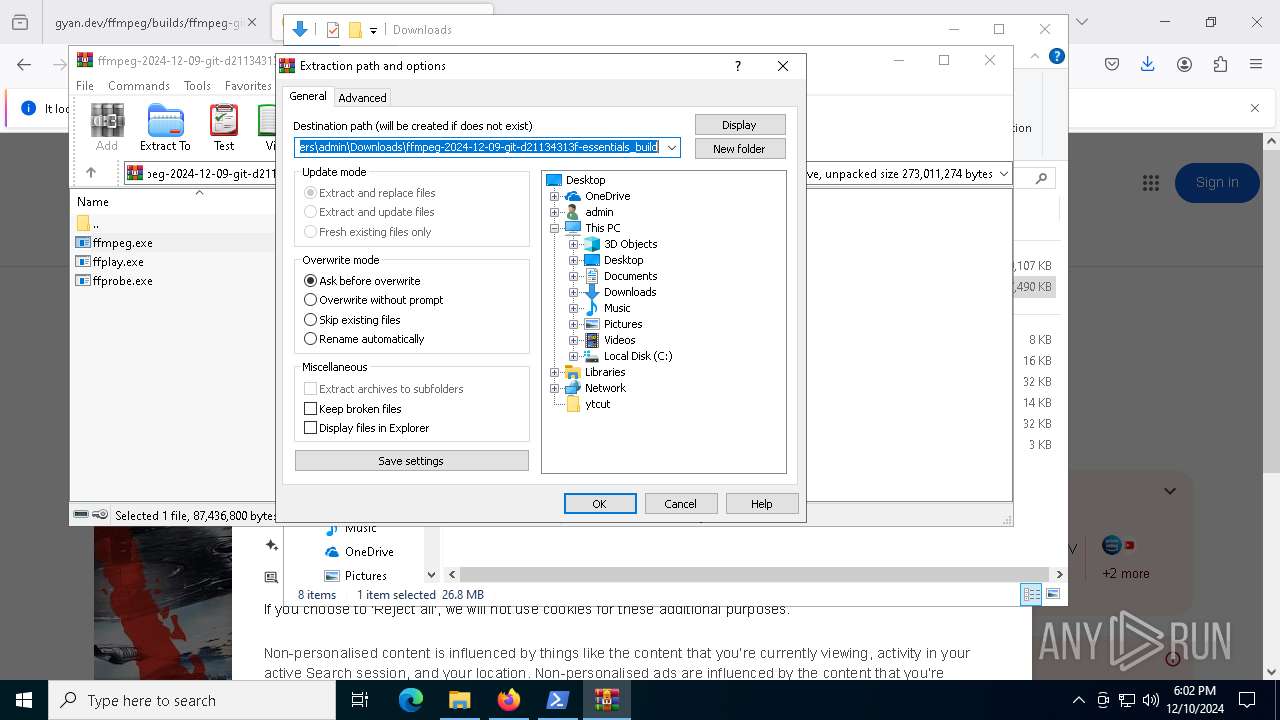
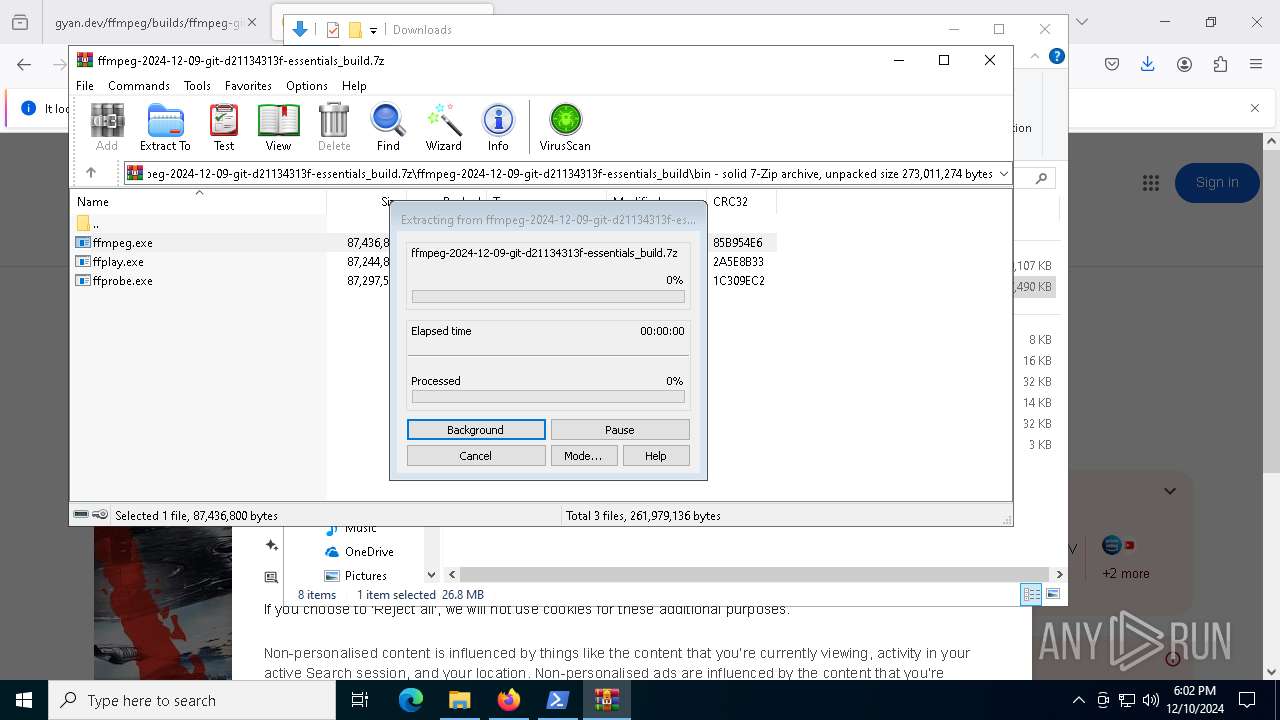
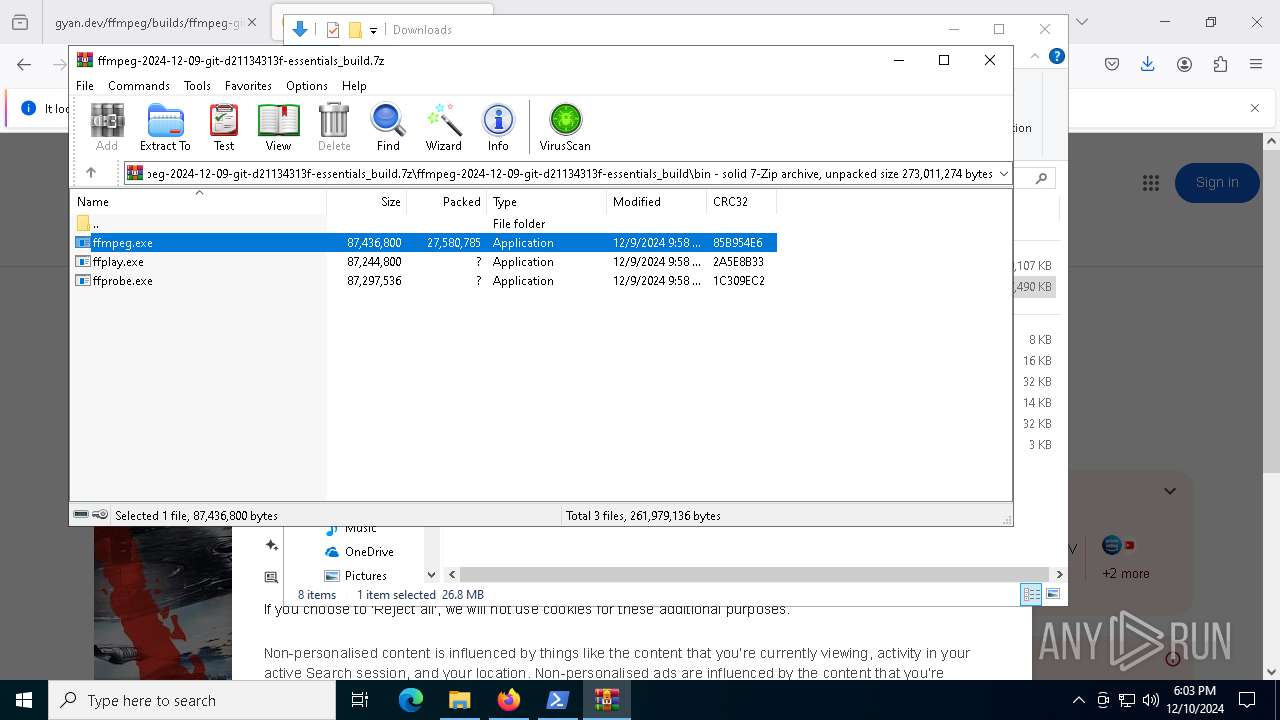
| 8024 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ffmpeg-2024-12-09-git-d21134313f-essentials_build.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
8 437
Read events
8 403
Write events
21
Delete events
13
Modification events
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\ffmpeg-2024-12-09-git-d21134313f-essentials_build.7z | |||
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (8024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
116
Suspicious files
11
Text files
26
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
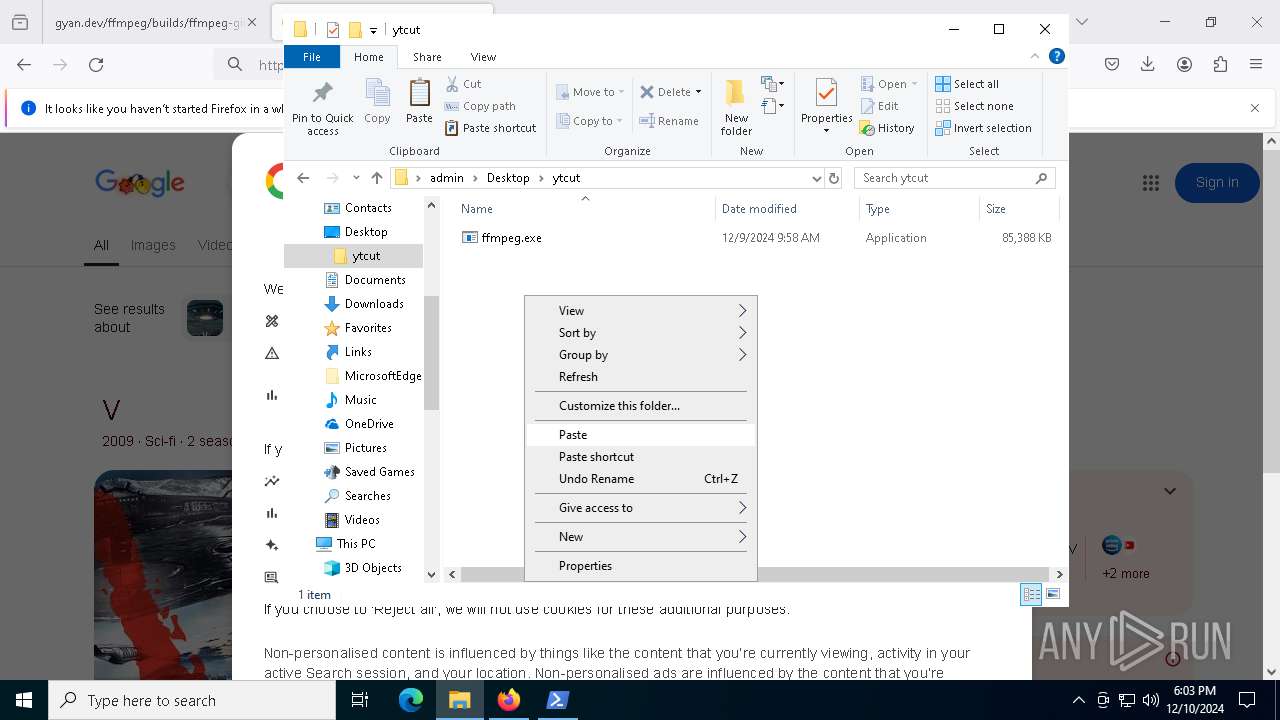
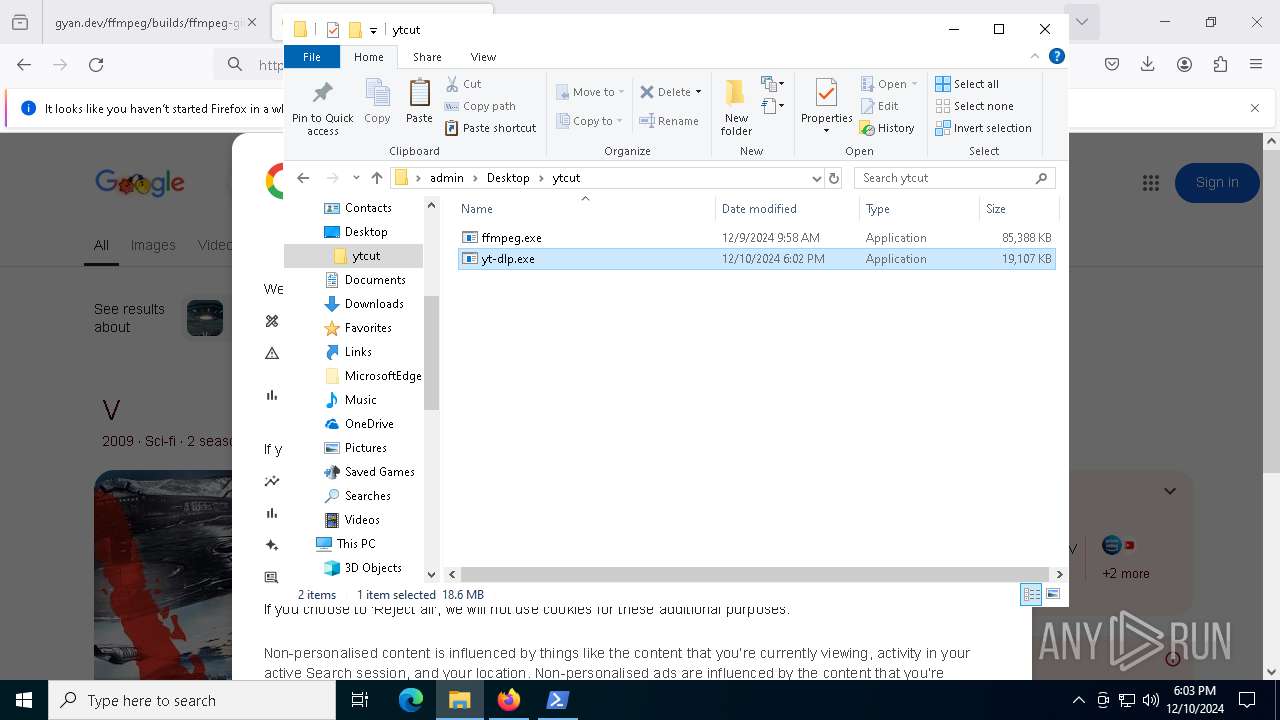
| 8024 | WinRAR.exe | C:\Users\admin\Desktop\ytcut\ffmpeg.exe | — | |
MD5:— | SHA256:— | |||
| 6404 | yt-dlp.exe | C:\Users\admin\AppData\Local\Temp\_MEI64042\Cryptodome\Cipher\_chacha20.pyd | executable | |
MD5:0BE007DD183DAF0F4B65E73CF19EA139 | SHA256:F6308DACB781C99D3B962451FC681973808792936690AF6AA7FA5B6DF40F4EAF | |||
| 6196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF13a377.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6196 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yjkmumlj.kwk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:26AE7DD7A0BAD3A2DEF2F4A2ED574A38 | SHA256:F4C2D6FB3F3F059186C4DB3CED0AFB6E43146CD4939B68C42CE045EA02A3FE57 | |||
| 6196 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_3ood012r.pd1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6404 | yt-dlp.exe | C:\Users\admin\AppData\Local\Temp\_MEI64042\Cryptodome\Cipher\_Salsa20.pyd | executable | |
MD5:2CE3043D6FBD62BCBE6948A1E6A789F0 | SHA256:C5A4AC8202A0211163938B6306E3A678CC461ED8E283F4C4601748D2E50783A3 | |||
| 6196 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YAQOJA2F0W155A8L1A7A.temp | binary | |
MD5:26AE7DD7A0BAD3A2DEF2F4A2ED574A38 | SHA256:F4C2D6FB3F3F059186C4DB3CED0AFB6E43146CD4939B68C42CE045EA02A3FE57 | |||
| 6196 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:3F95A05381C6D14195F6A1538F5FBADE | SHA256:0E753E9AD3EDE811C17D076B462F85321B8F559C2E462AF0990A1653573A525F | |||
| 6404 | yt-dlp.exe | C:\Users\admin\AppData\Local\Temp\_MEI64042\Cryptodome\Cipher\_raw_aes.pyd | executable | |
MD5:E306365BDC8D15B2F477E5AF252D0B59 | SHA256:2DCAC73EA3240A008D115BAC0EA4D7C65C8162676AB30BCAF7527C22B98B4929 | |||
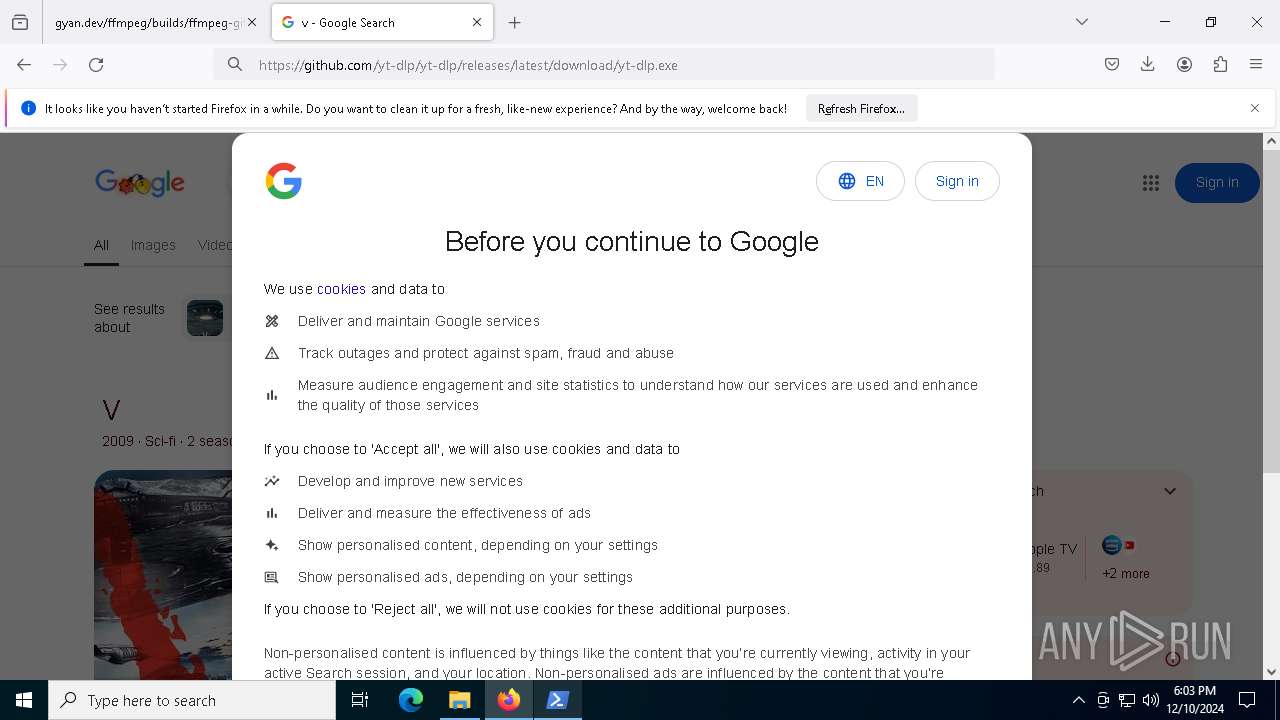
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
48
TCP/UDP connections
125
DNS requests
163
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4024 | svchost.exe | GET | 200 | 184.24.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | DE | binary | 504 b | whitelisted |
— | — | POST | 200 | 2.16.206.143:80 | http://r11.o.lencr.org/ | DE | binary | 504 b | whitelisted |
— | — | POST | — | 142.250.181.227:80 | http://o.pki.goog/wr2 | US | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
— | — | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | DE | binary | 504 b | whitelisted |
— | — | POST | 200 | 2.16.206.143:80 | http://r11.o.lencr.org/ | DE | binary | 504 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4024 | svchost.exe | 184.24.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4024 | svchost.exe | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.204.160:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.218.210.69:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
www.gyan.dev |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
gyan.nfshost.com |
| unknown |