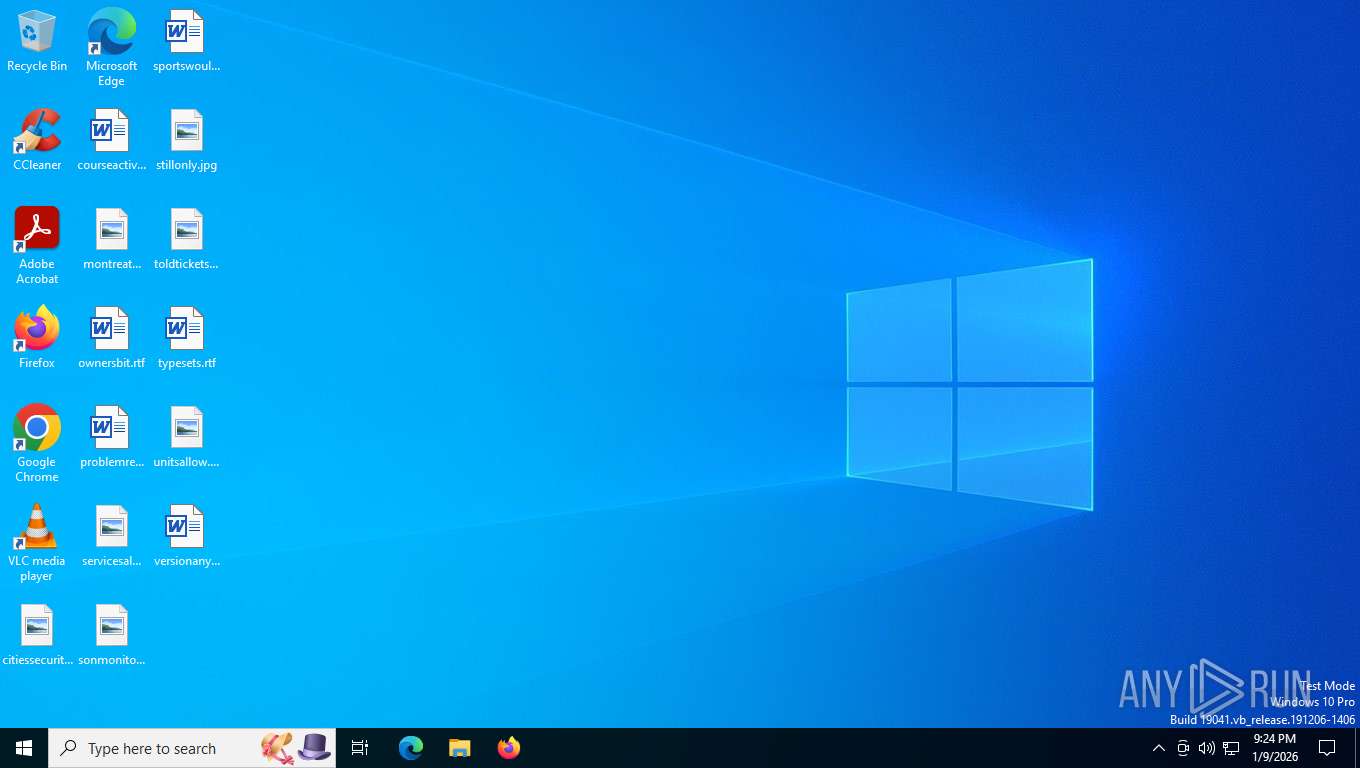
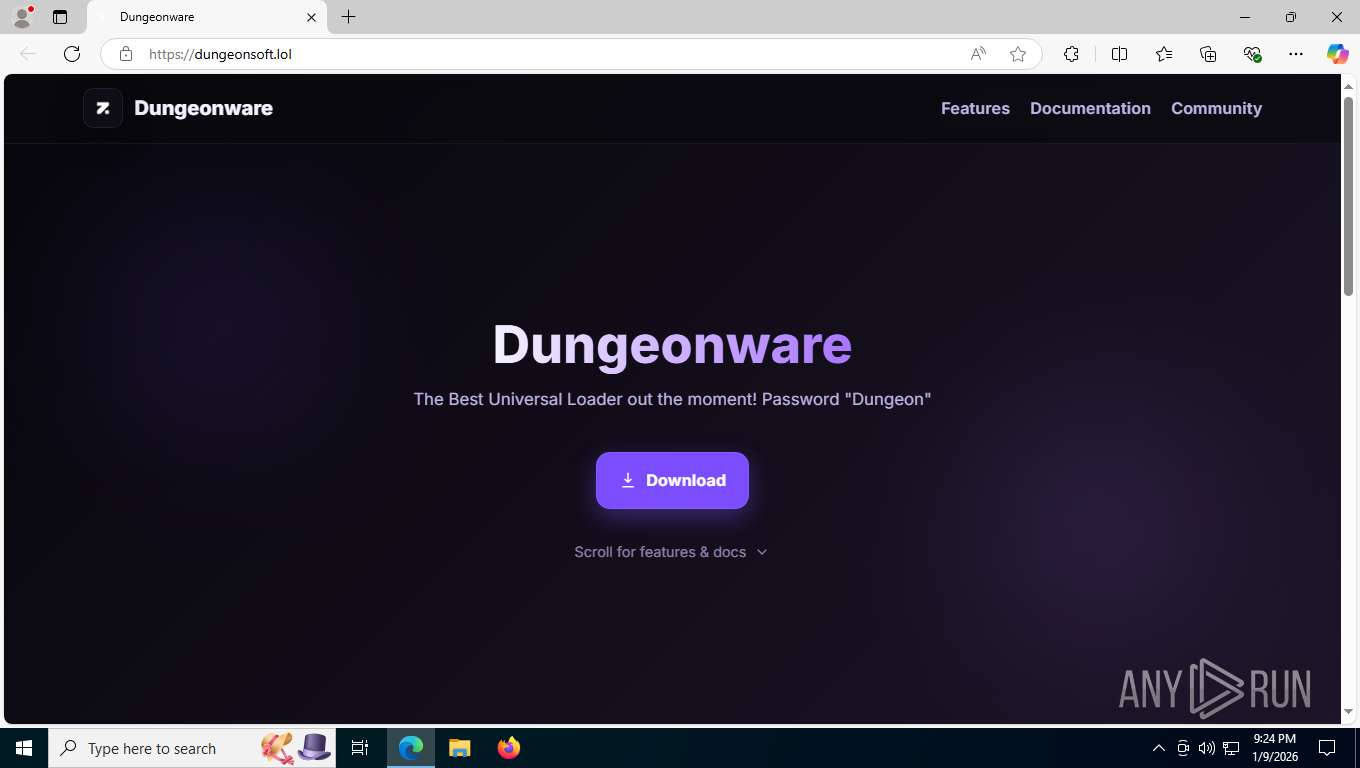
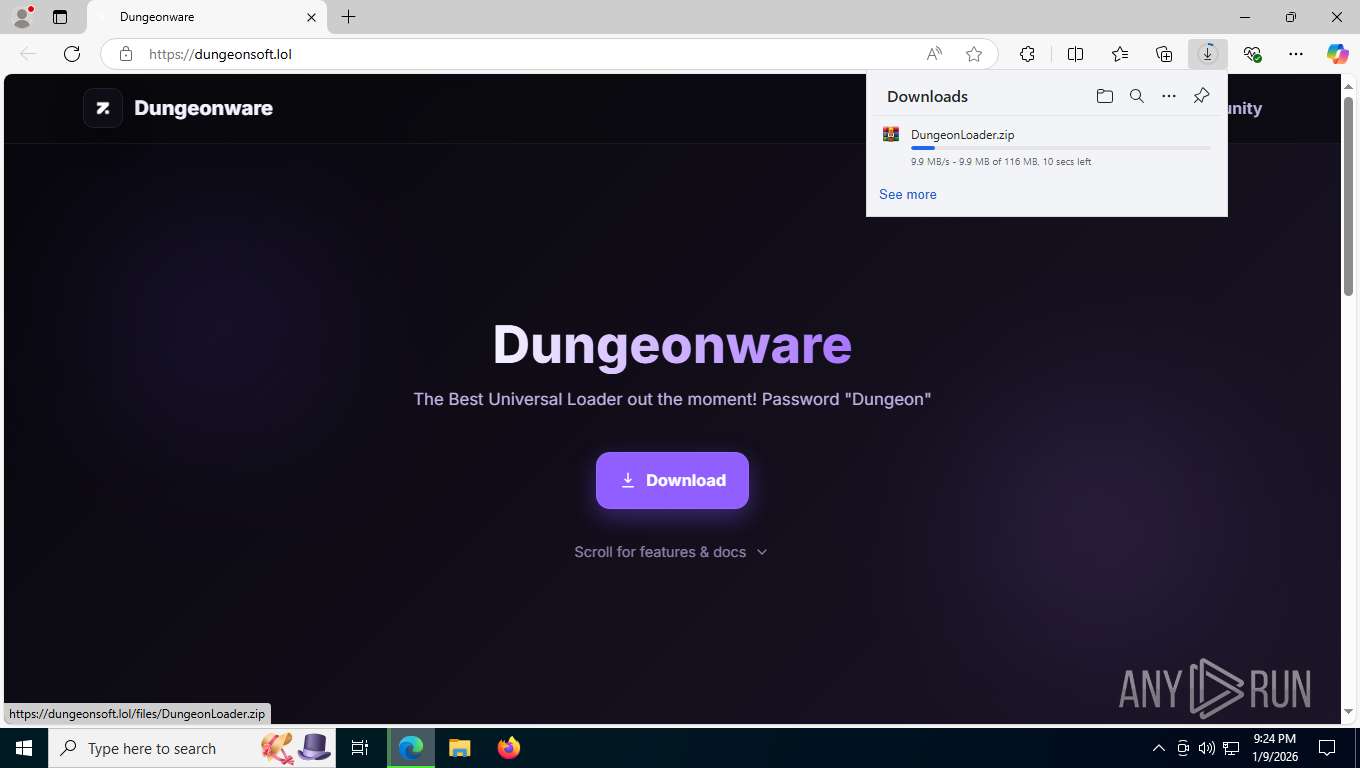
| URL: | https://dungeonsoft.lol/ |
| Full analysis: | https://app.any.run/tasks/c47a4266-3c69-46fa-8eb2-4864524db196 |
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2026, 02:24:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A9523140E1C498AB80000AE4C2E66E79 |
| SHA1: | 51D874957570FEEB609BE76BA4FB7C8D4E09EBB3 |
| SHA256: | 3011FC4BE3B8E0791CA3E68DC0A4286557E06C045E40B7D4BD3080233E61BFBF |
| SSDEEP: | 3:N8I2AQW895:2IQN5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
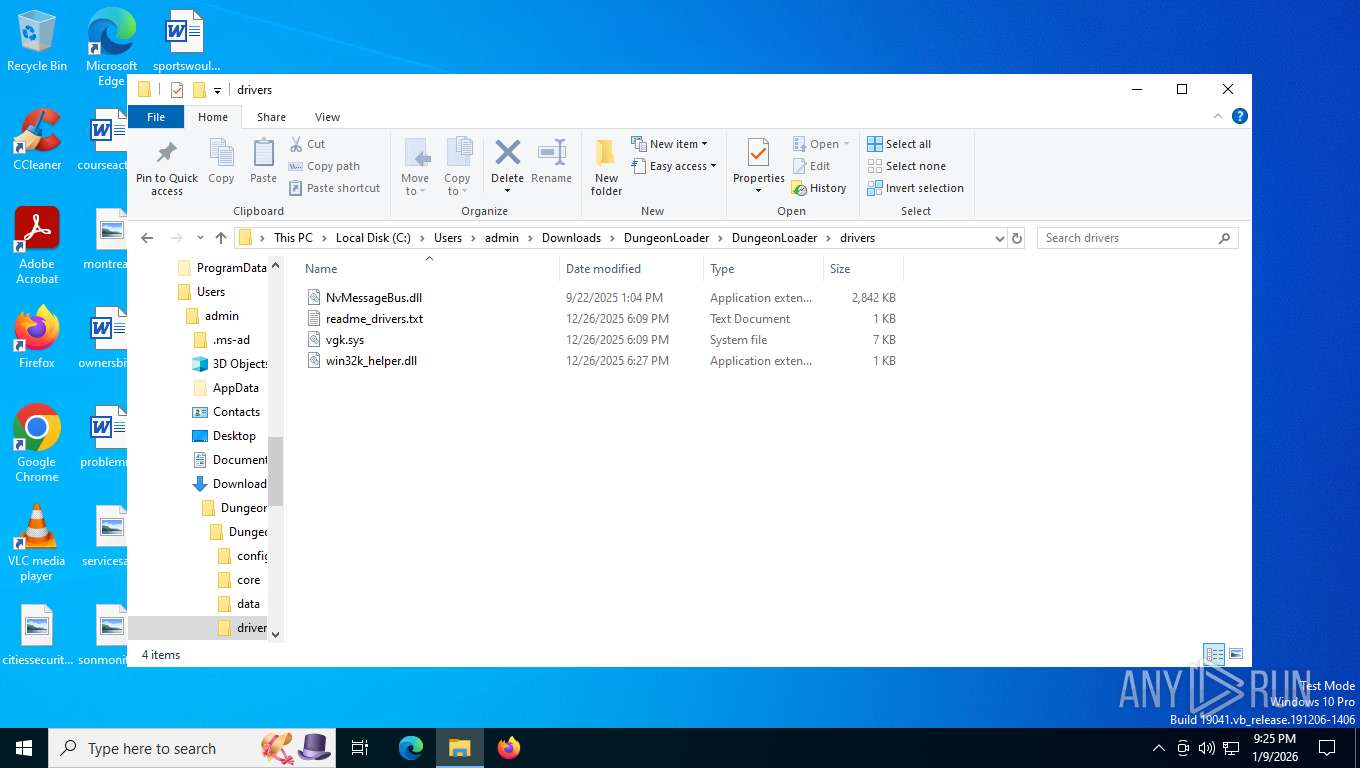
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 8816)
Executes as Windows Service
- VSSVC.exe (PID: 8992)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8300)
- wscript.exe (PID: 7536)
- wscript.exe (PID: 7336)
- wscript.exe (PID: 7996)
- wscript.exe (PID: 1188)
Get information on the list of running processes
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 8916)
The process bypasses the loading of PowerShell profile settings
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 8916)
BASE64 encoded PowerShell command has been detected
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 8916)
The process hide an interactive prompt from the user
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 8916)
Starts POWERSHELL.EXE for commands execution
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 8916)
Base64-obfuscated command line is found
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 8916)
INFO
Reads the computer name
- identity_helper.exe (PID: 7424)
- msiexec.exe (PID: 8944)
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- TextInputHost.exe (PID: 5172)
- puceS.exe (PID: 8916)
Application launched itself
- msedge.exe (PID: 7608)
Checks supported languages
- identity_helper.exe (PID: 7424)
- msiexec.exe (PID: 8944)
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8916)
- TextInputHost.exe (PID: 5172)
Reads Environment values
- identity_helper.exe (PID: 7424)
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 8916)
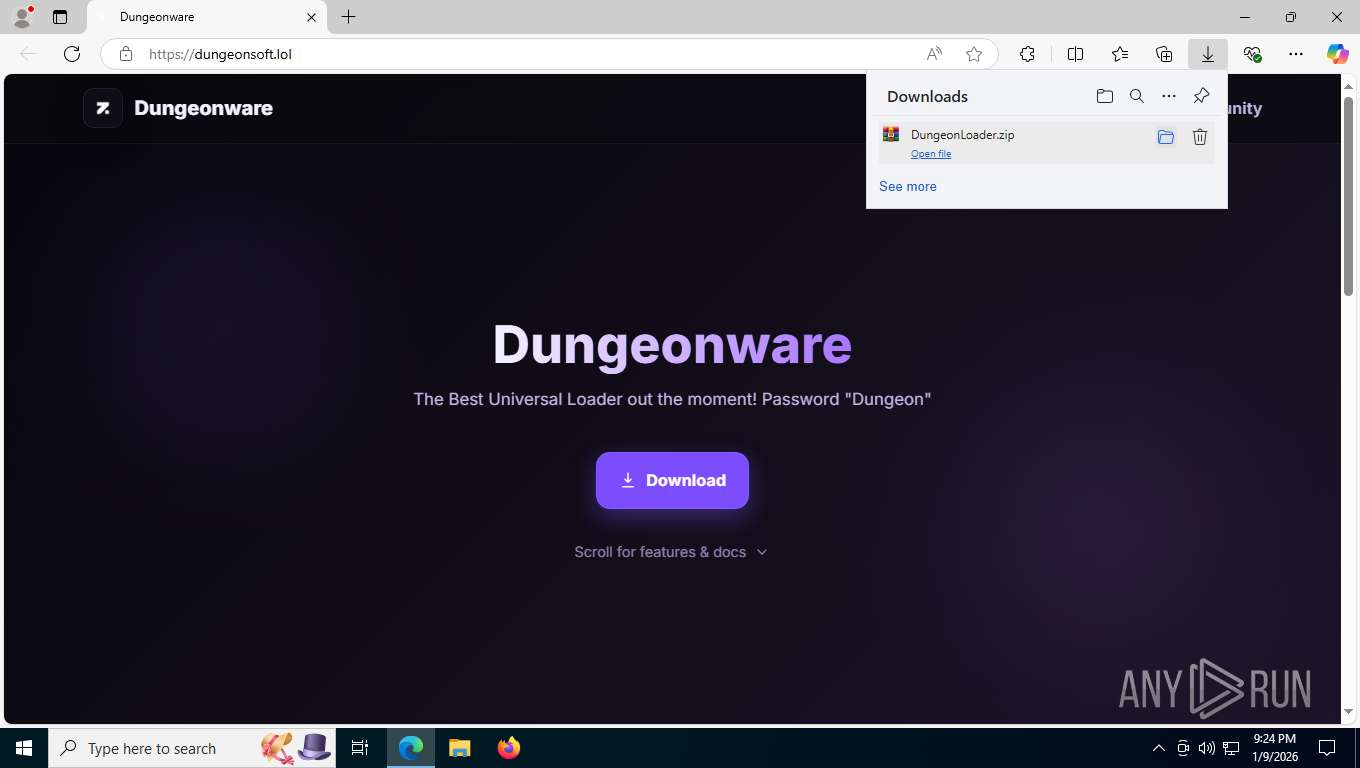
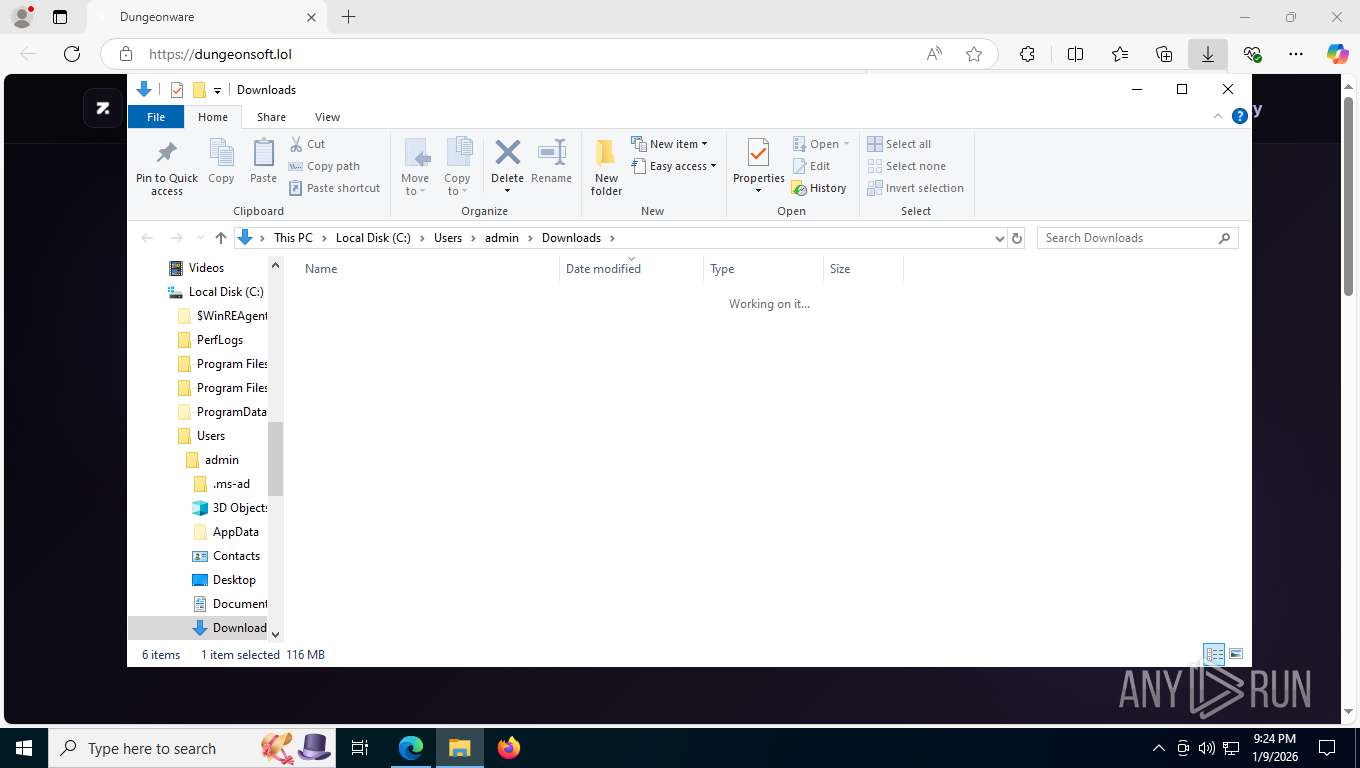
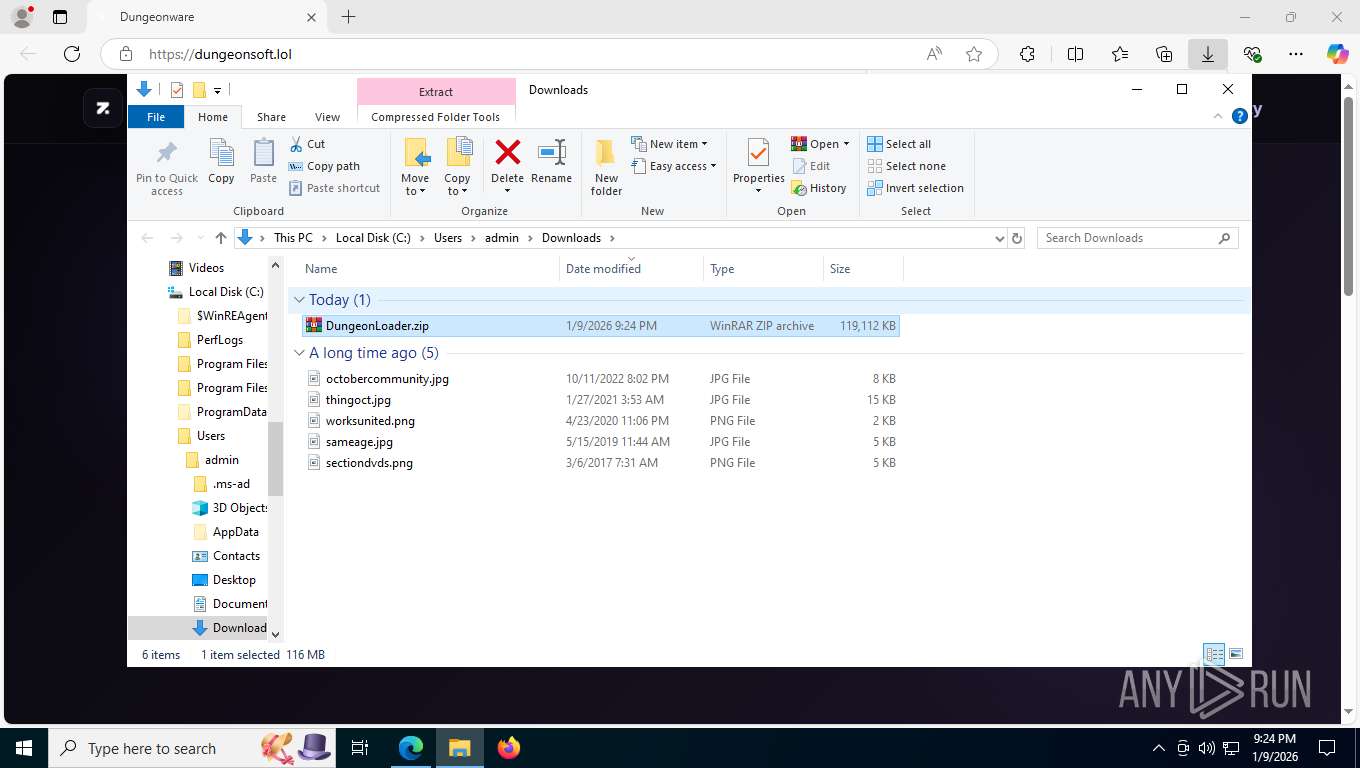
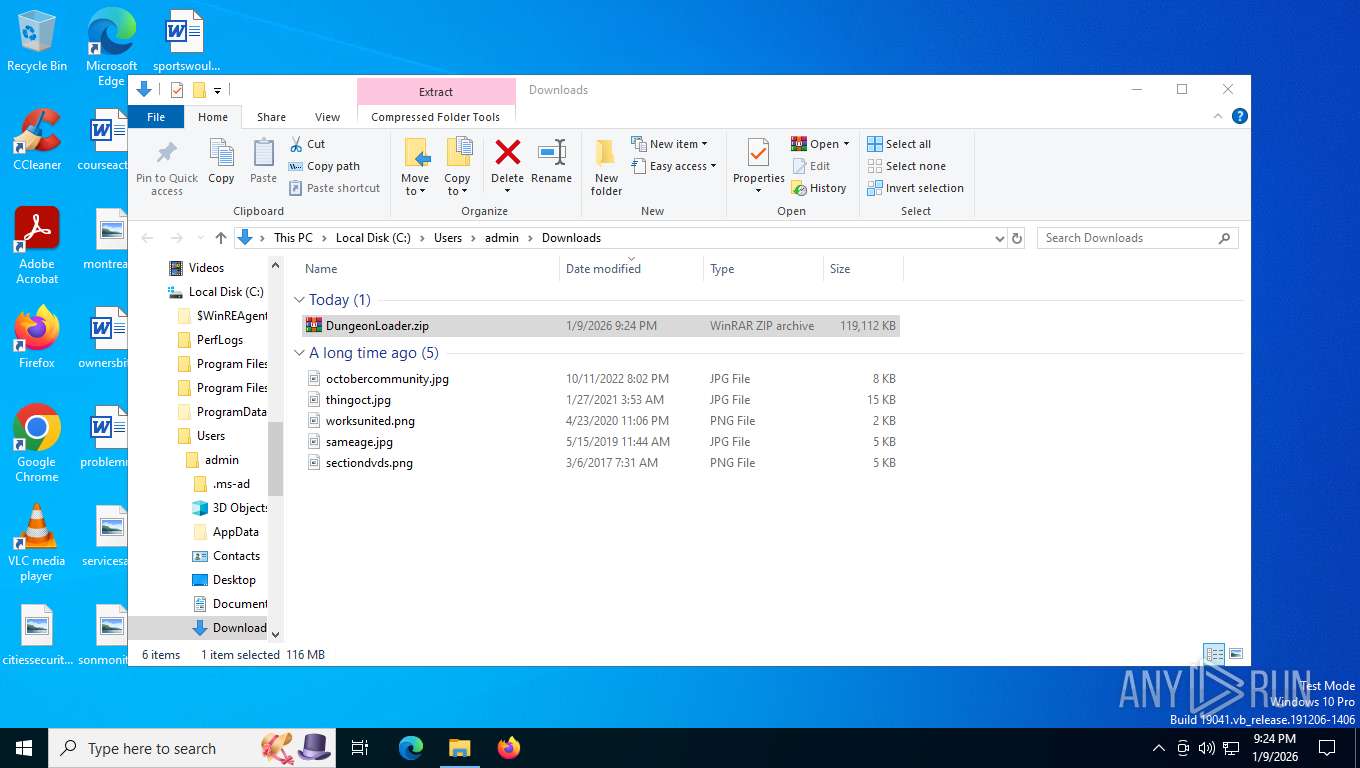
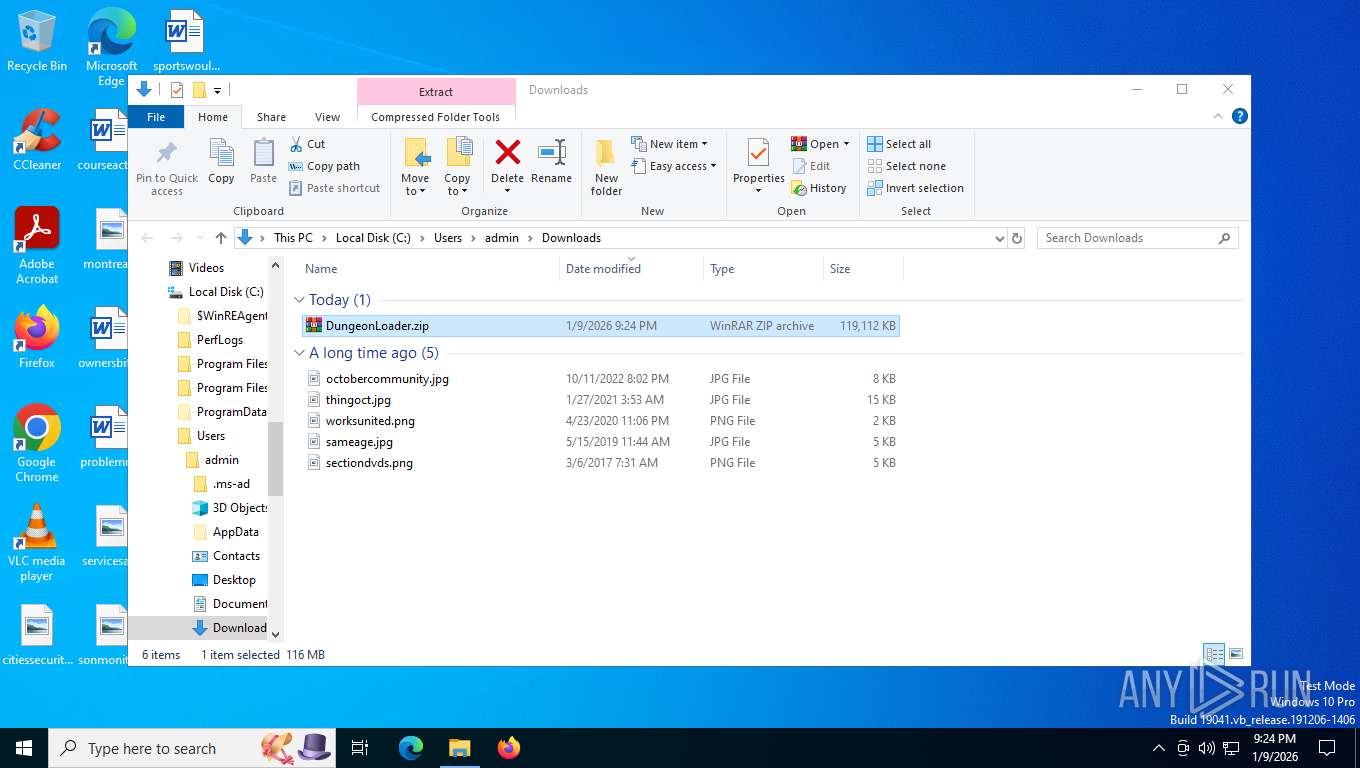
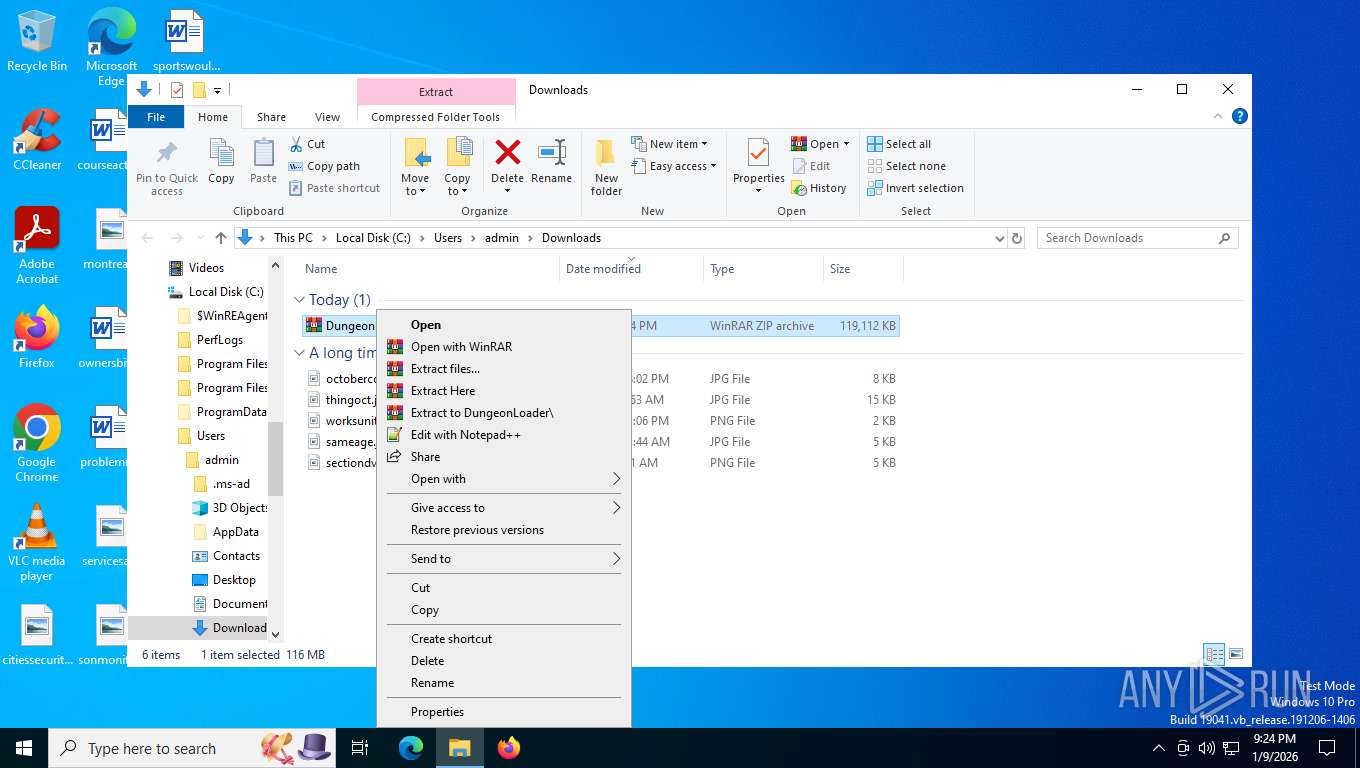
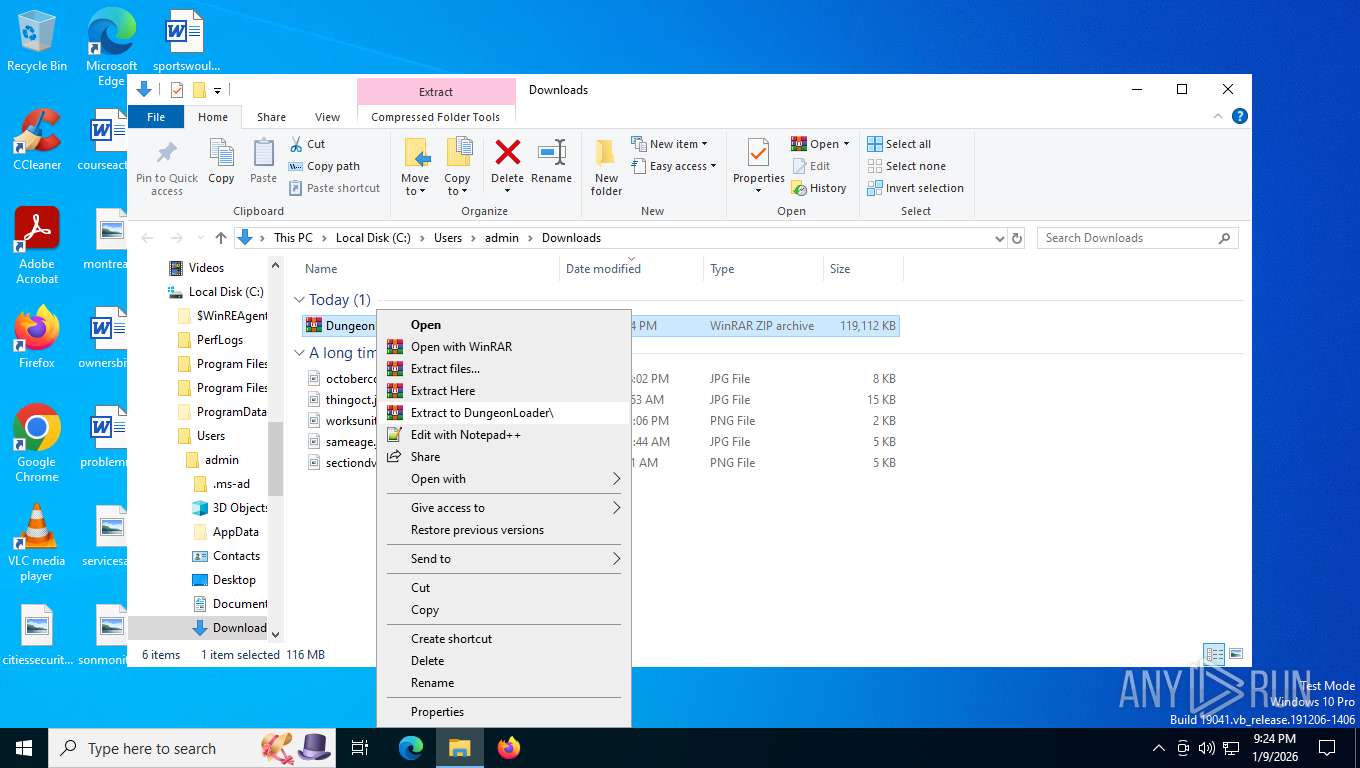
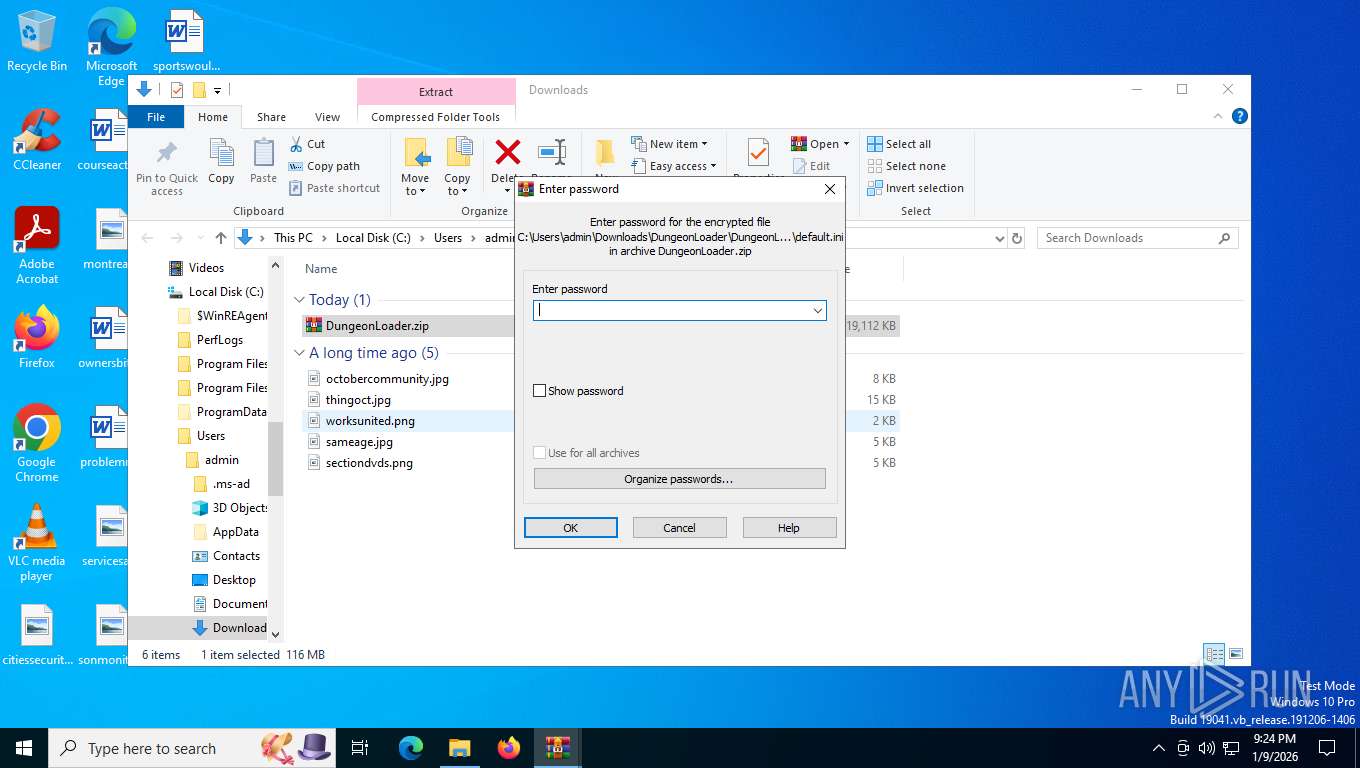
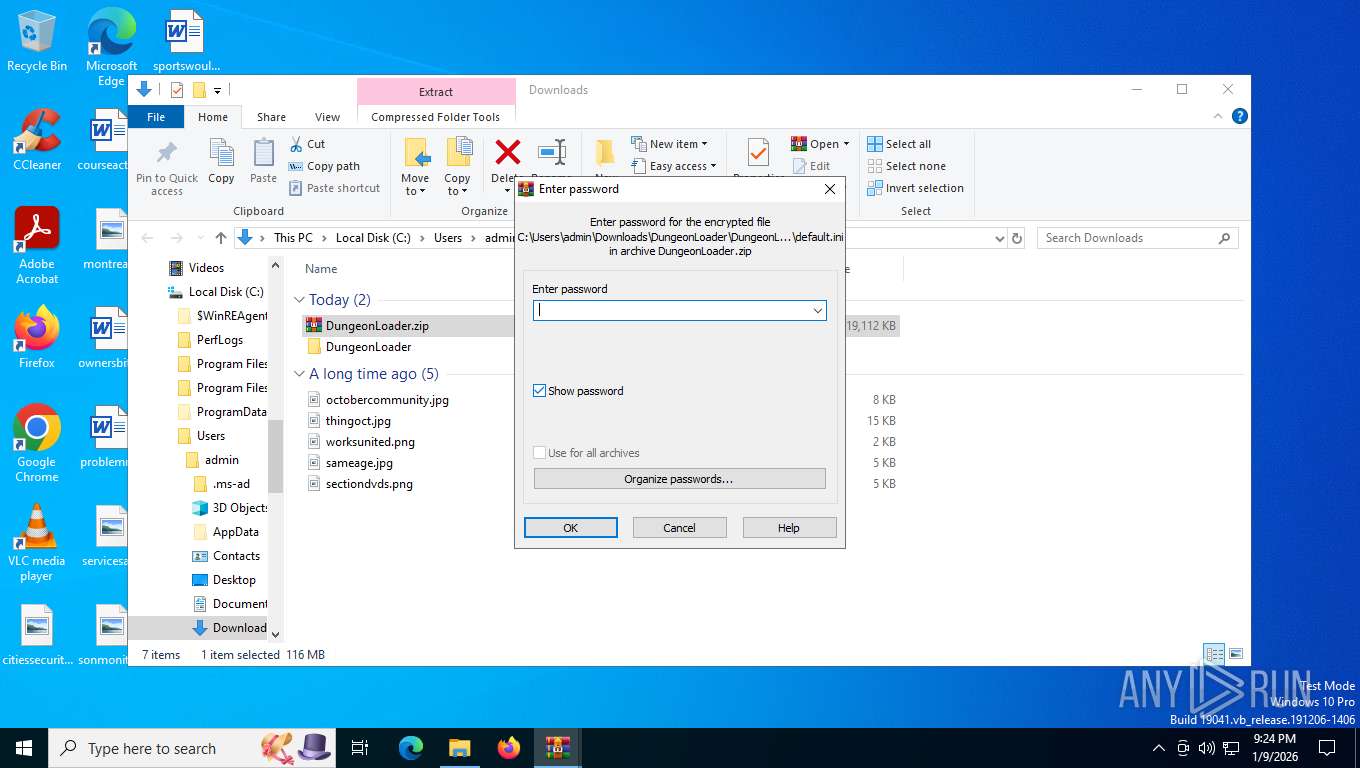
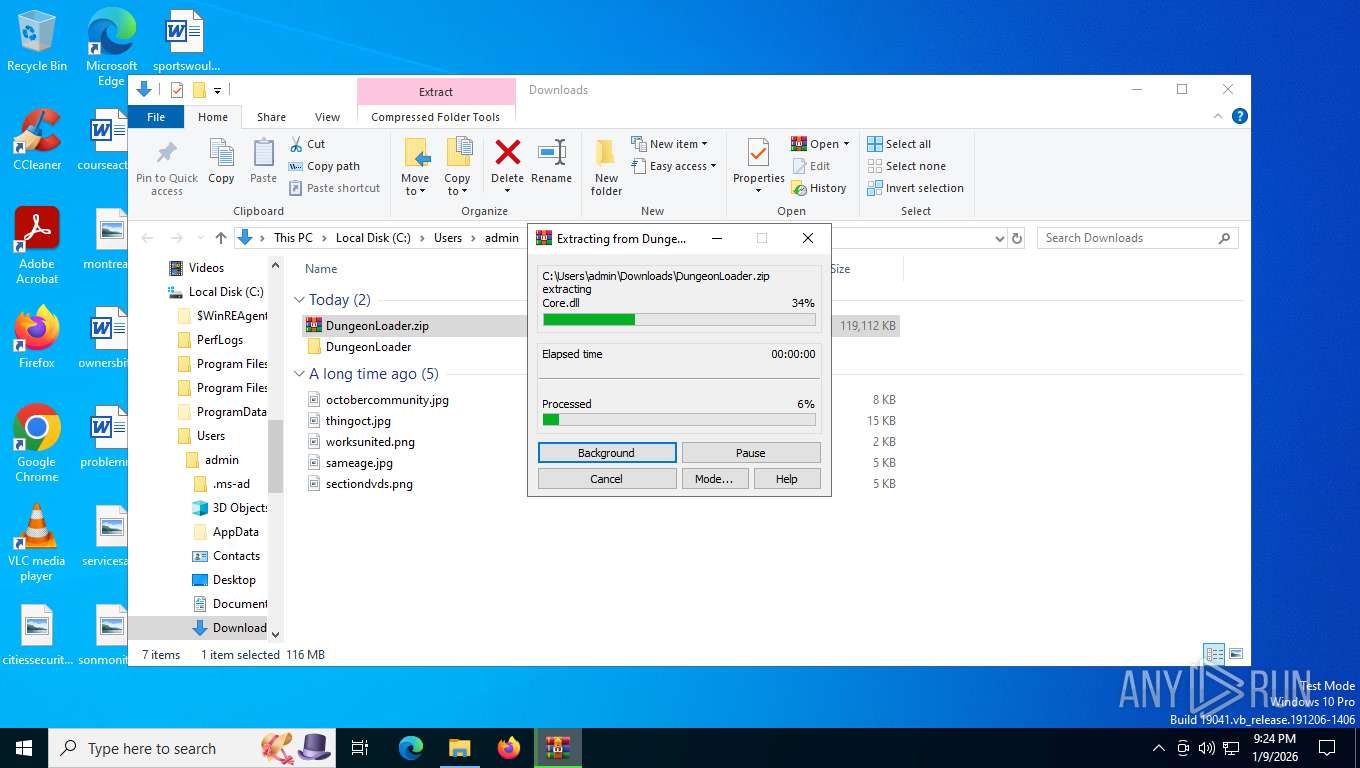
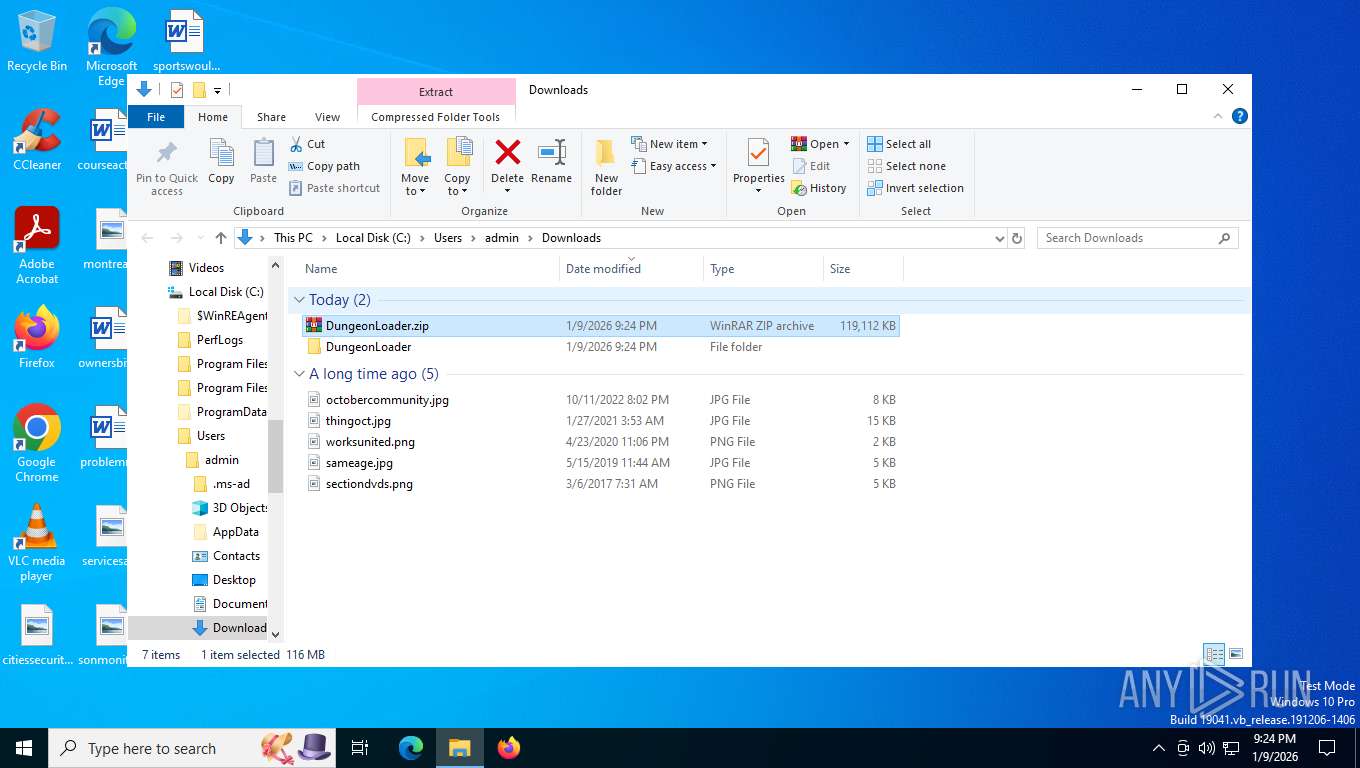
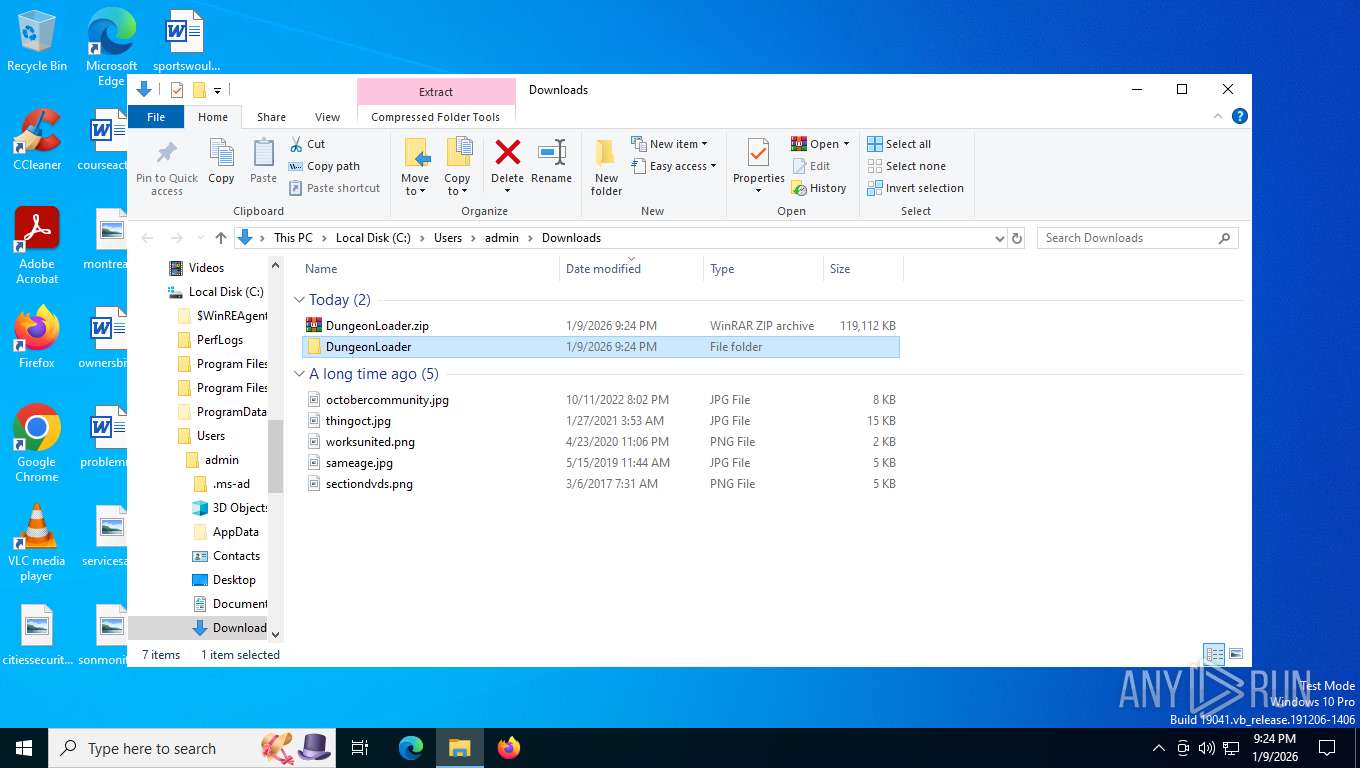
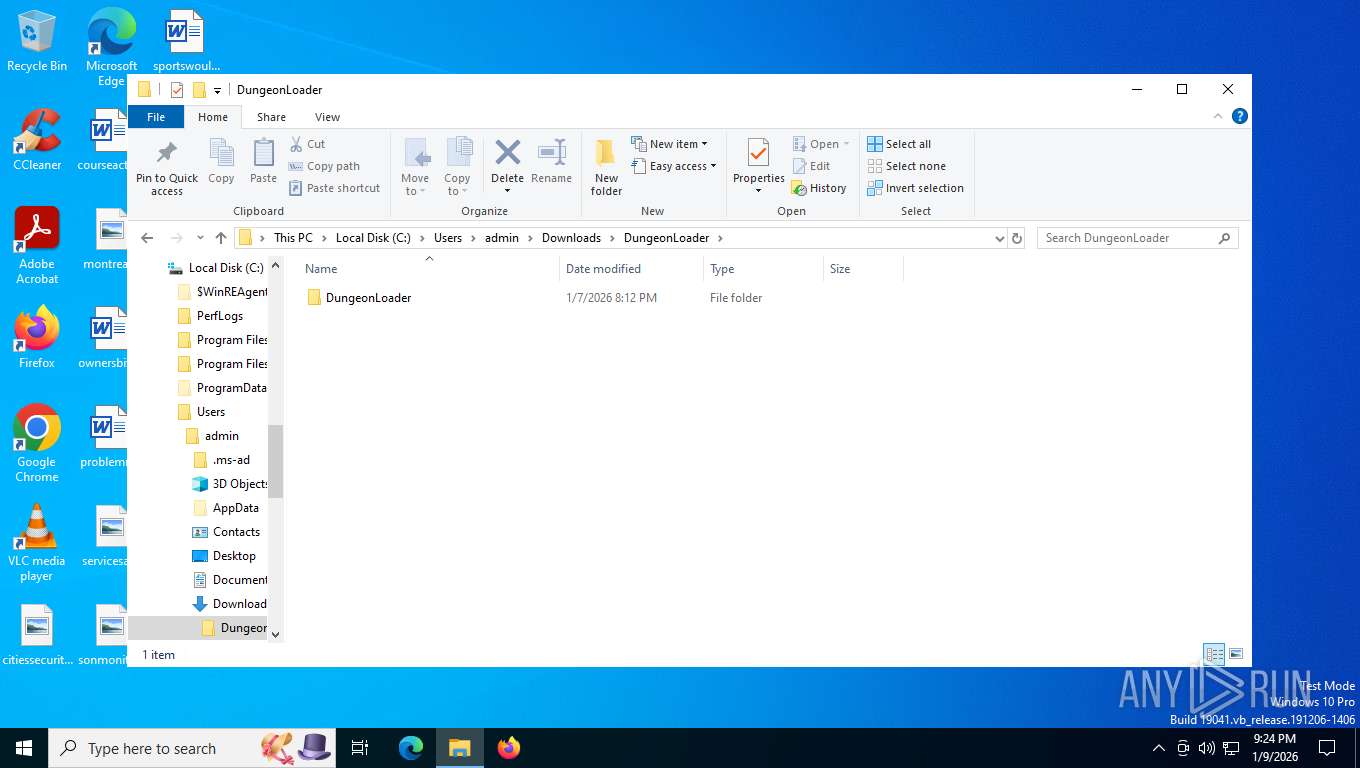
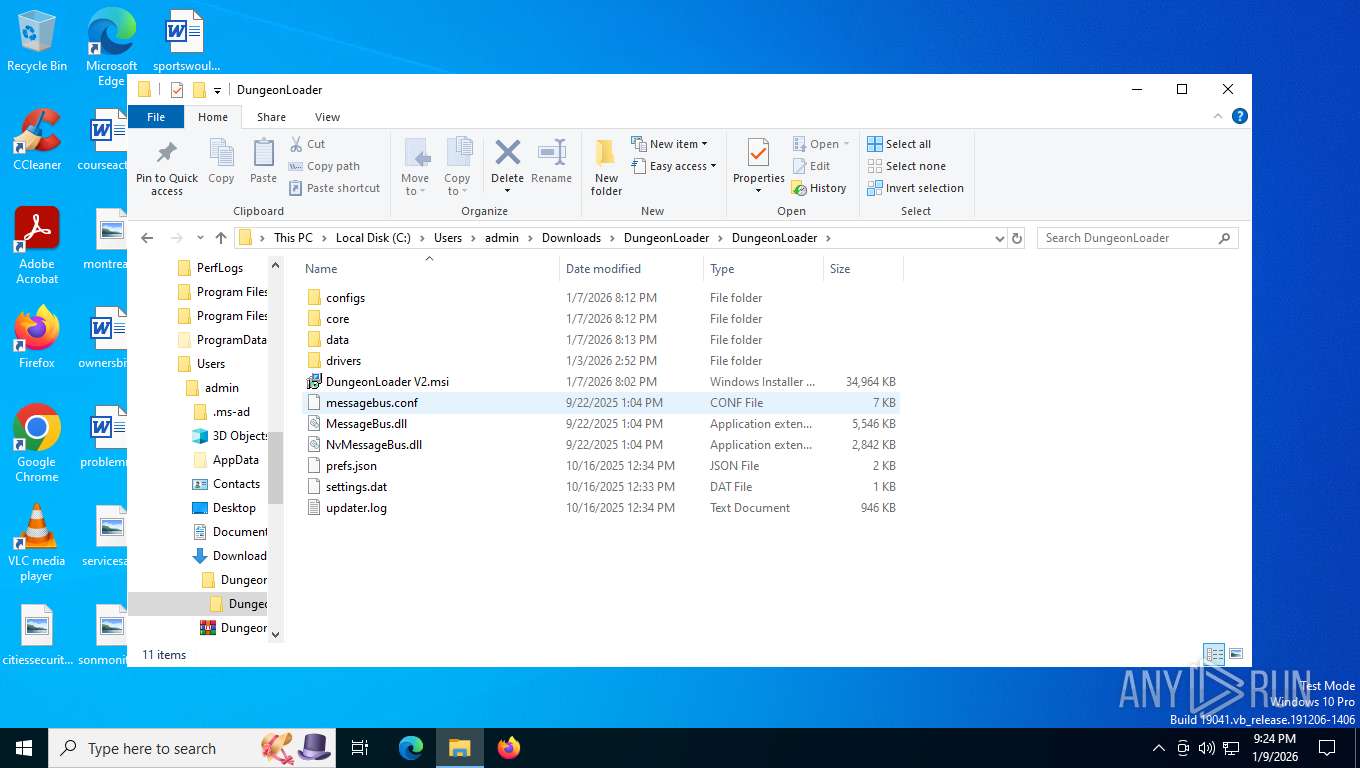
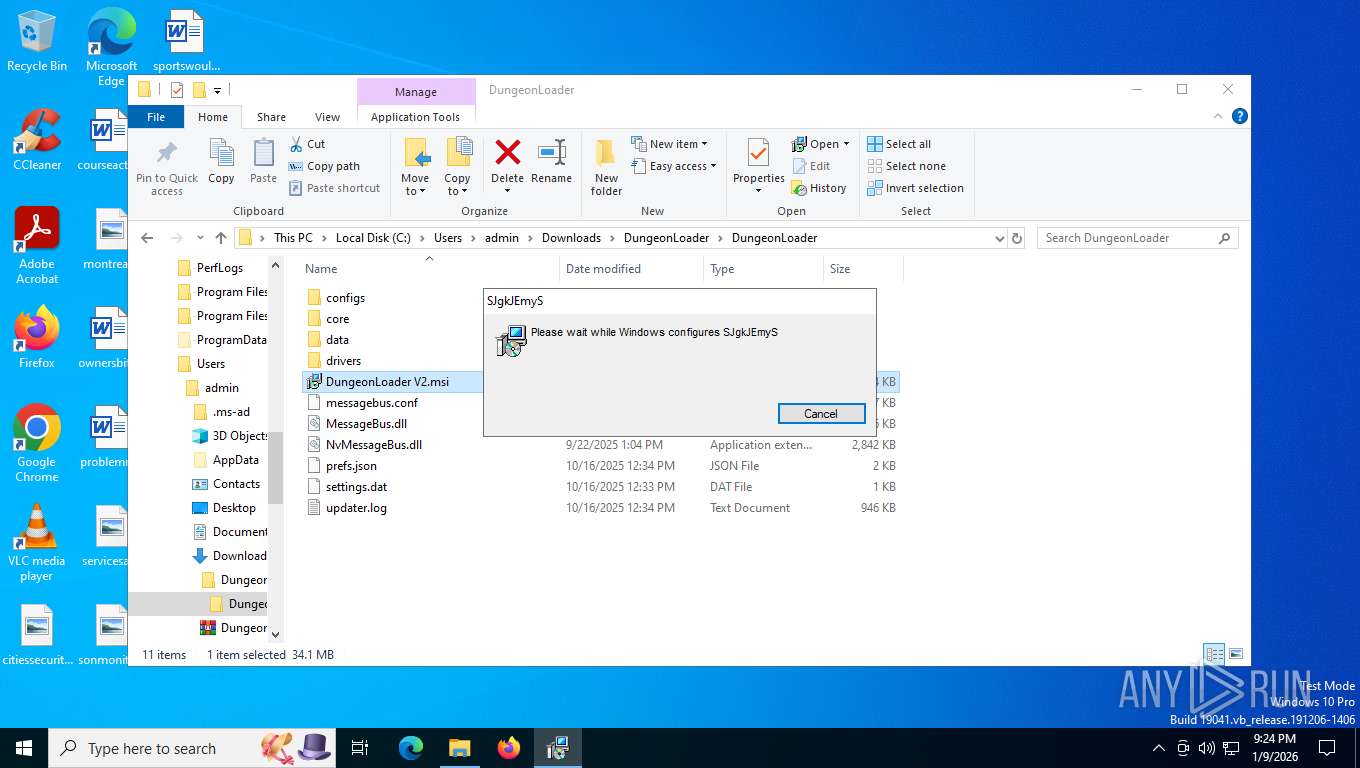
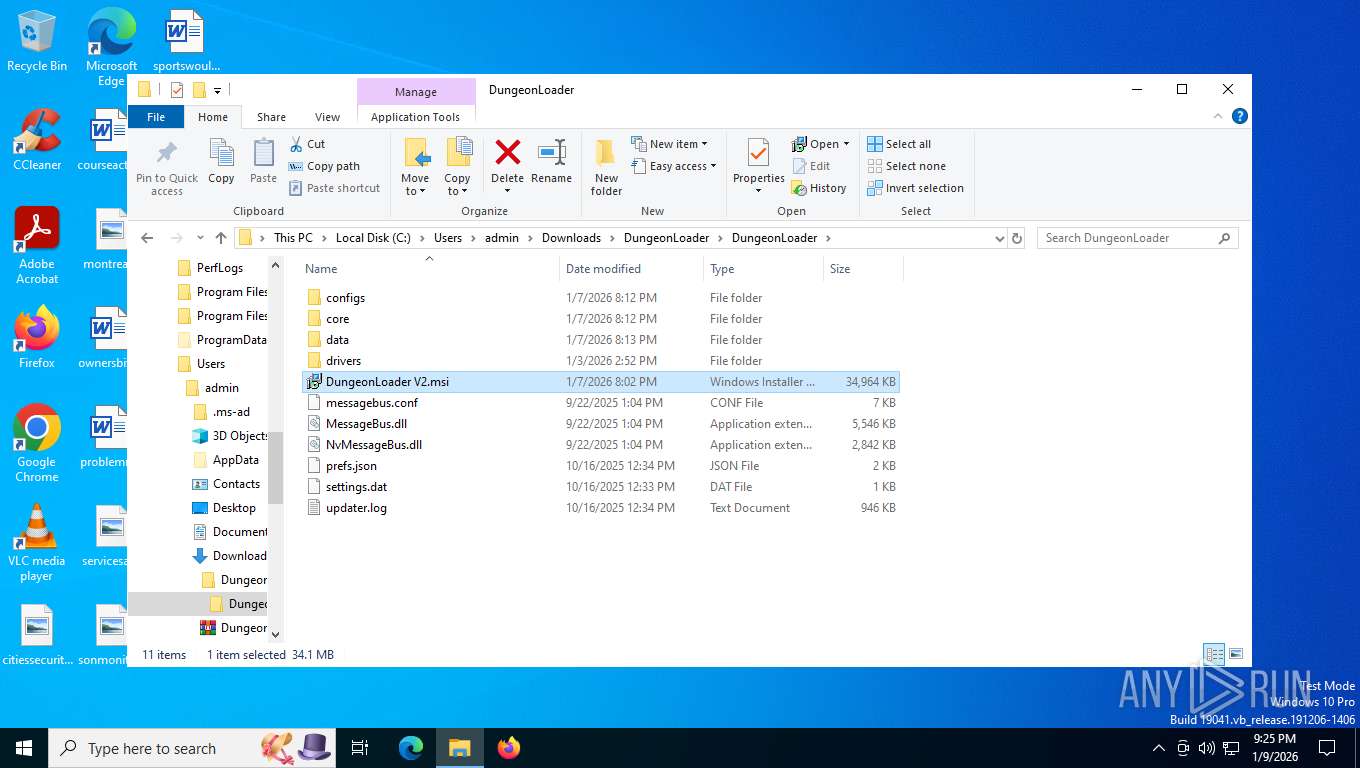
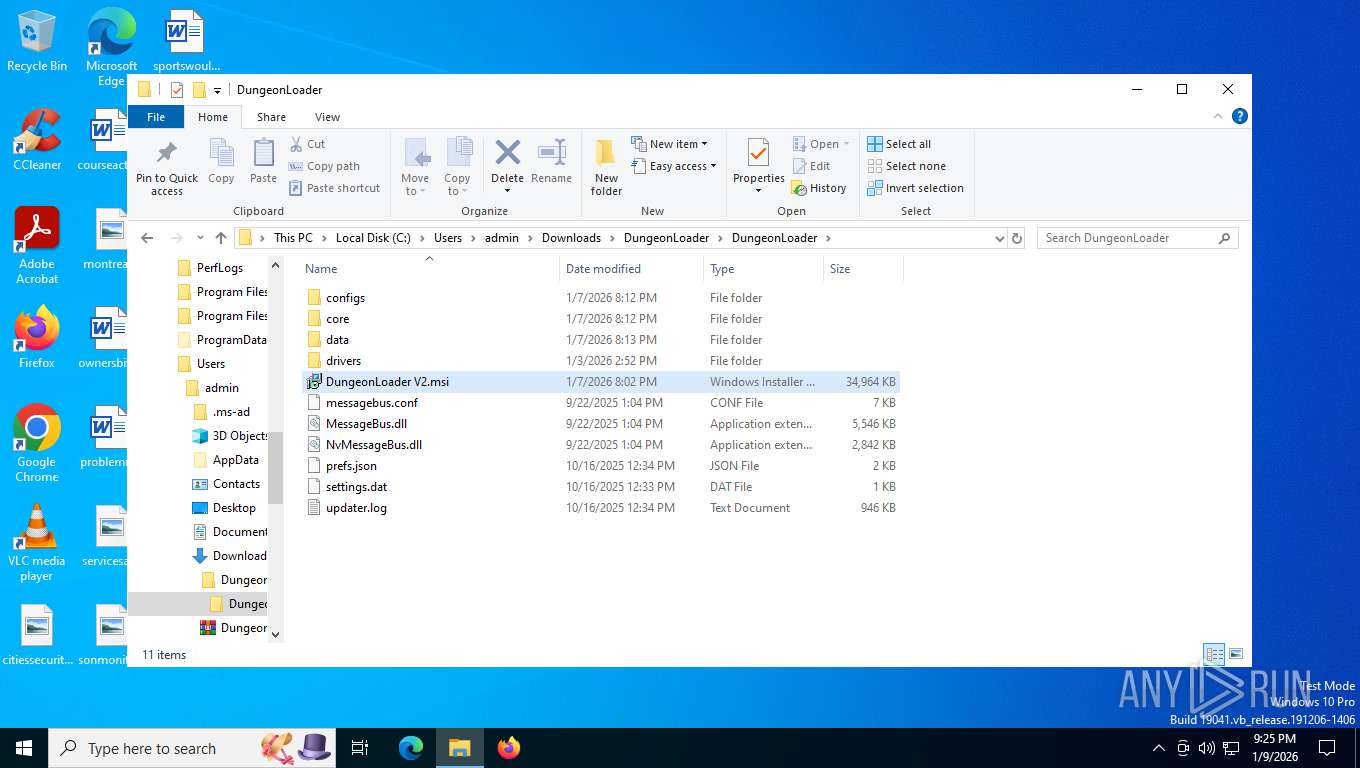
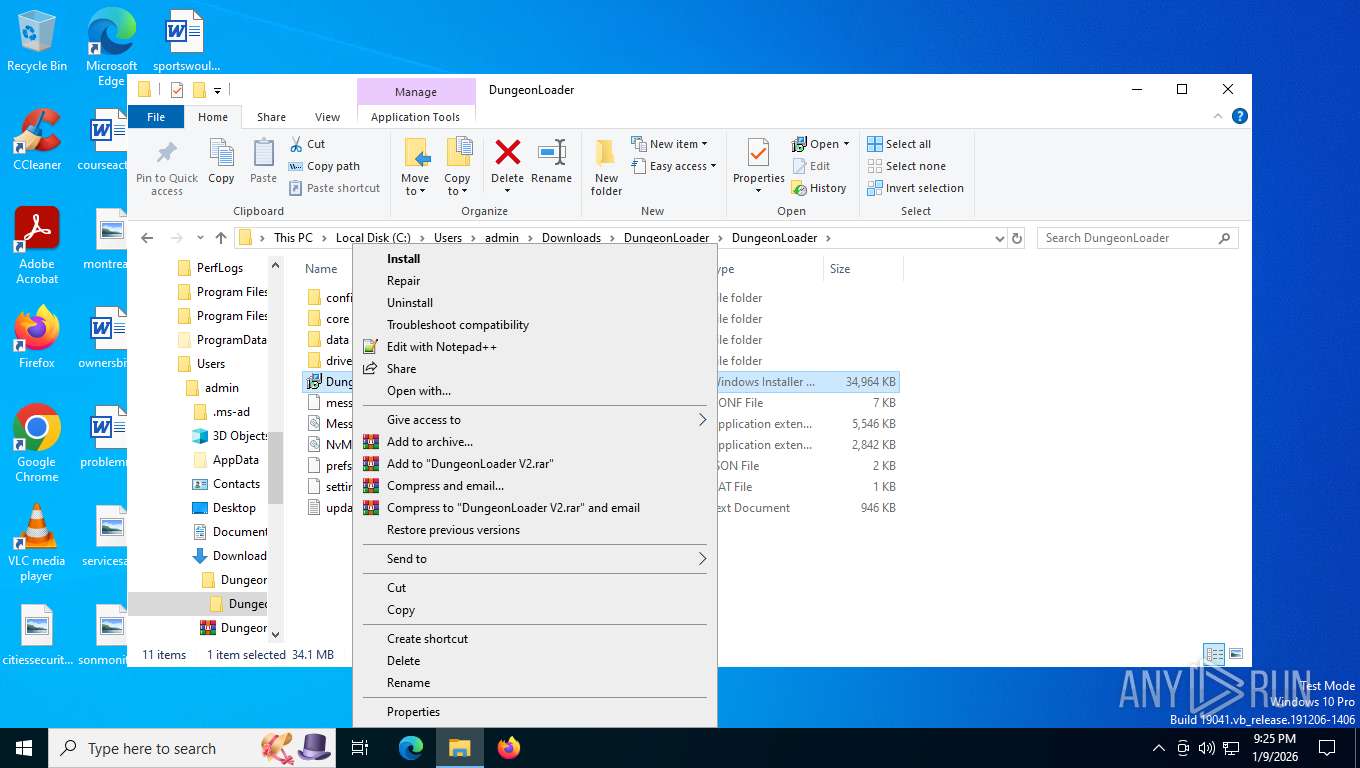
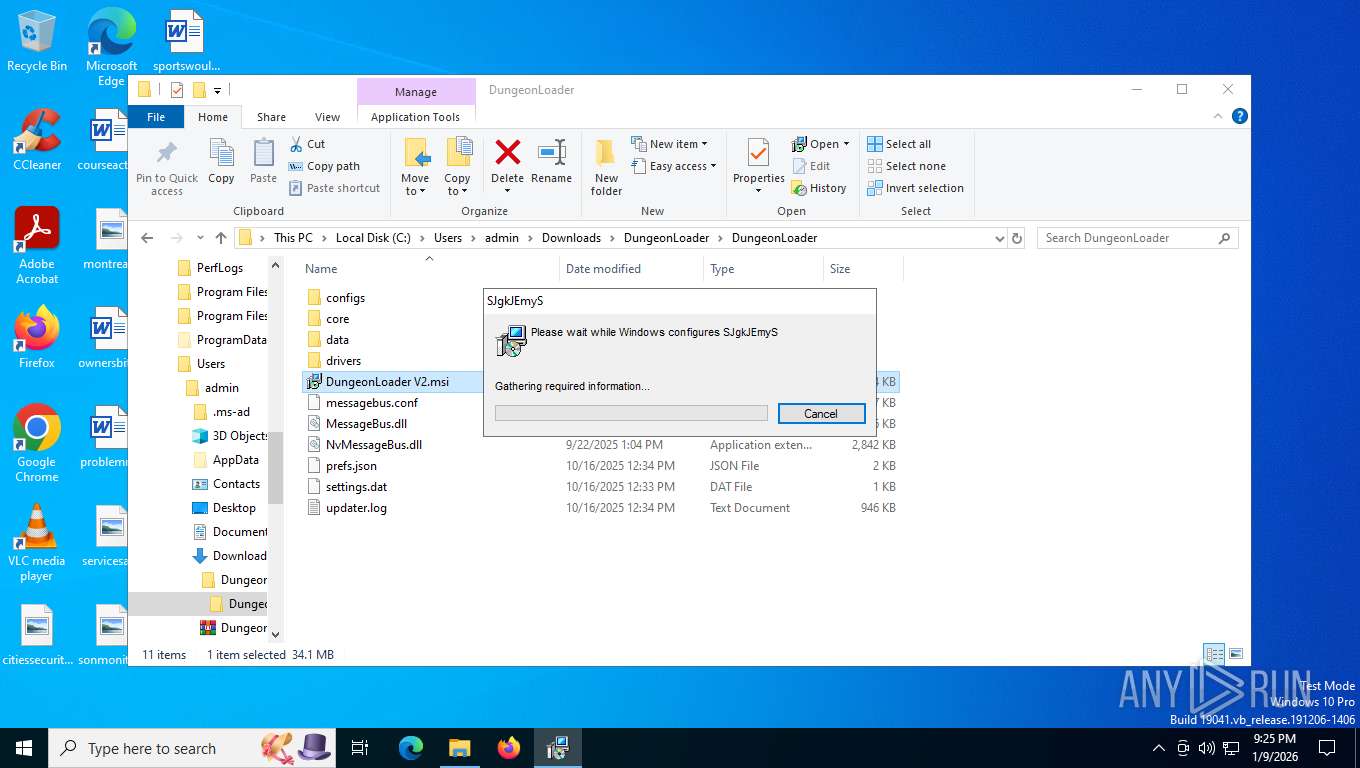
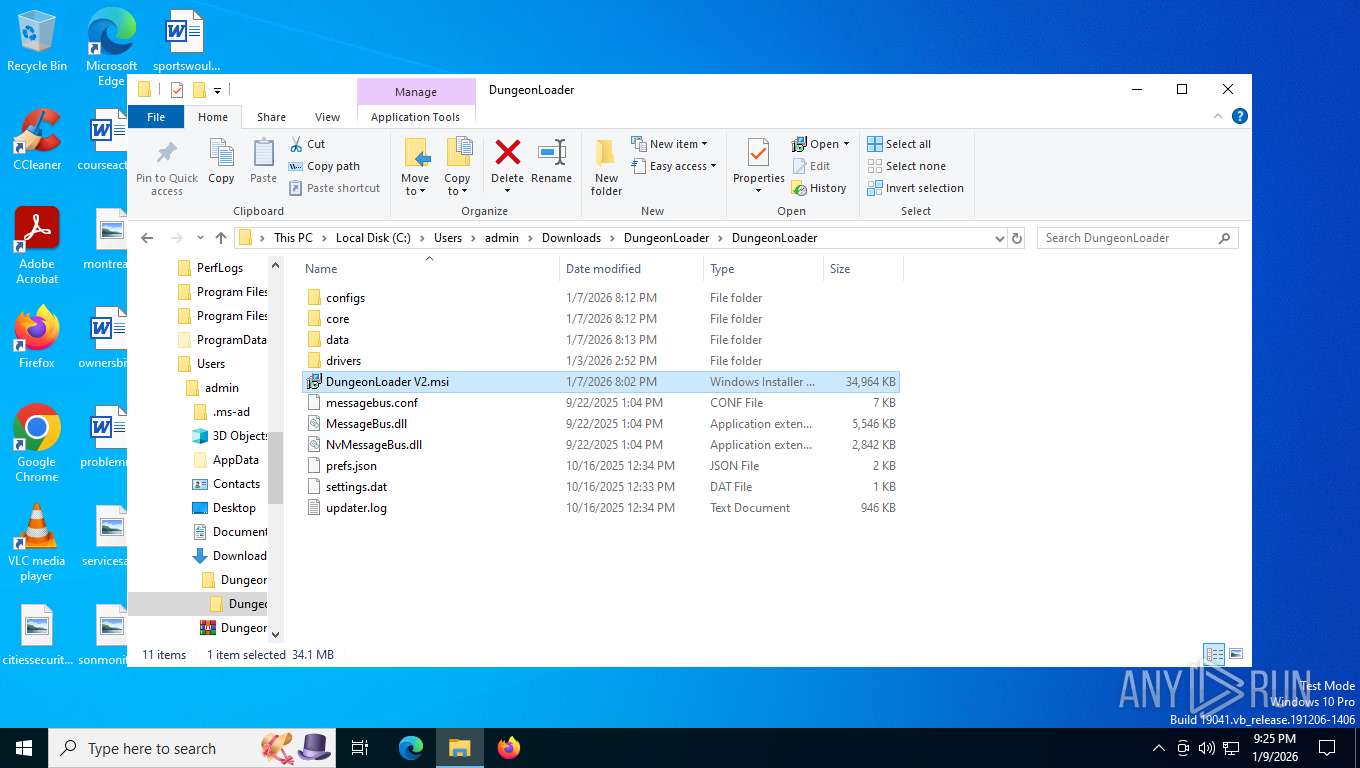
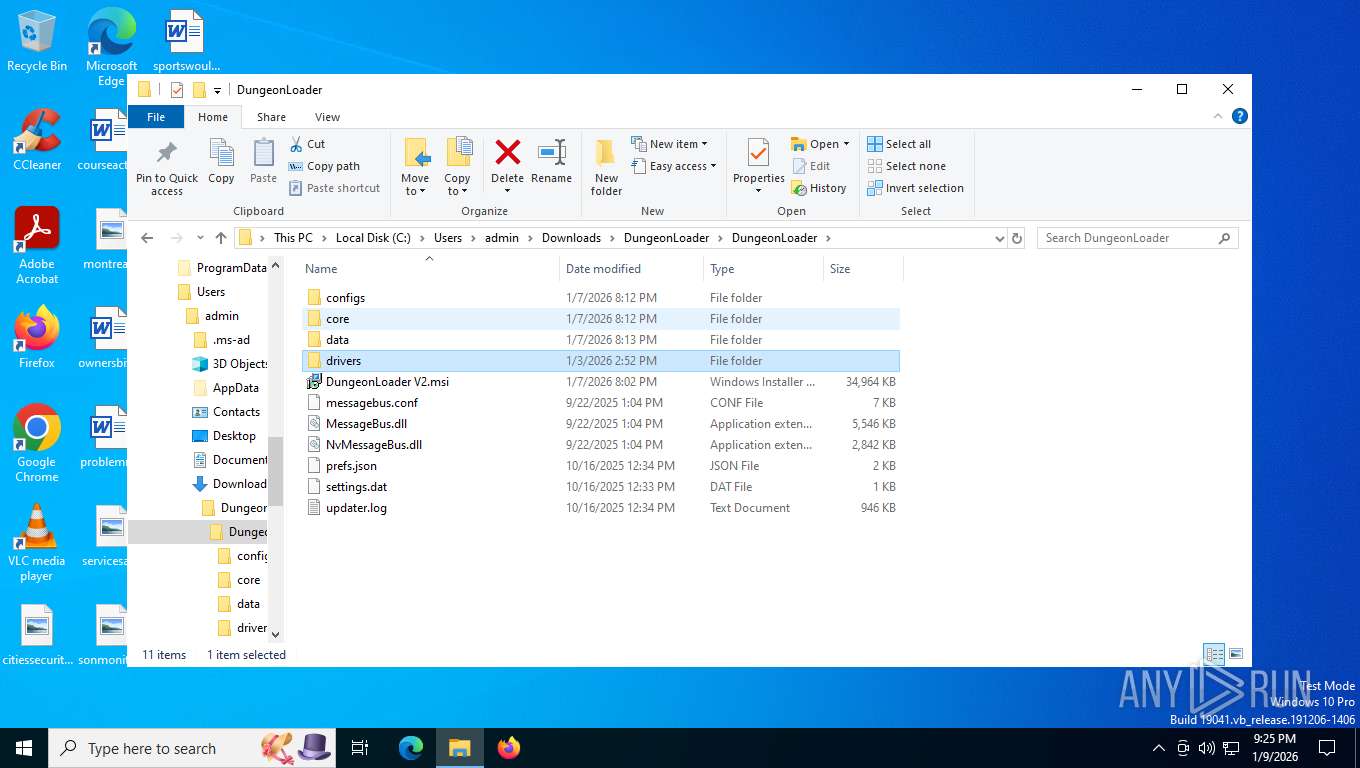
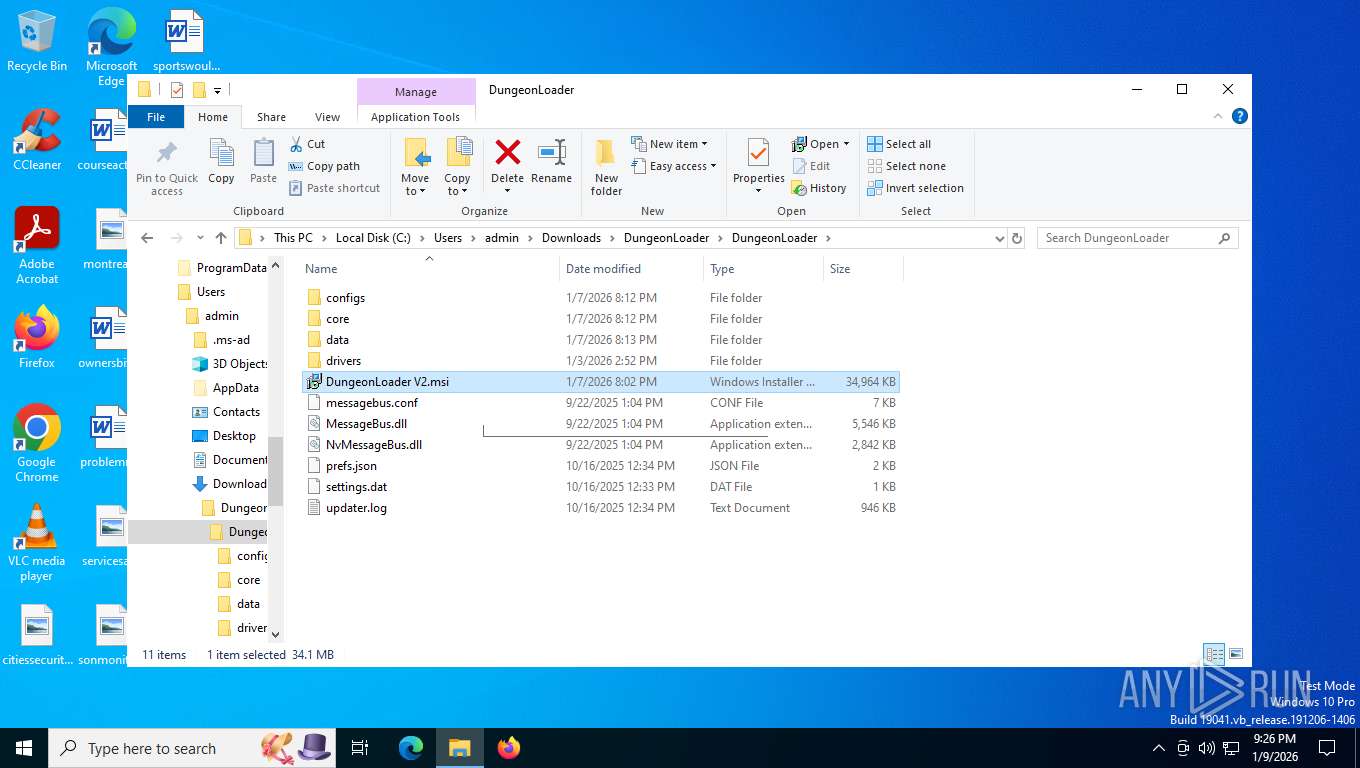
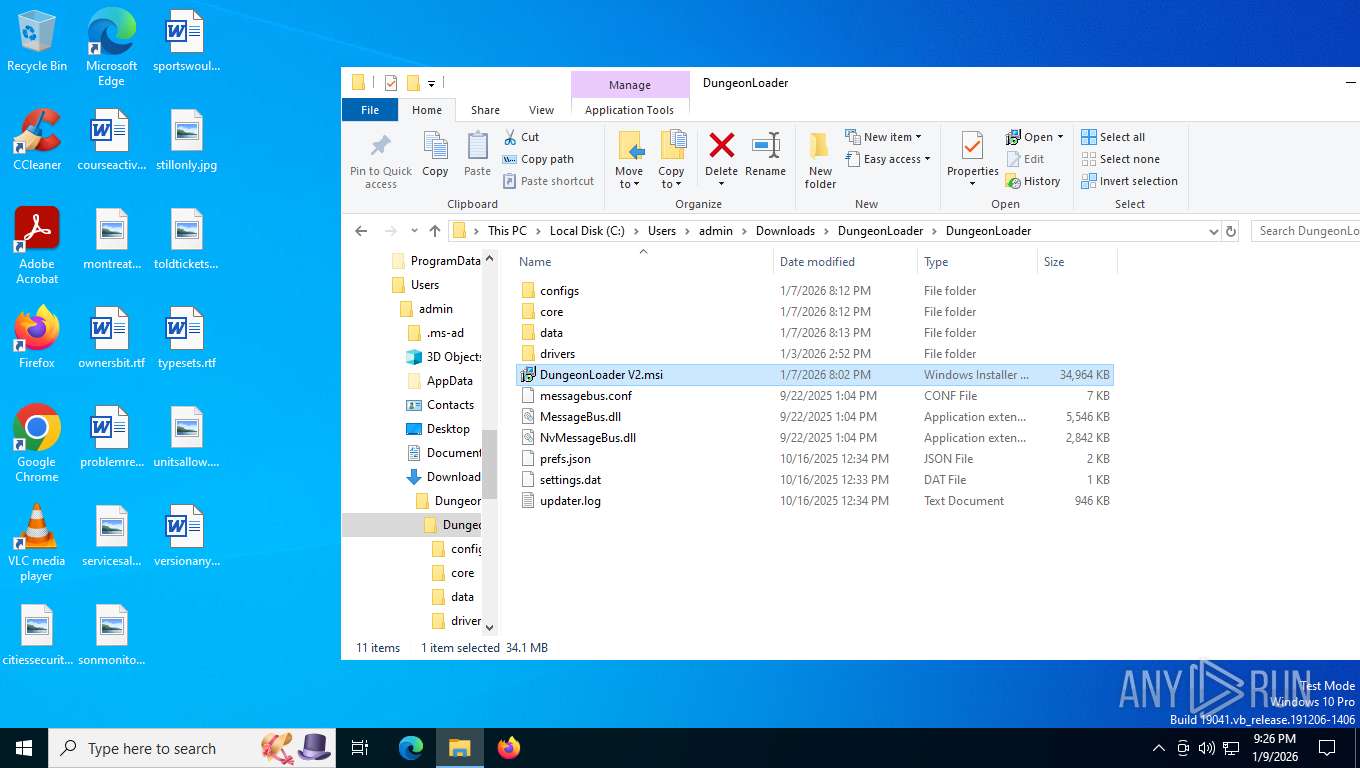
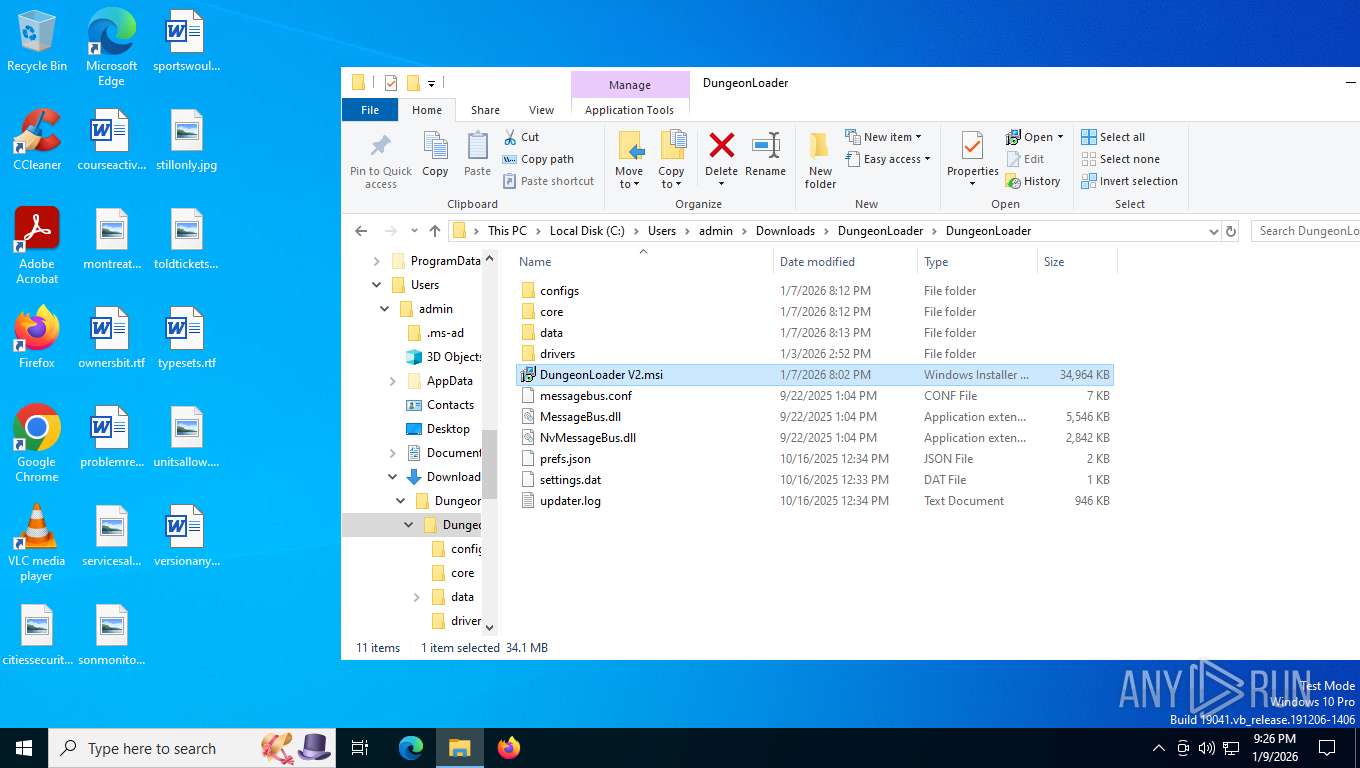
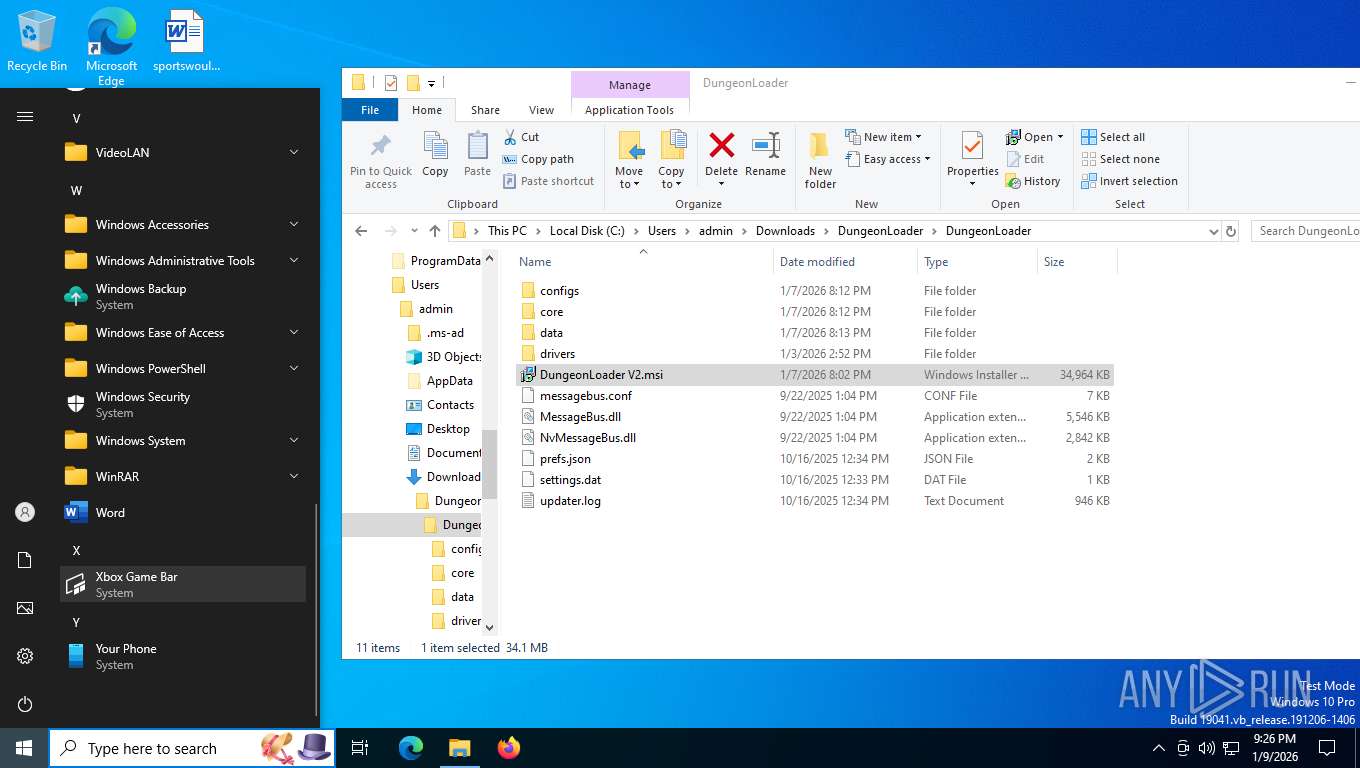
Manual execution by a user
- WinRAR.exe (PID: 8816)
- msiexec.exe (PID: 8908)
- msiexec.exe (PID: 7388)
- msiexec.exe (PID: 8096)
- msiexec.exe (PID: 2140)
- msiexec.exe (PID: 2236)
The sample compiled with english language support
- WinRAR.exe (PID: 8816)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 8816)
Manages system restore points
- SrTasks.exe (PID: 4828)
Reads product name
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 8916)
Reads CPU info
- puceS.exe (PID: 7376)
- puceS.exe (PID: 1088)
- puceS.exe (PID: 7220)
- puceS.exe (PID: 8060)
- puceS.exe (PID: 8916)
Checks proxy server information
- slui.exe (PID: 9192)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
222
Monitored processes
70
Malicious processes
1
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x139c460,0x139c46c,0x139c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 800 | tasklist /fo csv /nh | C:\Windows\System32\tasklist.exe | — | puceS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | "C:\Users\admin\AppData\Local\QNzJcmlW\puceS.exe" "fzIaXUTljrFgix" | C:\Users\admin\AppData\Local\QNzJcmlW\puceS.exe | — | wscript.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 1 Version: 20.19.0 Modules
| |||||||||||||||
| 1188 | wscript.exe //B /e:vbscript "sKbscaqnRcULro" | C:\Windows\System32\wscript.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=15 --always-read-main-dll --field-trial-handle=6668,i,14547610156471464413,9378003759885854064,262144 --variations-seed-version --mojo-platform-channel-handle=6764 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1844 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4980,i,14547610156471464413,9378003759885854064,262144 --variations-seed-version --mojo-platform-channel-handle=3840 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
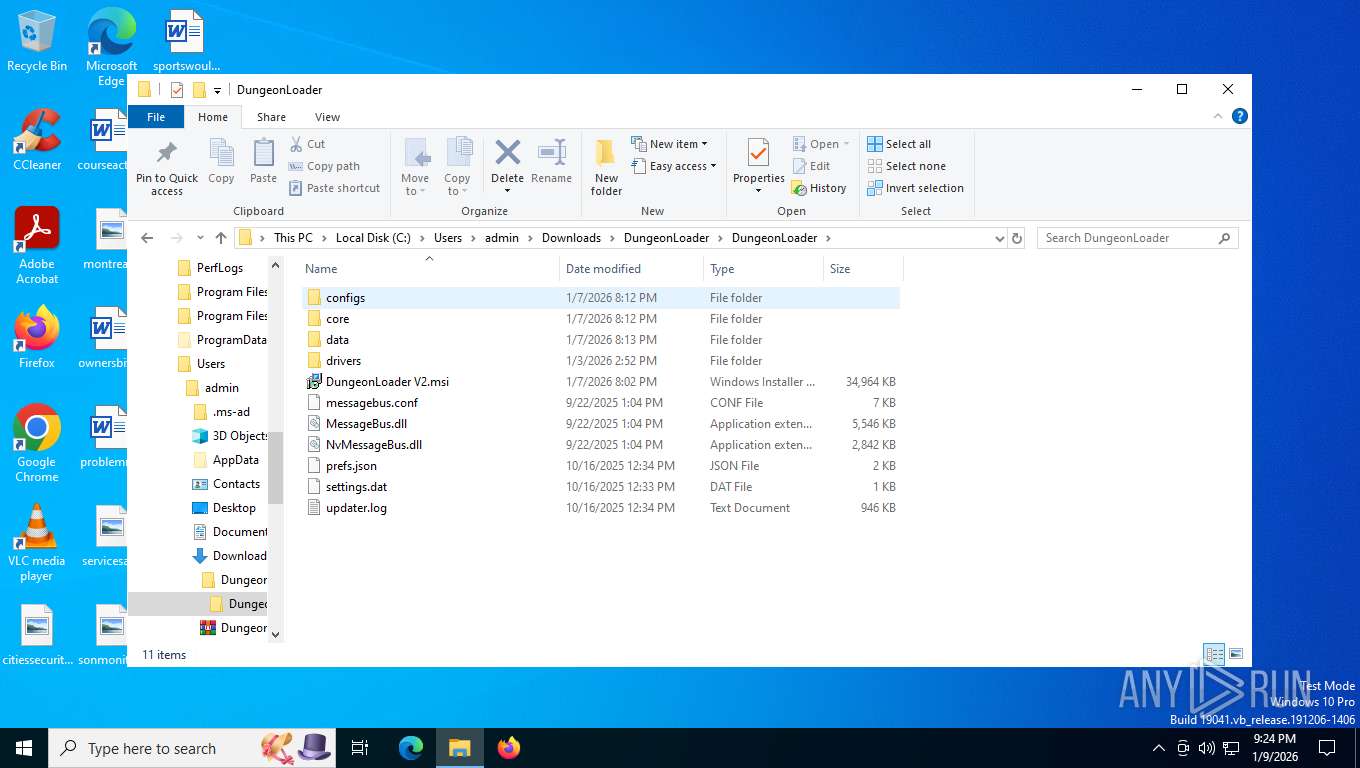
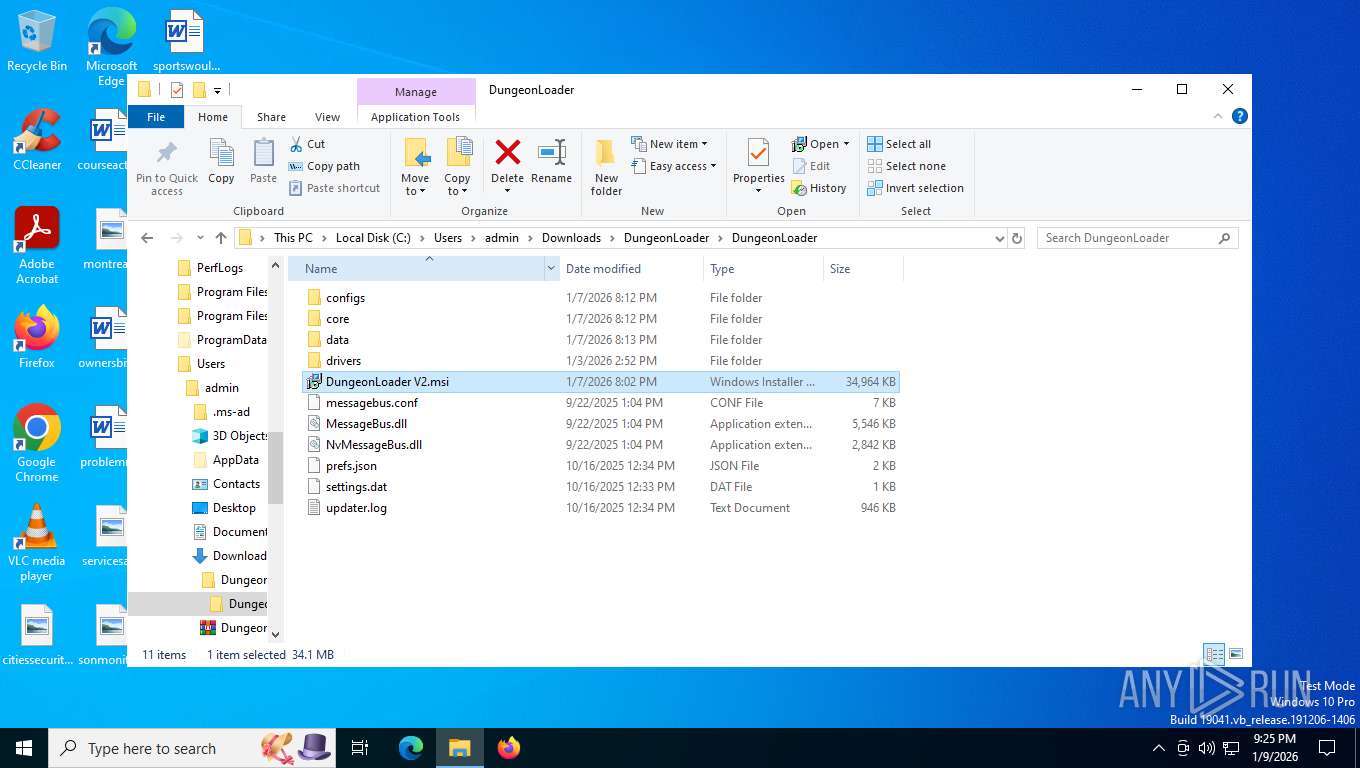
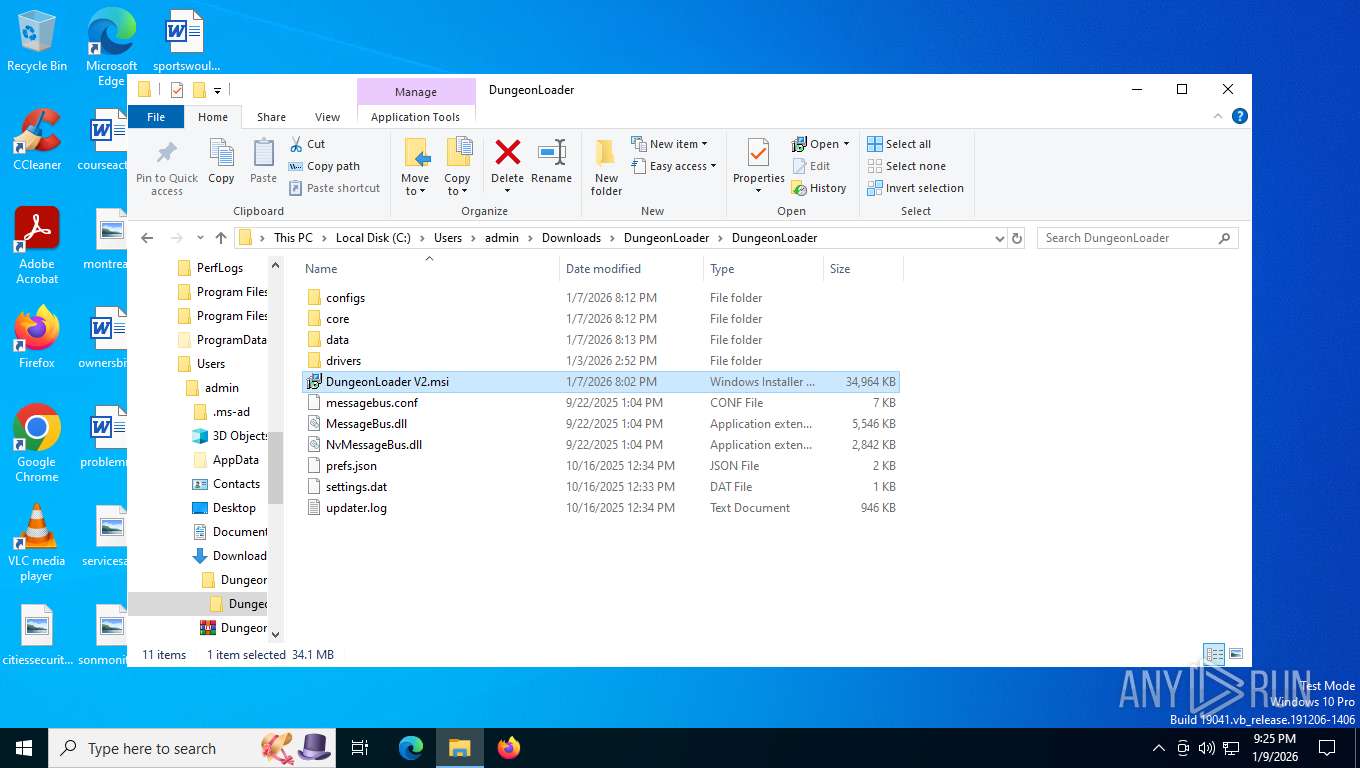
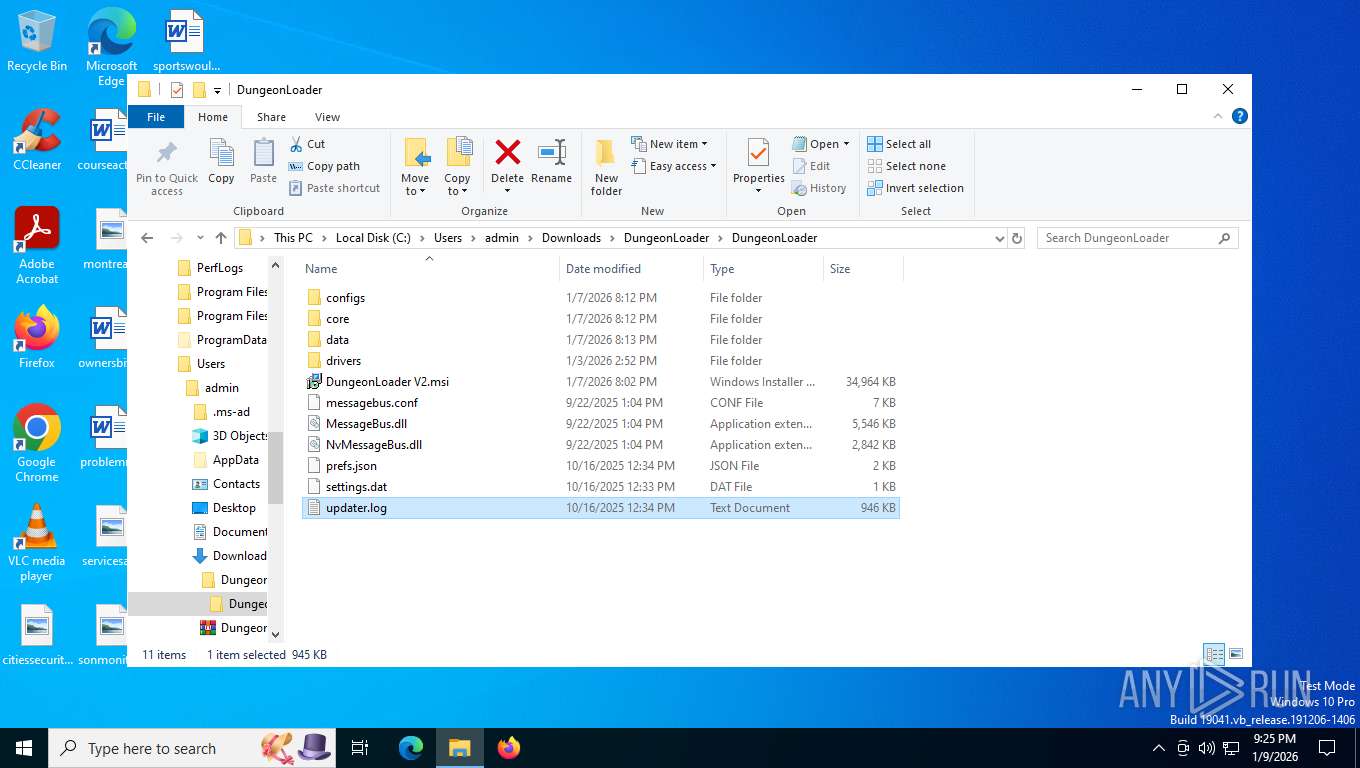
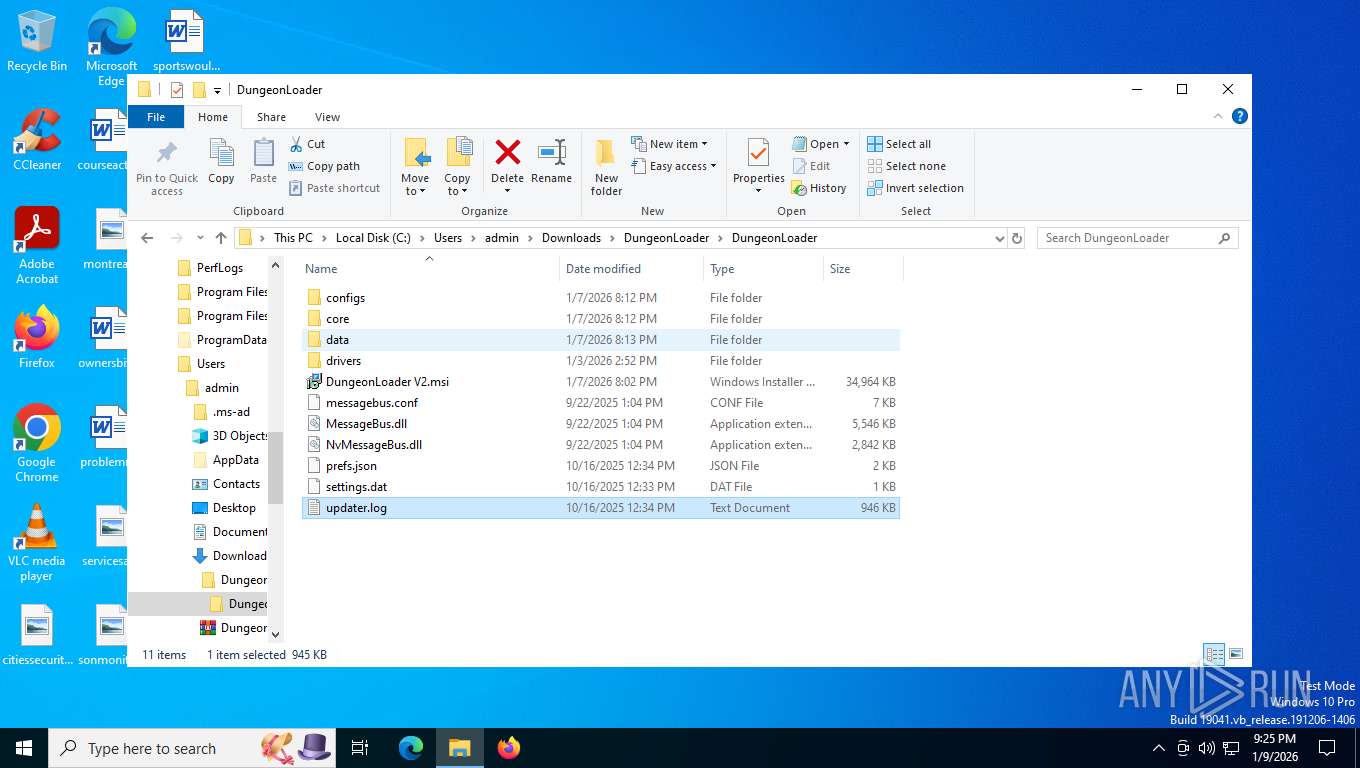
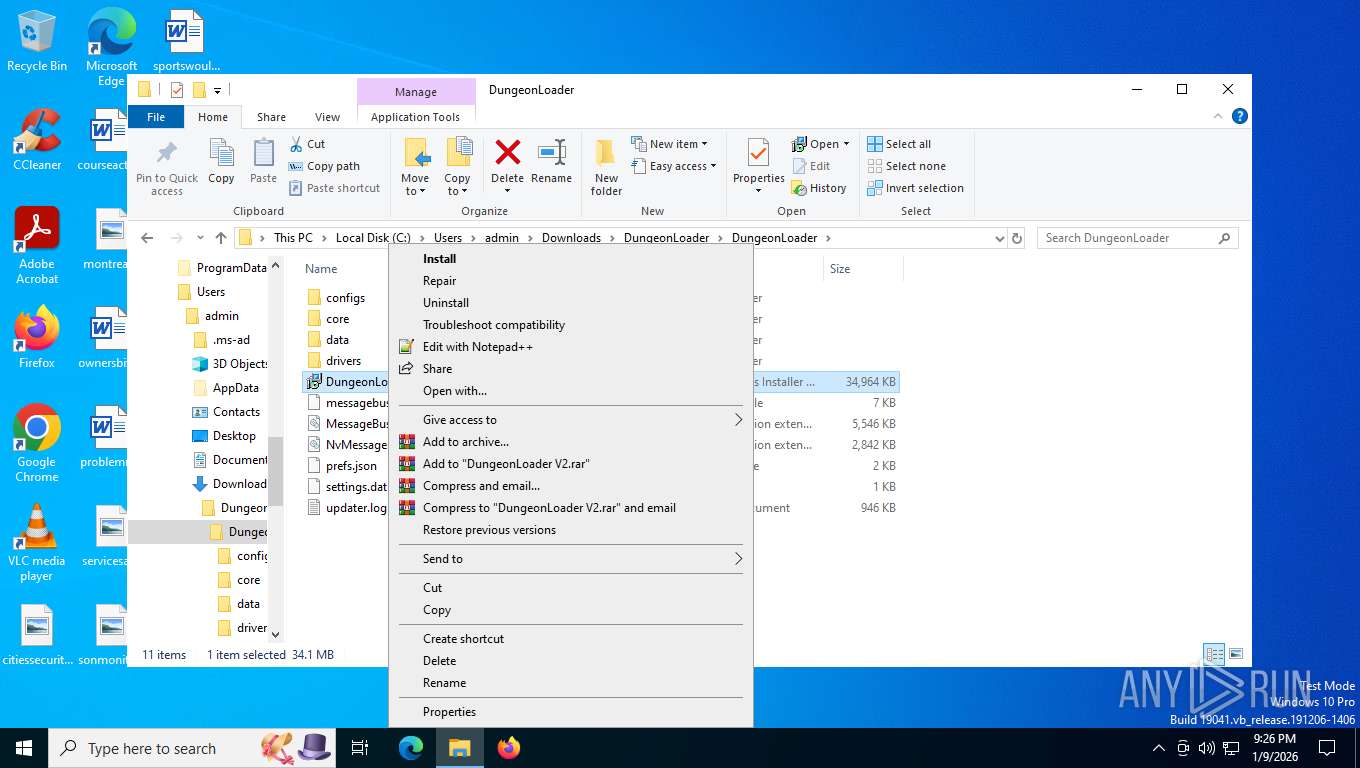
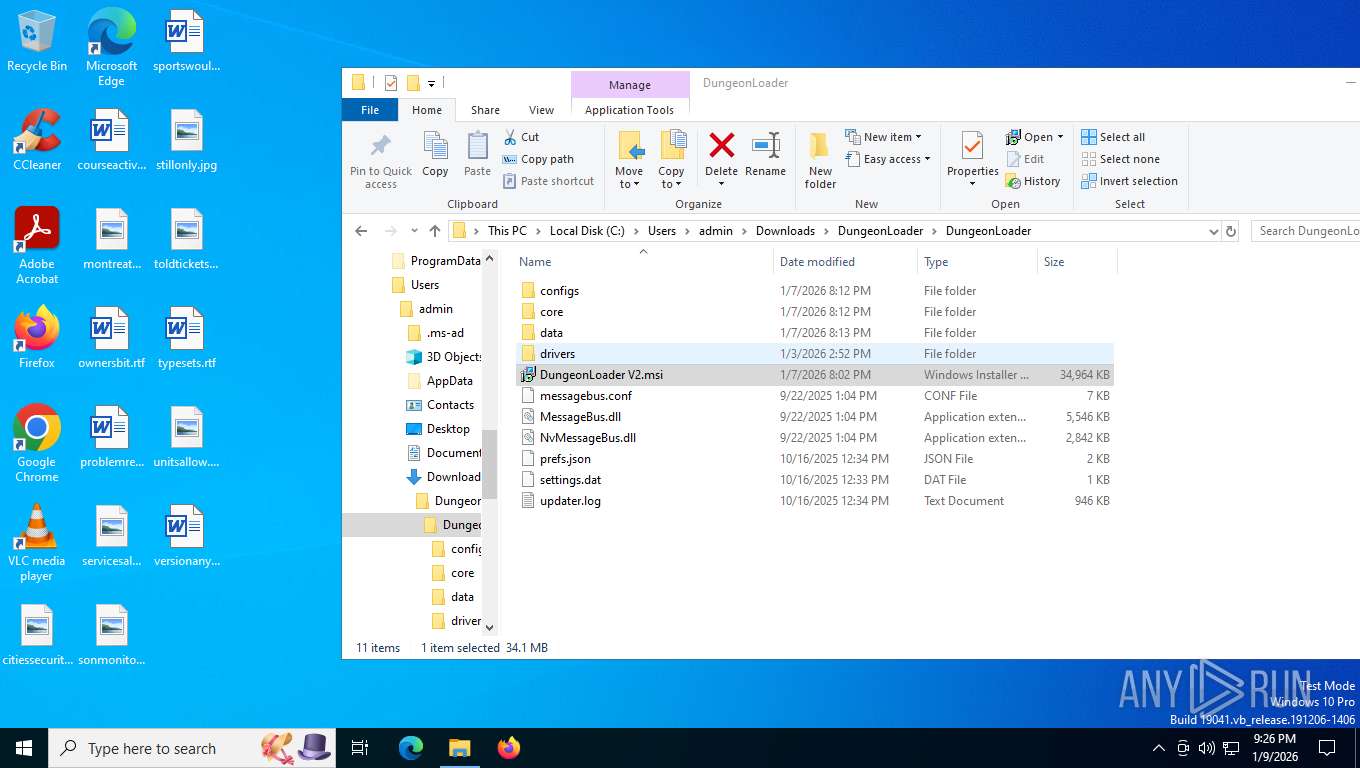
| 2140 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\Downloads\DungeonLoader\DungeonLoader\DungeonLoader V2.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\Downloads\DungeonLoader\DungeonLoader\DungeonLoader V2.msi" | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2292 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | puceS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
35 950
Read events
35 788
Write events
153
Delete events
9
Modification events
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (8816) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (8944) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000097A3B94FD881DC01F022000010230000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8944) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000097A3B94FD881DC01F022000010230000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8944) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000E13B3350D881DC01F022000010230000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8944) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000BA003850D881DC01F0220000A0230000E8030000010000000000000000000000C5857B5806503841B08D2F4F9DB3685200000000000000000000000000000000 | |||
| (PID) Process: | (8992) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E8B04850D881DC012023000040230000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
8
Suspicious files
146
Text files
277
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFfe025.TMP | — | |
MD5:— | SHA256:— | |||
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFfe035.TMP | — | |
MD5:— | SHA256:— | |||
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFfe035.TMP | — | |
MD5:— | SHA256:— | |||
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFfe035.TMP | — | |
MD5:— | SHA256:— | |||
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFfe035.TMP | — | |
MD5:— | SHA256:— | |||
| 7608 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
87
TCP/UDP connections
79
DNS requests
64
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7948 | msedge.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=Xgm1kCkCnH8orzMdJ9ZhCwCw31uA1H3vdUlYo07TLIY840oE%2FhrQ9eARvwpkmPIiO0iGlKNk7BosY5%2B%2FofpbBMVIzlb8zhF9SdCrxUQwAt5CYx%2B0us54uUTlQ5d6zjWYA%2BmnqQ%3D%3D | US | — | — | unknown |
7948 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=65&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1741678270&lafgdate=0 | US | text | 768 b | whitelisted |
7948 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:6T60Y6Arq1EmIVkvR8J5Ty0FpZhunp8dDEZr-azrO84&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 95 b | whitelisted |
7948 | msedge.exe | GET | 200 | 172.67.139.105:443 | https://dungeonsoft.lol/s/inter/v20/UcCO3FwrK3iLTeHuS_nVMrMxCp50SjIw2boKoduKmMEVuDyYMZg.ttf | US | binary | 128 Kb | unknown |
7948 | msedge.exe | GET | 200 | 172.67.139.105:443 | https://dungeonsoft.lol/s/inter/v20/UcCO3FwrK3iLTeHuS_nVMrMxCp50SjIw2boKoduKmMEVuGKYMZg.ttf | US | binary | 128 Kb | unknown |
7948 | msedge.exe | GET | 200 | 2.16.204.141:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 128 Kb | whitelisted |
7948 | msedge.exe | GET | 200 | 172.67.139.105:443 | https://dungeonsoft.lol/ | US | html | 24.5 Kb | unknown |
7948 | msedge.exe | GET | 200 | 172.67.139.105:443 | https://dungeonsoft.lol/s/inter/v20/UcCO3FwrK3iLTeHuS_nVMrMxCp50SjIw2boKoduKmMEVuFuYMZg.ttf | US | binary | 128 Kb | unknown |
7948 | msedge.exe | GET | 200 | 188.114.96.3:443 | https://api.lanyard.rest/v1/users/1017306008424566845 | US | text | 643 b | unknown |
7948 | msedge.exe | GET | 200 | 172.67.139.105:443 | https://dungeonsoft.lol/zensware/Webhook-IOS-App/refs/heads/main/icons/icon-192.png | US | image | 2.32 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4476 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6908 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7948 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7948 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7948 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7948 | msedge.exe | 104.18.22.222:443 | copilot.microsoft.com | CLOUDFLARENET | US | whitelisted |
7948 | msedge.exe | 172.67.139.105:443 | dungeonsoft.lol | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
dungeonsoft.lol |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
api.lanyard.rest |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7948 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7948 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7948 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
7948 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7948 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7948 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7948 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7948 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7948 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |