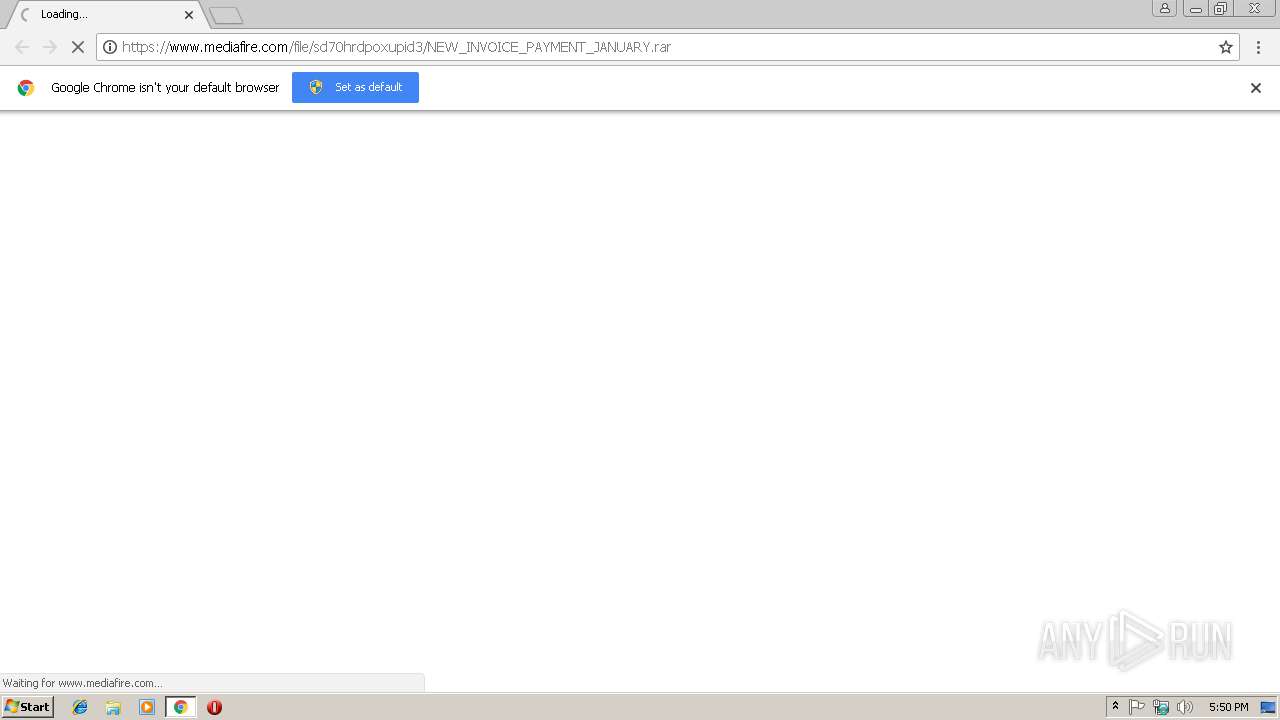
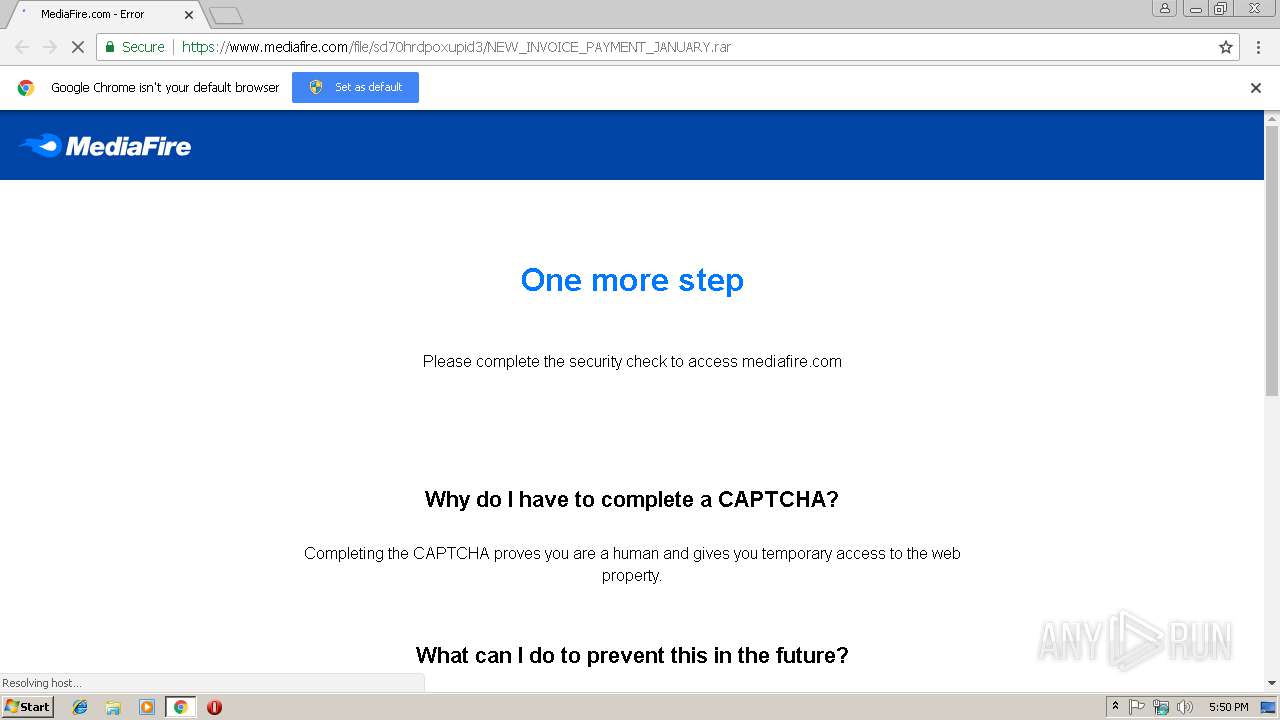
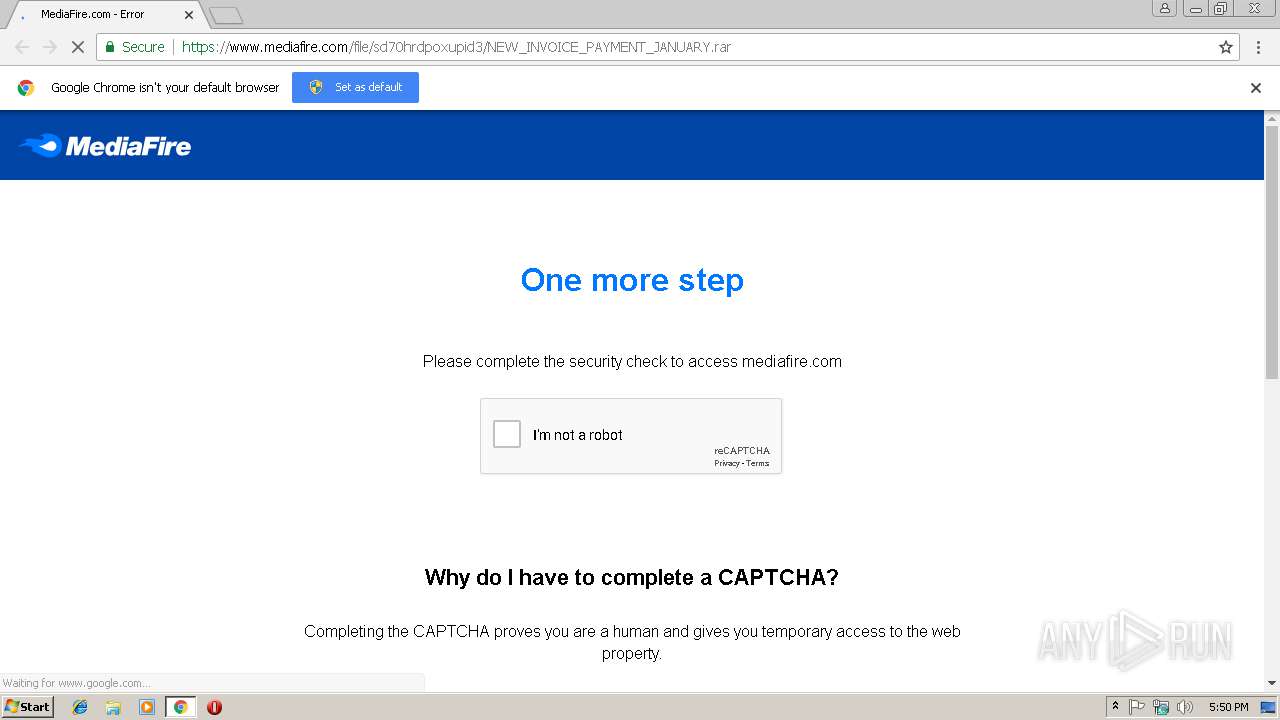
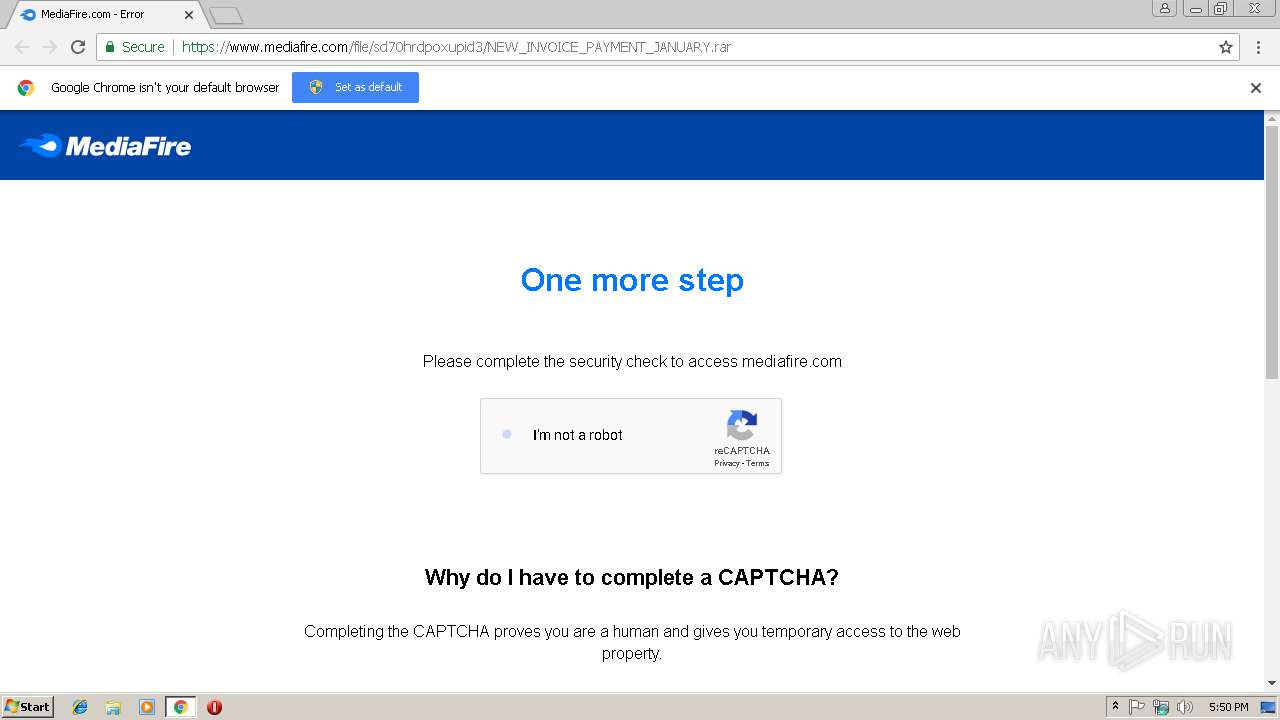
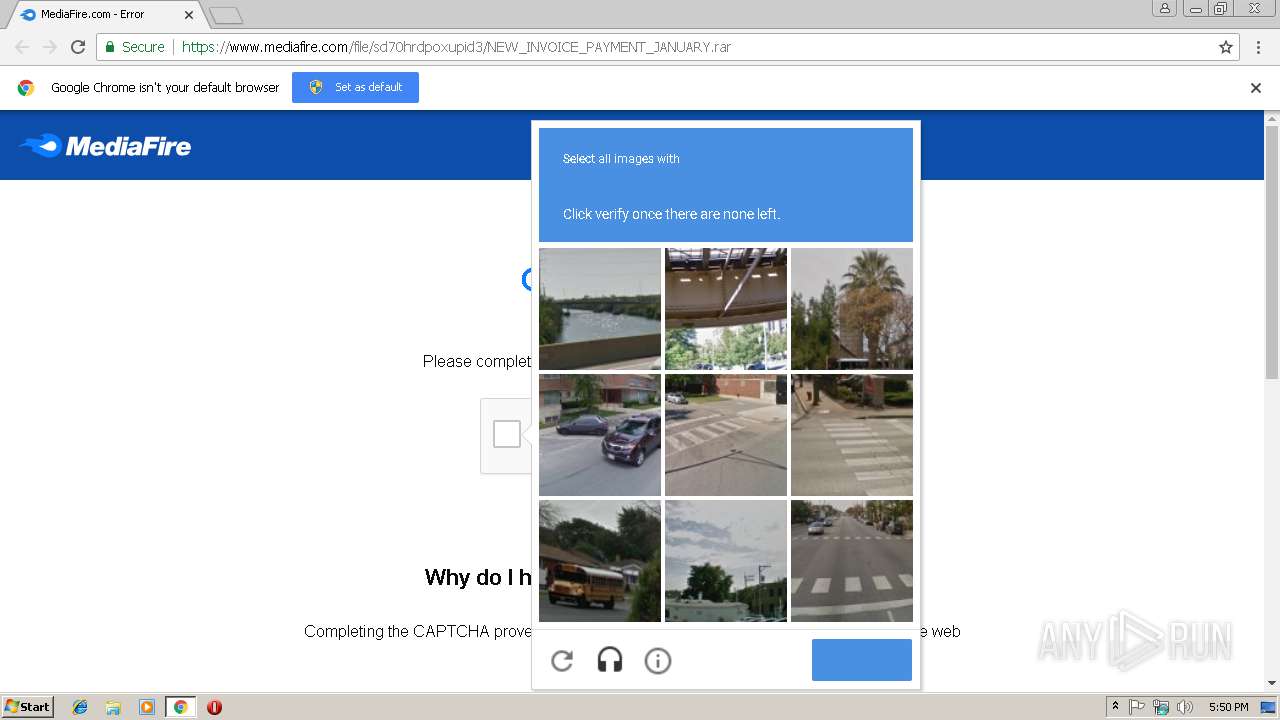
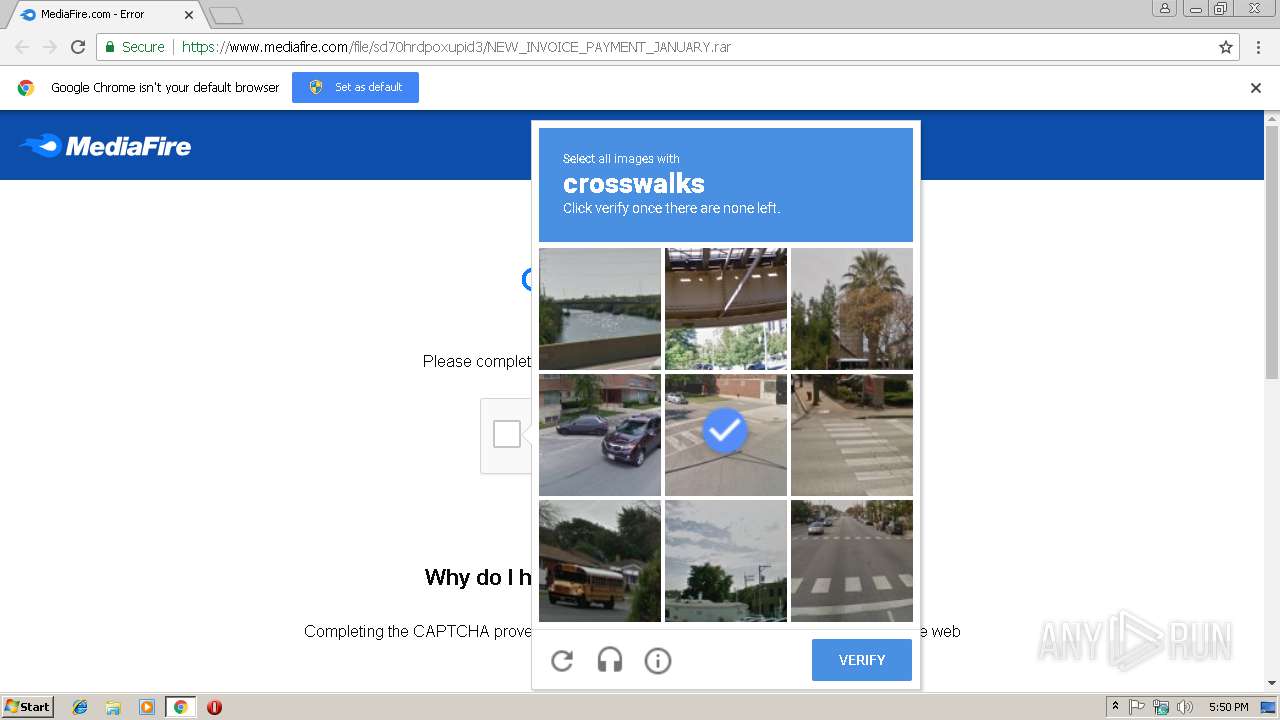
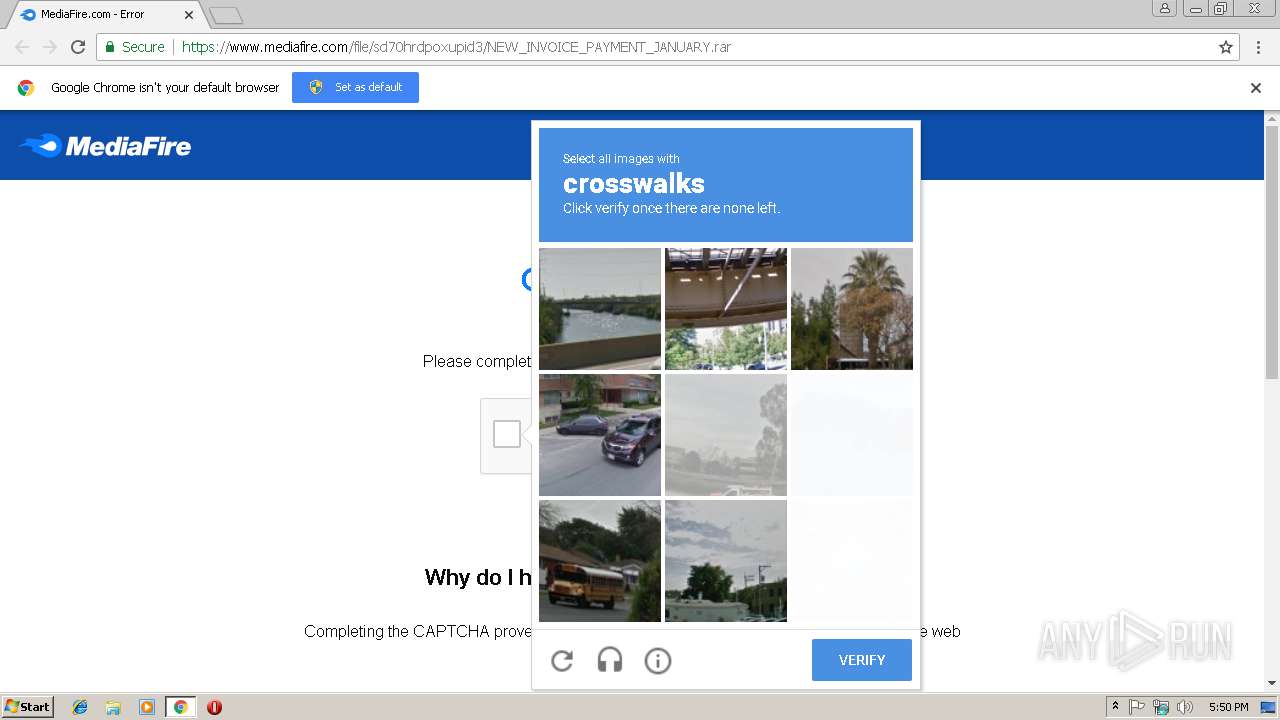
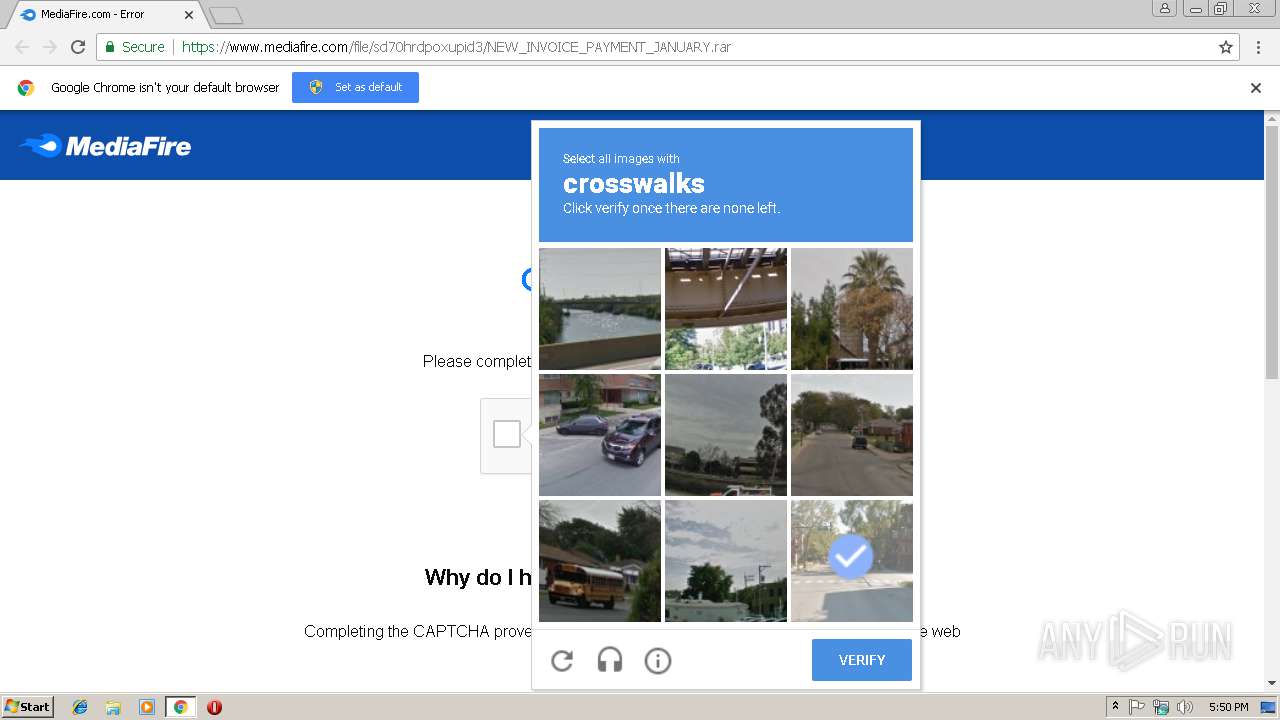
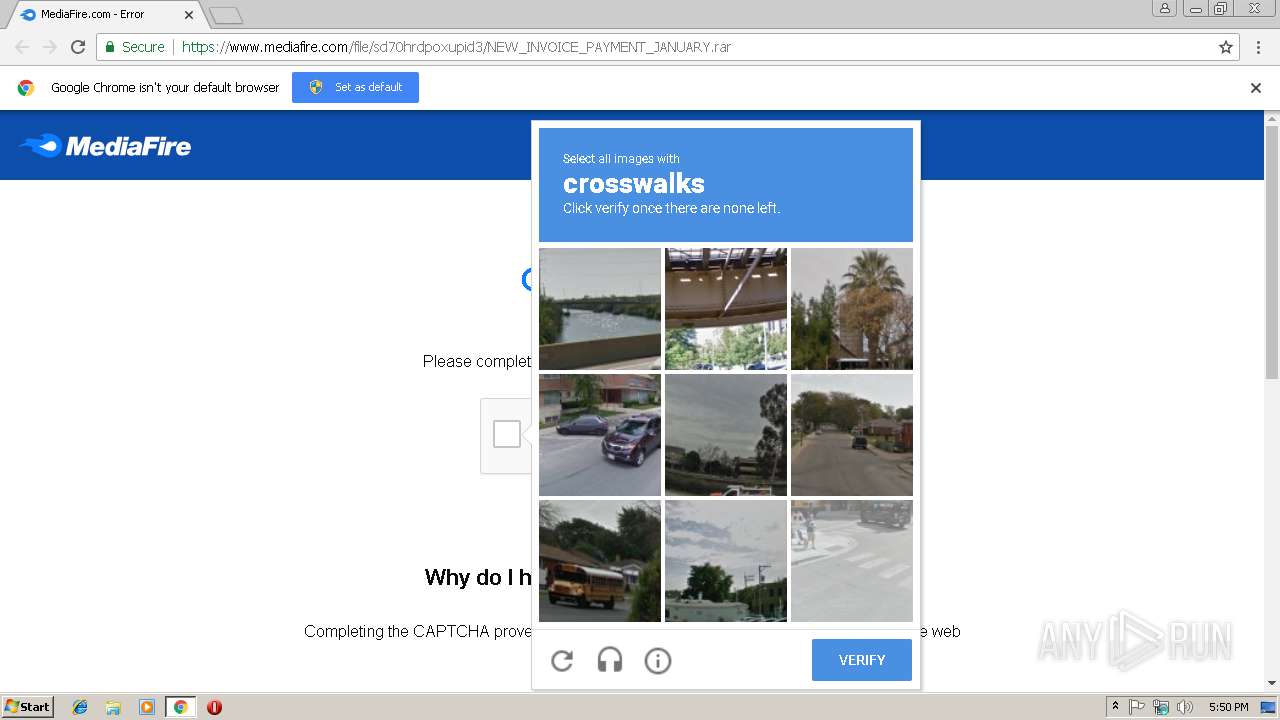
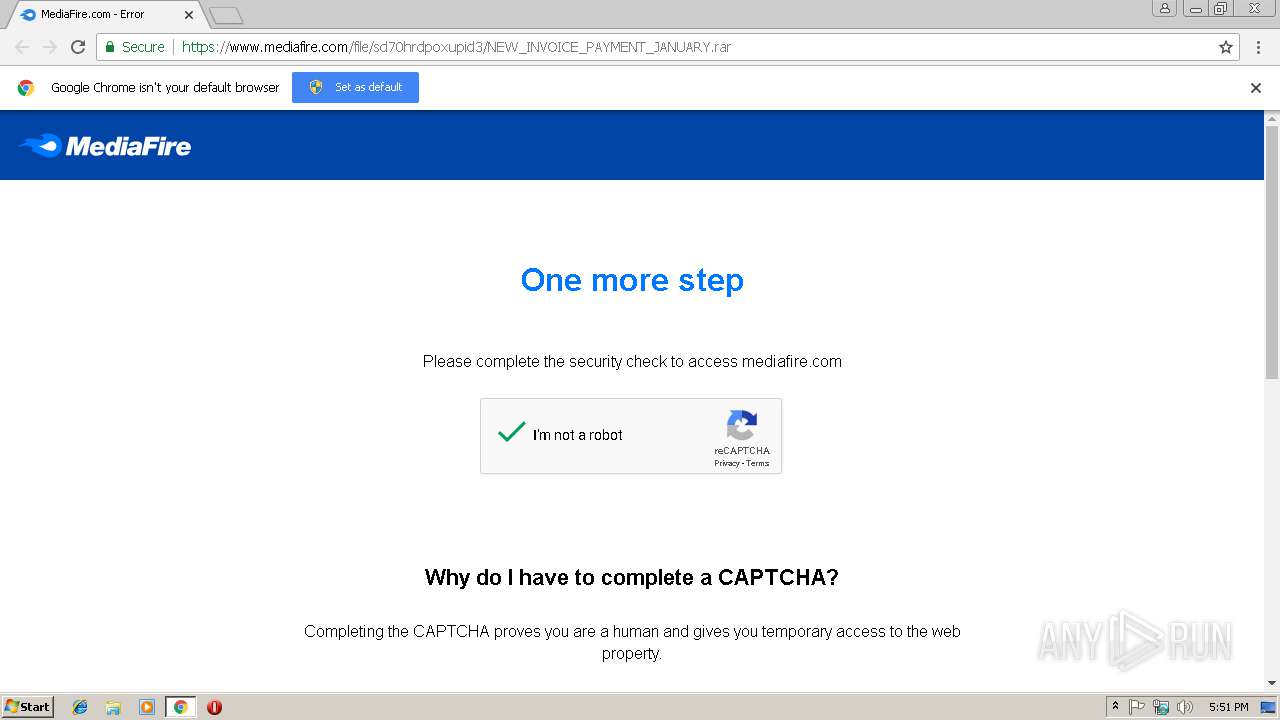
| URL: | https://www.mediafire.com/file/sd70hrdpoxupid3/NEW_INVOICE_PAYMENT_JANUARY.rar |
| Full analysis: | https://app.any.run/tasks/d8b80166-85a8-47f2-b457-01d0bb87d745 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2019, 17:50:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E1D04374F7D187E51737F968DE9119FD |
| SHA1: | 77C4581FD3A63122C0D3ACA90D3474BCDEEBBAD9 |
| SHA256: | 30097D798DFD5129298AFF40A45EA1A2CD79A0D3A9328518240636A38039D1C3 |
| SSDEEP: | 3:N8DSLw3eGUovF6QmT3nH6u8ogqqd:2OLw3eGD8QmT36u58d |
MALICIOUS
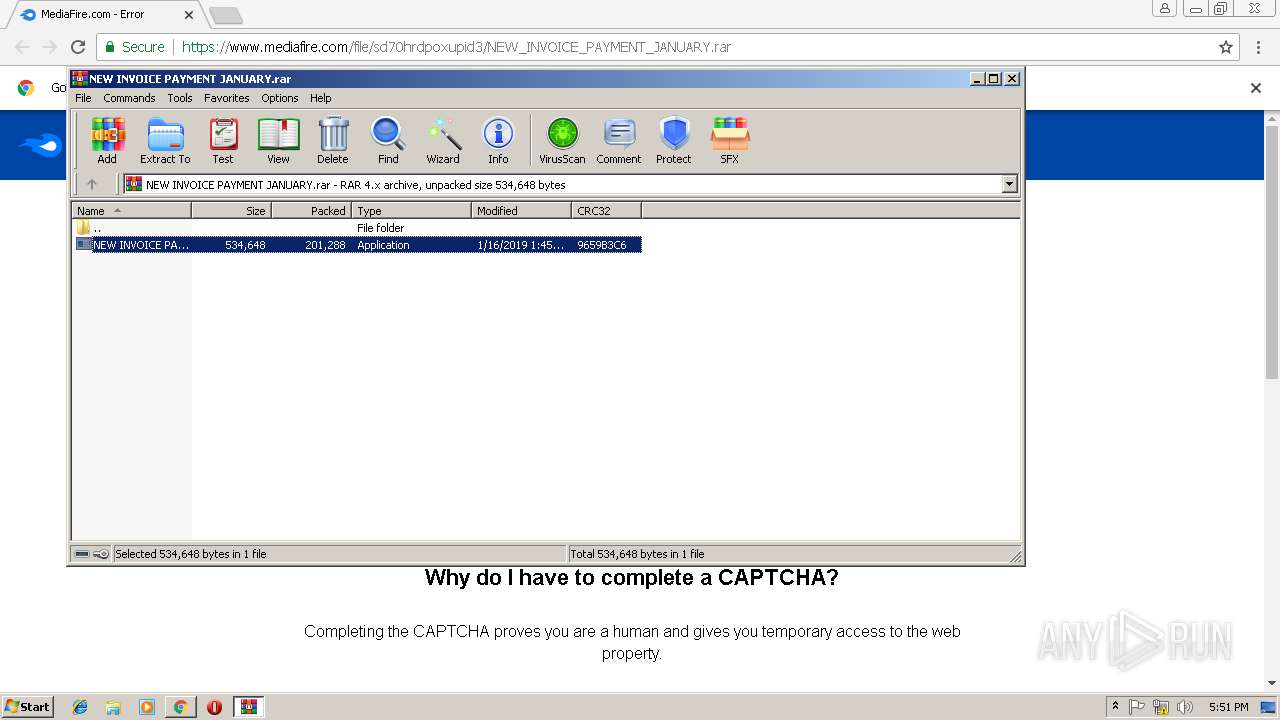
Application was dropped or rewritten from another process
- NEW INVOICE PAYMENT JANUARY.exe (PID: 3612)
SUSPICIOUS
Executable content was dropped or overwritten
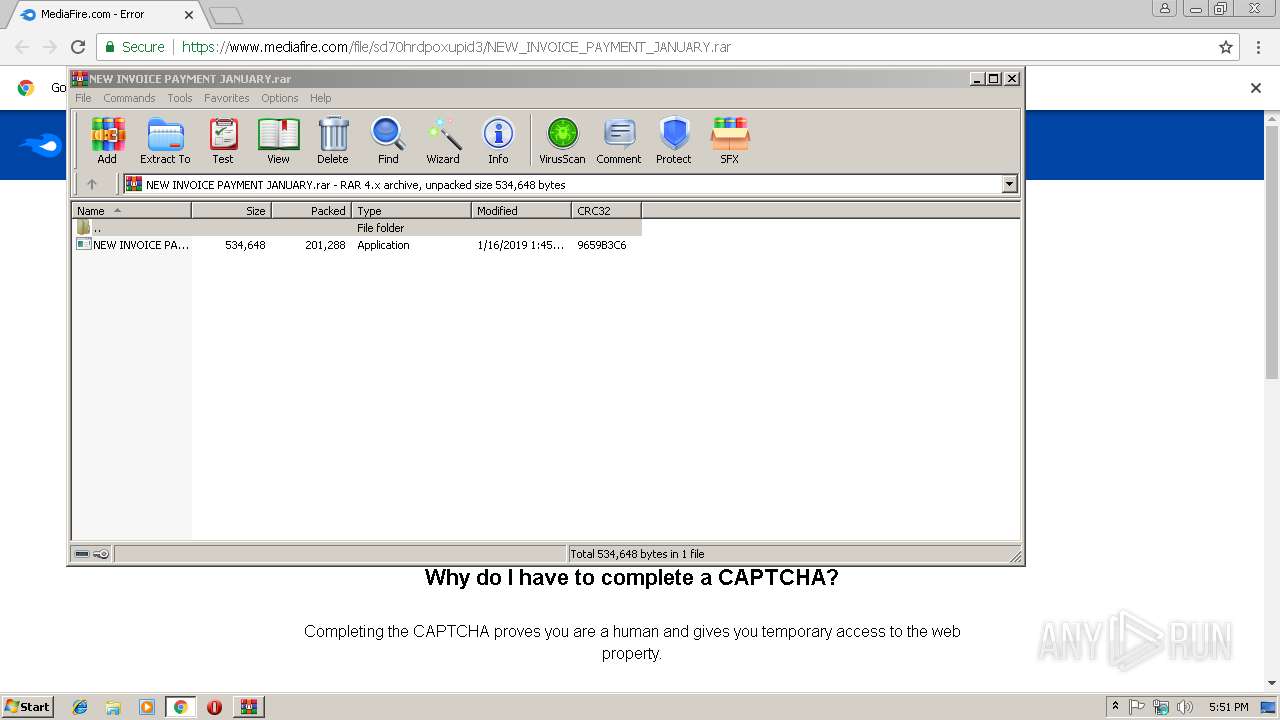
- WinRAR.exe (PID: 3716)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2984)
Application launched itself
- chrome.exe (PID: 2984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
11
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1528 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=B5765FECAF76E9E109A6DA453CB1BFCD --mojo-platform-channel-handle=2324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=A23055CE56D19F55B6D5059BEF9B09D8 --mojo-platform-channel-handle=3644 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=11BFF5CE3237868FC9DA1CE0606B0AEB --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9A0EAD4AFD8AFA7516EDF6E549A9802B --renderer-client-id=4 --mojo-platform-channel-handle=1892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2988 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://www.mediafire.com/file/sd70hrdpoxupid3/NEW_INVOICE_PAYMENT_JANUARY.rar | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --service-pipe-token=D98078C2AB2F37394DB98912B6D15B63 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=D98078C2AB2F37394DB98912B6D15B63 --renderer-client-id=3 --mojo-platform-channel-handle=2132 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,3031516371800422712,2667241742975915268,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=09708FFF45934FC3B19087F9ED5DECFF --mojo-platform-channel-handle=3444 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3612 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3716.48361\NEW INVOICE PAYMENT JANUARY.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3716.48361\NEW INVOICE PAYMENT JANUARY.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Bundesrath Integrity Level: MEDIUM Description: REPROCLAMATION Exit code: 0 Version: 4.02.0008 Modules
| |||||||||||||||
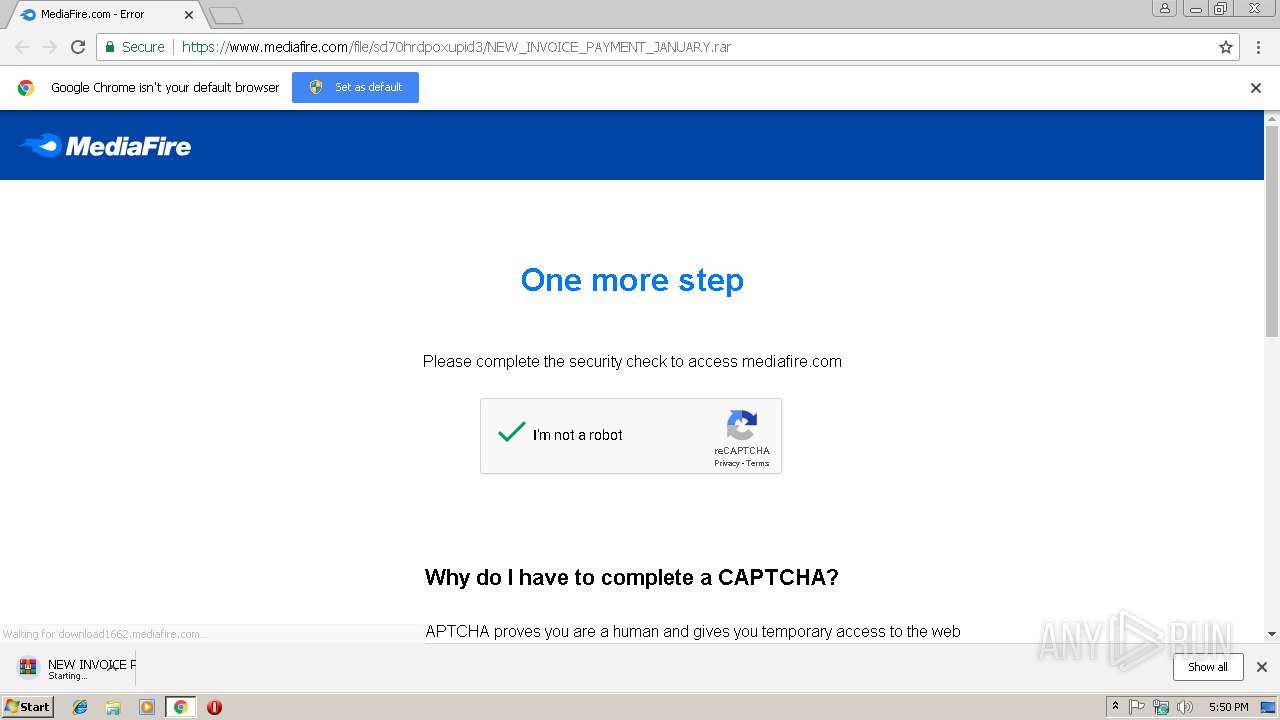
| 3716 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\NEW INVOICE PAYMENT JANUARY.rar" | C:\Program Files\WinRAR\WinRAR.exe | chrome.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 285
Read events
1 218
Write events
64
Delete events
3
Modification events
| (PID) Process: | (2924) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2984-13192221017622000 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2984-13192221017622000 |
Value: 259 | |||
| (PID) Process: | (2984) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
1
Suspicious files
17
Text files
69
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7b24d70b-91af-4da9-b195-dea8a7c6f700.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF20ea16.TMP | text | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\301fabe9-bc73-427f-9540-8663eddfbbd7.tmp | — | |
MD5:— | SHA256:— | |||
| 2984 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
15
DNS requests
10
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2984 | chrome.exe | 216.58.204.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 216.58.201.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 74.125.90.68:443 | www.google.com | Google Inc. | US | unknown |
2984 | chrome.exe | 104.19.195.29:443 | www.mediafire.com | Cloudflare Inc | US | shared |
2984 | chrome.exe | 172.217.17.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 199.91.152.162:443 | download1662.mediafire.com | MediaFire, LLC | US | malicious |
2984 | chrome.exe | 172.217.18.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 216.58.213.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 216.58.204.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2984 | chrome.exe | 172.217.22.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.mediafire.com |
| shared |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
download1662.mediafire.com |
| malicious |
sb-ssl.google.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2984 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |